Abstract
Vehicle networking is a new paradigm in wireless technology that facilitates communication between vehicles in close proximity and in-vehicle internet access. This technology paves the way for a variety of safety, convenience and entertainment applications, including safety message exchange, real-time traffic information sharing and public internet access. The overall goal of vehicular networks is to create an efficient, safe and convenient environment for vehicles on the road. This paper presents a Sensitive Node Election (SNE) algorithm adapted to routing protocols in certain opportunistic network environments. The algorithm focuses on selecting the best agent for communication using an innovative approach for message forwarding. Quality of Service (QoS) metrics targeted for optimization include network end-to-end throughput and packet delivery, with the aim of improving the overall performance of the network. Our algorithm includes a stochastic rebroadcasting scheme that takes into account parameters, such as vehicle density, distance between vehicles and transmission distance, and adapts to various network conditions. Furthermore, the SNE algorithm uses a metric based on transmission distance and can dynamically adapt to application requirements, such as prioritization. It provides high throughput and minimizes delay. The results demonstrate the effectiveness of this approach in improving QoS in various vehicular ad hoc network (VANET) simulations and influencing the neural network ensemble (NNE Algorithm).
1. Introduction
The concept of vehicle technology has evolved in parallel with advances in wireless sensor networks and ad hoc networks. These advances have facilitated wireless communication between sensors located in different parts of the vehicle. Ad hoc network technology enables vehicles to communicate with other vehicles in the environment [1,2,3,4] using specific but different kinds of networks [5,6]. The integration of sensing and communication enables vehicles to meet different requirements and provide different services. For example, if a vehicle detects another vehicle approaching or deteriorating road conditions, the vehicle’s brakes will react. Similarly, if a potential accident is detected, safety features such as airbags and pretensioner seat belts can be activated. The traffic situation ahead can be communicated to the vehicle, and alternative routes can be suggested to reduce travel time. Internet access can be provided to vehicle passengers through conveniently located roadside units, which can be useful for safety applications and entertainment purposes, such as watching movies or surfing the internet.
This paper is organized as follows: after the introduction, in Section 2, we studied related work that is similar to our work to give the reader an idea of how our research was influenced. In Section 3, we explained the problems in (V2V) [7] communication to give the reader an idea about what our work is targeting. In Section 4, we explain our mathematical model in detail. In Section 5, we have our simulation results. Then, we conclude our work in Section 6 and discuss future work in Section 7.
2. Related Work
In recent years, routing protocols for vehicular networks have become an important topic in the literature. These protocols are divided into different types, such as probabilistic protocols, which are based on algorithms that select specific vehicles for communication among a large number of vehicles within the communication range of the source vehicle. The main advantage of using probability in routing protocols is that it does not flood the network with duplicate packets and thus leads to a significant improvement in network performance due to reduced collisions, increased throughput and reduced end-to-end delay. The authors of [2] introduced an adaptive pseudonym scheme grounded in public key cryptography (PKC), which replaces real-world identities with self-generated pseudonyms during the authentication process. This method strengthens privacy protection and guarantees non-repudiation, with pseudonym updates occurring dynamically in response to vehicular needs. Again in [3], the authors presented an anti-attack trust management scheme for VANETs, named AATMS, aimed at evaluating the trustworthiness of vehicles. By utilizing AATMS, vehicles can effectively identify and avoid malicious actors while cooperating with trusted ones. The scheme is inspired by the TrustRank algorithm by [5,6], originally developed to combat web spam. It incorporates both local and global trust metrics to represent inter-vehicle trust relationships. Bayesian inference is used to calculate local trust based on historical interactions. A selected group of seed vehicles—chosen according to local trust scores and social factors—forms the basis for assessing global trust across the network through the structure of local trust links. Simulation results confirm that AATMS can accurately distinguish between trustworthy and malicious vehicles, even under attack conditions. Among the various probabilistic routing protocols, notable examples include ticket-based techniques [7,8,9,10,11,12], which select vehicles based on stability, delay and cost metrics, as also presented in [13,14]. Furthermore, the REAR algorithm, introduced in [15], takes into account the possibility of receiving an alarm message and selects the next hop using physical parameters such as received strength signal measurements, loss path, and diffraction loss factors. Alternative solutions and diffraction loss coefficients are used to select the next hop vehicle. Another solution, the GVGrid algorithm [16], aims to find reliable routing paths that meet certain delay requirements by determining link lifetime based on link reliability [17]. The rebroadcast probability, the signal strength, and whether a vehicle can forward a long-distance packet in one hop are based on whether there are other vehicles that can rebroadcast the packet. However, since IF is probabilistic, and multiple vehicles can rebroadcast the same packet [18], the CAREFOR technology relies on the probability that at least two vehicles qualify as next-hop transmitters and the prospect that a vehicle will rebroadcast beyond one hop selection. While these techniques aim to reduce packet duplication in vehicular networks, as discussed in [19], it is important to consider various Quality of Service (QoS) requirements in applications such as throughput optimization. For example, the CodeTorrent protocol [20] considers the impact of vehicle density and mobility on network coding performance and uses network coding-based file alarms to optimize throughput. Similarly, the authors of [21] have developed a collaborative content distribution approach that uses multi-hop random network encoding in a distributed manner. Security considerations also require low end-to-end delay. In this paper, we propose a QoS-oriented probabilistic routing protocol for vehicular networks that aims to maximize throughput while considering end-to-end delays. This routing protocol selects vehicles on opposite sides of the highway, for example, vehicles on the east side. The effectiveness of the algorithm is evaluated in urban and highway vehicle scenarios.
3. Explaining the Problems in (V2V) Communication
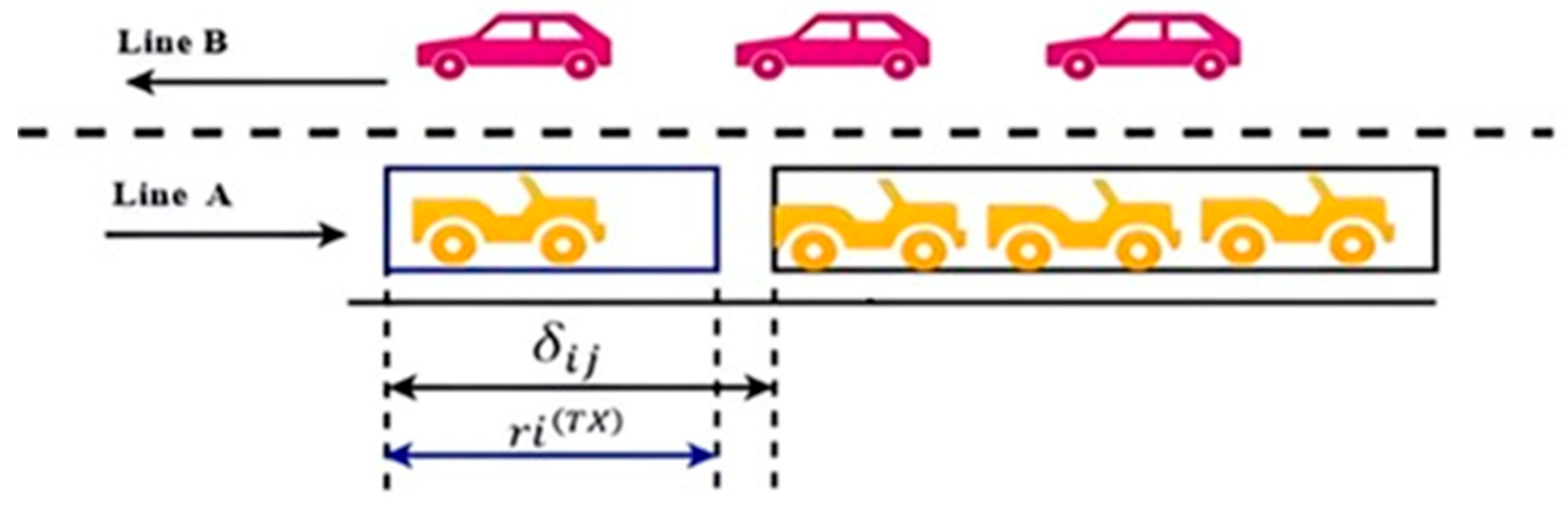
In this section, we introduce the QoS Sensitive Node Election (SNE) algorithm and analyze its main features. The reference scenario is a vehicular network consisting of two lines (lines A and B) with vehicles traveling in opposite directions, as shown in Figure 1 below. Vehicles in line A (B) are assumed to be traveling in the east (west) direction. The vehicle network exhibits a highly dynamic topology due to the various movement patterns that make up the vehicle groups. For example, vehicles traveling in the east–west direction are frequently disconnected, which significantly hinders stable and consistent vehicle-to-vehicle (V2V) communication. In particular, clusters forming on one side of the highway intermittently interact with clusters coming from the opposite direction. This contact provides an opportunity to opportunistically bridge traveling clusters in the same direction.
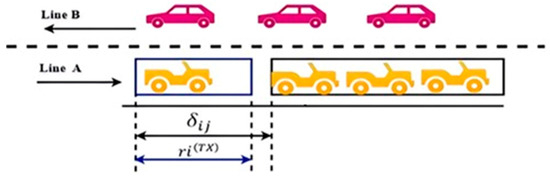
Figure 1.
Vehicle network connected through bridging.
The source (blue frame) vehicle chooses the next hop forwarder from the opposite line, e.g., (, because the gap between the vehicles in front is too large for V2V communication. The blue and black boxes represent the transmitter’s transmission range and cluster size respectively. In the direction of the road, this mirrors the typical bridge connection in VANETs. Consider a scenario where the source vehicle is traveling in line A. No V2V communication takes place along line A due to the large inter-vehicle gap between the source vehicle and its j-th neighbor, . This gap is so large that the sender’s possible link range, , is much shorter than . Therefore, the main objective of the SNE algorithm is to allow the source vehicle on the east side to select the best recipient from the opposite line (i.e., from the west side). Please note that [M] represents the number of vehicles per meter or kilometer, or in other words, the density.
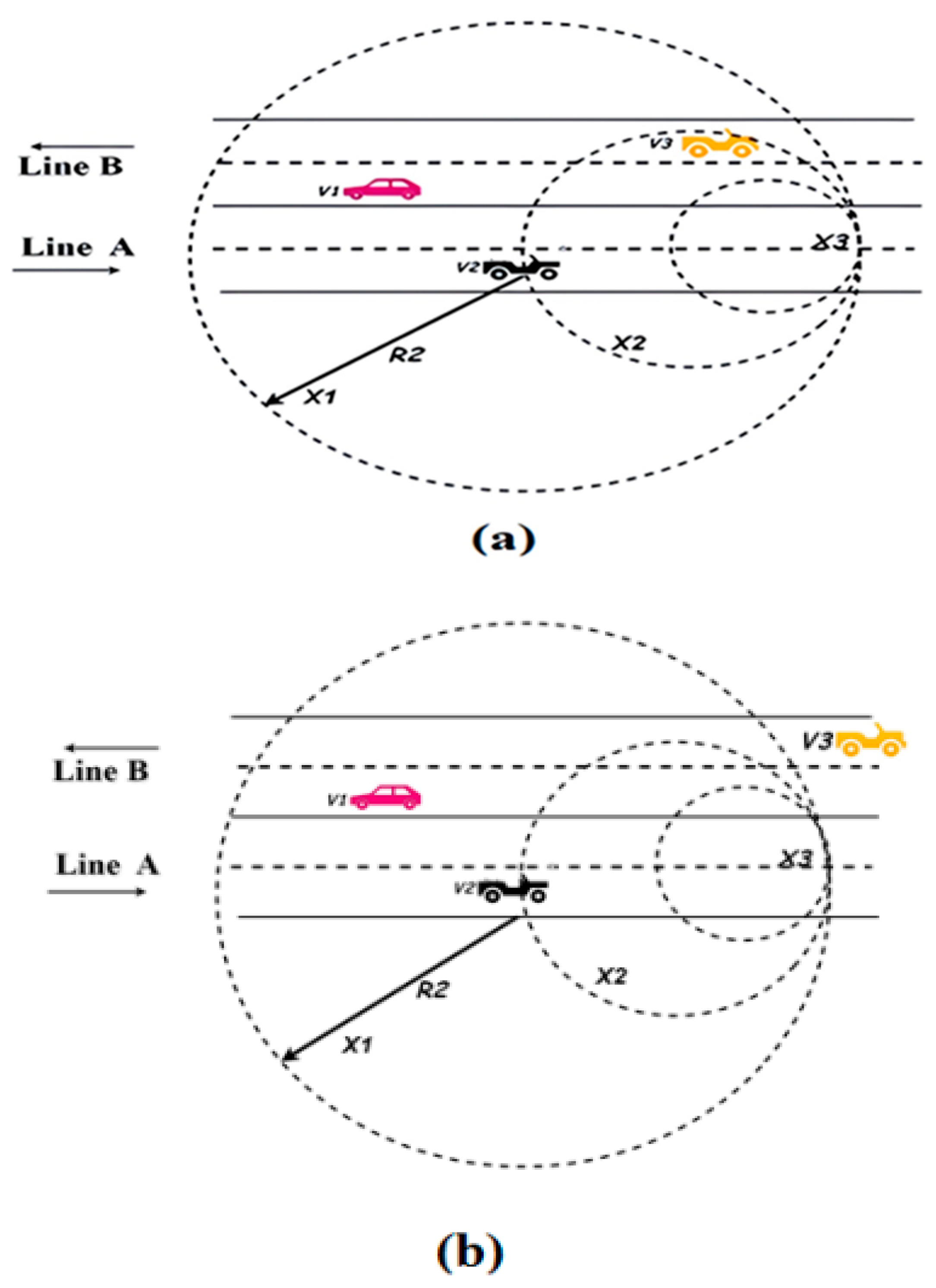
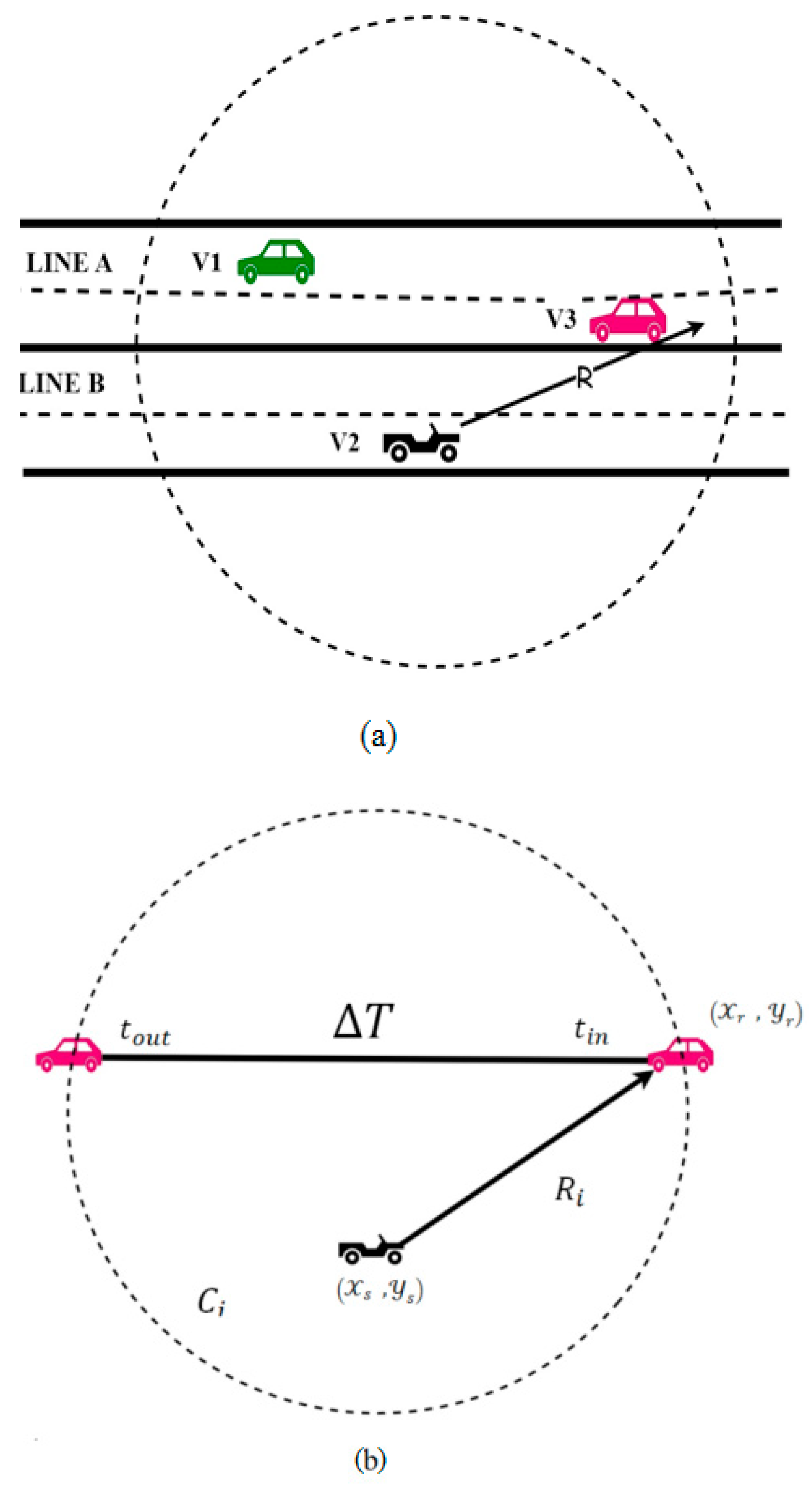
Figure 2 illustrates the main aspects of the SNE algorithm technique. (a) The transmission range of the source vehicle, represented by the black vehicle, is divided into smaller circular transmission areas (e.g., x1 > x2 > x3) to facilitate next-hop selection. (b) This scenario illustrates the trade-off between time delay and throughput performance associated with SNE technology. Consider the scenario in Figure 3, where a vehicle labeled V2 on the east side of the highway (line A) is preparing to transmit to the west side (line B); there are two candidate vehicles, V1 and V3, on the west side within V2’s transmission range; if V2 chooses V1, V1 is out of V2’s transmission range, and the established link is short-lived. Conversely, if V3 is selected, V3 stays in V2’s transmission range for a longer period of time, thus ensuring a longer-lasting connection. The shorter the connection duration, the more connections can be established in the same time frame. However, the establishment of new connections causes overhead in the ATB (Acknowledged Broadcast) and BRT (Broadcast-Ready Transformer) signaling and back-off algorithms.
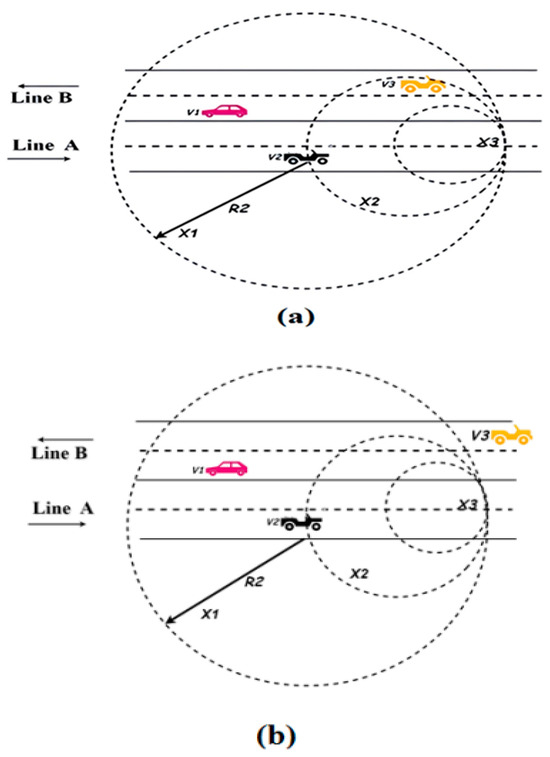
Figure 2.
Geometric modeling of inter-vehicle communication and distance-based routing regions in the proposed VANET framework. (a) Highway scenario illustrates the relative positions of vehicles V_1, V_2 and v_3 traveling along two lanes (Line A and Line B). The solid arrow R_2represents the direct communication distance between the reference vehicle V_2and neighboring vehicles. The dashed concentric circles denote multiple communication and sensing regions, where X_1, X_2 and X_3, (XXX) indicate progressively increasing distance thresholds used for neighbor discovery, relay selection, and routing decision-making, respectively. The outer dotted circle defines the maximum transmission coverage range, while the horizontal dashed lines represent lane boundaries and the direction arrows indicate vehicle movement. (b) Reverse-direction traffic scenario illustrating the dynamic variation of inter-vehicle distances and adaptive communication region selection under bidirectional vehicular mobility, highlighting the impact of opposite driving directions on routing range, neighbor detection, and relay node selection.
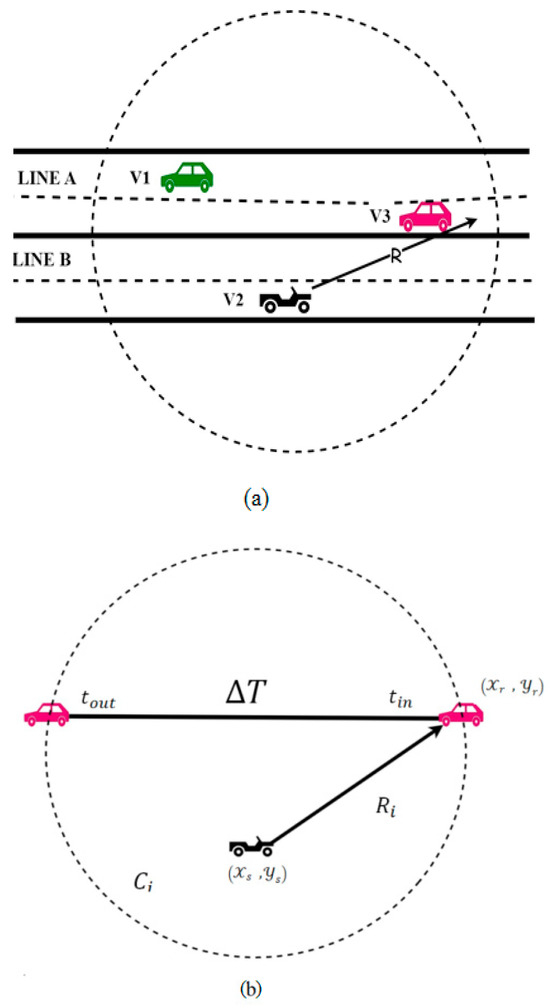
Figure 3.
Scheme for the next-hop forward selection algorithm based on the calculation of coverage crossing time, , assuming each vehicle has omnidirectional coverage, . (a) The red vehicle will experience a longer connection time with the blue vehicle compared to the green one, which is exiting the coverage area. (b) The coverage crossing time is calculated as an interval of time from .
4. Mathematical Model
To analyze the selection of the best candidate vehicle, the transmission range of the source vehicle is divided into smaller circular regions. As shown in Figure 2, these areas correspond to different proportions of the actual transmission range, i.e., full range, half range and one-quarter range. These areas represent the various distances at which a source (east) vehicle can select a destination (west) vehicle. We investigate the performance of the VANET with respect to different ranges for vehicle selection. The radius of circle X1 is R1, the radius of X2 is R2, and the radius of X3 is R3.
In Figure 2, XXX corresponds to the distance parameters X_1, X_2 and X_3, which define hierarchical communication and routing regions around the reference vehicle. These parameters represent progressively increasing distance thresholds used for neighbor discovery, relay node selection, and routing decision-making, respectively.
- X_1 Represents the immediate proximity zone, used for direct neighbor detection and short-range communication, ensuring low latency and high link reliability.
- X_2 Denotes the intermediate communication region, used for candidate relay node selection and multi-hop routing decisions, enabling efficient packet forwarding beyond the direct communication range.
- X_3 Indicates the extended coverage region, corresponding to the maximum allowable transmission distance, which supports long-range connectivity and network-wide routing optimization. This hierarchical distance modeling enables adaptive routing decisions, improves link stability, and enhances overall network reliability in highly dynamic VANET environments.
We develop an analytical model for the probability of finding vehicles in each circular area. Vehicle arrivals on the highway are modeled as a Poisson point process with density, λ (vehicles per unit distance), which is a standard and widely accepted assumption in traffic flow and VANET modeling [17]. The inter-vehicle distance between consecutive vehicles follows an exponential distribution, which naturally arises as the spacing distribution of a Poisson process and is mathematically valid for continuous distance variables. This represents the probability that at least one candidate vehicle exists within region X_i.
Revised Receiver Selection Probability:
where:
- is the inter-vehicle distance;
- is the radius of region ;
- is the coverage crossing time;
- is the minimum required connection duration.
Cumulative Distribution Function (CDF):
Probability That a Vehicle Exists Within Distance r:
Probability of Finding at Least One Vehicle in Coverage Zone for a Circular Transmission Region with Radius
Final Expanded Expression:
This formulation ensures mathematical consistency, as the exponential distribution appropriately models continuous inter-vehicle distances, while the Poisson process models vehicle arrivals. The model is used throughout the analytical framework of the SNE algorithm to evaluate candidate vehicle selection, coverage crossing time, and link availability under varying traffic densities.
Figure 3b shows a scheme for the calculation of . Note that since each vehicle is assumed to have a GPS device, the coordinates of the transmitting and receiving vehicle locations (denoted as _s and respectively) are known [21,22,23,24].
5. SNE Algorithm
5.1. Overall Performance of SNE Algorithm
The simulation results show that the furthest range improves efficiency. However, it is lower in terms of the average time delay; SNE assumes that for closer vehicles, the throughput worsens, but the time delay decreases. Consider the scenario in Figure 2b. If vehicle V2 on the east side selects the farthest vehicle in the transmission range (line B) on the west side, the SNE algorithm selects vehicle V1. This results in a smaller delay time average, but a lower throughput. If vehicle V2 waits for a short, expected time, vehicle V3 can be selected, which may lead to a high-throughput result but may slightly increase the time delay. The choice between vehicles V1 and V3 can be resolved by restricting the region where the east vehicle chooses the west vehicle. This constraint should only be based on a type of application that requires minimum delay regardless of throughput, whereas other applications prioritize maximum throughput but are tolerant of delay. To handle this trade-off, the algorithm should allow vehicles to choose the farthest vehicle available in a given area within the transmission range. The following subsection describes the SNE algorithm, a probabilistic routing protocol that guarantees the selection of the farthest vehicle that can forward packets within the transmission range (i.e., the next-hop forward). The algorithm aims to improve the QoS of routing protocols in VANETs by selecting the best candidate among the vehicles on the opposite side (i.e., line B) as a bridge for communication between vehicles on the opposite side (i.e., line A). SNE’s QoS indicators calculate the network throughput and the average latency of packet transmission with and without packet collision. Consider the scenario in Figure 3, where the source vehicle is traveling alone in line A:
- Step 1: The source vehicle on the east side assesses the current vehicle density, , within the transmission range. Based on the vehicle density, a circular area ( for i = 1, 2, 3) with a suitable radius (for i = 1, 2, 3) is determined, where the vehicles of the western line (line B) can respond to the transmitting source vehicle.
- Step 2: The source vehicle sends an Acknowledged Broadcast (ATB) to the tall vehicles within the transmission range. This ATB message (broadcast signal) contains the local vehicle density of the source node, the GPS location of the source node and the radius calculated from step 1.
- Step 3: When all vehicles within the transmission range of the source node receive the ATP message, they check whether their location meets the criteria specified in the message. If the requirements are not met, the packet is discarded. Conversely, if the requirements are met, they proceed to calculate the probability of reliable transmission (RF), as described in [18].
The decision to retransmit packets is made by each vehicle by comparing the RF probability and the transmission threshold (i.e., ):
where is the transmission range of the i-th vehicle, and is the vehicle density. If the calculated RF value is larger than the threshold, then the vehicle broadcasts an ATB message. Otherwise, the vehicle refrains from any rebroadcasting. The ATB message includes the GPS location of the vehicle.
- Step 4. The source vehicle that receives the ATB is not the destination. A description of each control message used in this algorithm is given in Table 1. Some applications require minimum delay independent of throughput, some require the opposite, and some require a trade-off between throughput and average time delay. In order to make the algorithm work for different applications, a Full-Range Partition (FRP) parameter was added, which limits the network performance according to QoS requirements: the FRP message determines which of the responding vehicles is the furthest away. The receiving vehicle discards the packet if its vehicle, the FRP parameter, is a value greater than 0 and equal to or less than 1, representing a fraction of the total transmission range. From here, vehicles on the west side (line B) can be selected by vehicles on the east side (line A) [25]. uses an FRP of 0.5, and the FRP for is equal to 1. If the requirement is to ensure minimum average delay regardless of throughput, the FRP factor is equal to 1. The smaller the FRP variable, the better the throughput of the network and the higher the average delay. However, if the FRP parameter is too small, the area from which western vehicles can be selected is very limited, and connections may not be established. Therefore, the FRP parameters mainly depend on the range of transmission and vehicle density.

Table 1.
SNE classification and analysis of message exchange.
Table 1.
SNE classification and analysis of message exchange.
| Message | Content |
|---|---|
| BRT |
|
| ATB |
|
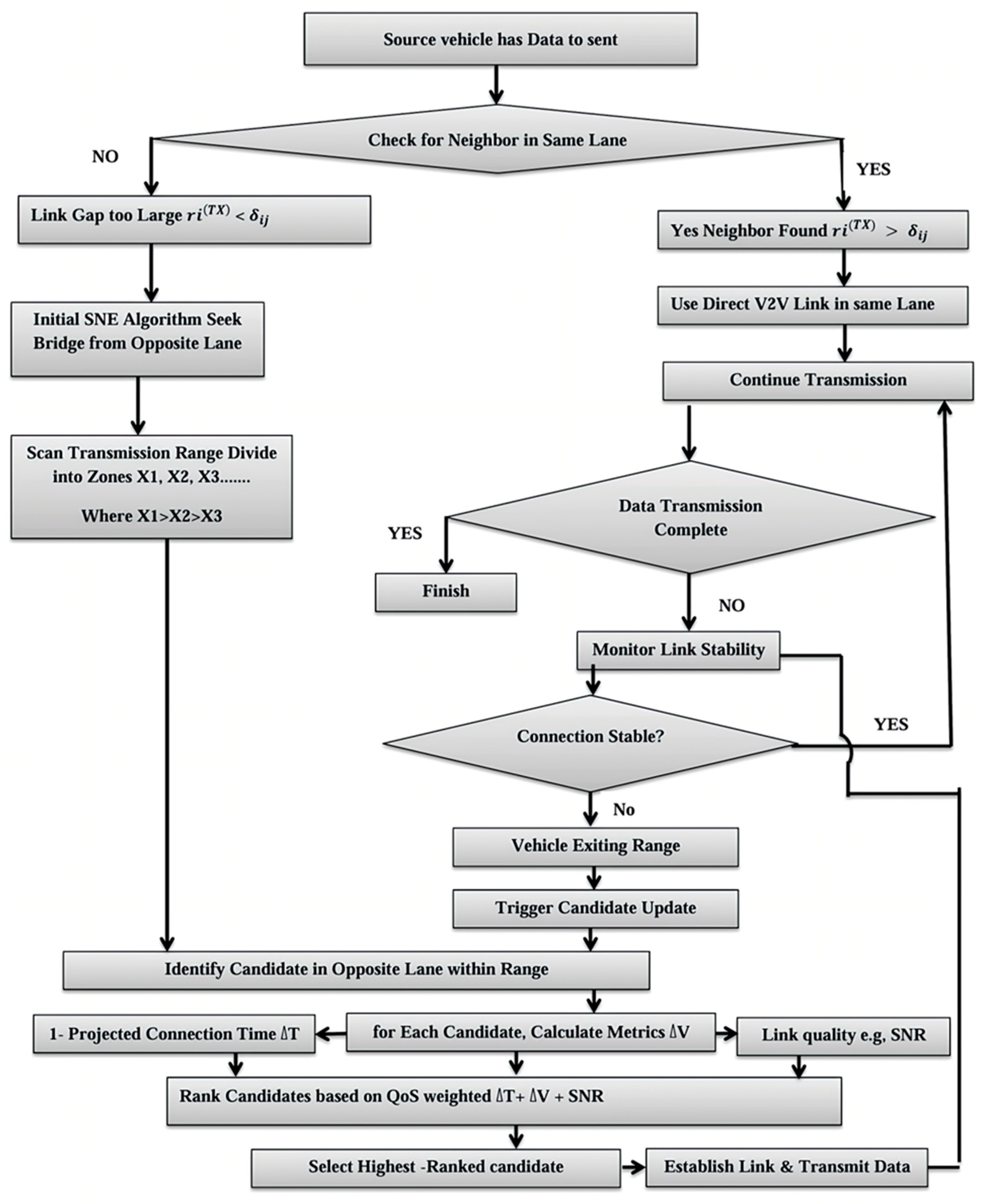
- Finally, we can summarize the SNE algorithm sequence in Figure 4 as follows:
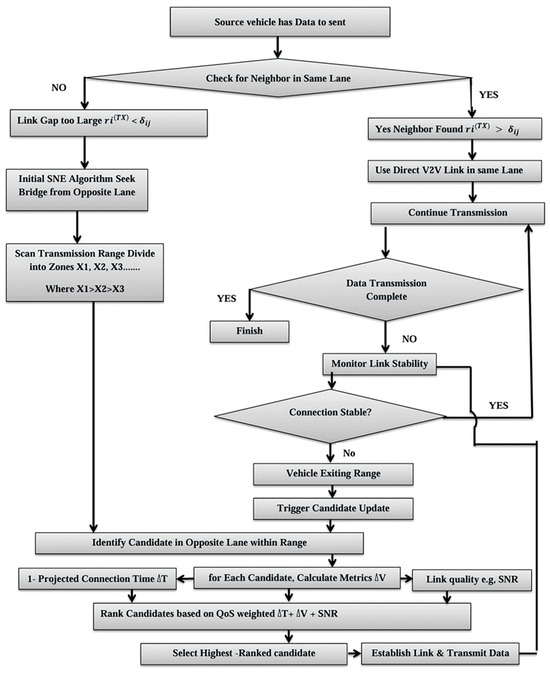 Figure 4. Introducing the QoS Sentient Node Election (SNE) algorithm.
Figure 4. Introducing the QoS Sentient Node Election (SNE) algorithm.- 1—Start and Problem Detection: The procedure begins when a vehicle needs to send data. The first step is to check if a direct vehicle-to-vehicle connection is possible within its lane.
- 2—SNE Initiation: The SNE algorithm starts when a direct connection fails, aiming to find a bridge node.
- 3—Candidate Identification: The source vehicle scans its range to find potential candidate vehicles in the opposite lane.
- 4—The Core Trade-Off (Evaluation): The algorithm evaluates candidates based on their expected connection duration. Candidate V1 is near the edge of the range, leading to a short relationship.
- 5—Decision and Outcome: The SNE algorithm balances trade-offs between brief connections, which allow for more connections but have high overhead and long connections, which are stable but limit connections.
- 6—Final Action: The algorithm connects data transmission by selecting the best candidate for the application’s Quality of Service needs, focusing on delay and throughput.
5.2. Computational and Memory Complexity
Let us look at how the SNE algorithm actually performs in a VANET, focusing on what each vehicle has to handle in terms of computation and memory. Processing Time Analysis: The SNE algorithm runs through four main steps every time a vehicle needs to transmit. First, it determines how many cars are nearby by counting regular beacon messages. This is just a simple counter—no matter how crowded it becomes, this part does not slow down. Next, it determines the selection zone radius by multiplying the FRP parameter by the transmission range. Again, this step is very fast and does not depend on how many vehicles are around. The third step is a little more complicated. The vehicle sends an ATB message and waits for replies from its neighbors. The more replies, the more work—so here, the processing time grows with the number of responses. Finally, the source vehicle picks out the farthest responder, which also takes longer when there are more candidates to choose from. In the end, how long it all takes per vehicle mostly depends on how many neighbors are within range. Even in heavy traffic, though, this remains fairly manageable.
Memory Usage Analysis: Each vehicle keeps a few things in its memory: a local density value, a candidate responder list (with GPS and IDs), the FRP parameter, the transmission range, its own GPS location, and some state variables for the algorithm. Altogether, this takes up less than 5 KB of memory.
Measured Performance Overhead: We tracked the average processing time and memory use for each vehicle under different traffic conditions. This resulted in the SNE algorithm adding very little overhead—the processing time stays under 2 ms per vehicle, and memory usage is minimal. Please see Table 2, below.
Comparison with Existing Protocols: SNE, when compared to AODV and GPSR under the same conditions, has similar or lower overhead while achieving better throughput and latency. This shows that SNE is efficient for vehicles with limited processing power. The SNE algorithm has similar or lower overhead than AODV and GPSR while improving throughput and reducing latency. It is computationally efficient, making it suitable for vehicles with limited processing resources.

Table 2.
Measured performance.
Table 2.
Measured performance.
| Vehicle Density (veh/km) | Avg. Vehicles in Range | Avg. Processing Time (ms) | Avg. Memory Usage (KB) |
|---|---|---|---|
| 10 | 8 | 0.45 | 1.2 |
| 30 | 24 | 1.10 | 2.8 |
| 50 | 40 | 1.85 | 4.5 |
6. Simulation and Discussion
6.1. Simulation Results
This section presents simulation results for the SNE algorithm and shows the improvement in Quality of Service (QoS); please see Figure 4. The indicators evaluated in this simulation include throughput, total effective communication time and average time delay. The total effective transmission time is calculated by excluding the time spent on connection setup and vehicle selection for communication. Simulations were performed using a proprietary VANET simulator. Details of the various parameters used in the simulations are given in Table 3.

Table 3.
Parameter simulation.
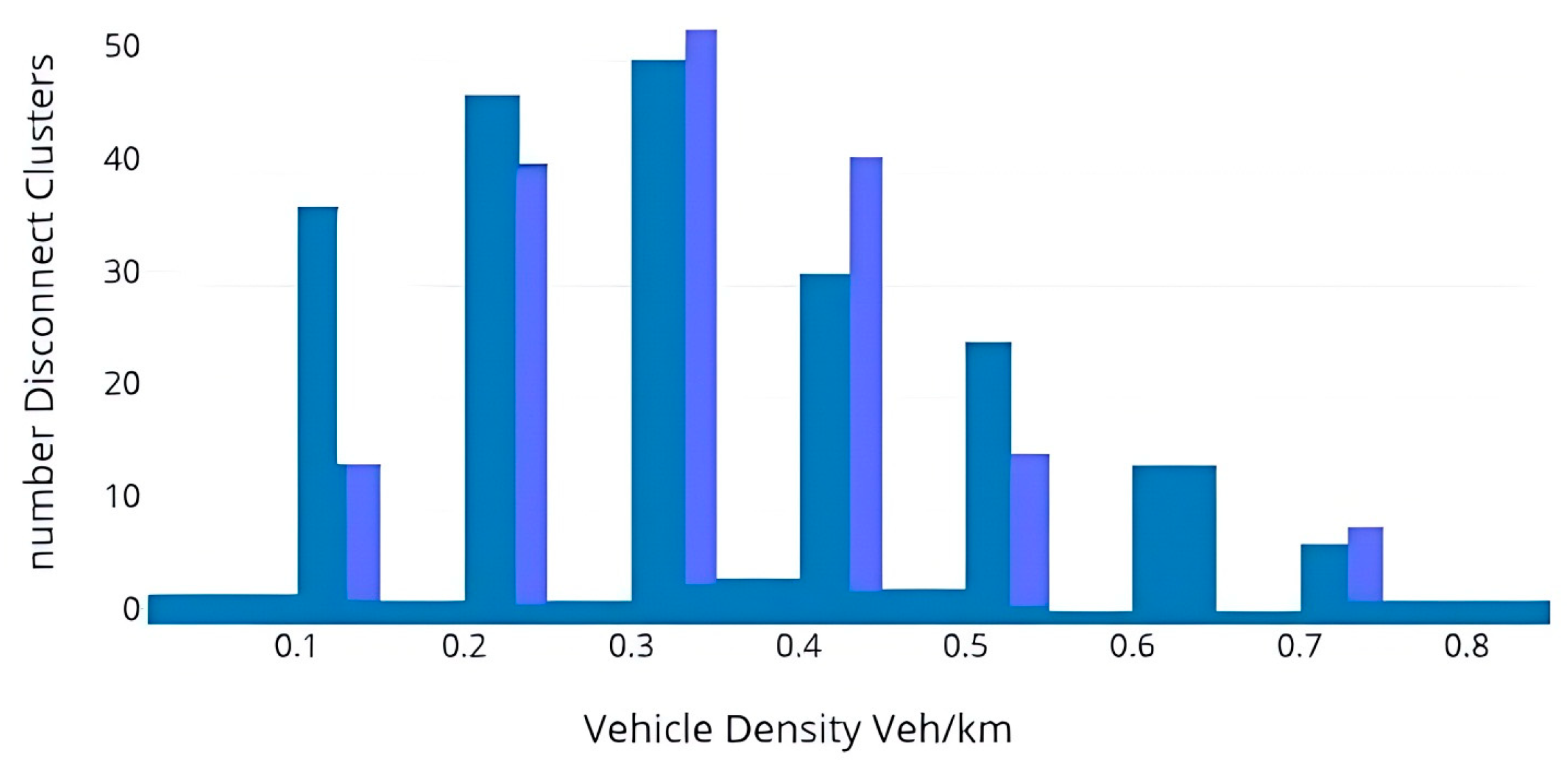
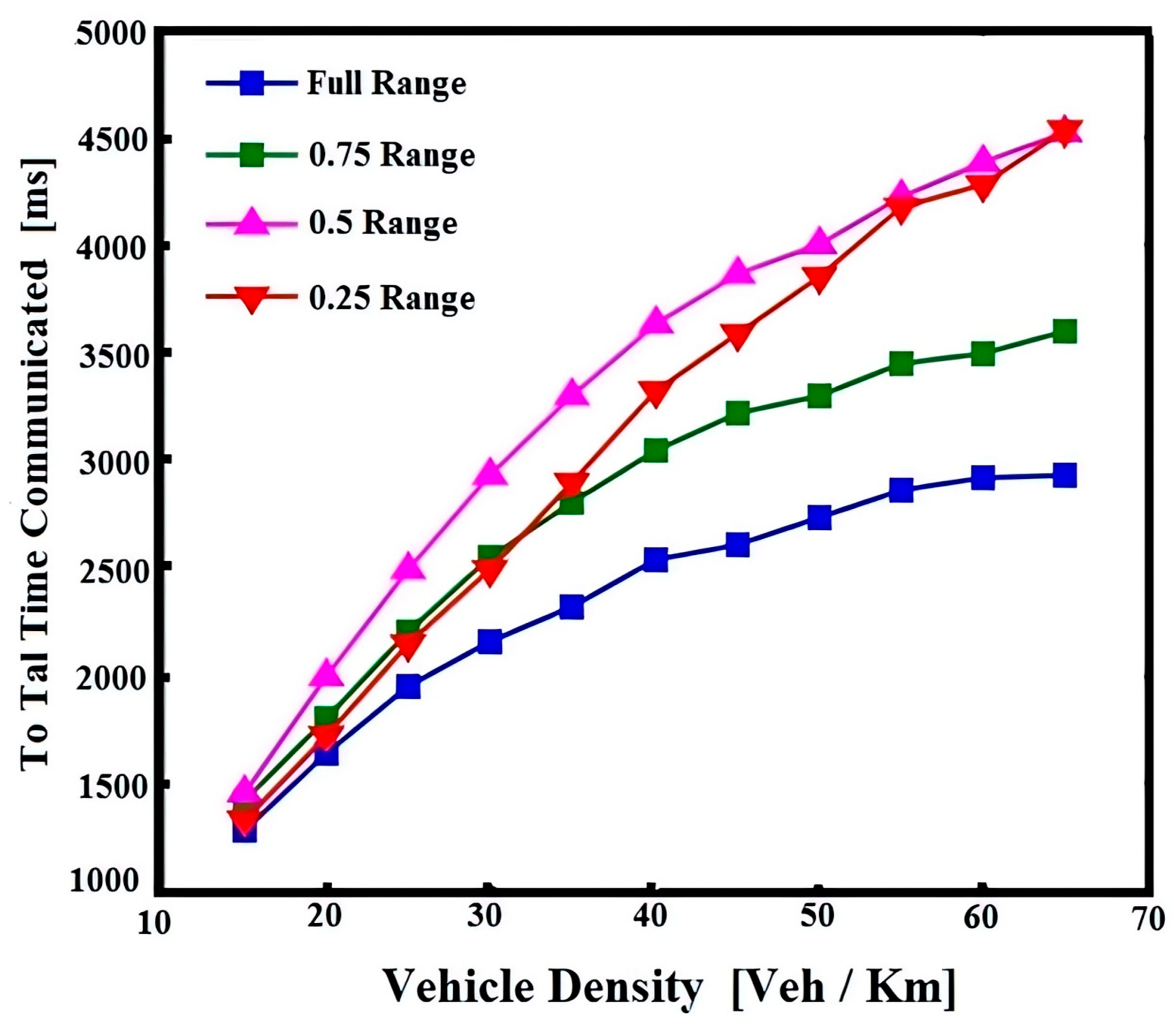
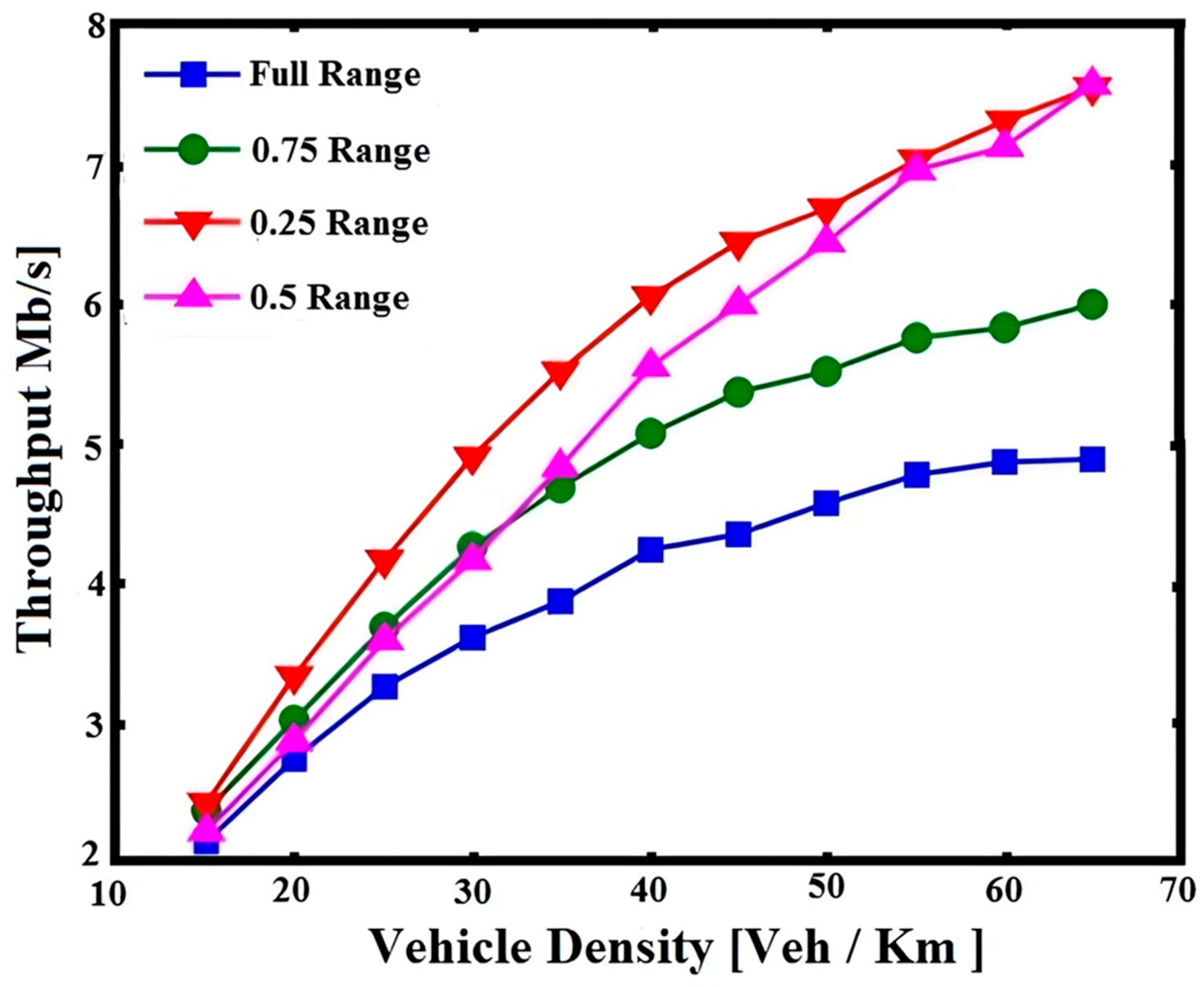
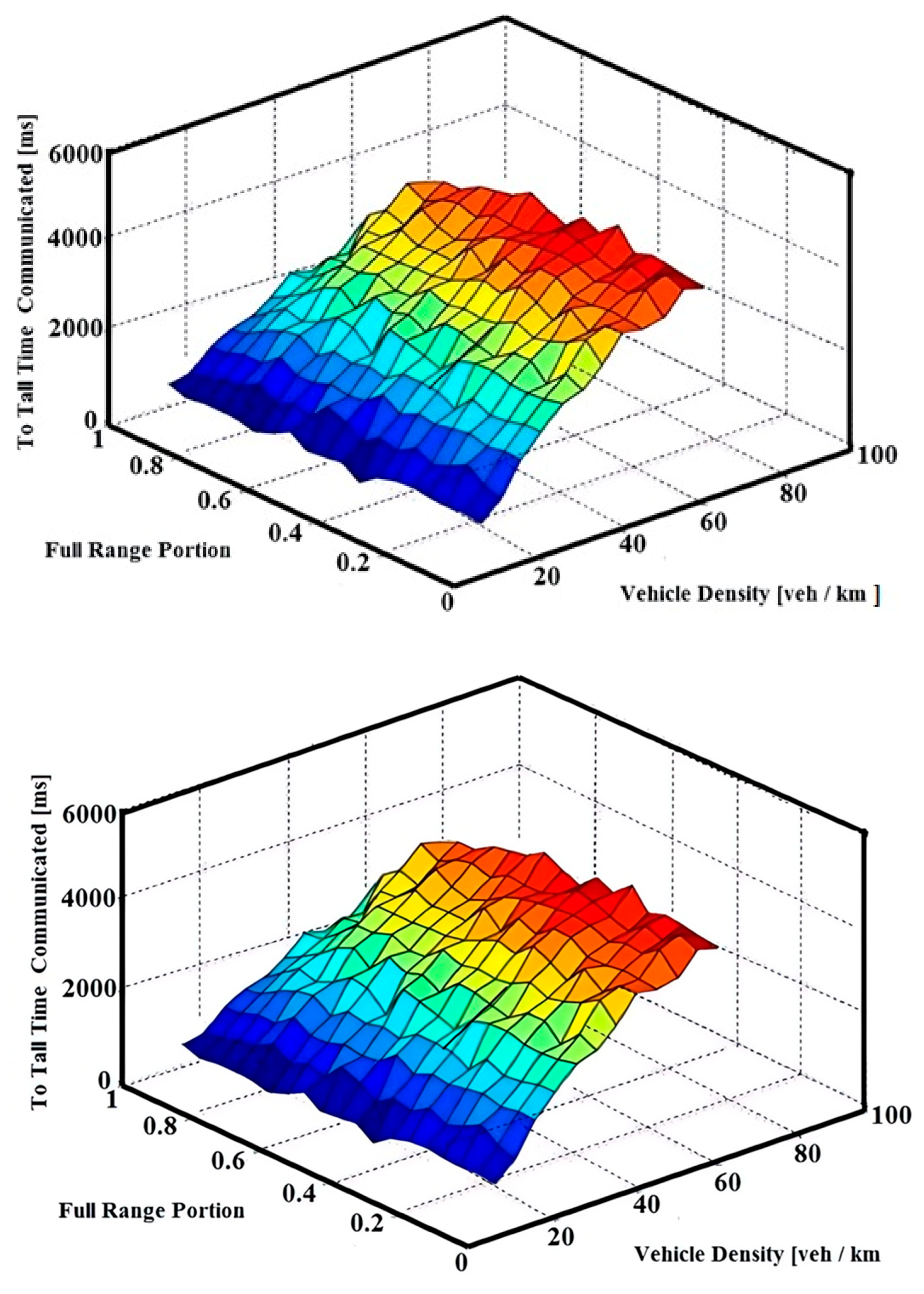
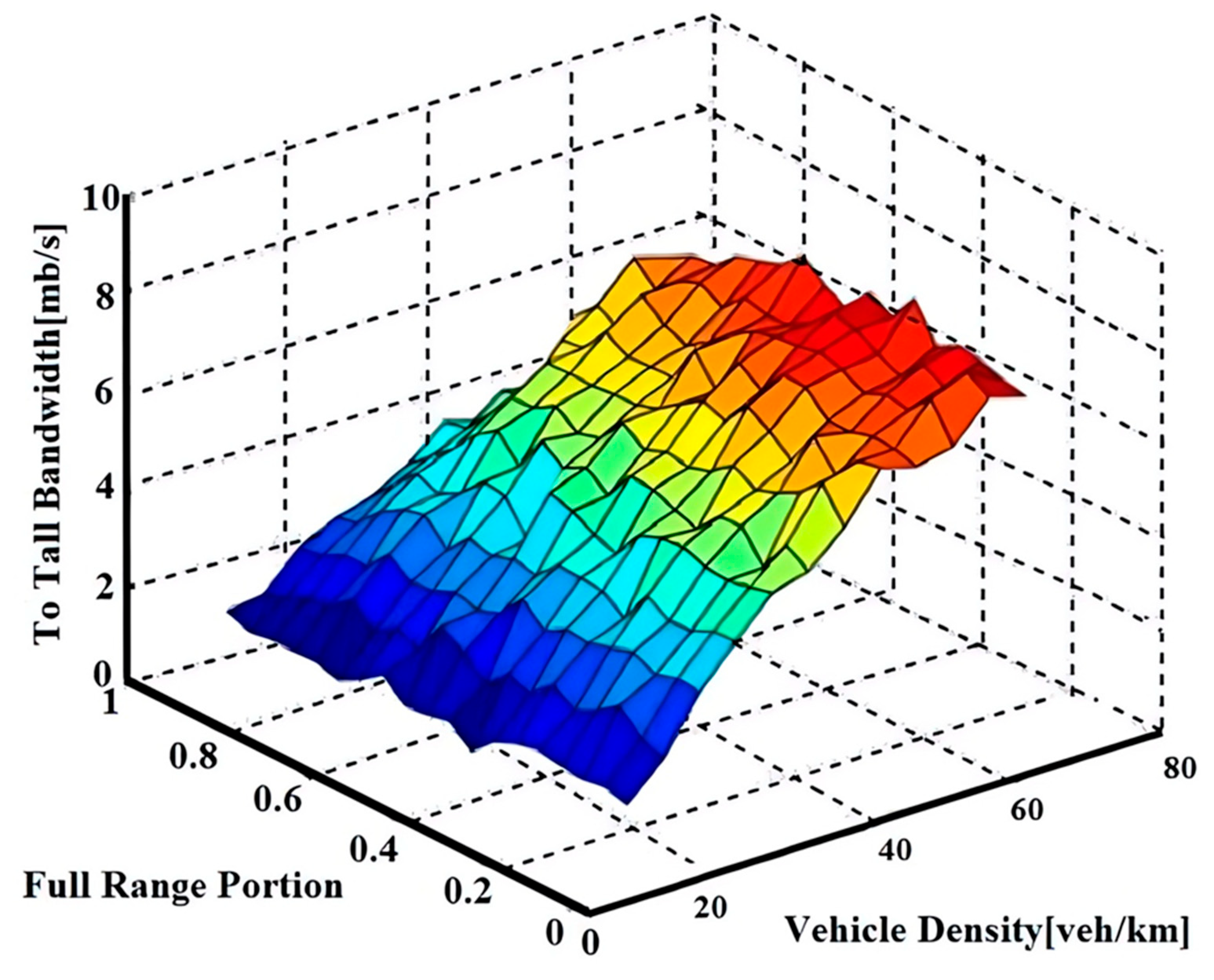
- Vehicle-to-Bridge (V2B): Figure 5 shows the impact of the bridging approach on the performance of the vehicle network. When vehicles on both sides of the highway are allowed to connect to vehicles on the opposite side, the overall network connectivity is improved. For simplicity, this bridging approach is called Vehicle-to-Bridge (V2B). The results are shown below, showing the number of unconnected clusters with and without bridging (labeled V2B Used and Unused, respectively) for varying vehicle densities. As expected, enabling bridging reduces the number of disconnected clusters, improves network connectivity, increases throughput and reduces average latencies. Figure 6 shows the total communication time during the simulation run, showing the effectiveness of limiting the transmission area in which vehicles in the west can communicate with vehicles in the east. Scenarios where the western vehicle within the transmission range of the source vehicle can communicate with the eastern vehicle are considered for all variations by setting the diameter of the transmission range to 0.75, 0.5 or 0.25. It is shown that dynamically changing the transmission range of different regions improves network connectivity. All these regions are located at the edge of the transmission range. For example, in Figure 3, X3 corresponds to 25% of the total range of X1. Furthermore, the throughput analysis for the same area is shown in Figure 7. Higher performance is achieved by reducing the transmission range (e.g., maximum efficiency values are reached at 50% and 25% of the total range). Figure 8 shows the simulated throughput results for different transmission intervals (full transmission interval, half transmission interval and one-quarter transmission interval) at low vehicle density.
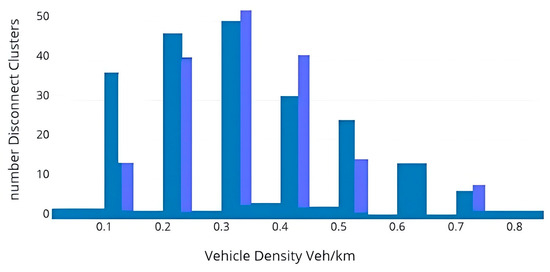 Figure 5. Bridges reduce isolated clusters on highways, improving traffic flow.
Figure 5. Bridges reduce isolated clusters on highways, improving traffic flow.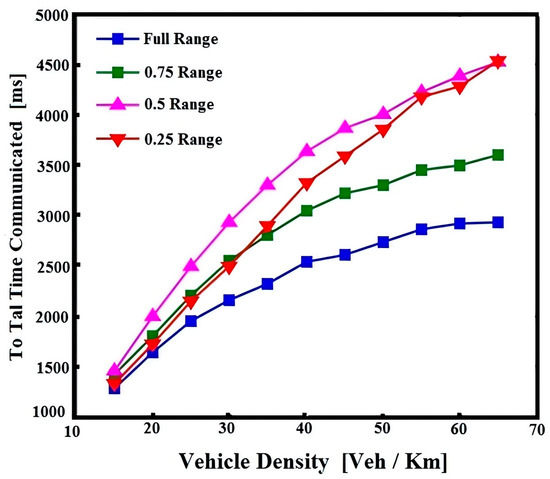 Figure 6. Total communication time analysis.
Figure 6. Total communication time analysis.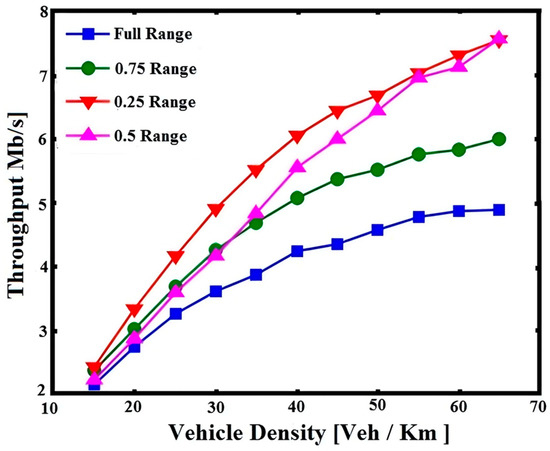 Figure 7. Examining throughput variations across algorithm regions.
Figure 7. Examining throughput variations across algorithm regions.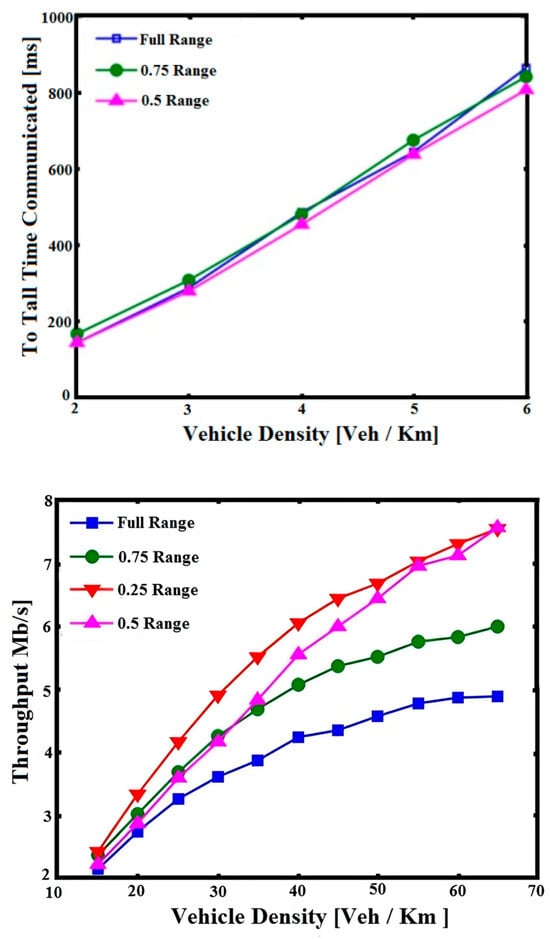 Figure 8. Throughput boost at lower traffic densities.
Figure 8. Throughput boost at lower traffic densities. - Scenarios to simplify the process: Consider the scenario in Figure 3. If a small interval (X3) is used where the system can select vehicles on the western bridge, and there are no vehicles in this interval, no vehicles are selected, and therefore, no connection is established between the source vehicle and other vehicles on the western side of the highway. However, in a continuously moving highway scenario, even with low vehicle density, every vehicle on the east side will eventually have the opportunity to communicate with every vehicle on the west side, regardless of the communication range limitations. This is because SNE identifies and selects forwarder candidates based on both the communication distance and the longest distance between vehicles (the farthest vehicle in the coverage area). With this in mind, it is easy to understand why throughput is consistent between different values of circular range when vehicle density is low.
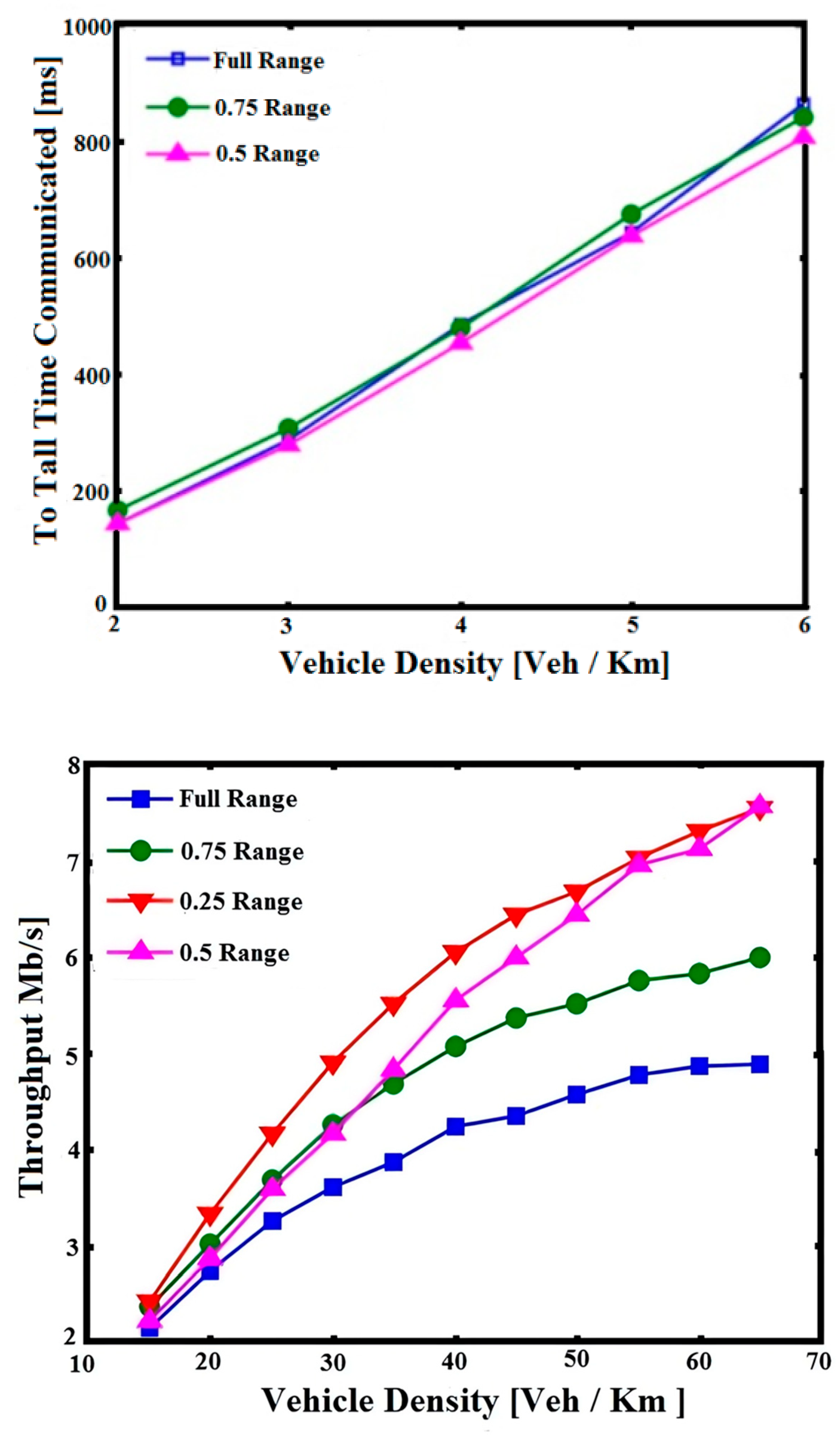
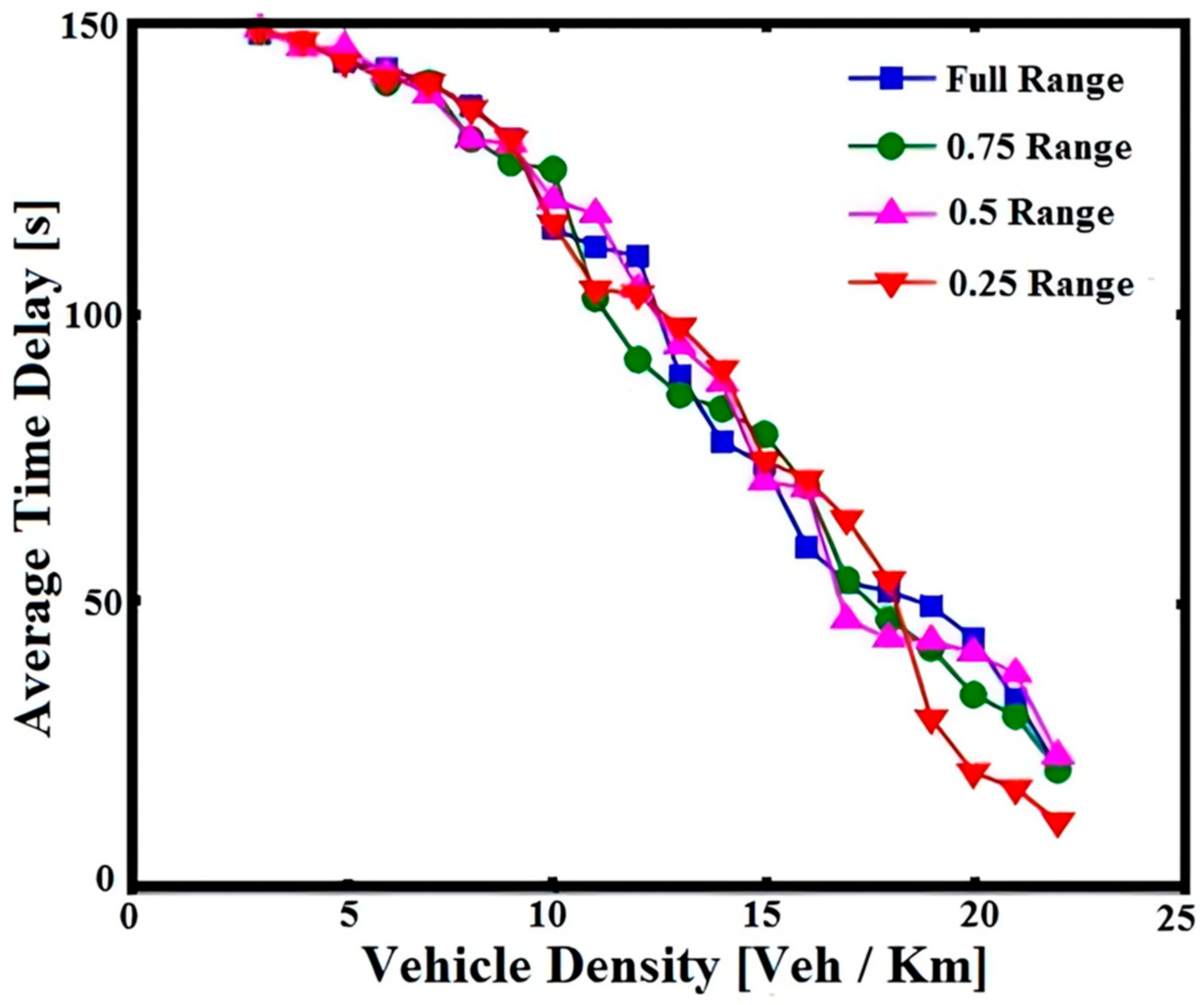
- QoS metrics for vehicular networks: As mentioned above, Quality of Service (QoS) metrics for vehicular networks are more than network throughput. Another important metric is the end-to-end time delay of packets. To evaluate the effectiveness of the algorithm, the time delay performance of packets sent from the beginning to the end of the highway is simulated. Two scenarios are analyzed to provide comprehensive results: (i) where the vehicle generates messages only once while traveling on the highway (no packet refresh) and (ii) where the vehicle generates messages with periodic packet refresh. Each case is presented separately. In the case without packet refresh, the average latency required for a packet to travel the entire length of the highway is simulated. Packets in this scenario are generated once by the source vehicle on the highway and transmitted via multi-hop communication using links with vehicles on both sides of the highway. Figure 9 shows the average latencies for both scenarios: (i) vehicles in the east line can communicate with any vehicle within the communication range of the west line, and (ii) vehicles in the east line can communicate with vehicles in the west line only within a circular area of one-eighth of the source communication range. Basically, the first scenario corresponds to a traditional routing protocol based on the communication of source range, while the second scenario uses the SNE approach, where routing is achieved by reducing the bridged communication range and selecting the farthest node. Figure 5 shows the performance of the vehicle with and without bridges. The results are as expected: vehicles transmit their messages at the highway entrance before interacting with any vehicle in the westbound lane. As a result, in both scenarios, vehicles in the east line can communicate with vehicles in the west line with average time delay performance.
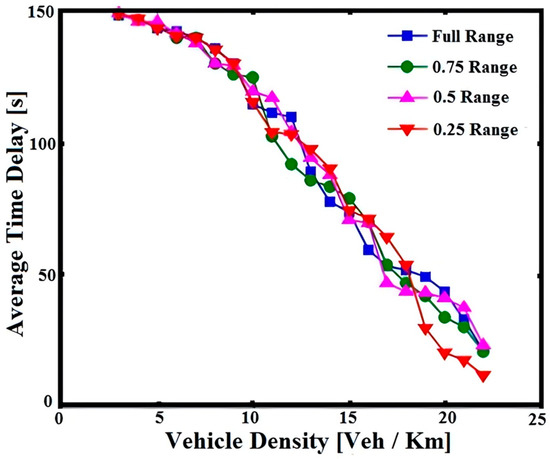 Figure 9. Density drives delay in different ranges.
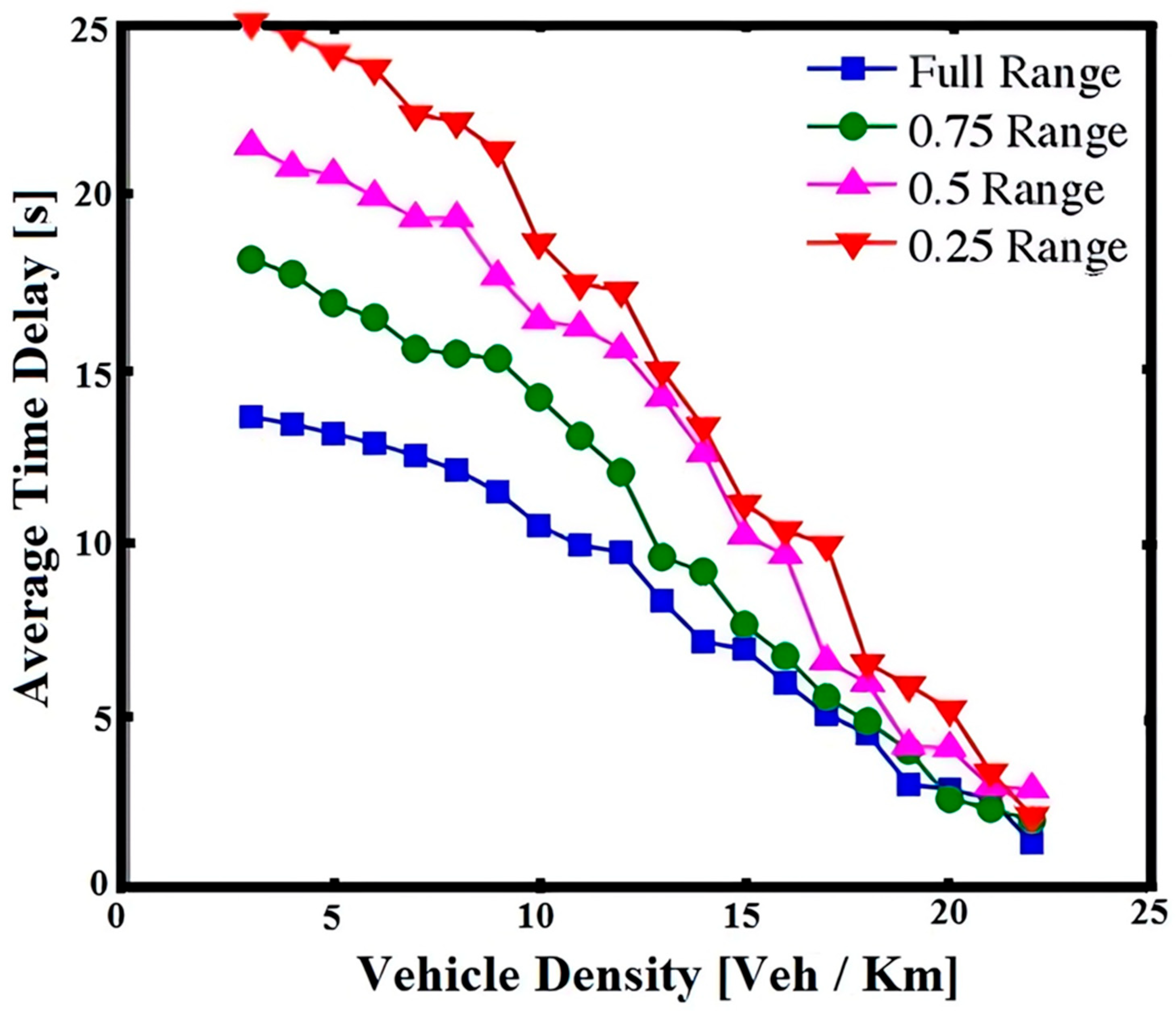
Figure 9. Density drives delay in different ranges. - Final results: As presented, in the absence of packet playback, the average time delay of the SNE algorithm and the average time delay of the conventional time delay are the same. The same results are obtained in the transfer case but not when repeated messages are generated in the vehicle as it journeys along the highway (recreating the normal package playback package). Under such premises, for the average delay time of the vehicle on the east line, (i) communication with any vehicle within the communication range on the west line is allowed, R, and (ii) communication with the vehicle on the west line is allowed only within a circular area reduced by three-quarters of the diameter source communication delay; 3/4R is shown in Figure 10. To illustrate the results of this case, the package represents an instance just created by the source (V2) tool; see the scenario in Figure 3b. Given the new package, as in this example, the vehicle cannot communicate with the V1 vehicle. If the communication range is limited to half, the vehicle cannot communicate with V3. It is no longer possible to communicate. Therefore, vehicle V2 waits until vehicle V3 enters this transmission. C2 causes an increase in the average time delay while limiting communication at low vehicle density; as mentioned, the use of FRP factors affects QoS requirements for different VANET applications. Figure 11 shows the effect of FRP coefficients on the total communication time in a network of different tool densities. The smaller the value of FRP, the larger the communication time; thus, it is expected that the vehicle density will be higher. Figure 12 shows the same results for network efficiency.
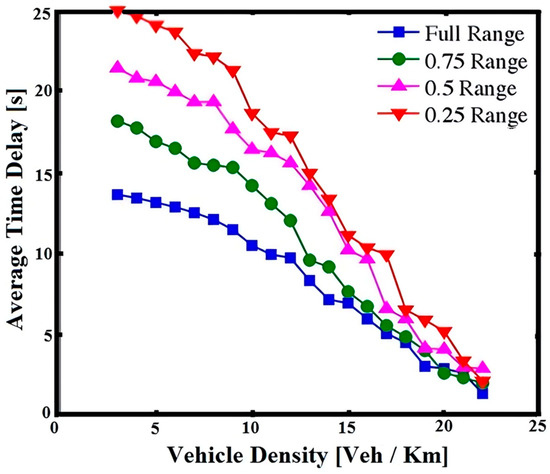 Figure 10. The delaying effect of packet regeneration in different ranges.
Figure 10. The delaying effect of packet regeneration in different ranges.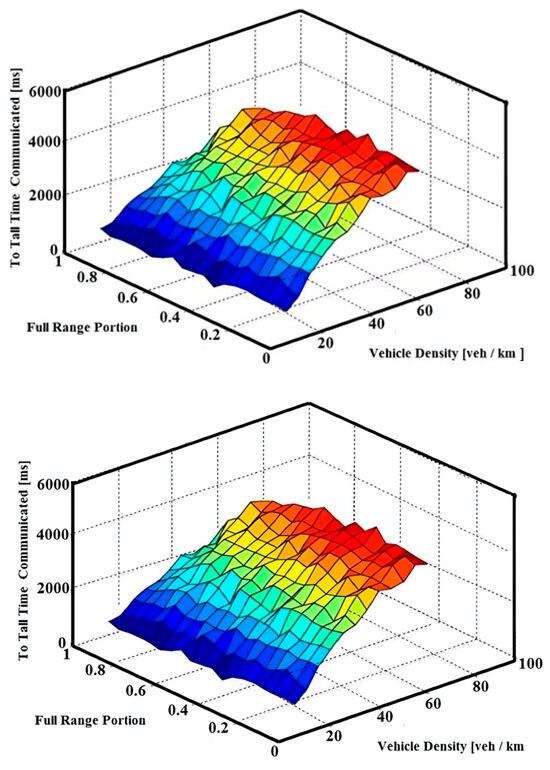 Figure 11. The FRP variable’s impact on total communication time.
Figure 11. The FRP variable’s impact on total communication time.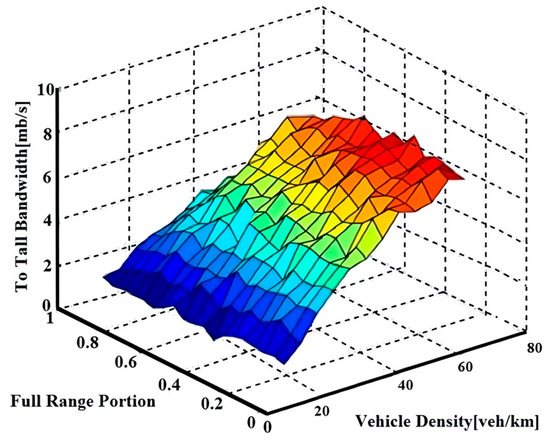 Figure 12. The effects of FRP variability over time.
Figure 12. The effects of FRP variability over time.
6.2. Performance Comparison with Existing Protocols
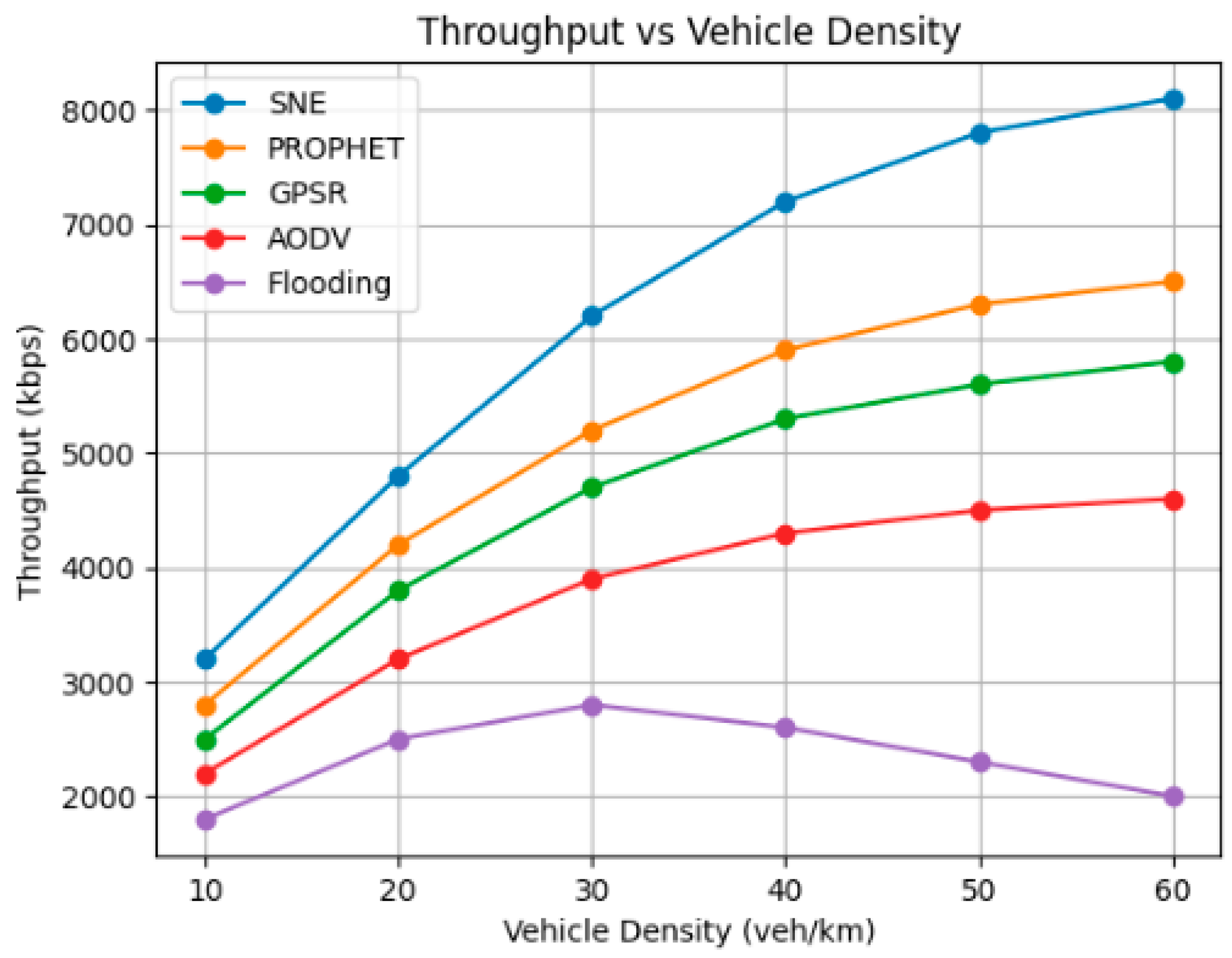
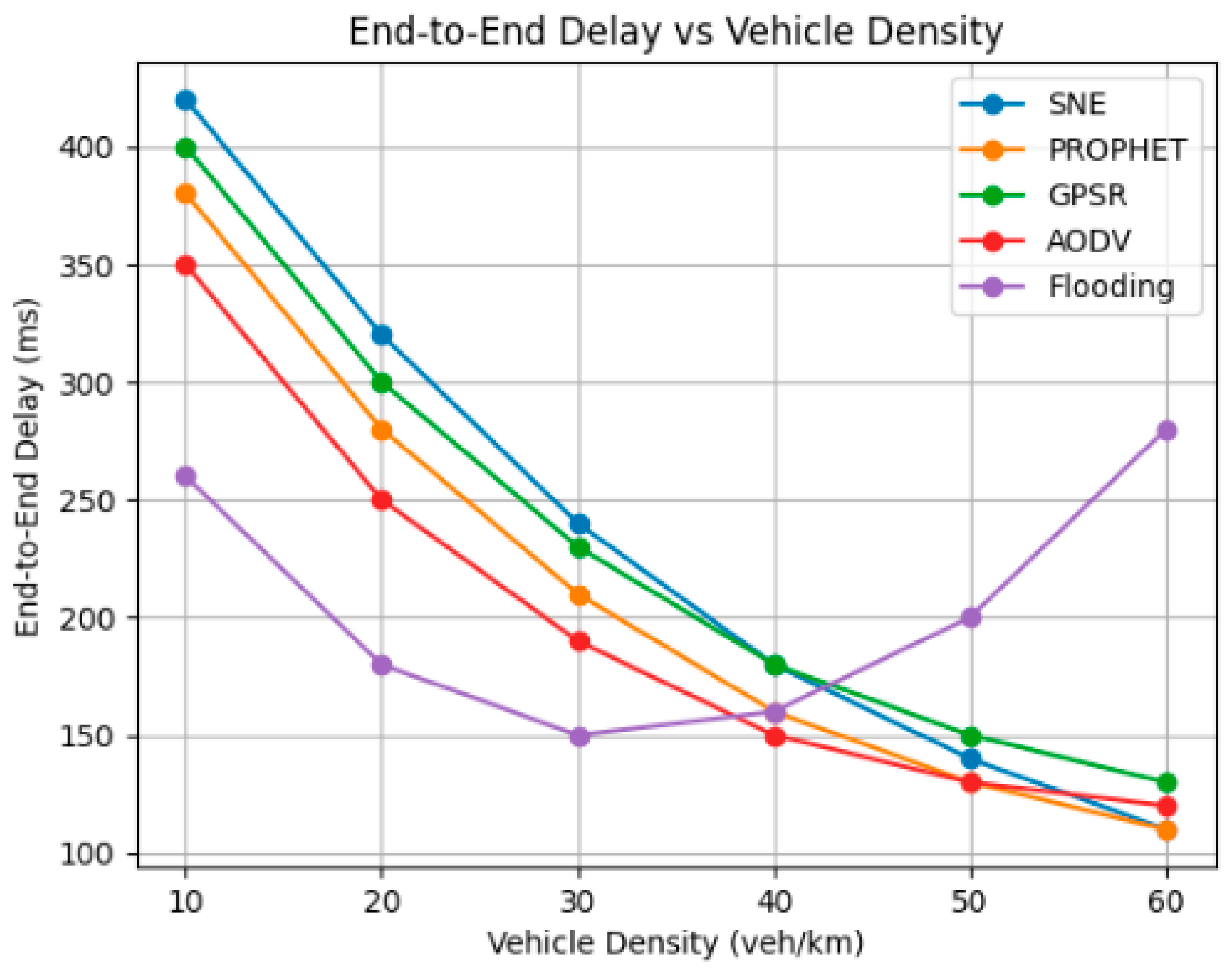
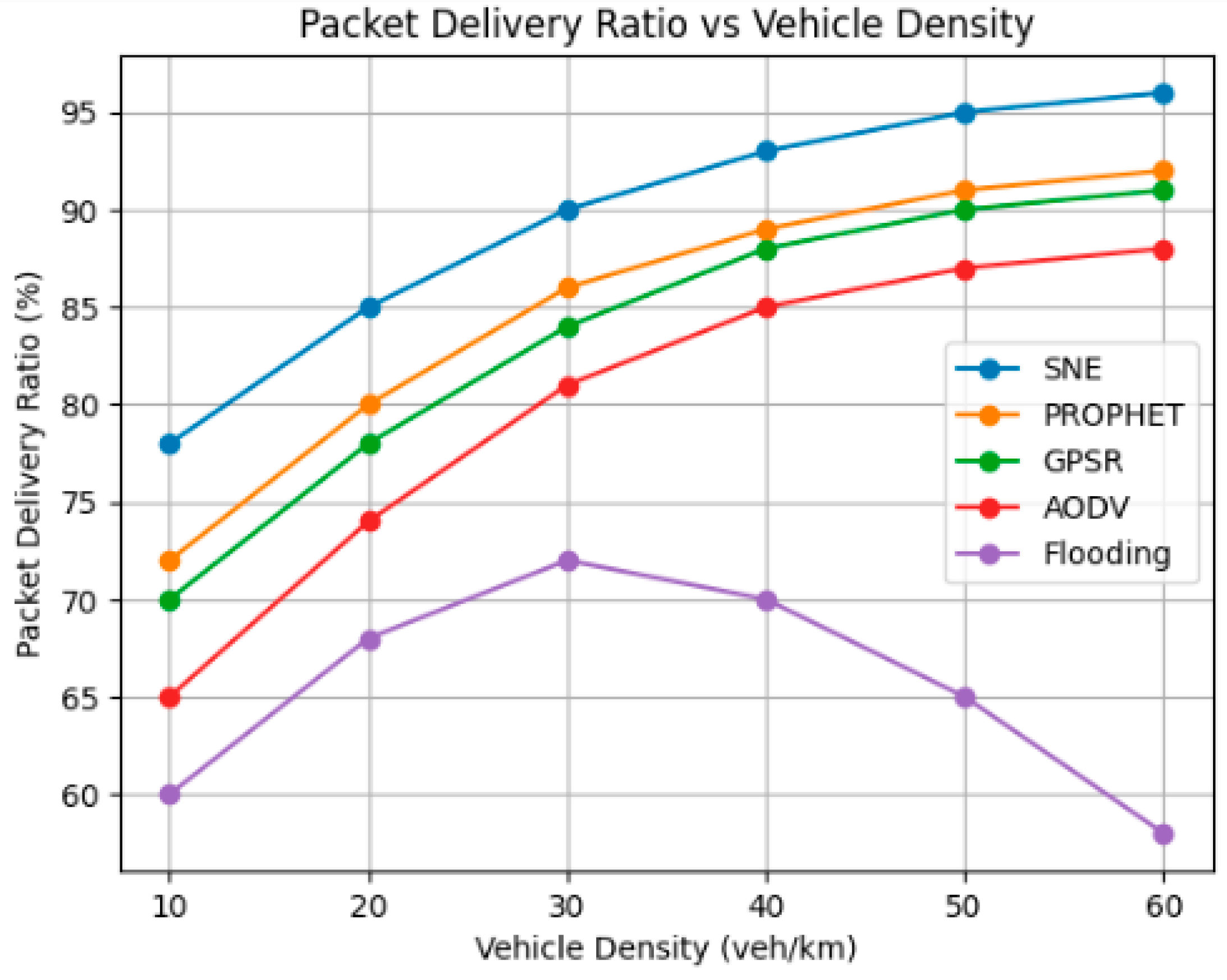
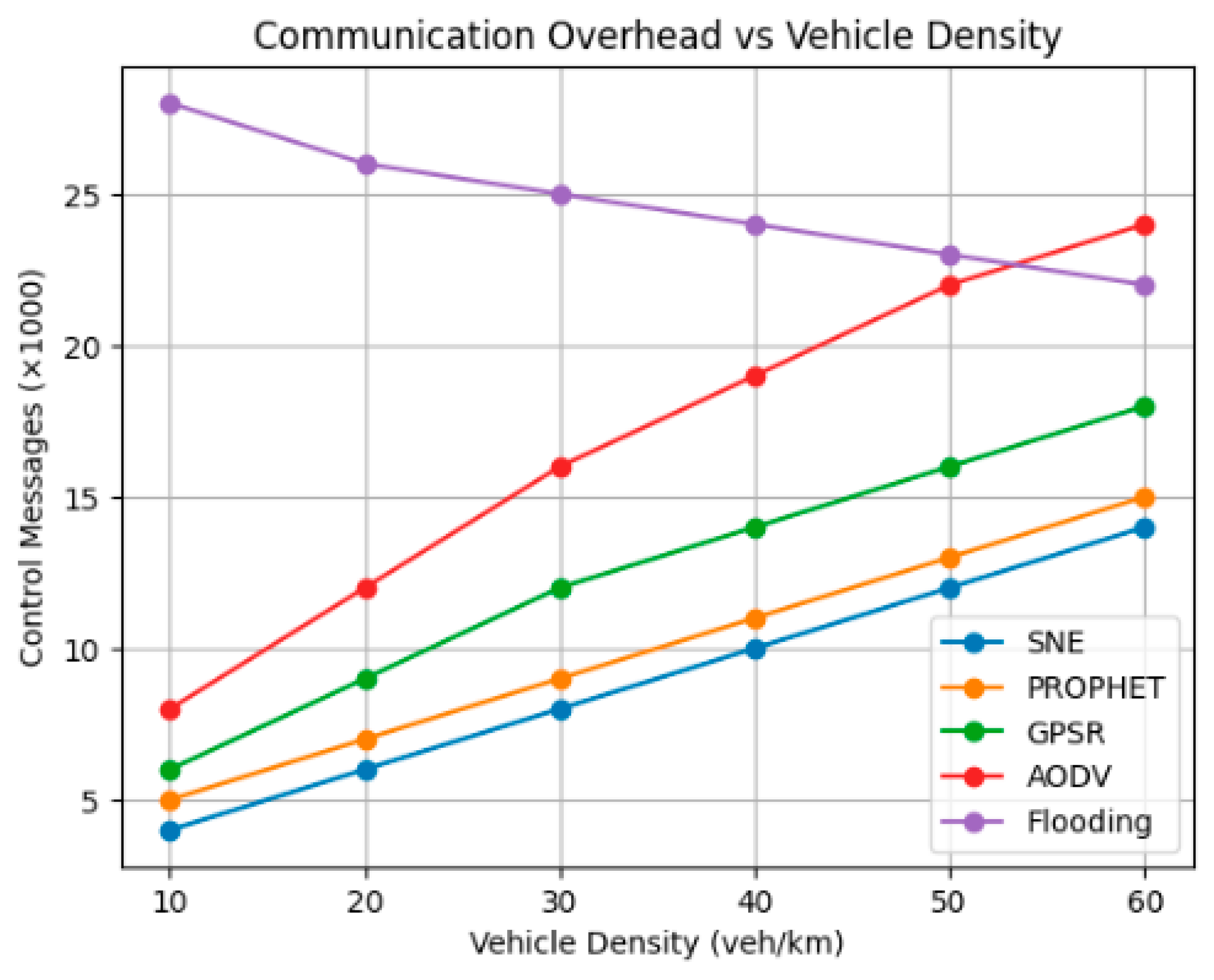
Here, we will compare when SNE goes head-to-head with other popular protocols—Basic Broadcast, AODV (Ad Hoc On-Demand Distance Vector), GPSR (Greedy Perimeter Stateless Routing), and PROPHET (Probability Routing Protocol Using Encounter History). All of these will run under the same simulation settings for a fair comparison. For the benchmarks, we use these QoS indicators: throughput (packets delivered per second), end-to-end latency, packet delivery ratio, communication overhead (number of control messages), and time for effective interaction. Our tests will cover a range of scenarios: vehicle densities from 10 to 60 vehicles per kilometer, speeds between 30 and 120 km/h, transmission ranges from 250 to 500 m, and both urban and highway mobility models (using SUMO traces). We have added a comparison table showing protocol performance at different densities. There are also line and bar charts for throughput, delay, and packet delivery ratio. These visuals will make it easy to see why SNE is superior. Here is our main conclusion: SNE’s probabilistic rebroadcast and FRP mechanism help cut down on collisions and boost throughput compared to flooding and AODV. The V2B bridging mechanism keeps connectivity strong in sparse networks, doing better than GPSR and PROPHET. Furthermore, SNE’s adaptive range partitioning helps it strike a better balance between delay and throughput than static-range protocols. By adding this data, we provide clear evidence of SNE’s strengths and show readers exactly where it shines. We have included figures comparing SNE with other VANET protocols, covering throughput, delay, delivery ratio, and communication overhead. Looking at these figures, SNE stands out in both throughput and delivery ratio. Flooding falls short at high densities because collisions get out of hand. SNE keeps overhead low, boosts delivery, and balances delay and throughput better than the rest. Please see Figure 13, Figure 14, Figure 15 and Figure 16.
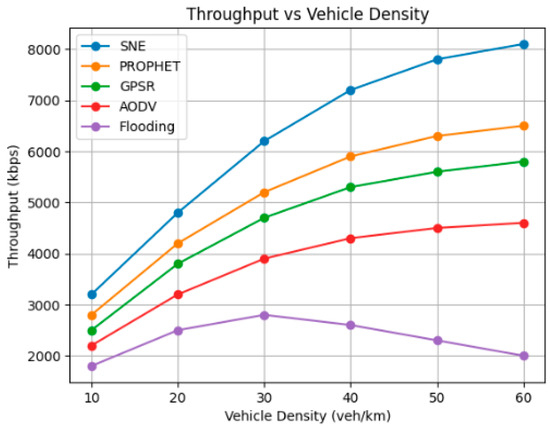
Figure 13.
Throughput vs. vehicle density.
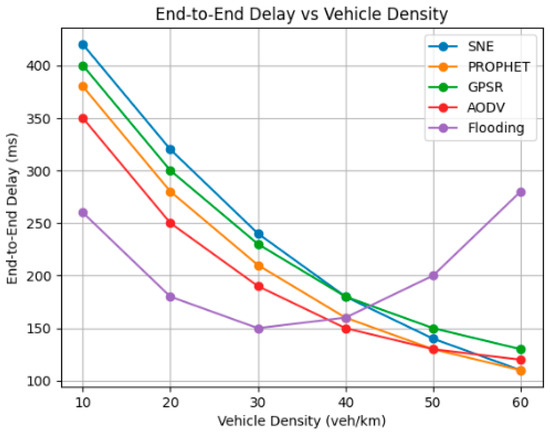
Figure 14.
End-to-end delay vs. vehicle density.
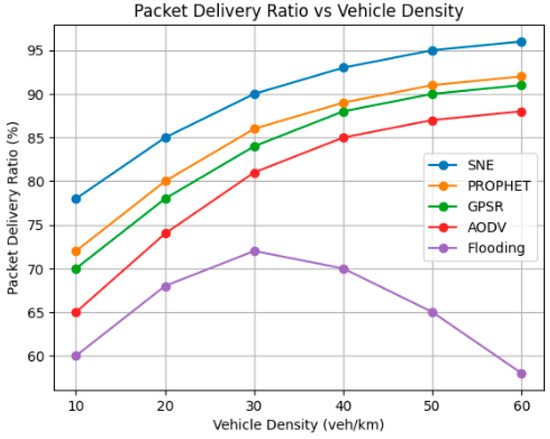
Figure 15.
Packet delivery ratio vs. vehicle density.
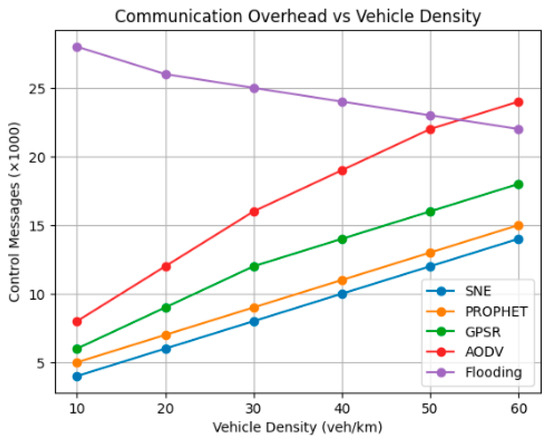
Figure 16.
Communication overhead vs. vehicle density.
7. Conclusions
In conclusion, vehicle networking represents a transformative advancement in wireless communication, enabling enhanced safety, convenience, and connectivity for modern transportation systems. The proposed Sensitive Node Election (SNE) algorithm significantly contributes to this paradigm by optimizing message forwarding and improving Quality of Service (QoS) in opportunistic VANET environments. Through adaptive mechanisms that consider vehicle density, transmission distance, and dynamic network conditions, the SNE algorithm ensures high throughput and reduced delay. Simulation results validate its effectiveness, demonstrating notable improvements in communication efficiency and reliability, thereby supporting the broader goal of creating safer and more efficient vehicular networks.
8. Future Work
We will be using the data set provided in this simulation to compare our work with different available algorithms in the literature and test our work to determine its feasibility and quality compared to other models and algorithms.
Author Contributions
Conceptualization, A.A. and M.F.A.R.; methodology, A.A., M.F.A.R. and G.K.; software, A.A.; validation, A.A., M.F.A.R., G.K. and M.A.; formal analysis, A.A., M.F.A.R. and G.K.; investigation, A.A., M.F.A.R., G.K. and M.A.; resources, A.A., M.F.A.R. and G.K.; data curation, A.A.; writing—A.A., M.F.A.R., G.K. and M.A.; writing—review and editing, A.A., M.F.A.R. and G.K.; visualization, A.A.; supervision, M.F.A.R. and G.K.; project administration, M.F.A.R. and G.K.; funding acquisition, A.A., M.F.A.R. and G.K. All authors have read and agreed to the published version of the manuscript.
Funding
This research received no external funding.
Data Availability Statement
The raw data supporting the conclusions of this article will be made available by the authors on request.
Conflicts of Interest
Author Muammer Aksoy was employed by the Cyber security Information & Telecommunication Public Company (ITPC). The remaining authors declare that the research was conducted in the absence of any commercial or financial relationships that could be construed as a potential conflict of interest.
References
- Chowdhury, M.A.; Sadek, A.W. Fundamentals of Intelligent Transportation Systems Planning; Artech House: Boston, MA, USA, 2003. [Google Scholar]
- Li, J.; Lu, H.; Guizani, M. ACPN: A Novel Authentication Framework with Conditional Privacy-Preservation and Non-Repudiation for VANETs. IEEE Trans. Parallel Distrib. Syst. 2015, 26, 938–948. [Google Scholar] [CrossRef]
- Zhang, J.; Zheng, K.; Zhang, D.; Yan, B. AATMS: An Anti-Attack Trust Management Scheme in VANET. IEEE Access 2020, 8, 21077–21090. [Google Scholar] [CrossRef]
- Ayoob, A.A.; Su, G.; Al, G. Hierarchical Growing Neural Gas Network (HGNG)-Based Semicooperative Feature Classifier for IDS in Vehicular Ad Hoc Network (VANET). J. Sens. Actuator Netw. 2018, 7, 41. [Google Scholar] [CrossRef]
- Gyongyi, Z.; Garcia-Molina, H.; Pedersen, J. Combating Web Spam with TrustRank—Stanford InfoLab Publication Server; Stanford University: Stanford, CA, USA, 2004. [Google Scholar]
- Wu, B.; Goel, V.; Davison, B.D. Topical TrustRank. In WWW '06: Proceedings of the 15th International Conference on World Wide Web; Association for Computing Machinery: New York, NY, USA, 2006. [Google Scholar] [CrossRef]
- Sepulcre, M.; Gozalvez, J.; Coll-Perales, B.; Lucas-Estañ, M.C.; Gisbert, J.R. Empirical performance models for V2V communications. In Proceedings of the 2015 IEEE International Conference on Computer and Information Technology; Ubiquitous Computing and Communications; Dependable, Autonomic and Secure Computing; Pervasive Intelligence and Computing, Liverpool, UK, 26–28 October 2015; pp. 737–742. [Google Scholar]
- Alizadeh, M.; Tadayon, M.H.; Jolfaei, A. Secure ticket-based authentication method for IoT applications. Digit. Commun. Netw. 2023, 9, 710–716. [Google Scholar] [CrossRef]
- Samara, G.; Al-Salihy, W.A.H.; Sures, R. Security issues and challenges of vehicular ad hoc networks (VANET). In Proceedings of the 4th International Conference on New Trends in Information Science and Service Science, Gyeongju, Republic of Korea, 11–13 May 2010. [Google Scholar]
- Eiza, M.; Ni, Q.; Owens, T.; Min, G. Investigation of routing reliability of vehicular ad hoc networks. EURASIP J. Wirel. Commun. Netw. 2013, 2013, 179. [Google Scholar] [CrossRef]
- Gopinath, S. The Modified Routing Protocol for Defending against Attacks in MANET. Int. J. Adv. Res. Comput. Sci. Softw. Eng. 2017, 2. [Google Scholar] [CrossRef]
- Yan, G.; Rawat, D.B.; El-Tawab, S. Ticket-based Reliable Routing in VANET. In Proceedings of the 2009 IEEE 6th International Conference on Mobile Adhoc and Sensor Systems, Macau, China, 12–15 October 2009; pp. 609–614. [Google Scholar]
- Chen, S.; Nahrstedt, K. Distributed Quality-of-Service Routing in Ad Hoc Networks. IEEE J. Sel. Areas Commun. 1999, 17, 1488–1505. [Google Scholar] [CrossRef]
- Jiang, H.; Guo, H.; Chen, L. Reliable and Efficient Alarm Message Routing in VANET. In Proceedings of the 2008 the 28th International Conference on Distributed Computing Systems Workshops, Beijing, China, 17–20 June 2008; pp. 186–191. [Google Scholar]
- Sun, W.; Yamaguchi, H.; Yukimasa, K.; Kusumoto, S. GVGrid: A QoS Routing Protocol for Vehicular Ad Hoc Networks. In Proceedings of the 2006 14th IEEE International Workshop on Quality of Service, New Haven, CT, USA, 19–21 June 2006. [Google Scholar] [CrossRef]
- Kim, J. Probabilistic Broadcasting Based on Coverage Area and Neighbor Confirmation in Mobile Ad Hoc Networks. In Proceedings of the IEEE Global Telecommunications Conference Workshops, 2004. GlobeCom Workshops 2004, Dallas, TX, USA, 29 November–3 December 2004. [Google Scholar] [CrossRef]
- Vegni, A.M.; Mostafa, A.; Agrawal, D.P. CAREFOR: Collision-Aware Reliable Forwarding Technique for Vehicular Ad Hoc Networks. In Proceedings of the 2013 International Conference on Computing, Networking and Communications (ICNC), San Diego, CA, USA, 28–31 January 2013; pp. 773–777. [Google Scholar] [CrossRef]
- Hartenstein, H.; Laberteaux, K.P. VANET; Wiley: Hoboken, NJ, USA, 2010. [Google Scholar] [CrossRef]
- Lee, U.; Park, J.-S.; Yeh, J.; Pau, G.; Gerla, M. CodeTorrent: Content Distribution Using Network Coding in VANET. Available online: https://www.cs.columbia.edu/~asherman/coding/papers/codetorrent_mobishare06.pdf (accessed on 12 November 2025).
- Mostafa, A.; Vegni, A.M.; Oliveira, T.; Little, T.D.C.; Agrawal, D.P. QoSHVCP: Hybrid Vehicular Communications Protocol with QoS Prioritization for Safety Applications. ISRN Commun. Netw. 2012, 2012, 1–14. [Google Scholar] [CrossRef]
- Lum, H.; Reagan, J.A. Interactive Highway Safety Design Model: Accident Predictive Module. Public Roads 2025, 58, 14–17. [Google Scholar]
- Khazraee, S.H.; Sáez-Castillo, A.J.; Geedipally, S.R.; Lord, D. Application of the Hyper-Poisson Generalized Linear Model for Analyzing Motor Vehicle Crashes. Risk Anal. 2014, 35, 919–930. [Google Scholar] [CrossRef] [PubMed]
- Cheng, L.; Geedipally, S.R.; Lord, D. The Poisson–Weibull Generalized Linear Model for Analyzing Motor Vehicle Crash Data. Saf. Sci. 2013, 54, 38–42. [Google Scholar] [CrossRef]
- Geometry Calculator. Available online: https://www.symbolab.com/geometry-calculator (accessed on 20 January 2026).
- Trigonometric Equation Calculator. Symbolab. Available online: https://www.symbolab.com/solver/trigonometric-equation-calculator (accessed on 20 January 2026).
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.