Real-Time Detection and Recovery Method Against Ransomware Based on Simple Format Analysis
Abstract
1. Introduction
- Real-time Ransomware Recovery: The method developed in this study introduces a novel approach that enables the immediate recovery of compromised files, even after a ransomware attack has completed its encryption process. Although conventional ransomware defense strategies emphasize periodic backups of critical files, RFRD provides an innovative solution that eliminates the need for scheduled backups by enabling real-time recovery.
- Preemptive Detection of Ransomware Damage: This study focuses on the preemptive detection of secondary ransomware behaviors, such as file encryption or deletion. The proposed SFA technique outperformed conventional detection methods by 25.4–31.4% in comparative experiments, demonstrating its superior detection performance.
- Response to Emerging Ransomware: Traditional antivirus software struggles to provide immediate protection against newly emerging ransomware. In contrast, the RFRD method holds significant value as it enables the real-time restoration of critical documents even before antivirus definitions are updated, thus offering proactive protection against novel threats.
2. Related Studies
2.1. Ransomware Detection
2.2. Detection of Ransomware Tampering
2.3. Ransomware Damage Recovery
2.4. Distinctions of Our Study
- Ransomware Detection Approach: Conventional detection mechanisms rely on post-discovery updates of signatures or behavioral rules, which are insufficient for preventing file modifications caused by newly emerging ransomware variants. Similarly, decoy-based methods cannot protect files until the decoy is activated by the ransomware. In contrast, the RFRD method shifts focus from traditional detection to real-time recovery of compromised files, employing the SFA technique to mitigate the damage as it occurs.
- File Modification Detection: Traditional entropy-based approaches apply statistical models and achieve a detection rate of 72.2% [6]. The RENTAKA framework uses ML to analyze API behavior with an accuracy of 97.5%. FFRecovery and CARDR rely on ML models that analyze SSD cache data. The proposed SFA technique is a real-time detection method based on file structure analysis. In extensive evaluation tests, it demonstrated an accuracy range of 95.0% to 97.9%, depending on file type, encryption method, and detection mode.
- Ransomware Recovery Method: Pre-backup techniques cannot recover data lost before the next scheduled backup. ML-based restoration methods, such as Jadon’s, do not fully ensure data integrity. FFRecovery and CARDR depend on the assumption that SSD cache content remains intact. In contrast, the proposed RFRD method incorporates an integrated SFA detection engine, meaning its recovery performance is closely linked to the accuracy of the SFA algorithm. Experimental results demonstrated that, based on the high detection rate of SFA, the RFRD method achieved high recovery accuracy as well.
3. Background
3.1. Ransomware
3.2. Windows Kernel I/O Monitoring
4. Materials and Methods
4.1. Dataset
4.2. Ransomware Distribution Analysis
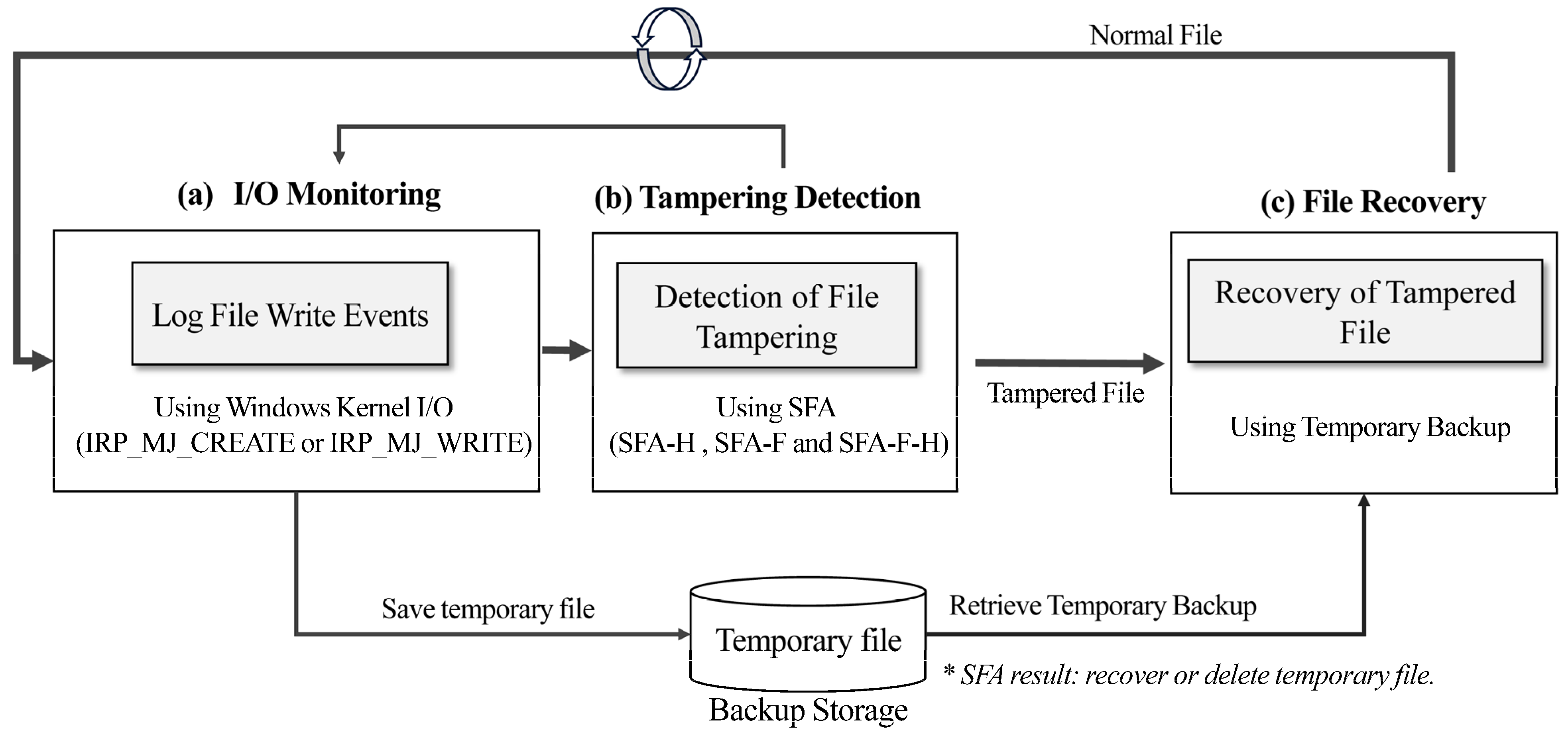
4.3. Real-Time File Restoration from Damage (RFRD) Method
4.3.1. I/O Monitoring
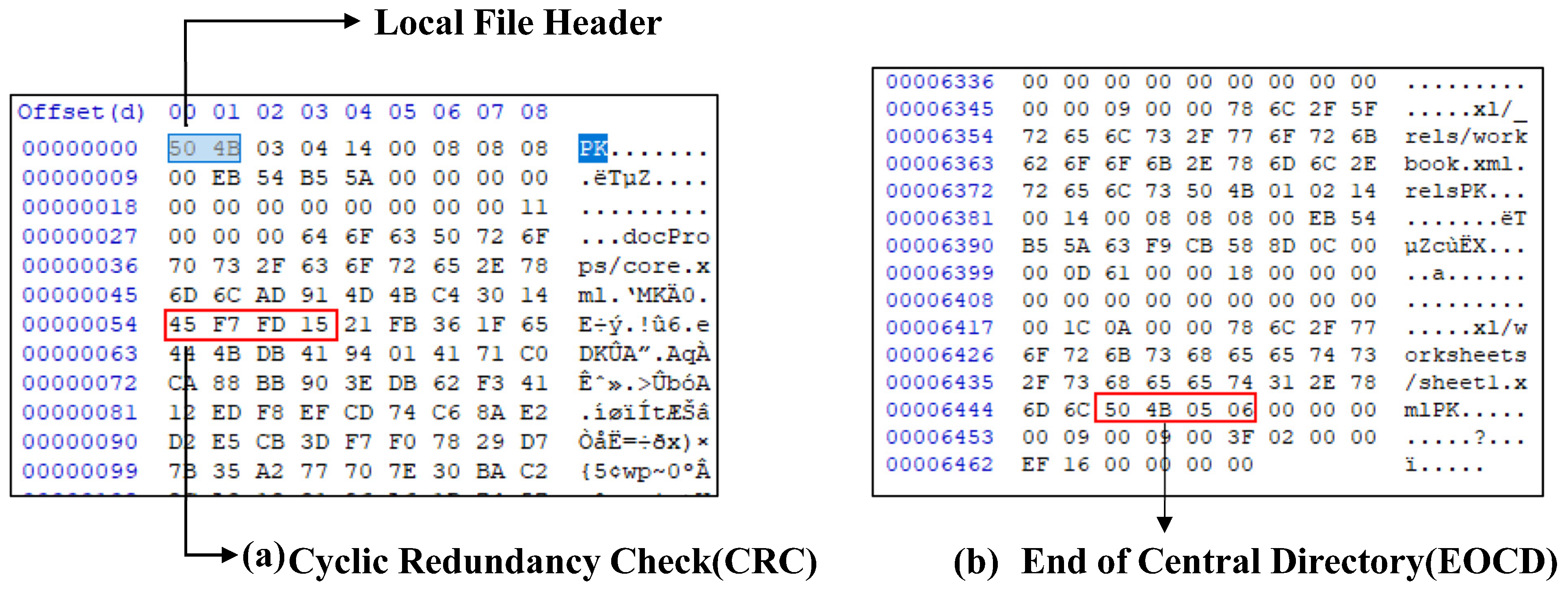
4.3.2. Detection of File Tampering
- This confirms the presence of the three predefined signature offsets. If any are missing, the file is classified as compromised.
- The reader scans the last 64 KB of the file for the end of central directory (EOCD) signature (0x06054B50) to locate the EOCD. It then reads the 4-byte offset field at bytes 16–19 of the EOCD, which points to the start of the central directory. If the data at that offset do not begin with the central directory entry signature (0x02014B50), the file may be flagged as having been tampered with.
| Header Format | Size (Bytes) | Signature Offset | Description |
|---|---|---|---|
| Local file header | 2 | 0x04034b50 (50 4B 03 04) | Basic file information |
| Central directory (CD) | 4 | 0x02014B50 (50 4B 01 02) | Metadata structure of the file |
| EOCD | 4 | 0x06054B50 (50 4B 05 06) | Pointer to the central directory start |
4.3.3. Recovery of Tampered File
5. Performance Evaluation
5.1. Performance Evaluation of Ransomware Detection Using Field-Collected Real-World Data
5.1.1. Hardware and Software Environment
5.1.2. Test Dataset
5.1.3. Evaluation Results
Comparison of Detection Performance: SFA-H vs. SFA-F
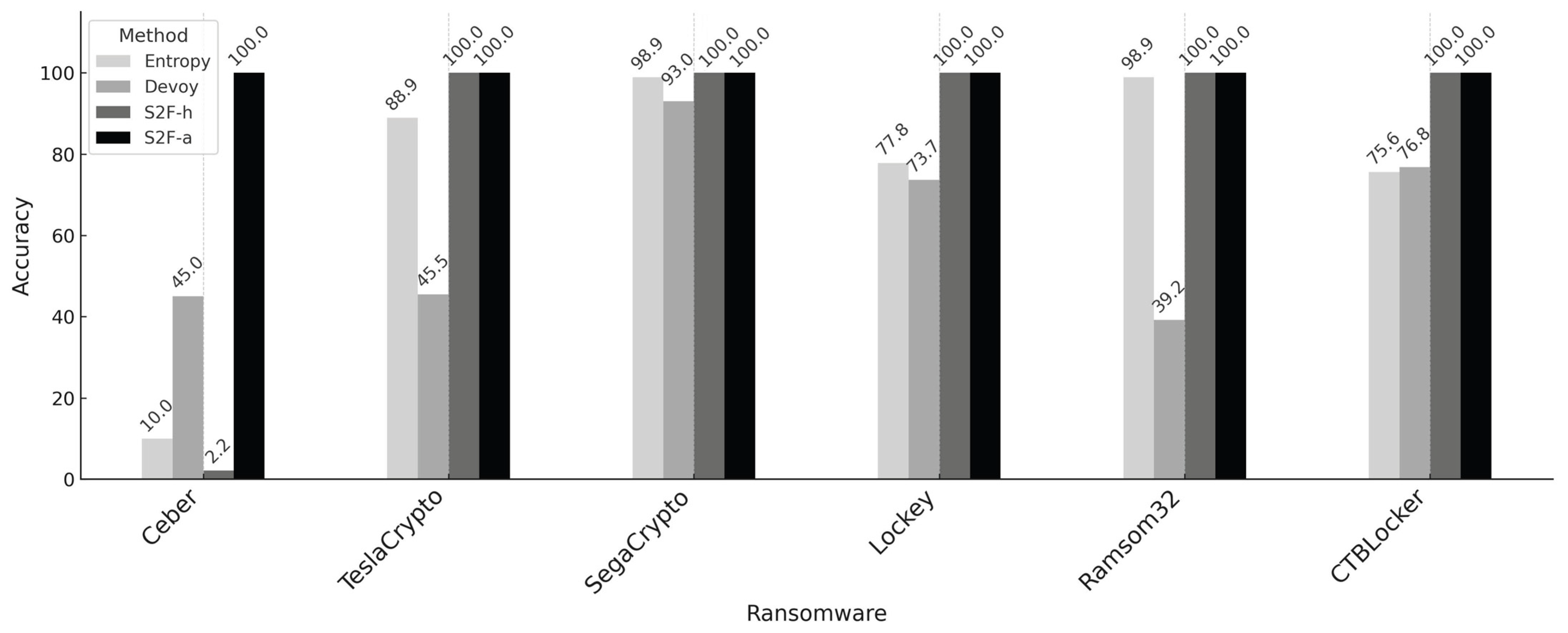
Comparison with Other Methods
5.2. In-Depth Analysis of Detection Scalability and Model Performance Using Publicly Available Ransomware Samples
5.2.1. Hardware and Software Environment
5.2.2. Extended Test Dataset
5.2.3. Experimental Method
“Please analyze the file I will now provide using various methods, and summarize the results in CSV format, including the file name, file size, upload time, entropy, encryption status, and analysis time.”
- True Positive (TP): The model correctly predicts a sample as positive when it is positive.
- True Negative (TN): The model correctly predicts a sample as negative when it is negative.
- False Positive (FP): The model incorrectly predicts a sample as positive when it is negative.
- False Negative (FN): The model incorrectly predicts a sample as negative when it is positive.
5.2.4. Extended Evaluation Results
Comparative Evaluation of Ransomware Detection Methods Using Structured File Formats
Performance Evaluation of SFA-F Hybrid Detection Methods for Unsupported File Extensions
- SFA-F-H: A hybrid method combining SFA-F and SFA-H.
- Simple Format Analysis—Fixed-structure and Entropy-based (SFA-F-Entropy): A static feature-based method that calculates entropy values (with a threshold of 7.5, as shown to be effective in Table 10).
- Simple Format Analysis—Fixed-structure and GPT (SFA-F-ChatGPT): A semantic analysis approach that leverages a large language model (LLM) to interpret content patterns within the file.
Performance Comparison of Detection Models in Terms of Processing Speed and Resource Utilization
6. Discussion and Limitation
7. Conclusions
Funding
Data Availability Statement
Conflicts of Interest
Correction Statement
Appendix A
Appendix A.1. Windows Kernel I/O Event Hooking Using IRP
| Algorithm A1: Windows Kernel I/O Processing Using IRP |
NTSTATUS DriverDispatch( PDEVICE_OBJECT DeviceObject, PIRP Irp ) { PIO_STACK_LOCATION irpSp = IoGetCurrentIrpStackLocation(Irp); NTSTATUS status = STATUS_SUCCESS; switch (irpSp->MajorFunction) { case IRP_MJ_CREATE: // Backup the file or log its access path BackupFileIfNeeded(irpSp->FileObject->FileName); break; case IRP_MJ_WRITE: // Create a temporary backup before modifying the file SaveTemporaryCopy(irpSp->FileObject); break; default: break; } Irp->IoStatus.Status = status; Irp->IoStatus.Information = 0; IoCompleteRequest(Irp, IO_NO_INCREMENT); return status; } |
Appendix A.2. Format-Based Structural Validation Using EOCD and CD Entry
| Algorithm A2: Format-Based Structural Validation for Encrypted File Detection (SFA-F) |
| #define DEF_EOCD_SIG “\x50\x4B\x05\x06” // EOCD signature: PK\x05\x06 #define DEF_CD_SIG “\x50\x4B\x01\x02” // Central Directory signature: PK\x01\x02 #define DEF_EOCD_SIZE 22 #define DEF_MAX_SCAN_SIZE 65557 // 64KB + EOCD_SIZE int SFA_Format(const char *ppath) { FILE *fp = fopen(ppath, “rb”); if (!fp) { printf(“Cannot open file.\n”); return −1; } // (1) Get total file size fseek(fp, 0, SEEK_END); long n_file_size = ftell(fp); // (2) Limit the scanning size to the last 64KB long n_skn_size = (n_file_size < DEF_MAX_SCAN_SIZE) ? n_file_size: MAX_SCAN_SIZE; fseek(fp, −n_skn_size, SEEK_END); // (3) Read the last scan size bytes unsigned char *szbuffer = (unsigned char *)malloc(n_skn_size); if (!szbuffer) { printf(“Memory allocation failed.\n”); fclose(fp); return −1; } fread(szbuffer, 1, n_skn_size, fp); // (4) Search EOCD signature (0x06054B50) from the end long n_eocd_index = −1; for (long i = n_skn_size − EDF_EOCD_SIZE; i >= 0; i--) { if (memcmp(szbuffer + i, DEF_EOCD_SIG, 4) == 0) { n_eocd_index = i; break; } } if (n_eocd_index == −1) { free(szbuffer); fclose(fp); return −1; } // (5) Read Central Directory offset from EOCD (bytes 16–19, little-endian) unsigned char *p_eocd = szbuffer + n_eocd_index; long cd_offset = p_eocd [16] | (p_eocd [17] << 8) | (p_eocd [18] << 16) | (p_eocd [19] << 24); // (6) Move to Central Directory offset and verify its signature fseek(fp, cd_offset, SEEK_SET); unsigned char lst_cd_sig[4]; fread(lst_cd_sig, 1, 4, fp); if (memcmp(lst_cd_sig, DEF_CD_SIG, 4) ! = 0) { // (5–1) It is tampered status printf(“Central Directory signature mismatch at offset %ld. File may be tampered.\n”, cd_offset); } else { // (5–1) It is Normal status printf(“EOCD and Central Directory are valid. CD starts at offset %ld.\n”, cd_offset); } free(szbuffer); fclose(fp); return 0; } |
Appendix A.3. Structural Validation of JPEG Files Based on SOI/EOI Signatures
| Algorithm A3: Structural Validation of JPEG Files Based on SOI/EOI Signatures |
| typedef unsigned char BYTE; int check_jpg_header(const char* path) { FILE* fp = fopen(path, “rb”); if (!fp) { perror(“Failed to open file”); return −1; } BYTE head[4] = {0}; fread(head, 1, 4, fp); // Check Start of Image (SOI) marker and APPn segment range // JPEG must begin with: 0xFF 0xD8 0xFF 0xE0~0xEF if (!(head[0] == 0xFF && head[1] == 0xD8 && head[2] == 0xFF && (head[3] & 0xF0) == 0xE0)) { fclose(fp); return −1; // Not a valid JPEG SOI + APPn segment } // Seek to last 2 bytes to verify End of Image (EOI) marker // JPEG must end with: 0xFF 0xD9 fseek(fp, −2, SEEK_END); BYTE tail[2] = { 0 }; fread(tail, 1, 2, fp); fclose(fp); if (tail[0] == 0xFF && tail[1] == 0xD9) return 0; // Valid JPEG file else return −1; // Invalid or missing EOI marker } |
Appendix A.4. Structural Validation of PDF Files
| Algorithm A4: Structural Validation of PDF Files |
| int check_pdf_file (const char* path) { float version = get_pdf_version(path); if (version < 0.0f) { printf("PDF header not found\n"); return 1; } FILE* fp = fopen(path, "rb"); if (!fp) return −1; fseek(fp, 0, SEEK_END); long filesize = ftell(fp); long seek_pos = (filesize > MAX_TAIL_SIZE) ? filesize - MAX_TAIL_SIZE : 0; fseek(fp, seek_pos, SEEK_SET); unsigned char* tail = (unsigned char*)mal loc(MAX_TAIL_SIZE); if (!tail) { fclose(fp); return −1; } size_t read = fread(tail, 1, MAX_TAIL_SIZE, fp); fclose(fp); int has_eof = mem_contains(tail, read, "%%EOF"); int has_startxref = mem_contains(tail, read, "startxref"); int result = 1; if (has_eof && has_startxref) result = 0; free(tail); return result; } |
References
- Cyberint. Ransomware Annual Report 2024. Available online: https://cyberint.com/blog/research/ransomware-annual-report-2024/ (accessed on 11 June 2025).
- Sophos. The State of Ransomware 2024; Sophos Ltd.: Oxford, UK, 2024; Available online: https://www.sophos.com/en-us/content/state-of-ransomware (accessed on 7 June 2025).
- Aung, Y.L.; Khoo, Y.L.; Zheng, D.Y.; Swee Duo, B.; Chattopadhyay, S.; Zhou, J.; Lu, L.; Goh, W. HoneyWin: High-Interaction Windows Honeypot in Enterprise Environment. arXiv 2025. [Google Scholar] [CrossRef]
- AV-TEST Institute. Every Day, the AV-TEST Institute Registers over 450,000 New Malicious Programs (Malware) and Potentially Unwanted Applications (PUA). Available online: https://www.av-test.org/en/statistics/malware/ (accessed on 11 June 2025).
- Bowen, B.M.; Hershkop, S.; Keromytis, A.D.; Stolfo, S.J. Baiting Inside Attackers Using Decoy Documents. In Security and Privacy in Communication Networks: Revised Selected Papers; Chen, Y., Dimitriou, T.D., Zhou, J., Eds.; Lecture Notes in Computer Sciences; Springer: Berlin/Heidelberg, Germany, 2009; Volume 19, pp. 51–70. [Google Scholar] [CrossRef]
- Kharraz, A.; Arshad, S.; Mulliner, C.; Robertson, W.; Kirda, E.A. Large-Scale, Automated Approach to Detecting Ransomware. In Proceedings of the 25th USENIX Security Symposium, Austin, TX, USA, 10–12 August 2016; pp. 757–772. Available online: https://www.usenix.org/conference/usenixsecurity16/technical-sessions/presentation/kharaz (accessed on 31 July 2025).
- Zakaria, W.Z.A.; Abdollah, M.F.; Mohd, O.; Yassin, S.M.W.M.; Ariffin, A. RENTAKA: A Novel Machine Learning Framework for Crypto-Ransomware Pre-Encryption Detection. Int. J. Adv. Comput. Sci. Appl. 2022, 13, 378–385. [Google Scholar] [CrossRef]
- Mehra, T. The Role of Encryption in Securing Backup Data Against Ransomware Threats. Int. J. Sci. Res. Arch. 2024, 13, 1971–1974. [Google Scholar] [CrossRef]
- Dafoe, J.; Chen, N.; Chen, B.; Wang, Z. Enabling Per-File Data Recovery from Ransomware Attacks via File System Forensics and Flash Translation Layer Data Extraction. Cybersecurity 2024, 7, 75. [Google Scholar] [CrossRef]
- Gayathri, G.; Arivoli, R.S. A Comprehensive Behavioural Study of Ransomware and Its Impact. In Proceedings of the International Conference on Innovative Computing & Communication (ICICC 2024), New Delhi, India, 16–17 February 2024; Available online: https://ssrn.com/abstract=5022928 (accessed on 11 June 2025).
- Thomas, M.C.; Joy, A.T. Elements of Information Theory; Wiley Interscience: Hoboken, NJ, USA, 2006. [Google Scholar]
- Hassan, M.W.; Goel, N.; Kalyan, T.V. CARDR: DRAM Cache Assisted Ransomware Detection and Recovery in SSDs. In Proceedings of the ACM International Symposium on Memory Systems (MEMSYS 2024), Washington, DC, USA, 30 September–3 October 2024. [Google Scholar] [CrossRef]
- Jadon, R.; Srinivasan, K.; Chauhan, G.S.; Budda, R.; Gollapalli, V.S.T.; Prema, R. Enhanced Ransomware Detection and Prevention Using CNN-BiLSTM for Deep Behavioural Analysis. Int. J. Recent Adv. Multidiscip. Res. 2025, 12, 10900–10904. Available online: https://ijramr.com/issue/enhanced-ransomware-detection-and-prevention-using-cnn-bilstm-deep-behavioural-analysis (accessed on 31 July 2025).
- Higuchi, K.; Kobayashi, R. ROFBSα: Real-Time Backup System Decoupled from ML-Based Ransomware Detection. arXiv 2025. [Google Scholar] [CrossRef]
- Microsoft Docs. IRP Major Function Codes. Available online: https://learn.microsoft.com/en-us/windows-hardware/drivers/kernel/irp-major-function-codes (accessed on 8 June 2025).
- ytisf. theZoo: A Live Repository of Malware Samples. Available online: https://github.com/ytisf/theZoo (accessed on 28 July 2025).
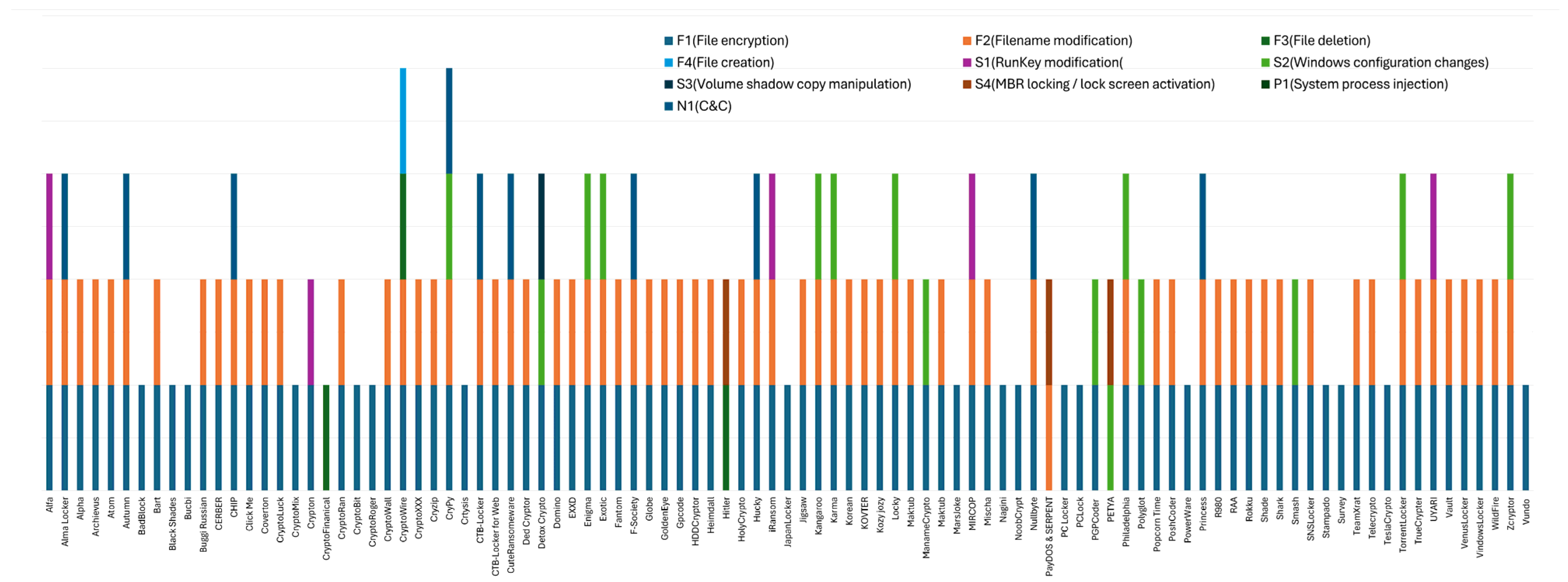
| Category | Behavior ID | Behavior Type | Distribution (%) |
|---|---|---|---|
| File (F) | F1 | File encryption | * 95.88 |
| F2 | Filename modification | 72.61 | |
| F3 | File deletion | 3.09 | |
| F4 | File creation | 1.03 | |
| System (S) | S1 | RunKey modification | 5.15 |
| S2 | Windows configuration changes | 15.46 | |
| S3 | Volume shadow copy manipulation | 1.03 | |
| S4 | MBR locking/lock screen activation | 3.09 | |
| Process (P) | P1 | System process injection | 0.00 |
| Network (N) | N1 | Connection to command and control (C & C) server | 9.70 |
| Ransomware | Behavior ID | Behavior Type | Recovery Possibility | Description |
|---|---|---|---|---|
| CryptoFinancial | F3 | File deletion | Not recoverable | Deceives the user by deleting files and presenting them as encryption. |
| Hitler | F3 | File deletion | Not recoverable | Deceives the user by deleting files and presenting them as encryption. |
| PayDos and SERPENT | F2 | Filename modification | Recoverable | Changes only one character in the file extension |
| Petya | S2 | Windows configuration changes | Data can be recovered | Encrypts the master boot record (MBR) boot sector |
| Ransomware | Behavior Description |
|---|---|
| Cerber | Changes file extensions to .hta or random strings during encryption. Skips 512 or 640 bytes at the beginning before encrypting. |
| TeselaCrypto | Distributed via vulnerable web pages and email attachments. Changes extensions to .ecc and .micr. |
| SegaCrypto | Delivered through emails or Word documents. Encrypts files and appends the .sega extension. |
| Locky | Renames files with the .locky extension and encrypts using RSA-2014 or AES-128. |
| Ransom32 | JavaScript-based ransomware with obfuscation techniques. |
| Name | Directory Path | Number of Files |
|---|---|---|
| Data 1 | C:\\ | 90 |
| Data 2 | C:\\library\doc | 90 |
| Data 3 | C:\\library\photo | 90 |
| Data 4 | C:\\Users | 90 |
| Sum | 4 Directory | 360 |
| Ransomware | DOCX | PPTX | XLSX | Average |
|---|---|---|---|---|
| Cerber | 3.3 | 0.0 | 3.3 | 2.2 |
| TeselaCrypto | 100.0 | 100.0 | 100.0 | 100.0 |
| SegaCrypto | 100.0 | 100.0 | 100.0 | 100.0 |
| Locky | 100.0 | 100.0 | 100.0 | 100.0 |
| Ransom32 | 100.0 | 100.0 | 100.0 | 100.0 |
| CTBLocker | 100.0 | 100.0 | 100.0 | 100.0 |
| Average | 83.9 | 83.3 | 83.9 | 83.7 |
| Ransomware | DOCX | PPTX | XLSX | Average |
|---|---|---|---|---|
| Cerber | 100.0 | 100.0 | 100.0 | 100.0 |
| TeselaCrypto | 100.0 | 100.0 | 100.0 | 100.0 |
| SegaCrypto | 100.0 | 100.0 | 100.0 | 100.0 |
| Locky | 100.0 | 100.0 | 100.0 | 100.0 |
| Ransom32 | 100.0 | 100.0 | 100.0 | 100.0 |
| CTBLocker | 100.0 | 100.0 | 100.0 | 100.0 |
| Average | 100.0 | 100.0 | 100.0 | 100.0 |
| Ransomware | Behavior Description |
|---|---|
| Cerber | Change file extensions to .hta or random strings during encryption. This ransomware sample was registered on the theZoo [16] repository in 2021. |
| Hive | Active since mid-2021, Hive employs a double extortion strategy and a Ransomware-as-a-Service (RaaS) model. It not only encrypts files but also exfiltrates data to pressure victims. |
| Thanos | Thanos is a customizable RaaS-based ransomware that began circulating on the dark web in early 2020. |
| XData | XData rapidly spread in Ukraine in May 2017. It is known for its fast propagation, primarily exploiting SMB vulnerabilities. |
| WannaCry | WannaCry is a notorious worm-type ransomware that spread globally in 2017 by exploiting a vulnerability in the SMB protocol. |
| File Type | Description |
|---|---|
| DOCX | Used in Section 5.1; includes an End of Central Directory (EOCD) structure. |
| PPTX | Used in Section 5.1; includes an End of Central Directory (EOCD) structure. |
| XLSX | Used in Section 5.1; includes an End of Central Directory (EOCD) structure. |
| Added in Section 5.2; the format analysis code is provided in Appendix A.4. | |
| HWPS | Added in Section 5.2; includes an EOCD structure. This is a word processing format widely used in South Korea. |
| ZIP | Added in Section 5.2; a compressed file format that includes an EOCD structure. |
| jpg | Added in Section 5.2; the format analysis code is provided in Appendix A.3. |
| Method | Ransomware | Precision | Recall | Accuracy | F1 Score | Avg. F1 Score |
|---|---|---|---|---|---|---|
| Entropy (5.5) | Cerber | 1.000 | 0.530 | 0.530 | 0.690 | 0.646 |
| Hive | 1.000 | 0.530 | 0.530 | 0.690 | ||
| Thanos | 0.600 | 0.400 | 0.320 | 0.480 | ||
| XData | 1.000 | 0.530 | 0.530 | 0.690 | ||
| WannaCry | 0.980 | 0.520 | 0.520 | 0.680 | ||
| Entropy (7.5) | Cerber | 1.000 | 0.530 | 0.560 | 0.690 | 0.680 |
| Hive | 0.980 | 0.520 | 0.550 | 0.680 | ||
| Thanos | 0.931 | 0.511 | 0.520 | 0.660 | ||
| XData | 0.990 | 0.530 | 0.550 | 0.690 | ||
| WannaCry | 0.980 | 0.520 | 0.550 | 0.680 | ||
| ChatGPT | Cerber | 0.920 | 0.630 | 0.700 | 0.750 | 0.706 |
| Hive | 0.980 | 0.650 | 0.730 | 0.780 | ||
| Thanos | 0.940 | 0.640 | 0.710 | 0.760 | ||
| XData | 0.820 | 0.610 | 0.650 | 0.700 | ||
| WannaCry | 0.560 | 0.510 | 0.520 | 0.540 | ||
| SFA-H | Cerber | 0.170 | 1.000 | 0.590 | 0.290 | 0.858 |
| Hive | 1.000 | 1.000 | 1.000 | 1.000 | ||
| Thanos | 1.000 | 1.000 | 1.000 | 1.000 | ||
| XData | 1.000 | 1.000 | 1.000 | 1.000 | ||
| WannaCry | 1.000 | 1.000 | 1.000 | 1.000 | ||
| SFA-F | Cerber | 1.000 | 1.000 | 1.000 | 1.000 | * 0.960 |
| Hive | 1.000 | 1.000 | 1.000 | 1.000 | ||
| Thanos | 0.700 | 1.000 | 0.850 | 0.820 | ||
| XData | 0.960 | 1.000 | 0.980 | 0.980 | ||
| WannaCry | 1.000 | 1.000 | 1.000 | 1.000 |
| Method | Ransomware | Accuracy | Precision | Recall | F1 Score | Avg. F1 Score |
|---|---|---|---|---|---|---|
| SFA-F-H | Cerber | 0.928 | 0.857 | 0.998 | 0.922 | * 0.979 |
| Hive | 0.999 | 1.000 | 0.998 | 0.999 | ||
| Thanos | 0.989 | 0.979 | 0.998 | 0.988 | ||
| XData | 0.989 | 0.979 | 0.998 | 0.988 | ||
| WannaCry | 0.999 | 1.000 | 0.998 | 0.999 | ||
| SFA-F-Entropy (7.5) | Cerber | 0.954 | 1.000 | 0.915 | 0.956 | 0.950 |
| Hive | 0.952 | 0.997 | 0.915 | 0.954 | ||
| Thanos | 0.940 | 0.973 | 0.913 | 0.942 | ||
| XData | 0.943 | 0.979 | 0.913 | 0.945 | ||
| WannaCry | 0.954 | 1.000 | 0.915 | 0.956 | ||
| SFA-F-ChatGPT | Cerber | 0.922 | 0.929 | 0.915 | 0.922 | 0.946 |
| Hive | 0.950 | 0.986 | 0.920 | 0.952 | ||
| Thanos | 0.957 | 1.000 | 0.921 | 0.959 | ||
| XData | 0.950 | 0.986 | 0.920 | 0.952 | ||
| WannaCry | 0.943 | 0.971 | 0.919 | 0.944 |
| Method | Ransomware | File Size (KB) | Processing Time (ms) | I/O Wait Time (ms) | Backup Time (ms) | CPU (%) |
|---|---|---|---|---|---|---|
| SFA-F | Cerber | 2324.8 | 2.9 | 0.5 | 23.3 | 1.8 |
| Hive | 2266.8 | 1.6 | 0.5 | 7.2 | 1.4 | |
| Thanos | 1795.5 | 2.5 | 0.1 | 7 | 1.3 | |
| XData | 2266.3 | 1.6 | 0.3 | 3.7 | 1.7 | |
| WannaCry | 2324.6 | 1.1 | 0.4 | 3.1 | 1.1 | |
| Average | 2195.6 | 1.94 | 0.36 | 8.86 | 1.46 | |
| SFA-H | Cerber | 2257.0 | 0.8 | 0.2 | 2.8 | 0.8 |
| Hive | 2332.0 | 1.6 | 0.4 | 5.0 | 0.7 | |
| Thanos | 1795.5 | 0.3 | 0.1 | 5.4 | 0.3 | |
| XData | 2266.3 | 1.5 | 0.4 | 5.5 | 0.4 | |
| WannaCry | 2324.6 | 0.9 | 0.2 | 5.7 | 0.6 | |
| Average | 2195.1 | 1.0 | 0.3 | 4.9 | 0.6 | |
| Entropy (7.5) | Cerber | 2324.8 | 5.3 | 0.4 | 3.4 | 7.8 |
| Hive | 2324.8 | 5.3 | 0.4 | 3.4 | 7.8 | |
| Thanos | 1795.5 | 1.4 | 0.0 | 0.3 | 5.8 | |
| XData | 2266.3 | 5.0 | 0.3 | 4.3 | 7.3 | |
| WannaCry | 2324.6 | 6.0 | 0.5 | 3.4 | 6.0 | |
| Average | 2207.2 | 4.6 | 0.3 | 2.9 | 2.9 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kim, J. Real-Time Detection and Recovery Method Against Ransomware Based on Simple Format Analysis. Information 2025, 16, 739. https://doi.org/10.3390/info16090739
Kim J. Real-Time Detection and Recovery Method Against Ransomware Based on Simple Format Analysis. Information. 2025; 16(9):739. https://doi.org/10.3390/info16090739
Chicago/Turabian StyleKim, JaeYeol. 2025. "Real-Time Detection and Recovery Method Against Ransomware Based on Simple Format Analysis" Information 16, no. 9: 739. https://doi.org/10.3390/info16090739
APA StyleKim, J. (2025). Real-Time Detection and Recovery Method Against Ransomware Based on Simple Format Analysis. Information, 16(9), 739. https://doi.org/10.3390/info16090739






