Ivy Oracle: A Robust and Time-Trustworthy Data Feed Framework for Smart Contracts
Abstract
1. Introduction
1.1. Technical Challenges
- Enduring Failure of TEE Time Source. TEEs such as Intel SGX and Arm TrustZone lack native support for trusted, high-resolution timekeeping. Existing approaches either rely on enclave timers (which are manipulable by the host) or assume external synchrony. This opens the door to time-delay attacks [20], where the host can freeze or replay stale data. However, in many time-sensitive applications (e.g., DeFi liquidations), ensuring that the datagram reflects the correct timestamp is critical to maintaining on-chain consistency and fairness.
- Malicious TEE Host. Although TEEs offer strong guarantees of execution integrity and confidentiality, they rely on a host machine for power, I/O, and scheduling. A malicious or compromised host may abort the TEE, tamper with data flow, or selectively censor outputs. Given that TEEs are often deployed in untrusted infrastructure (e.g., public cloud), ensuring liveness and delivery of oracle responses despite a hostile host remains an open problem.
- Unreliable Data Sources. To achieve robust blockchain oracle, the primary issue is to obtain reliable data from data sources. However, there is no, of course, fully trustworthy data sources in real-world. Thus, lots of schemes acquire data from multiple data sources and aggregate data as a final answer, e.g., the majority voting. That is, if majority of data sources return an identical answer, then the oracle returns this answer. Unfortunately, there exist many correlated data sources that inaccurate data from will definitely have influence on .
- Atomic Delivery of Datagrams. In traditional smart contract workflows, the user pays a transaction fee to invoke the oracle but may not receive any useful response if the oracle fails to deliver. This leads to both economic loss and poor user experience. Therefore, ensuring atomic delivery, meaning that the data and the fee are either both successfully exchanged or both withheld, is a key requirement for practical oracle adoption.
1.2. Contributions
- Identification and formalization of key challenges. We rigorously analyze the weaknesses of prior oracle systems and highlight two fundamental obstacles: the lack of a time trustworthy source in TEEs, which enables delay or replay attacks, and the prevalence of unreliable or correlated data sources, which undermines aggregation-based trust models.
- Hybrid architecture with verifiable time and trust evaluation. We design Ivy Oracle as a modular architecture that integrates TEE-based secure execution, an external time server for authenticated timestamp attestation, and a PageRank-inspired trust model for evaluating and weighting data sources. This hybrid design ensures both robustness and time trustworthiness, going beyond majority-voting assumptions.
- Configurable and auditable data feed. Ivy Oracle supports multi-round data collection and user-defined aggregation strategies (e.g., majority vote, averaging, or custom functions), allowing flexibility for diverse smart contract applications. All trust scores and timestamp attestations are committed on-chain, enabling auditability and dispute resolution in case of misbehavior.
- Atomic and incentive-compatible delivery. We incorporate an atomic delivery mechanism tied to deposits and signatures, ensuring that users either obtain both the data and pay the fee, or neither. This reduces economic risk and improves usability for latency-sensitive decentralized finance (DeFi) and supply-chain scenarios.
- Prototype implementation and evaluation. We implement Ivy Oracle on the Ethereum Sepolia testnet, demonstrating end-to-end feasibility. Our evaluation shows that Ivy Oracle achieves strong guarantees of robustness, time trustworthiness, and trust configurability with minimal off-chain and on-chain overhead, confirming its practicality for real-world deployment.
1.3. Paper Organization
2. Related Works
3. Preliminary Review
3.1. Smart Contract and Transaction
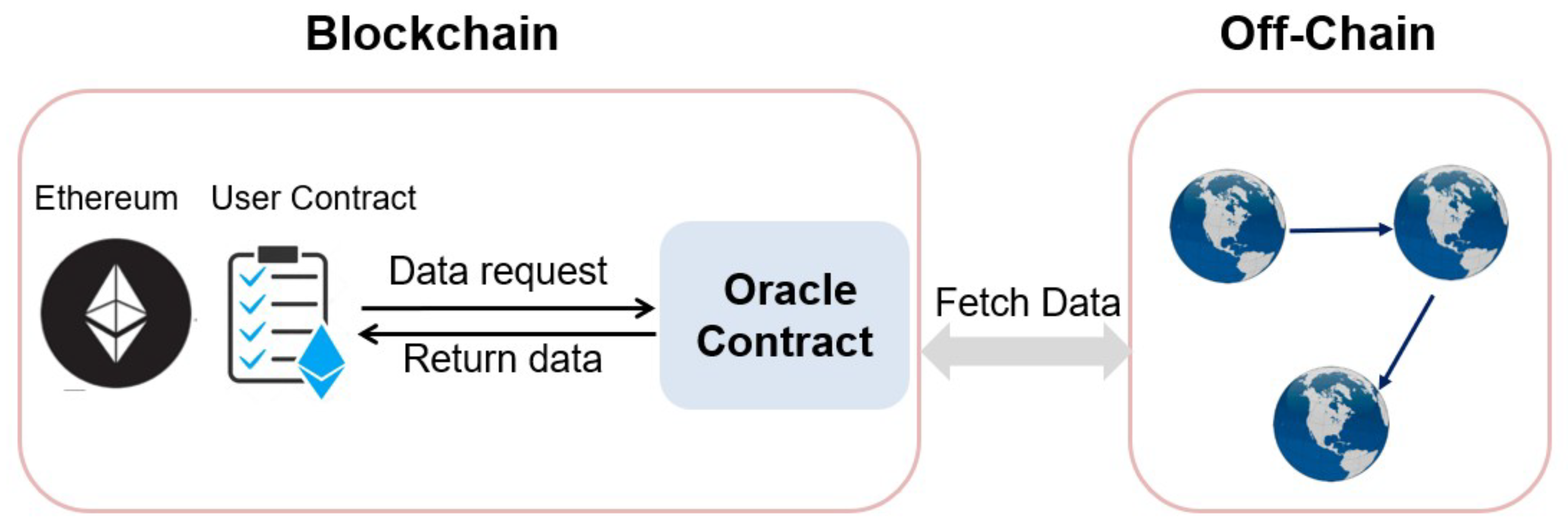
3.2. Blockchain Oracle
3.3. Time Server
3.4. Trust Execution Environment
3.5. PageRank
4. Overview of Ivy Oracle
4.1. System Model
- Ivy contract (): Deployed on the blockchain, it interacts directly with user contracts. It acts as the on-chain interface that receives data requests from users and dispatches them to the Ivy server based on the “Event” mechanism.
- Ivy Server (): It acts as a relay to acquire data from external data sources after receiving a request. Specifically, it embeds with TEE (e.g., SGX) that acquires data based on the HTTPS-enabled internet services, and is designed with a wallet that returns message to the user contract in a signed transaction.
- Time Server (): This trusted off-chain entity provides authenticated timestamps. It issues signatures on time-sensitive data operations initiated by the Ivy server or the data source using its private key . The corresponding public key is published on-chain so that the Ivy contract can verify the validity of time attestations before accepting results.
4.2. Security Model
4.3. Workflow
4.4. Desired Properties
- Robustness. The Ivy Oracle could obtain robust values from reliable data sources, that is, users can still obtain trustworthy data in spite of limited knowledge on selecting reliable data sources.
- Time-insensitivity. Data is called time-sensitive data when it changes dramatically within a small time interval. As for this type of data, the Ivy Oracle can provide reliable data based on users’ setting, which enables it to be time-insensitive data.
- Flexibility. As for the time-sensitive data, the Ivy Oracle allows user to select the model of data feed flexibly, e.g., setting data from Oracle as maximum value or average value.
5. The Ivy Oracle Protocol
5.1. Initialization
5.2. Contract Deployment
5.3. Request Analysis
| Algorithm 1: Data source selection based on LinkChecker and PageRank |
 |
5.4. Data Retrieval
| Algorithm 2: Data retrieval from stable data sources |
 |
5.5. Data Delivery
6. Security Analysis
- Authenticity and Integrity. The final result is accompanied by dual signatures: from the Ivy server and from the time server. These signatures are verified both by the Ivy contract and the user contract before any data is accepted on-chain. This ensures that responses are authentic and tamper-proof.
- Resilience Against Untrusted Data Sources. Given that external sources may return inaccurate or inconsistent values, the Ivy server employs a dual defense strategy. First, it assesses the trustworthiness of candidate sources using a PageRank score derived from the data relationship graph (DRG), built from inlinks and outlinks via hyperlink analysis. This score is committed to the blockchain for transparency and later audit. Second, performs timestamp consistency checks by comparing source time with a trusted time server, filtering out unreliable or manipulated sources.During retrieval, queries the selected source n times and applies a user-defined aggregation function (e.g., majority voting or averaging) over the results. This reduces the impact of individual corrupted responses and mitigates the influence of faulty or adversarial data providers.
- Freshness and Temporal Integrity. The system guarantees that retrieved data is recent and not replayed. This is achieved via two mechanisms: (1) sources are only selected if their clocks are aligned with a trusted time server, and (2) after aggregation, the final result is timestamped and signed by . This signature proves that was computed within the validity window specified in the request, preventing the use of outdated data.
- Dispute Resolution and Verifiability. In the event of incorrect or missing data, users can challenge the Ivy Oracle by invoking the time-locked deposit mechanism. Since the trust score computation, source selection, and timestamp checks are either logged or committed on-chain, any misbehavior can be publicly verified, and the user’s claim can be adjudicated automatically by smart contract logic. This incentivizes honest behavior from the Ivy server.
7. Performance Analysis
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Dos Santos, S.; Singh, J.; Thulasiram, R.K.; Kamali, S.; Sirico, L.; Loud, L. A new era of blockchain-powered decentralized finance (DeFi)—A review. In Proceedings of the 2022 IEEE 46th Annual Computers, Software, and Applications Conference (COMPSAC), Los Alamitos, CA, USA, 27 June–1 July 2022; pp. 1286–1292. [Google Scholar]
- Betti, Q.; Khoury, R.; Hallé, S.; Montreuil, B. Improving hyperconnected logistics with blockchains and smart contracts. IT Prof. 2019, 21, 25–32. [Google Scholar] [CrossRef]
- Malik, S.; Dedeoglu, V.; Kanhere, S.S.; Jurdak, R. PrivChain: Provenance and privacy preservation in blockchain enabled supply chains. In Proceedings of the 2022 IEEE International Conference on Blockchain (Blockchain), Espoo, Finland, 22–25 August 2022; pp. 157–166. [Google Scholar]
- Sriman, B.; Kumar, S.G. Decentralized finance (defi): The future of finance and defi application for ethereum blockchain based finance market. In Proceedings of the 2022 International Conference on Advances in Computing, Communication and Applied Informatics (ACCAI), Chennai, India, 28–29 January 2022; pp. 1–9. [Google Scholar]
- Wood, G. Ethereum: A Secure Decentralised Generalised Transaction Ledger. Technical Report, Ethereum Project. 2014. Available online: https://ethereum.github.io/yellowpaper/paper.pdf (accessed on 4 February 2025).
- Zou, W.; Lo, D.; Kochhar, P.S.; Le, X.B.D.; Xia, X.; Feng, Y.; Chen, Z.; Xu, B. Smart contract development: Challenges and opportunities. IEEE Trans. Softw. Eng. 2019, 47, 2084–2106. [Google Scholar] [CrossRef]
- Wang, S.; Yuan, Y.; Wang, X.; Li, J.; Qin, R.; Wang, F.Y. An overview of smart contract: Architecture, applications, and future trends. In Proceedings of the 2018 IEEE Intelligent Vehicles Symposium (IV), Changshu, Suzhou, China, 26–30 June 2018; pp. 108–113. [Google Scholar]
- Li, M.; Weng, J.; Weng, J.; Li, Y.; Wu, Y.; Li, D.; Xu, G.; Deng, R. IvyCross: A Privacy-Preserving and Concurrency Control Framework for Blockchain Interoperability. IEEE Trans. Mob. Comput. 2025, 24, 9334–9351. [Google Scholar] [CrossRef]
- Beniiche, A. A study of blockchain oracles. arXiv 2020, arXiv:2004.07140. [Google Scholar] [CrossRef]
- Caldarelli, G. Understanding the blockchain oracle problem: A call for action. Information 2020, 11, 509. [Google Scholar] [CrossRef]
- Zheng, Z.; Xie, S.; Dai, H.N.; Chen, W.; Chen, X.; Weng, J.; Imran, M. An overview on smart contracts: Challenges, advances and platforms. Future Gener. Comput. Syst. 2020, 105, 475–491. [Google Scholar] [CrossRef]
- Zhang, F.; Cecchetti, E.; Croman, K.; Juels, A.; Shi, E. Town crier: An authenticated data feed for smart contracts. In Proceedings of the 2016 ACM SIGSAC Conference on Computer and Communications Security, Vienna, Austria, 24–28 October 2016; pp. 270–282. [Google Scholar]
- Al-Breiki, H.; Rehman, M.H.U.; Salah, K.; Svetinovic, D. Trustworthy blockchain oracles: Review, comparison, and open research challenges. IEEE Access 2020, 8, 85675–85685. [Google Scholar] [CrossRef]
- Hassan, A.; Makhdoom, I.; Iqbal, W.; Ahmad, A.; Raza, A. From trust to truth: Advancements in mitigating the Blockchain Oracle problem. J. Netw. Comput. Appl. 2023, 217, 103672. [Google Scholar] [CrossRef]
- Cheng, R.; Zhang, F.; Kos, J.; He, W.; Hynes, N.; Johnson, N.; Juels, A.; Miller, A.; Song, D. Ekiden: A platform for confidentiality-preserving, trustworthy, and performant smart contracts. In Proceedings of the 2019 IEEE European Symposium on Security and Privacy (EuroS&P), Stockholm, Sweden, 17–19 June 2019; pp. 185–200. [Google Scholar]
- Breidenbach, L.; Cachin, C.; Chan, B.; Coventry, A.; Ellis, S.; Koushanfar, F.; Magauran, B.; Miller, A.; Moroz, D.; Nazarov, S.; et al. Chainlink 2.0: Next Steps in the Evolution of Decentralized Oracle Networks. White Paper. 2021. Available online: https://research.chain.link/whitepaper-v2.pdf (accessed on 15 April 2021).
- Ordoñez, C.C.; Ramirez-Gonzalez, G.; Corrales, J.C. Enhancing Data Integrity in Blockchain Oracles Through Multi-Label Analysis. Appl. Sci. 2025, 15, 2379. [Google Scholar] [CrossRef]
- Eskandari, S.; Salehi, M.; Gu, W.C.; Clark, J. Sok: Oracles from the ground truth to market manipulation. In Proceedings of the 3rd ACM Conference on Advances in Financial Technologies, Arlington, VA, USA, 26–28 September 2021; pp. 127–141. [Google Scholar]
- Qin, K.; Zhou, L.; Livshits, B.; Gervais, A. Attacking the defi ecosystem with flash loans for fun and profit. In Proceedings of the International Conference on Financial Cryptography and Data Security, Virtual, 1–5 March 2021; pp. 3–32. [Google Scholar]
- Behrens, J.; Cao, A.; Skeggs, C.; Belay, A.; Kaashoek, M.F.; Zeldovich, N. Efficiently mitigating transient execution attacks using the unmapped speculation contract. In Proceedings of the 14th USENIX Symposium on Operating Systems Design and Implementation (OSDI 20), Online, 4–6 November 2020; pp. 1139–1154. [Google Scholar]
- Guarnizo, J.; Szalachowski, P. PDFS: Practical data feed service for smart contracts. In Proceedings of the European Symposium on Research in Computer Security, Luxembourg, 23–27 September 2019; pp. 767–789. [Google Scholar]
- Park, J.; Kim, H.; Kim, G.; Ryou, J. Smart contract data feed framework for privacy-preserving oracle system on blockchain. Computers 2021, 10, 7. [Google Scholar] [CrossRef]
- Feng, L.; Zhu, H.; Yu, B.; Yao, S. Efficient Off-chain Data Feed Mechanism Using a Novel Blockchain Oracle Network Combined with Directed Acyclic Graph-Distributed Ledger. IEEE Trans. Netw. Sci. Eng. 2025, 12, 2810–2822. [Google Scholar] [CrossRef]
- Pasdar, A.; Lee, Y.C.; Dong, Z. Connect API with blockchain: A survey on blockchain oracle implementation. ACM Comput. Surv. 2023, 55, 1–39. [Google Scholar] [CrossRef]
- Kosba, A.; Miller, A.; Shi, E.; Wen, Z.; Papamanthou, C. Hawk: The blockchain model of cryptography and privacy-preserving smart contracts. In Proceedings of the 2016 IEEE Symposium on Security and Privacy (SP), San Jose, CA, USA, 23–25 May 2016; pp. 839–858. [Google Scholar]
- Mills, D.L. Network Time Protocol (Version 3) Specification, Implementation and Analysis. Rfc 1305, University of Delaware, 1992. Available online: https://datatracker.ietf.org/doc/html/rfc1305 (accessed on 24 November 2025).
- Zheng, W.; Wu, Y.; Wu, X.; Feng, C.; Sui, Y.; Luo, X.; Zhou, Y. A survey of Intel SGX and its applications. Front. Comput. Sci. 2021, 15, 1–15. [Google Scholar] [CrossRef]
- Costan, V.; Devadas, S. Intel SGX explained. Cryptology ePrint Archive 2016. Available online: https://ia.cr/2016/086 (accessed on 31 January 2016).
- Lee, D.; Kohlbrenner, D.; Shinde, S.; Asanović, K.; Song, D. Keystone: An open framework for architecting trusted execution environments. In Proceedings of the Fifteenth European Conference on Computer Systems, Heraklion, Greece, 27–30 April 2020; pp. 1–16. [Google Scholar]
- Haveliwala, T.H. Topic-sensitive pagerank. In Proceedings of the 11th International Conference on World Wide Web, Honolulu, HI, USA, 7–11 May 2002; pp. 517–526. [Google Scholar]
- Rogers, I. The Google Pagerank Algorithm and How It Works. 2002. Available online: http://www.iprcom.com/papers/pagerank/ (accessed on 24 November 2025).
- McBurney, P.W.; Liu, C.; McMillan, C. Automated feature discovery via sentence selection and source code summarization. J. Softw. Evol. Process 2016, 28, 120–145. [Google Scholar] [CrossRef]
- Inoue, K.; Yokomori, R.; Fujiwara, H.; Yamamoto, T.; Matsushita, M.; Kusumoto, S. Component rank: Relative significance rank for software component search. In Proceedings of the 25th International Conference on Software Engineering, Portland, OR, USA, 3–10 May 2003; pp. 14–24. [Google Scholar]
- Gleich, D.F. PageRank beyond the web. Siam Rev. 2015, 57, 321–363. [Google Scholar] [CrossRef]
- Garay, J.; Kiayias, A.; Leonardos, N. The bitcoin backbone protocol: Analysis and applications. In Proceedings of the Annual International Conference on the Theory and Applications of Cryptographic Techniques, Sofia, Bulgaria, 26–30 April 2015; pp. 281–310. [Google Scholar]
- Li, M.; Weng, J.; Yang, A.; Lu, W.; Zhang, Y.; Hou, L.; Liu, J.N.; Xiang, Y.; Deng, R. CrowdBC: A blockchain-based decentralized framework for crowdsourcing. IEEE Trans. Parallel Distrib. Syst. 2018, 30, 1251–1266. [Google Scholar] [CrossRef]



| Schemes | Authenticity | TEE-Based | Trusted | Data Source |
|---|---|---|---|---|
| Execution | Timestamp | Trust Evaluation | ||
| Town Crier [12] | ✓ | ✓ | × | × |
| Ekiden [15] | ✓ | ✓ | × | × |
| Chainlink [16] | ✓ | × | × | × |
| Al-Breiki et al. [13] | ✓ | × | × | × |
| Ordoñez et al. [17] | ✓ | × | × | × |
| PDFS [21] | ✓ | × | × | × |
| Park et al. [22] | ✓ | × | × | × |
| Feng et al. [23] | ✓ | × | × | × |
| Ivy Oracle | ✓ | ✓ | ✓ | ✓ |
| Request Numbers | 1 | 5 | 10 | 15 | 20 |
| Computation Overhead (ms) | 0.544 | 3.125 | 5.050 | 6.870 | 11.400 |
| Scheme | Signature | On-Chain (Bytes) |
|---|---|---|
| Chainlink | ECDSA-K1 | 580 |
| ECDSA-R1 | 580 | |
| Ed25519 | 516 | |
| Schnorr-K1 | 580 | |
| Ivy | ECDSA-K1 | 1028 |
| ECDSA-R1 | 1028 | |
| Ed25519 | 964 | |
| Schnorr-K1 | 1028 |
| Phase | Initialization | Contract Deployment | Data Retrieval |
|---|---|---|---|
| Time (s) | 13.241 | 66.779 | 0.132 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Xie, H.; Yan, Y.; Yao, X.; Zhang, K.; Liang, Y.; Lin, Z. Ivy Oracle: A Robust and Time-Trustworthy Data Feed Framework for Smart Contracts. Electronics 2025, 14, 4915. https://doi.org/10.3390/electronics14244915
Xie H, Yan Y, Yao X, Zhang K, Liang Y, Lin Z. Ivy Oracle: A Robust and Time-Trustworthy Data Feed Framework for Smart Contracts. Electronics. 2025; 14(24):4915. https://doi.org/10.3390/electronics14244915
Chicago/Turabian StyleXie, Hanyang, Yuping Yan, Xu Yao, Kun Zhang, Yingwei Liang, and Zhe Lin. 2025. "Ivy Oracle: A Robust and Time-Trustworthy Data Feed Framework for Smart Contracts" Electronics 14, no. 24: 4915. https://doi.org/10.3390/electronics14244915
APA StyleXie, H., Yan, Y., Yao, X., Zhang, K., Liang, Y., & Lin, Z. (2025). Ivy Oracle: A Robust and Time-Trustworthy Data Feed Framework for Smart Contracts. Electronics, 14(24), 4915. https://doi.org/10.3390/electronics14244915





