Abstract
Automated production lines are increasingly being expanded with Industrial Internet of Things (IIoT) devices, creating complex Cyber-Physical Systems (CPSs) that connect physical production with control and information infrastructure. However, the convergence of Information Technology (IT) and Operational Technology (OT) layers creates new entry points for attacks targeting communication availability. Most existing studies analyze Distributed Denial of Service (DDoS) attacks primarily in simulation or testbed environments, with limited experimental verification of their impact on real-world production systems. This article presents an experimental evaluation of the impact of DDoS and Distributed Reflection Denial of Service (DRDoS) attacks carried out directly on a physical automated production line with integrated IIoT infrastructure during real operation. Three attack scenarios (TCP SYN flood, TCP ACK flood, and ICMP reflected attack) were implemented, targeting Programmable Logic Controllers (PLCs), Radio-Frequency Identification (RFID) subsystems, and selected IIoT devices. The results showed rapid degradation of deterministic PROFINET communication, disruption of the link between the OT and IT layers, loss of digital product representation, and physical interruption of the production process. Based on the findings, a minimally invasive security solution based on perimeter protection was designed and experimentally verified. The results emphasize the need to design IIoT-based manufacturing systems with an emphasis on network segmentation and architectural separation of the IT and OT layers.
1. Introduction
Automated manufacturing systems in the Industry 4.0 concept are increasingly based on the integration of Industrial Internet of Things (IIoT) devices that connect the physical manufacturing process with the control and information infrastructure [1,2,3]. The convergence of Information Technology (IT) and Operational Technology (OT) enables advanced monitoring, remote access, and real-time data exchange, but it also fundamentally changes the security profile of industrial systems [4,5]. Thus, modern cyber-physical systems (CPSs) are exposed to network attacks that can threaten their availability and production continuity [6,7].
A particular risk is the possibility of IIoT devices being misused for attacks targeting availability, such as Denial of Service (DoS), Distributed Denial of Service (DDoS), or Distributed Reflection Denial of Service (DRDoS) [8,9,10]. IoT devices can represent a potential attack vector targeting the broader manufacturing environment given their architectural position between the IT and OT layers [11]. Their constant connectivity and often limited security mechanisms increase the risk of misuse as part of botnets or as a source of excessive network traffic directed at the control infrastructure [12,13]. In a CPS environment, such traffic can lead to the degradation of deterministic communication, disruption of control cycles, and physical shutdown of the manufacturing process in extreme cases.
Although the issue of DDoS attacks in IIoT and industrial networks is the subject of intensive research, most existing studies are conducted in simulation environments, laboratory testbeds, or with publicly available network traffic datasets. These approaches mainly focus on detecting or classifying attacks using analytical or machine learning methods [14].
However, experimental verification of the direct impact of an attack on a physically operated production system based on industrial hardware is significantly less common. Experimental studies systematically analyze the manifestations of excessive network traffic on real control units, communication modules, and IIoT devices and assess its impact on control communication and production process continuity remain relatively limited.
Therefore, the main objective of this research is to experimentally examine the vulnerability of specific industrial devices used in Industry 4.0 architecture, in particularly Programmable Logic Controller (PLC) control units, Radio Frequency Identification (RFID) subsystems, and IIoT devices. The IIoT area is specific in the context of cybersecurity, as these devices represent an integration point between the IT and OT layers and are exposed to a higher degree of network connectivity than traditional control elements.
The uniqueness of the presented research lies in the fact that the experiments are performed on a simulated or emulated model rather than on a physical automated production line built from commonly used industrial components, such as PLC control units, industrial Ethernet communication, identification systems, and IIoT devices.
Attacks are carried out during active system operation, analyzing the behavior of specific devices, control communication degradation, and physical consequences on the production process. The research focuses on experimentally investigating the vulnerability of real industrial architecture based on industrial devices, with an emphasis on the system’s physical behavior during an attack.
This research aims to extend the existing automated production line with elements of the IIoT in accordance with the principles of Industry 4.0, physically implement this architecture from industrial control and communication components representing the typical structure of modern production systems, and subsequently experimentally analyze its vulnerability to DDoS and DRDoS attacks during active system operation [15,16].
The experiments focused on assessing the impact of attacks on system availability, the functionality of industrial communication infrastructure, including data exchange between PLC control units, IIoT devices, and higher-level systems, as well as the stability of the production process during actual operation. At the same time, the aim was to identify critical architectural points of the system and experimentally verify the effectiveness of the proposed countermeasures in real operating conditions.
This study focuses on assessing the degradation of deterministic communication, the behavior of specific control and IIoT devices, disruptions in data exchange between the OT and IT layers, and the physical consequences of an attack on production continuity, while also analyzing the fact that these manifestations may appear to be a normal technical failure from the perspective of production operations, with no obvious indication of a cyber attack. The research also includes experimental verification of the effectiveness of architectural countermeasures, such as network segmentation and communication infrastructure perimeter protection.
The main contributions of this work can be summarized as follows:
- Experimental evaluation of the impact of DDoS and DRDoS attacks on a physically implemented cyber-physical production line without simulation or emulation.
- Analysis of the impact of cyber attacks on communication between production equipment and IIoT components, including identification of communication failure moments.
- Impact of internal and external network attack scenarios on production process stability.
- Identification of critical communication points and vulnerable components in a cyber-physical production system.
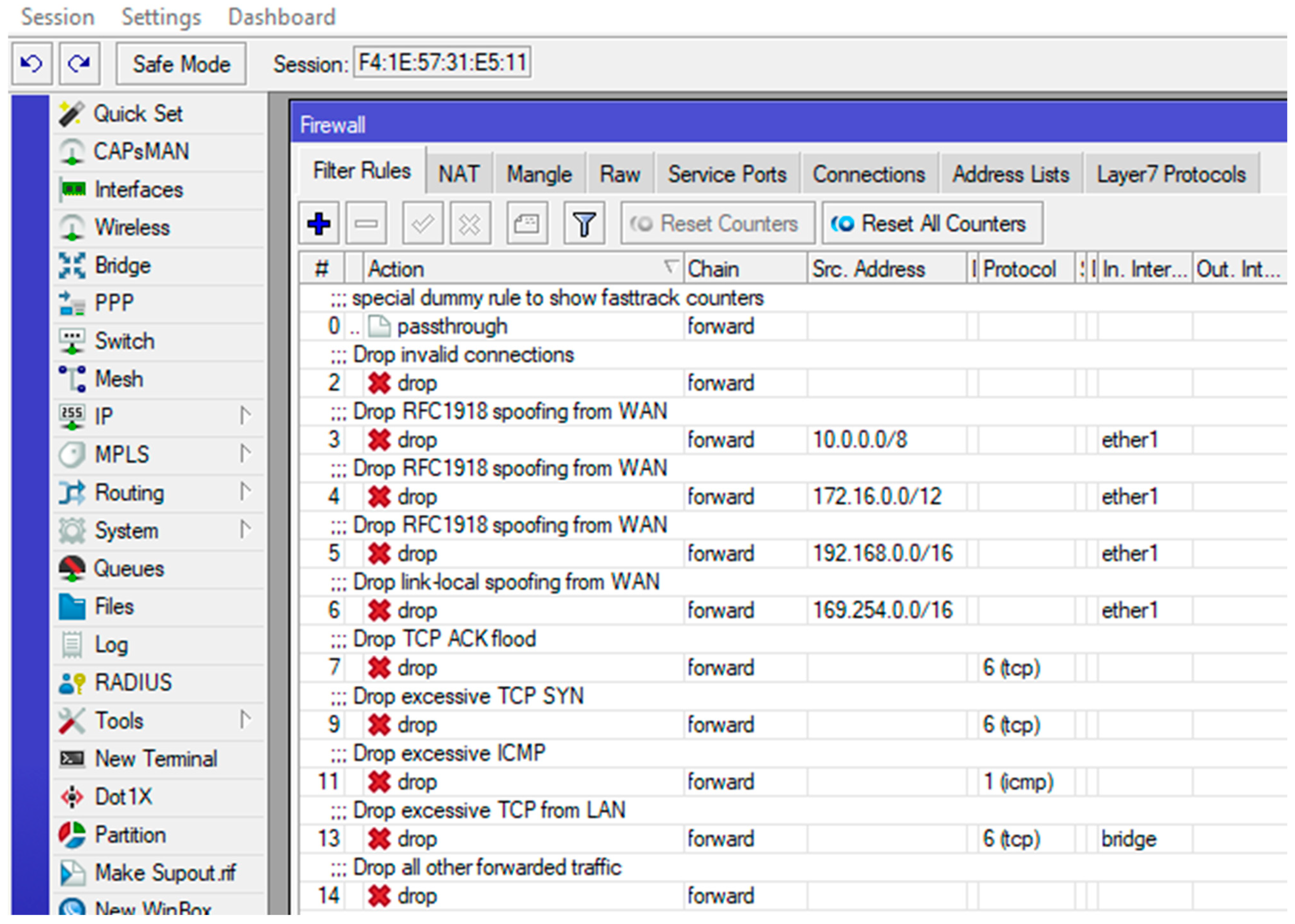
- Design and experimental verification of a firewall-based security solution that can be implemented without major changes to the existing infrastructure.
- Verification of the proposed security measures’ ability to mitigate the impact of attacks and maintain the availability of production communication.
Although the experimental infrastructure was implemented on a production line intended primarily for educational purposes, its control architecture, PLC units, and industrial communication protocols represent a fully fledged industrial solution. Therefore, the obtained experimental results and the identified mechanisms of communication degradation are applicable in the broader context of industrial production systems without the need for major architectural modifications.
The results highlight the need to design production systems based on the principle of security by design, with an emphasis on network segmentation, communication interface control, and architectural separation of IT and OT layers to minimize the risk of control communication degradation and disruption of production operations.
The rest of the article is structured as follows: Section 2 presents related work and theoretical background, Section 3 describes the materials and methods used, including the production line architecture and the attack scenarios implemented, Section 4 contains the results of experimental measurements and their analysis, Section 5 discusses the results along with the limitations of the study, and Section 6 presents conclusions and implications for the design of more secure industrial architectures.
2. Related Work
IoT devices represent a specific architectural element that fundamentally changes the integration of IT and OT layers in the context of modern manufacturing system security [17]. As stated by Wang et al. [18], the growing interconnectedness and convergence of IT and OT infrastructures significantly increase the number of entry points into industrial systems, thereby increasing their exposure to cyber threats.
Similarly, Comert et al. [19] pointed out that the integration of IIoT devices, especially when retrofitting existing production systems, creates new security gaps resulting from the simultaneous operation of legacy technologies and modern IoT solutions. Their integration position between OT and IT infrastructure, combined with a high degree of network connectivity, makes them critical points in terms of attacks targeting availability and unauthorized access.
IIoT has significantly transformed the manufacturing system architecture in the Industry 4.0 concept [20]. The integration of sensors, edge devices, communication gateways, and cloud platforms into the control infrastructure enables continuous operational data collection, real-time processing, and advanced analytical tool implementation.
As stated by Yousuf et al. [21], IIoT architectures play a key role in the predictive maintenance and diagnostics of electric drives, enabling early fault detection and optimization of service interventions.
Sundar et al. [22] demonstrated the use of IIoT in increasing assembly line productivity through data-driven optimization methodologies, while Mashayekhy et al. [23] highlighted the importance of IoT technologies in inventory management and logistics.
IIoT is also used to monitor production assets in automated work environments, for example, through RFID technologies, as documented by Vagaš et al. [24].
Advanced IIoT applications also lay the foundation for digital twin production equipment and processes. Hedayati Kia et al. [25] and Bokhtiar Al Zami et al. [26] point to the growing importance of digital twins in monitoring equipment status, simulating operating scenarios, and optimizing control. Purohit et al. [27] confirmed that one of the main trends in current industrial digitalization is connecting the IIoT infrastructure with digital models.
The development of IIoT as part of the Industry 4.0 concept is systematically analyzed, for example, in the work of Qiu et al. [28], who point to the integrative nature of IIoT as a connecting element between physical production equipment, analytical tools, and digital platforms in the smart manufacturing environment. Similarly, Marinova-Kostova and Kostov [29] emphasized that the implementation of IIoT technologies fundamentally changes the communication architecture of industrial systems and creates new data flows between the IT and OT layers.
Research on the IIoT and CPS security points to the growing complexity of architectures integrating IT and OT layers and the associated security risks.
Wang et al. systematically analyzed IIoT security challenges across individual architectural layers and identified recurring vulnerabilities in authentication, access rights management, communication protocol protection, and DoS/DDoS attack resistance. The authors also note that traditional security approaches developed for IT environments are not fully applicable to IIoT systems due to their close connection to physical processes.
In recent years, the security of industrial cyber-physical systems (ICPSs) and IIoT devices has been the subject of systematic research, with particular emphasis on the convergence of IT and OT layers and the associated expansion of the attack surface.
Kayan et al. [30] analyzed ICPS security from the perspective of architectures, communication protocols, and differences between IT and OT domains, pointing to a fundamental shift from “security by obscurity” to highly interconnected systems exposed to external threats. Most existing solutions focus on anomaly detection, Intrusion Detection Systems (IDSs) mechanisms, and network traffic analysis, but these approaches are insufficiently connected to real incidents and with the assessment of specific vulnerabilities reported in industrial practice.
This study focused on the IIoT and edge architectures [31,32]. They emphasize the growing role of distributed computing nodes, wireless communication, and cloud integration, while highlighting new risks arising from device heterogeneity, limited computing capacity, and the long-life cycle of industrial components. Identified weaknesses include insufficient authentication, weak security of industrial protocols, and insufficient network segmentation, which take on specific significance in the CPS environment given the deterministic nature of control cycles.
Other analyzed works focus on attack modeling, detection algorithm design, and security mechanism evaluation in simulation or testing environments [33]. The dominant research approach consists of using network traffic datasets and applying machine learning methods to classify attacks, with detection accuracy, false positive rate, or communication latency serving as evaluation metrics.
A comparative analysis of these works shows that although the literature systematically identifies vulnerabilities in IIoT and ICPS architectures and proposes advanced detection and defense mechanisms, experimental verification of the impact of attacks on physically implemented manufacturing systems during their actual operation remains limited. Most studies evaluate security mechanisms at the network layer or in simulated conditions, with less attention paid to analyzing the behavior of specific control units, IIoT devices, and deterministic industrial communication in active manufacturing operations.
These shortcomings create potential vulnerabilities in the system that can be exploited to compromise the availability, integrity, or confidentiality of transmitted data. However, in the CPS environment, the degradation of the communication layer has specific significance, as the disruption of deterministic communication can lead to the destabilization of control cycles and, consequently, to physical consequences for the production process.
Unlike traditional IT systems, attacks targeting availability in an industrial environment are not only a problem for network infrastructure but can also directly affect the operation of technological equipment.
DDoS attacks are among the most critical threats to availability in IIoT and CPS architectures because they can quickly exhaust network and computing resources, thereby indirectly disrupting the deterministic data exchange on which real-time process control relies.
Research focusing on DDoS attacks in IIoT and CPS environments is predominantly oriented toward the network and data layers of architecture. Current research in this area focuses primarily on the network and computing layers of architecture, particularly on edge cloud nodes, Software-Defined Networking (SDN) controllers, and communication infrastructure.
Anomaly detection approaches using machine learning and deep learning methods dominate, as do proposals for adaptive defense and resilient frameworks, whose effectiveness is evaluated using metrics such as accuracy, precision, recall, latency, throughput, and resource availability recovery.
Al-Obeidat et al. [34] analyzed DDoS attack detection in an Edge-IIoT environment supported by a digital twin using deep learning models verified on a publicly available dataset generated in a digitally modeled environment. They reported a detection accuracy of approximately 96% without a connection to physical control devices.
Zakariah et al. [35] proposed a hybrid machine learning-deep learning (ML/DL model for IDS in IIoT/SCADA environments with an accuracy exceeding 99%, with evaluation based on classification metrics (accuracy, precision, recall, and F1-score) over experimental network traffic datasets.
Alrumaih and Alenazi [36] present the ERINDA simulation framework for increasing the resilience of ICS to DDoS attacks, where they evaluate throughput, latency, and availability recovery rate (≈88% improvement in throughput recovery), but exclusively in a controlled simulation environment.
Orman [37] analyzes hybrid IDS architectures for IIoT and points to improvements in detection adaptability, with validation taking place primarily on datasets in his review study.
Zhukabayeva et al. [38] identified the architectural vulnerabilities of IIoT and edge systems from a conceptual perspective without experimentally verifying the physical impacts of attacks.
Hareesh et al. [39] experimentally quantified the impact of DoS attacks on SCADA system communication metrics (latency, packet loss) without analyzing the behavior of production modules.
Eryılmaz et al. [40] confirm the high accuracy of ML/DL models for DDoS detection but point out the limited verification in real industrial architectures in a systematic review.
Swati et al. [41] proposed an adaptive Moving Target Defense mechanism for IIoT edge environments tested in Mininet simulation, where they evaluated resource availability and service response, with no validation on physically implemented control systems.
The analyzed works show that the current research achieves very high classification of metric values and significant improvements in network resilience, confirming progress in the design of detection and mitigation mechanisms for IIoT environments. Nevertheless, these approaches are mainly evaluated at the level of datasets, simulation models, or virtualized testbeds, with an emphasis on detection accuracy, network throughput, and quality of service (QoS).
However, there is no systematic experimental verification of how a DDoS attack manifests on specific physically implemented control units, deterministic industrial protocols, and the stability of a real-world production process.
The result is a gap between the high detection accuracy achieved under controlled conditions and limited empirical knowledge about the physical consequences of attacks in realistic industrial architectures integrating IIoT elements.
Table 1 provides a structured overview of selected scientific papers focusing on DDoS attacks in IIoT environments and industrial control systems (ICSs/SCADA) for a systematic comparison of the methodological approaches, experimental environments, and evaluation metrics of published studies. The table summarizes the analyzed environment, methodology used, focus of the work, declared contribution, and the available quantitative results, enabling the identification of dominant research trends and existing gaps in the field of experimental verification.

Table 1.
Overview of selected research papers focused on DDoS attacks in IIoT/ICS environments.
These incidents and published analyses suggest that cyber attacks in industrial environments are no longer an isolated IT infrastructure problem but have a direct impact on the availability and continuity of production processes. The literature also points to a trend of combined and coordinated attacks, in which distributed denial of service (DDoS) attacks are used as a destabilizing element affecting communication and control infrastructure.
In addition to academic research, real-world security incidents highlight the growing vulnerability of industrial systems. Recent cases have shown that cyber attacks are no longer an isolated IT infrastructure problem but can directly impact the availability and continuity of production processes. Table 2 summarizes the selected incidents’ analysis and identifies several recurring characteristics.

Table 2.
Overview of selected incidents affecting industrial companies and infrastructure.
The interconnection of IT and OT layers creates an environment in which the consequences of attacks that originally targeted the information infrastructure are transferred to the control and technology environment. DDoS attacks are increasingly used in combination with ransomware or direct attacks on ICS/SCADA systems, intensifying production operations’ destabilizing effect. Simultaneously, incidents point to insufficient industrial network segmentation and the high dependence of physical processes on communication infrastructure availability.
Simultaneously, several empirical analyses from various sectors point to significant economic and operational damage caused by availability attacks, confirming their potential to disrupt critical processes beyond the purely network level. These findings suggest that DOS attacks have systemic impacts and can affect operational continuity, management stability, and technological operation security.
However, an analysis of the existing literature shows that research in the field of DDoS attacks in IIoT and ICS environments is predominantly focused on the design of detection algorithms, classification model optimization, and detection accuracy evaluation. Most studies use publicly available datasets or simulated testbeds and focus on network metrics such as accuracy, F1-score, throughput, and latency. Although these approaches provide significant insights into attack identification and mitigation, the physical consequences of attacks on real-world manufacturing systems are rarely evaluated.
Therefore, the research gap lies in the lack of experimental studies on physically implemented industrial architectures that would quantify the operational and technological consequences of attacks targeting availability in an environment integrating IT, OT, and IIoT elements. This study addresses this gap by conducting controlled experiments on a physically implemented production line with real PLC control units and Industry 4.0 architecture components, systematically quantifying the impact of availability attacks on deterministic industrial communication, control cycle stability, and production process continuity.
3. Materials and Methods
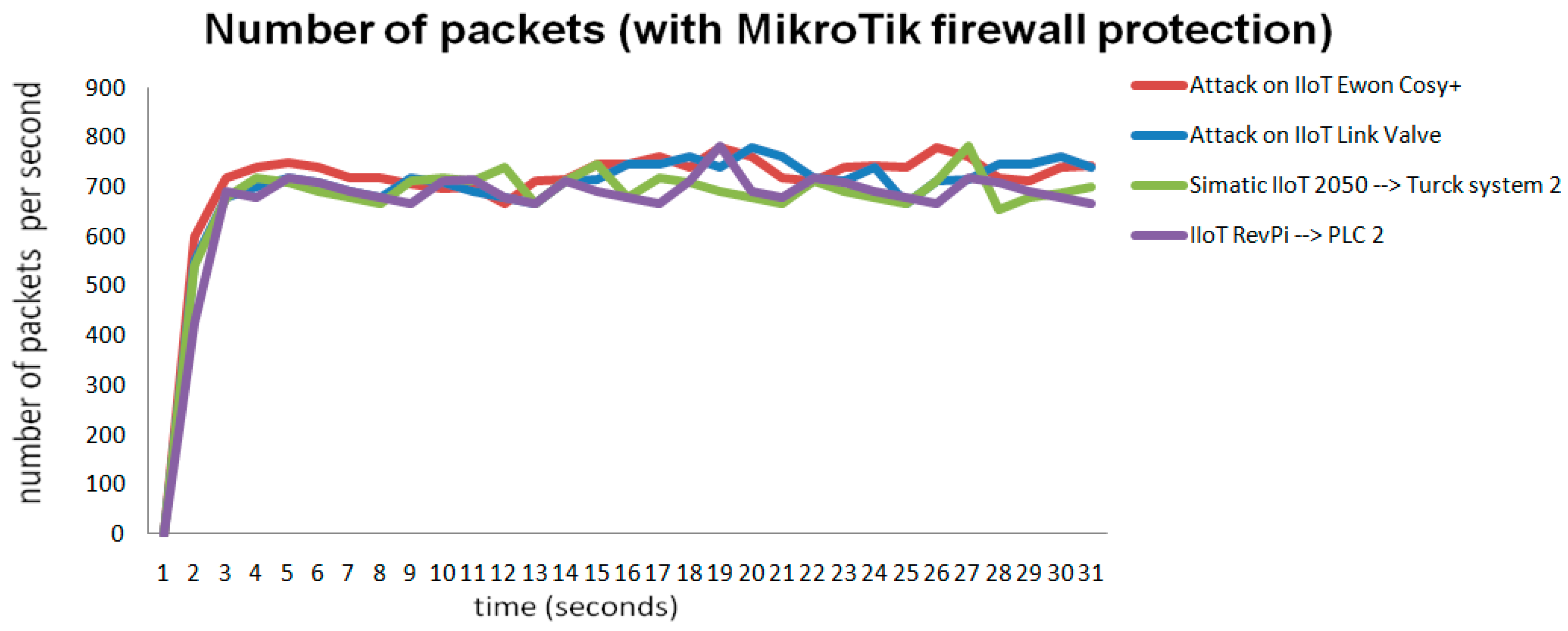
This chapter describes the experimental architecture, infrastructure extension, and cyber attack scenarios used to evaluate the impact of availability attacks on a physically implemented cyber-physical manufacturing system. This experimental study quantifies the operational and technological consequences of DDoS and DRDoS attacks on a real production line based on Industry 4.0 principles, integrating IT, OT, and IIoT layers.
Experiments were conducted on a physically implemented modular production system. The original architecture was purposefully expanded with IIoT integration elements, monitoring nodes, edge devices, and remote access elements to create a realistic industrial environment that reflects the current implementation principles of Industry 4.0 and the interconnection of IT and OT layers.
The experimental methodology is based on the controlled simulation of DDoS and DRDoS availability attacks and systematic monitoring of their impact on the control, communication, and technology layers of the system.
The experiment was designed in the form of three different scenarios representing different availability disruption mechanisms in a production line environment.
The first scenario represents a direct TCP SYN flood DDoS attack that targets selected control and monitoring layer elements.
The second scenario was implemented as a direct TCP ACK flood DDoS attack targeting control and IIoT integration devices.
The third scenario simulated a reflected DRDoS (ICMP flood) attack, in which the target was flooded through intermediary nodes, modeling a more realistic form of distributed attack with traffic amplification.
Each scenario was implemented within a controlled time interval with a defined traffic intensity, and the system behavior was compared with that of the reference no-traffic state.
Three main metrics were systematically monitored for all compromised devices:
- TTCL (Time to Communication Loss)—the time from the start of the attack to the loss of stable communication.
- Peak traffic (packets/s)—maximum intensity of network traffic during the attack.
- Peak CPU load (%)—maximum utilization of the device’s processor.
The TTCL metric is a key indicator of a system’s resilience to denial-of-service attacks because it expresses the time interval during which the device is capable of maintaining deterministic communication. Peak traffic characterizes the intensity of the attack and allows for comparison between scenarios, while Peak Central Processor Unit (CPU) load documents the depletion of computing resources during the load.
The following subchapters describe in detail the physical CPS infrastructure, its extension with IIoT elements, and the specific implementation of DDoS and DRDoS scenarios.
3.1. Cyber-Physical System (CPS) Infrastructure Based on IIoT
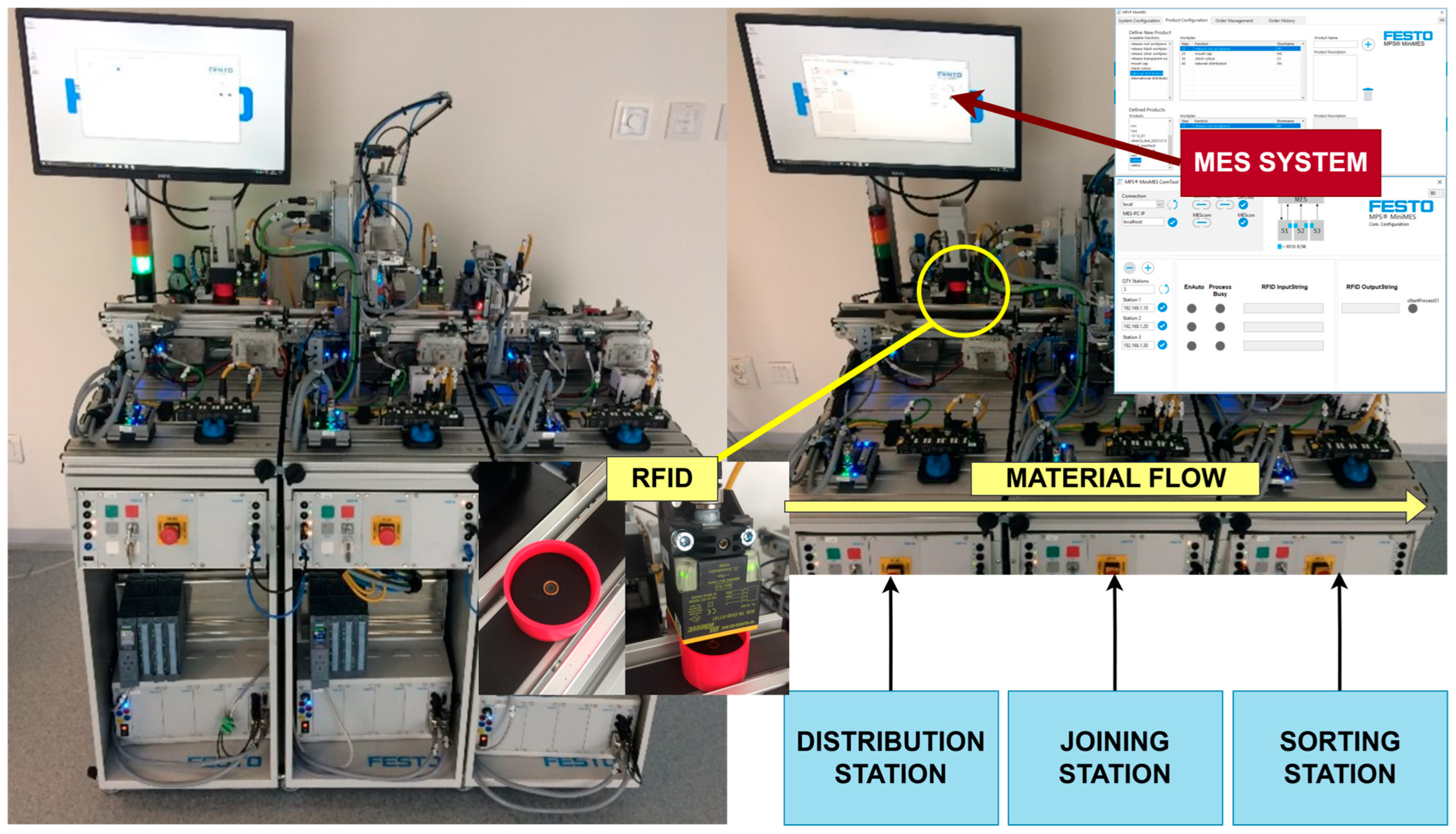
The experimental infrastructure of the cyber-physical system was implemented based on the modular production line Modular Production System (MPS) System 203 Industry 4.0 from Festo Didactic GmbH & Company KG, Munich, Germany [46]. This production line is shown in Figure 1. The system represents a compact but technologically representative production line that integrates physical production processes, decentralized control, identification technologies, and a higher-level Manufacturing Execution System (MES) information system, creating a suitable environment for researching the principles of Industry 4.0 and CPS.
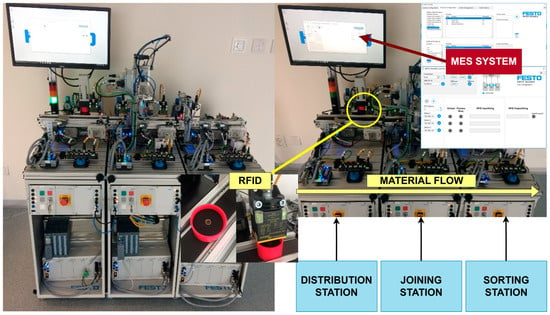
Figure 1.
Physically implemented cyber-physical production line MPS 203 Industry 4.0 (Festo Didactic, Munich, Germany), consisting of three autonomous stations (distribution, assembly, and sorting) controlled by Siemens SIMATIC S7-1512-1PN PLC units, Siemens AG, Munich, Germany. A superior MES coordinates the production process, with an integrated RFID subsystem ensuring material flow and digital product representation.
The production line represents a complex mechatronic environment comprising three autonomous stations: a distributing/conveyor station, a joining station, and a sorting station. Each of these stations forms a separate physical and mechatronic unit equipped with its own conveyor module with an electric motor drive, pneumatic actuators such as stoppers, deflectors, and ejectors, as well as sensors for detecting the presence and position of workpieces. The joining station is also extended with a suction gripper and a pick-and-place module, enabling the automated handling of parts during the production process.
The control of individual stations is decentralized using Siemens SIMATIC S7-1512C-1 PN, Siemens AG, Munich, Germany programable logic controllers (PLC), with each station controlled by a separate PLC.
Siemens SIMATIC S7-1512-1PN PLC units were selected as the S7 family’s highest-performance class of control units. Their use allows the evaluation of the system response even for devices with high computing and communication capacities, thereby minimizing the impact of any hardware limitations on the experimental results. The control units ensure sequential control of technological operations, processing of signals from sensors, control of electric motor drives and pneumatic actuators, as well as communication with the RFID system and the superior MES production system. The PLCs are configured as PROFINET controllers and the peripheral devices are connected via SysLink interfaces and bus I/O nodes, with the pick-and-place module integrated into the control architecture via a PROFINET bus node.
RFID technology ensures product identification and tracking within the manufacturing process, thereby creating a link between the system’s physical and digital layers. MPS 203, Industry 4.0 identification subsystem is implemented using Turck industrial RFID components and consists of RFID transponders integrated into workpieces and four high-frequency RFID read/write heads operating at 13.56 MHz in accordance with ISO 15693 [47], Turck GmbH, Mülheim an der Ruhr, Germany. The distribution and sorting stations are equipped with one RFID head, whereas the connection station uses two RFID heads, enabling identification and data updating when the product enters and exits the station.
The RFID read/write heads are not connected directly to the PLC control units but via decentralized Turck TBEN-S2-2RFID-4DXP modules, which function as PROFINET IO devices and RFID masters for one or two connected heads. In the case of a connection station, both RFID heads are connected to a single TBEN module, creating a local RFID subsystem. Data on the production order, required technological operations, and execution status are written to the RFID transponders, and this information is autonomously evaluated by the Siemens SIMATIC S7-1512C-1 PN PLC units and used to decide on the further processing of the product.
The production line’s communication infrastructure based on the PROFINET industrial Ethernet network, which connects Siemens control units, PROFINET I/O nodes, an RFID subsystem, an industrial Ethernet switch, and a computer with a higher-level MES. The network is implemented as a local industrial Local Area Network (LAN) in a private address space with a fixed Internet Protocol (IP) address for each device, which ensures deterministic communication, stable system operation, and repeatability of experimental conditions during cyber experiments.
At the protocol level, PROFINET communication between PLCs and IO devices is based on cyclical real-time data exchange, where process data are transferred within defined communication cycles. Each PLC functions as a PROFINET controller and regularly updates the connected IO devices’ input and output process images. This deterministic communication structure ensures the control cycle’s stable execution under normal operating conditions.
Each station is controlled by a separate PLC configured as a PROFINET controller. The RFID subsystem is implemented using decentralized Turck modules that function as PROFINET IO devices and communicate cyclically with the respective PLCs. Each TBEN module supports two HF RFID channels, and two RFID read/write heads in the connection station are connected to one TBEN module. The network also includes a pneumatic valve terminal with a PROFINET interface, which controls the pneumatic elements of the Joining station.
The superior cyber layer of the cyber-physical system comprises the MPS® MiniMES production information system from Festo Didactic, which runs on an industrial PC with the Windows 10 operating system. This system ensures product and work plan definition, production order generation and management, production and technological data recording in RFID transponders, and continuous production status monitoring. Thus, MiniMES is a key element of the system’s cyber part, integrating the production process’s planning, control, and supervision. The basic control and peripheral components of the original MPS 203 Industry 4.0 production line architecture are listed in Table 3.

Table 3.
Overview of the main control and peripheral components of the original architecture of the MPS 203 Industry 4.0 production line, including their functional role, network addressing, and communication protocol used.
The presented implementation uses the OPC DA (OLE for Process Control—Data Access) specification via the DELTALOGIC S7/S5 OPC Server (version 4.12.0.11527, Delta Logic Automatisierungstechnik GmbH, Schwäbisch Gmünd, Germany). Communication is implemented in a classic client-server architecture based on the COM/DCOM model, with the OPC server and Siemens SIMATIC S7-1512C-1 PN PLC units using the S7-TCP/IP within an industrial Ethernet network. The OPC interface enables the cyclic reading and writing of process variables, data blocks (DBs), memory words (MWs), and status variables between the PLC control layer and the higher-level MES. This ensures the continuous exchange of technological data, status information, and production parameters between the system’s OT and IT layers.
The OPC interface is used to transfer status information from the control units to the MES and distribute production orders and parameters to the production stations. The MES communicates primarily with the first station of the production line, while the production process, the status of individual orders, and product tracking are evaluated based on data stored in RFID tags and based on the status signals of the PLCs of individual stations.
The entire system is designed as a cyber-physical production system based on closed-loop feedback between the physical production process and decentralized control using Siemens SIMATIC S7-1512C-1 PN, digital product representation using RFID technology, and the MPS MiniMES higher-level information system. The production line implements discrete variant production of an assembled product consisting of a base body with an integrated RFID transponder and an optional cover, with data linked to each individual piece determining the specific product configuration.
The production process is initiated by creating a production order in the superior MES, which defines technological operations, production variants, quality control requirements, and shipping methods. At the distribution station, this data is recorded in the product’s RFID transponder, which carries information about the processing status and operations performed throughout the entire production cycle. The control units of the individual stations autonomously evaluate this data and use it to decide on the production cycle.
At the connecting station, a dynamic decision is made on whether to perform or skip the cover assembly using a pick-and-place module based on data read from the RFID transponder. The result of this operation is then updated back to the RFID tag, ensuring a consistent digital representation of the product status. The sorting station then checks the selected product properties and redirects the product to the appropriate output branch designated for domestic or international shipment or discarded as a defective item based on a combination of RFID data and inspection results.
Decisions on technological steps are not made according to a fixed production line sequence but are dynamically based on data linked to a specific product, with local control at the level of individual stations. After processing is complete, the product is transported to the output point, and the single-piece production cycle is closed, with all relevant data on the production process available in the superior MES.
3.2. Expanding Infrastructure Towards IIoT, Monitoring, and Remote Access
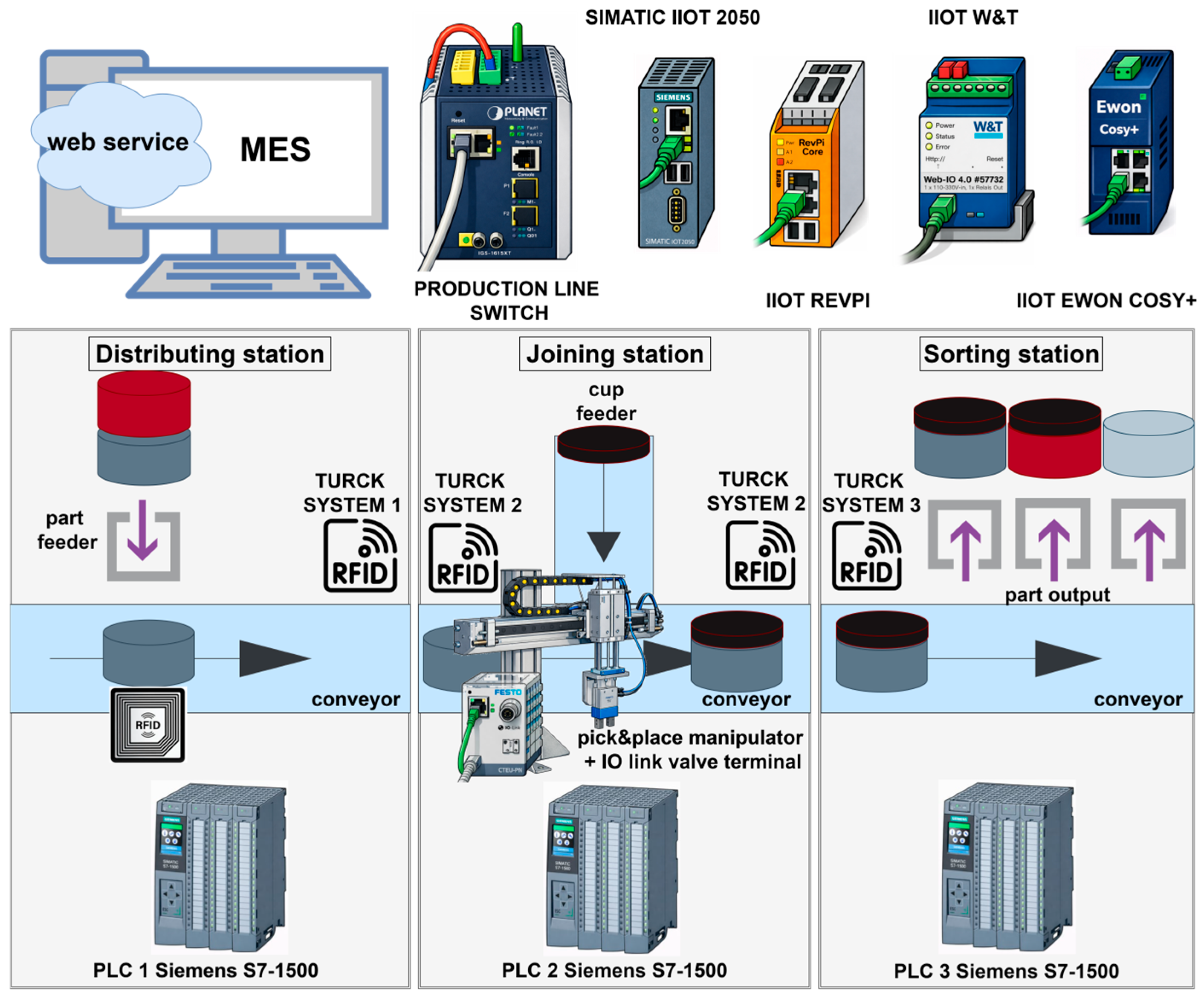
The MPS 203 Industry 4.0 system was originally designed as a didactic cyber-physical manufacturing system that supports selected Industry 4.0 principles, particularly in the area of production management through MES and RFID-based product identification. The basic architecture of the system primarily focuses on the production process, order flow, and product-oriented management. Although the system had a web interface at the MES level, this interface focused exclusively on production planning and monitoring and did not provide comprehensive options for technical monitoring, equipment diagnostics, network infrastructure, or remote service interventions.
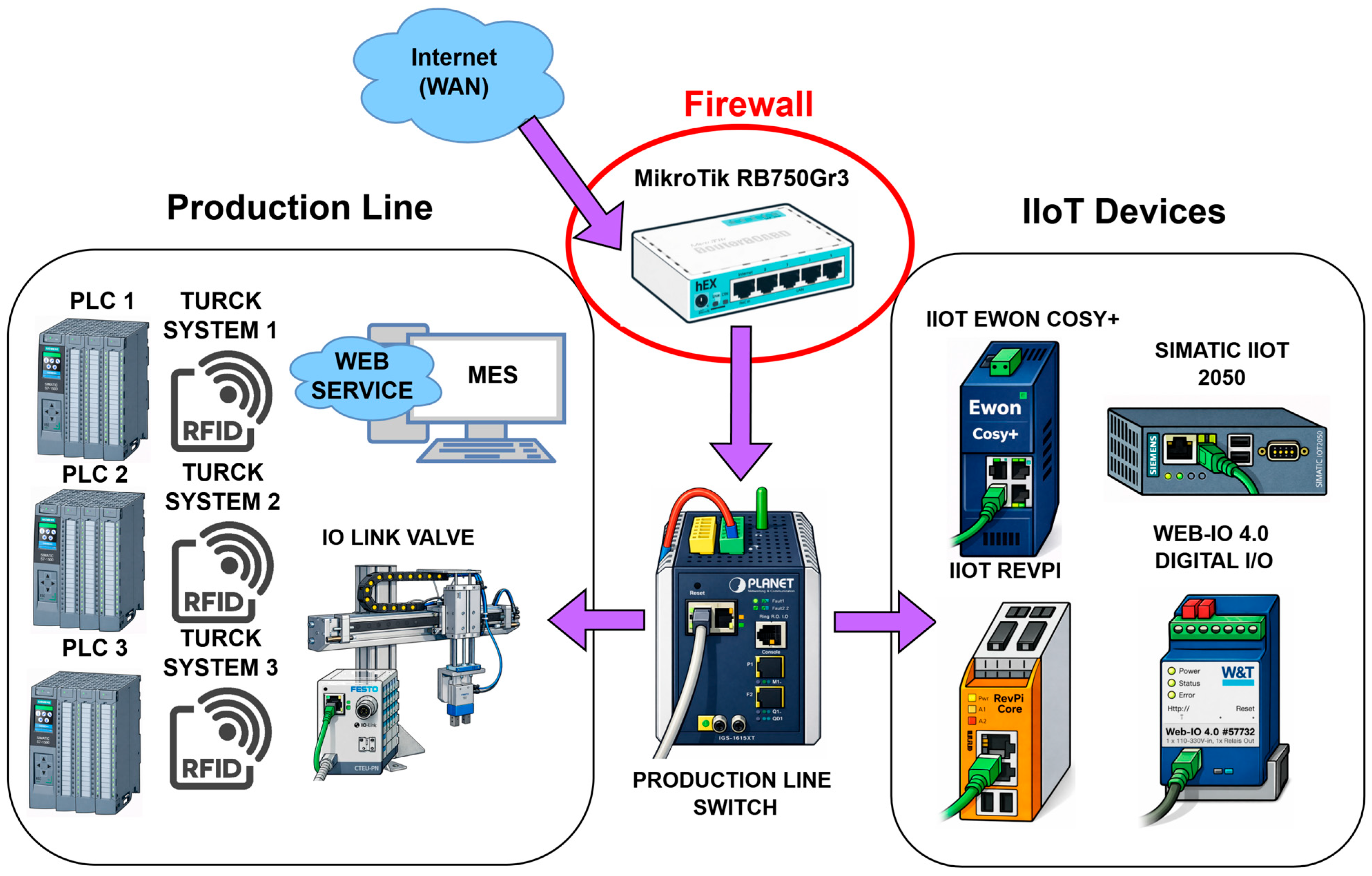
Figure 2 shows the overall configuration of the experimental production line, including the material flow between the distribution, connection, and sorting stations, the relevant PLCs, the RFID systems, and the IIoT infrastructure components. The figure provides a system-level overview of the physical process, control units, and communication elements that form the experimental cyber-physical architecture.
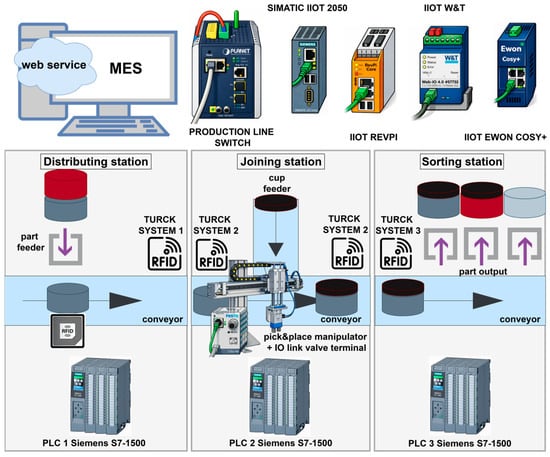
Figure 2.
Schematic representation of the MPS 203 Industry 4.0 production line showing material flow, control layer, and IIoT infrastructure extension. The architecture comprises three autonomous distribution, assembly, and sorting stations controlled by Siemens SIMATIC S7-1512C-1 PN, connected to an RFID subsystem and a high-level MES. The original control architecture is extended with an industrial network element, edge devices (Siemens SIMATIC IOT2050, Siemens AG, Munich, Germany, Revolution Pi, KUNBUS GmbH, Ostfildern, Germany), monitoring modules (W&T), and remote access elements (Ewon Cosy+), which ensure the connection of the IT and OT layers without interfering with the production process’s deterministic control.
Therefore, the original system architecture was purposefully expanded to include IIoT infrastructure, which aims to make operational and diagnostic data from automation devices accessible via standard network and application interfaces, enable remote monitoring and maintenance, and create an integration bridge between the OT and IT layers of the system.
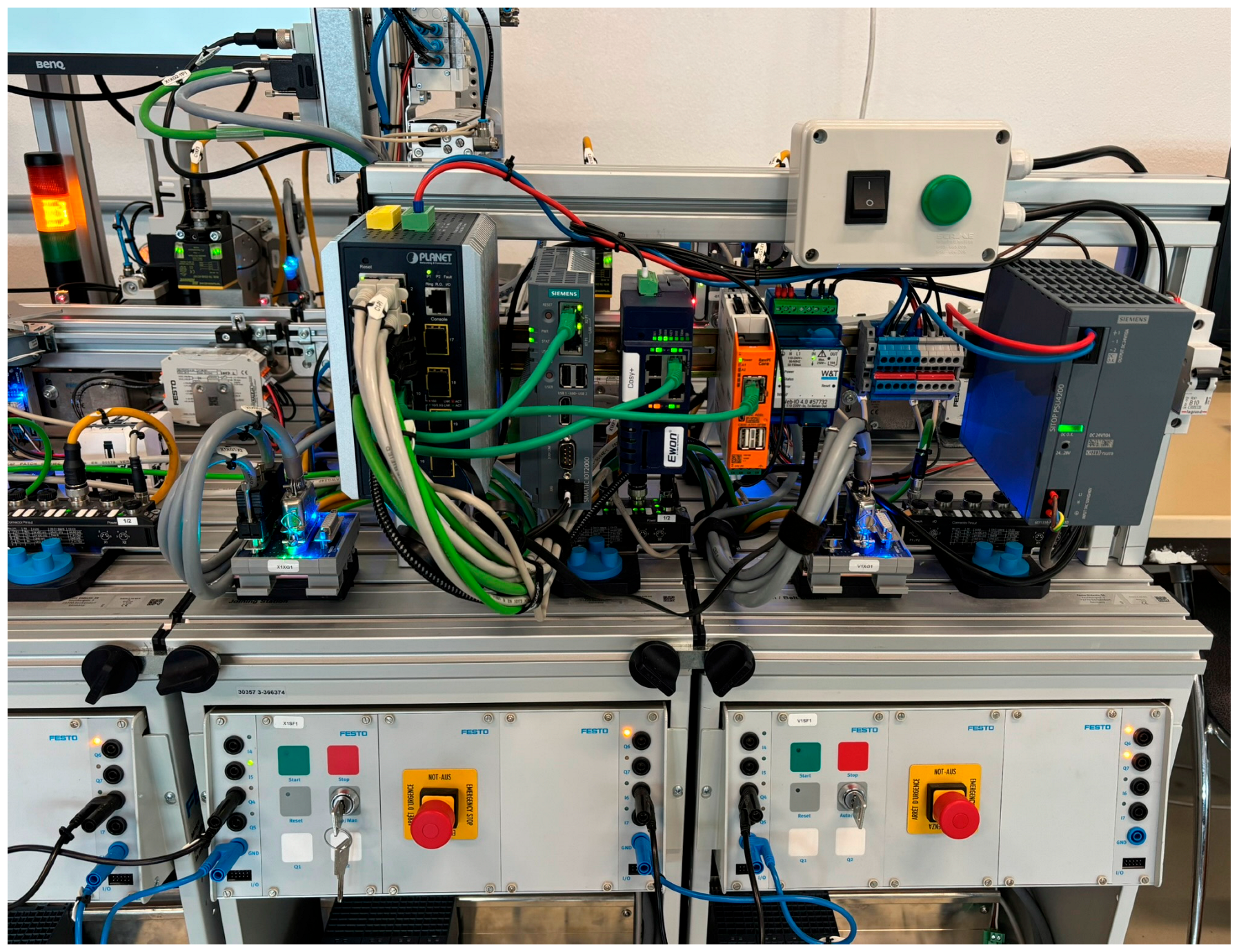
In this context, IIoT does not replace the control system but supplements it, expanding the system with monitoring, diagnostic, and integration functions without interfering with the deterministic control of production processes. The original architecture of the MPS 203 Industry 4.0 production line was subsequently expanded with IIoT infrastructure, which enables monitoring, remote access, and interconnection of the system’s IT and OT layers (Figure 3).
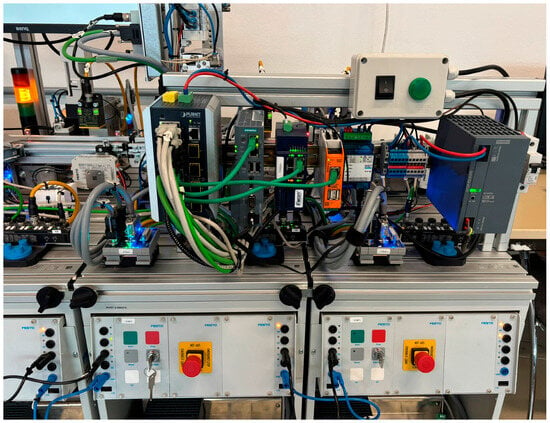
Figure 3.
IIoT and network infrastructure of the MPS 203 Industry 4.0 production line. The figure shows the fully assembled and interconnected elements of the extended architecture, including an industrial controllable network element, edge devices (Siemens SIMATIC IOT2050, Revolution Pi), VPN gateways for remote access, monitoring and I/O modules, and power supply infrastructure. The assembly forms an integration layer between the control (OT) and information (IT) parts of the system without interfering with the production process’s basic control logic.
This expansion was based on the integration of a central industrial network infrastructure, as the original system configuration did not include a separate manageable network element. Therefore, a manageable PLANET IGS-6325-8T8S4X (PLANET Technology Corporation, New Taipei City, Taiwan) industrial Ethernet switch was integrated into the architecture to form the central communication node of the entire IIoT network.
The switch connects PLC control units, edge devices, remote I/O modules, Virtual Private Network (VPN) routers, and monitoring nodes into a unified industrial network and provides support for manageable L2 and L3 layer functions such as Virtual Local Area Network (VLAN) segmentation, routing, redundancy, and basic security mechanisms. This creates a stable and expandable communication foundation for the system’s IIoT functions.
To support remote maintenance and service interventions, the architecture has been supplemented with an Ewon Cosy+ Ethernet industrial VPN router, which provides secure remote access to devices connected to the industrial Ethernet/PROFINET network, HMS Industrial Networks AB, Halmstad, Sweden. The router initiates an encrypted VPN connection to the Talk2M cloud service exclusively in the form of outgoing connections, eliminating the need to open network ports in the corporate or production network. This IIoT element enables remote diagnostics, programming, and maintenance of the control system and represents a practical implementation of Industry 4.0 principles in the field of operation and maintenance.
The IIoT monitoring layer also includes a Wiesemann & Theis Ethernet remote I/O module (Wiesemann & Theis GmbH, Wuppertal, Germany), which is used for the production system power supply. The module functions as an embedded network device with proprietary firmware and an integrated Web-IO interface accessible via HTTP/HTTPS. The digital input is used to detect the supply voltage, while the relay digital output controls the LED indication of the current system status. The power status is available independently of the PLC control logic owing to the web interface, which increases system transparency and supports rapid diagnostics within the IIoT infrastructure.
Revolution Pi Core SE (KUNBUS GmbH, Ostfildern, Germany) devices and Siemens SIMATIC IOT2050 (Siemens AG, Munich, Germany) industrial edge devices were integrated into the architecture to serve as IIoT integration nodes and connect the OT and information IT layers. These devices ensure the collection, pre-processing, and accessibility of operational data without interfering with the deterministic control of PLC units.
The Revolution Pi Core SE module is based on the Raspberry Pi Compute Module 4S platform and runs on the Revolution Pi OS operating system, which is based on Raspberry Pi OS and Debian distribution (current version Bookworm—Debian 12). It is an industrially modified Linux distribution with an implemented RT (real-time) kernel patch and additional KUNBUS packages (e.g., piControl, PiCtory, MQTT client, and OPC UA server) that provide image management and communication integration functions.
The Siemens SIMATIC IOT2050 runs on the SIMATIC Industrial OS operating system based on Linux (Debian). It provides a stable and industry-oriented platform for edge computing, data integration, and information processing at the industrial network level.
The Node-RED 5.0 environment, which acts as a middleware layer in the proposed architecture, was implemented on both edge devices. Node-RED performs data transformation, filtering, and routing between communication protocols and logically processes messages between the OT and IT parts of the system. The MQTT publish–subscribe communication mechanism makes the processed data available for web monitoring and other information layer tools.
It should be emphasized that part of the implemented IIoT infrastructure is based on open-source software components. The Revolution Pi OS operating system is based on the Debian distribution, and the Node-RED environment is an open middleware tool for data integration. The use of open-source solutions increases the transparency of the architecture, enables security control, and supports the reproducibility of experimental results, which is important in the context of modern industrial control scenarios.
This creates a unified IIoT integration and monitoring layer that provides a comprehensive view of the system status directly based on data from the control layer while maintaining a strictly separated control and monitoring architecture.
The Siemens SIMATIC IOT2050 device is used in the system primarily for centralized collection and monitoring of data from three Siemens SIMATIC S7-1512C-1 PN control units, from which selected database blocks (DBs) containing key status, diagnostic, and process information are read. This creates a unified IIoT monitoring layer that provides a comprehensive view of the status of the entire system based directly on data from the control layer while maintaining a strict separation of control and monitoring.
In normal operating conditions, communication between production components and IIoT devices follows a cyclic data exchange model, where PLC control units regularly exchange process data with operating devices and monitoring systems. The process variables, sensor data, and control commands are continuously updated to ensure a deterministic production operation. IIoT gateways and edge devices preprocess selected data and provide higher-level services, such as remote monitoring, visualization, and data logging. During cyber attacks, excessive network traffic disrupts this cyclical communication, causing delays or loss of control data, which directly affects production continuity. Therefore, the communication flow consists of repeated acquisition, processing, and forwarding of operational data between control units, industrial equipment, and supervisory systems, creating a closed control loop whose stability depends on reliable network communication.
The data flow can be summarized as follows: process variables generated at the PLC level are cyclically updated via PROFINET and made available to the MES via the OPC DA interface. Selected data blocks (DBs) are accessible via IIoT edge devices, where they undergo light preprocessing in the Node-RED middle layer, including filtering, formatting, and protocol translation. The processed data are then sent via MQTT to the monitoring and visualization services of the IT layer. This architecture creates a structured vertical data flow from the physical process to the supervisory information systems.
3.3. DDoS and DRDoS Attacks
DDoS attacks are one of the most serious threats to IIoT devices, which form the basis of modern cyber-physical manufacturing systems [48,49]. IIoT devices, such as programable logic controllers, industrial sensors, actuators, and edge gateways, are primarily designed with an emphasis on reliability, deterministic behavior, and long-term continuous operation, with security mechanisms historically considered secondary. Consequently, many industrial devices are vulnerable to attacks targeting service availability, with even relatively low-intensity attacks potentially leading to serious operational disruptions given the limited computational resources, memory, and network capacity of IIoT elements [18].
DDoS attacks differ from those in traditional IT systems in the context of industrial networks. The attacker’s goal is not only to overwhelm the network infrastructure but also to disrupt control and monitoring processes, delay or lose critical communication messages, and subsequently cause errors or unplanned production line downtime [50].
Attacks carried out at the transport or application layer, for example in the form of TCP SYN flood, UDP flood, or ICMP flood, can lead to the depletion of PLC and industrial gateway system resources, resulting in a loss of communication with SCADA or MESs [51].
Attacks targeting industrial communication protocols, such as Modbus/TCP, Profinet, EtherNet/IP, or OPC UA, which were originally designed without focusing on security mechanisms and flooding resistance, are also a serious problem [52].
DRDoS attacks represent a special category of attacks that differ from classic DDoS attacks in the way they generate and amplify attack traffic. In a DRDoS attack, the attacker does not communicate directly with the victim but exploits third parties, known as reflectors, which are legitimate servers or devices that provide network services. The attacker spoofs the source IP address of the victim and sends small requests to reflectors, which then respond with significantly larger packets to the target system. This mechanism leads to a significant amplification of attack traffic and makes identifying the actual attack origin difficult. In an IIoT environment, reflectors can be, for example, incorrectly configured UDP services, DNS, or NTP servers, as well as some industrial and diagnostic protocols, which increases the risk that the industrial devices themselves will be unwittingly involved in the attack [53].
This difference is particularly significant from the perspective of detection and defense mechanisms, as the traffic generated during a DRDoS attack may appear to be legitimate communication at first glance.
The fundamental difference between a classic DDoS and DRDoS attack is that in a classic DDoS attack, the target is directly flooded with attack traffic generated by a botnet of compromised devices, whereas in a DRDoS attack, the target is flooded with responses from legitimate systems that have been exploited as attack intermediaries [54].
In an industrial environment, this can lead to the attack being misinterpreted as a sudden increase in process or diagnostic communication, which significantly complicates the timely response of security mechanisms.
The consequences of DDoS and DRDoS attacks in the IIoT environment go beyond service availability and can also have physical and security implications. Disruption of communication between control units and higher-level systems can lead to loss of synchronization, erroneous decisions by control algorithms, or activation of emergency conditions, which can have a direct impact on operator safety and the technological equipment integrity.
Therefore, effective protection of the IIoT system requires a combination of network segmentation, strictly defined communication rules, and advanced detection mechanisms based on network traffic behavioral analysis. Therefore, the current research focuses on developing lightweight detection algorithms and creating realistic datasets that will enable the reliable identification of DDoS and DRDoS attacks in the Industry 4.0 environment.
3.4. Traffic Monitoring and Data Analysis
The professional packet capture and analysis tools Capsa Portable Network Analyzer (Colasoft LLC, Pleasanton, CA, USA) and NetworkMiner Packet Analyzer (Netresec AB, Stockholm, Sweden), operated in fully licensed versions, were used to monitor network traffic and subsequently analyze the attack course. The Capsa Portable Network Analyzer is a tool designed for real-time monitoring and network communication diagnostics, enabling detailed packet analysis, measurement of traffic volume, and identification of network behavior anomalies. The NetworkMiner Packet Analyzer is a forensic tool that passively analyzes captured packets and reconstructs network sessions.
The tools used enabled detailed inspection of communication in the industrial Ethernet network, identification of peak traffic intensity (packets/s), analysis of protocol behavior (TCP/UDP/ICMP), and correlation of communication loss moments with measured network parameters during individual experimental scenarios.
4. Results
This chapter focuses on describing experimental attack scenarios used in testing production line communication and identifying its vulnerabilities during the production process in interaction with other IIoT devices within a shared network infrastructure. Particular attention is paid to DDoS and DRDoS attacks, as well as the results of the experiments and proposed solutions aimed at increasing the security and reliability of production line operation with integrated IoT devices.
The test environment is based on a real-time system. The expansion of the production line with IIoT devices in accordance with the Industry 4.0 concept enables communication via an external Wide Area Network (WAN) environment, but at the same time increases its exposure to potential cyber attacks from the external network.
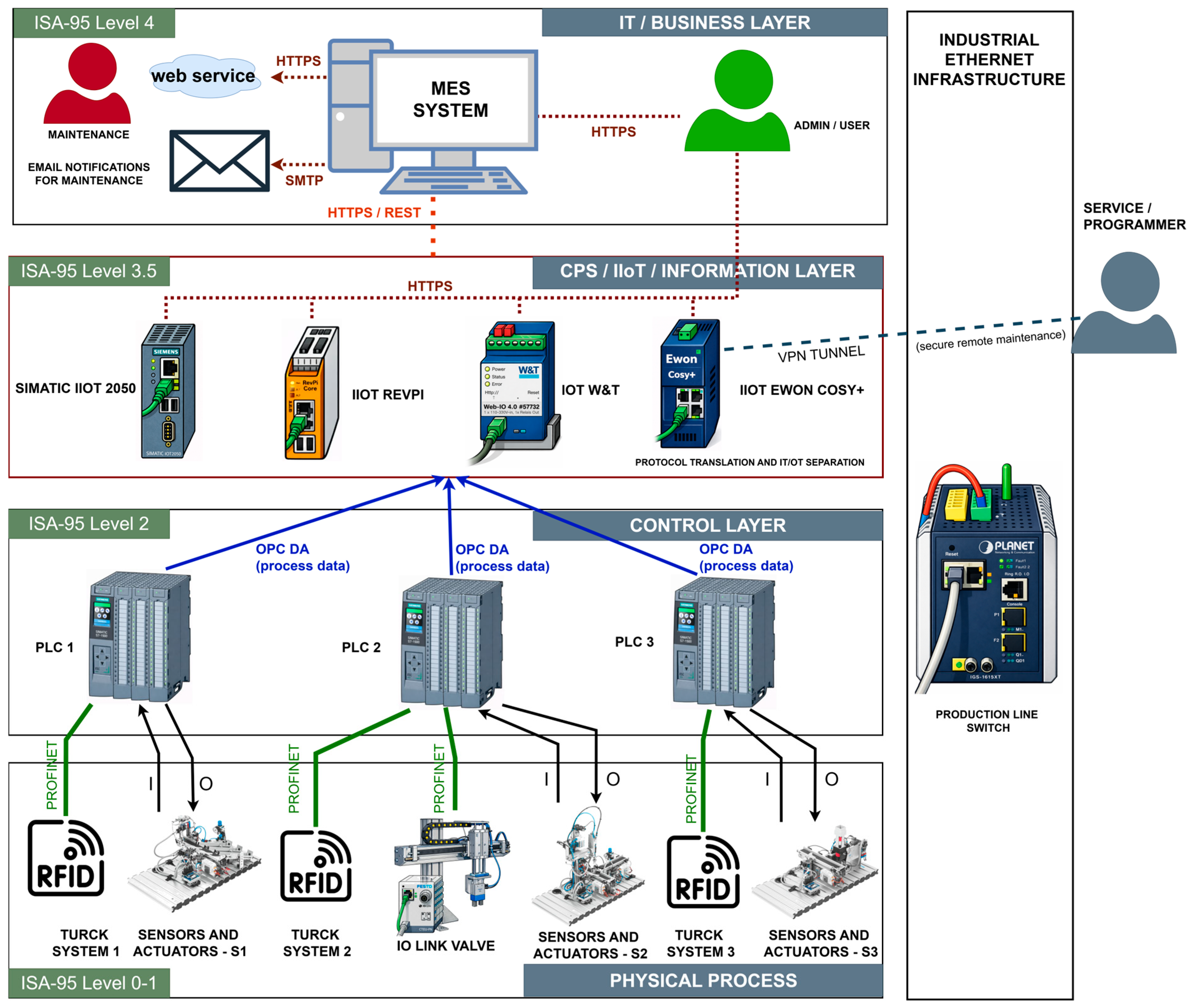
The IIoT devices used in the production line pose another security risk, particularly industrial computing, networking, and communication components such as Siemens SIMATIC IOT2050, Ewon Cosy+ gateway, RevPi Core industrial module, and Web-IO devices from Wiesemann & Theis (W&T), which have limited security mechanisms in their basic configuration, increasing their vulnerability to network attacks, as shown in Figure 4.
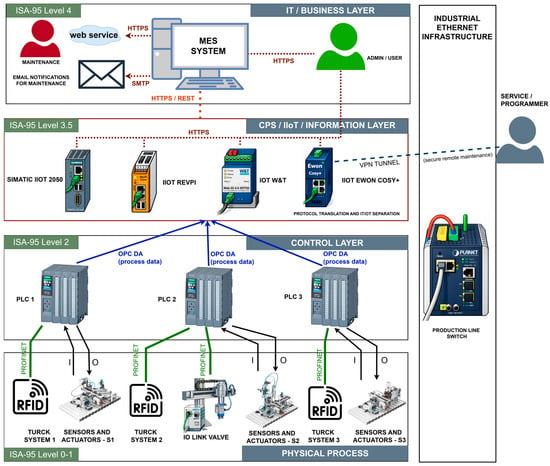
Figure 4.
Layered architecture of a cyber-physical manufacturing system based on the ISA-95 model, depicting the physical manufacturing process (levels 0–1), the PLC control layer with deterministic PROFINET communication (level 2), the CPS/IIoT information layer ensuring data collection, translation, and distribution (level 3.5), and the higher-level IT/MES layer for production planning, monitoring, and control (level 4), including remote access and network infrastructure. Although the presented architecture is structured according to the ISA-95 hierarchical model, it is compatible with the RAMI 4.0 framework, where the physical process corresponds to the Asset layer, the PLC control layer corresponds to the Integration and Communication layers, the CPS/IIoT layer corresponds to the Information layer, and the MES corresponds to the Functional and Business layers, especially in the context of vertical integration.
Although the architecture shown in Figure 4 is structured according to the ISA-95 hierarchical model, it is also compatible with the Industry 4.0 reference architecture model (RAMI 4.0). From the RAMI 4.0 perspective, the physical manufacturing process corresponds to the Asset layer, the PLC control layer corresponds to the Integration and Communication layers, the CPS/IIoT layer represents the Information layer, and the MES corresponds to the Functional and Business layers. Therefore, the presented implementation reflects practical vertical integration across RAMI 4.0 levels while maintaining the hierarchical structure of ISA-95.
To implement the test scenarios in the form of cyber attacks, the attacks were generated from a single personal computer (PC). This computer interfered with the communication of the network infrastructure consisting of IoT devices and a production line to verify its resistance to cyber attacks and identify potential vulnerabilities. The Kali Linux operating system, which is equipped with specialized tools designed to test the security of network systems, including the Hping3 tool, was used to operate the attack system.
The Hping3 tool enables the generation and analysis of network traffic using TCP, UDP, and ICMP protocols, with packet generation controlled via the command line. This tool is primarily intended for security analysts to test and scan network infrastructure, identify security weaknesses, and assess the level of vulnerability risk. Appropriate and effective security mechanisms aimed at reducing the risk of cyber threats are based on the identified deficiencies.
4.1. Scenarios
As part of the experiments, three experimental attack scenarios were implemented to verify the resilience of the production line and connected IIoT devices against DoS network attacks. All experiments were performed on a fully functional production line with integrated IIoT devices and without interfering with its normal operation. The internal and external LAN and WANs initiated the attacks, allowing the comparison of the impact of local and remote attacks on the availability of individual production system components to be compared.
Two basic types of attacks, namely a direct DDoS attack and an indirect DRDoS attack, were carried out as part of the experiments. In a direct DDoS attack, the attacker generated a high volume of network traffic directed directly at selected production line devices or PLC control units to significantly limit their ability to process network communications and control tasks.
In an indirect DRDoS attack, the attacker exploited IIoT devices to relay malicious network traffic without directly compromising them, sending packets to non-existent ports on these devices with a spoofed source IP address. The IIoT devices then generated error responses that were directed to the target devices on the production line without the knowledge of the compromised IIoT devices.
In individual scenarios, specific types of network attacks, including TCP SYN flood, TCP ACK flood, and ICMP-based reflective attacks, were used. Packet generation was set to the maximum possible speed with no time limit on the individual attack duration. The attacks continued until the compromised devices lost their ability to communicate on the network and ceased performing their control or production functions.
The KPIs recorded during individual experimental attack scenarios are summarized in Table 4. From the values shown, it can be observed that in direct DDoS attacks, the intensity of network traffic on target devices reached higher maximum values, approximately 18,000 packets per second, while the maximum values were lower in reflected DRDoS attacks, approximately 14,000 to 14,500 packets per second. This difference is due to the fact that in reflected attacks, malicious traffic is generated indirectly through intermediary IIoT devices, which naturally limits the maximum intensity of the generated attack compared to a direct flood of the target device. At the same time, it is clear from the KPI that the attacked devices experienced 100% CPU load (Peak CPU load = 100%) during the attacks, indicating that the main reason for the loss of communication is the exhaustion of the devices’ computing resources.

Table 4.
Summary of key performance indicators measured during all implemented attack scenarios.
During the attacks, the number of packets in the network gradually increased, which led to the overload of communication and computing resources of individual devices. Internal communication buffers, processor processing capacities, and resources dedicated to network communication were exhausted as malicious traffic volume increased. The devices stopped processing incoming packets after exceeding the available communication and computing resources, resulting in a sudden drop in the recorded number of packets per second and a complete loss of communication between individual devices. Different communication failure times between devices are caused by different computing capacities, communication mechanism implementation, and the overall ability of devices to process increased network load.
The results also show a sharp decline in recorded traffic after the compromised device lost its communication capability, as the device was no longer able to receive or process incoming packets, effectively eliminating the attack traffic from the monitored point of view. This confirms that the loss of communication was a direct result of the depletion of the attacked devices’ communication and computing resources.
The main objective of the attack scenarios implemented was to disrupt the production process by flooding the network communication of individual components of the production line, either through a direct attack on the target devices or an indirect attack mediated through IIoT devices, highlighting the real security risks arising from the integration of IoT technologies into industrial systems.
4.1.1. Scenario 1
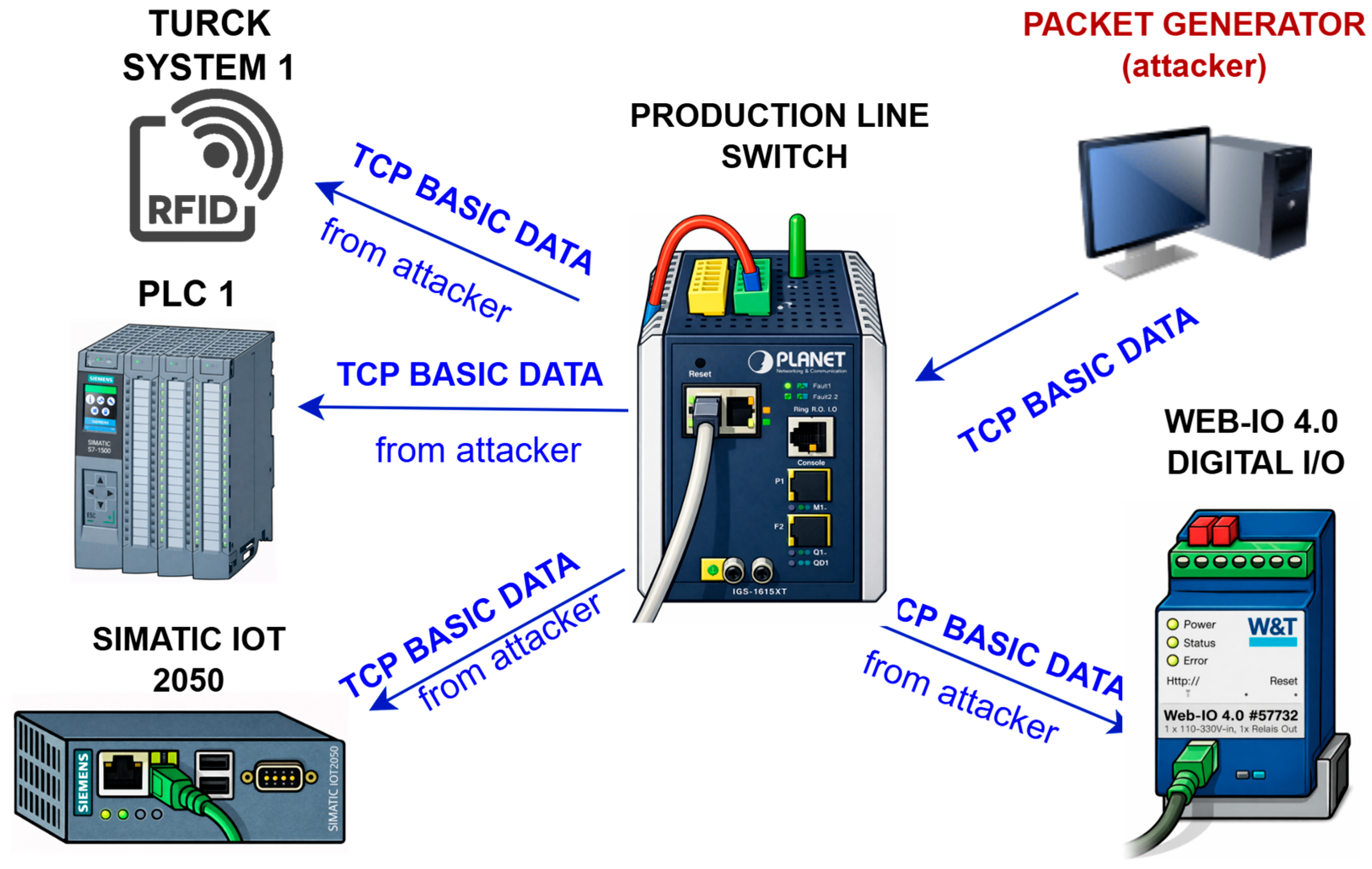
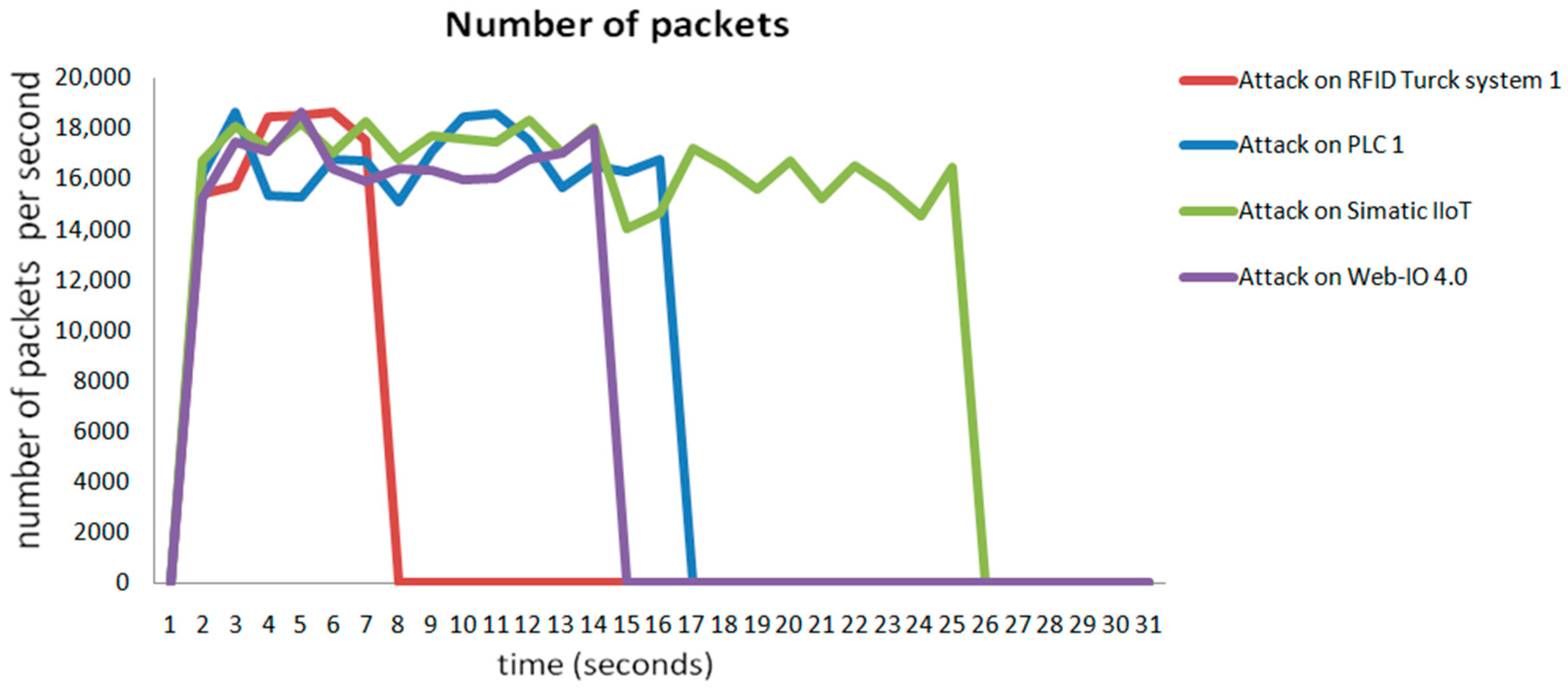
The first experimental scenario was implemented as a direct TCP SYN flood DDoS attack targeting production line devices and selected IIoT devices in the internal network infrastructure. The attacker generated a high number of network packets per second, simultaneously targeting multiple devices, as shown in Figure 5. During the attack, intense network traffic was recorded for each attacked device in the range of approximately 15,000–18,000 packets per second.
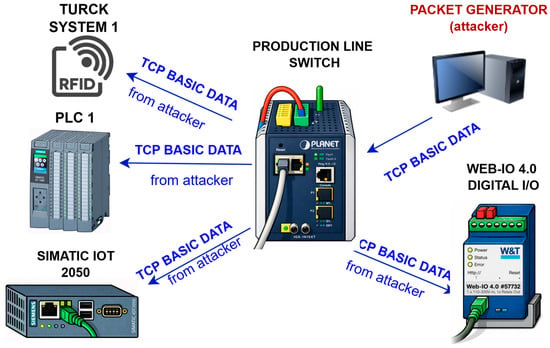
Figure 5.
Schematic of an experimentally implemented TCP SYN flood DDoS attack (Scenario 1). The attack is generated from an internal attack node (packet generator) and directed to selected production line components via an industrial network element, including the PLC control unit, Turck RFID subsystem, Siemens SIMATIC IOT2050 edge device, and Web-IO 4.0 module. The figure illustrates the routing of the generated TCP traffic and the attacked elements within the common industrial Ethernet infrastructure.
Figure 6 shows that individual devices responded to the attack with varying degrees of resilience. The Turck RFID system was the first to become inactive, ceasing to process network communication approximately 7 s after the start of the attack, as indicated by a sudden drop in the number of received packets to zero. Subsequently, approximately 16 s into the attack, the PLC 1 control unit stopped communicating, which led to an interruption in the control of the production line’s technological processes.
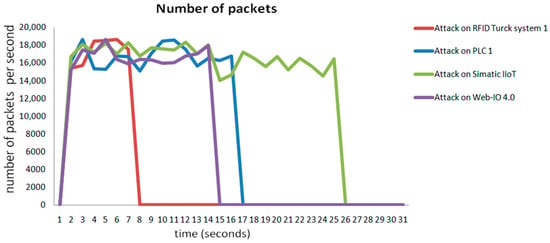
Figure 6.
Time course of network traffic intensity during an experimental TCP SYN flood DDoS attack (Scenario 1). The graph shows the number of packets per second recorded on individual attacked devices (RFID Turck system 1, PLC 1, Siemens SIMATIC IOT2050, and Web-IO 4.0). A sudden drop in the number of packets to zero indicates a loss of communication with the device (TTCL—Time to Communication Loss), with different outage times indicating different resilience of individual components to availability attacks.
The Web-IO 4.0 device showed slightly higher resistance, but even in this case, network communication failed after approximately 15 s of attack. The most resistant device in the tested scenario was the Siemens SIMATIC IOT2050, which retained its communication capability for approximately 25 s after the start of the attack, when it was completely knocked out of operation.
The results of the experiment clearly show the high effectiveness of a DDoS attack carried out on an internal network, as all tested devices were taken out of operation in less than 30 s. During the attack, the devices ceased to perform their production functions, and network communication with the control system and operator was lost. Restoring their functionality required manual intervention and restarting the devices, confirming the serious impact of this type of attack on the production system’s availability and reliability.
4.1.2. Scenario 2
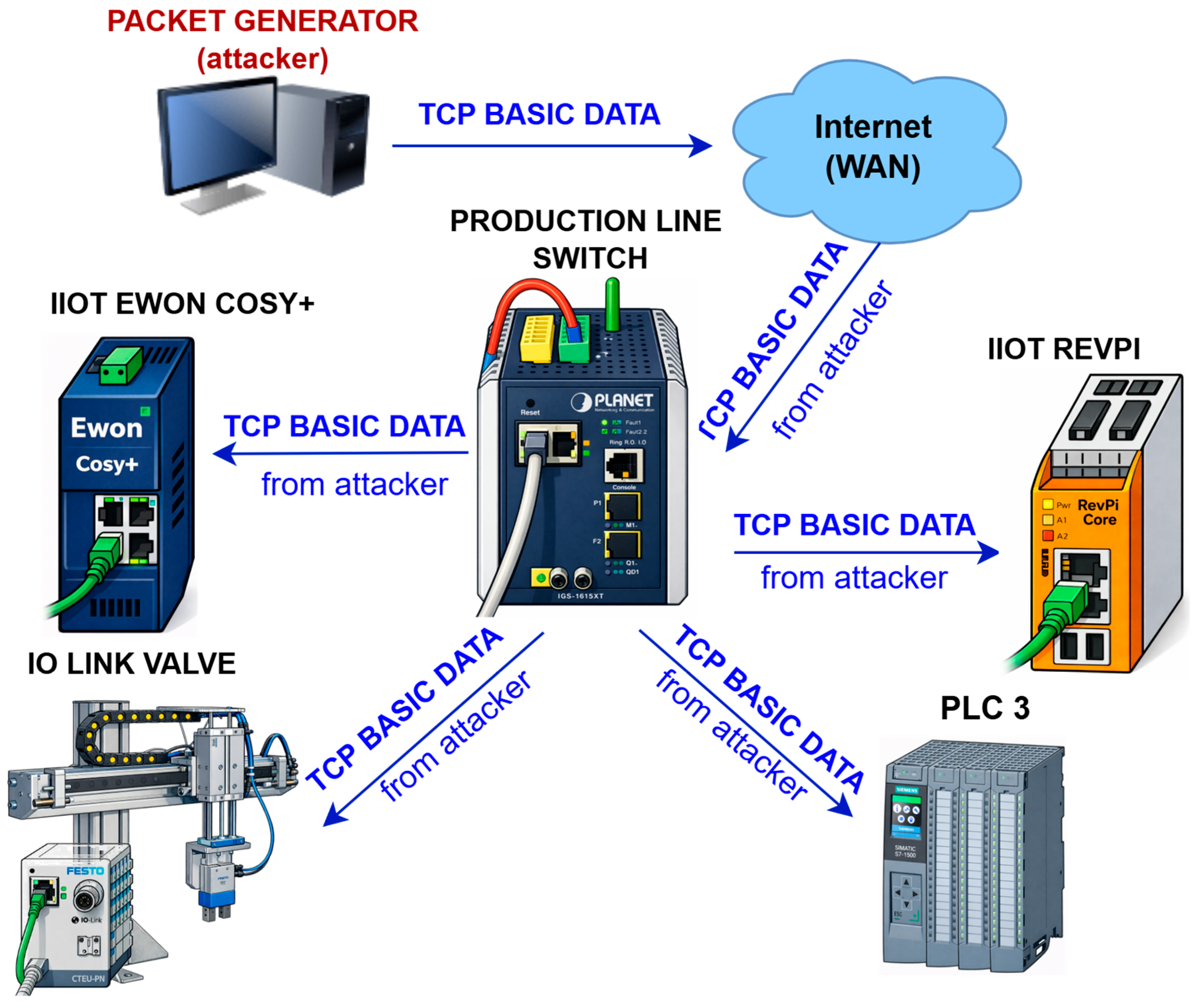
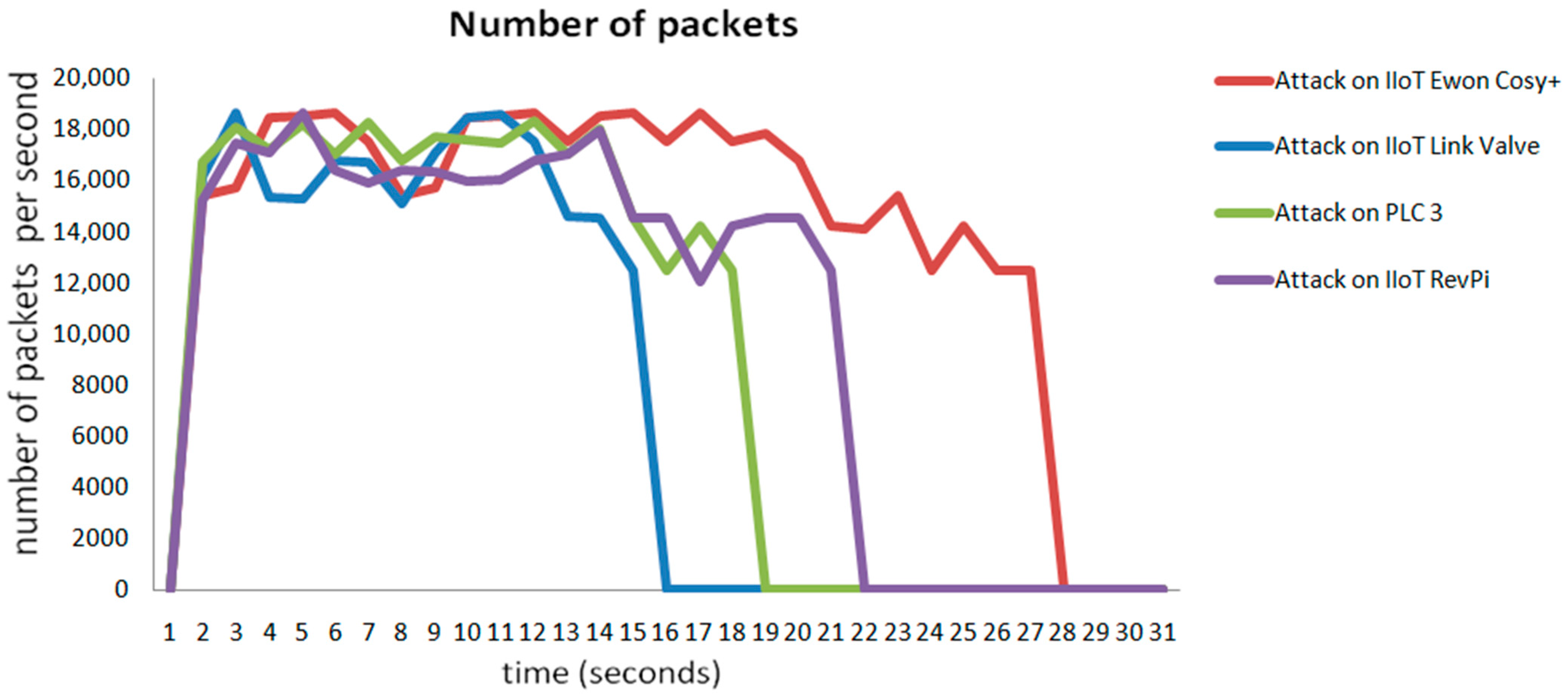
The second experimental scenario was implemented as a remote TCP ACK flood DDoS attack from an external WAN environment toward the production line’s internal network. The aim of the attack was to verify the resilience of selected IIoT devices to network communication overload during an external network attack. A high number of TCP ACK packets per second were generated during the attack, with traffic intensity ranging from approximately 15,000 to 19,000 packets per second (Figure 7).
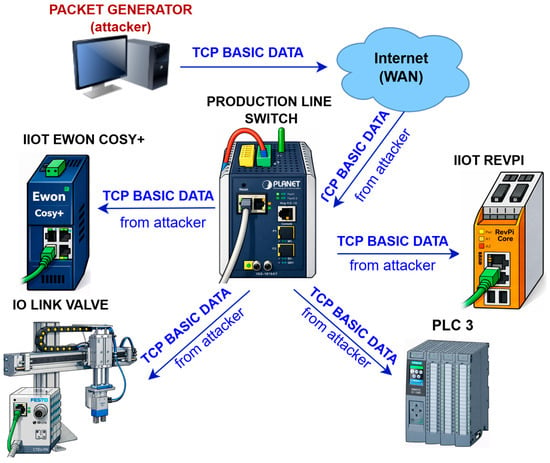
Figure 7.
Diagram of an experimentally implemented TCP ACK flood DDoS attack (Scenario 2), initiated from the WAN environment and directed at the Ewon Cosy+ IIoT gateway, Revolution Pi edge device, PLC, and IO-Link valve terminal via the production network. The figure illustrates the penetration of overwhelming TCP traffic from the IT layer into production line’s OT environment.
Figure 8 shows that individual devices responded differently to the TCP ACK flood attack. The first device to stop communicating was the IO-Link valve device, which became inactive approximately 15 s after the attack began, as indicated by a sudden drop in the number of received packets to zero. Approximately 18 s after the attack began, the PLC 3 control unit stopped communicating.
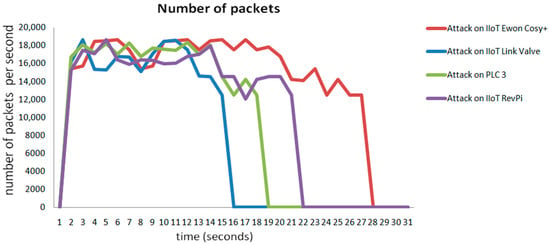
Figure 8.
Time course of network communication during an experimentally performed TCP ACK flood DDoS attack conducted from an external WAN environment (scenario 2), showing the number of packets per second recorded on the PLC control unit and selected IIoT devices on the production line.
The RevPi Core device showed a higher degree of resilience; however, even in this case, the network communication failed after approximately 21 s of attack. The most resilient device in this scenario was the Ewon Cosy+ IIoT router, which maintained its communication capability for approximately 28 s from the start of the attack before being taken out of service.
The results of the second experimental scenario confirm that even a remote TCP ACK flood DDoS attack launched from a WAN environment can have a significant negative impact on the availability of IIoT devices and production lines. All tested devices were taken out of service in less than 30 s, losing their ability to communicate with the higher-level control system and operator. Restoring device functionality requires manual intervention, highlighting the serious risk this type of attack poses to the operation of industrial systems connected to external networks.
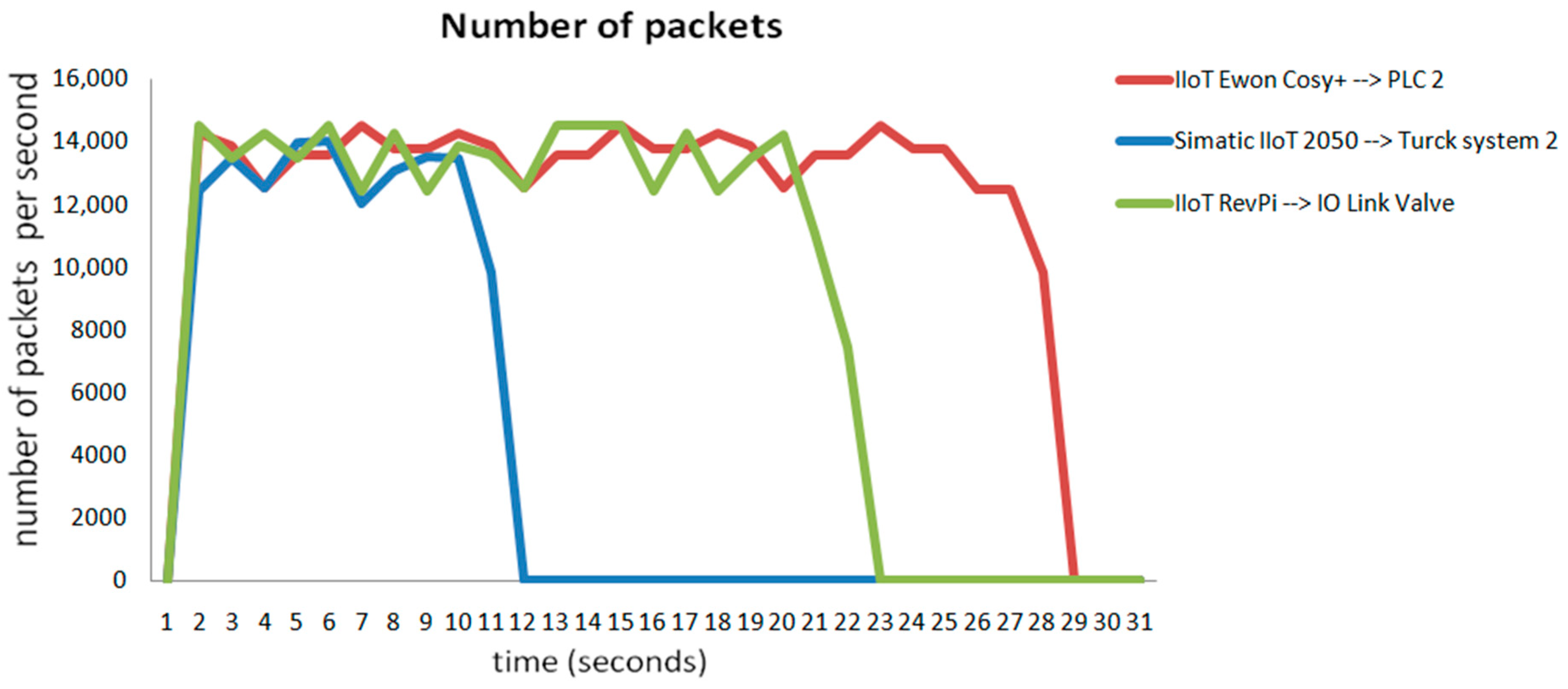
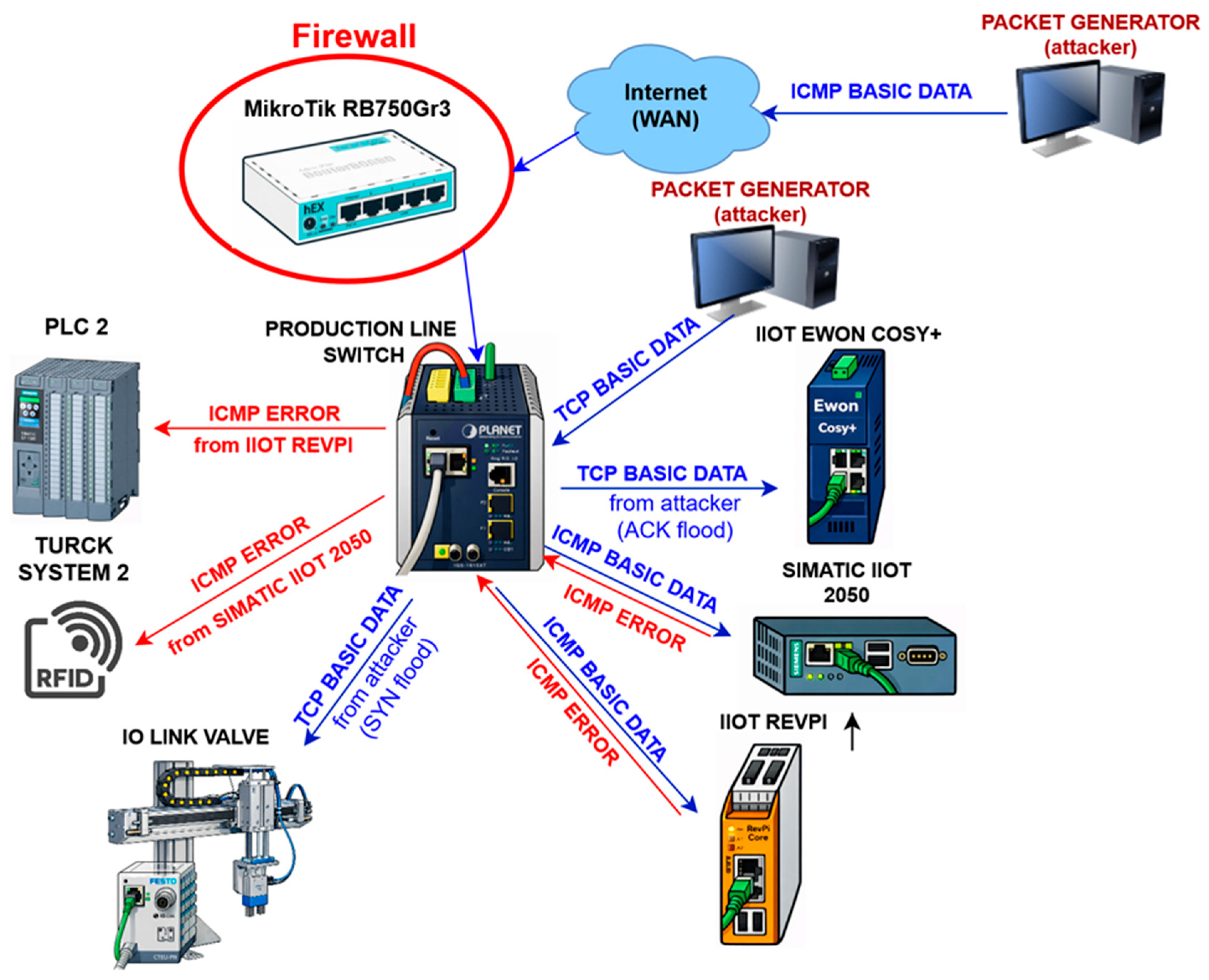
4.1.3. Scenario 3
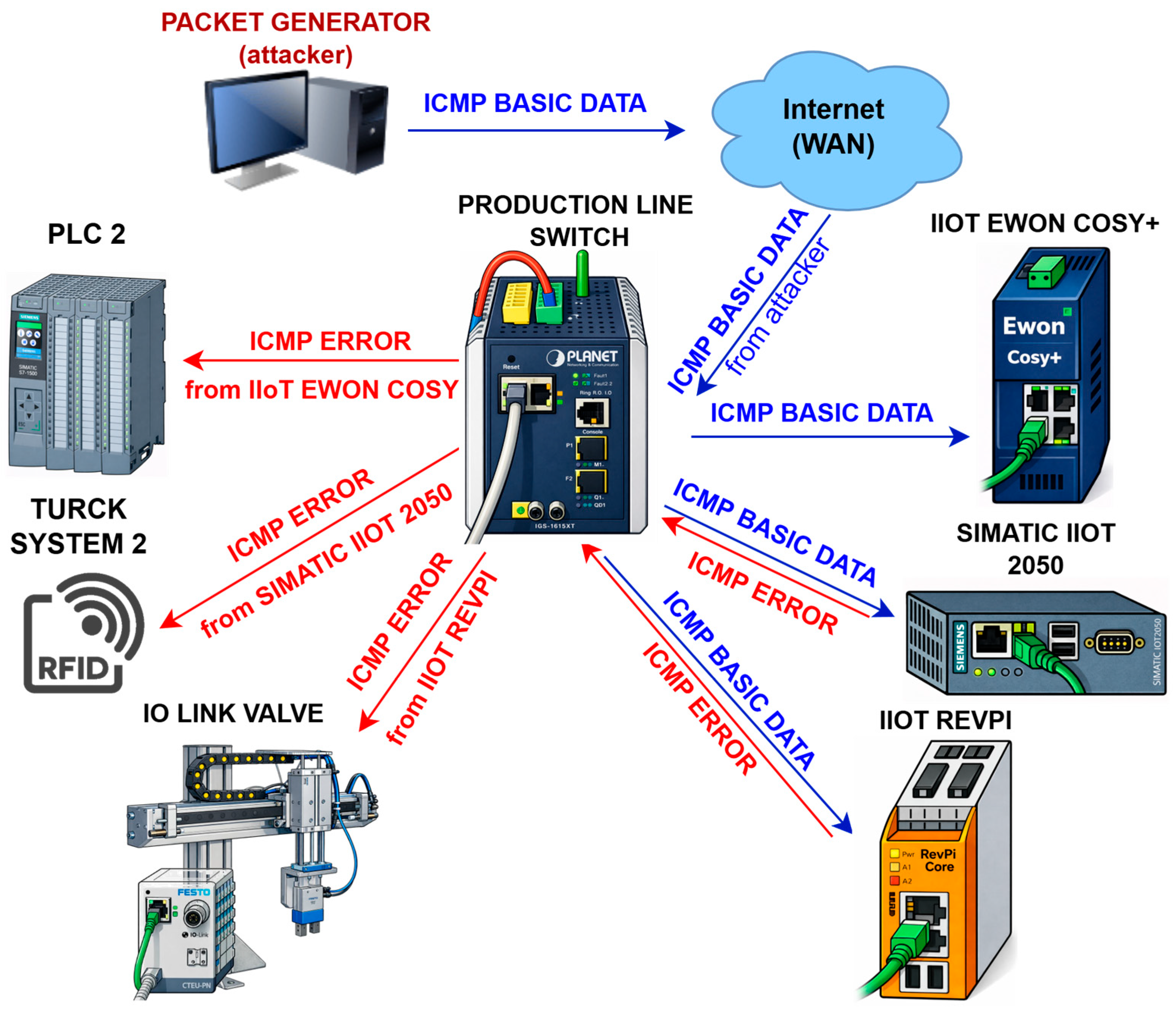
The third experimental scenario was implemented as a distributed reflective DoS (DRDoS) attack conducted from an external WAN environment, in which IIoT devices on the production line were exploited as attack reflectors without their knowledge. The attacker generated ICMP packets directed at IIoT devices on the internal network, with the target packets being sent to non-existent ports on these devices. The attacker spoofed the source IP address and corresponded to the IP address of the production line device.
Consequently, IIoT devices automatically generated ICMP error messages, which were then sent to the target devices’ spoofed IP address on the production line. As shown in the attack visualization in Figure 9, individual IIoT devices, specifically Ewon Cosy+, Siemens SIMATIC IOT2050, and RevPi Core, were exploited as intermediaries for reflective traffic directed at production components such as PLC 2, Turck RFID system, and IO-Link valve terminal.
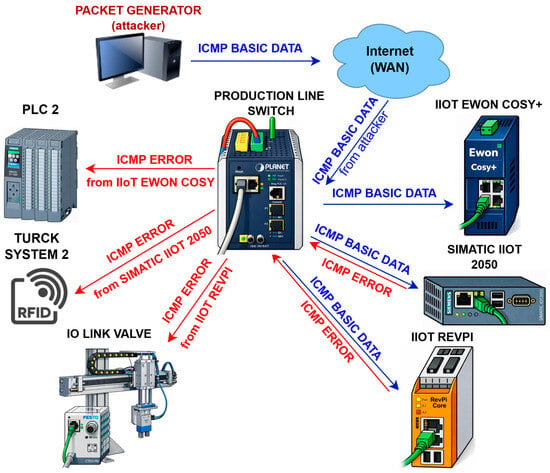
Figure 9.
Visualization of an experimentally implemented reflected ICMP flood-type DRDoS attack (Scenario 3) initiated from an external WAN environment. The attacker generates ICMP requests with a spoofed destination address, while selected IIoT devices (Siemens SIMATIC IOT2050, Revolution Pi, Ewon Cosy+) act as reflectors and generate ICMP error messages directed at the control and peripheral components of the production line (PLC, RFID subsystem, IO-Link valve terminal). The diagram illustrates the mechanism of traffic amplification and the spread of overwhelming communication across the production network’s IT and OT layers.
Figure 10 shows that the attack caused significant congestion of the target devices within a few seconds. The first to stop communicating was the Turck RFID system, which was hit by reflective ICMP traffic from the Siemens SIMATIC IOT2050 device, with complete communication failure occurring approximately 11 s after the start of the attack. Approximately 22 s into the attack, the IO-Link valve terminal stopped communicating, overwhelmed by ICMP error messages generated by the RevPi Core device.
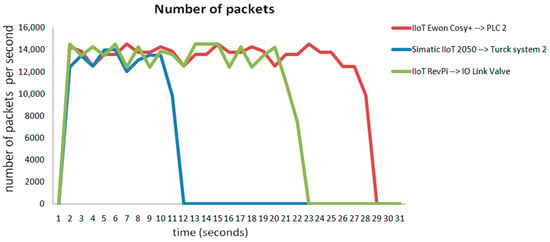
Figure 10.
Time course of network communication during an experimentally implemented reflected DRDoS attack based on ICMP communication (scenario 3), showing the number of packets per second generated by selected IIoT devices and directed at target components of the production line.
The highest level of resilience in this scenario was demonstrated by the PLC 2 control unit, which was the target of reflective traffic generated by the Ewon Cosy+ device. Even in this case, network communication was completely disrupted approximately 28 s after the start of the attack. All attacked devices ceased to perform their control and production functions and lost communication with the superior system.
The results of this experiment demonstrate the high effectiveness of a DRDoS attack carried out via ICMP reflection, in which the attacker can exploit legitimate IIoT devices to generate malicious traffic without directly compromising them. This type of traffic is particularly dangerous in industrial networks because it originates from internal security devices, making it significantly more difficult to detect and mitigate.
4.2. The Impact of DDoS and DRDoS Attacks on the Manufacturing Process
The previous chapters presented three experimental scenarios of cyber attacks carried out during the full operation of the production process. These attacks were specifically aimed at disrupting the continuity of the production line. The results of the individual scenarios clearly showed that the production components and other IIoT devices became uncontrollable and lost their ability to communicate within the network infrastructure.
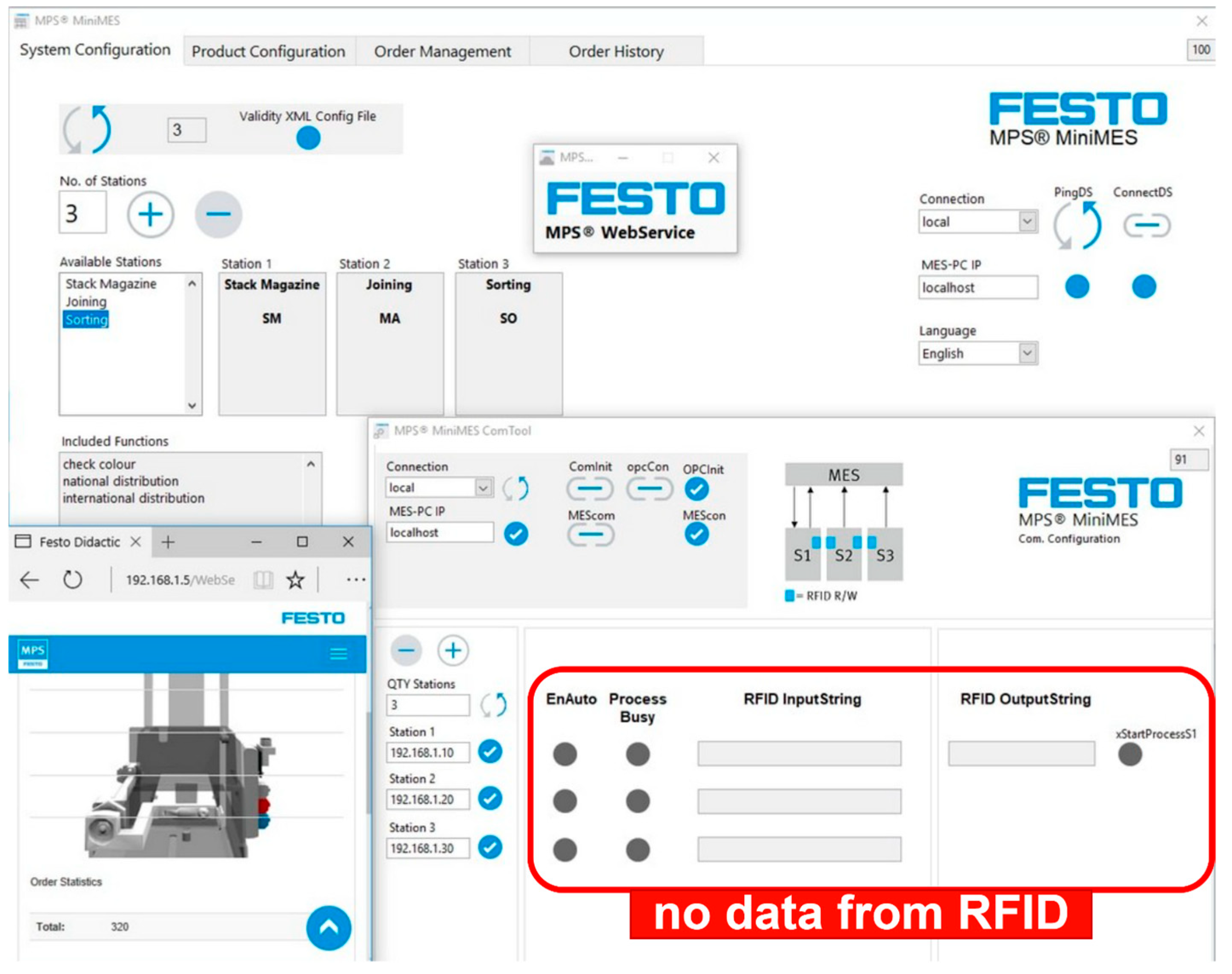
The failure of the RFID subsystem was the first problem encountered during the first experiment. The loss of communication between the Turck TBEN-S2-2RFID-4DXP modules and the PLC control units prevented the RFID read heads from reading data from the RFID transponders on the workpieces and prevented the PLC from further processing and transmitting this data to the higher-level MES. During the first experimental scenario, the first symptom was an RFID identification subsystem failure, which manifested itself as a loss of data exchange between the RFID modules and the higher-level MES system (Figure 11).
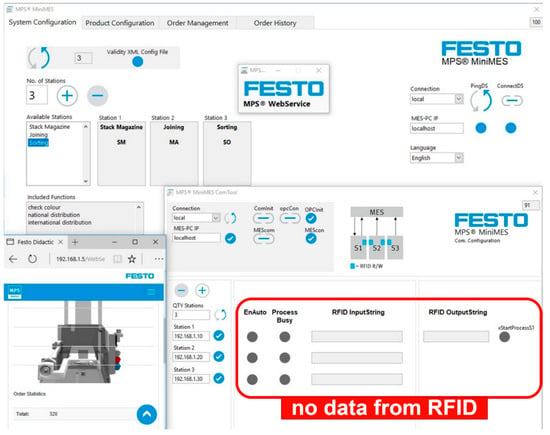
Figure 11.
Status of the superior MES during an experimental DDoS attack (scenario 1) documenting the failure of the RFID subsystem. The absence of RFID input and output data (RFID InputString, RFID OutputString) despite the active status of the production process is shown in the figure. Communication loss occurs between Turck TBEN-S2-2RFID-4DXP RFID modules and the PLC control units.
Despite this failure, the physical manufacturing process was initially continued because the local sequences controlling conveyors and technological operations at the PLC level were not immediately dependent on RFID data.
Therefore, the workpieces passed through the production line to the sorting station, where the fault became fully clear. The MES was unable to determine the correctness of the product due to missing or outdated identification data, and pieces that were physically correctly manufactured were automatically evaluated as defective and placed in the output bin for rejects. Since the identification and status data were not recorded in the MES system via the control layers, the digital representation of the product was lost and the continuity between the physical and cybernetic layers of the CPS was interrupted.
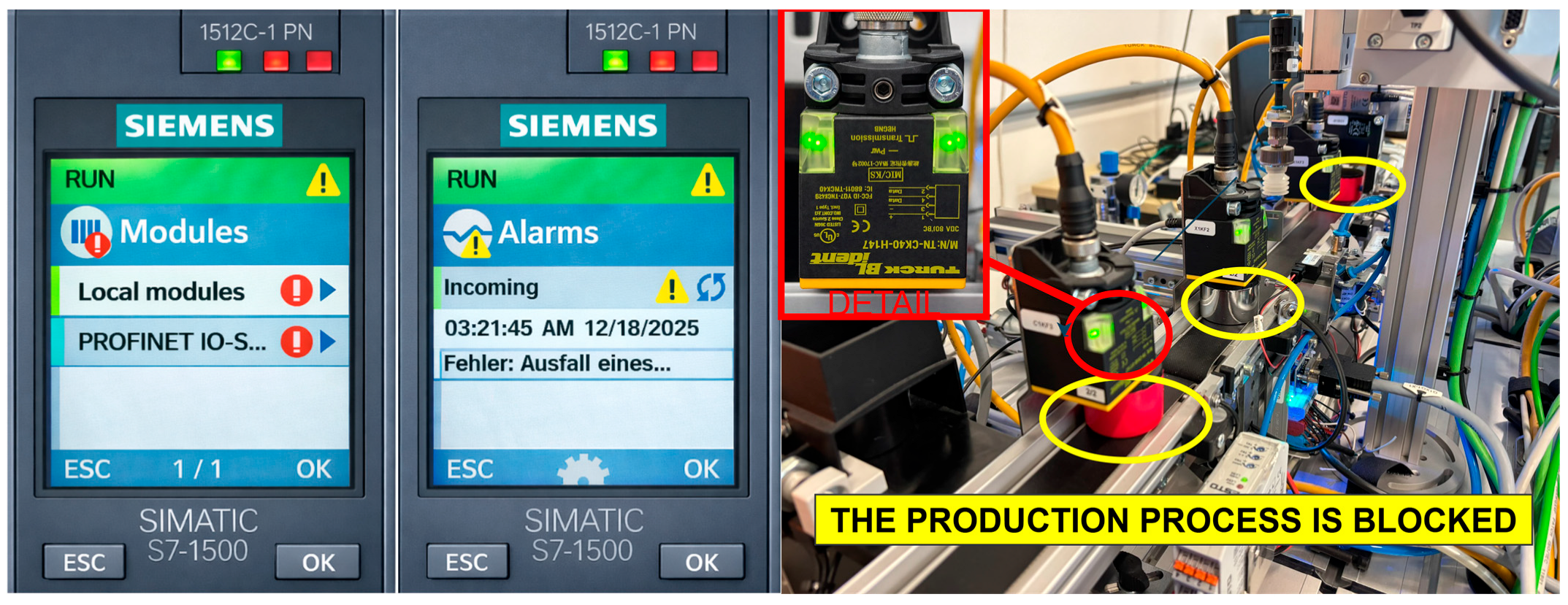
The second identified problem was a disruption in the PROFINET communication layer, which was directly observed in the Siemens SIMATIC S7-1512C-1 PN PLC control units.
The PLCs remained in the RUN mode, but with communication module failure signals and diagnostic messages indicating errors in the Local modules and PROFINET IO system categories. The control program continued to run without deterministic communication with the peripheral PROFINET IO devices. The loss of I/O device availability led to the PLC transitioning into a fault-safe state, interrupting control cycles, and physically stopping production, with workpieces remaining stuck on conveyors and requiring manual intervention to continue production.
The third problem manifested itself at the superior MES level, which did not explicitly record this failure. In the CPS’s cyber layer, the situation manifested itself only as a stagnation of production orders without clear information about the cause of the process interruption. The RFID InputString and RFID OutputString fields remained empty in the MES interface, while the status of the stations was indicated as “process busy.” Therefore, the MES system could not confirm the status of the product or decide on the next technological step, and the production history did not correctly record the events.
The loss of deterministic communication in the PROFINET communication layer meant that individual production stations were unable to correctly signal their status to higher-level or previous stations. Each station went into a fault or safe state and could not confirm its readiness to accept the next workpiece. Consequently, the material flow gradually halted, with workpieces remaining blocked at the conveyor ends of the individual stations, Figure 12.
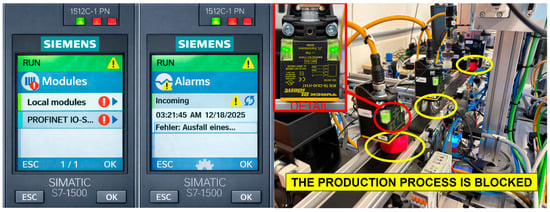
Figure 12.
Diagnostic status of the production line’s control and physical layers during an experimental DDoS attack (scenario 1). The left part of the image shows the Siemens SIMATIC S7-1512C-1 PN control unit’s diagnostics in RUN mode with signaled faults in the Local modules and PROFINET IO systems categories, indicating a loss of communication with peripheral PROFINET IO devices. The right part documents the physical blockage of the production process, in which the workpieces remain stopped at the conveyor ends because the individual production stations cannot signal their readiness to accept the next workpiece.
The fourth problem was the failure of the CPS support and monitoring layers. The IIoT monitoring element implemented by the Web-IO Ethernet module was designed to monitor the system status and support maintenance. However, the network connection was lost during the attack, making it impossible to verify whether the production line was powered or shut down. Simultaneously, the mechanism for email notifications about changes in system status failed, making diagnostics significantly more difficult.
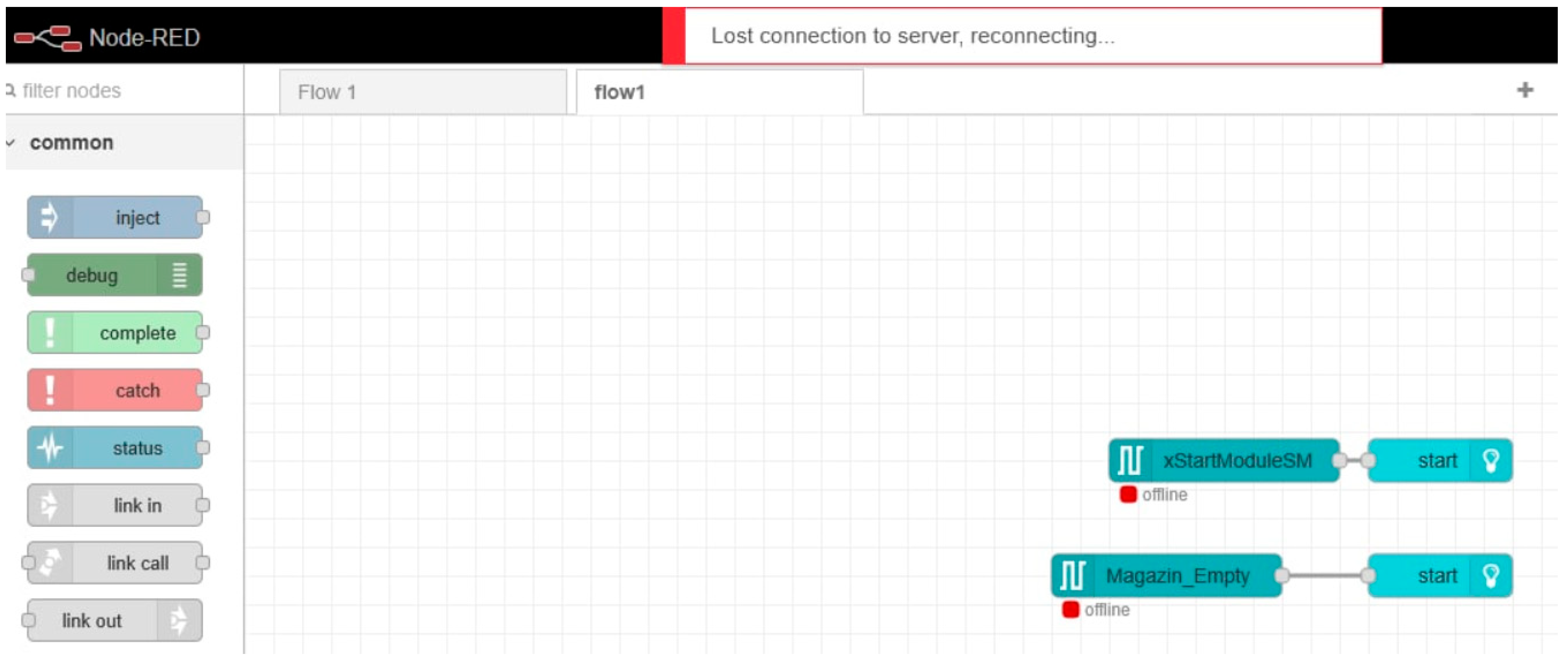
The IIoT layer using Siemens SIMATIC IOT2050 industrial edge devices was also disrupted. After the connection between the edge application in the Node-RED environment and the system was lost, the operating data remained offline, making it impossible to monitor process variables, analyze time series, and detect anomalies in real time. Thus, the attack affected not only the control of the production system but also its observability. Figure 13 illustrates the failure of the IIoT monitoring layer implemented using the Siemens SIMATIC IOT2050 edge device and the Node-RED environment.
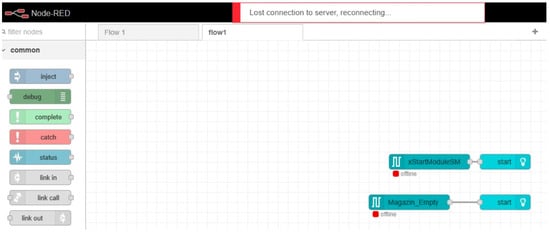
Figure 13.
Status of the IIoT supervision layer during an experimental DDoS attack (scenario 1). The figure shows the Node-RED application interface running on the Siemens SIMATIC IOT2050 edge device with a lost connection to the server (Lost connection to server, reconnecting…) and inactive data flows, indicating the unavailability of operational and status data from the production system and the inability to monitor them in real time.
These findings confirm that there was no immediate complete failure of the production system during the first attack scenario but rather its gradual degradation across multiple CPS layers. Although the system appeared to be partially functional, it could not ensure correct product identification, production continuity, or reliable fault diagnosis. From an operational point of view, the production line appeared to be “stuck” first, products were sorted incorrectly, workpieces accumulated, and the production flow stopped. The MES did not consider this a faulty condition.
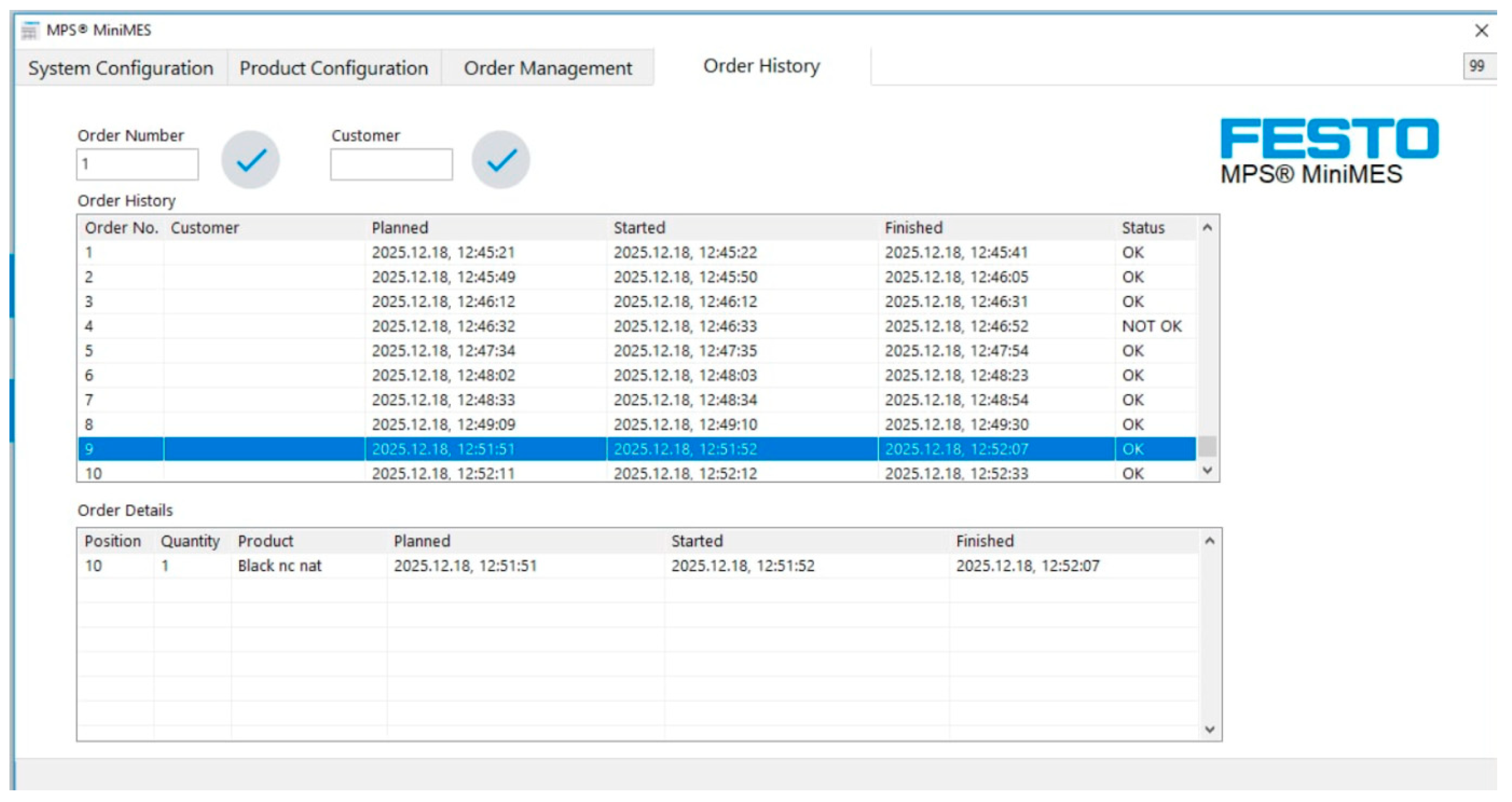
A particularly serious phenomenon was the systematic occurrence of products marked as NOT OK, even though the physical manufacturing process was running correctly. Physically correct products were rejected solely because of a failure in the CPS identification and communication layer, which led to a false decline in quality and a deterioration in performance indicators such as OEE. This scenario highlights a dangerous aspect of cyber attacks on manufacturing CPSs—the creation of false confidence in a system’s decision-making that can consistently provide incorrect information about the production status and quality.
After the attack subsided, it was necessary to restore control manually, including restarting the PLC. However, the previous failure of the RFID subsystem disrupted the consistency of production data, making it impossible to resume the original status of work-in-progress products. In some cases, manually moving products between stations or restarting production from the point of failure was necessary, which led to the loss of work-in-progress items and an interruption in production continuity. Figure 14 illustrates the impact of the failure of the CPS identification and communication layer on the production quality evaluation in the higher-level MES.
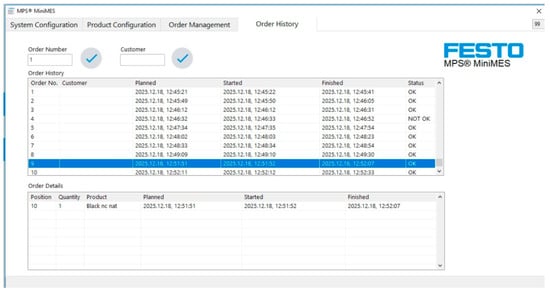
Figure 14.
The status of the superior MES during an experimental DDoS attack (scenario 1), documenting the systematic occurrence of products marked as NOT OK despite the production process being physically correct. The figure shows the discrepancy between the actual production status and the digital representation of products due to the failure of the CPS identification and communication layer, leading to incorrect quality assessment and distortion of production indicators.
During the second experimental scenario, several production system components gradually failed. The first problem was the failure of the IO-Link valve device in the connection station. The loss of communication with the valve terminal meant that the pneumatic operation of placing the cap was not physically performed, even though the production line’s control cycle continued without interruption. This manifested as the IO device’s unavailability at the PLC level. Figure 15 shows the consequence of the failure of the IO-Link valve device in the connection station, leading to the assembly operation not being executed despite the continuous control cycle.

Figure 15.
The physical condition of the product during the experimental DDoS attack (scenario 2), documenting the failure to perform the pneumatic operation of deploying the cap in the connection station. The image shows the workpiece without the cap attached due to a communication loss between the PLC control unit and the IO-Link valve terminal, with the control cycle of the production line continuing without immediate detection of this fault at the CPS control or information layer.
The absence of the assembly operation was not detected because neither the control system nor the superior MES was equipped with a feedback mechanism from the physical process, for example via sensors or a camera system. Therefore, the product without the cap was forwarded to the sorting station of the production line and incorrectly evaluated by the superior system as a compliant piece. At this point, a hidden production quality defect occurred in which the system declared the product to be correctly manufactured, even though the technological operation had not been physically performed.
The second problem was the failure of the PLC control unit responsible for one of the production line stations. The loss of deterministic communication caused the PLC to enter fault mode and interrupt the technological cycle. At this point, the production flow physically stopped, and the workpiece remained blocked at the station, turning a hidden quality defect into an obvious operational problem with a direct impact on production availability.
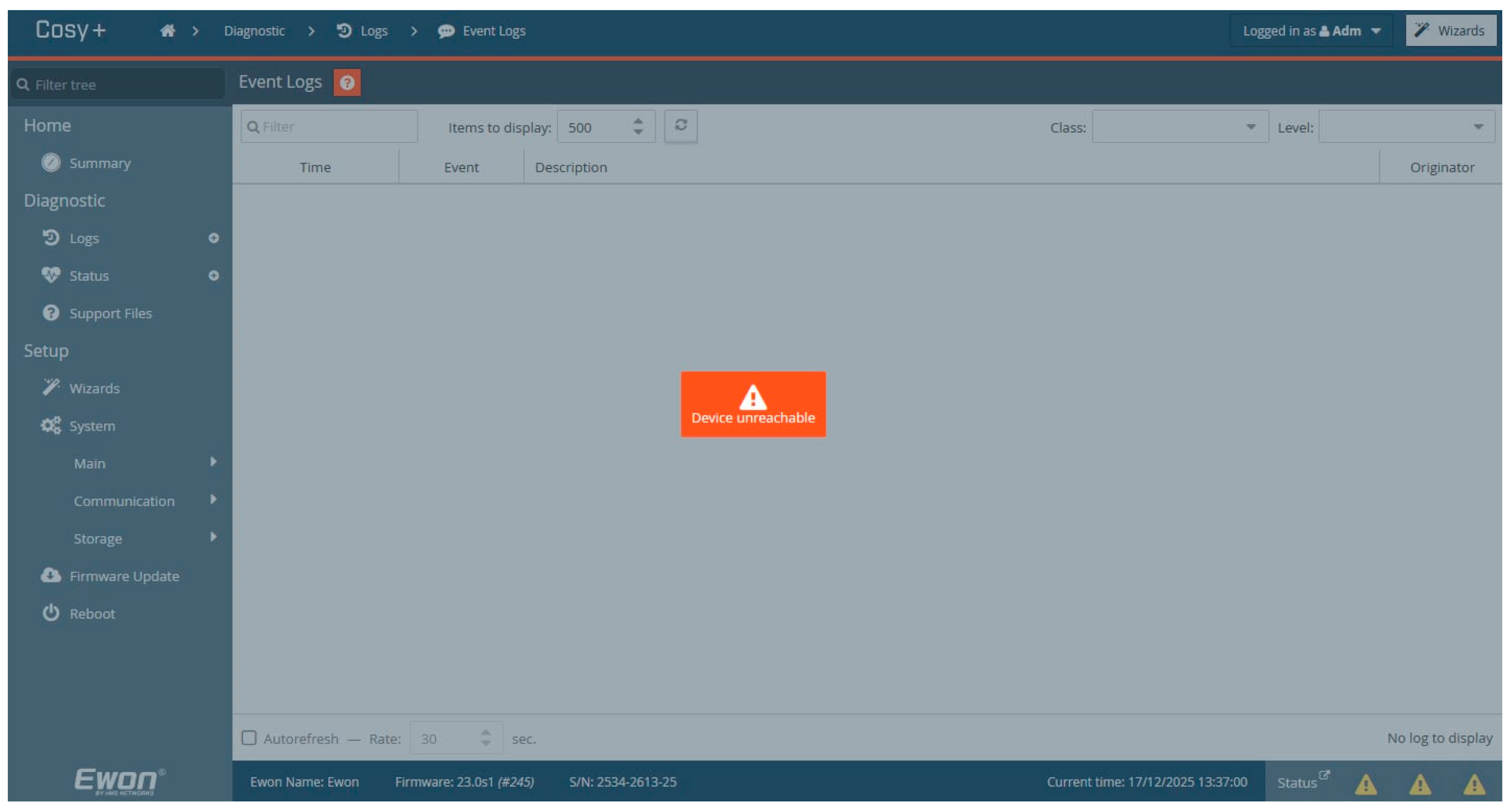
The third problem was the failure of the RevPi Core IIoT edge device, which collects and processes operational data in the Node-RED environment. The loss of communication caused the visualization and analysis layer to go offline, making it impossible to monitor the production system’s current process and status variables. Thus, the operational data ceased to reflect the actual state of production, which significantly reduced the observability of CPS.
The fourth problem was the loss of remote access to the production system via the EWON Cosy+ IIoT router. Consequently, it was not possible to reliably access the PLC control units, perform diagnostics, or intervene in the control system. From an operational and maintenance perspective, the system appeared to be unavailable. The status of the EWON Cosy+ IIoT device and the unavailability of remote service access during the experimental attack are shown in Figure 16.
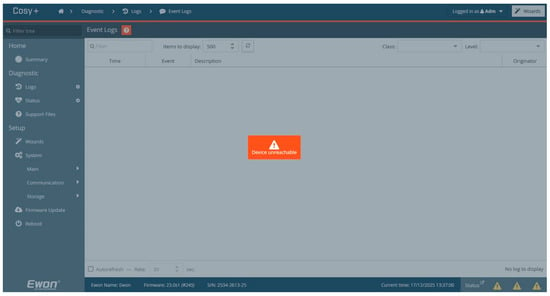
Figure 16.
Status of the EWON Cosy+ IIoT router during an experimental DDoS attack (scenario 2), documenting the loss of remote access to the production system. The image shows the device diagnostics interface with the message “Device unreachable,” indicating the unavailability of the VPN connection and the inability to perform remote diagnostics, monitoring, and service intervention in the PLC control units.
The same chain of operational problems as in the previous scenarios reappeared on the production line during the third experimental scenario, but with a different communication disruption source. First, the RFID subsystem failed, making it impossible to identify products or update their digital representation in the MES. The physical production process was initially continued without any obvious disruption.
Communication failure with the IO-Link valve terminal at the connection station. The superior MES sent a control instruction via the PLC to perform the assembly operation; however, due to communication failure, this instruction was not physically executed. The MES system did not have a feedback mechanism to detect failure to perform the operation, and the production process continued.
The PLC control unit failed only in the final stage, causing the production process to physically stop and the workpieces to become stuck on the conveyors. The production flow was completely interrupted, and manual intervention was required to resume production.
5. Discussion
Based on the implemented attack scenarios and the subsequent analysis of their impacts, it was possible to identify the behavior of the production line in terms of network communication resilience, as well as potential threats and disruptions to the production process that may arise due to the integration of IIoT devices into industrial infrastructure. The identified shortcomings indicate the need to implement additional security measures to increase the availability, reliability, and security of production line operations. Therefore, the following chapter focuses on the design and implementation of security rules and protective mechanisms to limit the effects of network attacks and reduce the disruption risk to the production process.
5.1. Proposed Solutions to Mitigate the Effects of DDoS and DRDoS Attacks
Implementing extensive changes to network infrastructure in long-term production systems and stable production lines is often technically, organizationally, and economically challenging. Production equipment and control systems are designed for continuous operation, and significant network architecture interventions can lead to unwanted downtime or disruption of technological processes. Therefore, security measures that increase the level of protection with minimal intervention in the existing infrastructure must be prioritized.
One option is to directly configure a software firewall on the network or computing devices (e.g., using the iptables tool). However, such a solution typically increases the demands on management, maintenance, and staff qualifications and may entail additional operating costs or risks associated with production system interference.
Therefore, a more suitable solution would be to supplement the existing infrastructure with a separate MikroTik RB750Gr3 network device, which allows the implementation of advanced security rules at the network communication level without directly interfering with production components. This approach represents an effective compromise between security level, costs, and production continuity while enabling the secure integration of IIoT devices into the industrial environment.
The proposed security architecture assumes that the production infrastructure operates on a long-term basis and that a fundamental reconstruction or replacement of existing equipment is not feasible. Therefore, the proposed solution is designed as a minimally invasive intervention in the existing network architecture to increase cybersecurity while maintaining the continuity of the production process. The architecture also reflects the findings from experimental attack scenarios, which demonstrated the high vulnerability of the production line and connected IIoT devices to DDoS and DRDoS attacks.
The MikroTik RB750Gr3 device acts as a perimeter security element at the interface between the internal production network and the external WAN or IT infrastructure (Figure 17). This device routed all network communication to and from the production network, enabling centralized control and traffic filtering without interfering with the configuration of individual production components, such as PLCs, I/O modules, or sensors. This location also allows for the logical separation of critical production equipment from IIoT elements used for data collection, remote monitoring, or integration with higher-level information systems.
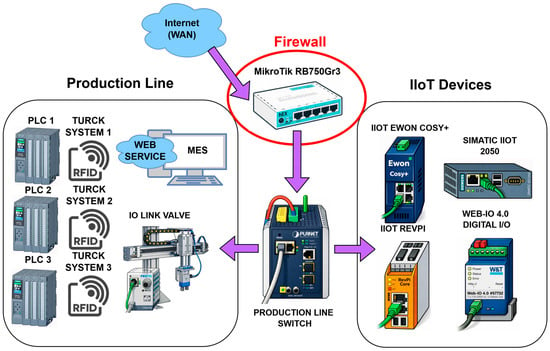
Figure 17.
The MikroTik RB750Gr3 device is located at the interface between the internal production network and the external WAN or IT infrastructure, where it acts as a perimeter security element. This device routed all network communication to and from the production network, enabling centralized control and traffic filtering without interfering with the configuration of individual production components, such as PLCs, I/O modules, or sensors. This placement also allows for the logical separation of critical production equipment from IIoT devices used for data collection, remote monitoring, or integration with higher-level information systems.
In terms of functionality, the MikroTik RB750Gr3 provides network communication filtering through a stateful firewall, restriction of unwanted traffic types, and protection against network congestion using flow control and packet limiting mechanisms. These mechanisms reduce the impact of TCP SYN flood, TCP ACK flood, and ICMP-based DRDoS attacks, which were analyzed in previous chapters. Simultaneously, security rules can be used to precisely define the permitted communication relationships between individual parts of the infrastructure, thereby reducing the risk of lateral spread of attacks within the production network.
5.2. Configuring Firewall Rules on a MikroTik RB750Gr3 Device
Table 5 presents the configuration of firewall rules implemented on the MikroTik RB750Gr3 device to increase the resilience of the production infrastructure against TCP SYN flood, TCP ACK flood, and ICMP-based DRDoS attacks. The rules are applied in the forward chain and focus on protecting communication between the OT network and the external WAN environment, as well as limiting unwanted internal traffic.

Table 5.
Overview of firewall rules implemented in MikroTik RouterOS on the RB750Gr3 device to protect the production network against TCP SYN flood, TCP ACK flood, and ICMP-based DRDoS attacks.
The configuration allows existing and related connections and immediately discards invalid packets, ensuring the integrity of legitimate communication while reducing the load on the device. Protection against TCP SYN and TCP ACK floods are protected by checking the TCP connection status and using a rate-limiting mechanism to limit the number of new SYN packets. Packets that do not meet these conditions are blocked.
Protect against DRDoS attacks by limiting ICMP traffic. ICMP packet processing is time-limited, minimizing the risk of flooding target devices with reflective communication generated by compromised IIoT elements. Excessive traffic is automatically blocked.
The configuration also includes rules for detecting and blocking spoofed source IP addresses from external environments, especially from private and link-local ranges, thereby reducing the risk of reflective and spoofing attacks.
The proposed solution represents a cost-effective way to increase production line cybersecurity and connected IIoT devices without interfering with existing production components. It is particularly suitable for long-term industrial infrastructures where maintaining production continuity is a priority.
Figure 18 shows the implementation of the firewall rules listed in Table 5 on a MikroTik RB750Gr3 device deployed in the production line network infrastructure during implementation and verification experiments.
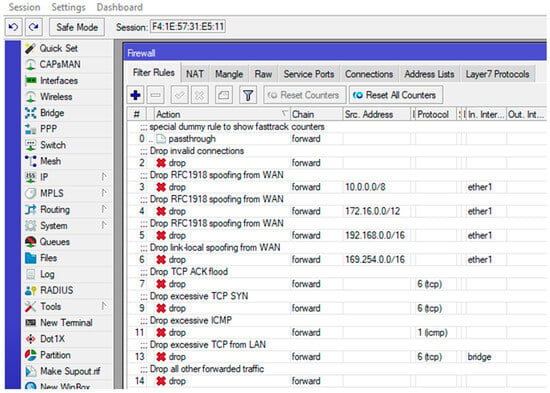
Figure 18.
Implemented firewall rules in the MikroTik RouterOS environment on the RB750Gr3 device. The rules applied in the forward chain are displayed to limit and block TCP SYN flood, TCP ACK flood, and ICMP flood (DRDoS) attacks, as well as rules for eliminating invalid connections and spoofed traffic (RFC1918 and link-local addresses) coming from the WAN environment. The configuration documents the filtering and segmentation mechanism application in the experimental network architecture.
5.3. Verification of the Proposed Configuration—Verification Scenario
The verification scenario was designed to comprehensively assess the effectiveness of implemented security measures in a production infrastructure environment with an active MikroTik RB750Gr3 firewall. As shown in Figure 19, the scenario involved the simultaneous execution of two direct DDoS attacks and two reflective DRDoS attacks to verify the ability of the proposed solution to protect the production line from various forms of network threats under conditions close to real-world operation.
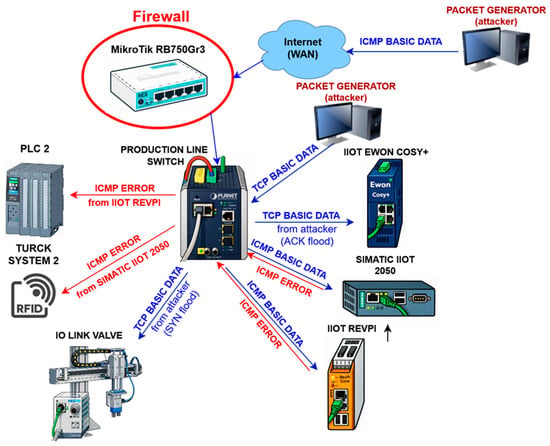
Figure 19.
Visual illustration of the verification scenario for the proposed security solution, showing the current implementation of direct TCP SYN flood and TCP ACK flood attacks and reflected ICMP-based DRDoS attacks directed at selected components of the production line and IIoT devices through the MikroTik RB750Gr3 perimeter firewall.
Direct attacks were conducted as a TCP ACK flood directed from an external WAN environment to the Ewon Cosy+ device and as a TCP SYN flood initiated from the local network against the IO-Link valve terminal. These scenarios simulate situations in which an attacker deliberately floods production components from an external environment or through a compromised device in the internal infrastructure.
Simultaneously, two reflective DRDoS attacks based on ICMP communication were conducted, in which Siemens SIMATIC IOT2050 and RevPi Core devices were exploited to generate ICMP error messages directed at target infrastructure elements, specifically the Turck RFID system and the PLC 2 control unit.
No complete network communication failure occurred on any of the tested devices during the execution of all four attacks (Figure 20). After an initial increase in traffic caused by initiating attacks, communication stabilized at a significantly lower level due to the firewall rules and traffic restriction mechanisms. The number of packets per second remained within the controlled range throughout the test, with only slight fluctuations recorded and no sudden drop to zero values.
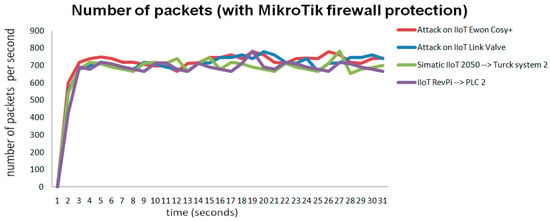
Figure 20.
Time course of network communication during the verification scenario with active protection by the MikroTik RB750Gr3 firewall, showing the number of packets per second recorded on selected target devices during the simultaneous execution of direct DDoS attacks of the TCP SYN flood and TCP ACK flood types and reflected ICMP-based DRDoS attacks.
This process confirms that harmful traffic is effectively filtered or restricted before reaching critical production components, thereby preventing communication and computing resource overload. The results also show that the implemented protection mechanisms could maintain the communication stability and operational continuity of the production line even during an ongoing attack. Thus, Figure 20 documents the practical effectiveness of the proposed security architecture in real operating conditions.
The results of the verification scenario confirm that the proposed security measures can effectively mitigate the impact of not only direct DDoS attacks but also reflective DRDoS attacks, in which malicious traffic originates from legitimate IIoT devices within the infrastructure. Maintaining the availability of the production line and the functionality of control components in all tested scenarios demonstrates that a combination of perimeter protection and internal network security rules is an appropriate approach to securing long-term industrial systems with integrated IIoT elements.
The proposed solution offers several practical advantages, including low financial costs, rapid implementation, and no interference with existing production equipment. The architecture also allows for the gradual integration of IIoT devices without significantly increasing the risk to the production process, making it ideal for use in industrial environments with limited modernization options.
5.4. Limitations and Generalization of Results
The proposed approach has some limitations. Protection is primarily implemented at the network boundary, which means that attacks generated directly from the internal network or from a compromised device within the production infrastructure may not be eliminated. The solution’s effectiveness also depends on the correct configuration of security rules and regular device management; incorrect settings can restrict legitimate communication or reduce the level of protection.
Security levels can also be increased by implementing a demilitarized zone (DMZ) between the production and external networks or using advanced network segmentation. Such measures can further reduce the exposure of production components to external threats without the need for major interventions in the existing infrastructure.
Experimental verification of the FESTO MPS 203 production line, which represents a modular, didactically oriented industrial environment, was experimentally verified. This is not a fully integrated commercial production system in continuous operation, which is a limitation of this study. In the case of large-capacity systems, the scope of production, data traffic volume, and economic consequences of outages may vary.
However, in practice, the experimental testing of availability attacks directly on commercial production lines is significantly limited due to economic and operational risks. However, the infrastructure used contained standard industrial components (PLC Siemens SIMATIC S7-1512C-1 PN, PROFINET communication, OPC interfaces, RFID system, and IIoT devices) that are commonly deployed in real production systems. Therefore, the experimental platform represents a relevant model of the industrial environment in terms of communication principles, deterministic control, and network architecture.
Although quantitative parameters (e.g., time to communication degradation) may vary in larger systems due to higher hardware performance or redundant architecture, the network congestion, computational resource depletion, and deterministic communication disruption mechanisms remain fundamentally the same. Therefore, the identified vulnerabilities are transferable to real production systems; the difference lies primarily in the scope of failure and economic impact.
Compared to protocol-oriented security mechanisms, including solutions using deep packet inspection (DPI) for industrial protocols such as PROFINET, the proposed firewall solution represents a cost-effective and minimally invasive risk mitigation strategy. The deployment of DPI mechanisms can provide more detailed control at the application layer, but is typically associated with higher costs, more complex configuration, and potential performance impact in real-time environments.
Therefore, the combination of perimeter firewall protection with future expansion to include protocol-oriented monitoring represents a promising direction for increasing the security of industrial networks.
6. Conclusions
This article analyzes the impact of DDoS and DRDoS attacks on a production line extended with IIoT devices in a real industrial environment. Experimental scenarios conducted from both internal and external networks demonstrated the high vulnerability of production components and IIoT devices to network attacks, leading to rapid communication loss and production process interruption in the absence of protective mechanisms. Reflected DRDoS attacks, in which legitimate IIoT devices were misused to generate malicious network traffic, proved particularly dangerous.
Based on the identified shortcomings, a security solution based on the MikroTik RB750Gr3 device was designed and implemented, which respects the limitations of the long-term operating production infrastructure. The verification of the proposed solution through repeated attacks confirmed that the implemented firewall rules can effectively mitigate the effects of both direct and reflected attacks while maintaining the production line’s network communication availability and stability.
The results of this study highlight the importance of combining network access protection and internal network security measures in an Industry 4.0 environment, confirming that even low-cost and minimally invasive solutions can significantly contribute to increasing the resilience of industrial systems against network threats.
Simultaneously, other architectural enhancements, such as the introduction of a demilitarized zone (DMZ) between industrial and external networks, together with the implementation of advanced network segmentation mechanisms, can further reduce the exposure of production components to external threats and represent effective complementary protective measures
The implementation of advanced network segmentation mechanisms can further reduce the exposure of production components to external threats and represent effective complementary protective measures that may be the subject of further research.
Future research will also focus on the systematic collection and processing of data from the production line’s network and control communications during normal operation and controlled cyber attacks to create a representative data set for the security analysis of industrial cyber-physical systems. The dataset will be made available as a reference dataset for further research in the field of industrial CPS security.
The data obtained will also be used to train neural networks, aiming to teach the model to distinguish between normal system operating conditions and conditions affected by cyber attacks based on network traffic dynamics and control unit status data.
Special attention will be paid to the design and implementation of lightweight machine learning models and neural networks intended for deployment in environments with limited computing resources, such as industrial edge devices. The goal is to develop adaptive detection mechanisms capable of operating in real time, complementing network-level protection with intelligent detection directly at the cyber-physical production system level.
Author Contributions
Conceptualization, T.H. and R.R.; methodology, T.H. and R.R.; validation, R.R., T.H. and R.Z.; formal analysis, T.H., R.R., M.C., J.Š. and R.Z.; investigation, T.H., R.R. and R.Z.; resources, T.H., R.R., R.Z., J.Š. and M.C.; writing—original draft preparation, T.H. and R.R.; writing—review and editing, J.Š., R.Z. and M.C.; visualization, T.H., R.R., J.Š., M.C. and R.Z.; supervision, T.H., R.R. and R.Z.; funding acquisition, T.H. All authors have read and agreed to the published version of the manuscript.
Funding
This research was funded by the call for doctoral students and young researchers of Slovak University of Technology in Bratislava to start a research career (project ESG 23-06-01-B Design and implementation of the security of industrial network systems with the creation of a standardized data set for security analyzes (NAIZPSS).
Data Availability Statement
The original contributions presented in this study are included in the article. Further inquiries can be directed to the corresponding author.
Conflicts of Interest
The authors declare no conflicts of interest.
References
- Fatima, Z.; Tanveer, M.H.; Waseemullah; Zardari, S.; Naz, L.F.; Khadim, H.; Ahmed, N.; Tahir, M. Production Plant and Warehouse Automation with IoT and Industry 5.0. Appl. Sci. 2022, 12, 2053. [Google Scholar] [CrossRef]
- Xu, H.; Yu, W.; Griffith, D.; Golmie, N. A Survey on Industrial Internet of Things: A Cyber-Physical Systems Perspective. IEEE Access 2018, 6, 78238–78259. [Google Scholar] [CrossRef] [PubMed]
- Morgan, J.; Halton, M.; Qiao, Y.; Breslin, J.G. Industry 4.0 Smart Reconfigurable Manufacturing Machines. J. Manuf. Syst. 2021, 59, 481–506. [Google Scholar] [CrossRef]
- da Rocha, H.; Abrishambaf, R.; Pereira, J.; Santo, A.E. Integrating the IEEE 1451 and IEC 61499 Standards with the Industrial Internet Reference Architecture. Sensors 2022, 22, 1495. [Google Scholar] [CrossRef]
- Vachálek, J.; Šišmišová, D.; Vašek, P.; Rybář, J.; Slovák, J.; Šimovec, M. Intelligent Dynamic Identification Technique of Industrial Products in a Robotic Workplace. Sensors 2021, 21, 1797. [Google Scholar] [CrossRef]
- Okunlola, O.A.; Olaoye, J.; Samuel, O.O.; Okunlola, A.O.; Alao, O. Cybersecurity Strategies for Integrating Industrial IoT and Edge Computing: Challenges, Risks, and Future Perspectives. Int. J. Future Eng. Innov. 2025, 2, 87–95. [Google Scholar] [CrossRef]
- Krejčí, J.; Babiuch, M.; Suder, J.; Krys, V.; Bobovský, Z. Internet of Robotic Things: Current Technologies, Challenges, Applications, and Future Research Topics. Sensors 2025, 25, 765. [Google Scholar] [CrossRef] [PubMed]
- Khaung Tin, H.H.; Thu, S.; Maung, K.K. IoT and Industrial Automation: A Review of Current Research and Emerging Trends. FMDB Trans. Sustain. Technoprise Lett. 2024, 2, 151–160. [Google Scholar] [CrossRef]
- Ahmmed, M.S.; Khan, L.; Mahmood, M.A.; Liou, F. Digital Twins, AI, and Cybersecurity in Additive Manufacturing: A Comprehensive Review of Current Trends and Challenges. Machines 2025, 13, 691. [Google Scholar] [CrossRef]
- Bajwa, A.; Tonoy, A.A.R.; Rana, S.; Ahmed, I. CYBERSECURITY IN INDUSTRIAL CONTROL SYSTEMS: A SYSTEMATIC LITERATURE REVIEW ON AI-BASED THREAT DETECTION FOR SCADA AND IOT NETWORKS. ASRC Procedia Glob. Perspect. Sci. Scholarsh. 2025, 1, 1–15. [Google Scholar] [CrossRef]
- Sarjan, H.; Ameli, A.; Ghafouri, M. Cyber-Security of Industrial Internet of Things in Electric Power Systems. IEEE Access 2022, 10, 92390–92409. [Google Scholar] [CrossRef]
- Singh, B.; Kumar, B. Navigating Cybersecurity Risks in Industry 4.0: Challenges, Threats, and Defense Strategies. J. Inf. Syst. Eng. Manag. 2025, 10, 266–275. [Google Scholar] [CrossRef]
- Pal, S.; Jadidi, Z. Analysis of Security Issues and Countermeasures for the Industrial Internet of Things. Appl. Sci. 2021, 11, 9393. [Google Scholar] [CrossRef]
- Alnajim, A.M.; Habib, S.; Islam, M.; Thwin, S.M.; Alotaibi, F. A Comprehensive Survey of Cybersecurity Threats, Attacks, and Effective Countermeasures in Industrial Internet of Things. Technologies 2023, 11, 161. [Google Scholar] [CrossRef]
- Horak, T.; Strelec, P.; Huraj, L.; Tanuska, P.; Vaclavova, A.; Kebisek, M. The Vulnerability of the Production Line Using Industrial IoT Systems under DDoS Attack. Electronics 2021, 10, 381. [Google Scholar] [CrossRef]
- Cui, W.; Liao, X.; Yang, Y.; Feng, S.; Song, M. Informer-Based DDoS Attack Detection Method for the Power Internet of Things. PLoS ONE 2025, 20, e0322329. [Google Scholar] [CrossRef]
- Calderón, D.; Folgado, F.J.; González, I.; Calderón, A.J. Implementation and Experimental Application of Industrial IoT Architecture Using Automation and IoT Hardware/Software. Sensors 2024, 24, 8074. [Google Scholar] [CrossRef] [PubMed]
- Wang, M.; Sun, Y.; Sun, H.; Zhang, B. Security Issues on Industrial Internet of Things: Overview and Challenges. Computers 2023, 12, 256. [Google Scholar] [CrossRef]
- Comert, M.; Ahmed, A.; Ahmed, H. Identifying Security Challenges in the Transition from Traditional to Smart Manufacturing Through IIoT Retrofitting. In Proceedings of the IoT 2024: 14th International Conference on the Internet of Things, Oulu, Finland, 19–22 November 2024; pp. 285–289. [Google Scholar] [CrossRef]
- Zheng, R.; Zheng, S.; Liu, C.; Yue, L.; Wu, H. A Software-Defined Gateway Architecture with Graphical Protocol Modeling for Industrial Control Systems. Electronics 2025, 14, 4369. [Google Scholar] [CrossRef]
- Yousuf, M.; Alsuwian, T.; Amin, A.A.; Fareed, S.; Hamza, M. IoT-Based Health Monitoring and Fault Detection of Industrial AC Induction Motor for Efficient Predictive Maintenance. Meas. Control 2024, 57, 1146–1160. [Google Scholar] [CrossRef]
- Sundar, P.S.; Chowdhury, C.; Kamarthi, S. Industrial Internet of Things Enabled Kata Methodology of Assembly Line Productivity Improvement: Insights from a Case Study. Processes 2024, 12, 2611. [Google Scholar] [CrossRef]
- Mashayekhy, Y.; Babaei, A.; Yuan, X.M.; Xue, A. Impact of Internet of Things (IoT) on Inventory Management: A Literature Survey. Logistics 2022, 6, 33. [Google Scholar] [CrossRef]
- Vagaš, M.; Galajdová, A.; Šimšík, D.; Onofrejová, D. Wireless Data Acquisition from Automated Workplaces Based on RFID Technology. IFAC-PapersOnLine 2019, 52, 299–304. [Google Scholar] [CrossRef]
- Kia, S.H.; Dunai, L.; Antonino-Daviu, J.A.; Razik, H. Real-Time Digital Twins for Intelligent Fault Diagnosis and Condition-Based Monitoring of Electrical Machines. Energies 2025, 18, 4637. [Google Scholar] [CrossRef]
- Al Zami, M.B.; Shaon, S.; Quy, V.K.; Nguyen, D.C. Digital Twin in Industries: A Comprehensive Survey. IEEE Access 2025, 13, 47291–47336. [Google Scholar] [CrossRef]
- Purohit, S.; Purohit, S.; Jain, A.K. From Simulation to Strategy: Integrating Generative AI and Digital Twins in the Downstream Oil And Gas Sector. Econ. Sci. 2025, 21, 104–114. [Google Scholar] [CrossRef]
- Qiu, F.; Kumar, A.; Hu, J.; Sharma, P.; Tang, Y.B.; Xu Xiang, Y.; Hong, J. A Review on Integrating IoT, IIoT, and Industry 4.0: A Pathway to Smart Manufacturing and Digital Transformation. IET Inf. Secur. 2025, 2025, 9275962. [Google Scholar] [CrossRef]
- Marinova-Kostova, K.; Kostov, I. Application of Internet of Things in Industry 4.0. Econ. Ecol. Socium 2021, 5, 49–58. [Google Scholar] [CrossRef]
- Kayan, H.; Nunes, M.; Rana, O.; Burnap, P.; Perera, C. Cybersecurity of Industrial Cyber-Physical Systems: A Review. ACM Comput. Surv. 2023, 54, 229. [Google Scholar] [CrossRef]
- Simola, J.; Takala, A.; Lehkonen, R.; Frantti, T.; Savola, R. Impact of Cyber Security Operations on Hardware Requirements for Stable and Workable Industrial Environments. Int. Conf. Cyber Warf. Secur. 2024, 19, 348–357. [Google Scholar] [CrossRef]
- Alqudhaibi, A.; Albarrak, M.; Aloseel, A.; Jagtap, S.; Salonitis, K. Predicting Cybersecurity Threats in Critical Infrastructure for Industry 4.0: A Proactive Approach Based on Attacker Motivations. Sensors 2023, 23, 4539. [Google Scholar] [CrossRef]
- Sechi, F. Critical Convergence for Enhanced Safety: A Literature Review on Integrated Cybersecurity Strategies for Information Technology and Operational Technology Systems within Critical Infrastructure. In Proceedings of the 33rd European Safety and Reliability Conference, (ESREL 2023), Southampton, UK, 3–8 September 2023; pp. 3414–3421. [Google Scholar] [CrossRef]
- Al-Obeidat, F.; Amin, A.; Shuhaiber, A.; ul Haq, I. DDoS Attack Detection in Edge-IIoT Digital Twin Environment Using Deep Learning Approach. PeerJ Comput. Sci. 2025, 11, e3052. [Google Scholar] [CrossRef]
- Zakariah, M.; Amin, S.U.; Alrayes, F.S.; Helal, M.; Khan, Z.I. SCADA Intrusion Detection Using Deep Factorization Machines. Sci. Rep. 2025, 15, 39753. [Google Scholar] [CrossRef]
- Alrumaih, T.N.I.; Alenazi, M.J.F. ERINDA: A Novel Framework for Enhancing the Resilience of Industrial Networks against DDoS Attacks with Adaptive Recovery. Alex. Eng. J. 2025, 121, 248–262. [Google Scholar] [CrossRef]
- Orman, A. Cyberattack Detection Systems in Industrial Internet of Things (IIoT) Networks in Big Data Environments. Appl. Sci. 2025, 15, 3121. [Google Scholar] [CrossRef]
- Zhukabayeva, T.; Zholshiyeva, L.; Karabayev, N.; Khan, S.; Alnazzawi, N. Cybersecurity Solutions for Industrial Internet of Things–Edge Computing Integration: Challenges, Threats, and Future Directions. Sensors 2025, 25, 213. [Google Scholar] [CrossRef] [PubMed]
- Hareesh, R.; Kalluri, R.; Mahendra, L.; Kumar, R.K.S.; Bindhumadhava, B.S. Passive Security Monitoring for IEC-60870-5-104 Based SCADA Systems. Int. J. Ind. Control Syst. Secur. 2020, 3, 90–99. [Google Scholar] [CrossRef]
- Eryılmaz, E.E.; Akleylek, S.; Ertek, Y.; Kılıç, E. A Systematic Survey of Machine Learning and Deep Learning Models Used in Industrial Internet of Things Security. MANAS J. Eng. 2024, 12, 1–28. [Google Scholar] [CrossRef]
- Swati; Roy, S.; Singh, J.; Mathew, J. Securing IIoT Systems against DDoS Attacks with Adaptive Moving Target Defense Strategies. Sci. Rep. 2025, 15, 9558. [Google Scholar] [CrossRef]
- Alamri, A.H.; Mooney, L. Dragos Industrial Ransomware Analysis: Q3 2025. Available online: https://www.dragos.com/blog/dragos-industrial-ransomware-analysis-q3-2025 (accessed on 10 January 2026).
- Sekonya, N.; Sithungu, S. An Analysis of Critical Cybersecurity Controls for Industrial Control Systems. Eur. Conf. Cyber Warf. Secur. 2023, 22, 410–419. [Google Scholar] [CrossRef]
- de-Marcos, L.; Domínguez-Díaz, A.; Cilleruelo, C.; Rodríguez, D. Ransomware Threats in Manufacturing Industry: Patterns Based on Dark Web Tor Groups. In Proceedings of the 2025 55th Annual IEEE/IFIP International Conference on Dependable Systems and Networks Workshops (DSN-W), Naples, Italy, 23–26 June 2025; pp. 79–82. [Google Scholar] [CrossRef]
- Salviotti, G.; Abbatemarco, N.; De Rossi, L.M.; Bjoernland, K. Understanding the Role of Leadership Competencies in Cyber Crisis Management: A Case Study. In Proceedings of the Annual Hawaii International Conference on System Sciences, Maui, HI, USA, 3–6 January 2023; pp. 6068–6077. [Google Scholar] [CrossRef]
- Ružarovský, R.; Holubek, R.; Janíček, M.; Velíšek, K.; Tirian, G.O. Analysis of the Industry 4.0 Key Elements and Technologies Implementation in the Festo Didactic Educational Systems MPS 203 I4.0. J. Phys. Conf. Ser. 2021, 1781, 012030. [Google Scholar] [CrossRef]
- ISO/IEC 15693-3; Cards and Security Devices for Personal Identification—Contactless Vicinity Objects—Part 3: Anticollision and Transmission Protocol. International Organization for Standardization: Geneva, Switzerland, 2019.
- Zhou, H.; Pal, S.; Jadidi, Z.; Jolfaei, A. A Fog-Based Security Framework for Large-Scale Industrial Internet of Things Environments. IEEE Internet Things Mag. 2023, 6, 64–68. [Google Scholar] [CrossRef]
- Alotaibi, B. A Survey on Industrial Internet of Things Security: Requirements, Attacks, AI-Based Solutions, and Edge Computing Opportunities. Sensors 2023, 23, 7470. [Google Scholar] [CrossRef]
- Saghezchi, F.B.; Mantas, G.; Violas, M.A.; de Oliveira Duarte, A.M.; Rodriguez, J. Machine Learning for DDoS Attack Detection in Industry 4.0 CPPSs. Electronics 2022, 11, 602. [Google Scholar] [CrossRef]
- Söğüt, E.; Erdem, O.A. A Multi-Model Proposal for Classification and Detection of DDoS Attacks on SCADA Systems. Appl. Sci. 2023, 13, 5993. [Google Scholar] [CrossRef]
- Shin, D.-H.; Kim, G.-Y.; Euom, I.-C. Vulnerabilities of the Open Platform Communication Unified Architecture Protocol in Industrial Internet of Things Operation. Sensors 2022, 22, 6575. [Google Scholar] [CrossRef]
- Kang, H.-S.; Kim, K.; Kim, S.-R. A New Mitigation Method against DRDoS Attacks Using a Snort UDP Module in Low-Specification Fog Computing Environments. Electronics 2024, 13, 2919. [Google Scholar] [CrossRef]
- Nuiaa, R.R.; Manickam, S.; Alsaeedi, A.H. Distributed Reflection Denial of Service Attack: A Critical Review. Int. J. Electr. Comput. Eng. (IJECE) 2021, 11, 5327–5341. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.