-
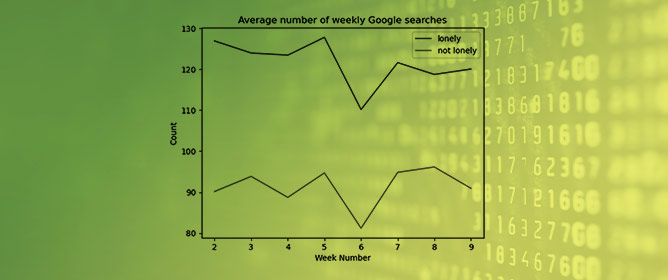 Predicting Loneliness through Digital Footprints on Google and YouTube
Predicting Loneliness through Digital Footprints on Google and YouTube -
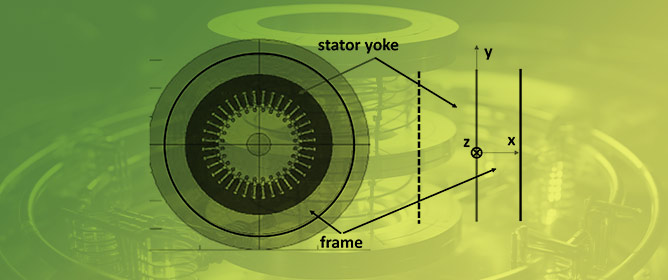 Influence of the Cast Iron Frame on the Distribution of the Magnetic Field in the Stator Yoke and Additional Power Losses in the Induction Motor
Influence of the Cast Iron Frame on the Distribution of the Magnetic Field in the Stator Yoke and Additional Power Losses in the Induction Motor -
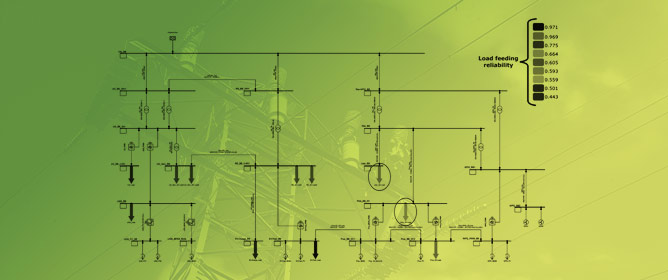 Innovative Method for Reliability Assessment of Power Systems: From Components Modeling to Key Indicators Evaluation
Innovative Method for Reliability Assessment of Power Systems: From Components Modeling to Key Indicators Evaluation -
 A Basic Design Tool for Grid-Connected AC–DC Converters Using Silcon Carbide MOSFETs
A Basic Design Tool for Grid-Connected AC–DC Converters Using Silcon Carbide MOSFETs
Journal Description
Electronics
Electronics
is an international, peer-reviewed, open access journal on the science of electronics and its applications published semimonthly online by MDPI. The Polish Society of Applied Electromagnetics (PTZE) is affiliated with Electronics and their members receive a discount on article processing charges.
- Open Access— free for readers, with article processing charges (APC) paid by authors or their institutions.
- High Visibility: indexed within Scopus, SCIE (Web of Science), CAPlus / SciFinder, Inspec, and other databases.
- Journal Rank: JCR - Q2(Electrical and Electronic Engineering) CiteScore - Q2 (Electrical and Electronic Engineering)
- Rapid Publication: manuscripts are peer-reviewed and a first decision is provided to authors approximately 15.6 days after submission; acceptance to publication is undertaken in 2.6 days (median values for papers published in this journal in the second half of 2023).
- Recognition of Reviewers: reviewers who provide timely, thorough peer-review reports receive vouchers entitling them to a discount on the APC of their next publication in any MDPI journal, in appreciation of the work done.
- Companion journals for Electronics include: Magnetism, Signals, Network and Software.
Impact Factor:
2.9 (2022);
5-Year Impact Factor:
2.9 (2022)
Latest Articles
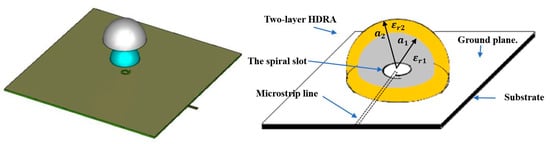
Wideband Millimeter-Wave Perforated Hemispherical Dielectric Resonator Antenna
Electronics 2024, 13(9), 1694; https://doi.org/10.3390/electronics13091694 (registering DOI) - 27 Apr 2024
Abstract
This paper presents a novel wideband circularly polarized millimeter-wave (mmWave) hemispherical dielectric resonator antenna (HDRA). Two distinct configurations of alumina dielectric resonator antennas (DRAs) are investigated, each featuring a different coating: the first configuration incorporates a polyimide layer, while the second involves a
[...] Read more.
This paper presents a novel wideband circularly polarized millimeter-wave (mmWave) hemispherical dielectric resonator antenna (HDRA). Two distinct configurations of alumina dielectric resonator antennas (DRAs) are investigated, each featuring a different coating: the first configuration incorporates a polyimide layer, while the second involves a perforated alumina. Both configurations demonstrate promising characteristics, including impedance and axial ratio (AR) bandwidths of 58% and 17.7%, respectively, alongside a maximum gain of 10 dBic at 28 GHz. Leveraging additive manufacturing technology, the HDRA with the perforated coating layer is fabricated, simplifying assembly and eliminating potential air gaps between layers, thereby enhancing the overall performance. This innovative approach yields a circularly polarized (CP) HDRA suitable for Beyond 5G (B5G) communication systems. Agreement between measurements and simulations validates the efficacy of the proposed design, affirming its potential in practical applications.
Full article
(This article belongs to the Special Issue Smart Communication and Networking in the 6G Era)
►
Show Figures
Open AccessArticle
Industry 4.0 Transformation: Analysing the Impact of Artificial Intelligence on the Banking Sector through Bibliometric Trends
by
Alina Georgiana Manta, Roxana Maria Bădîrcea, Nicoleta Mihaela Doran, Gabriela Badareu, Claudia Gherțescu and Jenica Popescu
Electronics 2024, 13(9), 1693; https://doi.org/10.3390/electronics13091693 (registering DOI) - 27 Apr 2024
Abstract
The importance of artificial intelligence in the banking industry is reflected in the speed at which financial institutions are adopting and implementing AI solutions to improve their services and adapt to new market demands. The aim of this research is to conduct a
[...] Read more.
The importance of artificial intelligence in the banking industry is reflected in the speed at which financial institutions are adopting and implementing AI solutions to improve their services and adapt to new market demands. The aim of this research is to conduct a bibliometric analysis of the involvement of artificial intelligence in the banking sector to provide a comprehensive overview of the current state of research to guide future directions and support the sustainable development of this rapidly expanding field. Another important objective is to identify research gaps and underexplored areas in the field of artificial intelligence in banking. The methodology used is a bibliometric analysis using VOSviewer, analysing 1089 papers from the Web of Science database. The results of the study provide relevant information for banking professionals but also for policy makers. Thus, the study highlights key areas where banks are using artificial intelligence to gain competitive advantage, thereby guiding practitioners in strategic decision making. Moreover, by identifying emerging trends and patterns in AI adoption, the study helps banking practitioners with foresight, enabling them to anticipate and prepare for future developments in the field. In terms of governmental implications, the study can contribute to the development of more nuanced regulatory frameworks that effectively balance the promotion of AI innovation with the protection of ethical standards and consumer protection.
Full article
(This article belongs to the Special Issue Future Trends of Artificial Intelligence (AI) and Big Data)
Open AccessArticle
Function-Level Compilation Provenance Identification with Multi-Faceted Neural Feature Distillation and Fusion
by
Yang Gao, Lunjin Liang, Yifei Li, Rui Li and Yu Wang
Electronics 2024, 13(9), 1692; https://doi.org/10.3390/electronics13091692 (registering DOI) - 27 Apr 2024
Abstract
In the landscape of software development, the selection of compilation tools and settings plays a pivotal role in the creation of executable binaries. This diversity, while beneficial, introduces significant challenges for reverse engineers and security analysts in deciphering the compilation provenance of binary
[...] Read more.
In the landscape of software development, the selection of compilation tools and settings plays a pivotal role in the creation of executable binaries. This diversity, while beneficial, introduces significant challenges for reverse engineers and security analysts in deciphering the compilation provenance of binary code. To this end, we present MulCPI, short for Multi-representation Fusion-based Compilation Provenance Identification, which integrates the features collected from multiple distinct intermediate representations of the binary code for better discernment of the fine-grained function-level compilation details. In particular, we devise a novel graph-oriented neural encoder improved upon the gated graph neural network by subtly introducing an attention mechanism into the neighborhood nodes’ information aggregation computation, in order to better distill the more informative features from the attributed control flow graph. By further integrating the features collected from the normalized assembly sequence with an advanced Transformer encoder, MulCPI is capable of capturing a more comprehensive set of features manifesting the multi-faceted lexical, syntactic, and structural insights of the binary code. Extensive evaluation on a public dataset comprising 854,858 unique functions demonstrates that MulCPI exceeds the performance of current leading methods in identifying the compiler family, optimization level, compiler version, and the combination of compilation settings. It achieves average accuracy rates of 99.3%, 96.4%, 90.7%, and 85.3% on these tasks, respectively. Additionally, an ablation study highlights the significance of MulCPI’s core designs, validating the efficiency of the proposed attention-enhanced gated graph neural network encoder and the advantages of incorporating multiple code representations.
Full article
(This article belongs to the Special Issue Machine Learning (ML) and Software Engineering, Volume II)
Open AccessArticle
Polymorphic Clustering and Approximate Masking Framework for Fine-Grained Insect Image Classification
by
Hua Huo, Aokun Mei and Ningya Xu
Electronics 2024, 13(9), 1691; https://doi.org/10.3390/electronics13091691 (registering DOI) - 27 Apr 2024
Abstract
Insect diversity monitoring is crucial for biological pest control in agriculture and forestry. Modern monitoring of insect species relies heavily on fine-grained image classification models. Fine-grained image classification faces challenges such as small inter-class differences and large intra-class variances, which are even more
[...] Read more.
Insect diversity monitoring is crucial for biological pest control in agriculture and forestry. Modern monitoring of insect species relies heavily on fine-grained image classification models. Fine-grained image classification faces challenges such as small inter-class differences and large intra-class variances, which are even more pronounced in insect scenes where insect species often exhibit significant morphological differences across multiple life stages. To address these challenges, we introduce segmentation and clustering operations into the image classification task and design a novel network model training framework for fine-grained classification of insect images using multi-modality clustering and approximate mask methods, named PCAM-Frame. In the first stage of the framework, we adopt the Polymorphic Clustering Module, and segmentation and clustering operations are employed to distinguish various morphologies of insects at different life stages, allowing the model to differentiate between samples at different life stages during training. The second stage consists of a feature extraction network, called Basenet, which can be any mainstream network that performs well in fine-grained image classification tasks, aiming to provide pre-classification confidence for the next stage. In the third stage, we apply the Approximate Masking Module to mask the common attention regions of the most likely classes and continuously adjust the convergence direction of the model during training using a Deviation Loss function. We apply PCAM-Frame with multiple classification networks as the Basenet in the second stage and conduct extensive experiments on the Insecta dataset of iNaturalist 2017 and IP102 dataset, achieving improvements of 2.2% and 1.4%, respectively. Generalization experiments on other fine-grained image classification datasets such as CUB200-2011 and Stanford Dogs also demonstrate positive effects. These experiments validate the pertinence and effectiveness of our framework PCAM-Frame in fine-grained image classification tasks under complex conditions, particularly in insect scenes.
Full article
(This article belongs to the Special Issue Applications of Artificial Intelligence in Image and Video Processing)
►▼
Show Figures
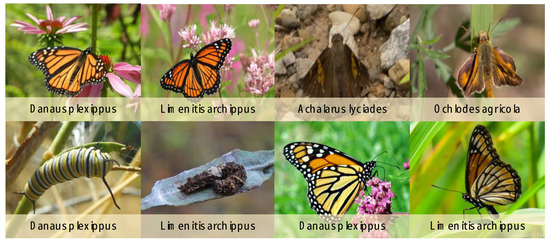
Figure 1
Open AccessArticle
ML-Based Software Defect Prediction in Embedded Software for Telecommunication Systems (Focusing on the Case of SAMSUNG ELECTRONICS)
by
Hongkoo Kang and Sungryong Do
Electronics 2024, 13(9), 1690; https://doi.org/10.3390/electronics13091690 (registering DOI) - 26 Apr 2024
Abstract
Software stands out as one of the most rapidly evolving technologies in the present era, characterized by its swift expansion in both scale and complexity, which leads to challenges in quality assurance. Software defect prediction (SDP) has emerged as a methodology crafted to
[...] Read more.
Software stands out as one of the most rapidly evolving technologies in the present era, characterized by its swift expansion in both scale and complexity, which leads to challenges in quality assurance. Software defect prediction (SDP) has emerged as a methodology crafted to anticipate undiscovered defects, leveraging known defect data from existing codes. This methodology serves to facilitate software quality management, thereby ensuring overall product quality. The methodologies of machine learning (ML) and one of its branches, deep learning (DL), exhibit superior accuracy and adaptability compared to traditional statistical approaches, catalyzing active research in this domain. However, it makes it hard to generalize, not only because of the disparity between open-source projects and commercial projects but also due to the differences in each industrial sector. Consequently, further research utilizing datasets sourced from diverse real-world sectors has become imperative to bolster the applicability of these findings. For this study, we utilized embedded software for use with the telecommunication systems of Samsung Electronics, supplemented by the introduction of nine novel features to train the model, and a subsequent analysis of the results ensued. The experimental outcomes revealed that the F-measurement metric has been enhanced from 0.58 to 0.63 upon integration of the new features, thereby signifying a performance augmentation of 8.62%. This case study is anticipated to contribute to bolstering the application of SDP methodologies within analogous industrial sectors.
Full article
(This article belongs to the Special Issue Software Analysis, Quality, and Security)
Open AccessFeature PaperArticle
Characterization of Unit Cells of a Reconfigurable Intelligence Surface Integrated with Sensing Capability at the mmWave Frequency Band
by
Biswarup Rana, Sung-Sil Cho and Ic-Pyo Hong
Electronics 2024, 13(9), 1689; https://doi.org/10.3390/electronics13091689 (registering DOI) - 26 Apr 2024
Abstract
Integrated sensing and communication (ISAC) is emerging as a main feature for 5G/6G communications. To enhance spectral and energy efficiencies in wireless environments, reconfigurable intelligent surfaces (RISs) will play a significant role in beyond-5G/6G communications. Multi-functional RISs, capable of not only reflecting or
[...] Read more.
Integrated sensing and communication (ISAC) is emerging as a main feature for 5G/6G communications. To enhance spectral and energy efficiencies in wireless environments, reconfigurable intelligent surfaces (RISs) will play a significant role in beyond-5G/6G communications. Multi-functional RISs, capable of not only reflecting or transmitting the beam in desired directions but also sensing the signal, wirelessly transferring power to nearby devices, harvesting energy, etc., will be highly beneficial for beyond-5G/6G applications. In this paper, we propose a nearly 2-bit unit cell of RISs integrated with sensing capabilities in the millimeter wave (mmWave) frequency band. To collect a very small fraction of the impinging signals through vias, we employed substrate integrated waveguide (SIW) technology at the bottom of the unit cell and a via. This enabled the sensing of incoming signals, requiring only a small amount of the impinging signal to be collected through SIW. Initially, we utilized Floquet ports and boundary conditions to obtain various parameters of the unit cells. Subsequently, we examined 1 × 3-unit cells, placing them on the waveguide model to obtain the required parameters of the unit cell. By using the waveguide and 1 × 3-unit cell arrays, the sensing amount was also determined.
Full article
(This article belongs to the Special Issue Trends and Prospects in 6G Wireless Communication)
Open AccessArticle
Joint Base Station Selection and Power Allocation Design for Reconfigurable Intelligent Surface-Aided Cell-Free Networks
by
Qingyu Bie, Yuhan Zhang, Yufeng He and Yilin Lin
Electronics 2024, 13(9), 1688; https://doi.org/10.3390/electronics13091688 (registering DOI) - 26 Apr 2024
Abstract
Cell-free (CF) networks can reduce cell boundaries by densely deploying base stations (BSs) with additional hardware costs and power sources. Integrating a reconfigurable intelligent surface (RIS) into CF networks can cost-effectively increase the capacity and coverage of future wireless systems. This paper considers
[...] Read more.
Cell-free (CF) networks can reduce cell boundaries by densely deploying base stations (BSs) with additional hardware costs and power sources. Integrating a reconfigurable intelligent surface (RIS) into CF networks can cost-effectively increase the capacity and coverage of future wireless systems. This paper considers an RIS-aided CF system where each user is supported by a devoted RIS and can establish connections with multiple BSs for coherent transmission. Specifically, each RIS can enhance signal transmission between users and their selected BSs through passive beam-forming, but also randomly scattered signals from other non-selected BSs to users, causing additional signals and interference in the network. To gain insights into the system performance, we first derive the average signal-to-interference-plus-noise ratio (SINR) received by each user in a closed-form expression. Subsequently, we formulate an optimization problem aimed at maximizing the weighted sum-SINR of all users in the RIS-CF network. This optimization considers both BS transmit power allocation and BS selections as variables to be jointly optimized. To tackle the complexity of this nonconvex optimization problem, we develop an innovative two-layer iterative approach that offers both efficiency and efficacy. This algorithm iteratively updates the transmit power allocation and BS selections to converge to a locally optimal solution. Numerical results demonstrate significant performance improvement for the RIS-CF network using our proposed scheme. These results also highlight the effectiveness of jointly optimizing BS transmit power allocation and BS selections in the RIS-CF network.
Full article
(This article belongs to the Special Issue Energy-Efficient Wireless Solutions for 6G/B6G)
Open AccessArticle
The Use of Technology Assisted by Artificial Intelligence Depending on the Companies’ Digital Maturity Level
by
Gabriel Brătucu, Eliza Ciobanu, Ioana Bianca Chițu, Adriana Veronica Litră, Alexandra Zamfirache and Marius Bălășescu
Electronics 2024, 13(9), 1687; https://doi.org/10.3390/electronics13091687 (registering DOI) - 26 Apr 2024
Abstract
Major companies in the global market have made significant investments in artificial intelligence-assisted technology to increase the value of their products and services, which gives the implementation of artificial intelligence an extremely important role. Starting from these premises, the authors set out to
[...] Read more.
Major companies in the global market have made significant investments in artificial intelligence-assisted technology to increase the value of their products and services, which gives the implementation of artificial intelligence an extremely important role. Starting from these premises, the authors set out to evaluate the transformation level of companies in terms of adopting technology based on artificial intelligence according to their level of digital maturity. For this purpose, qualitative research was used by deploying the inductive method, which allowed five distinct categories of companies with unique characteristics to be identified, generating an interval scale that illustrates the level of digital maturity and the ability to adopt and implement viable solutions based on artificial intelligence technology. This paper, in addition to identifying the digital transformation level of companies, offers solutions and recommendations for addressing the challenges encountered by the business environment, thus contributing to the understanding and development of strategies adapted to each situation that may appear on the market.
Full article
Open AccessArticle
Constant-Voltage and Constant-Current Controls of the Inductive Power Transfer System for Electric Vehicles Based on Full-Bridge Synchronous Rectification
by
Jin Cai, Pan Sun, Kai Ji, Xusheng Wu, Hang Ji, Yuxiao Wang and Enguo Rong
Electronics 2024, 13(9), 1686; https://doi.org/10.3390/electronics13091686 - 26 Apr 2024
Abstract
When an inductive power transfer (IPT) system conducts wireless charging for electric cars, the coupling coefficient between the coils is easily affected by fluctuations in the external environment. With frequent changes in the battery load impedance, it is difficult for the IPT system
[...] Read more.
When an inductive power transfer (IPT) system conducts wireless charging for electric cars, the coupling coefficient between the coils is easily affected by fluctuations in the external environment. With frequent changes in the battery load impedance, it is difficult for the IPT system to achieve constant-voltage and constant-current (CVCC) controls. A CVCC control method is proposed for the IPT system that has a double-sided LCC compensation structure based on full-bridge synchronous rectification. The proposed method achieved good dynamic stability and was able to effectively switch between the output current and voltage of the system by adjusting only the duty cycle of the switch on the secondary side of the rectification bridge. As a result, the system efficiency was improved. The output characteristics of the double-sided LCC compensation structure was derived and the conduction condition with zero voltage was analyzed by using four switches through two conduction time series of the rectifier circuit. Then, the output voltage of the synchronized rectifier was derived. The hardware implementation of the full-bridge controllable rectifier was described in detail. Finally, a MATLAB/Simulink 2018a simulation model was developed and applied to an 11 kW prototype to analyze and validate the design. The results showed that the designed system had good CVCC output characteristics and could maintain constant output under certain coupling offsets. Compared with semi synchronous rectification methods, the proposed method had a higher efficiency, which was 95.6% at the rated load.
Full article
(This article belongs to the Special Issue Recent Advances in High-Performance Wireless Power Transfer Technologies)
Open AccessArticle
An Enhanced Hidden Markov Model for Map-Matching in Pedestrian Navigation
by
Shengjie Ma, Pei Wang and Hyukjoon Lee
Electronics 2024, 13(9), 1685; https://doi.org/10.3390/electronics13091685 - 26 Apr 2024
Abstract
Map-matching is a core functionality of pedestrian navigation applications. The localization errors of the global positioning systems (GPSs) in smartphones are one of the most critical factors that limit the large-scale deployment of pedestrian navigation applications, especially in dense urban areas where multiple
[...] Read more.
Map-matching is a core functionality of pedestrian navigation applications. The localization errors of the global positioning systems (GPSs) in smartphones are one of the most critical factors that limit the large-scale deployment of pedestrian navigation applications, especially in dense urban areas where multiple road segments exist within the range of GPS errors, which can be increased by tall buildings neighboring each other. In this paper, we address two issues of practical importance for map-matching based on the Hidden Markov Model (HMM) in pedestrian navigation systems: large localization error in the initial phase of map-matching and HMM breaks in open field traversals. A heuristic method to determine the probability of initial states of the HMM based on a small number of GPS data received during the short warm-up period is proposed to improve the accuracy of initial map-matching. A simple but highly practical method based on a heuristic evaluation of near-future locations is proposed to prevent the malfunction of the Viterbi algorithm within the area of open fields. The results of field experiments indicate that the enhanced HMM constructed via the proposed methods achieves significantly higher map-matching accuracy compared to that of state of the art.
Full article
(This article belongs to the Special Issue Recent Research in Positioning and Activity Recognition Systems)
Open AccessArticle
Nonlinear Modeling and Control Strategy Based on Type-II T-S Fuzzy in Bi-Directional DC-AC Converter
by
Zhihua Chen, Ruochen Huang, Qiongbin Lin, Xinhong Yu and Zhimin Dan
Electronics 2024, 13(9), 1684; https://doi.org/10.3390/electronics13091684 - 26 Apr 2024
Abstract
Bi-directional DC-AC converters are widely used in the field of electric vehicle-to-grid. However, the inductance of the grid-side interface filter is affected by the length of the grid connection and the power level, which presents nonlinear characteristics. This poses challenges for high-performance grid
[...] Read more.
Bi-directional DC-AC converters are widely used in the field of electric vehicle-to-grid. However, the inductance of the grid-side interface filter is affected by the length of the grid connection and the power level, which presents nonlinear characteristics. This poses challenges for high-performance grid waveform control. In this paper, a modeling method for bi-directional DC-AC grid-connected converters based on type-II T-S fuzzy models is proposed, and the corresponding type-II T-S fuzzy control strategy is designed to address the parameter uncertainty and non-linearity issues. Simulation results show that type-II T-S fuzzy control offers superior control performance and better current waveform quality compared to type-I T-S fuzzy control under uncertainty parameter conditions. The effectiveness of the proposed strategy is further validated through a 1 kW prototype of a bi-directional DC-AC converter.
Full article
(This article belongs to the Special Issue Recent Advances in Electrified Vehicles and Transportation Electrification)
Open AccessReview
Neurogaming in Virtual Reality: A Review of Video Game Genres and Cognitive Impact
by
Jesus GomezRomero-Borquez, Carolina Del-Valle-Soto, J. Alberto Del-Puerto-Flores, Ramon A. Briseño and José Varela-Aldás
Electronics 2024, 13(9), 1683; https://doi.org/10.3390/electronics13091683 - 26 Apr 2024
Abstract
This work marks a significant advancement in the field of cognitive science and gaming technology. It offers an in-depth analysis of the effects of various video game genres on brainwave patterns and concentration levels in virtual reality (VR) settings. The study is groundbreaking
[...] Read more.
This work marks a significant advancement in the field of cognitive science and gaming technology. It offers an in-depth analysis of the effects of various video game genres on brainwave patterns and concentration levels in virtual reality (VR) settings. The study is groundbreaking in its approach, employing electroencephalograms (EEGs) to explore the neural correlates of gaming, thus bridging the gap between technology, psychology, and neuroscience. This review enriches the dialogue on the potential of video games as a therapeutic tool in mental health. The study’s findings illuminate the capacity of different game genres to elicit varied brainwave responses, paving the way for tailored video game therapies. This review contributes meaningfully to the state of the art by offering empirical insights into the interaction between gaming environments and brain activity, highlighting the potential applications in therapeutic settings, cognitive training, and educational tools. The findings are especially relevant for developing VR gaming content and therapeutic games, enhancing the understanding of cognitive processes, and aiding in mental healthcare strategies.
Full article
(This article belongs to the Special Issue Serious Games and Extended Reality (XR))
Open AccessArticle
Research on 3D Visualization of Drone Scenes Based on Neural Radiance Fields
by
Pengfei Jin and Zhuoyuan Yu
Electronics 2024, 13(9), 1682; https://doi.org/10.3390/electronics13091682 - 26 Apr 2024
Abstract
Neural Radiance Fields (NeRFs), as an innovative method employing neural networks for the implicit representation of 3D scenes, have been able to synthesize images from arbitrary viewpoints and successfully apply them to the visualization of objects and room-level scenes (<50 m2).
[...] Read more.
Neural Radiance Fields (NeRFs), as an innovative method employing neural networks for the implicit representation of 3D scenes, have been able to synthesize images from arbitrary viewpoints and successfully apply them to the visualization of objects and room-level scenes (<50 m2). However, due to the capacity limitations of neural networks, the rendering of drone-captured scenes (>10,000 m2) often appears blurry and lacks detail. Merely increasing the model’s capacity or the number of sample points can significantly raise training costs. Existing space contraction methods, designed for forward-facing trajectory or the 360° object-centric trajectory, are not suitable for the unique trajectories of drone footage. Furthermore, anomalies and cloud fog artifacts, resulting from complex lighting conditions and sparse data acquisition, can significantly degrade the quality of rendering. To address these challenges, we propose a framework specifically designed for drone-captured scenes. Within this framework, while using a feature grid and multi-layer perceptron (MLP) to jointly represent 3D scenes, we introduce a Space Boundary Compression method and a Ground-Optimized Sampling strategy to streamline spatial structure and enhance sampling performance. Moreover, we propose an anti-aliasing neural rendering model based on Cluster Sampling and Integrated Hash Encoding to optimize distant details and incorporate an L1 norm penalty for outliers, as well as entropy regularization loss to reduce fluffy artifacts. To verify the effectiveness of the algorithm, experiments were conducted on four drone-captured scenes. The results show that, with only a single GPU and less than two hours of training time, photorealistic visualization can be achieved, significantly improving upon the performance of the existing NeRF approaches.
Full article
(This article belongs to the Special Issue Advances in Computer Vision and Deep Learning and Its Applications)
Open AccessArticle
CFIEE: An Open-Source Critical Metadata Extraction Tool for RISC-V Hardware-Based CFI Schemes
by
Wenxin Li, Weike Wang and Senyang Li
Electronics 2024, 13(9), 1681; https://doi.org/10.3390/electronics13091681 - 26 Apr 2024
Abstract
Control flow critical metadata play a key role in hardware-based control flow integrity (CFI) mechanisms that effectively monitor and secure program control flow based on pre-extracted metadata. The existing control flow analysis tools exhibit some deficiencies, including inadequate compatibility with the RISC-V architecture,
[...] Read more.
Control flow critical metadata play a key role in hardware-based control flow integrity (CFI) mechanisms that effectively monitor and secure program control flow based on pre-extracted metadata. The existing control flow analysis tools exhibit some deficiencies, including inadequate compatibility with the RISC-V architecture, a steep learning curve, limited automation capabilities, and restricted data output formats. CFIEE is an open-source tool with a graphical interface for the automated extraction of control flow critical metadata. The tool possesses the capability to analyze RISC-V binary executables, transforming the binary into an intermediate representation (IR) in the form of the disassembled code, and extracting the critical metadata required for studying hardware-based CFI mechanism through a designed control flow transfer relationship analysis algorithm. The extracted metadata include program basic blocks and their corresponding hash values, control flow graphs, function call relationships, distribution of forward transfer instructions, etc. We selected 15 embedded system programs with processor adaptation for functional verification. The results demonstrate the CFIEE’s capability to automatically analyze programs within the supported RISC-V instruction set and generate comprehensive and precise metadata files. This tool can significantly enhance the efficiency of control flow metadata extraction and furnish configurable metadata for the hardware-based security mechanisms.
Full article
Open AccessArticle
Measurement and Assessment of Reactive, Unbalanced and Harmonic Line Losses
by
Qun Zhou, Yulin Dian, Xueshan Liu, Minrui Leng, Canyu Chen and Haibo Liu
Electronics 2024, 13(9), 1680; https://doi.org/10.3390/electronics13091680 - 26 Apr 2024
Abstract
►▼
Show Figures
This study investigates the feasibility of utilizing the line loss power factor to assess the reactive, unbalanced, and harmonic line losses in low-voltage distribution networks and explores the method of calculating decoupled line loss values based on this factor. To achieve this objective,
[...] Read more.
This study investigates the feasibility of utilizing the line loss power factor to assess the reactive, unbalanced, and harmonic line losses in low-voltage distribution networks and explores the method of calculating decoupled line loss values based on this factor. To achieve this objective, we establish preliminary definitions of single-phase and three-phase reactive, unbalanced, and harmonic line loss power factors, drawing upon the principles of electrical theory outlined in IEEE Standard 1459. These power factors serve as crucial indicators for evaluating the severity of line losses caused by reactive power, unbalance, and harmonic problems. Subsequently, the values of line loss attributed to reactive, unbalanced, and harmonic components are decoupled and quantified using the line loss power factor as a fundamental parameter. The effectiveness and accuracy of the proposed method were verified in Matlab simulation and physical experiments.
Full article

Figure 1
Open AccessArticle
Comparative Study on Schottky Contact Behaviors between Ga- and N-Polar GaN with SiNx Interlayer
by
Zhehan Yu, Yijun Dai, Ke Tang, Tian Luo, Shengli Qi, Smriti Singh, Lu Huang, Jichun Ye, Biplab Sarkar and Wei Guo
Electronics 2024, 13(9), 1679; https://doi.org/10.3390/electronics13091679 - 26 Apr 2024
Abstract
We conducted a comparative study on the characterization of Ga-polar and N-polar GaN metal–insulator–semiconductor (MIS) Schottky contact with a SiNx gate dielectric. The correlation between the surface morphology and the current–voltage (I–V) characteristics of the Ga- and N-polar GaN Schottky contact with
[...] Read more.
We conducted a comparative study on the characterization of Ga-polar and N-polar GaN metal–insulator–semiconductor (MIS) Schottky contact with a SiNx gate dielectric. The correlation between the surface morphology and the current–voltage (I–V) characteristics of the Ga- and N-polar GaN Schottky contact with and without SiNx was established. The insertion of SiNx helps in reducing the reverse leakage current for both structures, even though the leakage is still higher for N-polar GaN, consistent with the Schottky barrier height calculated using X-ray photoelectron spectroscopy. To optimize the electric property of the N-polar device, various substrate misorientation angles were adopted. Among the different misorientation angles of the sapphire substrate, the GaN MIS Schottky barrier diode grown on 1° sapphire shows the lowest reverse leakage current, the smoothest surface morphology, and the best crystalline quality compared to N-polar GaN grown on 0.2° and 2° sapphire substrates. Furthermore, the mechanism of the reverse leakage current of the MIS-type N-polar GaN Schottky contact was investigated by temperature-dependent I–V characterization. FP emissions are thought to be the dominant reverse conduction mechanism for the N-polar GaN MIS diode. This work provides a promising approach towards the optimization of N-polar electronic devices with low levels of leakage and a favorable ideality factor.
Full article
(This article belongs to the Special Issue Wide and Ultrawide Band Gap Semiconductors: Materials and Devices)
Open AccessArticle
Using Feature Selection Enhancement to Evaluate Attack Detection in the Internet of Things Environment
by
Khawlah Harahsheh, Rami Al-Naimat and Chung-Hao Chen
Electronics 2024, 13(9), 1678; https://doi.org/10.3390/electronics13091678 - 26 Apr 2024
Abstract
The rapid evolution of technology has given rise to a connected world where billions of devices interact seamlessly, forming what is known as the Internet of Things (IoT). While the IoT offers incredible convenience and efficiency, it presents a significant challenge to cybersecurity
[...] Read more.
The rapid evolution of technology has given rise to a connected world where billions of devices interact seamlessly, forming what is known as the Internet of Things (IoT). While the IoT offers incredible convenience and efficiency, it presents a significant challenge to cybersecurity and is characterized by various power, capacity, and computational process limitations. Machine learning techniques, particularly those encompassing supervised classification techniques, offer a systematic approach to training models using labeled datasets. These techniques enable intrusion detection systems (IDSs) to discern patterns indicative of potential attacks amidst the vast amounts of IoT data. Our investigation delves into various aspects of supervised classification, including feature selection, model training, and evaluation methodologies, to comprehensively evaluate their impact on attack detection effectiveness. The key features selected to improve IDS efficiency and reduce dataset size, thereby decreasing the time required for attack detection, are drawn from the extensive network dataset. This paper introduces an enhanced feature selection method designed to reduce the computational overhead on IoT resources while simultaneously strengthening intrusion detection capabilities within the IoT environment. The experimental results based on the InSDN dataset demonstrate that our proposed methodology achieves the highest accuracy with the fewest number of features and has a low computational cost. Specifically, we attain a 99.99% accuracy with 11 features and a computational time of 0.8599 s.
Full article
(This article belongs to the Section Artificial Intelligence)
►▼
Show Figures
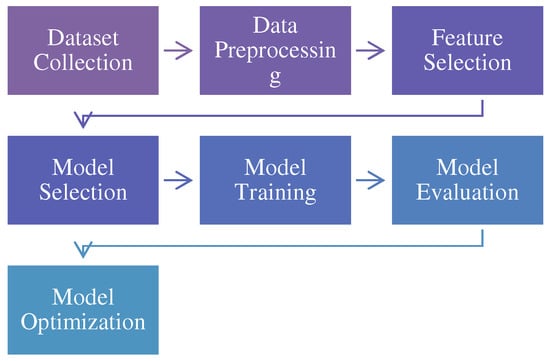
Figure 1
Open AccessArticle
Exhaustive Study into Machine Learning and Deep Learning Methods for Multilingual Cyberbullying Detection in Bangla and Chittagonian Texts
by
Tanjim Mahmud, Michal Ptaszynski and Fumito Masui
Electronics 2024, 13(9), 1677; https://doi.org/10.3390/electronics13091677 - 26 Apr 2024
Abstract
Cyberbullying is a serious problem in online communication. It is important to find effective ways to detect cyberbullying content to make online environments safer. In this paper, we investigated the identification of cyberbullying contents from the Bangla and Chittagonian languages, which are both
[...] Read more.
Cyberbullying is a serious problem in online communication. It is important to find effective ways to detect cyberbullying content to make online environments safer. In this paper, we investigated the identification of cyberbullying contents from the Bangla and Chittagonian languages, which are both low-resource languages, with the latter being an extremely low-resource language. In the study, we used both traditional baseline machine learning methods, as well as a wide suite of deep learning methods especially focusing on hybrid networks and transformer-based multilingual models. For the data, we collected over 5000 both Bangla and Chittagonian text samples from social media. Krippendorff’s alpha and Cohen’s kappa were used to measure the reliability of the dataset annotations. Traditional machine learning methods used in this research achieved accuracies ranging from 0.63 to 0.711, with SVM emerging as the top performer. Furthermore, employing ensemble models such as Bagging with 0.70 accuracy, Boosting with 0.69 accuracy, and Voting with 0.72 accuracy yielded promising results. In contrast, deep learning models, notably CNN, achieved accuracies ranging from 0.69 to 0.811, thus outperforming traditional ML approaches, with CNN exhibiting the highest accuracy. We also proposed a series of hybrid network-based models, including BiLSTM+GRU with an accuracy of 0.799, CNN+LSTM with 0.801 accuracy, CNN+BiLSTM with 0.78 accuracy, and CNN+GRU with 0.804 accuracy. Notably, the most complex model, (CNN+LSTM)+BiLSTM, attained an accuracy of 0.82, thus showcasing the efficacy of hybrid architectures. Furthermore, we explored transformer-based models, such as XLM-Roberta with 0.841 accuracy, Bangla BERT with 0.822 accuracy, Multilingual BERT with 0.821 accuracy, BERT with 0.82 accuracy, and Bangla ELECTRA with 0.785 accuracy, which showed significantly enhanced accuracy levels. Our analysis demonstrates that deep learning methods can be highly effective in addressing the pervasive issue of cyberbullying in several different linguistic contexts. We show that transformer models can efficiently circumvent the language dependence problem that plagues conventional transfer learning methods. Our findings suggest that hybrid approaches and transformer-based embeddings can effectively tackle the problem of cyberbullying across online platforms.
Full article
(This article belongs to the Special Issue Advanced Natural Language Processing Technology and Applications)
►▼
Show Figures
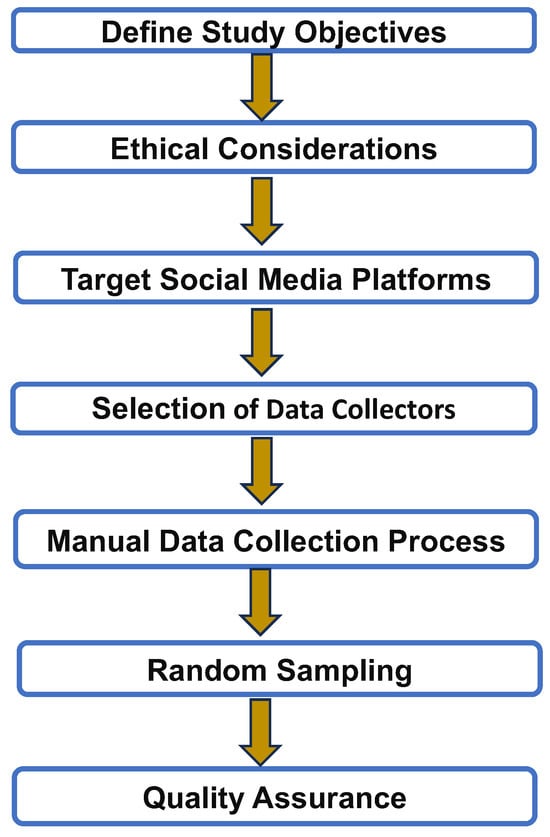
Figure 1
Open AccessArticle
A Dynamic Network with Transformer for Image Denoising
by
Mingjian Song, Wenbo Wang and Yue Zhao
Electronics 2024, 13(9), 1676; https://doi.org/10.3390/electronics13091676 - 26 Apr 2024
Abstract
Deep convolutional neural networks (CNNs) can achieve good performance in image denoising due to their superiority in the extraction of structural information. However, they may ignore the relationships between pixels to limit effects for image denoising. Transformer, focusing on pixel to pixel relationships
[...] Read more.
Deep convolutional neural networks (CNNs) can achieve good performance in image denoising due to their superiority in the extraction of structural information. However, they may ignore the relationships between pixels to limit effects for image denoising. Transformer, focusing on pixel to pixel relationships can effectively solve this problem. This article aims to make a CNN and Transformer complement each other in image denoising. In this study, we propose a dynamic network with Transformer for image denoising (DTNet), with a residual block (RB), a multi-head self-attention block (MSAB), and a multidimensional dynamic enhancement block (MDEB). Firstly, the RB not only utilizes a CNN but also lays the foundation for the combination with Transformer. Then, the MSAB adds positional encoding and applies multi-head self-attention, which enables the preservation of sequential positional information while employing the Transformer to obtain global information. Finally, the MDEB uses dimension enhancement and dynamic convolution to improve the adaptive ability. The experiments show that our DTNet is superior to some existing methods for image denoising.
Full article
(This article belongs to the Special Issue Big Model Techniques for Image Processing)
►▼
Show Figures
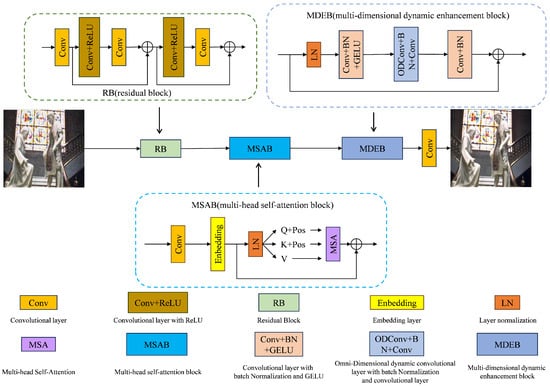
Figure 1
Open AccessArticle
State of Health (SOH) Estimation of Lithium-Ion Batteries Based on ABC-BiGRU
by
Hao Li, Chao Chen, Jie Wei, Zhuo Chen, Guangzhou Lei and Lingling Wu
Electronics 2024, 13(9), 1675; https://doi.org/10.3390/electronics13091675 - 26 Apr 2024
Abstract
As a core component of new energy vehicles, accurate estimation of the State of Health (SOH) of lithium-ion power batteries is essential. Correctly predicting battery SOH plays a crucial role in extending the lifespan of new energy vehicles, ensuring their safety, and promoting
[...] Read more.
As a core component of new energy vehicles, accurate estimation of the State of Health (SOH) of lithium-ion power batteries is essential. Correctly predicting battery SOH plays a crucial role in extending the lifespan of new energy vehicles, ensuring their safety, and promoting their sustainable development. Traditional physical or electrochemical models have low accuracy in measuring the SOH of lithium batteries and are not suitable for the complex driving conditions of real-world vehicles. This study utilized the black-box characteristics of deep learning models to explore the intrinsic correlations in the historical cycling data of lithium batteries, thereby eliminating the need to consider the internal chemical reactions of lithium batteries. Through Pearson correlation analysis, this study selects health indicators (HIs) from lithium battery cycling data that significantly impact SOH as input features. In the field of lithium batteries, this paper applies ABC-BiGRU for the first time to SOH prediction. Compared with other recursive neural network models, ABC-BiGRU demonstrates superior predictive performance, with maximum root mean square error and mean absolute error of only 0.016799317 and 0.012626847, respectively.
Full article
(This article belongs to the Special Issue Energy Storage, Analysis and Battery Usage)
►▼
Show Figures

Figure 1

Journal Menu
► ▼ Journal Menu-
- Electronics Home
- Aims & Scope
- Editorial Board
- Reviewer Board
- Topical Advisory Panel
- Instructions for Authors
- Special Issues
- Topics
- Sections & Collections
- Article Processing Charge
- Indexing & Archiving
- Editor’s Choice Articles
- Most Cited & Viewed
- Journal Statistics
- Journal History
- Journal Awards
- Society Collaborations
- Conferences
- Editorial Office
Journal Browser
► ▼ Journal BrowserHighly Accessed Articles
Latest Books
E-Mail Alert
News
Topics
Topic in
Applied Sciences, Designs, Electronics, Energies, JLPEA
Power Electronics Converters
Topic Editors: Mohsin Jamil, Yuanmao Ye, Tomasz PajchrowskiDeadline: 30 April 2024
Topic in
Coatings, Electronics, JSAN, Nanomaterials, Sensors
Modeling, Fabrication, and Characterization of Semiconductor Materials and Devices
Topic Editors: Andrei Avram, Ana-Maria Lepadatu, Florin Nastase, Martino AldrigoDeadline: 15 May 2024
Topic in
Energies, Materials, Electronics, Machines, WEVJ
Advanced Electrical Machine Design and Optimization Ⅱ
Topic Editors: Youguang Guo, Gang Lei, Xin BaDeadline: 31 May 2024
Topic in
Applied Sciences, Electricity, Electronics, Energies, Sensors
Power System Protection
Topic Editors: Seyed Morteza Alizadeh, Akhtar KalamDeadline: 20 June 2024

Conferences
Special Issues
Special Issue in
Electronics
Advance of Cooperative Working in Design, Visualization and Engineering
Guest Editors: Yuhua Luo, Tony HuangDeadline: 5 May 2024
Special Issue in
Electronics
Application of Power Electronics Technology in Energy System
Guest Editors: Jizhong Zhu, Lei Xi, Yun Liu, Weiye ZhengDeadline: 15 May 2024
Special Issue in
Electronics
Network Intrusion Detection Using Deep Learning
Guest Editor: Harald VrankenDeadline: 31 May 2024
Special Issue in
Electronics
Satellite-Terrestrial Integrated Internet of Things
Guest Editors: Min Jia, Zhenyu Na, Xin Liu, Lexi XuDeadline: 15 June 2024
Topical Collections
Topical Collection in
Electronics
Application of Advanced Computing, Control and Processing in Engineering
Collection Editors: Sudip Chakraborty, Robertas Damaševičius, Sergio Greco
Topical Collection in
Electronics
Instrumentation, Noise, Reliability
Collection Editor: Graziella Scandurra
Topical Collection in
Electronics
Computer Vision and Pattern Recognition Techniques
Collection Editor: Donghyeon Cho
Topical Collection in
Electronics
Deep Learning for Computer Vision: Algorithms, Theory and Application
Collection Editors: Jungong Han, Guiguang Ding