A Certificateless Online/Offline Aggregate Signcryption Scheme against Collusion Attacks Based on Fog Computing
(This article belongs to the Section Electrical and Autonomous Vehicles)
Abstract
:1. Introduction
1.1. Related Work
1.1.1. Fog Architecture
1.1.2. Scheme for Certificateless Aggregate Signcryption
1.1.3. Technology for Online and Offline Encryption
1.1.4. Collusion Attack
1.2. Research Contributions
- We suggest the anti-collusion component to thwart this type of assault, which is known as a collusion attack, taking into account that in particular schemes two vehicles might deliberately trade their signcryption information. This exchange can be successfully validated. Compared with the existing the scheme in [23], our proposed scheme can effectively resist collusion attacks;
- Based on the proposed scheme, we use fog computing to design a certificateless online/offline aggregate signcryption, which enhances the security of data and increases efficiency in the VANETs. The scheme realizes mutual authentication, anonymity, undeniability, untraceability, and confidentiality;
- In VANETs, the authentication of vehicle identity and the privacy of the messages as well as vehicles are both important [25]. In our scheme, we not only protect the privacy of messages but also use a vehicle pseudonym system to secure the privacy of vehicles as well as realize vehicle identification.
1.3. Paper Structure
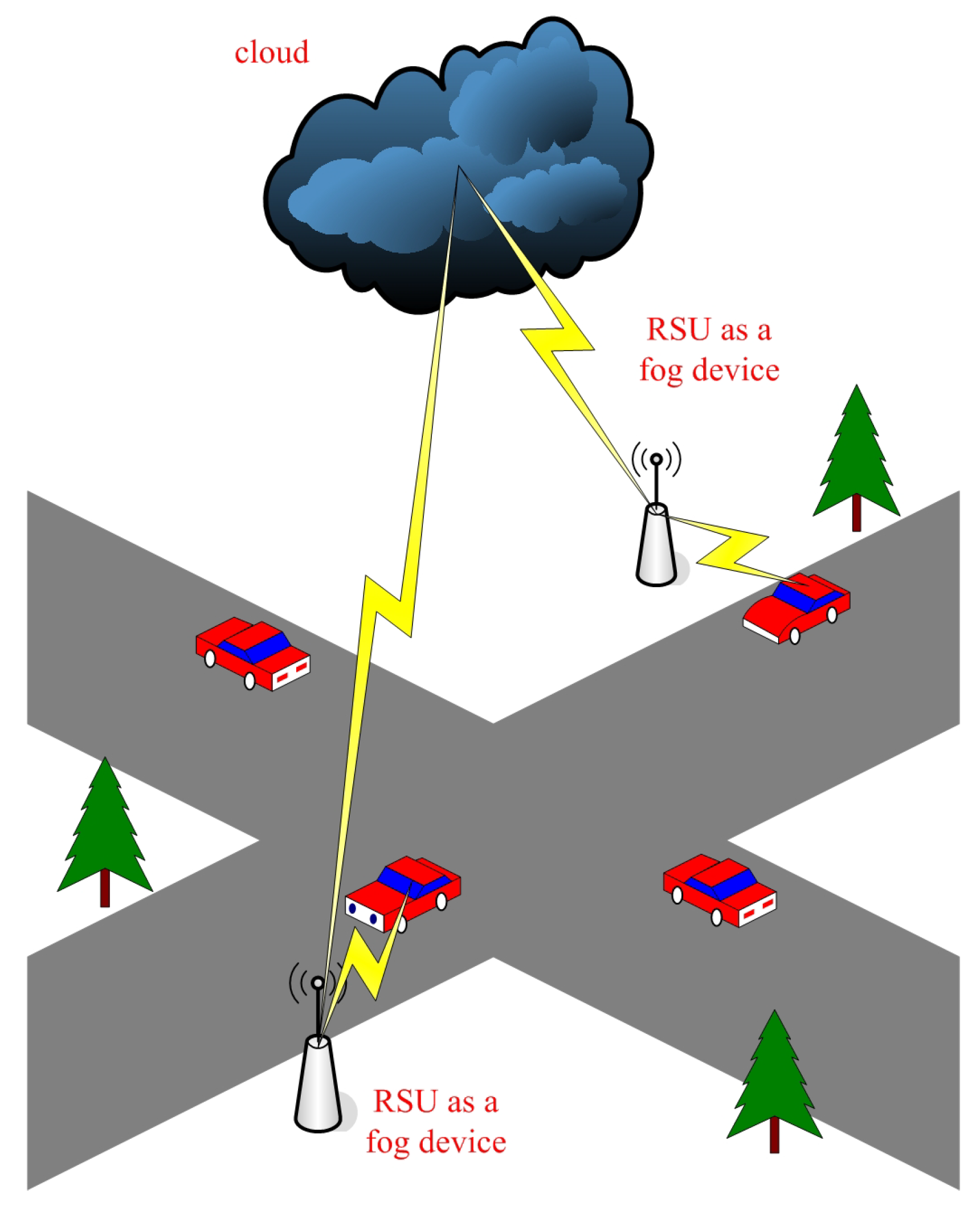
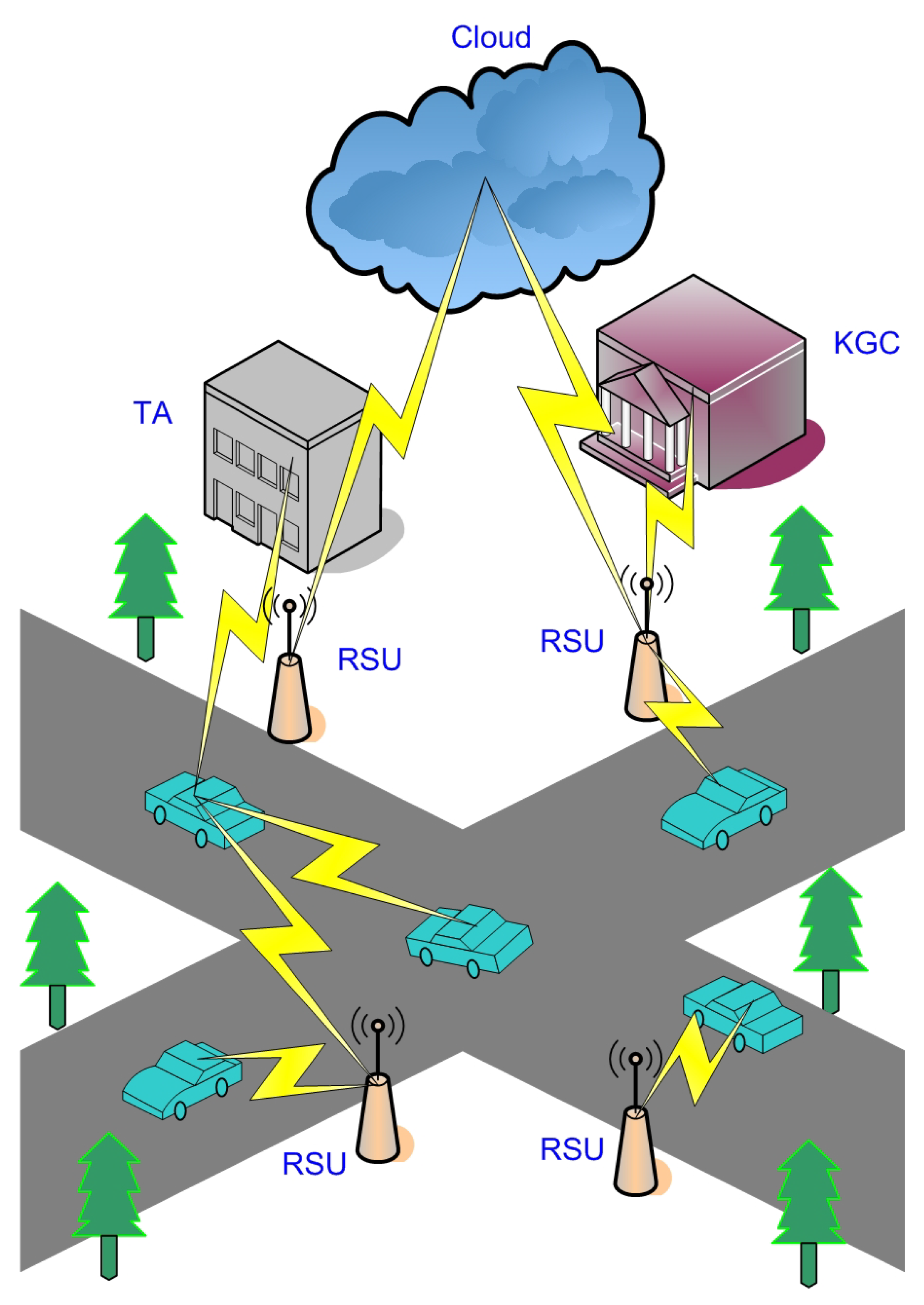
2. System Model, Attack Model, and Design objectives
2.1. System Model
- Intelligent devices are always embedded in vehicles to send signals, location, and road events and accept relevant information;
- The RSU is regarded as a fog device since it is closer than a cloud. It can process data in real-time while having less computational and storage capacity than the cloud;
- The system’s cloud server is designated as CS. The data will be sent here for long-term storage following processing at the RSU. Fog devices offer mobility, location awareness, and low latency in contrast to transmitting all of the sensor’s data straight to the cloud;
- The TA is a trusted authority, playing a crucial role in system initialization and vehicle pseudonym generation;
- KGC, a dependable organization, is in charge of setting up the system and producing a portion of the customers’ private keys. In particular, it cannot access the private data of RSUs and sensors.
2.2. Attack Model
- Attack obtaining the content of the message: Attackers can obtain user identity information or encrypted messages through eavesdropping on public channels or for further attacks;
- Traffic analysis attack: By observing and analyzing message patterns, the attackers can obtain the format of the message and determine the location and identity of both communication parties, which is sensitive to drivers.
- Reply attack: The attacker sends the ciphertext that the RSU has received and verified successfully to deceive the system;
- Tampering attack: Attackers may modify the information originally sent, causing the RSU to receive incorrect information and make incorrect decisions;
- Denial of service: The attacker delivers the ciphertext that the RSU has successfully received and validated in a reply to trick the system.
2.3. Design Objectives
- Mutual authentication: It is required between the RSU and the user in order to confirm the legitimacy of the network’s members;
- Vehicle identity verification: By verifying the vehicle’s identity through the TA, the sender of the message can be determined, enabling the tracking of malicious users to ensure the security of the vehicle’s environment;
- The user anonymity: All users who send messages must be anonymous to ensure the privacy of their information;
- Untraceability: Although the enemy intercepted the communication message, they were unable to track the user’s behavior;
- Undeniability: When a vehicle is involved in the authentication scheme, no vehicle can deny its behavior;
- Low computing cost: In the context of limited bandwidth, it is necessary to meet the requirement of low computing cost. Our proposed scheme is combines with CLASC and OOE, greatly reducing the computing overhead;
- Quick verification: Batch validation can be achieved through aggregation technology;
- Resist collusion attacks: In part of the schemes, two vehicles can maliciously exchange their signcryption information, which can be verified successfully. This can be very dangerous and even cause irreversible damage to the vehicles in the vehicular ad hoc networks (VANETs). Thus, it is very important to design a scheme that can resist collusion attacks.
3. Preliminaries
- The elliptic curve discrete logarithmic problem (also known as the elliptic curve discrete logarithm problem, or ECDLP): Given any point Q ∈ G, an a ∈ on the elliptic curve, and a set of elements , solving a is challenging. G is an additive group on the elliptic curve of q-order and P is the generator of G;
- The elliptic curve computational Diffie–Hellman problem (also known as the EC-CDH assumption) is defined as follows: G is an additive group on the elliptic curve of q-order. Let P be one of G’s generators. Given , , and a, , it is difficult to compute ;
- Hash collision resistance: Finding x and such that is a challenging task for a hash function.
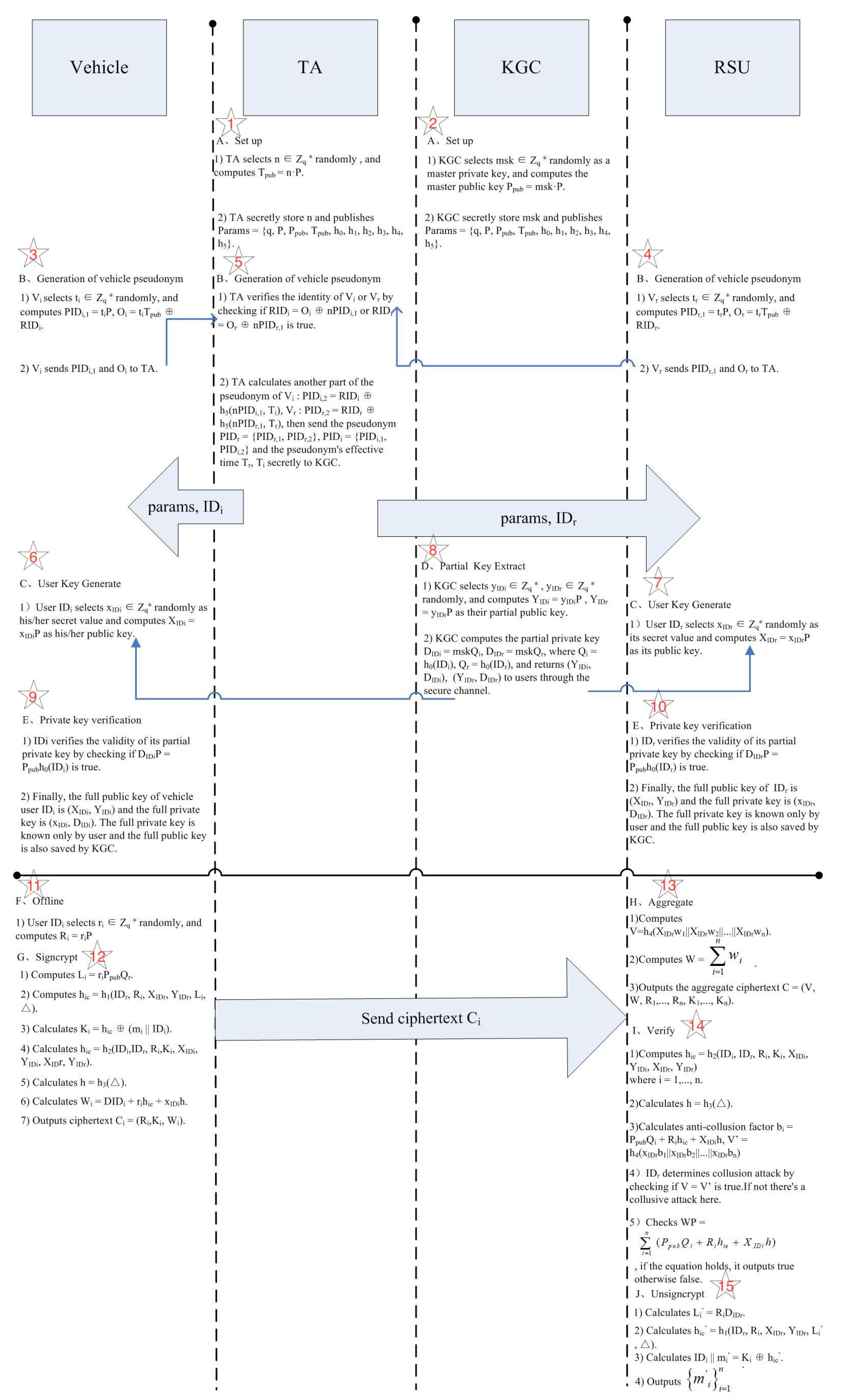
4. Proposed Scheme
4.1. Set Up
- A q-order additive group G on the elliptic curve is chosen, where q is a 160-bit prime number, and its generator is a 512-bit prime number P;
- KGC selects stochastically from as a master private key, and then the master public key is computed as ;
- The TA selects n ∈ randomly, and computes ;
- Six cryptographic hash functions are chosen: , : (n represents the bit-length of plaintexts), : , : , : , and : ;
- The KGC and the TA each secretly store and n and publish ..
4.2. Generation of Vehicle Pseudonym
- selects ∈ randomly, and computes = , = ;
- sends and to the TA, and the TA verifies the identity of by checking if = is true;
- The TA calculates another part of the pseudonym of : , and then sends the pseudonym and the pseudonym’s effective time secretly to KGC.
| Algorithm 1 Generation of vehicle pseudonym by the TA |
| Input: |
| Output: |
| 1. Computes , |
| 2. Calculates |
| 3. Sends to KGC |
4.3. The User Key Generation
4.4. Partial Key Extraction
- KGC selects ∈ stochastically, and computes as his or her partial public key;
- The partial private key is computed by KGC , where , and returns to the user through the secure channel.
4.5. Private Key Verification
- By checking if is true, the user can verify the validity of its partial private key;
- Lastly, the whole public key of vehicle user is and the whole private key is .
4.6. Offline
4.7. Signcrypt
- The user figures out ;
- The user figures out ;
- The user figures out part of the ciphertext ;
- The user calculates another hash function ;
- Then calculates ;
- The user calculates another part of the ciphertext ;
- Finally, the user obtains ciphertext .
4.8. Aggregate
- The RSU computes , which is used to verify whether there is a collusive attack;
- The RSU computes to aggregate;
- Lastly, the RSU acquires the aggregate ciphertext .
| Algorithm 2 Aggregation by fog device RSU |
| Input: , |
| Output: C |
| 1. Computes |
| 2. Computes |
| 3. Acquires the aggregate ciphertext |
4.9. Verification
- To begin with, the receiver computes where ;
- Secondly, it calculates ;
- Then, in the most crucial step, the receiver calculates the anti-collusion factor , ;
- The receiver determines the collusion attack by checking if is true. If not, there is a collusive attack here;
- In the end, the receiver checks , and if the equation holds, validation is successful.
4.10. Unsigncryption
- First, the receiver computes ;
- Second, using the given parameters, it calculates ;
- Then, the receiver can obtain ;
- Finally, it obtains .
| Algorithm 3 Unsigncryption by recipient |
| Input: C |
| Output: |
| 1. Computes |
| 2. Computes |
| 3. Obtains |
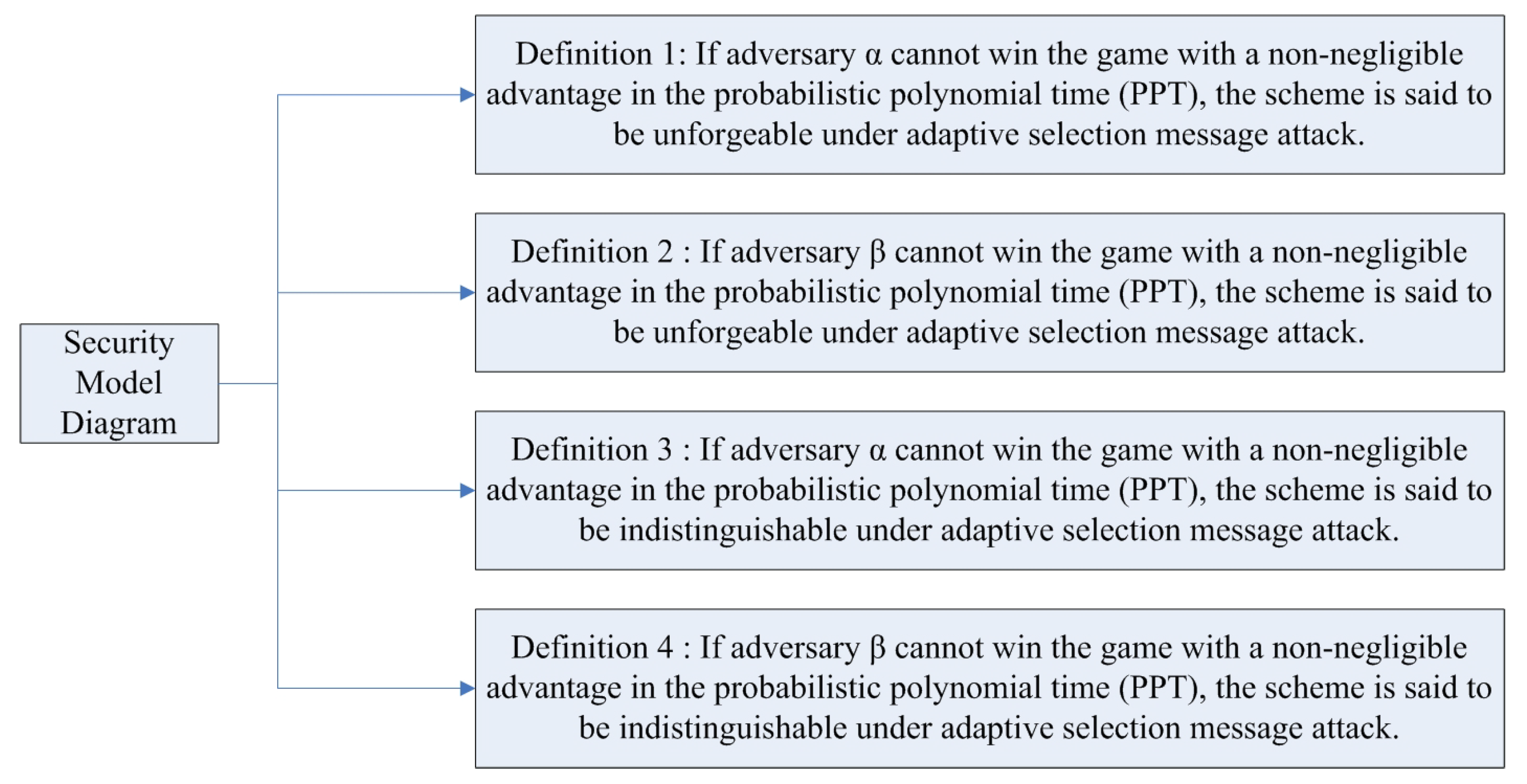
5. Security Analysis
5.1. Security Model
5.2. Provable Security
- Correctness: First, we prove the proposed scheme to be correct.
- a.
- User authentication;
- b.
- Private key verification;
- c.
- Verification of the existence of anti collusion attacks;
- d.
- Unsigncrypt verification.
- Resisting collusion attacks: Second, we demonstrate that our scheme can resist collusion attacks.
5.3. Analysis of Security Requirements
- Mutual authentication: Participants can identify each other by checking if the message they receive is activating;
- Vehicle identity verification: The decrypted plaintext package contains the user’s pseudonym. At this time, the TA can trace the user’s true identity back to the user’s real identity through the pseudonym, its own private key, and timestamp to complete user identity verification, and this operation can only be performed by the TA;
- User anonymity: Due to the use of pseudonyms throughout the entire process and the fact that the user’s true identity can only be acquired by trusted institutions, the anonymity of the user’s identity is ensured;
- Untraceability: The user chooses the stochastic number , calculates and , and then computes to acquire ciphertext . Hence, the attackers cannot follow the trail of vehicle users. At the same time, due to the use of pseudonyms throughout the entire process, attackers will not track information related to the user’s identity;
- Nondeniability: The received message contains the identity of the sender and of the receiver, and the identity of the sender is also included in the decryption result, so the vehicle user cannot deny participation.
- Resist collusion attacks: Because of the collision resistance of the hash function, collusion attacks can be detected by utilizing the anti-collusion factor.
6. Performance Analysis
6.1. Functionality
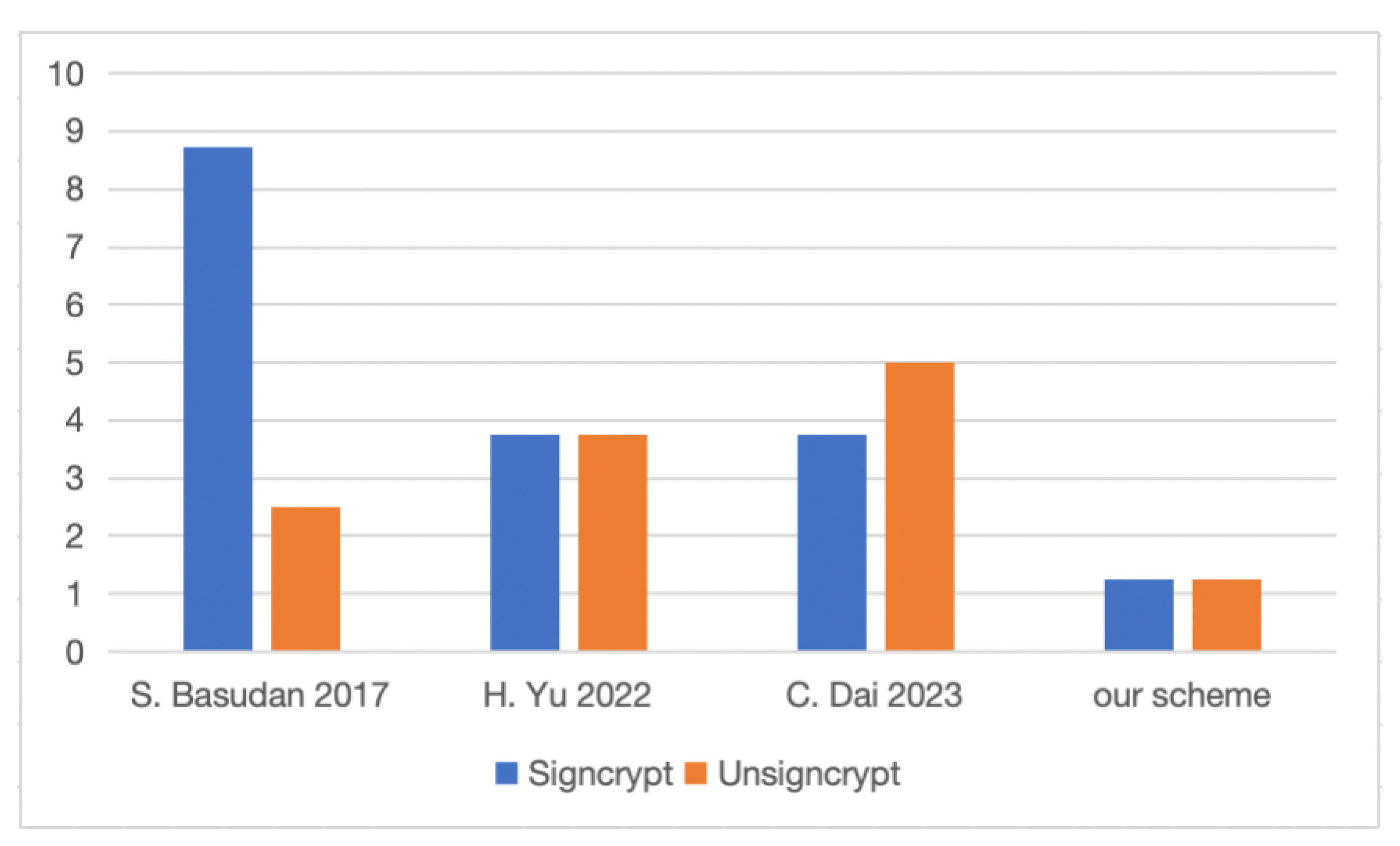
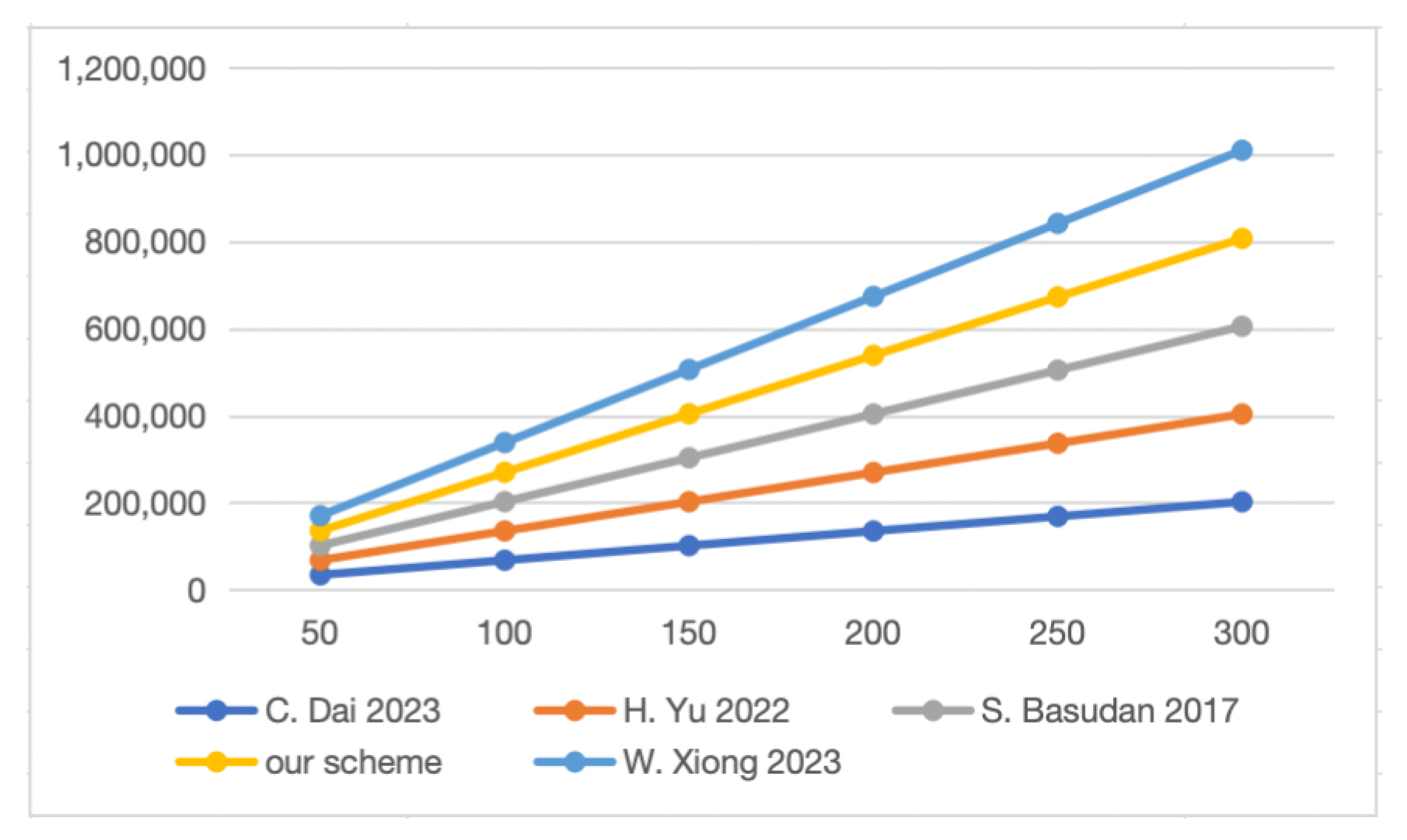
6.2. Computational Cost
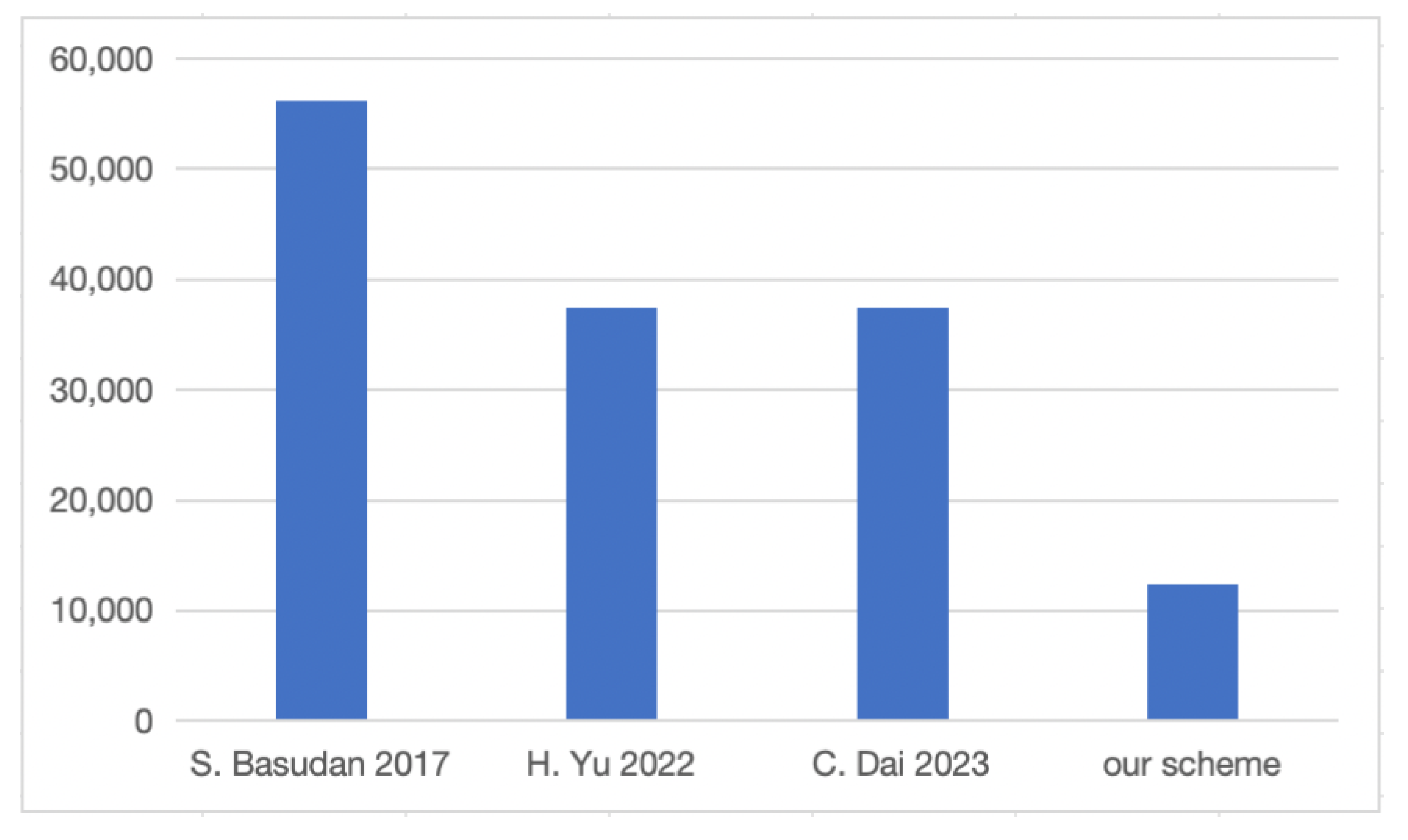
6.3. Communication Cost
7. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Ros, F.J.; Martinez, J.A.; Ruiz, P.M. A survey on modeling and simulation of vehicular networks: Communications mobility and tools. Comput. Commun. 2014, 43, 1–15. [Google Scholar] [CrossRef]
- Satyanarayanan, M.; Bahl, P.; Caceres, R.; Davies, N. The Case for VM-based Cloudlets in Mobile Computing. IEEE Pervasive Comput. 2011, 8, 14–23. [Google Scholar] [CrossRef]
- Bessis, N.; Dobre, C. Big Data and Internet of Things: A Roadmap for Smart Environments; Springer: Cham, Switzerland, 2014. [Google Scholar]
- Hu, P.; Ning, H.; Qiu, T.; Song, H.; Wang, Y.; Yao, X. Security and privacy preservation scheme of face identification and resolution framework using fog computing in Internet of Things. IEEE Internet Things J. 2017, 4, 1143–1155. [Google Scholar] [CrossRef]
- Xie, Z.; Chen, Y.; Ali, I.; Pan, C.; Li, F.; He, W. Efficient and Secure Certificateless Signcryption without Pairing for Edge Computing-Based Internet of Vehicles. IEEE Trans. Veh. Technol. 2023, 72, 5642–5653. [Google Scholar] [CrossRef]
- Li, L.; Li, Y.; Hou, R. A novel mobile edge computing-based architecture for future cellular vehicular networks. In Proceedings of the 2017 IEEE Wireless Communications and Networking Conference (WCNC), San Francisco, CA, USA, 19–22 March 2017; pp. 1–6. [Google Scholar]
- Wang, G.; Wang, J.; Guo, Z. Online/offline self-updating encryption. IEICE Trans. Fundam. Electron. Commun. Comput. Sci. 2016, 99, 2517–2526. [Google Scholar] [CrossRef]
- Yuan, Y. Security Analysis of an Enhanced Certificateless Signcryption in the Standard Model. Wirel. Pers. Commun. 2020, 112, 1. [Google Scholar] [CrossRef]
- Al-Riyami, S.; Paterson, K. Certificateless public key cryptography. Proc. Asiacrypt. 2003, 2894, 452–473. [Google Scholar]
- Eslami, Z.; Pakniat, N. Certificateless aggregate signcryption: Security model and a concrete construction secure in the random oracle model. J. Comput. Inf. Sci. 2014, 26, 276–286. [Google Scholar] [CrossRef]
- Zhang, L.; Hu, C.; Wu, Q.; Domingo-Ferrer, J.; Qin, B. Privacy-Preserving Vehicular Communication Authentication with Hierarchical Aggregation and Fast Response. IEEE Trans. Comput. 2016, 65, 2562–2574. [Google Scholar] [CrossRef]
- Sun, D.; Mu, Y.; Susilo, W. A Generic Construction of Identity-Based Online/Offline Signcryption. In Proceedings of the 2008 IEEE International Symposium on Parallel and Distributed Processing with Applications, Sydney, NSW, Australia, 10–12 December 2008; pp. 707–712. [Google Scholar]
- Sabireen, H.; Neelanarayanan, V. A Review on Fog Computing: Architecture, Fog with IoT, Algorithms and Research Challenges. ICT Express 2021, 7, 2. [Google Scholar] [CrossRef]
- Dastjerdi, A.V.; Gupta, H.; Calheiros, R.N.; Ghosh, S.K.; Buyya, R. Fog Computing: Principles Architectures and Applications; Morgan Kaufmann: Burlington, MA, USA, 2016; pp. 61–75. [Google Scholar]
- Erskine, S.K.; Elleithy, K.M. Secure Intelligent Vehicular Network Using Fog Computing. Electronics 2019, 8, 455. [Google Scholar] [CrossRef]
- Nayak, P.; Swapna, G. Security issues in IoT applications using certificateless aggregate signcryption schemes: An overview. IEEE Internet Things J. 2023, 21, 100641. [Google Scholar] [CrossRef]
- Lu, H.; Xie, Q. An efficient certificateless aggregate signcryption scheme from pairings. In Proceedings of the 2011 International Conference on Electronics, Communications and Control (ICECC), Ningbo, China, 9 September 2011; pp. 132–135. [Google Scholar]
- Kim, T.H.; Kumar, G.; Saha, R.; Alazab, M.; Buchanan, W.J.; Rai, M.K.; Geetha, G.; Thomas, R. CASCF: Certificateless Aggregated SignCryption Framework for Internet-of-Things Infrastructure. IEEE Access 2020, 8, 94748–94756. [Google Scholar] [CrossRef]
- Dai, C.; Xu, Z. Pairing-Free Certificateless Aggregate Signcryption Scheme for Vehicular Sensor Networks. IEEE Internet Things J. 2023, 10, 5063–5072. [Google Scholar] [CrossRef]
- Hou, Y.; Cao, Y.; Xiong, H.; Song, Y.; Xu, L. An Efficient Online/Offline Heterogeneous Signcryption Scheme with Equality Test for IoVs. IEEE Trans. Veh. Technol. 2023, 72, 12047–12062. [Google Scholar] [CrossRef]
- Lai, J.; Mu, Y.; Guo, F. Efficient identity-based online/offline encryption and signcryption with short ciphertext. Int. J. Inf. Security 2017, 16, 299–311. [Google Scholar] [CrossRef]
- An, H.; He, D.; Peng, C.; Luo, M.; Wang, L. Efficient Certificateless Online/Offline Signcryption Scheme without Bilinear Pairing for Smart Home Consumer Electronics. IEEE Trans. Consum. Electron. 2023, 1. [Google Scholar] [CrossRef]
- Cui, M.; Han, D.; Wang, J. An Efficient and Safe Road Condition Monitoring Authentication Scheme Based on Fog Computing. IEEE Internet Things J. 2019, 6, 9076–9084. [Google Scholar] [CrossRef]
- Pan, S.; Wang, S. Certificateless aggregate signcryption scheme against forgery attacks for vehicular ad hoc networks. J. Xidian Univ. 2023, 50, 169–177. [Google Scholar]
- Alice, G.S.; Maria, S.S.; Arunita, J. Blockchain-Based Pseudonym Management Scheme for Vehicular Communication. Electronics 2021, 10, 13. [Google Scholar]
- Wang, D.; Cheng, H.; Wang, P.; Huang, X.; Jian, G. Zipf’s law in passwords. IEEE Trans. Inf. Forensics Secur. 2017, 12, 2776–2791. [Google Scholar] [CrossRef]
- Shabani, F.; Gharaee, H.; Ghaffari, F. An intelligent RFIDenabled authentication protocol in VANET. In Proceedings of the 2018 9th International Symposium on Telecommunications (IST), Tehran, Iran, 17–19 December 2018; pp. 587–591. [Google Scholar]
- Basudan, S.; Lin, X.; Sankaranarayanan, K. A privacy-preserving vehicular crowdsensing-based road surface condition monitoring system using fog computing. IEEE Internet Things J. 2017, 4, 772–782. [Google Scholar] [CrossRef]
- Yu, H.; Ren, R. Certificateless Elliptic Curve Aggregate Signcryption Scheme. IEEE Syst. J. 2022, 16, 2347–2354. [Google Scholar] [CrossRef]
- Xiong, W.; Wang, R.; Wang, Y.; Wei, Y.; Zhou, F.; Luo, X. Improved Certificateless Aggregate Signature Scheme against Collusion Attacks for VANETs. IEEE Syst. J. 2023, 17, 1098–1109. [Google Scholar] [CrossRef]

| Symbol | Descritption |
|---|---|
| K | Security parameter |
| G | q–order additive group |
| P | Generator of G |
| System master private key | |
| System master public key | |
| Vehicle | |
| Authentic identity of | |
| Authentic identity of receiver | |
| Pseudonym of | |
| Pseudonym of receiver | |
| Full public key of | |
| Full private key of | |
| Full public key of receiver | |
| Full private key of receiver | |
| n | Number of signcrypted messages |
| Timestamp |
| Schemes | [28] | [23] | [29] | [30] | [19] | Our Scheme |
|---|---|---|---|---|---|---|
| Message Confidentiality | √ | √ | √ | × | √ | √ |
| Message Verifiability | √ | √ | √ | √ | √ | √ |
| Vehicle Verifiability | × | × | × | √ | √ | √ |
| Key Escrow Resilience | √ | √ | √ | √ | √ | √ |
| Quick Verification | √ | √ | √ | √ | √ | √ |
| Resist Collusion Attack | × | × | × | √ | × | √ |
| Hardware | CPU | Apple M1 |
| Hardware | Memory | 8 GB |
| Software | Operating System | macOS Big Sur 11.6 |
| Software | Program Language | C 17 and JAVA 1.8.0 |
| Software | Library | MIRACL 5.5.4 and JPBC 2.0.0 |
| Symbol | Computing Operation | Executing Time (ms) |
|---|---|---|
| Scalar multiplication in G | 1.248 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zhang, W.; Liu, S.; Liu, Y.; Cao, J.; Fu, B.; Du, Y. A Certificateless Online/Offline Aggregate Signcryption Scheme against Collusion Attacks Based on Fog Computing. Electronics 2023, 12, 4747. https://doi.org/10.3390/electronics12234747
Zhang W, Liu S, Liu Y, Cao J, Fu B, Du Y. A Certificateless Online/Offline Aggregate Signcryption Scheme against Collusion Attacks Based on Fog Computing. Electronics. 2023; 12(23):4747. https://doi.org/10.3390/electronics12234747
Chicago/Turabian StyleZhang, Wanju, Shuanggen Liu, Yaowei Liu, Junjie Cao, Bingqi Fu, and Yun Du. 2023. "A Certificateless Online/Offline Aggregate Signcryption Scheme against Collusion Attacks Based on Fog Computing" Electronics 12, no. 23: 4747. https://doi.org/10.3390/electronics12234747
APA StyleZhang, W., Liu, S., Liu, Y., Cao, J., Fu, B., & Du, Y. (2023). A Certificateless Online/Offline Aggregate Signcryption Scheme against Collusion Attacks Based on Fog Computing. Electronics, 12(23), 4747. https://doi.org/10.3390/electronics12234747