1. Introduction
Intimate partner violence (IPV)—physical, sexual and psychological aggression enacted through any means and in any form by former or current partners—is encountered on a daily basis by millions of women across the globe. Statistics compiled by the United Nations (UN) indicate that just under 35% of women globally have been subjected to physical or sexual aggression [
1] while as many as three quarters are deemed potentially vulnerable to it. Moreover, data gathered by the UN Office on Drugs and Crime (UNODC) suggest that in 2017 alone, a global total of 87,000 women were murdered, with 58% (50,000) meeting their deaths at the hands of either their spouse or another family member. Given these figures, there is clearly a need to address this epidemic of gender-based violence and to take steps to safeguard victims (hereafter, ‘survivors’) [
2].
When Information and Communication Technologies (ICT) were at a relatively early stage of development, at the start of the 1990s, Haraway [
3] presciently predicted the effect they might have on gender and other social issues. At the start of 2020, the wearing of devices such as biosensors has become a reality in society and their use in e-health practices is part of many people’s everyday lives. Given that the possibilities of ICT have been expanded by the Internet of Things (IoT) [
4], new tools have emerged to manage and prevent the incidence of intimate partner and other types of gender-based violence. However, even though biosensors and other resources have had positive outcomes in healthcare [
5], challenges remain to their use among IPV survivors seeking protection. In particular, previous trials have focused on finding means by which a victim of assault can set off an alarm; however, given the speed and unpredictability which characterize acts of IPV, most women do not have the chance to consciously activate a safety device.
Machine Learning (ML), big data and other methods of smart data processing [
6] may, however, offer a solution to this aspect of gender-based violence. In essence, data collected by wearable biosensors can be collated and processed in order to autonomously activate an alarm when the wearer is in danger, rather than requiring her to do so herself. To enable such a solution, data concerning every possible aspect of the subject’s life must be gathered so her status can be characterized and learnt from and changes to it can then trigger the alarm. This type of solution lies in the rapidly-developing area of emotion recognition [
7]. However, to date, and as far as the authors of the present study are aware, little in-depth work has been carried out in this field to develop strategies specifically for IPV survivors.
Hence, the objective of the current paper is to explore the potential for a safety device to be worn by women at risk of IPV, whereby an alarm is autonomously triggered whenever a continuous passive monitoring system enabled by biosensor technology identifies threat. To this end, we review the current range of wearable applications designed to promote the safety of IPV survivors, as well as the underlying monitoring technology which allows a continuous inference of the woman’s status and the automatic activation of an alarm when that status indicates alarming change. We also emphasize that wearers may turn off such devices during sports or other activities which might mistakenly trigger an alarm.
The rest of the paper is organized as follows.
Section 2 presents a literature review in order to contextualize the topic and
Section 3 outlines passive telemonitoring.
Section 4 investigates the variables to be monitored in order to detect and warn of the onset of aggression and describes the wearable devices and biosensors which are currently available.
Section 5 focuses on the possibilities of leveraging ML to detect aggression;
Section 6 suggests areas to be considered by future research and
Section 7 presents conclusions.
2. Relevant Literature and Context
2.1. The ‘Fight or Flight’ Response
When a person is subjected to IPV, her body displays what is known as the “fight or flight”, or acute stress, response, namely the physiological changes triggered by extreme mental or physical fear. The body is flooded with hormones designed to equip it with the means to either fight the threat or to flee it [
8]. Wearable devices and ML solutions are designed to continuously monitor for these physiological responses and send an alert if they are detected. The sympathetic nervous system reacts immediately to the threat of aggression by stimulating the adrenal glands to release a large number of neurotransmitters known as catecholamines, including adrenaline and noradrenaline. These hormones have immediate effects, including increased heart and breathing rates and a rise in blood pressure, all enabling the body to tense and prepare to take whatever action is required to combat the threat. It takes between twenty minutes and an hour for the body to fully recover from this response and return to its pre-threat status [
9].
The following are among the body’s fight-or-flight responses:
Digestive difficulties, which may include constipation, feelings of nausea and diarrhea;
Aches and pains; tense muscles;
Chest pain and tachycardia;
Disturbed sleep patterns;
Nervousness; trembling; ringing in the ear; abnormally cold or sweaty extremities;
Dry (“cotton”) mouth and difficulty in swallowing;
Clenched jaw; grinding the teeth;
Anxiety; and
Mood swings.
The following sections describe these signals in greater detail and lay out how biosensor technology can undertake real-time monitoring of them as a means to protect individuals against IPV.
2.2. Smart Wearables
Biosensors can be defined as devices or components of a device, which monitor and quantify environmental physical and chemical data, which is then output as an electrical signal. Smart wearable devices incorporate one or several biosensors in garments or other elements worn on the body, which may be accessories such as wristbands, headbands and belts, as well as non-clothing items such as adhesive patches.
Recent advances in electronic technologies have been exploited in the field of biometrics (the measuring of biological characteristics) to enable the production of ever smaller and more powerful devices. Some discreet wearable devices can now continuously monitor variables including vital signs such as the heart rate (HR), which are among those affected by the fight-and-flight reaction and thus indicate that the wearer has perceived an environmental threat. Smart devices including bands, watches and items of fitness and medical equipment can now amass a large amount of important data about their wearers’ status [
10] and share it by connecting the devices to systems such as Bluetooth, ZigBee or near-field communication (NFC). These wearable items and the range of physiological data they can capture [
11], can thus provide a useful and shareable picture of the wearer’s physical condition, which is of obvious benefit in the context of IPV survivors.
Another option which can be used to monitor the physiological status of vulnerable individuals is the Smartphone, an item now used by vast numbers of people. Incorporating accelerometer sensors, pedometers, gyroscopes and similar monitoring devices into this item of everyday use can also gather huge amounts of quantifiable data concerning physical activity [
12]. Although these particular sensors are generally used by recreational users, other sensors can be targeted at specific groups. Sensors offering greater accuracy are described below.
2.3. Emotion Recognition
Toolkits used in the field of emotion recognition (“affective computing”) can be easily extended to detect and monitor for IPV. Human emotions are expressed in a wide variety of ways: from facial expression through vocal pitch, tone and volume, gait, gesture, choice of words and so forth. These visible or audible means to express emotion are accompanied by less easily perceptible physiological cues, which may be, for example, a rise in HR, skin conductance (SC) or body temperature. Unlike those previously listed, these physiological changes, which are no less strongly associated with emotion, are not (or are only rarely) under conscious control; hence, it is virtually impossible to prevent or disguise the biosignals, which indicates that an individual is experiencing an affective response. The present research aims to determine the characteristics of emotional response triggered in the body by the threat of IPV, such as fear, distress, anxiety and other elements of the fight-or-flight response and thus enable the immediate recognition that an IPV situation is occurring or about to occur.
Emotion recognition is a relatively new area within computer science, although research on characterizing emotions has been ongoing for about two decades [
13]. It focuses on the interpretation of human emotion and the research and production of processing data to create software which monitors and adapts to affective change in users in order to offer better recognition and fulfilment of their needs. “Affect-aware” software has potential for use across a wide range of applications, such as healthcare, e-learning and recreation, as well as software engineering itself [
14,
15]. Affective information can be gathered from various channels, among which audio/video [
16], standard input devices [
17], physiological responses [
18] and facial expressions [
19] have all received recent attention.
2.4. Existing Proposals for Violence Detection Based on Biosensors
Many researchers have investigated how ICT can be leveraged to safeguard IPV survivors [
20]. A range of possibilities has been considered, including not only ML but also Artificial Intelligence (AI), cloud computing, domotics and other innovative technologies. The current paper, however, focuses on the potential of smart passive biosensors in monitoring survivors and safeguarding them through a device which detects aggression and autonomously triggers an alarm.
With this, some previous attempts need to be highlighted. The idea of continuous monitoring for violence detection is presented in the work of Hany et al. [
21], where it is proposed to monitor, among others, electrodermal activity, EEG (electroencephalogram) and ECG (electrocardiogram), but, to the authors’ opinion, some other features could complete the frame. Patel and Hassan [
22], in their work, proposed detecting violence with a smart bracelet using an embedded accelerometer. Unfortunately, the detection only relies in this sensor. Goodwin et al. [
23] also presented a remarkable way to detect violence by using cardiovascular, electrodermal activity and motion (accelerometry) but focused on people with autism spectrum disorder, so the circumstances are not exactly similar to a IPV context.
Therefore, although being some proposal very complete [
24], previous proposals have a lack of completeness, this is, relying in a couple of features and other works with a more complete monitoring in order to continuously monitor daily activities (which could include an assault) like the exposed ones in the review done by Kumari et al. [
25] are not specifically designed for IPV survivors monitoring.
3. Passive Telemonitoring
In this context, telemonitoring refers to the practice of continuously gathering data from IPV survivors to determine their precise status and location. Developments in biometrics and IoT technologies now enable 24/7 monitoring of vulnerable individuals; thus, vital biometric data can be harvested and used to both detect (and even predict, as described in more detail in later sections) dangerous situations. All this can be achieved through the use of a Smartphone. The potential of the data collected is extremely high. In this sense, the recent work of Wu et al. [
26] shows how sensors can adequately catch, through sensor combination, movement of day by day living, which is a huge indicator of the freedom and the practical capacities of a person.
Several solutions exist to measure the physical variables of the wearer, among which Smartbands show considerable potential [
27]. Different manufacturers are marketing reasonably-priced and reliable models which not only monitor an ever-increasing list of variables, such as body temperature, blood pressure and perspiration rates but whose battery life and connectivity are also rapidly improving. Most models monitor HR, which Ferdinando et al. identify as being is a valuable indicator of affective state [
28], while more sophisticated ones also use ECG to detect response to threat [
29]. The section below addresses in greater detail the variables which need to be measured and how continuous monitoring can be achieved. As large amounts of data are accumulated by the continuous monitoring of multiple features, a new challenge arises—what type of ICT solution can most efficiently gather and process such data and extract the necessary information from it.
A body area network (BAN) offers an alternative solution. This wireless network, made up of the wearable monitoring and communication applications described in previous sections, is worn on or carried near, the body of a vulnerable person and also monitors biophysical signals to detect response to attack. Broens et al. [
30], researching solutions for epileptics, first proposed the BAN several years ago. They suggested that a 24-h monitoring system could predict the onset of attacks and thus prevent the patient coming to harm. Other researchers later refined the proposal by adding a data-exchange platform to direct the information gathered [
31]. A BAN depends on the wearer/user having permanently to hand a responsive monitoring wearable device with adequate connectivity, accelerometers and GPS capability; these days, a majority of people have precisely this in the form of a Smartphone.
4. Schema of the Autonomous System Proposed
The solution we propose comprises four stages, as outlined below:
Passive monitoring of IPV survivors to detect biophysical signs;
Leveraging ML solutions to enable the autonomous detection of anomalous situations;
If the ML algorithms sense impeding or actual attack, autonomous trigger of an alarm; and
Ability for the IPV survivor to disable the system for a 30-min period (“muted mode”) so that it does not infer from non-threatening situations (e.g., the practice of sports) that an attack is happening. After 30 min have elapsed, system would be automatically re-activated unless the survivor chose to repeat the deactivation for a further half-hour period.
The principal goal of the current study is to investigate the feasibility of gathering comprehensive data on the user’s status and thereafter using ML technology and an alarm system, as applicable, to identify an attack scenario. The following sections elaborate on these points and
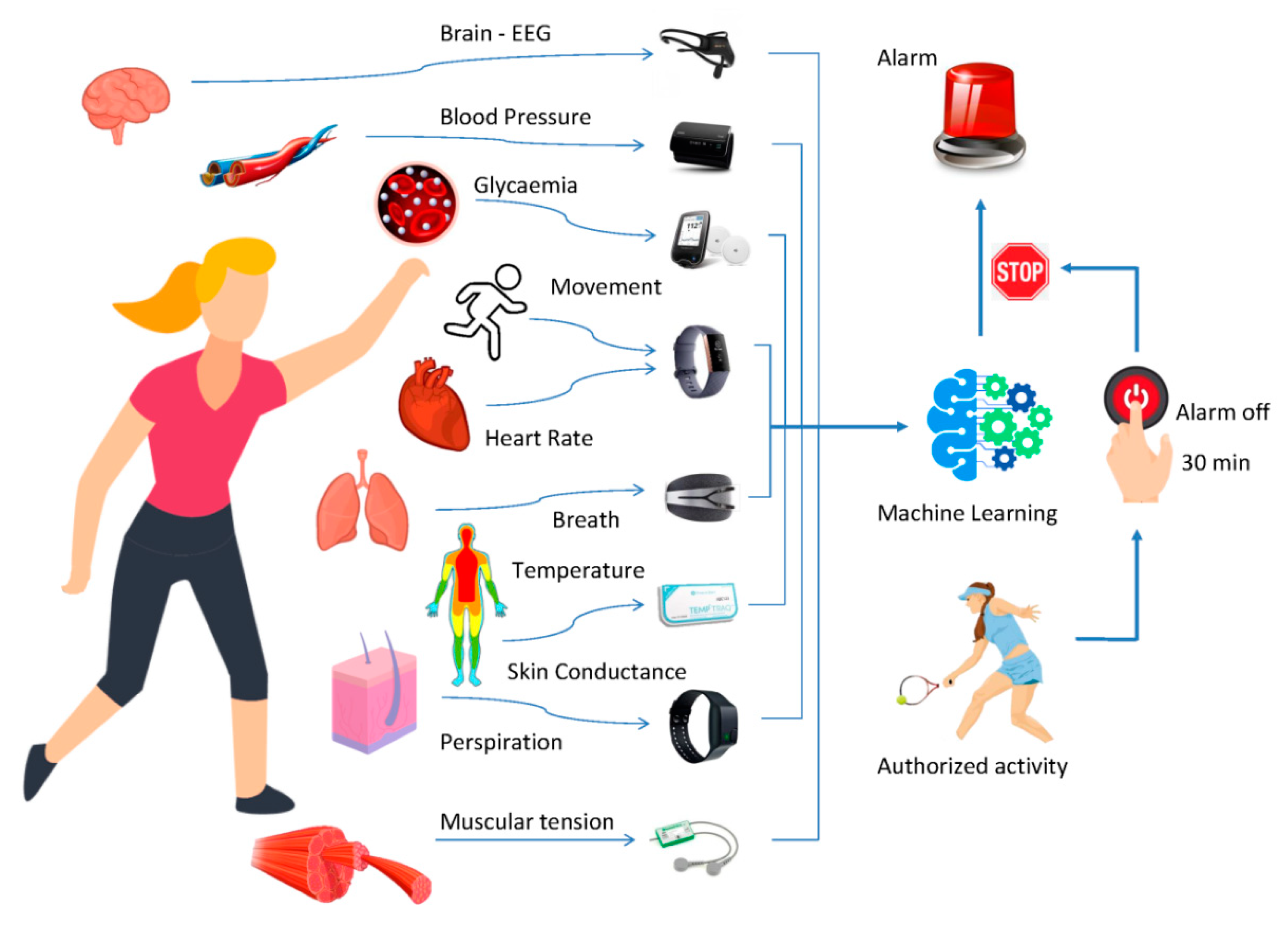
Figure 1, below, presents a summary in graphic form of the proposed solution.
5. Variables to Be Monitored to Detect a Situation of Aggression
Data on human emotion can be harvested from a range of physiological changes; these can also, therefore, be leveraged to trigger an alarm should an IPV survivor be threatened. Cardiac-related signals include changes in HR and pulse, body temperature, respiratory and muscle electrical activity, SC (also known as Electrodermal Activity (EDA) and Galvanic Skin Response (GSR)) and the brain’s electrical activity, all of which can be measured by commonly available sensors.
Figure 1 presents these variables and the devices which measure each.
5.1. Abrupt Movements
Among the abnormal physical changes caused by the threat or occurrence of physical violence, several studies have investigated accelerated motion and velocity. The findings of Ye et al. [
32] demonstrate that the activity of the wearer of a monitoring device which uses accelerometers to extract and filter patterns of movement can indicate that violence is occurring or likely to occur. A more recent and extensive study by Elbasiony et al. [
33] investigated whether normal human behaviors can be described through the use of recorded movements alone, a possibility also explored by smartphones in which accelerometers are embedded [
34,
35]. A further innovation was introduced by the monitoring solution proposed by Jesudoss et al. [
36], namely a tilt sensor.
Wearables designed to monitor specific features also frequently have an accelerometer; therefore, the current paper will not discuss any particular smart device.
Table 1 gives a summary of the wearable solutions discussed in the present paper and lists the principal characteristics measured by each.
5.2. Breath
The acute stress response causes survivors to breathe both faster and more deeply in an attempt to take in greater amounts of oxygen, which is required by the muscles to generate the energy necessary for flight or fight. During this response, first the chest and then the diaphragm rise and fall and signals given by both thorax and diaphragm respiration can be captured. Data concerning velocity and depth of breathing is useful in assessing health, condition, emotion and response status.
Consequently, emotion research makes significant use of respiration signals and expressions of emotion (crying, laughing, etc.) have their own respiratory signature. A picture of respiratory patterns can therefore be created, in which the parameters of volume, depth and timing can indicate a range of emotional states, which are generally mapped along axes of calm-excited, relaxed-stressed and active coping-passive coping [
37]. It would appear from preliminary findings that these parameters also underlie the ‘emotional space’ axes of valence (aversive/appetitive stimulus) and arousal (activating/calming stimulus) [
38].
Breath sensors have brought significant change to medical diagnostics by enabling the non-invasive, personalized detection and monitoring of a range of health parameters and also have potential in the monitoring of persons vulnerable to intimate partner or other forms of violence. Despite this potential, however and the approximately twenty years’ research undertaken in this field, breath sensors are still little used by clinicians [
39]. One such device has been tested in the context of behavior research [
40,
41]: Spire Stone (Spire Health), a small contraption designed to be worn in a belt to monitor breathing and other features such as sleep patterns and pulse rate.
5.3. Heart Activity
During an assault, the body is required to carry oxygen and nutrients to the muscles in order to enable either fight or flight. For this to be possible, HR and heartbeat strength must both rise. This change in cardiac activity can be measured by ECG, which requires the placing of electrodes at various points of the subject’s body, a technique frequently used for detecting the presence of disease.
A further affect-related physiological signal is HR. Arousal increases variability and HR is determined by two branches of the autonomous nervous system, together or independently, namely the sympathetic (which increases it) and the parasympathetic (which decreases it) [
42].
Most current wearables incorporate a HR monitor. Additionally, many Smartbands enable non-invasive monitoring of pulse rates as well as photoplethysmography (optical heart rate monitoring). The different between ECG and photoplethysmography is that the former detects electrical activity whereas the latter shines a penetrating light on the skin in order to examine the underlying blood flow. One well-known fitness tracker incorporating this feature is the Fitbit, which offers accuracy levels which meet the needs of our target group, IPV survivors [
43].
5.4. Blood Pressure
The acute stress response also causes the body to secrete a greater volume of stress hormones, which is associated with rising blood pressure. The medical profession has been aware of this connection for several decades [
44].
The devices available to monitor blood pressure today are considerably more sophisticated than their predecessors, being cheaper, more accurate and smaller and thus more easily carried or worn. Several researchers have investigated the possibility of using Bluetooth to connect wearable blood-pressure monitors to Smartphones [
45] and the consensus is that doing so would give satisfactory results. However, it has also been suggested [
46] that Bluetooth Low Energy (BLE) would be a better mode of connecting the two, as operationalized by Omron’s EVOLV range. A recent comparison of the models was recently carried out and indicates that all perform to a high standard [
47].
5.5. Glycaemia
The actuality or threat of aggression can also be detected in healthy subjects by changes to glycaemia. Associations have been identified between glucose concentrations, behavioral changes characteristic of stress and the blood variables present in stress hyperglycemia (namely plasma glucose, lactate, insulin, glucagon, cortisol, epinephrine and norepinephrine concentrations). Moreover, there is a strong correlation between stress and the body’s glucose and lactate concentrations, as the latter rise sharply and detectably in the presence of risk [
48].
Diabetes research produced Continuous Glucose Monitoring (CGM) devices as a means of managing diabetes mellitus and these can also be used to monitor glycaemia levels. This innovation dramatically changed diabetes management, as these devices can simultaneously detect changes to the size, tendency, frequency and length of fluctuations in glucose levels [
49]. Certain CGM solutions are available commercially, including a relatively low-priced model marketed by Abbott since 2014 (the Freestyle Libre) [
50] and the Dexcom G6, which offers enhanced accuracy [
51]. A connection with an IoT device such as a Smartphone can be simply achieved through NFC or Bluetooth.
5.6. Temperature
A person’s body temperature can not only be measured with ease, for example by attaching electrodes to the subject’s fingers but gives valuable data on health status. The data obtained can indicate changes in mood and affective state; however, it is essential to bear in mind context and conditions, such as where on the body the measurement is taken, time of day and whether—and to what extent—the person has been recently active. The downside of using temperature as an indication of stress is that it changes relatively slowly; thus, there may be a delay in tracking emotional changes.
Shusterman and Barnea [
52] studied the effect of affective stimuli on temperature change. Moreover, work carried out in e-Health, specifically pediatrics, research has investigated the utility of continuous temperature monitoring [
53], which can be carried out via the medical device TempTraq—a non-invasive solution which consists of a soft pad attached to the subject to detect changes in axillary temperature and transmit real-time data via Bluetooth. The device is known to achieve accuracy of ± 0.1 °C at temperatures of between 30 and 42.4 °C.
5.7. Perspiration
IPV survivors are also known to respond to threat by increased perspiration or sweat, which can be conceived of as the body’s natural air-conditioning system. The evaporating of perspiration allows the body to cool when it is in danger of overheating and consequently an increase of sweat ensures we can fight or flee without suffering heat exhaustion.
Considerable research into ways to continuously monitor perspiration has been carried out, given that it is a symptom common to many diseases and conditions [
54]. Researchers have investigated both sweat flux and the presence of anomalies; however, despite promising studies [
55], no continuous perspiration monitoring solution has yet advanced beyond prototype stage.
5.8. Skin Conductance
Skin conductance (SC) measures the skin’s electrical conductance, for example through the attachment of electrodes to the subject’s skin. As the degree of conductance is determined by the nervous system, an association can be detected between state of arousal and SC. Hence, SC signals are often utilized in polygraph (lie detector) tests and it is often used to measure arousal, with which it is associated [
56], with low levels of SC indicating low levels of arousal.
A large range of sensor devices incorporating an SC monitor is available, many at relatively low cost. A recent comparison was undertaken of such devices [
57]—Empatica E4 (Empatica), Microsoft Band2 (Microsoft; no longer available) and the My Signals eHealth Sensor Platform. Among the advantages listed is the fact that Empatica E4 and Microsoft Band2 can be connected through Bluetooth.
5.9. Brain Activity
Stress can cause changes to electrical activity in the brain, which can be detected by EEG. Electrodes are attached to several places on the subject’s scalp to record the electrical signals. Although this technique yields important data, the downside is that the cumbersome equipment required makes it an intrusive experience for patients [
58]. On the other hand, wavelet analysis is proven to be a delay-free and accurate feature extraction technique. Its effectiveness is out of doubt even during a general anesthesia [
59,
60].
Nevertheless, it is widely acknowledged as being among the best affordable solutions for measuring electrical activity in the human brain and is frequently used in the detection of brain disorders such as epileptic seizures as well as to harvest data for Brain Computer Interfacing (BCI). A range of commercially available devices is available, some of which offer acceptable levels of accuracy and ease of wear [
61]. Among them are MindWave Mobile 2 (NeuroSky) [
62] and Emotiv Insight (Emotiv), with the latter having been used for several research studies [
63]. In any case, these devices are still used only with a research purpose, which certainly introduces a limitation in a real life use. All in all, according to their development status, it is interesting to include this feature as it is presumed that, in the near future, more practical EEG sensors will be launched.
5.10. Muscular Tension
A further element in the fight-or-flight response to a threat situation is the tensing of muscle groups. Subjects experience tension, which may manifest as trembling, shaking or behaviors such as twitching, blinking or other movements of the body for which no medical explanation has yet been found. Muscle electrical activity takes place during the cyclical process of the contraction and relaxation of muscles and can be recorded by electromyography (EMG).
As humans cannot control the minor contractions of the facial muscles which make emotion visible to others, a facial electromyogram could be useful in emotion recognition. However, it is a very invasive process, as electrodes have to be attached to the subject’s face, which most people find unpleasant and thus the procedure has little practical value.
Measuring EMG is not only valuable in monitoring and detecting the presence of threat but in several types of laboratory research, including the fields of biomechanics, motor control, neuromuscular physiology, movement disorders, postural control and physical therapy. Several wearable EMG solutions are commercially available, including two devices—Shimmer 3 (Shimmer Sensing, Ireland) and Biometrics (Biometrics Ltd., UK), which were compared by Reference [
64].
5.11. Voice, Ambient Sound
Many researchers have underlined that the voice is a key aspect of emotion recognition [
65] and certain vocal monitoring and detection solutions have been implemented, as indicated by Reference [
66]. A further element which can contain important information is ambient or environmental, sound, which allows the inference of tension, fear or similar emotions in the voice of the subject. While the use of a keyword to trigger an alarm is feasible, the current paper aims, instead, to devise an alarm system whose activation remains completely independent of the wearer. A range of smart devices incorporating microphones for voice monitoring is available and use of environmental control units (ECUs), more popularly known as “smart speakers” or “virtual assistants,” has become increasingly widespread with the marketing of AI-enabled equipment such as Amazon’s “Alexa,” Apple’s “Siri Homepod” and Google’s “Google Home.” All these are not only valuable in the care of the disabled and elderly but also for surveillance [
67]. Given the objective of the present paper is to devise a wearable monitoring system for IPV survivors, however, a Smartphone with a microphone is also suitable for the purpose.
5.12. Additional Biological Variables
A further element in the physiological fight-or-flight response is the dilation of the pupils, which increases the amount of light available to the body to enable the necessary action in the face of threat [
68]. Moreover, the response triggers a decrease in the activity of the digestive system in order to divert energy to the tasks required by pure survival. Consequently, salivation decreases, leading to a feeling of dryness in the mouth (“cotton mouth”). Other common side effects can include nausea, diarrhea and a feeling of heaviness in the stomach.
As mentioned in previous sections, emotions can be recognized from a variety of signals, including facial expressions, tone and timbre of voice, gait and gesture. Some subjects remain in control of certain of these signals (in particular, facial expression and tone of voice); however, very few if any humans can control physiological changes such as temperature change, SC and HR. For this reason, monitoring these physiological events will produce valuable objective data for the purpose of emotion recognition.
5.13. Features Selection
Albeit numerous bio signals identified with the status of the survivor can be recorded, as referenced previously, it is conceivable to derive that, under certain conditions, an ideal subset of factors can be sufficient to identify an aggression. The features ought to be expressed as time series data, on the grounds that the quantity of authentic occasions considered is significant. Feature selection in time series is not the same as feature selection in typical static information [
69]. The objective estimation of the last just identifies with the present estimations of features, while the objective estimation of the previous identifies with the estimations of features in the past time stamps just as in the present time stamp. Consequently in include determination, evacuating superfluous or potentially excess features/variables just as picking the best possible past qualities is a basic assignment so as to appropriately assemble the dataset [
70].
Features selection techniques in time series can ordinarily be characterized into filter and wrapper approaches. The filter approach uses the information alone to choose which features ought to be kept. Then again, the wrapper approach wraps the variable search around a learning technique and uses its performance to choose the features.
6. The Use of Machine Learning for Identifying Aggression
The schema presented in
Section 4 illustrates how comprehensive characterization of an IPV survivor is followed by processing of the data in an ML module—an AI application which enables ICT systems to autonomously learn from experience, with iterative improvements, without the need for human programming interventions. There are three phases: firstly, ML algorithms extract knowledge from input data; secondly, they learn from that data; and lastly, they carry out a task of greater or lesser complexity. These algorithms can be leveraged for several purposes, such as diagnosis, forecasting and analysis, in all of which raw data is transformed into knowledge. Hence, ML enables the independent detection of aggression on the basis of the set of variables being monitored.
Preprocessing of bio- and other signals is necessary for data to be acquired. This is achieved through a series of operations, including amplifying, filtering, averaging, identifying and extracting suitable characteristics for the purpose of training and so forth. Features selection procedures should be sufficiently able to consider as a lot of information/variables as required so as to guarantee the viability of the framework. Since a few reasons can cause a particular articulation, it is important to incline toward solid markers like blends of situational structures that are unequivocal of a hostility. Regardless, the chance of a bogus caution is genuine and this issue is talked about in the following area.
So as to construct a structure for the recognizable proof of IPV circumstances, ML can be utilized, as it tends to be effortlessly adjusted to bioinformatics and human-related frameworks. Example acknowledgment strategies are a subset of ML systems [
71] which are fascinating for the distinguishing proof of certain circumstances like could be brutality against women.
Classification techniques are used so that a ML device can identify anomalous physical signals. Frequently used techniques include least squares, K-nearest neighbors (
k-NN), artificial neural networks (ANN) decision tree classification and support vector machines (SVM) [
72].
It is additionally conceivable to exploit past works concentrated on automatic recognition of activities in a daily life, since the primary principle will be comparable. Utilizing wearable sensors, this action recognition has been recently concentrated with various methodologies. Conditions like standing or walking might be perceived by utilizing ANN [
73]. Different examinations especially utilize Deep Neural Networks (DNN), Probabilistic Neural Networks (PNN), Recurrent Neural Networks (RNN) or Long Short Term Memory (LSTM) yet in addition the referenced SVM, Decision Trees, Bayesian Network, Random Forest, Logistic Regression, Naïve Bayes, Sequential Minimal Optimization (SMO) and numerous others for the acknowledgment of jogging, running, driving, hopping, moving, cycling, sitting, standing, lying, strolling on stairs, going up on an elevator, setting down, washing hands, cleaning, cooking and watering plants [
74,
75,
76,
77,
78,
79].
Hidden Markov Models (HMM) have likewise been actualized a few times in recognition of day by day life exercises, as in the work by Liu et al. [
80]. A few variations, as Hidden Markov Model Ensemble (HMME) [
81] or Sliding-Window-based Hidden Markov Model (SW-HMM) [
82] are likewise utilized for activities like running, sitting and so forth.
The HMM technique is generally utilized for the recognition of walking, strolling on stairs, standing, running, sitting and laying exercises, though the SVM, ANN and their variations, HMM and RF strategies are helpful for the recognition of complex exercises (e.g., cooking, clearing, cleaning, washing hands, medication and watering plants) [
83].
Ye et al. [
84] created a physical violence detection algorithm for school bullying prevention, which could be easily adapted to IPV survivors. Similarly, Hegde et al. [
85] used data collected from wearable sensors to identify the activities of daily life. This could also be useful to detect unexpected situations, such as a potential aggression.
7. Related Considerations
The current paper has discussed monitoring devices with a focus on the particular requirements of IPV survivors. It is recommended that future investigators pursue related avenues of research.
7.1. Emergency Activation, False Alarms and Unintended Deactivation
Firstly, the possibility that the activation of an alarm triggers emergency calls to relevant agencies should be explored, as this function is already widely incorporated in other types of technology-based emergency systems used by survivors. Harikiran et al., for example, used Arduino based on IoT [
86] to propose a screaming alarm, embedded in either a belt or an armband worn by the subject, with the dual purpose of transmitting an alert to the necessary agencies and simultaneously filming evidence of the attack [
87]. A similar system was suggested by Mohanaprakash and Sekar [
88], whose solution was a Smartband designed for self-defense, which would not only activate an alarm but also inform emergency agencies about where the attack was taking place. As discussed above, using an app in a Smartphone is a further possibility in this regard.
Sun et al. [
89] also focused on improving emergency response to attack, proposing a system to support decision-making which would make local agencies such as police forces aware of the occurrence of threatening situations and improve their ability to respond adequately to them.
One possible scenario which must also be considered is that a survivor may unintentionally trigger an alarm by misinterpreting a situation. For this reason, we have privileged the idea of continuous independent response, including the possibility for the survivor to deactivate the device temporarily, over a system which relies on the survivor to consciously take the decision to activate. Thirty-minute deactivation periods, which may be repeated, allow the wearer to undertake sports or other recreational activities; thereafter, monitoring automatically recommences.
In addition, providing a deactivation alarm can be taken as an advantage for the assaulter, switching off the alarm as the first step of the aggression. In this sense, it will be necessary to provide a safe way of disablement, using a password and/or biometrical key.
7.2. Security and Privacy Issues
Most technology applications operating in a BAN environment must negotiate the difficult issue of security. Devices operating in IoT environments can be particularly vulnerable, given that this environment is at a very early stage of development, IoT devices are affordable and thus used by huge numbers and their storage and computing capacity is restricted.
Privacy, an area closely connected to security, must also be carefully considered, given the particularly delicate status of IPV survivors. A large range of algorithms to protect the privacy of personal data has been devised, including k-anonymity and l-diversity [
90].
7.3. Hardware Limitations and ICT Weaknesses
Despite the clear value of gathering data from IPV survivors to enable better protection for them, for the data to be efficiently and effectively shared and leveraged, the monitoring devices must be compatible among themselves. Bearing in mind also that survivors are not static but in motion for much of their daily lives, the devices must be fully integrated into Wireless Sensor Networks [
91]. Further requirements for the continuous transmission of large amounts of data through Smartphones acting as gateways include adequate bandwidth and low energy consumption. The work of healthcare researchers can be drawn upon in this regard, including a study by Talpur et al. [
92], who investigate low-power BANs, using BLE, NFC or Wi-Fi [
30]. A further possibility is Zigbee, which has already been used to operate blood pressure and weight sensors [
93] in a low-power, wireless BAN and could be adapted for use by IPV survivors.
It can also be mentioned as a limitation the possibility that the survivor will not wear all the chosen devices throughout 24 h, as could be the case of bed time. Although some biosensors will be removed before sleeping, some other could stay and be useful. For instance, smartbands are designed to be worn continuously. Many of these smart watches can also monitor sleep and awakening, which in conjunction with their HR monitor and accelerometer, can detect a violent situation. Ambient sound monitored by smart speakers or the smartphone can complete the schema.
7.4. Survivor Acceptance
The success of any telemonitoring system will ultimately depend on its being accepted and used by IPV survivors themselves. Although wearing monitoring devices is proven to offer useful protection, survivors may nonetheless be wary of providing the huge amounts of sensitive data required for the system to be effective. If they consider the harvesting of data to constitute an unacceptable intrusion, they may reject the technology, as has happened among users of other emergency healthcare and other monitoring systems surveyed by Claudio et al. [
94].
8. Conclusions
The sophisticated technology which has become available in the past few years has brought novelty and innovation into a range of daily-life activities and scenarios, including the use of wearable devices for recreational and healthcare purposes. The possibilities offered by such devices should be examined by researchers and practitioners in a variety of other areas. Statistics reveal that gender-based violence, including IPV, remains a serious threat to women in all parts of the world and that the home is frequently a place of danger. Moreover, gender-based violence is a continuum rather than an event, occurring not only during a relationship but after it has ended, while a criminal trial is being prepared and held and even after the guilty party has been convicted and sentenced, following his release from jail.
Consequently, an alarm system which leverages the technological possibilities available to us in today’s world could be a valuable means to prevent aggression and alert emergency forces should one occur. The present paper has established that smart devices and wearable technology exist that can autonomously identify a threat, on the basis of characterizing the biophysical status of wearers through telemonitoring so that the occurrence of anomalous physiological signals automatically triggers an alarm, which will notify to emergency services (police, security systems, medical care, reliable person, etc.), depending on the country/region resources for IPV survivors.
In this paper, we propose removing the need for the survivor to take conscious action in order to send out an alert. Rather, the alert is automatically transmitted through an ML decision algorithm. The possibility of periods of deliberate deactivation is also enabled to preclude the triggering of false alarms.
Thus, we have investigated and extended the possibility that wearable devices can enhance the safety of IPV survivors (and other vulnerable individuals). Future research should be undertaken within collaborative multi-team research to extend the range of technology-based measures available to women, to enable take-up of our proposed system and to investigate its use in real-world contexts.
Author Contributions
Conceptualization, I.R.-R. and J.-V.R.; methodology, A.E.-M. and P.H.-G.; formal analysis, J.-V.R. and P.H.-G.; investigation, I.R.-R. and P.H.-G.; writing—original draft preparation, I.R.-R.; writing—review and editing, J.-V.R., A.E.-M. and P.H.-G.; supervision, A.E.-M.; project administration, J.-V.R. and I.R.-R.; funding acquisition, I.R.-R., J.-V.R. and A.E.-M. All authors have read and agreed to the published version of the manuscript.
Funding
This research received no external funding.
Acknowledgments
Authors would like to thank the Instituto Universitario de Estudios de Género of Universidad de Alicante (Spain) for its support.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Devries, K.M.; Mak, J.Y.; Garcia-Moreno, C.; Petzold, M.; Child, J.C.; Falder, G.; Lim, S.; Bac, L.J.; Pallitto, C. The global prevalence of intimate partner violence against women. Science 2013, 340, 1527–1528. [Google Scholar] [CrossRef] [PubMed]
- Hyman, I.; Forte, T.; Mont, J.D.; Romans, S.; Cohen, M.M. Help-seeking rates for intimate partner violence (IPV) among Canadian immigrant women. Health Care Women Int. 2006, 27, 682–694. [Google Scholar] [CrossRef] [PubMed]
- Haraway, D. A manifesto for cyborgs: Science, technology and socialist feminism in the 1980s. Fem. Postmod. 1990, 190–233. [Google Scholar]
- Harikiran, G.C.; Menasinkai, K.; Shirol, S. Smart security solution for women based on Internet of Things (IOT). In Proceedings of the 2016 International Conference on Electrical, Electronics and Optimization Techniques (ICEEOT), Chennai, India, 3–5 March 2016; pp. 3551–3554. [Google Scholar]
- Rodríguez-Rodríguez, I.; Zamora-Izquierdo, M.Á.; Rodríguez, J.V. Towards an ICT-based platform for type 1 diabetes mellitus management. Appl. Sci. 2018, 8, 511. [Google Scholar] [CrossRef]
- Bryant, R.; Katz, R.H.; Lazowska, E.D. Big-data computing: Creating revolutionary breakthroughs in commerce. Sci. Soc. 2008, 8, 1–5. [Google Scholar]
- Fabiano, D.; Canavan, S. Emotion Recognition Using Fused Physiological Signals. In Proceedings of the 2019 8th International Conference on Affective Computing and Intelligent Interaction (ACII), Cambridge, UK, 3–6 September 2019; pp. 42–48. [Google Scholar]
- Goldstein, D.S. Adrenal responses to stress. Cell. Mol. Neurobiol. 2010, 30, 1433–1440. [Google Scholar] [CrossRef]
- Gordan, R.; Gwathmey, J.K.; Xie, L.H. Autonomic and endocrine control of cardiovascular function. World J. Cardiol. 2015, 7, 204. [Google Scholar] [CrossRef]
- Rodríguez-Rodríguez, I.; Rodríguez, J.V.; Zamora-Izquierdo, M.Á. Variables to Be Monitored via Biomedical Sensors for Complete Type 1 Diabetes Mellitus Management: An Extension of the “On-Board” Concept. J. Diabetes Res. 2018, 2018, 4826984. [Google Scholar] [CrossRef]
- El-Gayar, O.F.; Ambati, L.S.; Nawar, N. Wearables, Artificial intelligence and the Future of Healthcare. In AI and Big Data’s Potential for Disruptive Innovation; IGI Global: Dauphin County, PA, USA, 2020; pp. 104–129. [Google Scholar]
- Case, M.A.; Burwick, H.A.; Volpp, K.G.; Patel, M.S. Accuracy of smartphone applications and wearable devices for tracking physical activity data. JAMA 2015, 313, 625–626. [Google Scholar] [CrossRef]
- Picard, R. Affective Computing: From Laughter to IEEE. IEEE Trans. Affect. Comput. 2010, 1, 11–17. [Google Scholar] [CrossRef]
- Landowska, A. Affect-awareness Framework for Intelligent Tutoring Systems. In Proceedings of the 6th International Conference on Human System Interaction, Sopot, Poland, 6–8 June 2013; pp. 540–547. [Google Scholar]
- Wróbel, M.R. Emotions in the software development process. In Proceedings of the 6th International Conference on Human System Interaction, Sopot, Poland, 6–8 June 2013; pp. 518–523. [Google Scholar]
- Zeng, Z.; Pantic, M.; Roisman, G.; Huang, T. A survey of affect recognition methods: Audio, visual and spontaneous expressions. IEEE Trans. Pattern Anal. Mach. Intell. 2009, 31, 39–58. [Google Scholar] [CrossRef]
- Kołakowska, A. A review of emotion recognition methods based on keystroke dynamics and mouse movements. In Proceedings of the 6th International Conference on Human System Interaction, Sopot, Poland, 6–8 June 2013; pp. 548–555. [Google Scholar]
- Rattanyu, K.; Ohkura, M.; Mizukawa, M. Emotion Monitoring from Physiological Signals for Service Robots in the Living Space. In Proceedings of the International Conference on Control, Automation and Systems, Gyeonggi-do, South Korea, 27–30 October 2010; pp. 580–583. [Google Scholar]
- Szwoch, M. On Facial Expressions and Emotions RGB-D Database. In Communications in Computer and Information Science, Proceedings of the 10th International Conference, BDAS 2014, Ustron, Poland, 27–30 May 2014; Springer: Cham, Switzerland, 2014; pp. 384–394. [Google Scholar]
- Rodríguez-Rodríguez, I.; Rodríguez, J.V.; Elizondo-Moreno, A.; Heras-González, P.; Gentili, M. Towards a Holistic ICT Platform for Protecting Intimate Partner Violence Survivors Based on the IoT Paradigm. Symmetry 2020, 12, 37. [Google Scholar] [CrossRef]
- Ferdinando, H.; Huuki, T.; Ye, L.; Han, T.; Zhang, Z.; Sun, G.; Alasaarela, E. VITEC: A Violence Detection Framework. In Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, Proceedings of the International Conference on Artificial Intelligence for Communications and Networks, Harbin, China, 25–26 May 2019; Springer: Cham, Switzerland, 2019; pp. 3–17. [Google Scholar]
- Patel, J.; Hasan, R. Smart bracelets: Towards automating personal safety using wearable smart jewelry. In Proceedings of the 2018 15th IEEE Annual Consumer Communications & Networking Conference (CCNC), Las Vegas, NV, USA, 12–15 January 2018; pp. 1–2. [Google Scholar]
- Goodwin, M.S.; Mazefsky, C.A.; Ioannidis, S.; Erdogmus, D.; Siegel, M. Predicting aggression to others in youth with autism using a wearable biosensor. Autism Res. 2019, 12, 1286–1296. [Google Scholar] [CrossRef] [PubMed]
- Jatti, A.; Kannan, M.; Alisha, R.M.; Vijayalakshmi, P.; Sinha, S. Design and development of an IOT based wearable device for the safety and security of women and girl children. In Proceedings of the 2016 IEEE International Conference on Recent Trends in Electronics, Information & Communication Technology (RTEICT), Bangalore, India, 20–21 May 2016; pp. 1108–1112. [Google Scholar]
- Kumari, P.; Mathew, L.; Syal, P. Increasing trend of wearables and multimodal interface for human activity monitoring: A review. Biosens. Bioelectron. 2017, 90, 298–307. [Google Scholar] [CrossRef] [PubMed]
- Islam, M.N.; Promi, N.T.; Shaila, J.M.; Toma, M.A.; Pushpo, M.A.; Alam, F.B.; Khaledur, S.N.; Anannya, T.T.; Rabbi, M.F. SafeBand: A Wearable Device for the Safety of Women in Bangladesh. In Proceedings of the 16th International Conference on Advances in Mobile Computing and Multimedia, Yogyakarta, Indonesia, 19–21 November 2018; pp. 76–83. [Google Scholar]
- Wu, J.; Feng, Y.; Sun, P. Sensor fusion for recognition of activities of daily living. Sensors 2018, 18, 4029. [Google Scholar] [CrossRef] [PubMed]
- Ferdinando, H.; Ye, L.; Seppänen, T.; Alasaarela, E. Emotion recognition by heart rate variability. Aust. J. Basic Appl. Sci. 2014, 8, 50–55. [Google Scholar]
- Ferdinando, H.; Ye, L.; Han, T.; Zhang, Z.; Sun, G.; Huuki, T.; Seppänen, T.; Alasaarela, E. Violence detection from ECG signals: A preliminary study. J. Pattern Recognit. Res. 2017, 12, 7–18. [Google Scholar] [CrossRef]
- Broens, T.; Van Halteren, A.; Van Sinderen, M.; Wac, K. Towards an application framework for context-aware m-health applications. Int. J. Internet Protocol Technol. 2007, 2, 109–116. [Google Scholar] [CrossRef]
- Yuce, M.R. Implementation of wireless body area networks for healthcare systems. Sens. Actuators A Phys. 2010, 162, 116–129. [Google Scholar] [CrossRef]
- Ye, L.; Wang, L.; Wang, P.; Ferdinando, H.; Seppänen, T.; Alasaarela, E. Physical Violence Detection with Movement Sensors. In Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering, Proceedings of the International Conference on Machine Learning and Intelligent Communications, Hangzhou, China, 6–8 July 2018; Springer: Cham, Switzerland, 2018; pp. 190–197. [Google Scholar]
- Elbasiony, R.; Gomaa, W. A Survey on Human Activity Recognition Based on Temporal Signals of Portable Inertial Sensors. In Advances in Intelligent Systems and Computing, Proceedings of the International Conference on Advanced Machine Learning Technologies and Applications; Springer: Cham, Switzerland, 2019; pp. 734–745. [Google Scholar]
- Nakano, K.; Chakraborty, B. Effect of dynamic feature for human activity recognition using smartphone sensors. In Proceedings of the 2017 IEEE 8th International Conference on Awareness Science and Technology (iCAST), Taichung, Taiwan, 8–10 November 2017; pp. 539–543. [Google Scholar]
- Alruban, A.; Alobaidi, H.; Clarke, N.; Li, F. Physical activity recognition by utilising smartphone sensor signals. In Proceedings of the 8th International Conference on Pattern Recognition Applications and Methods, Prague, Czech Republic, 19–21 February 2019; pp. 342–351. [Google Scholar]
- Jesudoss, A.; Nikhila, Y.; Reddy, T.S. Smart solution for women safety using IoT. Int. J. Pure Appl. Math. 2018, 119, 43–49. [Google Scholar]
- Grossman, P.; Wientjes, C.J. How Breathing Adjusts to Mental and Physical Demands, Respiration and Emotion; Springer: New York, NY, USA, 2001; pp. 43–53. [Google Scholar]
- Ritz, J.; Nixon, A. Airway response of healthy individuals to affective picture series. Int. J. Psychophysiol. 2002, 46, 67–75. [Google Scholar] [CrossRef]
- Güntner, A.T.; Abegg, S.; Königstein, K.; Gerber, P.A.; Schmidt-Trucksäss, A.; Pratsinis, S.E. Breath Sensors for Health Monitoring. ACS Sens. 2019, 4, 268–280. [Google Scholar] [CrossRef] [PubMed]
- Cai, R.; Guo, A.; Ma, J.; Huang, R.; Yu, R.; Yang, C. Correlation analyses between personality traits andpersonal behaviors under specific emotion states using physiological data from wearable devices. In Proceedings of the 2018 IEEE Cyber Science and Technology Congress (CyberSciTech), Athens, Greece, 12–15 August 2018; pp. 46–53. [Google Scholar]
- Tan, S.; Guo, A.; Ma, J.; Ren, S. Personal Affective Trait Computing Using Multiple Data Sources. In Proceedings of the 2019 International Conference on Internet of Things (iThings) and IEEE Green Computing and Communications (GreenCom) and IEEE Cyber, Physical and Social Computing (CPSCom) and IEEE Smart Data (SmartData), Atlanta, GA, USA, 14–17 July 2019; pp. 66–73. [Google Scholar]
- Berntson, G.G.; Cacippo, J.T.; Quigley, K.S. Autonomic determinism: The modes of autonomic control, the doctrine of autonomic space and the laws of autonomic constraint. Psychol. Rev. 1991, 98, 459–487. [Google Scholar] [CrossRef] [PubMed]
- Haghayegh, S.; Khoshnevis, S.; Smolensky, M.H.; Diller, K.R. Accuracy of PurePulse photoplethysmography technology of Fitbit Charge 2 for assessment of heart rate during sleep. Chronobiol. Int. 2019, 36, 927–933. [Google Scholar] [CrossRef]
- Sherwood, A.; Dolan, C.A.; Light, K.C. Hemodynamics of blood pressure responses during active and passive coping. Psychophysiology 1990, 27, 656–668. [Google Scholar] [CrossRef]
- Singh, M.; Jain, N. Performance and evaluation of smartphone based wireless blood pressure monitoring system using Bluetooth. IEEE Sens. J. 2016, 16, 8322–8328. [Google Scholar] [CrossRef]
- Lin, Z.M.; Chang, C.H.; Chou, N.K.; Lin, Y.H. Bluetooth Low Energy (BLE) based blood pressure monitoring system. In Proceedings of the 2014 International Conference on Intelligent Green Building and Smart Grid (IGBSG), Taipei, Taiwan, 23–25 April 2014; pp. 1–4. [Google Scholar]
- Takahashi, H. Validation of Home Blood Pressure-monitoring Devices Omron EVOLV (HEM-7600T-E), HEM-9210T and M3 Comfort (HEM-7134-E) According to European Society of Hypertension International Protocol (ESH-IP) Revision 2010. J. Clin. Physiol. 2019, 49, 37–46. [Google Scholar]
- Rand, J.S.; Kinnaird, E.; Baglioni, A.; Blackshaw, J.; Priest, J. Acute stress hyperglycemia in cats is associated with struggling and increased concentrations of lactate and norepinephrine. J. Vet. Intern. Med. 2002, 16, 123–132. [Google Scholar] [CrossRef]
- Cappon, G.; Acciaroli, G.; Vettoretti, M.; Facchinetti, A.; Sparacino, G. Wearable Continuous Glucose Monitoring Sensors: A Revolution in Diabetes Treatment. Electronics 2017, 6, 65. [Google Scholar] [CrossRef]
- Leelarathna, L.; Wilmot, G. Flash forward: A review of flash glucose monitoring. Diabet. Med. 2018, 35, 472–482. [Google Scholar] [CrossRef]
- Vettoretti, M.; Del Favero, S.; Sparacino, G.; Facchinetti, A. Modeling the error of factory-calibrated continuous glucose monitoring sensors: Application to Dexcom G6 sensor data. In Proceedings of the 2019 41st Annual International Conference of the IEEE Engineering in Medicine and Biology Society (EMBC), Berlin, Germany, 23–27 July 2019; pp. 750–753. [Google Scholar]
- Shusterman, V.; Barnea, O. Analysis of skin-temparature variability compared to variability of blood pressure and heart rate. In Proceedings of the 17th International Conference of the Engineering in Medicine and Biology Society, Montreal, QC, Canada, 20–23 Septembre 1995; pp. 1027–1028. [Google Scholar]
- Sampson, M.; Hickey, V.; Huber, J.; Alonso, P.B.; Davies, S.M.; Dandoy, C.E. Feasibility of continuous temperature monitoring in pediatric immunocompromised patients: A pilot study. Pediatr. Blood Cancer 2019, 66, e27723. [Google Scholar] [CrossRef] [PubMed]
- Chung, M.; Fortunato, G.; Radacsi, N. Wearable flexible sweat sensors for healthcare monitoring: A review. J. R. Soc. Interface 2019, 16, 20190217. [Google Scholar] [CrossRef] [PubMed]
- Sim, J.K.; Yoon, S.; Cho, Y.H. Wearable sweat rate sensors for human thermal comfort monitoring. Sci. Rep. 2018, 8, 1181. [Google Scholar] [CrossRef] [PubMed]
- Brouwer, A.M.; van Wouwe, N.; Mühl Ch van Erp, J.; Toet, A. Perceiving blocks of emotional pictures and sounds: Effects on physiological variables. Front. Hum. Neurosci. 2013, 7, 295. [Google Scholar] [CrossRef] [PubMed]
- Kutt, K.; Binek, W.; Misiak, P.; Nalepa, G.J.; Bobek, S. Towards the Development of Sensor Platform for Processing Physiological Data from Wearable Sensors. In Lecture Notes in Computer Science, Proceedings of the International Conference on Artificial Intelligence and Soft Computing, Zakopane, Poland, 3–7 June 2018; Springer: Cham, Switzerland, 2018; pp. 168–178. [Google Scholar]
- Byrom, B.; McCarthy, M.; Schueler, P.; Muehlhausen, W. Brain monitoring devices in neuroscience clinical research: The potential of remote monitoring using sensors, wearables and mobile devices. Clin. Pharmacol. Ther. 2018, 104, 59–71. [Google Scholar] [CrossRef] [PubMed]
- Zikov, T.; Bibian, S.; Dumont, G.A.; Huzmezan, M.; Ries, C.R. Quantifying cortical activity during general anesthesia using wavelet analysis. IEEE Trans. Biomed. Eng. 2006, 53, 617–632. [Google Scholar] [CrossRef] [PubMed]
- Sadati, N.; Hosseinzadeh, M.; Dumont, G.A. Multi-model robust control of depth of hypnosis. Biomed. Signal Process. Control 2018, 40, 443–453. [Google Scholar] [CrossRef]
- Pathirana, S.; Asirvatham, D.; Johar, G. A Critical Evaluation on Low-Cost Consumer-Grade Electroencephalographic Devices. In Proceedings of the 2018 2nd International Conference on BioSignal Analysis, Processing and Systems (ICBAPS), Kuching, Malaysia, 24–26 July 2018; pp. 160–165. [Google Scholar]
- Hasbulah, M.H.; Jafar, F.A.; Nordin, M.H.; Yokota, K. Brain-Controlled for Changing Modular Robot Configuration by Employing Neurosky’ s Headset. Brain 2019, 10. [Google Scholar] [CrossRef]
- Strmiska, M.; Koudelková, Z.; Žabčíková, M. Measuring brain signals using emotiv devices. WSEAS Trans. Syst. Control 2018, 13, 537–542. [Google Scholar]
- González-Mendoza, A.; Pérez-SanPablo, A.I.; López-Gutiérrez, R.; Quiñones-Urióstegui, I. Validation of an EMG sensor for Internet of Things and Robotics. In Proceedings of the 2018 15th International Conference on Electrical Engineering, Computing Science and Automatic Control (CCE), Mexico City, Mexico, 5–7 September 2018; pp. 1–5. [Google Scholar]
- Szwoch, W. Using Physiological Signals for Emotion Recognition. In Proceedings of the 6th International Conference on Human System Interaction, Sopot, Poland, 6–8 June 2013; pp. 556–561. [Google Scholar]
- Sumathy, B.; Shiva, P.D.; Mugundhan, P.; Rakesh, R.; Prasath, S.S. Virtual Friendly Device for Women Security. In Proceedings of the Journal of Physics: Conference Series, International Conference on Physics and Photonics Processes in Nano Sciences, Eluru, India, 20–22 June 2019; Volume 1362, p. 012042. [Google Scholar]
- Hoy, M.B. Alexa, Siri, Cortana and more: An introduction to voice assistants. Med. Ref. Serv. Q. 2018, 37, 81–88. [Google Scholar] [CrossRef]
- Guyon, I.; Elissee, A. An introduction to variable and feature selection. J. Mach. Learn. Res. 2003, 3, 1157–1182. [Google Scholar]
- Yang, K.; Yoon, H.; Shahabi, C. A supervised feature subset selection technique for multivariate time series. In Proceedings of the Workshop on Feature Selection for Data Mining: Interfacing Machine Learning with Statistics, New Port Beach, CA, USA, 23 April 2005; pp. 92–101. [Google Scholar]
- Chen, Y.; Lyga, J. Brain-skin connection: Stress, inflammation and skin aging. Inflamm. Allergy Drug Targets (Former. Curr. Drug Targets Inflamm. Allergy) 2014, 13, 177–190. [Google Scholar] [CrossRef] [PubMed]
- Bhatnagar, R. Machine Learning and Big Data Processing: A Technological Perspective and Review. In Proceedings of the International Conference on Advanced Machine Learning Technologies and Applications; Springer: Cham, Switzerland, 2018; pp. 468–478. [Google Scholar]
- Bishop, C.M. Pattern Recognition and Machine Learning; Springer: Berlin, Germany, 2006. [Google Scholar]
- Lorenzi, P.; Rao, R.; Romano, G.; Kita, A.; Irrera, F. Mobile Devices for the Real-Time Detection of Specific Human Motion Disorders. IEEE Sens. J. 2016, 16, 8220–8227. [Google Scholar]
- Lau, S.L.; König, I.; David, K.; Parandian, B.; Carius-Düssel, C.; Schultz, M. Supporting patient monitoring using activity recognition with a smartphone. In Proceedings of the 2010 7th International Symposium on Wireless Communication Systems (ISWCS), York, UK, 19–22 September 2010. [Google Scholar]
- Lau, S.L. Comparison of orientation-independent-based-independent-based movement recognition system using classification algorithms. In Proceedings of the 2013 IEEE Symposium onWireless Technology and Applications (ISWTA), Kuching, Malaysia, 22–25 September 2013. [Google Scholar]
- Duarte, F.; Lourenco, A.; Abrantes, A. Activity classification using a smartphone. In Proceedings of the 2013 IEEE 15th International Conference on e-Health Networking, Applications & Services (Healthcom), Lisbon, Portugal, 9–12 October 2013. [Google Scholar]
- Fahim, M.; Lee, S.; Yoon, Y. SUPAR: Smartphone as a ubiquitous physical activity recognizer for u-healthcare services. In Proceedings of the 2014 36th Annual International Conference of the IEEE Engineering in Medicine and Biology Society, Chicago, IL, USA, 26–30 August 2014; pp. 3666–3669. [Google Scholar]
- Bajpai, A.; Jilla, V.; Tiwari, V.N.; Venkatesan, S.M.; Narayanan, R. Quantifiable fitness tracking using wearable devices. In Proceedings of the 37th Annual International Conference of the IEEE Engineering in Medicine and Biology Society (EMBC), Milan, Italy, 25–29 August 2015. [Google Scholar]
- Nguyen, P.; Akiyama, T.; Ohashi, H.; Nakahara, G.; Yamasaki, K.; Hikaru, S. User-friendly Activity Recognition Using SVM Classifier and Informative Features. In Proceedings of the 2015 International Conference on Indoor Positioning and Indoor Navigation (Ipin), Banff, AB, Canada, 13–16 October 2015; pp. 1–8. [Google Scholar]
- Liu, Y.Y.; Fang, Z.; Wenhua, S.; Haiyong, Z. An Hidden Markov Model based Complex Walking Pattern Recognition Algorithm. In Proceedings of the 2016 Fourth International Conference on Ubiquitous Positioning, Indoor Navigation and Location Based Services (IEEE UPINLBS 2016), Shanghai, China, 2–4 November 2016; pp. 223–229. [Google Scholar]
- Kim, Y.J.; Kang, B.N.; Kim, D. Hidden Markov Model Ensemble for Activity Recognition using Tri-axis Accelerometer. In Proceedings of the 2015 IEEE International Conference on Systems, Man and Cybernetics (Smc 2015): Big Data Analytics for Human-Centric Systems, Kowloon, China, 9–12 October 2015; pp. 3036–3041. [Google Scholar]
- Wang, C.; Xu, Y.; Zhang, J.; Yu, W. SW-HMM: A Method for Evaluating Confidence of Smartphone-Based Activity Recognition. In Proceedings of the 2016 IEEE Trustcom/BigDataSE/ISPA, Tianjin, China, 23–26 August 2016. [Google Scholar]
- Pires, I.M.; Garcia, N.M.; Pombo, N.; Flórez-Revuelta, F.; Spinsante, S. Approach for the development of a framework for the identification of activities of daily living using sensors in mobile devices. Sensors 2018, 18, 640. [Google Scholar] [CrossRef] [PubMed]
- Ye, L.; Ferdinando, H.; Seppanen, T.; Huuki, T.; Alasaarela, E. An instance-based physical violence detection algorithm for school bullying prevention. In Proceedings of the 2015 International Wireless Communications and Mobile Computing Conference (IWCMC), Dubrovnik, Croatia, 24–28 August 2015. [Google Scholar] [CrossRef]
- Hegde, N.; Bries, M.; Swibas, T.; Melanson, E.; Sazonov, E. Automatic recognition of activities of daily living utilizing insole-based and wrist-worn wearable sensors. IEEE J. Biomed. Health Inform. 2017, 22, 979–988. [Google Scholar] [CrossRef]
- Pavithra, R.; Sangeetha, P.S.; Devi, M.S.; Vanila, S. Design and Implementation of a Rescue System for the Safety of Women by using Arduino Controller. Int. J. Adv. Res. Idea’s Innov. Technol. 2018, 4, 329–333. [Google Scholar]
- Toney, G.; Jabeen, F.; Puneeth, S. Design and implementation of safety armband for women and children using ARM7. In Proceedings of the 2015 International Conference on Power and Advanced Control Engineering (ICPACE), Bangalore, India, 12–14 August 2015; pp. 300–303. [Google Scholar]
- Mohanaprakash, K.; Sekar, T.G. A Smart Alarm System for Women’s Security. Int. J. Eng. Manag. Res. (IJEMR) 2018, 8, 89–92. [Google Scholar]
- Li, N.; Sun, M.; Bi, Z.; Su, Z.; Wang, C. A new methodology to support group decision-making for IoT-based emergency response systems. Inf. Syst. Front. 2014, 16, 953–977. [Google Scholar] [CrossRef]
- Machanavajjhala, A.; Gehrke, J.; Kifer, D.; Venkitasubramaniam, M. l-diversity: Privacy beyond k-anonymity. In Proceedings of the 22nd International Conference on Data Engineering (ICDE’06), Atlanta, GA, USA, 3–7 April 2006; p. 24. [Google Scholar]
- Lim, H.B.; Teo, Y.M.; Mukherjee, P.; Lam, V.T.; Wong, W.F.; See, S. Sensor grid: Integration of wireless sensor networks and the grid. In Proceedings of the IEEE Conference on Local Computer Networks 30th Anniversary (LCN’05), Sydney, Australia, 15–17 November 2005; pp. 91–99. [Google Scholar]
- Talpur, M.S.H.; Bhuiyan, M.Z.A.; Wang, G. Energy-efficient healthcare monitoring with smartphones and IoT technologies. Int. J. High Perform. Comput. Netw. 2015, 8, 186–194. [Google Scholar] [CrossRef]
- Omre, A.H.; Keeping, S. Bluetooth low energy: Wireless connectivity for medical monitoring. J. Diabetes Sci. Technol. 2010, 4, 457–463. [Google Scholar] [CrossRef]
- Claudio, D.; Velázquez, M.A.; Bravo-Llerena, W.; Okudan, G.E.; Freivalds, A. Perceived usefulness and ease of use of wearable sensor-based systems in emergency departments. IIE Trans. Occup. Ergon. Factors 2015, 3, 177–187. [Google Scholar] [CrossRef]
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).