Symmetric Image Encryption Algorithm Based on a New Product Trigonometric Chaotic Map
Abstract
:1. Introduction
- (1)
- A new product trigonometric chaotic system is constructed. By means of various measures, the chaotic dynamic behavior of the system is analyzed in detail, and the good chaotic characteristics of the system are verified.
- (2)
- A novel symmetric image encryption scheme based on the novel product trigonometric chaotic system is proposed. The system consists of an efficient scrambling process and a secure diffusion operation. The secret keys are generated from the plaintext image by using SHA-256 to resist the chosen-plaintext attacks. Such that any slight change in the plaintext image will affect the whole ciphertext image.
- (3)
- The proposed scheme has been compared with some other recently proposed image encryption schemes. It is verified that the present work outperforms other previously published image encryption schemes and shows better cryptographic performance, while using less computational resources.
2. The New Chaotic Product Trigonometric Map
2.1. The Sine Map System
2.2. The Proposed Chaotic Product Trigonometric Map
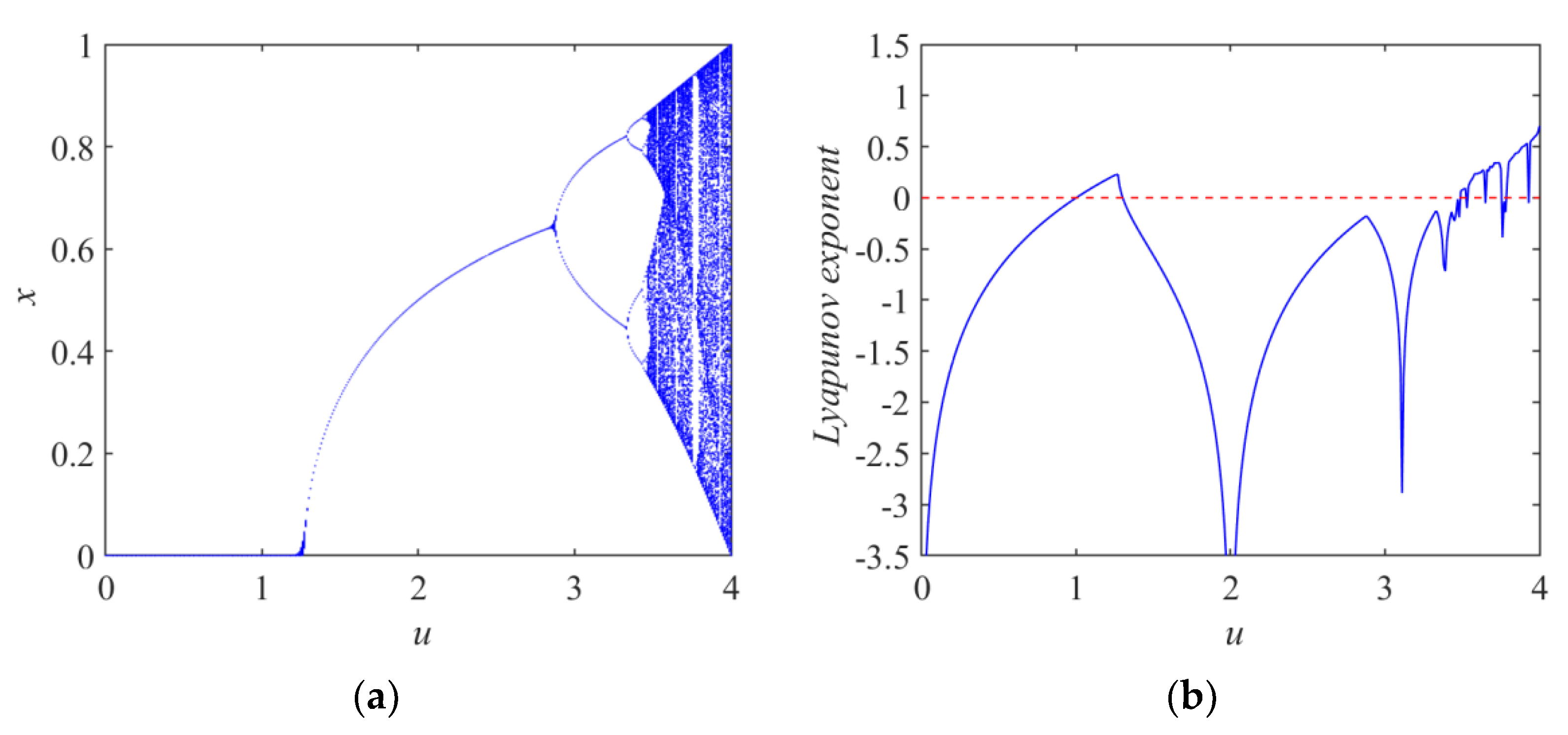
2.2.1. Bifurcation and Lyapunov Exponent Diagram of PTM System
2.2.2. Approximate Entropy and Permutation Entropy of PTM System
2.2.3. The Time-Series and Cobweb Graph of PTM System
2.2.4. The NIST Test of PTM System
| Algorithm 1: Convert a chaotic real number x into an 8-bit binary number uIntx. |
| Input: A real number x |
| Output: A byte digital uIntx |
| 1: Convert the x to a 64-bit binary string b1b2…b64 following the IEEE 754 standard; |
| 2: Intercept 8 digits of the binary x to form unsigned integer: uIntx ← b33b34…b40; |
| 3: Output the unsigned integer uIntx in binary format. |
3. Image Encryption and Decryption Algorithm
3.1. The Encryption Algorithm
| Algorithm 2: Generating a pseudo random integer number sequence. |
| Input: x0, u, k, integer M |
| Output: A pseudorandom integer number sequence X with length of M |
| 1: Initialize: flag ← zeros(1, M); X ← zeros(1, M); x ← x0; |
| 2: Circularly generate M mutually different integers: 1, 2, …, M. |
| for i ← 1: M do |
| x ← u/4*sin(2π/k*x)*cos(π/k*x); |
| j ← mod(floor(x*10^12), M)+1; |
| while (flag(j) = 1) do |
| x ← u/4*sin(2π/k*x)*cos(π/k*x); |
| j ← mod(floor(x*10^12), M)+1; |
| end while |
| X(i) ← j; flag(j) ← 1; |
| end for i |
| 3: Output X = {X(i)} |
3.2. The Decryption Algorithm
4. Security Analysis and Simulation Results
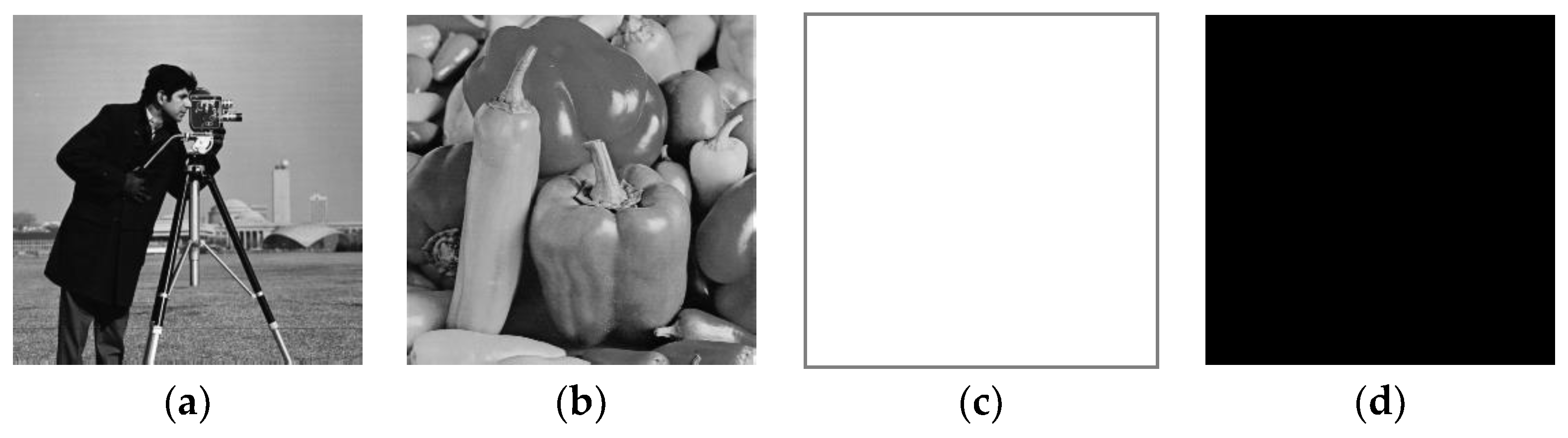
4.1. Encryption Effect
4.2. Key Space Analysis
4.3. Histogram Analysis
4.4. Information Entropy
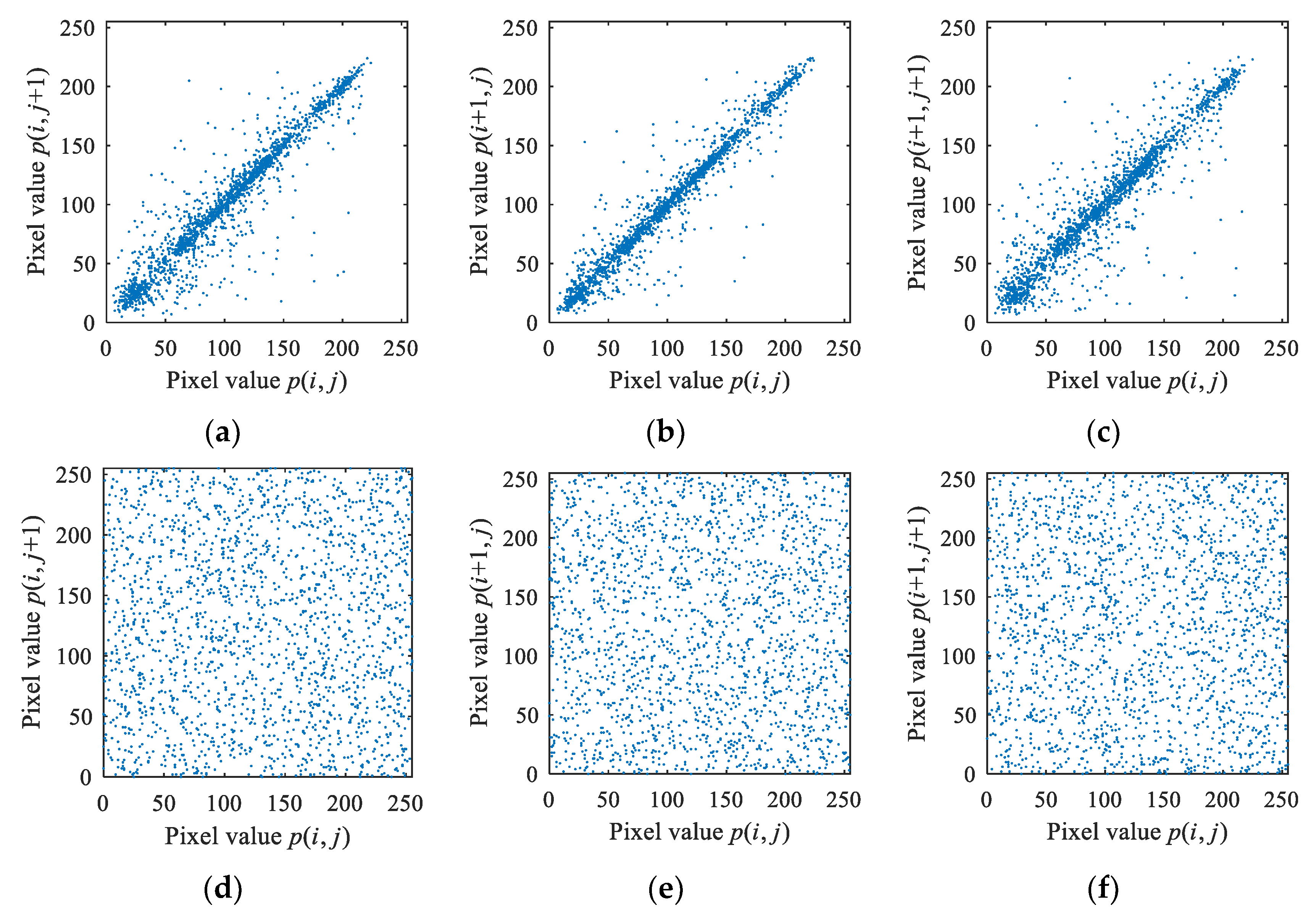
4.5. Correlation Coefficients between Consecutive Pixels
4.6. Resistance to Differential Attacks
4.7. Time Performance Analysis
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Ahmad, J.; Masood, F.; Shah, S.A.; Jamal, S.S.; Hussain, I. A Novel Secure Occupancy Monitoring Scheme Based on Multi-Chaos Mapping. Symmetry 2020, 12, 350. [Google Scholar] [CrossRef] [Green Version]
- Masood, F.; Boulila, W.; Ahmad, J.; Arshad; Sankar, S.; Rubaiee, S.; Buchanan, W.J. A Novel Privacy Approach of Digital Aerial Images Based on Mersenne Twister Method with DNA Genetic Encoding and Chaos. Remote Sens. 2020, 12, 1893. [Google Scholar] [CrossRef]
- Buell, D. Modern Symmetric Ciphers—DES and AES. In Fundamentals of Cryptography; Morgan Kaufmann: Burlington, MA, USA, 2021; pp. 123–147. [Google Scholar] [CrossRef]
- Hua, Z.; Zhou, Y.; Huang, H. Cosine-transform-based chaotic system for image encryption. Inf. Sci. 2019, 480, 403–419. [Google Scholar] [CrossRef]
- Khan, J.S.; Ahmad, J. Chaos based efficient selective image encryption. Multidimens. Syst. Signal Process. 2019, 30, 943–961. [Google Scholar] [CrossRef]
- Lu, Q.; Yu, L.; Zhu, C. A New Conservative Hyperchaotic System-Based Image Symmetric Encryption Scheme with DNA Coding. Symmetry 2021, 13, 2317. [Google Scholar] [CrossRef]
- Zhu, S.; Deng, X.; Zhang, W.; Zhu, C. A New One-Dimensional Compound Chaotic System and Its Application in High-Speed Image Encryption. Appl. Sci. 2021, 11, 11206. [Google Scholar] [CrossRef]
- Masood, F.; Ahmad, J.; Shah, S.A.; Jamal, S.S.; Hussain, I. A Novel Hybrid Secure Image Encryption Based on Julia Set of Fractals and 3D Lorenz Chaotic Map. Entropy 2020, 22, 274. [Google Scholar] [CrossRef] [Green Version]
- Zhu, S.; Wang, G.; Zhu, C. A Secure and Fast Image Encryption Scheme based on Double Chaotic S-Boxes. Entropy 2019, 21, 790. [Google Scholar] [CrossRef] [Green Version]
- Shannon, C.E. Communication theory of secrecy systems. Bell Syst. Tech. J. 1949, 28, 656–715. [Google Scholar] [CrossRef]
- Ouannas, A.; Khennaoui, A.A.; Wang, X.; Pham, V.-T.; Boulaaras, S.; Momani, S. Bifurcation and chaos in the fractional form of Hénon-Lozi type map. Eur. Phys. J. Spec. Top. 2020, 229, 2261–2273. [Google Scholar] [CrossRef]
- Ouannas, A.; Khennaoui, A.A.; Oussaeif, T.-E.; Pham, V.-T.; Grassi, G.; Dibi, Z. Hyperchaotic fractional Grassi–Miller map and its hardware implementation. Integration 2021, 80, 13–19. [Google Scholar] [CrossRef]
- Khennaoui, A.A.; Ouannas, A.; Boulaaras, S.; Pham, V.-T.; Azar, A.T. A fractional map with hidden attractors: Chaos and control. Eur. Phys. J. Spec. Top. 2020, 229, 1083–1093. [Google Scholar] [CrossRef]
- Liu, L.; Miao, S. A new simple one-dimensional chaotic map and its application for image encryption. Multimed. Tools Appl. 2018, 77, 21445–21462. [Google Scholar] [CrossRef]
- Li, Y.; Li, X.; Liu, X. A fast and efficient hash function based on generalized chaotic mapping with variable parameters. Neural Comput. Appl. 2016, 28, 1405–1415. [Google Scholar] [CrossRef]
- Yu, W.; Yu, T. Analysis of chaotic characteristics of trigonometric function system. Mod. Phys. Lett. B 2020, 34, 2050210. [Google Scholar] [CrossRef]
- Elghandour, A.N.; Salah, A.M.; Elmasry, Y.A.; Karawia, A.A. An Image Encryption Algorithm Based on Bisection Method and One-Dimensional Piecewise Chaotic Map. IEEE Access 2021, 9, 43411–43421. [Google Scholar] [CrossRef]
- Gopalakrishnan, T.; Ramakrishnan, S. Image Encryption Using Hyper-chaotic Map for Permutation and Diffusion by Multiple Hyper-chaotic Maps. Wirel. Pers. Commun. 2019, 109, 437–454. [Google Scholar] [CrossRef]
- Zahmoul, R.; Ejbali, R.; Zaied, M. Image encryption based on new Beta chaotic maps. Opt. Lasers Eng. 2017, 96, 39–49. [Google Scholar] [CrossRef]
- Alawida, M.; Samsudin, A.; Teh, J.S.; Alkhawaldeh, R.S. A new hybrid digital chaotic system with applications in image encryption. Signal Process. 2019, 160, 45–58. [Google Scholar] [CrossRef]
- Nepomuceno, E.G.; Nardo, L.G.; Arias-Garcia, J.; Butusov, D.N.; Tutueva, A. Image encryption based on the pseudo-orbits from 1D chaotic map. Chaos 2019, 29, 061101. [Google Scholar] [CrossRef]
- Mansouri, A.; Wang, X. A novel one-dimensional sine powered chaotic map and its application in a new image encryption scheme. Inf. Sci. 2020, 520, 46–62. [Google Scholar] [CrossRef]
- Huang, H.; Yang, S.; Ye, R. Efficient symmetric image encryption by using a novel 2D chaotic system. IET Image Process. 2020, 14, 1157–1163. [Google Scholar] [CrossRef]
- Askar, S.; Karawia, A.; Al-Khedhairi, A.; Al-Ammar, F. An Algorithm of Image Encryption Using Logistic and Two-Dimensional Chaotic Economic Maps. Entropy 2019, 21, 44. [Google Scholar] [CrossRef] [Green Version]
- Khan, J.S.; Boulila, W.; Ahmad, J.; Rubaiee, S.; Rehman, A.U.; Alroobaea, R.; Buchanan, W.J. DNA and Plaintext Dependent Chaotic Visual Selective Image Encryption. IEEE Access 2020, 8, 159732–159744. [Google Scholar] [CrossRef]
- Lu, Q.; Zhu, C.; Deng, X. An Efficient Image Encryption Scheme Based on the LSS Chaotic Map and Single S-Box. IEEE Access 2020, 8, 25664–25678. [Google Scholar] [CrossRef]
- Zhu, S.; Zhu, C. Security Analysis and Improvement of an Image Encryption Cryptosystem Based on Bit Plane Extraction and Multi Chaos. Entropy 2021, 23, 505. [Google Scholar] [CrossRef]
- Zhu, S.; Zhu, C. An efficient chosen-plaintext attack on an image fusion encryption algorithm based on DNA operation and hyperchaos. Entropy 2021, 23, 804. [Google Scholar] [CrossRef]
- Stoyanov, B.; Kordov, K. Image Encryption Using Chebyshev Map and Rotation Equation. Entropy 2015, 17, 2117–2139. [Google Scholar] [CrossRef]
- Yan, X.; Wang, X.; Xian, Y. Chaotic image encryption algorithm based on arithmetic sequence scrambling model and DNA encoding operation. Multimed. Tools Appl. 2021, 80, 10949–10983. [Google Scholar] [CrossRef]







| NIST Statistical Test Item | p-Value | Pass Rate | Results |
|---|---|---|---|
| Frequency (monobit) | 0.763677 | 986/1000 | passed |
| Block Frequency (m = 128) | 0.745908 | 990/1000 | passed |
| Cumulative Sums (Forward) | 0.984881 | 988/1000 | passed |
| Cumulative Sums (Reverse) | 0.599693 | 987/1000 | passed |
| Runs | 0.195864 | 993/1000 | passed |
| Longest Run of Ones | 0.820143 | 985/1000 | passed |
| Rank | 0.016149 | 994/1000 | passed |
| FFT | 0.014754 | 987/1000 | passed |
| Non-Overlapping Templates (m = 9, B = 000000001) | 0.711601 | 990/1000 | passed |
| Overlapping Templates (m = 9) | 0.953089 | 986/1000 | passed |
| Universal | 0.410055 | 991/1000 | passed |
| Approximate Entropy (m = 10) | 0.725829 | 987/1000 | passed |
| Random-Excursions (X = −4) | 0.663542 | 628/631 | passed |
| Random-Excursions Variant (X = −9) | 0.422753 | 622/631 | passed |
| Serial Test 1 (m = 16) | 0.877083 | 996/1000 | passed |
| Serial Test 2 (m = 16) | 0.848027 | 989/1000 | passed |
| Linear complexity (M = 500) | 0.329850 | 992/1000 | passed |
| Images | χ2 of Plaintext Images | χ2 of Encrypted Images (This Work) | χ2 of Encrypted Image (Ref. [17]) |
|---|---|---|---|
| Lena (256 × 256) | 3.0666 × 104 | 217.8984 | 230.1484 |
| Cameraman (256 × 256) | 1.1097 × 105 | 219.4609 | 234.3047 |
| Lena (512 × 512) | 1.5802 × 105 | 249.7266 | 239.7539 |
| Cameraman (512 × 512) | 4.1853 × 105 | 261.8965 | 278.0410 |
| Barbara (512 × 512) | 9.5552 × 104 | 227.0996 | 253.9297 |
| Boat (512 × 512) | 3.8397 × 105 | 207.9766 | 246.9434 |
| Mandrill (512 × 512) | 2.1137 × 105 | 241.0781 | 245.0137 |
| Image Name | Image Size | Ours | Ref. [20] | Ref. [29] | Ref. [30] |
|---|---|---|---|---|---|
| 5.1.10 | 256 × 256 | 7.99665 | 7.99720 | 7.99717 | 7.99680 |
| 5.1.11 | 256 × 256 | 7.99717 | 7.99730 | 7.96999 | 7.99710 |
| 5.1.12 | 256 × 256 | 7.99727 | 7.99540 | 7.99757 | 7.99730 |
| 5.1.13 | 256 × 256 | 7.99707 | 7.99630 | 7.99735 | 7.99680 |
| 5.1.14 | 256 × 256 | 7.99711 | 7.99730 | 7.99674 | 7.99690 |
| 5.2.08 | 512 × 512 | 7.99931 | 7.99920 | 7.99934 | 7.99920 |
| 5.2.09 | 512 × 512 | 7.99930 | 7.99900 | 7.99930 | 7.99940 |
| 5.2.10 | 512 × 512 | 7.99928 | 7.99870 | 7.99926 | 7.99930 |
| 7.1.01 | 512 × 512 | 7.99932 | 7.99800 | 7.99929 | 7.99930 |
| 7.1.02 | 512 × 512 | 7.99944 | 7.99490 | 7.99931 | 7.99930 |
| 7.1.03 | 512 × 512 | 7.99935 | 7.99830 | 7.99925 | 7.99940 |
| 7.1.04 | 512 × 512 | 7.99926 | 7.99850 | 7.99923 | 7.99940 |
| 7.1.05 | 512 × 512 | 7.99924 | 7.99880 | 7.99929 | 7.99930 |
| 7.1.06 | 512 × 512 | 7.99932 | 7.99900 | 7.99933 | 7.99930 |
| 7.1.07 | 512 × 512 | 7.99924 | 7.99870 | 7.99931 | 7.99910 |
| 7.1.08 | 512 × 512 | 7.99930 | 7.99880 | 7.99923 | 7.99920 |
| 7.1.09 | 512 × 512 | 7.99926 | 7.99850 | 7.99219 | 7.99920 |
| Elaine | 512 × 512 | 7.99926 | 7.99930 | 7.99922 | 7.99930 |
| 5.3.01 | 1024 × 1024 | 7.99985 | 7.99930 | 7.99983 | 7.99980 |
| 5.3.02 | 1024 × 1024 | 7.99977 | 7.99920 | 7.99981 | 7.99990 |
| Testpat | 1024 × 1024 | 7.99983 | 7.98470 | 7.99982 | 7.99980 |
| Algorithm | Image Name | Horizontal | Vertical | Diagonal |
|---|---|---|---|---|
| This work | 5.1.10 | 0.001403 | 0.000645 | −0.002410 |
| Ref. [29] | 5.1.10 | −0.002971 | −0.000897 | 0.003682 |
| Ref. [30] | 5.1.10 | −0.007100 | 0.008500 | 0.000200 |
| This work | 5.1.11 | −0.010029 | 0.002503 | −0.000842 |
| Ref. [29] | 5.1.11 | 0.001757 | −0.010444 | 0.001124 |
| Ref. [30] | 5.1.11 | −0.004800 | −0.001700 | 0.006800 |
| This work | 5.1.12 | −0.000273 | −0.000764 | −0.001682 |
| Ref. [29] | 5.1.12 | 0.009575 | −0.002502 | −0.000582 |
| Ref. [30] | 5.1.12 | 0.005500 | −0.004900 | 0.000100 |
| This work | 5.1.13 | 0.002899 | −0.000105 | −0.001305 |
| Ref. [29] | 5.1.13 | 0.000347 | 0.004691 | −0.009999 |
| Ref. [30] | 5.1.13 | 0.003800 | 0.002500 | 0.003200 |
| This work | 5.1.14 | 0.004723 | 0.000035 | −0.000283 |
| Ref. [29] | 5.1.14 | 0.008773 | −0.011971 | 0.000220 |
| Ref. [30] | 5.1.14 | 0.000400 | 0.000400 | 0.001200 |
| This work | 5.2.08 | −0.001405 | −0.002724 | 0.0009704 |
| Ref. [29] | 5.2.08 | −0.002389 | −0.003528 | −0.003059 |
| Ref. [30] | 5.2.08 | 0.004100 | 0.001400 | 0.000054 |
| This work | 5.2.09 | −0.003732 | 0.002767 | 0.000471 |
| Ref. [29] | 5.2.09 | 0.000783 | −0.003316 | −0.000207 |
| Ref. [30] | 5.2.09 | −0.001700 | −0.001800 | −0.001900 |
| This work | 5.2.10 | 0.003098 | −0.001703 | −0.001175 |
| Ref. [29] | 5.2.10 | −0.006168 | −0.007614 | 0.000369 |
| Ref. [30] | 5.2.10 | 0.000007 | 0.002100 | 0.001200 |
| This work | 7.1.01 | 0.001635 | −0.001531 | 0.000747 |
| Ref. [29] | 7.1.01 | −0.002843 | 0.000667 | 0.004116 |
| Ref. [30] | 7.1.01 | −0.000100 | 0.001300 | −0.001300 |
| This work | 7.1.02 | 0.002013 | 0.000773 | −0.000288 |
| Ref. [29] | 7.1.02 | −0.003666 | −0.001386 | −0.001295 |
| Ref. [30] | 7.1.02 | 0.000900 | 0.001600 | 0.005700 |
| This work | 7.1.03 | 0.000500 | 0.000885 | −0.003690 |
| Ref. [29] | 7.1.03 | −0.002931 | −0.004124 | 0.003147 |
| Ref. [30] | 7.1.03 | 0.000100 | 0.000200 | 0.003100 |
| This work | 7.1.04 | 0.000826 | −0.000919 | −0.001786 |
| Ref. [29] | 7.1.04 | −0.004028 | −0.001065 | −0.000901 |
| Ref. [30] | 7.1.04 | −0.001400 | 0.000811 | −0.003100 |
| This work | 7.1.05 | −0.002312 | 0.001432 | 0.001277 |
| Ref. [29] | 7.1.05 | 0.001735 | −0.003046 | −0.002081 |
| Ref. [30] | 7.1.05 | −0.002400 | −0.000700 | 0.003400 |
| This work | 7.1.06 | 0.001373 | 0.001590 | −0.005810 |
| Ref. [29] | 7.1.06 | −0.001395 | −0.003363 | −0.001516 |
| Ref. [30] | 7.1.06 | 0.000832 | 0.001700 | 0.001800 |
| This work | 7.1.07 | −0.002871 | −0.000073 | 0.000955 |
| Ref. [29] | 7.1.07 | −0.000608 | 0.000682 | −0.000090 |
| Ref. [30] | 7.1.07 | 0.003900 | 0.002100 | 0.002500 |
| This work | 5.3.01 | −0.000665 | 0.000425 | 0.000494 |
| Ref. [29] | 5.3.01 | 0.000606 | 0.000090 | 0.002417 |
| Ref. [30] | 5.3.01 | 0.000400 | 0.002600 | 0.001200 |
| This work | 5.3.02 | −0.000417 | −0.000375 | −0.000678 |
| Ref. [29] | 5.3.02 | 0.000502 | 0.001669 | −0.000435 |
| Ref. [30] | 5.3.02 | −0.000377 | −0.000474 | −0.000301 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Lu, Q.; Yu, L.; Zhu, C. Symmetric Image Encryption Algorithm Based on a New Product Trigonometric Chaotic Map. Symmetry 2022, 14, 373. https://doi.org/10.3390/sym14020373
Lu Q, Yu L, Zhu C. Symmetric Image Encryption Algorithm Based on a New Product Trigonometric Chaotic Map. Symmetry. 2022; 14(2):373. https://doi.org/10.3390/sym14020373
Chicago/Turabian StyleLu, Qing, Linlan Yu, and Congxu Zhu. 2022. "Symmetric Image Encryption Algorithm Based on a New Product Trigonometric Chaotic Map" Symmetry 14, no. 2: 373. https://doi.org/10.3390/sym14020373
APA StyleLu, Q., Yu, L., & Zhu, C. (2022). Symmetric Image Encryption Algorithm Based on a New Product Trigonometric Chaotic Map. Symmetry, 14(2), 373. https://doi.org/10.3390/sym14020373






