Interoperability Challenges in the Cybersecurity Information Sharing Ecosystem
Abstract
:1. Introduction
2. Background
- Indicators of Compromise (IOCs), i.e., system artefacts or observables that contain patterns, such as malicious Internet Protocol addresses (IPs) or hashes of files containing malware, which can help identify suspicious or malicious activity.
- Tactics, Techniques and Procedures (TTPs), i.e., (detailed) description of the behaviour of an actor that can assist operational activities, such as details of exploits and malware delivery mechanisms. TTPs include tradecrafts, i.e., behaviour used to conduct a malicious activity, infrastructure used to deliver malicious content or maintain command and control capabilities, and attackers’ intentions [11].
- Security alerts, i.e., notification, usually human-readable regarding security issues, such as vulnerabilities.
- Threat intelligence reports, i.e., collections of threat intelligence for various topics, such as threat actors, malware and attack techniques.
- Recommended security tool configurations, regarding automated collection and processing as well as healing of identified security issues.
- Vulnerabilities, i.e., known weaknesses in software implementations or procedures, and corresponding mitigations, such as security patches. Although in the information security literature, vulnerabilities are not threats, they are considered as an important component in the CTII sharing ecosystem.
- Strategic reports providing high level threat analyses that is consumed at board level or by other senior decision-makers.
- Operational details providing information about impending attacks against an organisation.
- Advisories which include vulnerabilities, exploits patches and patch status, or high-level tactical patterns of activity on a host, service, network or internet level, tools and methodologies.
- Indicators of compromise, which include IP addresses, DNS names, URLs, specific values of format-specific fields (e.g., email headers), artefacts (e.g., hashes, registry and keys) related to malware and sequences of low-level events (e.g., syscalls and packets) linked to malicious behaviour.
- Low-level, i.e., network flow records and full packet captures, application logs, including typical IDS alerts, samples of executable files, documents and email messages.
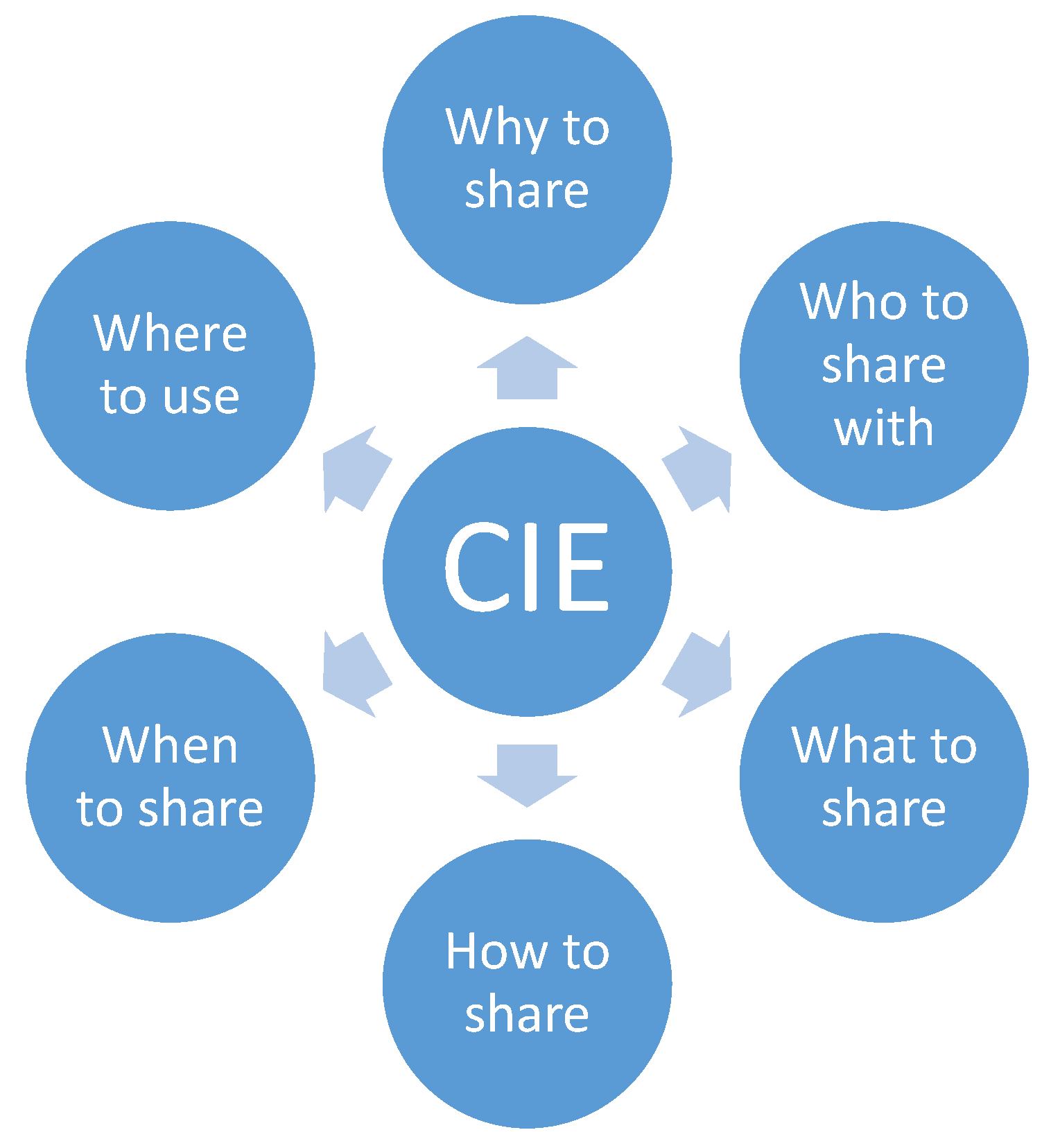
3. Interoperable CTII Sharing
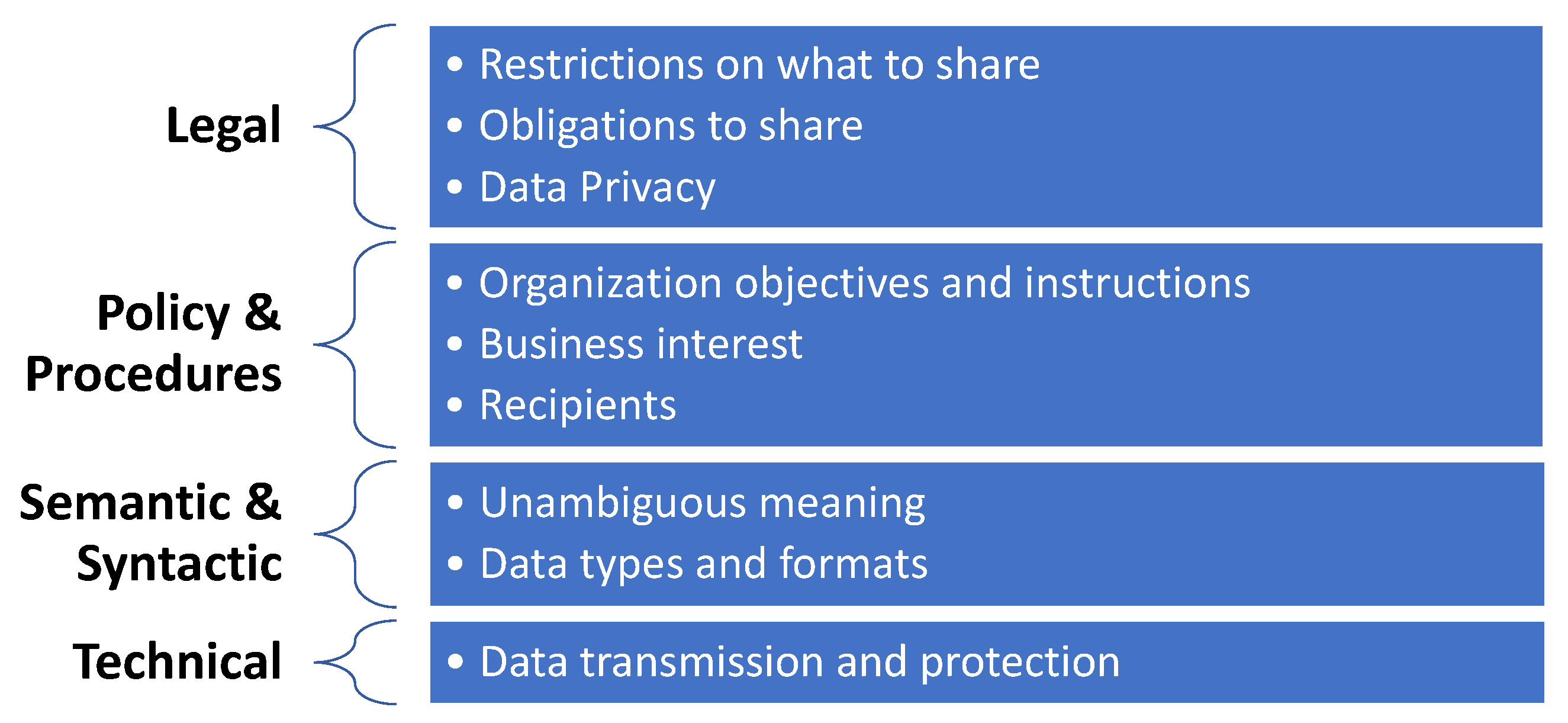
3.1. Legal Interoperability
3.2. Policies and Procedures for Interoperability
- The type of information that satisfies the organisations’ business needs.
- The form of information exchange that is going to take place, such as emails, bulletins, documents and automated sharing.
- The confidentiality requirements for the exchanged information and the dissemination restrictions.
- Parties authorised to access, process and use the information.
- Technical standards used for the exchange of information to satisfy the syntactic and semantic interoperability.
- Language issues for cross-border dissemination.
- Communication protocols and access to services.
3.3. Semantic and Syntactic Interoperability
- Structured Threat Information Expression (STIX) [25]: This OASIS adopted standard is an information model and serialization solution used to exchange CTII. STIX 2.X is based on JSON, while its predecessors, i.e., STIX 1.X were XML-based. STIX 1.X together with the CybOX 2.X [26], a standardised language for encoding and communicating information about cyber observables, were integrated into STIX 2.0.
- Malware Information Sharing and Threat Intelligence Sharing Platform (MISP) [27]: A data model composed of “events”, which usually represent threats or incidents, which in turn are composed of a list of “attributes”, such as IP addresses and domain names. Objects in MISP allow combinations of attributes and “galaxies”, which enable a deeper analysis and categorisation of events.
- Common Attack Pattern Enumeration and Classification (CAPEC) [28]: It provides a comprehensive dictionary of known patterns of attack employed by adversaries to exploit known weaknesses.
- Malware Attribute Enumeration and Characterization (MAEC) [29]: A structured language used for encoding and sharing information about malware based upon attributes such as behaviours, artefacts and relationships between malware samples. It facilitates correlation, integration, and automation of malware analysis and reduces potential duplication of malware during analysis.
- IETF’s Managed Incident Lightweight Exchange (MILE) set of standards: MILE working group develops standards to support computer and network security incident management focusing on the definition of data formats for representing incident and indicator data, and on standardising how application layer protocols such as HTTPS and XMPP are utilised for sharing the structured data. Among the standards adopted by MIME are the following.
- –
- IODEF v2 (Incident Object Description Exchange Format) [30,31]: It is an XML-based data representation of security incident reports and indicators. It is designed so that to be compatible with IDMEF (Intrusion Detection Message Exchange Format) and capable to include IDMEF message into incident objects.
- –
- Intrusion Detection Message Exchange Format (IDMEF) [32]: An XML-based data format that is used by intrusion detection and response systems to report alerts about suspicious events.
- Statements, e.g., copyright, terms of use, applied to the shared content.
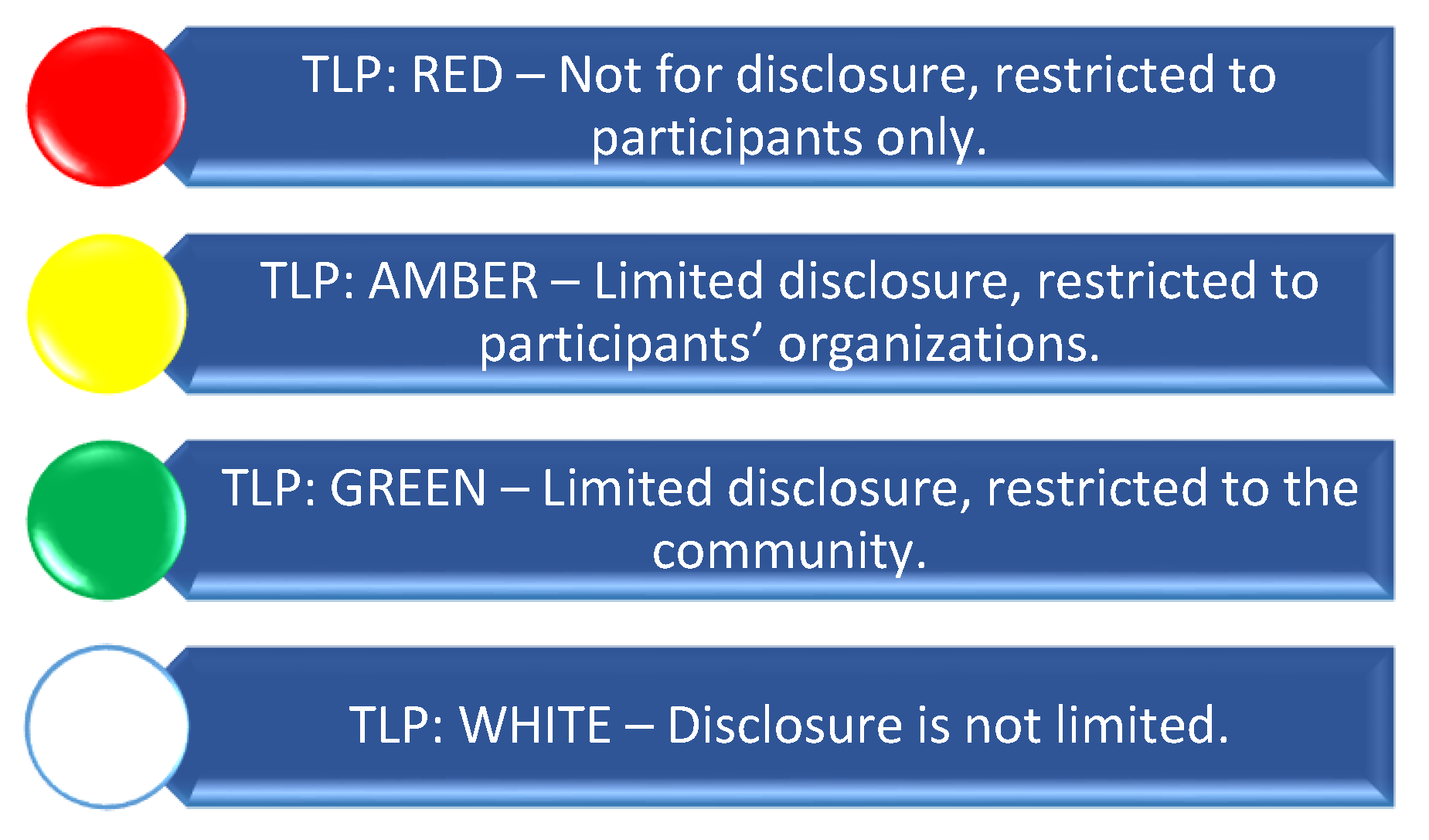
- Traffic Light Protocol (TLP v1.0) [23]: It is a set of designations used to ensure that sensitive information is shared with the appropriate audience by providing four options as shown in Figure 3. Although optimised for human readability and person-to-person sharing and not for automated sharing exchanges, TLP can help restrict information sharing only with specific entities or platforms and avoid any further unnecessary or unauthorised dissemination thereof. TLP is supported by STIX 2.0 and MISP protocols.
- Handling: It can be used to ensure the confidentiality of the information being shared.
- Action: It can be used to define the permitted actions or uses of the information received that can be carried out by a recipient.
- Sharing: It can be used to define any permitted redistribution of information that is received.
- Licensing: It can be used to define any applicable agreements, licenses or terms of use that govern the information being shared.
- Common Vulnerability Enumeration (CVE): A de facto standard for listing vulnerability information where each CVE entry should include:
- –
- A CVE ID number,
- –
- A description of the vulnerability,
- –
- The anticipated impact in the form of a CVSS (Common Vulnerability Scoring System) value, and
- –
- References to vulnerabilities reports and/or advisories.
- Common Vulnerability Reporting Framework (CVRF) [36]: An XML-based standard that supports creation, update and interoperable exchange of security advisories as structured information on products, vulnerabilities and the status of impact and remediation among interested parties. According to MITRE, CVRF allows interested parties to download the entire CVE list at once, or download CVEs for a specific year, whereas each CVE can record when it was initially published by the CVE Team, and when it was most recently modified.
- Open Vulnerability and Assessment Language (OVAL): A language that can be used for representing system information, expressing specific machine states, and reporting the results of an assessment.
3.4. Technical Interoperability
- Trusted Automated Exchange of Intelligence Information (TAXII) [37]: It is an application layer protocol that is used to exchange CTII, represented in STIX, over HTTPS.
- Resource-Oriented Lightweight Information Exchange (ROLIE) [38]: It defines a REST style approach for security information publication, discovery and sharing. Using ROLIE, security incidents, attack indicators, software vulnerabilities, configuration checklists, and other security automation information are provided as web-addressable resources. IETF’s MILE working group has drafted two extensions to ROLIE for CSIRTs needs [39] and for the exchange of vulnerabilities [40].
4. The CTII Landscape
5. Conclusions
Author Contributions
Funding
Conflicts of Interest
Appendix A
Appendix B
| Generic Properties | Explanation |
|---|---|
| 1. Type of Data | A CTII source may manage and share different types of data, ranging from vulnerabilities and exploits to sightings and courses of actions |
| 1.1 Indicators | An indicator is a collection of cyber security relevant information containing patterns that can be used to detect suspicious or malicious cyber activity. |
| 1.2 Sightings | A sighting is an observation that someone has shared with the community, without adding additional intelligence to it. |
| 1.3 Courses of Action | A course of action is information concerning how to prevent or mitigate an event shared by, e.g., an indicator. |
| 1.4 Vulnerabilities | A vulnerability is a weakness in a hardware or software appliance that could be exploited to breach the appliance. |
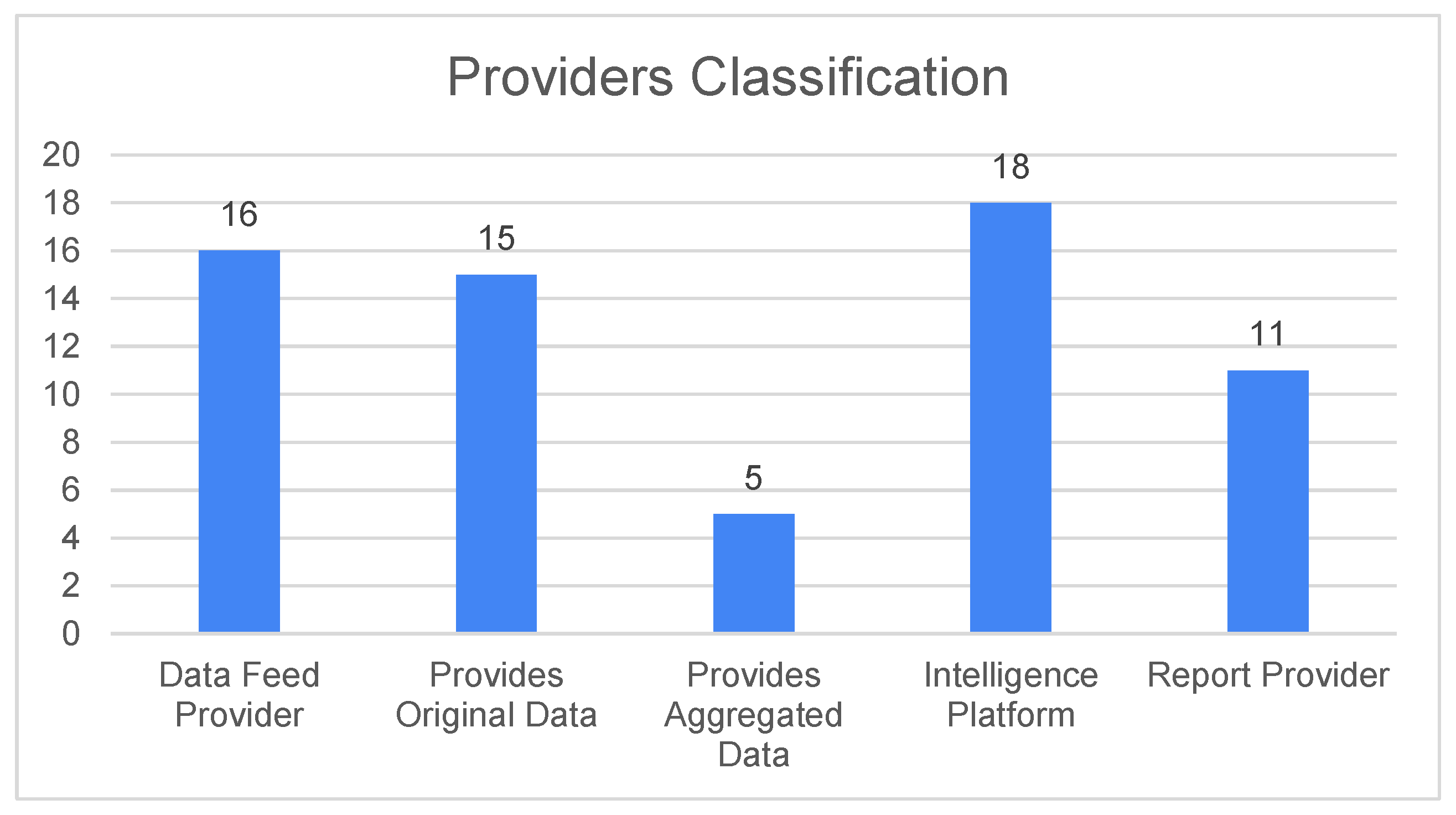
| 2 Provider Classification | An indicator to assess the type of sharing an information sharing provider does, and how much original information can be expected from this provider. |
| 2.1 Data Feed Provider | A data feed provider is the entity that produces cyber security information, or shares received information with minimal or no additional intelligence added to it. |
| 2.1.1 Provides Original Data | A data feed provider that is the original provider of this information, which has been shared in one form or another by the source of, e.g., an incident. |
| 2.1.2 Provides Aggregated Data | A feed provider that does not provide information originally shared with this provider, but shares information aggregated from other feeds. |
| 2.2 Intelligence Platform | A provider that adds additional intelligence/ analysis to the information that is shared with the provider in one form or another. |
| 2.3 Report Provider | A provider that provides, e.g., statistical information in form of reports rather than data feeds. |
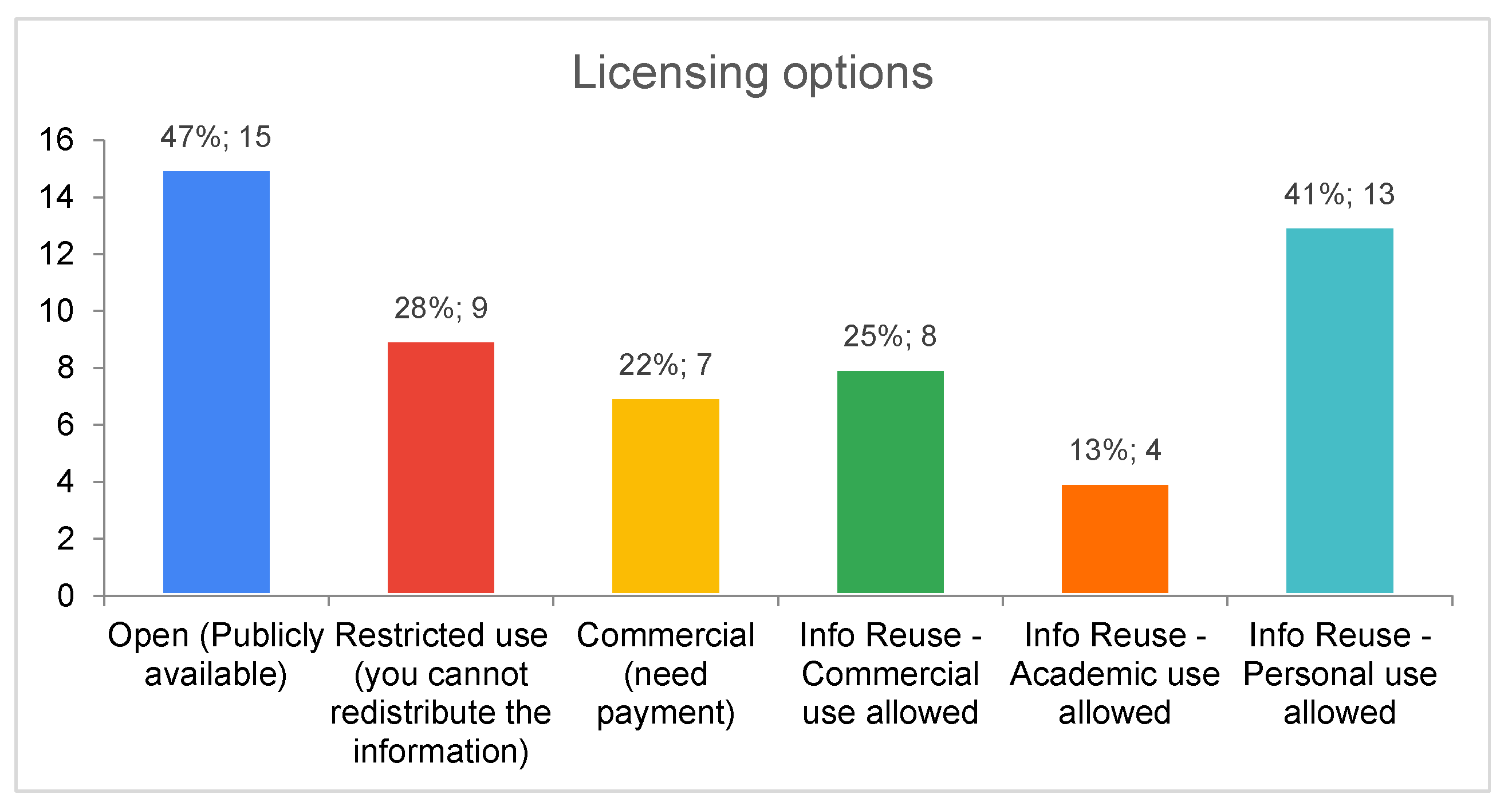
| 3 Licencing Options | An indicator to assess the licencing of data use and/or access to the data source API. |
| 3.1 Open (Publicly available) | The data is freely available to collect and use. |
| 3.2 Restricted use | Some restrictions apply as to how the data can be used (e.g. academic or commercial context). |
| 3.3 Commercial | The data provider has commercial interest and provides the data for a fee. |
| 3.4 Information Reuse | Specifies how the data provided by a data source can be reused. Options include commercial, academic or personal use. |
| 3.4.1 Commercial use allowed | The data can be reused in a commercial context, offering services and collecting fees based on this data is allowed. |
| 3.4.2 Academic use allowed | The data can be used in an academic context without restrictions, restrictions apply in other contexts. |
| 3.4.3 Personal use allowed | The data can be used for personal use without restrictions, restrictions apply for other contexts. |
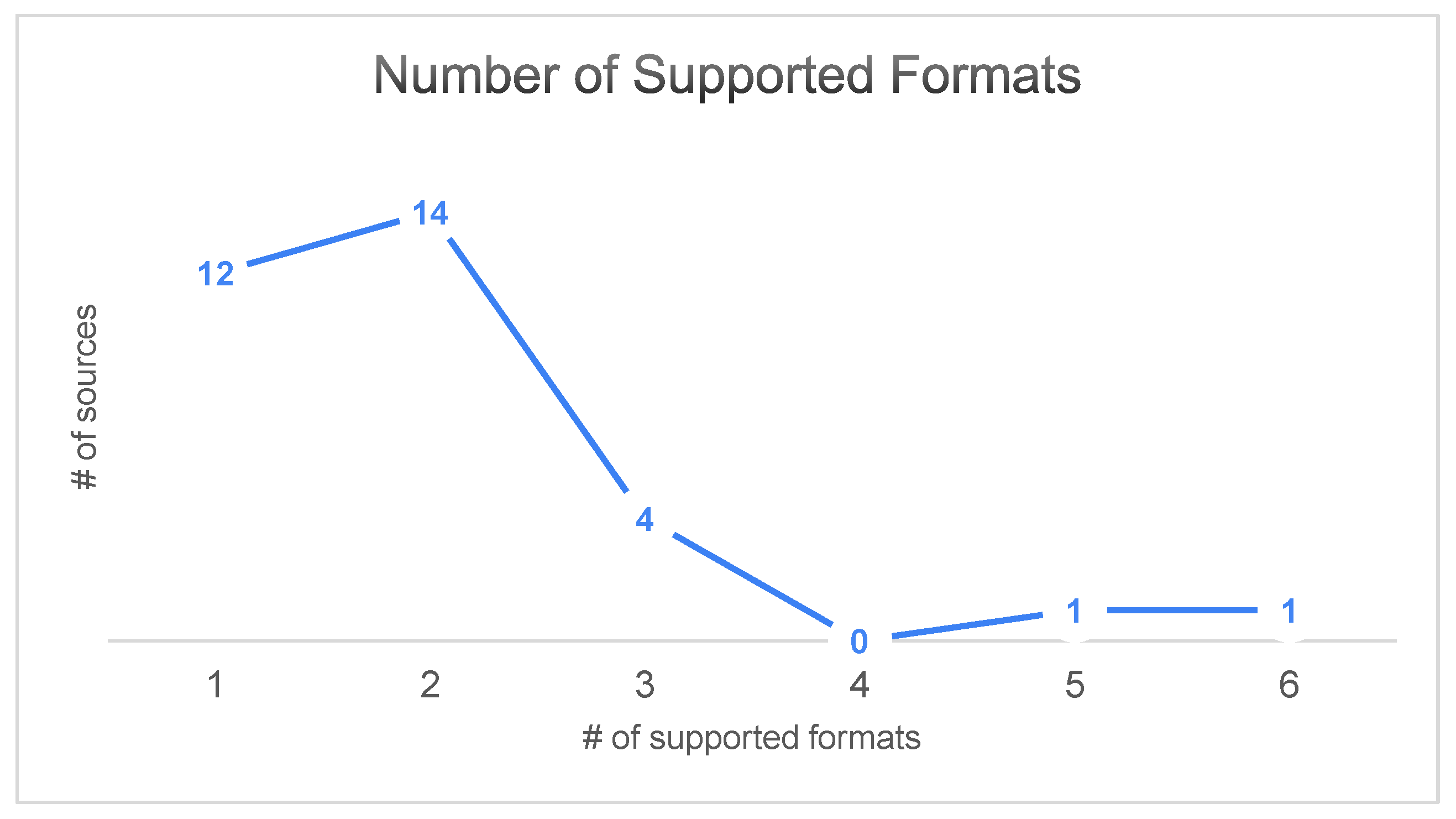
| 4 Interoperability/Standards | An indicator to assess the interoperability of a tool provider with state-of-the art cybersecurity threat exchange standards and relevant tools/libraries. |
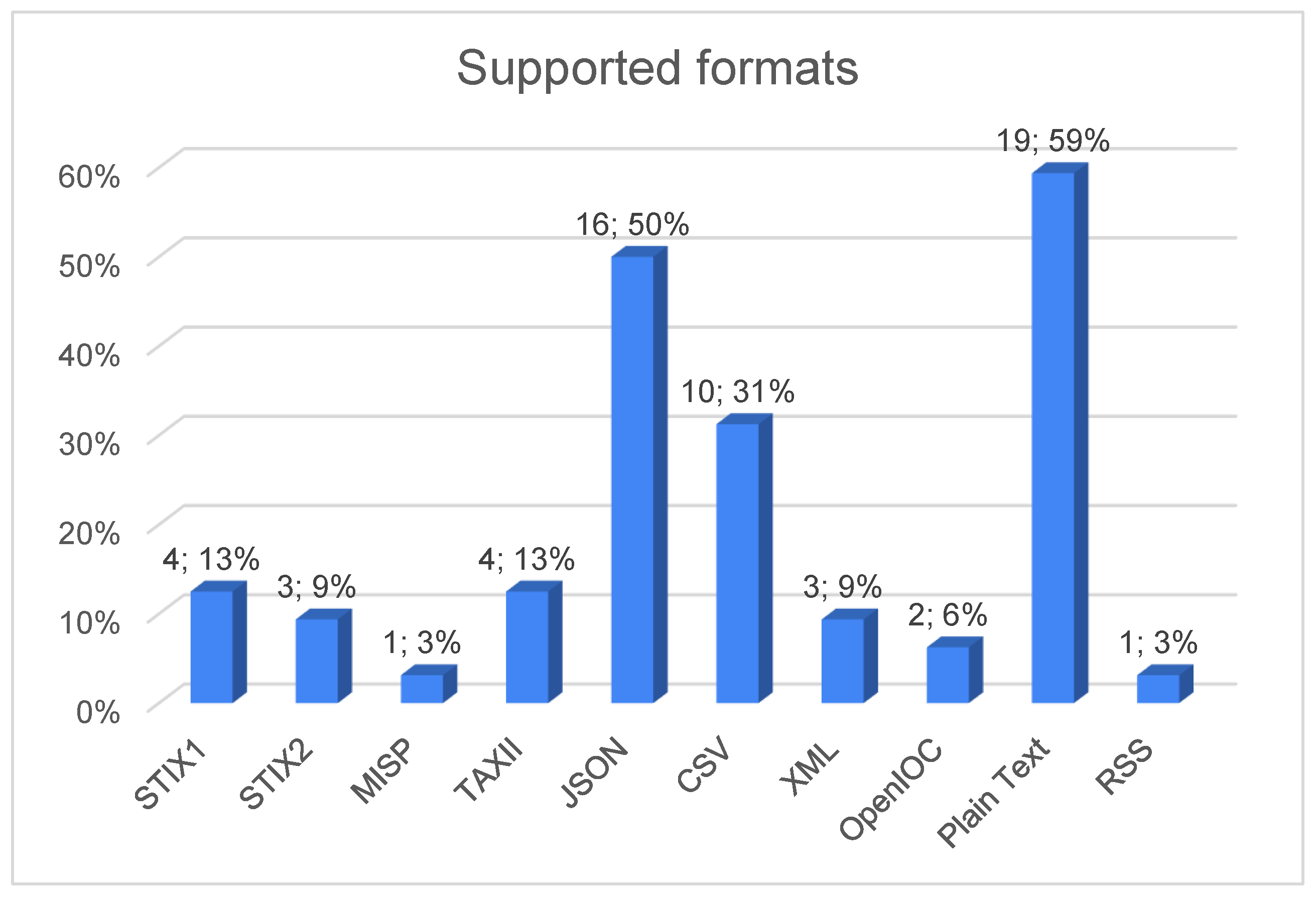
| 4.1 STIX1 | Supports the STIX1 threat expression standard. |
| 4.2 STIX2 | Supports the STIX2 threat expression standard. |
| 4.3 MISP | Supports the MISP threat exchange protocol. |
| 4.4 TAXII | Supports the TAXII threat exchange protocol standard. |
| 4.5 JSON | Supports the JSON protocol data exchange format. |
| 4.6 CSV | Supports the CSV data expression standard. |
| 4.7 XML | Supports the XML-based threat exchange. |
| 4.8 OpenIOC | Supports the OpenIOC cybersecurity artefact description standard. |
| 4.9 Plain Text | Supports plain text data expression. |
| 4.10 RSS | Supports the RSS feed standard. |
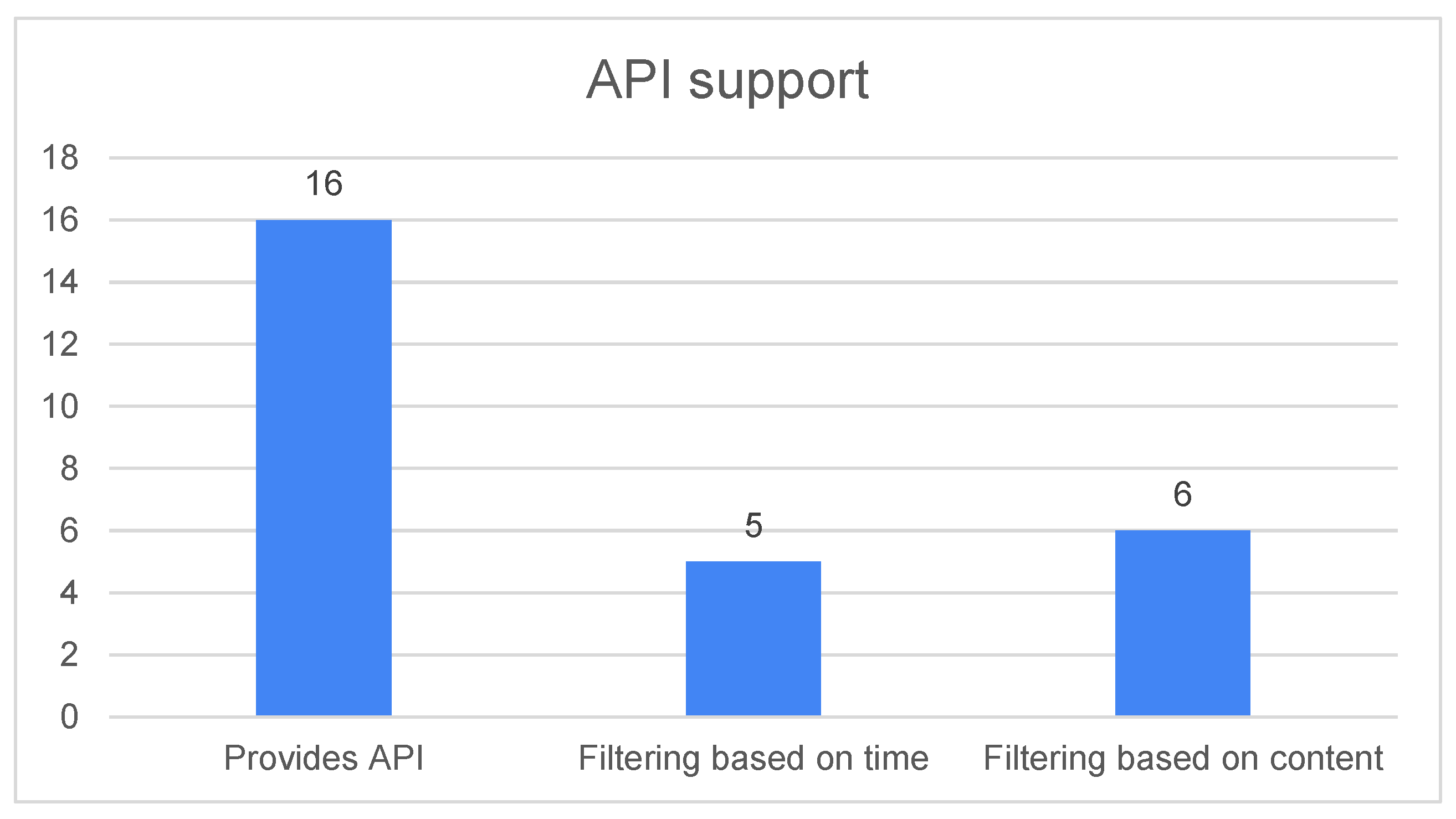
| 5 Advanced API | Indicates whether a data source supports or enables relevant advanced API features. |
| 5.1 Supports API | The source implements an API, such as REST. |
| 5.2 Filtering based on time | Supports filtering based on time for data access. Relevant for data collection to only collect entries since last access. |
| 5.3 Filtering based on content | Supports filtering based on content. Relevant for context specific data collection. |
References
- Bissell, K.; LaSalle, R.M.; Dal Cin, P. The cost of cybercrime—Ninth annual cost of cybercrime study. Technical report, Accenture, 2019. Independently conducted by Ponemon Institute LLC and jointly developed by Accenture. Available online: https://www.accenture.com/_acnmedia/pdf-96/accenture-2019-cost-of-cybercrime-study-final.pdf (accessed on 3 March 2020).
- Kellermann, T.; Young, B. Modern Bank Heists: The Bank Robbery Shifts to Cyberspace. Technical report, Carbon Black, OPTIV, 2019. Available online: https://www.carbonblack.com/resources/threat-research/modern-bank-heists-the-bank-robbery-shifts-to-cyberspace/ (accessed on 3 March 2020).
- Johnson, C.S.; Badger, M.L.; Waltermire, D.A.; Snyder, J.; Skorupka, C. Guide to Cyber Threat Information Sharing; Special Publication (SP) 800-150; National Institute of Standards and Technology: Gaithersburg, MD, USA, 2016. [Google Scholar] [CrossRef]
- Brown, R.; Lee, R.M. The Evolution of Cyber Threat Intelligence (CTI): 2019 SANS CTI Survey, 2019. SANS Institute. Available online: https://www.sans.org/reading-room/whitepapers/threats/paper/38790 (accessed on 3 March 2020).
- Tounsi, W.; Rais, H. A survey on technical threat intelligence in the age of sophisticated cyber attacks. Comput. Secur. 2018, 72, 212–233. [Google Scholar] [CrossRef]
- European Parliament and Council. Directive (EU) 2016/1148 concerning measures for a high common level of security of network and information systems across the Union. Official Journal of the European Union. 2016. Available online: https://eur-lex.europa.eu/eli/dir/2016/1148/oj (accessed on 3 March 2020).
- European Telecommunications Standards Institute (ETSI). CYBER; Implementation of the Network and Information Security (NIS) Directive; TR 103 456; European Telecommunications Standards Institute: Sophia Antipolis, France, 2017. [Google Scholar]
- ENISA. CSIRTs in Europe. Available online: https://www.enisa.europa.eu/topics/csirts-in-europe/csirt-inventory (accessed on 3 March 2020).
- US Department of Homeland Security. Cyber Information Sharing and Collaboration Program (CISCP). Available online: https://www.cisa.gov/ciscp (accessed on 3 March 2020).
- US Department of Homeland Security. Automated Indicator Sharing (AIS). Available online: https://www.cisa.gov/automated-indicator-sharing-ais (accessed on 3 March 2020).
- ODNI. A Guide to Cyber Attribution. Office of the Director of National Intelligence, 2018. Available online: https://www.dni.gov/files/CTIIC/documents/ODNI_A_Guide_to_Cyber_Attribution.pdf (accessed on 3 March 2020).
- Chismon, D.; Ruks, M. Threat Intelligence: Collecting, Analysing, Evaluating. MWR InfoSecurity, Whitepaper, 2015. Available online: https://www.foo.be/docs/informations-sharing/Threat-Intelligence-Whitepaper.pdf (accessed on 3 March 2020).
- ENISA. Actionable Information for Security Incident Response; Technical Report; European Union Agency for Network and Information Security: Helion, Greece, 2014; Available online: https://www.enisa.europa.eu/publications/actionable-information-for-security/at_download/fullReport (accessed on 3 March 2020).
- Burger, E.W.; Goodman, M.D.; Kampanakis, P.; Zhu, K.A. Taxonomy Model for Cyber Threat Intelligence Information Exchange Technologies. In Proceedings of the 2014 ACM Workshop on Information Sharing & Collaborative Security, Vienna, Austria, 23–25 October 2014; pp. 51–60. [Google Scholar] [CrossRef]
- Skopik, F.; Settanni, G.; Fiedler, R. A problem shared is a problem halved: A survey on the dimensions of collective cyber defense through security information sharing. Comput. Secur. 2016, 60, 154–176. [Google Scholar] [CrossRef]
- European Parliament and Council. Regulation (EU) 2016/679 of 27 April 2016 on the protection of natural persons with regard to the processing of personal data and on the free movement of such data, and repealing Directive 95/46/EC (General Data Protection Regulation). Off. J. Eur. Union L 2016, 119, 1–88. Available online: http://eur-lex.europa.eu/legal-content/en/TXT/?uri=CELEX%3A32016R0679 (accessed on 3 March 2020).
- ISO Central Secretary. ISO/IEC 27010:2015: Information Technology—Security Techniques—Information Security Management for Inter-Sector and Inter-Organizational Communications; Standard; International Organization for Standardization: Geneva, Switzerland, 2015. [Google Scholar]
- Schaberreiter, T.; Kupfersberger, V.; Rantos, K.; Spyros, A.; Papanikolaou, A.; Ilioudis, C.; Quirchmayr, G. A Quantitative Evaluation of Trust in the Quality of Cyber Threat Intelligence Sources. In Proceedings of the 14th International Conference on Availability, Reliability and Security, Canterbury, UK, 26–29 August 2019; pp. 83:1–83:10. [Google Scholar] [CrossRef]
- Rutkowski, A.; Kadobayashi, Y.; Furey, I.; Rajnovic, D.; Martin, R.; Takahashi, T.; Schultz, C.; Reid, G.; Schudel, G.; Hird, M.; et al. CYBEX – The Cybersecurity Information Exchange Framework (X. 1500). Comput. Commun. Rev. 2010, 40, 59–64. [Google Scholar] [CrossRef]
- Sadique, F.; Bakhshaliyev, K.; Springer, J.; Sengupta, S. A System Architecture of Cybersecurity Information Exchange with Privacy (CYBEX-P). In Proceedings of the 2019 IEEE 9th Annual Computing and Communication Workshop and Conference (CCWC), Las Vegas, NV, USA, 7–9 January 2019; pp. 493–498. [Google Scholar] [CrossRef]
- Bishop, M.; Bhumiratana, B.; Crawford, R.; Levitt, K. How to sanitize data? In Proceedings of the 13th IEEE International Workshops on Enabling Technologies: Infrastructure for Collaborative Enterprises, Modena, Italy, 14–16 June 2004; pp. 217–222. [Google Scholar] [CrossRef]
- ISAO Standards Organization. ISAO 300-2: Automated Cyber Threat Intelligence Sharing; Standard; ISAO Standards Organization: San Antonio, TX, USA, 2019. [Google Scholar]
- FIRST. Traffic Light Protocol (TLP), FIRST Standards Definitions and Usage Guidance—Version 1.0. Forum of Incident Response and Security Teams (FIRST). Available online: https://www.first.org/tlp/docs/tlp-v1.pdf (accessed on 3 March 2020).
- FIRST. Information Exchange Policy Framework, Version 1.0. Forum of Incident Response and Security Teams (FIRST). Available online: https://www.first.org/iep/ (accessed on 3 March 2020).
- OASIS. Structured Threat Information Expression (STIX). Available online: https://www.oasis-open.org/committees/tc_home.php?wg_abbrev=cti (accessed on 3 March 2020).
- MITRE. Cyber Observable eXpression. A Structured Language for Cyber Observables (CybOX). Available online: https://cybox.mitre.org/about/ (accessed on 3 March 2020).
- Malware Information Sharing Platform (MISP). Available online: https://www.misp-project.org/ (accessed on 3 March 2020).
- MITRE. Common Attack Pattern Enumeration and Classification (CAPEC). Available online: https://capec.mitre.org/index.html (accessed on 3 March 2020).
- Malware Attribute Enumeration and Characterization (MAEC). Available online: https://maecproject.github.io/ (accessed on 3 March 2020).
- Danyliw, R. The Incident Object Description Exchange Format Version 2. RFC 7970, 2016. Available online: https://tools.ietf.org/html/rfc7970 (accessed on 3 March 2020).
- Kampanakis, P.; Suzuki, M. Incident Object Description Exchange Format Usage Guidance. RFC 8274, 2017. Available online: https://tools.ietf.org/html/rfc8274 (accessed on 3 March 2020).
- Debar, H.; Curry, D.; Feinstein, B. The Intrusion Detection Message Exchange Format (IDMEF). RFC 4765, 2007. Available online: https://tools.ietf.org/html/rfc4765 (accessed on 3 March 2020).
- Characterizing Malware with MAEC and STIX, Version 1.0, 2014. Available online: https://stixproject.github.io/about/Characterizing_Malware_MAEC_and_STIX_v1.0.pdf (accessed on 3 March 2020).
- OASIS. stix2-elevator Documentation; Release 1.0.0; OASIS Open: Burlington, MA, USA, 2019. [Google Scholar]
- OASIS. stix2-elevator – Mappings from STIX 1.x to STIX 2.x. Available online: https://stix2-elevator.readthedocs.io/en/latest/stix-mappings.html (accessed on 3 March 2020).
- Common Vulnerability Reporting Framework (CVRF). Version 1.2. OASIS Common Security Advisory Framework (CSAF). Available online: http://docs.oasis-open.org/csaf/csaf-cvrf/v1.2/csaf-cvrf-v1.2.html/ (accessed on 3 March 2020).
- OASIS. TAXIITM Version 2.0, Working Draft 02. OASIS standard, 2017. Available online: https://www.oasis-open.org/committees/cti/ (accessed on 3 March 2020).
- Field, J.; Banghart, S.; Waltermire, D. Resource-Oriented Lightweight Information Exchange (ROLIE). RFC 8322, 2018. Available online: https://tools.ietf.org/html/rfc8322 (accessed on 3 March 2020).
- Banghart, S.; Field, J. Definition of ROLIE CSIRT Extension. Internet-Draft draft-ietf-mile-rolie-csirt-05, IETF Secretariat, 2019. Available online: http://www.ietf.org/internet-drafts/draft-ietf-mile-rolie-csirt-05.txt (accessed on 3 March 2020).
- Banghart, S. Definition of the ROLIE Vulnerability Extension. Internet-Draft draft-ietf-mile-rolie-vuln-02, IETF Secretariat, 2019. Available online: http://www.ietf.org/internet-drafts/draft-ietf-mile-rolie-vuln-02.txt (accessed on 3 March 2020).
- ENISA. State of Vulnerabilities 2018/2019—Analysis of Events in the Life of Vulnerabilities. Technical report, European Union Agency for Network and Information Security, 2019. Available online: https://www.enisa.europa.eu/publications/technical-reports-on-cybersecurity-situation-the-state-of-cyber-security-vulnerabilities/ (accessed on 3 March 2020).
| Technology | Format | Type of Data |
|---|---|---|
| STIX1.x | XML | TTP, Threat Actor, Incident, Exploit Target, Course of Action, Report, Package |
| STIX2.x | JSON | Attack Pattern, Campaign, Course of Action, Identity, Indicator, Intrusion Set, Malware, Observed Data, Report, Threat Actor, Tool, Vulnerability, Sighting |
| MISP | JSON | Sighting, Threat Actor, Incident, Network Activity, Antivirus Detection, Hashes, Malware Sample, External Analysis, Traffic Light Protocol |
| CAPEC | XML | Attack Pattern, Cross Site Forgery, SQL Injection, Buffer Overflow |
| MAEC | JSON | Malware, Cyber Observable, Entity Association, Incident Management |
| IODEFv2 | XML/HTML | Incident Management, Hashes, Indicator |
| IDMEF | XML | IP Addresses, Malware, Alert, (Login, Date of Creation, Classification) |
| Semantic/Syntactic Formats | Sources |
|---|---|
| STIX1 | CRITs, MISP Platform, OTX AlienVault, US CERT AIS |
| STIX2 | Abuse.ch, Anomali STAXX, MISP Platform |
| MISP | MISP Platform |
| TAXII | Anomali STAXX, CRITs, OTX AlienVault, US CERT AIS |
| JSON | Block List Project, CINSscore, Dshield, Fortinet, Google Safebrowsing, Hybrid Analysis, Malc0de, MalShare, MISP Platform, OpenPhish, OTX AlienVault, PhishTank, Proofpoint, Shadowserver, ThreatMiner, VirusTotal |
| CSV | Abuse.ch, Autoshun, MISP Platform, OpenPhish, OTX AlienVault, PhishTank, Proofpoint, Shadowserver, Spamhaus, ThreatMiner |
| XML | Fortinet, Hybrid Analysis, PhishTank |
| OpenIOC | MISP Platform, OTX AlienVault |
| Plain Text | Abuse.ch, Bambenek, Bitdefender (Advanced Threat Intelligence), Block List Project, BruteForceBlocker, CERT-EU, CINSscore, Comodo Site Inspector, DNS8, Dshield, ESET, Fortinet, Malc0de, MalShare, National CERTs (CERT-FI), OpenPhish, Spamhaus, TalosIntelligence, Trustwave |
| RSS | CERT-EU |
| API Support | Sources |
|---|---|
| Provides API | Abuse.ch, Autoshun, Bitdefender (Advanced Threat Intelligence, CRITs, Dshield, ESET, Fortinet, Google Safebrowsing, Hybrid Analysis, Malshare, MISP Platform, OTX AlienVault, PhishTank, Threat Miner, Virus Total |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Rantos, K.; Spyros, A.; Papanikolaou, A.; Kritsas, A.; Ilioudis, C.; Katos, V. Interoperability Challenges in the Cybersecurity Information Sharing Ecosystem. Computers 2020, 9, 18. https://doi.org/10.3390/computers9010018
Rantos K, Spyros A, Papanikolaou A, Kritsas A, Ilioudis C, Katos V. Interoperability Challenges in the Cybersecurity Information Sharing Ecosystem. Computers. 2020; 9(1):18. https://doi.org/10.3390/computers9010018
Chicago/Turabian StyleRantos, Konstantinos, Arnolnt Spyros, Alexandros Papanikolaou, Antonios Kritsas, Christos Ilioudis, and Vasilios Katos. 2020. "Interoperability Challenges in the Cybersecurity Information Sharing Ecosystem" Computers 9, no. 1: 18. https://doi.org/10.3390/computers9010018
APA StyleRantos, K., Spyros, A., Papanikolaou, A., Kritsas, A., Ilioudis, C., & Katos, V. (2020). Interoperability Challenges in the Cybersecurity Information Sharing Ecosystem. Computers, 9(1), 18. https://doi.org/10.3390/computers9010018







