1. Introduction
The supply chain refers to the entire process from acquiring materials to delivering the finished products, which is mentioned in relevant literature [
1,
2]. It involves many different stages and many stakeholders, such as suppliers, manufacturers, storage facilities, logistics providers, and merchants, etc. As supply chains become increasingly complex, the concept of supply chain traceability has emerged, utilizing information technology to ensure that data at each link remains traceable, transparent, and immutable [
3]. By employing technologies such as blockchain, supply chain traceability can monitor the origin, quality, and transportation path of products in real time [
4], thereby enhancing both transparency and efficiency while ensuring product safety and compliance [
5]. From 2015 to 2025, the adoption rate of blockchain technology in global supply chain management has risen steadily, reaching nearly 75% by 2024 [
6]. The cyber-physical system (CPS) is a networked system that integrates different physical systems [
7]. Within the framework of the CPS, it integrates computing, networking, and physical operations [
8]. After the digital and physical domains are merged, it offers revolutionary possibilities to the supply chain. Topics within CPS, such as real-time data acquisition and smart automation, closely align with traceability requirements, facilitating seamless monitoring and control of physical supply chain activities through cyber-infrastructure.
Blockchain technology is vital to supply chain traceability due to its decentralized, immutable, and transparent characteristics [
9]. By recording data from each link of the supply chain (such as raw material sources, production information, transportation routes, etc.), it ensures that the data is immutable and transparent, thereby solving the problems of information asymmetry and tampering in supply chains [
10]. The traceability of blockchain means that the whole process of each product’s production and sales can be precisely recorded on the blockchain, and the information of any node can be queried and verified in a minute, ensuring the transparency and reliability of the supply chain [
11]. Consumers and regulatory agencies can easily trace all information of products by scanning QR codes, ensuring the authenticity and safety of products. At the same time, blockchain reduces intermediary links, improves the supply chain efficiency, enhances trust among participants, and promotes the intelligence and transparency of supply chain management [
12].
Consortium chains are often used in product supply chain traceability scenarios [
13]; moreover, in consortium blockchain networks like Hyperledger, Practical Byzantine Fault Tolerance (PBFT) and its enhanced algorithms are typically employed as consensus protocols. Although existing consensus mechanisms have made certain progress, under large-scale nodes, the existing PBFT improvement schemes still have deficiencies in supply chain traceability [
14]. Therefore, we propose a hybrid consensus algorithm named Node Rating-Based and Grouping Raft cluster Practical Byzantine Fault Tolerance (NG-RPBFT) using node comprehensive rating and grouping to address the issues of high communication complexity, insufficient scalability, and limited security in existing consortium chain consensus algorithms in supply chain traceability scenarios. This algorithm builds a multi-index comprehensive rating model for nodes, calculates the comprehensive score of supply chain participating nodes, and screens the candidate central nodes of each group based on the rating results. Combining the geographical location and comprehensive scores of nodes, the network nodes are grouped, and the leader nodes and supervisory nodes within the group are selected by the comprehensive score of nodes to form a multi-group consensus architecture. The central nodes of each group use the PBFT consensus protocol for inter-group consensus in the consensus process, the Raft consensus algorithm with supervisory nodes is introduced to achieve data synchronization in the group. At the same time, Brotli compression is introduced to optimize network bandwidth through data compression, reduce data transmission volume, and improve consensus efficiency. The NG-RPBFT algorithm demonstrates significant advantages in blockchain-based supply chain traceability, particularly in addressing the limitations of existing consensus mechanisms. By dynamically adjusting weights to evaluate service levels, consensus success rates, and resource attributes, the NG-RPBFT algorithm ensures that high-security, high-performance nodes are prioritized as leaders or central nodes. Secondly, enhanced K-medoids clustering algorithm optimizes network topology, reduces communication distances between nodes, and lowers communication complexity, addressing scalability issues faced by traditional grouping algorithms like PBFT that ignore geographical location. Third, the hybrid inter-group/intra-group consensus mechanism balances efficiency while maintaining Byzantine fault tolerance. Experiments demonstrate that NG-RPBFT outperforms PBFT, LRBFT, and TP-PBFT in consensus latency, exhibiting superior scalability and stability in large-scale networks.
2. Related Works
Among various practical application examples of blockchain technology, the consortium chain, with its relatively trustworthy participants and certain privacy protection features, demonstrates unique advantages in areas such as product supply chain traceability [
15]. Regarding the PBFT, as a classic consensus mechanism, this article aims to withstand a specific number of malicious nodes and ensure the distributed system consistency. It has been widely applied in consortium chains. However, the traditional PBFT protocol still has some obvious shortcomings [
16]. Firstly, in the consensus process, the PBFT algorithm requires an army of message interaction among nodes. For each iteration of consensus, nodes send various types of messages including pre-prepare, prepare, and submit to other nodes. As the quantity of participants continues to grow, the number of messages grows exponentially, resulting in significant increases in communication overhead and latency, which affect the system efficiency [
17,
18]. Also, PBFT uses a fixed rotation of the master node mechanism. The master node’s failure may lead to a decline in system performance or consensus failure, and the centralized role of the master node increases the risk of single-point failure, limiting its adaptability and fault tolerance in large-scale distributed environments [
19]. Therefore, the research and improvement of PBFT used in consortium chains have attracted widespread attention from the academic community and the industry [
20].
Zhao et al. [
21] presented RP-PBFT which can reduce the range of nodes engaged in the consensus process. By the classification of node reputation values, it simplifies the three-stage consensus. Chen et al. [
22] presented the DT-PBFT model, which eliminates the Pre-Prepare stage and optimizes the consensus process through a reputation-based double-layer structure. Wang et al. [
23] presented the PenguinBFT algorithm to significantly improve communication efficiency by introduces reputation assessment and node partitioning. Liu et al. [
24] presented P-PBFT which provides low latency and high throughput through group consensus. Tang et al. [
17] presented tPBFT which simplifies the preparation stage and reduces interaction overhead for high-frequency trading scenarios. Xu et al. [
25] presented ABC-GSPBFT which combines group scores and swarm optimization to reduce latency and overhead and improve performance. Ding et al. [
26] proposed CE-PBFT, which optimizes microgrid transactions through node credit value stratification and segmented consensus mechanism, improving throughput and reducing latency and communication overhead. Dong et al. [
27] presented IPBFT based on group signature, which optimizes the application of PBFT in the IoT, enhancing privacy protection and reducing communication overhead and bandwidth occupation. YANG et al. [
16] proposed NBFT in reference, which has a relatively high fault tolerance. This algorithm adheres to the decentralized and democratic principles of blockchain, which ensures that the upper limit of fault tolerance can be increased and also guarantees the performance of scalability, as Othmen and some others have pointed out. Reference [
28] proposed the RC-PBFT algorithm, a low-latency parallel consensus algorithm for blockchain platforms, which reduces communication complexity by executing consensus in parallel on different cluster nodes and performs better in network load and response time. Zeng et al. [
29] proposed a PBFT consensus optimization algorithm by using Vague sets and credit ratings, introducing Vague sets for node voting and master node selection, optimizing the consistency protocol and setting an elimination mechanism to update the node set, effectively reducing communication overhead, transaction latency, and improving throughput, enhancing security and performance. Wang et al. [
30] proposed LRBFT with Lagrange interpolation, which optimizes the election of master nodes through generating random seeds, leveraging delegated nodes to improve consensus efficiency, and leveraging a supervision mechanism to ensure security. It has significant improvements compared to PBFT in consensus efficiency and has good characteristics, but the information exchange process still needs optimization. Bai et al. [
31] proposed RaBFT based on Raft, introducing dynamic committees and new election algorithms, performing well in throughput, consensus delay, leader election delay, and Byzantine fault tolerance. Tang et al. [
32] presented a PBFT consensus protocol using threshold proxy signatures. They enhanced scalability and offline tolerance through methods such as two-step clustering and introduced a reputation mechanism to evaluate nodes. Wu et al. [
33] proposed DBPBFT, a hierarchical PBFT consensus algorithm with dual blockchain, which separates chain responsibilities, divides the mining chain into data-specific groups, selects master nodes based on multi-factor reputation values. Liu et al. [
34] presented 5G-PBFT, which constructs a reputation model based on node performance and behavior, selects primary nodes via reputation values and verifiable random functions.
Existing scholars have primarily improved PBFT in areas such as optimizing node selection, reducing communication complexity, enhancing scalability, integrating hybrid/complementary mechanisms, strengthening security, and adding additional capabilities. Based on the above analysis, although the improved PBFT method has better fault tolerance and lower confirmation delay, it still has some shortcomings in the supply chain traceability scenario. Supply chain traceability usually involves complex participating roles, strong mobility, uneven node distribution, and large participation scale. Over time, the number of supply chain participants has been continuously increasing, the improved PBFT consensus algorithm still faces the inability to meet the requirements of low communication load, security, scalability, high throughput, etc. Therefore, this paper deeply analyzes the deficiencies of the existing improved PBFT consensus algorithm, and proposes a hybrid consensus algorithm NG-RPBFT based on node comprehensive rating and grouping for supply chain traceability. Improvements are implemented across multiple dimensions, including master node selection, scalability optimization, and communication complexity reduction. These enhancements elevated the system’s consensus efficiency in large-scale, dynamic environments, decreased communication load, and ensured the security, reliability, and supply chain traceability efficiency. The proposed solution mainly works as follows:
Developing a multi-index rating model that comprehensively evaluates and ranks nodes by considering factors such as their service level within the supply chain, consensus success rate, and resource attributes. This evaluation aims to prioritize the selection of nodes characterized by high security and exceptional performance as candidate central nodes for each group. These nodes will participate in the inter-group PBFT consensus process and serve as the Raft consensus leader node, thereby improving the reliability and efficiency of both inter-group and intra-group consensus.
Utilizing the geographical location and comprehensive scores of nodes, the enhanced K-medoids clustering algorithm is employed to categorize nodes into multiple groups, thereby establishing a multi-group consensus structure. This structure optimizes network topology, minimizes communication distances between nodes, and effectively reduces communication overhead.
Inter-group employs the PBFT protocol to maintain data consistency and incorporates Brotli data compression technology to minimize message size and reduce communication load. Intra-group utilizes an enhanced Raft protocol with supervisory nodes to bolster Byzantine fault tolerance and improve the data synchronization efficiency.
3. Node Rating-Based and Grouping Raft Cluster Practical Byzantine Fault Tolerance
To address the limitations of the blockchain consensus mechanism in supply chain traceability, including master node selection, scalability, and communication complexity, we propose a hybrid consensus algorithm, NG-RPBFT, which is based on node rating and grouping.
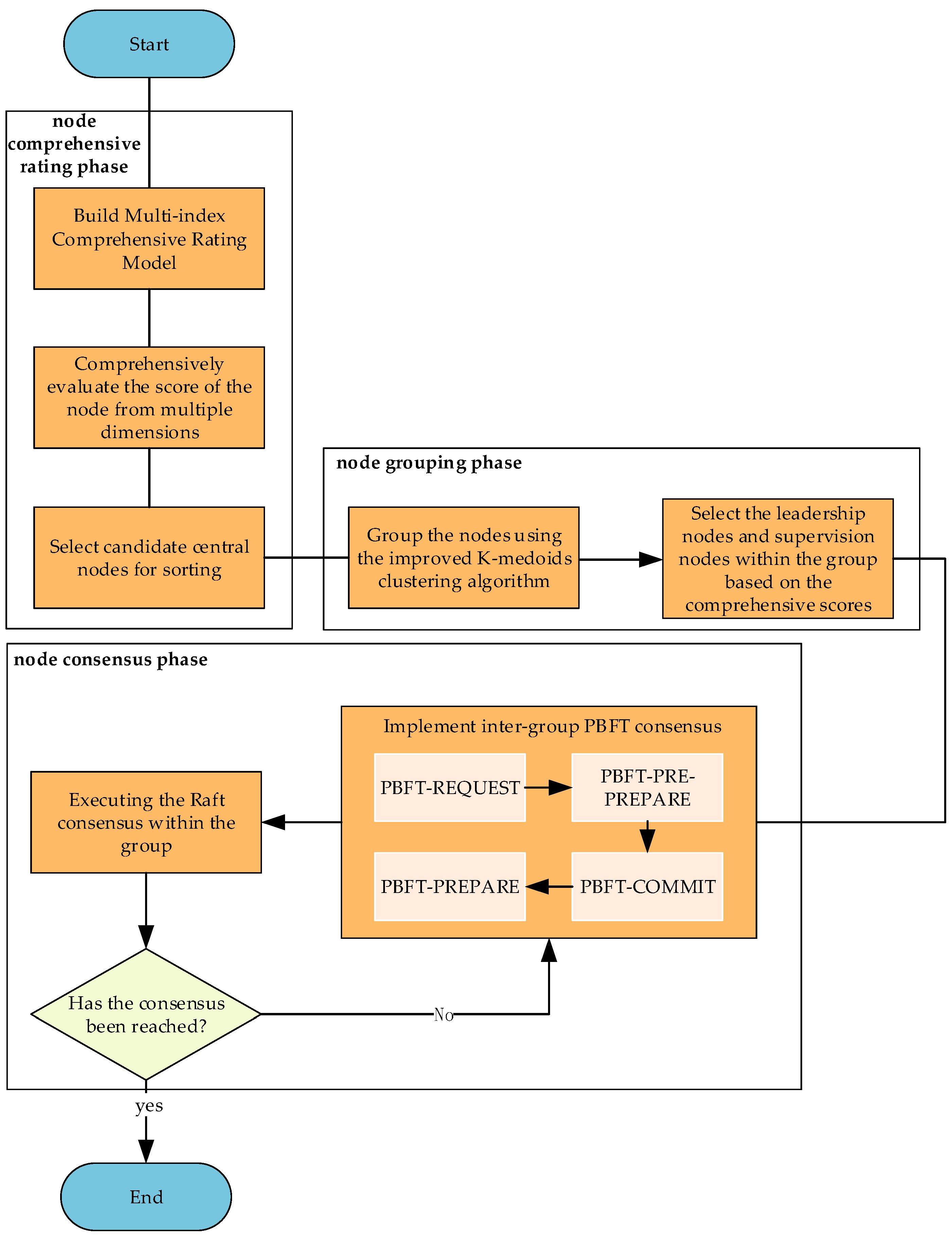
Figure 1 shows the algorithm flow. The execution of this algorithm comprises three primary stages: node comprehensive rating, node grouping, and node consensus. Initially, the process begins with the comprehensive rating stage, where a multi-index comprehensive rating model for nodes is constructed. This model evaluates the scores of supply chain participating nodes across several dimensions, including service level, consensus success rate, and resource attributes. Candidate central nodes are selected according to their rankings. Subsequently, the process advances to the node grouping stage, where the geographical locations of the nodes are integrated with their comprehensive scores. An improved K-medoids clustering algorithm is employed to group nodes, and leader nodes as well as supervisory nodes are identified within each group based on their comprehensive scores, thereby forming multiple consensus architectures. Finally, the consensus stage is executed. Inter-group consensus is established via the PBFT protocol to ensure data consistency among groups. Intra-group consensus is achieved through the optimized Raft protocol implemented by the supervisory node, which facilitates data synchronization and verification. Additionally, Brotli data compression technology is utilized to reduce communication overhead.
3.1. Supply Chain Node Multi-Index Comprehensive Rating Model
In the supply chain, the nodes participating in the consensus can include various types of nodes such as suppliers, retailers, and logistics service providers. To comprehensively and accurately evaluate the participating nodes overall performance, this algorithm constructs a multi-index comprehensive rating model for nodes. This model is based on blockchain system nodes’ performance in the supply chain, their historical interaction behaviors, and resource attributes, and calculates the comprehensive score of the nodes from three key dimensions: service level , consensus success rate , and resource attribute score . It serves as the foundation for the subsequent processes of node screening, grouping, and reaching consensus. The architecture of each index is outlined below:
The service degree
of a node is an important indicator for measuring its role and contribution in the supply chain. The calculation method varies depending on the position of the node in the supply chain. For upstream nodes (such as suppliers), the service degree is measured by the supply ratio, while for downstream nodes (such as retailers), it is measured by the sales ratio. This distinction between upstream and downstream nodes in the calculation method enables a more accurate reflection of the service capabilities and contribution levels of different types of nodes in the supply chain:
Among them, is the service level of the i-th node when reaching consensus at the -th round; is the supply proportion of node i in the upstream; means the sales proportion of node i in the downstream; is the supply quantity of node i, and is the total upstream supply quantity; and is the sales quantity of node i, and is the total downstream sales quantity.
- 2.
Node consensus success rate
The node consensus success rate
is to judge the node performance in historical consensus process, and its formula is:
Among them, is the consensus success rate of the i-th node when reaching consensus at the t-th round; is the count of successful consensuses of the i-th node, and is the count of failed consensuses; is the consensus success proportion. This formula uses the Sigmoid function. By dynamically adjusting the ratio of reward and punishment, it effectively smooths the impact caused by fluctuations in the consensus success rate, avoids the interference of extreme situations on node evaluation, and thus more accurately reflects the stability and reliability of the node in the consensus process.
- 3.
Resource attribute score
The resource attribute score
mainly considers the potential impact of the computing resources of the nodes on the consensus process. It covers multiple key dimensions such as CPU, memory capacity, hard disk capacity, and network bandwidth. In this way, it can comprehensively and objectively assess the resource status of the nodes, providing an important basis for the comprehensive score of the nodes. Its calculation formula is as follows:
Among them,
is the resource attribute score of the
i-th node when reaching consensus at the
t-th round;
,
is the score of the
i-th node in the
j-th resource dimension (CPU core count, memory, hard disk, bandwidth);
is the weight of each resource dimension, which are 0.25 (CPU), 0.25 (memory), 0.3 (hard disk), and 0.2 (bandwidth), respectively. We assign weights based on the contribution of each node’s overall resource capabilities—specifically hard disk, CPU, memory, and bandwidth—to its overall resource capacity score. Priority is given to nodes with robust storage capacity, capable of real-time data processing and consensus computation, and possessing fundamental communication capabilities. The main calculation formula of
is:
Among them, is the growth rate control parameter, whose values are 0.2 (CPU), 0.01 (memory), 0.0005 (hard disk), and 0.1 (bandwidth), respectively. Avoid excessive allocation of low-value resources to nodes. is the specific value of the i-th node in the j-th resource dimension.
- 4.
Comprehensive score of the node
Based on evaluation indicators of the above three dimensions, the calculation formula for the comprehensive score
of the node is as follows:
Among them, is the comprehensive score of the i-th node when reaching consensus at the t-th round; is the service level of the i-th node when reaching consensus at the t-th round; is the consensus success rate of the i-th node when reaching consensus at the t-th round; is the resource attribute score of the i-th node when reaching consensus at the t-th round; , , , are the corresponding weight coefficients, and satisfy . Weighting allocation is aligned with the actual importance of resources. In this algorithm, the default weight coefficients are 0.4, 0.2, 0.2, and 0.2, respectively. But these coefficients can be dynamically resized according to the needs of the supply chain scenario. For example, in scenarios with high requirements for computing resources, the weight coefficient of the resource attribute dimension can be appropriately increased; while in situations where the historical consensus performance of nodes is emphasized, the weight coefficient of the consensus success rate dimension can be increased. This flexible weight adjustment mechanism makes the model to better fit diverse application scenarios, ensuring the accuracy and effectiveness of the comprehensive node score.
3.2. Grouping Model Based on Comprehensive Node Rating and Geographical Location
The supply chain network comprises various participants, including suppliers, manufacturers, logistics enterprises, retailers, and regulatory agencies. These entities collaborate and exchange information, collectively establishing a complex multi-node alliance blockchain network. Each node displays distinct characteristics, which arise from its unique position within the supply chain process, the specific functions it performs, and its individual resources and capabilities.
To effectively navigate the complexity and diversity of the supply chain network, this algorithm presents a grouping model that integrates a comprehensive assessment of nodes with geographical location data. The model aims to synthesize these two components and employs an enhanced K-medoids clustering algorithm to categorize the nodes. This approach facilitates the construction of multiple consensus architectures, ultimately optimizing network topology, reducing communication costs among nodes, and enhancing consensus efficiency. The grouping model, which is based on the comprehensive assessment of nodes and geographical location, is illustrated in
Figure 2.
To achieve grouping by the comprehensive score of nodes and their geographical locations, the following key components are mainly involved:
The precise calculation of the distance between nodes is the foundation for achieving reasonable grouping. This algorithm takes into account the geographical locations (longitude and latitude) of the nodes as well as the comprehensive score information, and improves the calculation formula of the weighted Euclidean distance between nodes. The weighted Euclidean distance between nodes is calculated using the following formula:
Among them, is the weighted Euclidean distance from node i to node ; is the longitude and latitude of node i; is the longitude and latitude of node ; and are the comprehensive scores of node i and node respectively; , , are the weight coefficients of longitude, latitude, and comprehensive score, respectively, and satisfy. Clustering prioritizes geographical concentration of nodes while maintaining performance consistency, thereby achieving a holistic assessment of both historical node performance and real-time capabilities.
Weighting coefficients can be flexibly adjusted based on the characteristics and requirements of actual supply chain situations. For example, in scenarios with extremely high requirements for logistics distribution timeliness, the weights of geographical location factors ( and ) can be appropriately increased to ensure that geographical proximity is prioritized when grouping nodes, thereby effectively reducing data transmission delay and enhancing the timeliness and accuracy of logistics information. In situations involving core production links where extremely strict requirements are placed on node performance and reliability, the weight of the comprehensive score () can be increased accordingly, making the grouping focus more on the comprehensive capabilities of nodes and ensuring the efficient processing of key production data and the achievement of consensus.
- 2.
Grouping process of K-medoids clustering algorithm
The K-medoids algorithm is an unsupervised clustering method that is widely utilized across various applications and is commonly found in related fields. The initial clustering centers are strictly confined to the sample points. In comparison to clustering algorithms like K-means, K-medoids demonstrates greater robustness in the presence of noise within the data [
35]. Consequently, utilizing the weighted Euclidean distance defined previously, this algorithm is employed to group the nodes. Algorithm 1 provides the pseudo-code for the Improved K-medoids algorithm, detailing the specific steps involved in the grouping process.
| Algorithm 1. Improved K-medoids pseudo-code. |
Input: N, k, sortedNodeList
Output: multiGroupArch
1: candidateCentralNodes = TOP 20% OF sortedNodeList
2: initialCentralNodes = RANDOM SELECT k NODES FROM candidateCentralNodes
3: groups = INITIALIZE k GROUPS WITH initialCentralNodes AS INITIAL CENTERS
4: REPEAT
5: FOR EACH node i NOT IN initialCentralNodes DO
6: FOR EACH central node c_j IN currentCentralNodes DO
7:
8: END FOR
9: nearestGroup = Group WITH MINIMUM d(i,j)
10: ASSIGN node i TO nearestGroup
11: END FOR
12: FOR EACH group g IN groups DO
13: IF SIZE(g) > N/k THEN
14: IexcessNodes = SIZE(g) − N/k
15: FOR EACH excessNode IN g (SELECTED BY MAX d(excessNode, g.central)) DO
16: secondNearestGroup = Group WITH SECOND MINIMUM d(excessNode, j)
17: MOVE excessNode TO secondNearestGroup
18: END FOR
19: END IF
20: END FOR
21: prevCentralNodes = currentCentralNodes
22: FOR EACH group g IN groups DO
23: currentCenter = g.central
24: minTotalDist = SUM(d(node, currentCenter) FOR node IN g)
25: FOR EACH candidate IN candidateCentralNodes ∩ g.nodes DO
26: newTotalDist = SUM(d(node, candidate) FOR node IN g)
27: IF newTotalDist < minTotalDist THEN
28: g.central = candidate
29: minTotalDist = newTotalDist
30: END IF
31: END FOR
32: END FOR
33: currentCentralNodes = [g.central FOR g IN groups]
34: UNTIL currentCentralNodes == prevCentralNodes
35: multiGroupArch = groups
36: RETURN multiGroupArch |
Step 1: Selection of initial central nodes. Based on the comprehensive score , select the top 20% of nodes with the highest scores as candidate central nodes. Then, randomly select ( represents the pre-defined number of groups) nodes from these candidate central nodes as the initial central nodes, and divide the ( refers to the total quantity of nodes) nodes into groups.
Step 2: Node Allocation. Calculate the weighted Euclidean distance between each remaining node and central nodes, then assign nodes to the group containing the nearest central node based on the principle of closest proximity. If the quantity of nodes in a specific group exceeds the pre-set threshold, then the remaining nodes should be assigned to the group where the second nearest central node is located. Continue this process until all nodes are successfully assigned to a group.
Step 3: Central node Update. For each cluster, compute the sum of distances from all nodes within the cluster to the current central node, and use this sum as the objective value. Then, try to replace the candidate central nodes within the group with other nodes, recalculate the sum of the distances from the group’s nodes to the new central node, and select the node that minimizes the target value as the new central node. Through continuous optimization of the selection of central nodes, the grouping structure is continuously optimized, and the node distribution becomes more compact and reasonable, thereby further reducing the communication overhead within the groups.
Step 4: Repeat Steps 2 and 3 until the central nodes of all groups no longer change. At this point, it is determined that the grouping has reached a stable state. Finally, all nodes are assigned to groups, successfully constructing a multi-group consensus architecture.
- 3.
Grouping parameter design
The candidate central nodes, distance weights , , , the pre-set threshold established during the grouping phase directly impact the rationality of node grouping and subsequent consensus performance. Through theoretical analysis and simulation testing tailored to supply chain traceability scenarios, we have defined the default settings, design rationale, and recommended ranges for each parameter.
The default configuration for candidate central nodes entails selecting nodes within the top 20% of the comprehensive score ranking to establish the candidate pool. Concerning scale balance: Selecting fewer than 10% yields an inadequate number of candidate nodes, resulting in an 18% incidence of central node resource shortages and CPU/memory utilization exceeding 95%. Selecting more than 30% prolongs initial clustering time relative to the 20% benchmark, while the consensus failure rate for the top 30% nodes markedly exceeds that of the top 20%, thereby diminishing the precision of high-quality node selection. Regarding reliability, the average composite score of the top 20% of nodes significantly surpasses the overall average. Selecting these nodes effectively reduces the risks associated with central node failures. Consequently, we recommend choosing nodes within the top 15% to 25% range. Specifically, when the total number of nodes is fewer than 50, select from the 15% to 20% range. When the total number of nodes exceeds 200, select from the 20% to 25% range.
The default distance weighting parameters are as follows: longitude weight () = 0.3, latitude weight () = 0.3, and comprehensive score weight () = 0.4. The comprehensive capability of the node () directly influences consensus efficiency, whereas geographical proximity (, ) affects data transmission latency, necessitating a balance with overall performance. The weighting coefficients can be adjusted flexibly based on the specific characteristics and requirements of the supply chain. In scenarios where timeliness is prioritized, geographical weighting may be increased; conversely, in performance-critical situations, such as core production data traceability, the weighting for the comprehensive score may be elevated.
The threshold facilitates the equitable distribution of nodes across clusters, thereby averting the concentration of excessive nodes in certain clusters while others remain underpopulated. We establish the default total node count at 40 and the default number of clusters at 4. In calculating the minimum distance from a node to a center, we initially assess whether the cluster associated with that center has met or surpassed the average node count. If it has, that center is excluded, and the center with the next smallest distance is chosen instead. This approach ensures a relatively balanced distribution of nodes across clusters. Consequently, this mechanism mitigates the risk of skewed clustering outcomes, ensures clusters of reasonable size, and enhances the stability and efficacy of the clustering process.
- 4.
Grouping stability and load balance
Load balancing during grouping is accomplished through the K-medoids clustering process, which prevents the formation of uneven cluster sizes. When nodes are assigned to clusters, the algorithm verifies whether the current size of the target cluster surpasses the average number of nodes per cluster. If this threshold is exceeded, the cluster is excluded, and the node is reassigned to the nearest available cluster. This mechanism guarantees that, despite a geographically skewed distribution of nodes, the sizes of the clusters remain relatively balanced.
Group stability is attained through a series of incremental clustering iterations. The K-medoids algorithm operates for a predetermined number of iterations, terminating prematurely if the cluster centers stabilize, thereby avoiding unnecessary reorganizations. Node grouping takes into account not only geographical factors but also a composite score that integrates historical performance and resource metrics. This multi-factor weighting mitigates fluctuations that may arise from purely geographical drift or node mobility.
The cost of reorganization entails recalculating distances among all nodes and reassessing cluster centers when executing K-medoids clustering, with the computational burden increasing in proportion to the number of nodes. To mitigate excessive volatility, we implemented several throttling strategies: establishing a maximum iteration limit during clustering to prevent infinite recalculations; initiating early termination when cluster centers stabilize to reduce redundant reorganization; and conducting periodic reassessments of clusters.
3.3. Execution Steps of the NG-RPBFT Consensus Algorithm
The NG-RPBFT consensus algorithm is mainly divided into three stages: node comprehensive rating, node grouping, and node consensus. The specific implementation process is shown in
Figure 3:
Step 1: In the node comprehensive rating phase, a multi-index comprehensive rating model for supply chain nodes is constructed, and based on the constructed rating model, the comprehensive scores of each participating node are calculated and ranked.
Step 1.1: Firstly, a comprehensive node rating model is established based on the historical interaction behaviors of nodes within the blockchain system, the resource attributes, and the performance in the supply chain.
Step 1.2: At the beginning of each consensus cycle, the comprehensive node rating model established in Step 1.1 is used to calculate the comprehensive score .
Step 1.3: Finally, the calculated comprehensive scores of each node are sorted in descending order, and the sorted node list will serve as the basis for subsequent grouping and selection of the leader nodes within the group.
Step 2: In the node grouping phase, based on the comprehensive scores of nodes obtained in Step 1 and geographical location information, the weighted Euclidean distance between each pair of nodes is calculated. By using the improved K-medoids clustering algorithm, participating nodes are grouped to form multiple consensus architectures.
Step 2.1: Based on the overall score obtained by each node, this paper selects those nodes with the highest scores in the top one-fifth and regards them as potential central nodes. After that, this paper randomly selects nodes from these already chosen potential central nodes and uses them as the initial central nodes.
Step 2.2: Utilize the improved K-medoids clustering algorithm to partition nodes into groups.
Step 2.3: In this study, the cluster center node within each group is designated as the leading node. For each group, in addition to the leading node, the node with the highest total score is selected as the monitoring node. This methodology establishes a multi-group consensus framework.
Step 3: In the consensus phase, nodes achieve agreement through a hybrid consensus algorithm that incorporates data compression technology. This phase comprises two components: inter-group consensus and intra-group consensus. The central node of each group functions as the leader node. Inter-group consensus is attained using the PBFT consensus protocol, while intra-group consensus is facilitated by the Raft protocol in conjunction with the supervisory node. Simultaneously, Brotli data compression technology is employed to enhance network bandwidth and minimize data transmission volume. The execution process of the consensus phase is illustrated in
Figure 4.
Step 3.1: First, conduct inter-group consensus. Utilizing the comprehensive scores of each group’s central nodes, the node which has the highest score is chosen as the PBFT consensus master node. Then enter the PBFT-REQUEST phase. At this stage, the Client will send a REQUEST message to the master node. The format of this message is , where represents the client number and represents the message content.
Step 3.2: Enter the PBFT-PRE-PREPARE phase. The pre-preparation message is created by the master node, with the message format being . represents the current view number, represents the current request number, represents the digest of message , and i represents the node number. Subsequently, the Brotli compression algorithm is used to compress the message body in the message, and the compressed message is broadcast to other inter-group nodes.
Step 3.3: Enter the PBFT-PREPARE phase. After receiving the pre-preparation message, other inter-group nodes first decompress the compressed message and verify its content. If, after a series of operations, the entire verification process is ultimately proven to have achieved a successful result, the node generates a prepare message with the format , and continues to compress the prepare message using the compression algorithm. After compression is completed, it is broadcast to other inter-group nodes. When the inter-group central nodes receive at least 2 valid prepare messages ( represents the count of Byzantine nodes), they enter the PBFT-COMMIT phase.
Step 3.4: In the PBFT-COMMIT phase, the inter-group central nodes first generate a commit message with the format . Then, the compression algorithm is used to compress the of the commit message, and the compressed message is broadcast to all inter-group consensus nodes. Once the central nodes between each group have obtained at least valid commit messages, the group enters its internal consensus phase.
Step 3.5: In the intra-group consensus phase, each group’s central node acts as the Raft leader node, and the remaining nodes are follower nodes. The leader node first uses the Brotli compression algorithm to compress the log message that needs to be sent, with the message format . Then, it broadcasts the compressed log to the follower nodes within the group.
Step 3.6: Upon receiving the compressed log, the follower nodes transmit the data to the supervisory node for verification of legality and consistency. Once the supervisory node completes this verification, it disseminates the results to other supervisory nodes within the group. Following mutual confirmation among the supervisory nodes across groups, these nodes send confirmation messages to all follower nodes within their respective groups, informing them that the data has been validated.
Step 3.7: After the follower nodes receive the confirmation message from the supervisory node, they complete the consensus and feed back the information to the leader node. The leader node will count the number of additional log preparation messages received and record it as . When , the nodes within the group reach consensus and submit the log. The leader of this group enters the PBFT-REPLY phase.
Step 3.8: The inter-group nodes send a message indicating the completion of consensus to the client as a reply, completing the consensus among the network nodes. The message format is where represents the timestamp and represents the execution result of the request.
4. Results Analysis
This section presents theoretical analysis and experimental simulation tests of NG-RPBFT. The theoretical analysis will evaluate the algorithm’s performance across three key dimensions: consistency, security, and communication efficiency. The experimental tests will validate the algorithm’s advantages in consensus delay, transaction throughput, and message load by comparing it with other existing algorithms.
4.1. Theoretical Analysis
4.1.1. Number of Communications
The volume of communication serves as a critical metric for assessing the complexity of information exchange among nodes in a blockchain network during the consensus process. When the frequency of communications becomes excessive, the system may face issues such as increased latency, diminished throughput, and excessive consumption of network resources. Consequently, an efficient consensus mechanism can effectively mitigate communication complexity and substantially enhance system performance.
This section will first analyze the specific amount of communication required to reach consensus when using PBFT and Raft, then analyzes the quantity of communications required for reaching a consensus using NG-RPBFT and compares it with the quantity of communications of the above two algorithms. In the following analysis, we assume the system’s total number of nodes is .
First, during the pre-preparation phase, the master node will propagate pre-preparation-related messages to other nodes, which means the master node selection sends one message to
nodes, so the total number of messages is
. Then, in the prepare phase, all follower nodes broadcast verified messages to all other nodes. Each node sends messages to
other nodes, so each node sends
messages. Since there are
nodes involved, the total messages is
. Finally, each node broadcasts a confirmation message to other nodes again in the commit phase to indicate that it is ready and agrees to commit the proposal. Similarly to the prepare phase, each node sends a confirmation message to
nodes, and the total number of messages is
. Therefore, the communication times
for PBFT to reach a consensus once is [
36]:
- 2.
Communication times of Raft algorithm
In the log replication phase, the leader node duplicates and distributes its log entries to every follower node. Each replication requires the leader node to send log entries to
nodes, and each follower node sends an acknowledgment message back to the leader node after receiving the log entries. Therefore, the leader sends log messages to
nodes, and the follower nodes send confirmation messages to the leader node, so the total number of messages is
. Subsequently, when the leader node receives enough confirmation messages, it will reply to the client and all follower nodes, and the number of messages is
. The communication times
for Raft to reach a consensus once is:
- 3.
Communication times of NG-RPBFT algorithm
The NG-RPBFT algorithm divides nodes in the system into groups, with each group containing approximately nodes. In the inter-group consensus phase, PBFT is adopted for consensus. The central nodes among the groups need to exchange and verify messages. Based on the communication count of PBFT, the total communication count for inter-group consensus is .
In the intra-group consensus phase, the leader node first broadcasts log messages to all follower nodes and supervisory nodes within the group, and the communication times is . Subsequently, all follower nodes send the received data to the supervisory node for legality and consistency verification, and the communication times of this process is .
After completing the verification, the supervisory node broadcasts the verification results to other supervisory nodes within the group, with a communication count of . After the supervisory nodes between groups confirm each other, they transmit confirmation notifications to all intragroup follower nodes, notifying them of the data’s successful verification and they can continue to execute the subsequent steps of the Raft algorithm. The communication times of this process is . Finally, after the intra-group consensus is completed, the follower nodes send commit messages back to the leader node to confirm the log commit status, and the communication times is .
Comprehensively considering the communication overhead of the above phases, the total communication times can be calculated by the following formula:
To sum up, the communication complexity for a single consensus round in the PBFT algorithm is
, while that of the Raft algorithm is
, When compared with these two algorithms, our algorithm exhibits a communication complexity of
. In this paper, by implementing the grouping mechanism, our algorithm successfully avoids the exponential growth of communication frequency induced by the growth of node numbers in PBFT. As the node scale continues to expand, the communication overhead of our algorithm gradually approaches the communication complexity of Raft. This approach cuts down the overall communication overhead significantly and secures the system’s efficiency and adaptability when applied to large-scale supply chain traceability.
Figure 5 below presents the specific comparison regarding communication times.
In Raft, the costs associated with leader replacement arise mainly from the duration of elections, the overhead of log synchronization, and diminished availability. In PBFT, view changes necessitate broadcasts that require confirmation from 2f + 1 nodes, resulting in message volume that scales with the number of nodes. Additionally, new views require the resynchronization of checkpoints and uncommitted transactions, while nodes must also track timed-out transactions. Nevertheless, we consider this expenditure to be acceptable.
4.1.2. Security
In distributed systems, security is important in safeguarding the system’s correctness and stability, especially when dealing with Byzantine node attacks. The NG-RPBFT consensus algorithm effectively enhances the system’s security by combining PBFT and introducing supervisory nodes from Raft.
The master node is selected using a multi-index comprehensive rating model. This model evaluates node performance and credibility, thereby ensuring that the node with the highest score in each consensus round is chosen as the master. This approach prevents malicious nodes from tampering with the election results through random selection or unreliable mechanisms, thereby improving the system’s stability.
In inter-group consensus, the PBFT protocol can tolerate up to 2/3 Byzantine nodes, ensuring the correctness of cross-group consensus. In intra-group consensus, the node boasting a higher comprehensive score is chosen as the supervisory node, tasked with verifying data synchronicity and consistency. Upon receiving log entries broadcast by the leader node, all group followers transmit the data to the supervisory node to verify its legality and consistency. The supervisory node uses the SHA algorithm to calculate the log summary and generates a verification message, which is broadcast to other supervisory nodes. When the supervisory node receives more than valid verification messages, it disseminates a confirmation message to every node within the group. If it fails to receive sufficient verification messages within the specified time, the leadership re-selection mechanism is triggered, and the intra-group consensus process is re-executed.
Through these security mechanisms, the NG-RPBFT algorithm can effectively prevent malicious behavior of Byzantine nodes and ensure security as well as data consistency.
4.1.3. Consistency
To ensure the high availability of the system, the BASE (Basically Available, Soft State, Eventually Consistent) theory is usually adopted to construct distributed systems. The consistency in this context refers to eventual consistency rather than strong consistency. Eventually consistency means that the system can ensure that all non-byzantine nodes reach a consensus within a certain period of time [
37,
38].
In the NG-RPBFT consensus algorithm, inter-group consensus is achieved through the PBFT protocol, which demonstrates high fault tolerance by accommodating up to f Byzantine nodes while maintaining consistency. The PBFT protocol authenticates the legitimacy of messages through multiple validation phases, ensuring consistent consensus among all participating nodes. Within each group, the Raft protocol is utilized to uphold log consistency, even in the face of node failures or network disruptions. Successful group consensus can be attained as long as more than half of the nodes receive log messages from the leader node. This algorithm specifically enhances consensus efficiency both within and between groups by integrating supervisory nodes and Brotli data compression technology, thereby improving the system’s fault tolerance and stability.
First, PBFT manages the overall coordination of cross-group transactions. When a PBFT node enters the PBFT-COMMIT phase, the processing of the COMMIT message activates the initiation of intra-group Raft consensus. PBFT guarantees cross-group transaction consistency by disseminating PREPREPARE, PREPARE, and COMMIT messages, whereas Raft finalizes local transaction commits within groups via log replication and acknowledgment mechanisms.
Cross-group transactions undergo the complete consensus process of PBFT, which includes the phases of pre-prepare, prepare, and commit, necessitating agreement from more than 2f + 1 nodes. The checkpoint mechanism periodically synchronizes the global state; each checkpoint comprises transaction summaries and node signatures, thereby ensuring eventual consistency across groups. Within individual groups, leader-broadcasted logs and majority confirmation mechanisms facilitate log synchronization among nodes. The leader maintains a committed log track, and upon receiving majority confirmation, it updates the commit index to ensure intra-group consistency. The PBFT-COMMIT phase initiates Raft’s intra-group consensus. Only after Raft completes its commit within the group does PBFT send a REPLY to the client, thus ensuring consistency in multi-group commits.
Therefore, the NG-RPBFT algorithm can ultimately ensure the consistency of the system within the upper limit of tolerable Byzantine nodes, meeting the requirements of distributed systems for high availability and eventual consistency.
4.1.4. Cross-Group Mutual Confirmation of the Impact on Latency and Throughput
Cross-group mutual acknowledgment primarily increases end-to-end latency through several mechanisms. Within the multi-phase messaging of PBFT, cross-group confirmation necessitates waiting for consensus outcomes from multiple clusters. Each phase entails message serialization, network transmission, and validation, resulting in cumulative delays. In the Raft consensus algorithm, the leader must wait for LOG_ACK from all replicas; in cross-group scenarios, the increased number of replicas extends waiting times. Intra-cluster nodes communicate through sockets, while cross-group communication involves longer network paths and necessitates managing connections and data transfers across a greater number of nodes.
Throughput degradation primarily arises from concurrency constraints. Cross-group acknowledgements extend the processing times of individual requests, thereby diminishing the number of requests handled per unit time. When multiple groups process messages concurrently, the presence of global counters and locking mechanisms adversely affects throughput as the number of supervisory nodes increases. Cross-group acknowledgements require the transmission of larger volumes of metadata; however, our implementation utilizes data compression to mitigate the impact on throughput. While higher supervisory quorum sizes and thresholds enhance security, they also introduce increased latency. Practical deployment necessitates a balance between these factors and fault tolerance requirements, favoring lower thresholds in real-time systems and higher thresholds in security-critical environments.
4.2. Experimental Measurement
The experiment was carried out on a PC featuring an Intel(R) Core(TM) i7-12700H processor and 16 GB of memory, with the operating system being Windows 11 and the experimental development language being Python 3.8. The proposed NG-RPBFT consensus algorithm in this paper was compared with traditional PBFT, LRBFT [
30], and TP-PBFT [
32]. This paper compares the differences between this algorithm and the existing ones. During the comparison, many aspects were taken into consideration, including consensus delay, transaction processing capability, anti-attack performance, as well as the analysis of message compression before and after the implementation of the scheme.
The experimental test analyzed the compression rates of four compression algorithms (Brotli, ZSTD, GZIP, SNAPPY) under four message types (Checkpoint, Checkpoint_Vote, Commit, New_View). A compression rate closer to 1 indicates a weaker compression effect, while a smaller value corresponds to a higher compression ratio. The experimental result is shown in
Figure 6.
The experimental results indicate that Brotli exhibits the lowest compression rate across all message types, yet it achieves the highest compression ratio. This method ensures security while delivering optimal compression, effectively reducing network bandwidth usage, decreasing the time cost associated with message transmission, and enhancing the overall efficiency of the NG-RPBFT consensus.
The experiment used Brotli data compression technology to compress the message load for reaching a consensus among 30 nodes.
Table 1 shows the experiment results.
The experimental results demonstrate that Brotli compression technology significantly reduces the volume of message transmission during the consensus process. This optimization lowers communication costs and minimizes network bandwidth usage, thereby enhancing the overall efficiency of the blockchain consensus mechanism. By integrating Brotli technology, the NG-RPBFT algorithm is better suited for operation in large-scale node network environments, providing effective support for high communication demand scenarios, such as supply chain traceability.
- 2.
Comparison of anti-attack capability
The consensus success rate measures the proportion of times the algorithm successfully reaches consensus under specific conditions. The formula for calculating the consensus success rate is:
Among them, represents the consensus success rate, indicates the number of rounds in which consensus was successfully achieved, and denotes the total number of test rounds.
The security score provides a comprehensive quantification of various security dimensions, which includes the algorithm’s ability to resist attacks as well as its tolerance for faults. Typically, it is computed using a weighted scoring method that integrates multiple sub-indicators. This paper evaluates the consensus algorithm’s performance in an attack scenario based on success rate, latency, throughput, and security reward points.
Among them, represents the security score, represents the consensus success rate, represents the delay penalty term, represents the throughput reward term, represents the security bonus points, and , , , are the score weights.
The anti-attack capability was assessed by calculating the consensus success rate and security score performance of four consensus algorithms (NG-RPBFT, PBFT, LRBFT, and TP-PBFT) under various attack types in the “100 nodes, 30% Byzantine nodes” scenario.
Figure 7 illustrates the experimental results.
Experimental results indicate that NG-RPBFT offers substantial advantages in mitigating multiple attack scenarios. In five distinct scenarios—double spending attack, leader attack, network partition, Sybil attack, and eclipse attack—the consensus success rate and security scores of PBFT exhibit considerable fluctuations, highlighting its limited security protection capabilities. Although TP-PBFT and LRBFT show less volatility in their consensus success rates and security scores compared to PBFT, their overall performance remains inferior to that of NG-RPBFT. In contrast, NG-RPBFT achieves the highest consensus success rate and security score, suggesting that it sustains exceptionally high consensus levels when faced with various malicious attacks. Moreover, NG-RPBFT’s Byzantine fault-tolerant design effectively addresses numerous tampering and forgery attempts, showcasing robust security resilience against malicious threats.
- 3.
Comparison of consensus delay
Consensus delay serves as a critical metric for evaluating the performance of consensus algorithms. It denotes the duration necessary for nodes to initiate a consensus request and for the system to achieve consensus. A reduced consensus delay indicates superior performance of the consensus method. The formula for calculating consensus delay is:
Among them, represents the consensus delay, is the time at which the master node receives the reply message and the transaction is successful, and is the time when the client initiates the consensus request.
During the experiment, the average of 20 experimental data points was used as the consensus delay. The algorithm was tested under the conditions of 5 groups and a fixed group size of 10, respectively. The results obtained from the experiment are presented in
Figure 8.
Experimental results indicate that the proposed NG-RPBFT algorithm demonstrates a significantly lower consensus delay compared to the PBFT, LRBFT, and TP-PBFT algorithms. As the number of nodes increases, the traditional PBFT algorithm exhibits the most rapid increase in consensus delay, highlighting its inadequacy for large-scale applications. Although LRBFT and TP-PBFT show slower rates of delay growth than PBFT, their delays still escalate with an increasing number of nodes, resulting in markedly inferior performance relative to NG-RPBFT. In contrast, NG-RPBFT reveals the slowest growth rate in consensus delay, with its performance advantage becoming especially evident in scenarios involving a large number of nodes. The optimized grouping strategy employed by the NG-RPBFT algorithm effectively mitigates consensus delay. When the number of nodes reaches 100, its consensus delay is approximately one-tenth that of PBFT, signifying a substantial performance enhancement. At 160 nodes, regardless of whether the number of groups is set to 5 or the number of nodes per group is fixed at 10, NG-RPBFT consistently achieves a low consensus delay, significantly outperforming the PBFT, LRBFT, and TP-PBFT algorithms. This approach markedly improves efficiency while maintaining security, ultimately realizing low-delay characteristics in large-scale node configurations.
In conclusion, NG-RPBFT demonstrates strong performance in small-scale node networks and exhibits a notable advantage in maintaining a slow growth rate of consensus delay in large-scale node networks. Furthermore, it can be effectively utilized in supply chain traceability scenarios.
- 4.
Comparison of transaction throughput
Transaction throughput denotes the volume of transactions or data that the system processes within a unit of time, usually represented by the number of transactions processed per second (TPS).
Among them, represents the time interval required for processing transactions, and represents the count of transactions processed within that time span.
The experiment involved setting the number of transactions to 2000. Through varying the count of nodes, we tested the per-second transaction throughput, and
Figure 9 shows the test results.
Experimental results indicate that the NG-RPBFT algorithm significantly outperforms traditional PBFT, LRBFT, and TP-PBFT algorithms in terms of throughput. With 20 nodes, NG-RPBFT achieves a throughput nearing 2000 Tx/s, greatly exceeding the performance of the other algorithms. Even when scaled to 40 nodes, the throughput remains robust at approximately 1600 Tx/s, demonstrating exceptional processing capabilities. As the number of nodes increases further, all algorithms experience some degree of throughput decline; however, the extent of this decline varies considerably. The traditional PBFT algorithm shows the most substantial decrease, with its throughput falling to around 100 Tx/s when the node count reaches 160. The throughput of LRBFT and TP-PBFT continues to diminish as the number of nodes rises, stabilizing at only 300–400 transactions per second at 160 nodes, which reflects a significant efficiency decay. In contrast, the NG-RPBFT algorithm employs a group optimization method to mitigate the throughput decline associated with the increasing number of nodes. At 160 nodes, configured into 5 groups of 10 nodes each, the throughput remains stable at approximately 400 Tx/s, surpassing that of the other algorithms.
The NG-RPBFT algorithm exhibits enhanced scalability and stability in large-scale networks, making it particularly well-suited for complex scenarios such as supply chain traceability, which demand high throughput and the ability to support numerous nodes.
- 5.
Evaluation of Grouping Model Based on Comprehensive Node Rating and Geographical Location
The NG-RPBFT algorithm presents a grouping model that integrates comprehensive node scores with geographical locations. Initially, we assessed the inherent limitations of single-grouping strategies by employing experimental control variables. Standardized test nodes, characterized by randomized latitude and longitude coordinates and composite scores ranging from 0.5 to 1.0, were generated using a specific function. The experiments were conducted under controlled conditions, involving 50 nodes, 5 groups, and 5 repeated rounds, with each round comprising 50 transactions.
The results obtained from the experiment are presented in
Figure 10. The results indicated that grouping based solely on geographical location, despite reducing physical communication distances through latitude-longitude clustering, did not effectively filter node quality. This oversight permitted low-scoring nodes to infiltrate groups, resulting in consensus challenges such as response timeouts and data synchronization failures. Conversely, while grouping exclusively by node rating selected high-quality nodes, it overlooked variations in geographical distribution. Cross-regional nodes experienced elevated network hop counts and significant bandwidth fluctuations, which exacerbated message exchange delays during consensus phases and compromised real-time performance. Random grouping neither incorporates node quality screening nor optimizes geographical clustering. As a result, it demonstrates the highest message transmission delays and consensus failure rates among all grouping strategies, failing to satisfy the efficiency and stability requirements of distributed systems.
NG-RPBFT effectively filters out nodes with low reliability and performance through a comprehensive scoring system. This process guarantees that group members maintain stable computational and communication capabilities, thereby minimizing interference from anomalous nodes and enhancing the success rates of consensus. Building on this foundation, the selected high-quality nodes are further clustered according to their geographical coordinates of latitude and longitude. This clustering ensures that nodes within the same group are located in close proximity within the network, which shortens message transmission paths. Experimental data indicate that NG-RPBFT achieves lower average delays compared to any single grouping strategy, while also demonstrating significantly higher average throughput and success rates. These findings validate the necessity and superiority of both comprehensive node rating and geographical grouping.
5. Case Studies
To validate the practical applicability of the NG-RPBFT algorithm in real-world supply chain traceability under CPS, this section presents five daily life cases where the model can be immediately integrated. Each case highlights the algorithm’s ability to address industry-specific pain points and deliver tangible value.
5.1. Food Supply Chain Traceability
The organic food supply chain involves multiple stakeholders—farmers, processing facilities, cold-chain logistics providers, retailers, and regulatory agencies—with nodes distributed across regions. Key challenges include ensuring data transparency, real-time tracking of perishable goods, and resistance to malicious tampering.
The NG-RPBFT algorithm evaluates nodes across three dimensions: service level (farmers’ on-time delivery rate, retailers’ shelf-life maintenance capability), consensus success rate (historical data accuracy), and resource attributes (logistics providers’ cold chain equipment operational status). Nodes with higher scores are prioritized for selection as group leader nodes. Then, Geographical Grouping: Use the improved K-medoids algorithm to group geographically proximate nodes, reducing cross-regional communication delays for time-sensitive data such as temperature records during transportation. Inter-group PBFT ensures data consistency across the entire chain, while intra-group Raft with supervisory nodes accelerates real-time updates. Brotli compression reduces bandwidth usage for frequent temperature/humidity sensor data in CPS. Consumers scan QR codes to access tamper-proof traceability records, regulators efficiently audit compliance, and retailers minimize losses from spoiled goods via real-time monitoring.
5.2. Pharmaceutical Supply Chain
Vaccine supply chains require strict temperature control, batch traceability, and anti-counterfeiting measures. Stakeholders include pharmaceutical manufacturers, cold-chain carriers, hospitals, and drug regulators, with nodes spanning global production sites, regional distribution centers, and local clinics. Challenges include high communication complexity, data security, and low latency.
The NG-RPBFT algorithm can evaluate nodes across three dimensions: pharmaceutical manufacturers’ production capacity, transporters’ temperature control reliability, and on-time delivery rates to clinics alongside historical batch data accuracy. Grouping shall be determined by combining comprehensive scores across production zones, distribution centers, and nodes, ensuring that high-performance nodes such as certified cold chain transporters serve as consensus leader nodes within their respective groups. The inter-group PBFT consensus mechanism can tolerate Byzantine attacks such as malicious nodes tampering with temperature data, while intra-group supervisory nodes are responsible for verifying data integrity. Brotli compression technology optimizes transmission efficiency for real-time sensor data such as vaccine storage temperatures. Regulators trace vaccine batches from production to administration, hospitals verify product authenticity, and manufacturers reduce recall risks by identifying bottlenecks in real time.
5.3. Luxury Goods Anti-Counterfeiting & Traceability
The luxury goods supply chain faces rampant counterfeiting issues involving multiple entities such as raw material suppliers, manufacturers, distributors, and authorized retailers. Core challenges include ensuring transparency requirements like authenticating raw material sourcing, preventing tampering with traceability records, and accommodating scalability demands across global node networks.
The NG-RPBFT algorithm’s node credibility scoring mechanism evaluates suppliers across three dimensions: service levels (such as raw material quality stability), consensus success rates corresponding to historical product traceability data accuracy, and resource attributes (like production facility security). Only high-scoring nodes, such as authorized suppliers, are selected as central nodes within groups. During grouping, clustering is performed based on the comprehensive scores of nodes and production regions (e.g., suppliers, manufacturers), reducing communication delays between design studios and factories. At the consensus mechanism level, inter-group PBFT consensus ensures tamper-proof recording throughout the entire process of raw material procurement, production, and distribution. Intra-group Raft consensus, incorporating supervisory nodes, prevents internal fraud such as factory personnel substituting genuine parts with counterfeits.
This ultimately delivers application value enabling consumers to verify product authenticity via blockchain records detailing leather origin and production dates, allowing brands to protect intellectual property, and enabling retailers to eliminate losses from counterfeit inventory.
5.4. Automotive Parts Supply Chain
The electric vehicle supply chain encompasses hundreds of component suppliers, assembly plants, logistics providers and distributors, featuring a vast network of nodes distributed globally. Key challenges in this domain include the high scalability of nodes, the complexity of cross-regional communications, and stringent requirements for component compatibility and quality.
The NG-RPBFT algorithm prioritizes nodes with ample computational/storage resources and accurate component quality records. It groups components based on type and geographical location to optimize communication efficiency among complementary component manufacturers. Brotli compression technology reduces transmission volumes for component specifications and real-time quality data; intra-group Raft consensus mechanisms accelerate data sharing between assembly plants and suppliers, while inter-group PBFT consensus mechanisms ensure data consistency across the entire chain.
As a result, automotive manufacturers can trace component origins and swiftly pinpoint quality issues; suppliers can shorten delivery cycles through real-time collaboration; regulatory bodies can verify whether components meet safety standards.
5.5. Fast-Moving Consumer Goods Supply Chain
The fast-moving consumer goods supply chain encompasses raw material suppliers, manufacturing plants, distributors and supermarkets. With nodes densely distributed across a wide geographical area, core challenges include real-time tracking of product shelf life, preventing grey market goods, and managing high transaction volumes.
NG-RPBFT scores raw material suppliers based on delivery timeliness and production plants according to batch data accuracy; groups nodes by urban-rural regions to optimize local data synchronization efficiency; employs intra-group Raft to accelerate real-time inventory updates while inter-group PBFT ensures cross-chain consistency of production dates; Brotli compression technology reduces sales transaction data volume, enabling real-time sales record uploads even from convenience stores with limited bandwidth.
Therefore, brands can track product distribution channels to prevent parallel imports, retailers can optimize inventory, and consumers can use product barcodes to check expiry dates and production origins.