A Multimodal Phishing Website Detection System Using Explainable Artificial Intelligence Technologies
Abstract
1. Introduction
- Malicious links, which appear as impostor websites infected with malware;
- Malicious file attachments, which are infected with malware to compromise the user’s computer or files;
- Fraudulent data entry forms, which prompt the user to enter their login credentials or other sensitive information to log in.
- The ambiguity in choosing a suitable dataset (training dataset);
- The composition of features included in the dataset;
- The architecture of the classifier model;
- The values of its hyperparameters;
- The means of selecting effective training algorithms (tuning) for the detection system;
- The mechanisms in interpreting the results, considering the natural limitations associated with the required computational costs of system implementation.
- Incorporate specialized models for four heterogeneous modalities (URL features and metadata, URL symbolic representation, HTML code, and web page screenshot) within a late fusion architecture;
- Incorporate a comprehensive, end-to-end explainable AI pipeline (SHAP, Grad-CAM, attention matrix analysis) that subsequently generates human-readable explanations utilizing a local LLM;
- Guarantee operational suitability in an SOC environment by means of microservice implementation, TI/SIEM integration, and testing against zero-day links and obfuscated attacks.
- A multimodal, late fusion architecture for the detection of phishing web resources is proposed. In this architecture, independent, specialized models for four modalities (CatBoost for URL features and metadata, CNN1D for symbolic URLs, a CodeBERT Transformer for HTML code, and EfficientNet-B7 for screenshots) are combined via a trainable meta-classifier that optimises the F1-score for the “phishing” class.
- A comprehensive, end-to-end explainable AI (XAI) pipeline is developed. It includes SHAP coefficients for tabular features, Grad-CAM and integrated gradients for symbolic and visual models, Transformer attention matrix analysis for HTML code, and the subsequent aggregation of these explanations by a local LLM into structured text reports intended for SOC analysts.
- An industrial-grade prototype system based on a microservice architecture with integration into the SOC/TI/SIEM framework is implemented and experimentally tested. It can process 0.5–1.1 thousand events per second, degrading to a subset of models while maintaining acceptable detection quality.
- A quality assessment is performed, which includes
- A comparison of single-modal and multimodal configurations on a proprietary, updated dataset (3.2 million URLs) and the public MTLP dataset, where the multimodal ensemble achieves an F1-score of 0.989 and 0.953, respectively;
- An exploratory assessment of resistance to typical obfuscation techniques;
- An expert review of the explanation utility with SOC analysts, using Fleiss’s and Cronbach’s to demonstrate the XAI component’s high consistency and practical applicability.
2. Analysis of Relevant Works
2.1. Description of Data Collection Methodology for Review of Sources
- “multimodal phishing detection” AND (“explainable AI” OR “XAI”);
- “deep learning” AND “phishing detection” AND (“SHAP” OR “LIME”);
- “large language models” AND “phishing”;
- “visual phishing detection” AND “interpretability”;
- “multimodal fusion” AND “cybersecurity”.
2.2. Review of Major Publications on Research into Multimodal Phishing Detection Systems
- There are now fairly representative open datasets containing a large number of URL samples with a wide variety of characteristics for both phishing sites (Kaggle, PhishTank, OpenPhish, etc.) and legitimate sites (Alexa Rank, crawlcommon, etc.), which can be used in the training phase for phishing web detection systems (see also [18]).
- An important stage preceding the training of such systems is a detailed study (preprocessing) of the set of features of phishing and legitimate websites contained in the dataset, including their normalization and coding, the analysis of correlations and informational significance, the possible reduction of the dimensionality of the feature space, etc., using methods of feature selection (detailed information about this can be found in [19,20,21]).
- Based on their research, the authors of several publications [21,22,23] pay close attention to the comparative assessment of the effectiveness of different ML models (as used in the specific issue of phishing web addresses) using such quality metrics as accuracy, recall, accuracy, and F1-score (harmonic mean). Based on their research, random forest algorithms, decision trees, and multilayer perceptrons are preferred.
- A hybrid ML model based on a set of classifiers [11] (for example, implemented by an RF algorithm) is particularly interesting in terms of improving the accuracy of phishing detection, where each individual classifier interacts with its own set of URL features and the final decision on the presence or absence of a phishing threat is taken by an arbitrator (MLP) using a separate voting system.
- The combination of the capabilities of natural language text analysis (natural language processing, NLP), including such features as URLs, text blocks, domains, and logs, with the processing of visual elements (screenshots) of a web page, as well as structural features of HTML code, within the framework of a multimodal concept [10,24,25], allows one not only to increase the precision and recall but also to predict the development of new types of phishing attacks, including generative adversarial attacks.
| No. | Authors | Dataset | ML/DL Models | Accuracy |
|---|---|---|---|---|
| 1. | Al-Diabat M. [19] | University of Irvine Repository (11,000 URLs, based on PhishTank and Yahoo Directory, 30 features) | Classifiers based on C4.5 and IREP algorithms The scikit-learn library version 1.8 was used. | C4.5—96% IREP—95% |
| 2. | Mahajan R., Siddavatam I. [22] | Phishtank (19,653 URLs) + Alexa Rank (17,058 URLs) | Decision trees (DT), RF, SVM The scikit-learn library version 1.8 was used. | RF—97.14% |
| 3. | Almomani A., Alauthman M., Shatnawi M.T. et al. [20] | Huddersfield University Dataset 1 (2456 URLs, 30 features); Dataset 2 (10,000 URLs, 48 features) | 16 ML models (RF, classification and regression trees (CART), logistic regression (LR), SVM, NN, Bayesian additive regression trees (BART), etc.) The scikit-learn library version 1.8 was used. | RF—96% (Dataset 1) and 98% (Dataset 2) |
| 4. | Khera M., Prasad T., Xess L.D., et al. [23] | Phishing website dataset | 9 ML models (RF, DT, LR, K-nearest neighbors (kNN), XGBoost, XBNet, etc.) The scikit-learn library version 1.8 was used. | RF—97.3% |
| 5. | Alazaidah R., Al-Shaikh A., Almousa M.R. et al. [21] | Dataset 1 (11,055 URLs, 30 features, 2 classes) Dataset 2 (1353 URLs, 9 features, 3 classes) | 24 ML models, 6 learning strategies (Naive Bayes, LR, MLP, AdaBoost, RF, random tree, etc.) The scikit-learn library version 1.8 was used. | Filtered Classification J-48— 90.76% (Dataset 1); RF—97.26% (Dataset 2) |
| 6. | Aslam, S., Aslam, H., Manzoor, A. et al. [4] | Dataset 1 (DS1): Benign Yandex sites Dataset 2 (DS2): Benign sites from Common Crawl, the Alexa database, and phishing sites from PhishTank | LSTM | 96.04% |
| 7. | Ghaleb F.A., Alsaedi M., Saeed F., et al. [11] | Malicious URLs dataset (651,191 URLs) | Hybrid ML model: 3 × RF + multilayer perceptron (MLP) | 96.80% |
| 8. | Krotov E.Yu., [10] | Phishing website dataset (10,000 URLs) + Common Crawe | Multimodal system: CNN + LSTM (image + text) | 92% |
| 9. | Lee J., Lim P., et al. [24] | Open Phish (1585 URLs) + Alexa Rank (3000 URLs) | Multimodal system: GPT-4-turbo, Claude 3, Gemini Pro-Vision 1.0 | GPT-4—92% Claude 3—90% |
| 10. | Syed Sh. A., [25] | PhishTank, APWG, Open Phish | BERT (text) + ResNet + VGG16 (image) | 96.2% |
2.3. Classification of Data Types for Feature Generation in the Detection of Phishing Attacks
- The main categories of URL features: lexical, syntactic, semantic, entropic, statistical;
- The main categories of structural HTML features: DOM structural, data entry form structure, characteristics of the page’s script component, CSS and style features of the design template, and semantic HTML features;
- The main categories of visual features: logo detection, layout analysis, color analysis, visual similarity, and image quality.
- URL features provide fast initial analysis with relatively high accuracy (up to 93%) but are vulnerable to attacks by URL obfuscation;
- HTML features provide the most detailed information about the attack structure and are particularly effective in detecting credential phishing;
- Visual features are critical in detecting brand impersonation and visual cloning attacks, achieving 94–98% accuracy, but require significant computational resources;
- Multimodal integration outperforms single-modal approaches in the F1-score by 8–15 percent, but it increases the time to classify (up to 5–10 s);
- Feature engineering remains an important step even in the use of deep learning, as hand-selected and hand-crafted features ensure interpretability and resilience to adversarial perturbations.
| Combination of Modalities | Number of Systems | Average Accuracy | Typical Architectures of ML Models |
|---|---|---|---|
| URL + HTML | 18 | 96.5–99.2% | CNN + LSTM, BERT [34,35] |
| URL + Visual | 12 | 93.4–97.8% | CNN + ResNet/VGG [36,37] |
| URL + HTML + Visual | 8 | 98.0–99.4% | Transformers, LLM [27,28] |
| All 5 types | 3 | 98.4–99.6% | Agent-based LLM systems [27] |
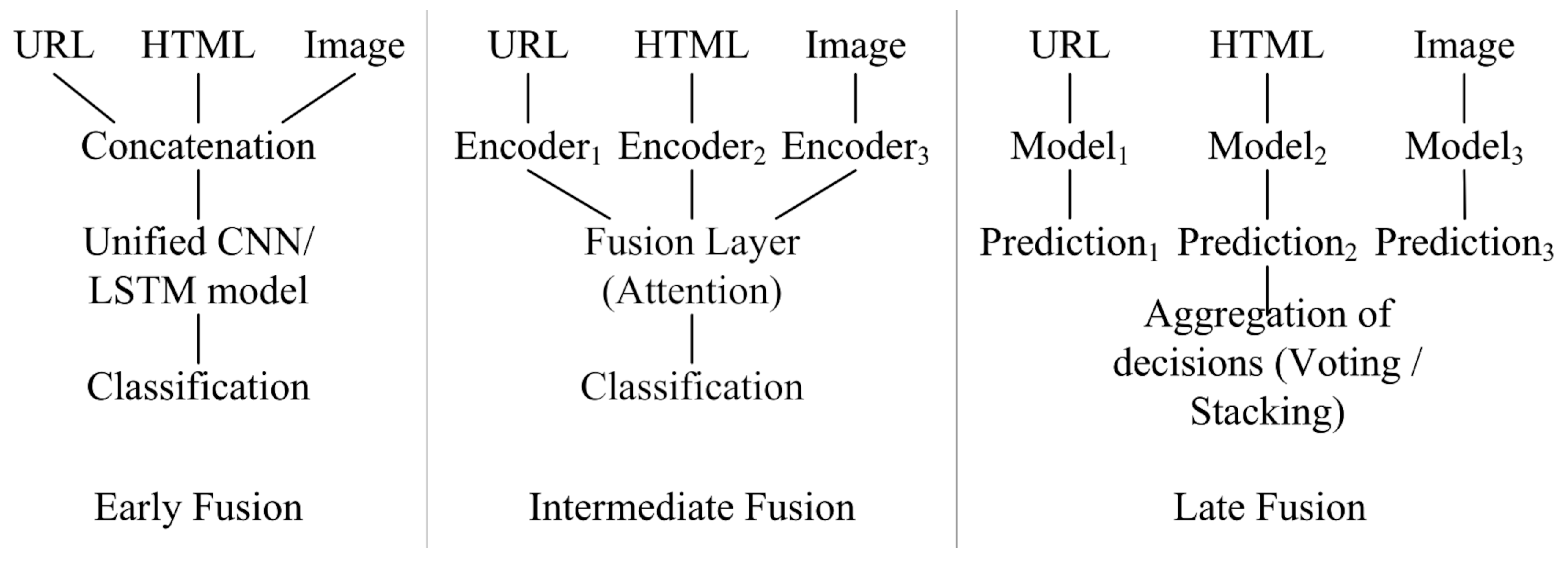
- Early fusion: Concatenates the properties of all modalities at the input level, followed by processing with one model. Advantages: Captures low-level correlations of features, simple architecture of the final model. Disadvantages: Loss of specificity of the modality, complexity of training.
- Intermediate fusion: Each modality is processed by a separate encoder and then the features are combined at an intermediate level by means of an attentional mechanism. It provides a balance between specificity and modality interaction.
- Late fusion: Independently train specialized models for each modality with decision aggregation by means of voting or stacking. Advantages: Model specialization, modularity, parallelism. Best results for heterogeneous data.
- Hybrid fusion: Combination of early and late fusion with adaptive weights. This strategy shows maximum performance with high architectural complexity.
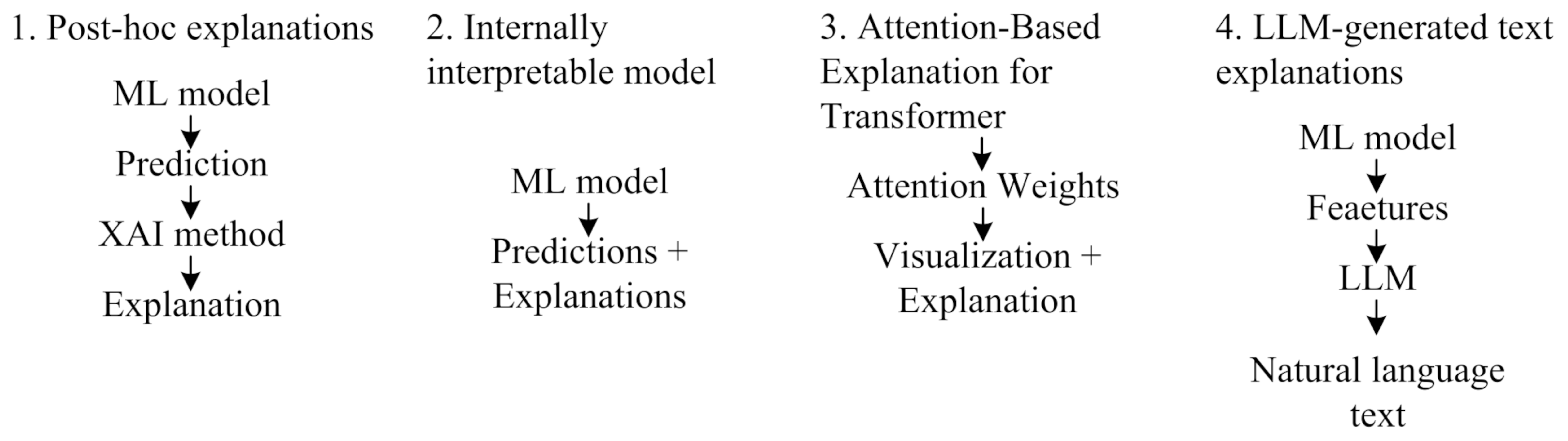
2.4. Explainable Artificial Intelligence Methods for Detecting Phishing Attacks
- Phishing website detection system [16]: Base classifier model (ML)—random forest (RF); training datasets (datasets)—PhishTank and Tranco; number of used URL features—26; Lorenz Zonoids (multivariate extension of the Gini coefficient) was used as a feature selection procedure (XAI method).
- Phishing website detection system [42]: Base classifier models—SVM and RF; dataset—Ebbu 2017; number of URL features—40; XAI methods—LIME and Explainable Boosting Machine (EBM); prediction accuracy—94.7% (for SVM) and 97.3% (for RF).
- A system for detecting phishing websites [43]: six ML models were studied (XGBoost, LightGBM, RF, kNN, Twin SVM, CNN) using four datasets (ISCX-URLs, P.L-URLs, Phish Guard URLs, Suspicious-URLs) and the XAI-LIME method; the XGBoost model showed the highest forecast accuracy of 96.8%.
2.5. Main Datasets Used to Train Multimodal ML Models for Phishing Attack Detection
- Phishing sites are accessible for an average of 4–8 h before being blocked, and datasets become quickly outdated;
- The ratio of legitimate URLs to phishing URLs ranges from 100 to 1 to 1000 to 1 in real traffic among corporate information systems;
- The percentage of annotation errors in community-driven datasets is quite high (up to 15%);
- Feature distributions are dynamic and change over time (concept drift).
2.6. Promising Multimodal Systems for Analysis of Phishing Attacks
2.7. Findings from the Systematic Review
- Contemporary machine learning models exhibit susceptibility to adversarial attacks [53], while existing certified defences impose prohibitive computational overheads. This highlights critical research needs: (1) the development of scalable certified defences for deployment in production systems, (2) the implementation of adaptive adversarial training robust to unknown attack types, and (3) the creation of robustness benchmarks tailored to the domain of phishing attacks.
- The most advanced detection systems for zero-day phishing threats attain recall metrics in the range of 87–94%. Existing systems consistently fail to detect 6–13% of unknown threats. To mitigate this vulnerability, actual research [26,28] efforts are focused on advancing few-shot learning, meta-learning, and anomaly detection to address these limitations.
- Current hybrid architectures demonstrate good detection accuracy, achieving performance rates of 98–99.68%. The integration of large language models (LLMs) has yielded a significant advancement in zero-day detection, with recall metrics ranging from 87 to 94%, while also enabling the generation of natural language explanations. Additionally, explainable artificial intelligence (XAI) methodologies are utilized in a substantial portion (80%) of recent research.
- The adoption of multimodal systems has resulted in an improvement in accuracy metrics ranging from 5% to 12%. It has been demonstrated that late fusion techniques produce better outcomes when dealing with heterogeneous modalities. Furthermore, agent-based LLM architectures constitute a new paradigm characterized by their integrated reasoning functionalities.
- A critical challenge is to ensure model adversarial robustness. This problem is characterized by a 3–9% decrease in accuracy, a temporal decay effect (an 8–15% degradation in performance without overfitting), and high LLM latency, which imposes significant real-time operational constraints.
- Utilize multiple heterogeneous modalities (URL and metadata, symbolic URL, HTML code, page screenshot) in a late-binding architecture featuring a trainable meta-classifier;
- Incorporate an end-to-end explainable AI (XAI) loop with modality-specific interpretation methods and the consolidation of natural language explanations via a local LLM;
- Are implemented as an industrial microservice prototype, integrated with SOC/TI/SIEM frameworks, and evaluated using both standard classification metrics and an assessment of explanation usefulness for real SOC analysts.
3. Design of a Multimodal Phishing Website Detection System Using Explainable Artificial Intelligence
3.1. Structural Diagram of the Web Resource Analysis System
- Feature Extraction;
- Context enrichment with data from external sources;
- Normalization, standardization, and the generation of a multimodal context.
- A module dedicated to data labeling, relabeling, and label validation;
- A database (DB1) for storing enriched and prepared data;
- A version management module for dataset tracking and synchronization with corresponding machine learning (ML) models;
- A balancing and augmentation module configured to generate training, validation, and test datasets.
- Machine learning (ML) models specifically designed for the analysis of URLs/metadata, images, and the source code of target resource pages;
- A late fusion multimodal module that operates based on a weighted model voting mechanism;
- A product model database (DB2).
- A performance monitoring module;
- A data drift detection module, which detects decreased model classification accuracy on freshly labeled data;
- The retraining and/or updating of model modules at specified intervals.
- SOC analytics dashboard;
- Decision verification and data markup module.
3.2. Key ML Models in a Multimodal Web Resource Analysis System
3.2.1. Developing a URL Analysis Model
—CatBoost Model for Analysis of URL-Extracted Features and Metadata
- More than 150,000 domain names from real phishing campaigns (picked by PhishTank, OpenPhish, VirusTotal);
- 200,000 legitimate domains from Alexa Top and SSL certificates (Let’s Encrypt, Mozilla).
—CNN1D for URL Analysis at the Character Level
- The ability to extract local patterns as substrings characteristic of phishing URLs (e.g., “login,” “secure”) through the use of convolutions with kernels of varying sizes;
- High analysis efficiency on the CPU because of the reduced number of model parameters, which allows for the simultaneous analysis of short (“@,” “//”) and long (“login”) URL anomalies, improving the classification accuracy.
- Phishing URLs (from open sources such as PhishTank and OpenPhish);
- Legitimate URLs (from popular services, including Google, Microsoft, and banking portals);
- Metadata—page source code, domain WHOIS data, screenshots, and binary labels (“phishing”/“not phishing”).
3.2.2. Development of a Model for the Analysis of Visual Images of the Main Page of a Web Resource
—CNN2D Model for Visual Image Analysis Based on Pretrained EfficientNet-B7
3.2.3. Development of a Model for the Analysis of the HTML Code of the Main Page of a Web Resource
—Transformer for Analysis of the HTML Code of the Main Page Based on the Pretrained CodeBERT
3.2.4. Development of a Meta-Classifier Model
- Utilizes estimations of class membership probabilities derived from the base models;
- Determines the weighting of modality contributions based on the validation sample to optimize the F1-score for the positive class (phishing);
- Facilitates operation with partially accessible modalities (for example, instances where screenshots are unavailable or HTML cannot be downloaded), which is essential for security operations center (SOC) environments.
- Description of the process of base model training. Models to are trained utilizing the original features of their respective modalities. For each object within the validation set, phishing probability predictions are generated by the four models.
- Creating the training set for model M5. For each URL, a meta-feature vector is developed comprising the M1–M4 predictions and consistency aggregates—specifically, the mean, variance, and the total number of models that identified the phishing class. The target labels are consistent with those specified in the original problem.
- Training a meta-classifier. A secondary tabular classifier is developed to optimize the F1-score for the positive class, utilizing the derived meta-features. Cross-validation is employed to select hyperparameters and the decision threshold; this facilitates a reduction in unidentified phishing attacks while simultaneously managing the proliferation of false positives.
- Inference mode on new data. During the operational phase, models to calculate probability estimates in parallel. These probabilities are subsequently provided to model , which generates the final estimate.
- Adaptive modality weighting. URL-based models occasionally generate false positives for popular legitimate domains (such as vk.com and rutube.ru), whereas a visual model correctly identifies these sites as non-phishing. A meta-classifier facilitates the downweighting of the URL branch in such instances—for example, when a high-confidence URL model prediction coincides with a low-confidence visual model output. Conversely, it enhances the contributions of those modalities that provide more reliable indicators for a specific class of examples.
- Accounting for non-linear interactions between modalities. Stacking facilitates the consideration of complex scenarios—for instance, where a URL appears relatively innocuous yet the HTML code contains suspicious input forms and redirects, and the visual appearance mimics a brand logo. These combinations are characteristically found in phishing attacks. Simple voting mechanisms fail to distinguish between instances where “two moderately confident models agree” and those where “one model strongly disagrees while others remain uncertain”; conversely, a meta-classifier can be trained to assign distinct final decisions to these specific patterns.
- Prioritizing the positive class (phishing) and managing the balance between false positives and false negatives. In the training of the classifier, the primary performance metric utilized is the F1-score for the “phishing” class. This approach facilitates a strategic shift in the balance towards minimizing false negatives (missed attacks) while maintaining an acceptable false positive rate, as previously established for the CatBoost model. Furthermore, the decision threshold for may be independently adjusted for positive and negative alerts, in accordance with specific SOC regulations.
- Preserving functionality during modality unavailability. In a production environment, various data sources may periodically become unavailable; for instance, a screenshot might be absent, HTML code may fail to load, or integration with external threat intelligence (TI) services could be temporarily suspended owing to security policies. The meta-classifier can be trained on incomplete feature combinations—utilizing techniques such as modality masking or dropout—enabling it to transition seamlessly from full multimodal operation to a reduced configuration. Compared to a monolithic hybrid architecture, this strategy substantially increases the system’s fault tolerance.
3.3. Key XAI Technologies as Part of a Multimodal Web Resource Analysis System
3.3.1. SHAP Coefficients for Interpreting the Performance of the M1 CatBoost Model
3.3.2. Grad-CAM and Integrated Gradients for Interpreting the Performance of the M2 CNN1D Model
3.3.3. Grad-CAM for Interpreting the Performance of the CNN2D Model
3.3.4. Attention Matrix for Interpreting the Work of the Model, CodeBERT
3.3.5. LLM Explainer for Preparing Final Reports in Natural Language
3.4. Software Architecture of a Web Resource Analysis System
- “Telegram bot” (App-tg_bot)—Implements the functionality of receiving incoming messages from users and serves as the first link in the value verification chain.
- “Machine learning module”—A container with a machine learning model is deployed on the basis of the “m_service” image, where the “/check_domain” endpoint is implemented via the Flask API. When a POST request with a domain is received, multistage processing occurs.
- “Threat intelligence module” (App-ti_service)—A container for integration with external reputation services such as Kaspersky TI, VirusTotal TI, and others via an API implemented on FastAPI.
- “Data storage service”—A database for the long-term storage of all system operation results; a container with a MongoDB database is used.
- Container for updating Elasticsearch (“App-update_es”)—In the test environment, the project uses Elasticsearch to analyze domains, where the “update_es” container is responsible for regularly updating the “idecoutm” index. Each time the script is run, a complete check is performed to see if the current domain has been processed before: if a match is found, the document is updated to reflect the new results, and, if not, a full check cycle is started. The update occurs every 3 s, which ensures that the data in Elasticsearch are up-to-date and enables the quick tracking of changes in the analyzed domains. With the help of Praeco (Elasticsearch alerting made simple; URL: https://github.com/johnsusek/praeco (accessed on 15 February 2025)), a correlation rule was created to notify analysts at the SOC, which allows for a prompt response to information security incidents.
- Container management component (“Portainer”)—Uses the “portainer/portainer-ce:latest” image and provides a web interface for managing all of the project’s Docker containers. Special attention was paid during the design to safety and data isolation. All containers run in a single virtual segment, with no external ports exposed except for the Telegram API and the web administration interfaces. All requests are handled over HTTPS, logged, and may be signed for investigation.
- Processing queries in real time;
- Storing results and metadata for subsequent analysis;
- Scaling individual modules independently (e.g., multiplying ml_service);
- Integrating with external sources via APIs and with internal security systems via SIEM interfaces;
- Providing a visual interface for both users (via Telegram) and administrators (via Portainer and Mongo Express).
4. Computational Experiment to Evaluate the Performance of the Web-Based Resource Analysis System
4.1. Computational Experiment I on the Prepared Dataset for Models and
4.1.1. First Phase of Testing: Collecting the Dataset () and Preparing Models
- Phishing URLs were obtained from open repositories Phishing Site URLs (Kaggle), OpenPhish, URLHaus, and PhishTank, where malicious link databases are updated daily;
- Legitimate URLs were selected from the Alexa and Majestic Million Top 1 Million Websites lists, as well as downloaded from secure corporate proxy logs.
- Cross-checks via the VirusTotal API;
- A built-in reputational score checking module;
- Manual checks by WHOIS data (registration date, TLD zone, domain activity);
- Validation using OpenAI and QwQ-32B models in batch mode.
- 1.6 million phishing web resources;
- 1.6 million legitimate web resources.
4.1.2. Second Stage of Testing—System Throughput Assessment
- Corporate mail gateway logs;
- Traffic through proxy servers and web filters;
- Specially generated requests through a Telegram bot.
4.1.3. Third Stage of Testing—Testing as Part of the SOC
4.1.4. Fourth Stage of Testing—Zero-Day Resource Testing
- Google Safe Browsing;
- The OpenPhish Detection API;
- The URLhaus API.
4.1.5. Testing the Subsystem for the Explanation of Positive Responses
4.1.6. Summary Results of Computational Experiment I
4.2. Computational Experiment II on the Prepared Dataset for Models and
4.3. Computational Experiment III on the Prepared Dataset for All Models
4.4. Exploratory Assessment of Robustness of a Multimodal Architecture Against Conventional Obfuscation Techniques
4.5. Evaluating the Quality of Explanations Provided for Resulting Decisions
- Invents non-existent facts (non-existent organizations, IOCs, tactics, and techniques);
- Incorrectly associates URLs with techniques/tactics;
- Generates explanations that do not logically follow from internal features and the retrieved context.
4.6. Discussion
- Enhanced detection accuracy: It improves the detection accuracy for phishing attacks that are not identifiable by a single modality. This is because attackers face a greater challenge in bypassing all analysis modalities simultaneously.
- Reduced false positives: Using a set of models reduces the number of false positives.
- Zero-day attack detection: The system is capable of detecting novel (zero-day) attacks by analyzing a comprehensive combination of features across different modalities.
- Improved interpretability: The XAI subsystem provides insights into each modality’s contribution, helping analysts to understand the rationale behind a detection decision.
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Abbreviations
| AI | Artificial Intelligence |
| APWG | Anti-Phishing Working Group |
| CNNs | Convolutional Neural Networks |
| DL | Deep Learning |
| DOM | Document Object Model |
| DT | Decision Trees |
| EBM | Explainable Boosting Machine |
| ELK | Elasticsearch, Logstash, Kibana |
| HTML | HyperText Markup Language |
| IS | Information Security |
| kNN | k-Nearest Neighbors |
| LIME | Local Interpretable Model-Agnostic Explanations |
| LLMs | Large Language Models |
| LR | Logistic Regression |
| LSTM | Long Short-Term Memory |
| ML | Machine Learning |
| MTLP | Multitype Logo Phishing |
| NLP | Natural Language Processing |
| NNs | Neural Networks |
| PaaS | Phishing-as-a-Service |
| RF | Random Forest |
| ROC-AUC | Area Under the ROC Curve |
| SHAP | Shapley Additive Explanations |
| SIEM | Security Information and Event Management |
| SOC | Security Operations Center |
| SVMs | Support Vector Machines |
| TI | Threat Intelligence |
| TLD | Top-Level Domain |
| URL | Uniform Resource Locator |
| VGG | Visual Geometry Group |
| XAI | Explainable Artificial Intelligence |
Appendix A. Excerpt from a Technical Report on the Results of the Classification of a Synthetic Web Resource, Which Was Generated Utilizing a Localized Large Language Model
| ## TECHNICAL APPENDIX ### Complete Model Predictions CatBoost (URL features): 98.7% phishing Character-CNN (URL chars): 96.2% phishing CodeBERT (HTML structure): 95.8% phishing EfficientNet-B7 (Visual): 97.8% phishing Consensus Average: 97.1% phishing Standard Deviation: 1.3% Agreement Level: VERY HIGH ### Complete SHAP Values (CatBoost) domain_age: −0.45 (3 days old → suspicious) tld_type: −0.38 (.tk → free, abuse-prone) typosquatting_score: −0.52 (paypa1 vs paypal → deliberate) url_length: −0.12 (slightly long) subdomain_count: −0.08 (1 subdomain) has_https: +0.15 (has HTTPS, but…) …[additional features] ### Character-CNN Attribution Top 10 Position 8–13 “paypa1”: IG attribution 0.92 Position 13 “1”: IG attribution 0.95 (critical!) Position 22–24 “.tk”: IG attribution 0.88 Position 15–21 “secure”: IG attribution 0.45 …[full attribution map available] ### CodeBERT Attention Top 10 Tokens <input name=“creditcard”>: 0.95 weight (CRITICAL) <input type=“password”>: 0.89 weight <form action=“http://…”>: 0.82 weight (insecure) “urgent”: 0.78 weight “suspended”: 0.78 weight “verify”: 0.68 weight “account”: 0.65 weight …[full token list available] Visual Grad-CAM Regions (Top 5) |
| Region 1: Logo area - Position: top-left (header) - Activation: 0.95/1.0 - Area: 2.1% of page - Text: “PAYPA1 Security Center” - Elements: visual_element, square_element Region 2: Warning banner - Position: center (main_content) - Activation: 1.0/1.0 (maximum!) - Area: 8.5% of page - Text: “URGENT: Account suspended in 24 h” - Elements: visual_element Region 3: Form area - Position: center (form_area) - Activation: 0.88/1.0 - Area: 3.2% of page - Text: “Credit Card Number”, “CVV” - Elements: input_field (multiple) Region 4: URL bar representation - Position: top-center (header) - Activation: 0.85/1.0 - Text: “https://paypa1-secure.tk” Region 5: Footer - Position: bottom (footer) - Activation: 0.45/1.0 - Text: “Copyright 2024 PayPa1” [with typo] - Elements: text, poor_quality |
| REPORT METADATA Report Generated: 23 October 2025 18:30:51 UTC Analysis Duration: 3.7 s Models Used: 4 (CatBoost, CharCNN, CodeBERT, EfficientNet-B7) XAI Methods: 6 (SHAP, Grad-CAM 1D, IntGrad, Attention, Grad-CAM 2D, Text Convert) LLM Model: Qwen2.5-32B-Instruct Confidence: VERY HIGH Analyst Review: RECOMMENDED (for quality assurance) |
| END OF REPORT This report was generated by an AI-powered phishing detection system combining multiple deep learning models with explainable AI techniques. While highly accurate, human expert review is recommended for critical cases. |
References
- Golushko, A. Current Cyber Threats: Q4 2024–Q1 2025. Available online: https://ptsecurity.com (accessed on 2 February 2025).
- Group, A.P.W. Phishing Activity Trends Reports—1Q 2025. Available online: https://www.apwg.org (accessed on 2 February 2025).
- zvelo. Phishing Detection in Depth: Attack Types, Detection Tools, and More. Available online: https://www.zvelo.com (accessed on 2 February 2025).
- Aslam, S.; Aslam, H.; Manzoor, A.; Chen, H.; Rasool, A. AntiPhishStack: LSTM-Based Stacked Generalization Model for Optimized Phishing URL Detection. Symmetry 2024, 16, 248. [Google Scholar] [CrossRef]
- Basit, A.; Zafar, M.; Liu, X.; Javed, A.R.; Jalil, Z.; Kifayat, K. A comprehensive survey of AI-enabled phishing attacks detection techniques. Telecommun. Syst. 2021, 76, 139–154. [Google Scholar] [CrossRef]
- Lukmanova, K.; Kartak, V. The development of a phishing attack protection system using software-hardware implementation of machine learning methods. Model. Optim. Inf. Technol. 2024, 4, 1–8. [Google Scholar] [CrossRef]
- Kavya, S.; Sumathi, D. Staying ahead of phishers: A review of recent advances and emerging methodologies in phishing detection. Artif. Intell. Rev. 2024, 58, 50. [Google Scholar] [CrossRef]
- Kornyukhina, S.; Laponina, O. Exploring the Potential of Deep Learning Algorithms to Protect Against Phishing Attacks. Int. J. Open Inf. Technol. 2023, 11, 163–174. [Google Scholar]
- Li, W.; Manickam, S.; Chong, Y.W.; Leng, W.; Nanda, P. A State-of-the-Art Review on Phishing Website Detection Techniques. IEEE Access 2024, 12, 187976–188012. [Google Scholar] [CrossRef]
- Krotov, E. Applying Deep Learning Methods to Phishing Website Detection: Performance Analysis and Model Optimization. Curr. Res. 2025, 256, 60–69. [Google Scholar]
- Alsaedi, M.; Ghaleb, F.; Saeed, F.; Ahmad, J.; Alasli, M. Cyber Threat Intelligence-Based Malicious URL Detection Model Using Ensemble Learning. Sensors 2022, 22, 3373. [Google Scholar] [CrossRef]
- Aljofey, A.; Jiang, Q.; Rasool, A.; Chen, H.; Liu, W.; Qu, Q.; Wang, Y. An effective detection approach for phishing websites using URL and HTML features. Sci. Rep. 2022, 12, 8842. [Google Scholar] [CrossRef]
- Wangchuk, T.; Gonsalves, T. Multimodal Phishing Detection on Social Networking Sites: A Systematic Review. IEEE Access 2025, 13, 103405–103416. [Google Scholar] [CrossRef]
- Baltrušaitis, T.; Ahuja, C.; Morency, L.P. Multimodal Machine Learning: A Survey and Taxonomy. IEEE Transactions on Pattern Analysis and Machine Intelligence 2019, 41, 423–443. [Google Scholar] [CrossRef]
- Govindaraaj, J. The Role of Explainable AI in Understanding Phishing Susceptibility. J. Recent Trends Comput. Sci. Eng. JRTCSE 2024, 12, 1–6. [Google Scholar]
- Calzarossa, M.C.; Giudici, P.; Zieni, R. An assessment framework for explainable AI with applications to cybersecurity. Artif. Intell. Rev. 2025, 58, 150. [Google Scholar] [CrossRef]
- Shyni, E. Enhancing Phishing Detection with Explainable AI (XAI): A Transparent Cybersecurity Approach. 2025. Available online: https://smartsecuritytips.com/phishing-xai/ (accessed on 2 February 2025).
- Vrbančič, G.; Fister, I.; Podgorelec, V. Datasets for phishing websites detection. Data Brief 2020, 33, 106438. [Google Scholar] [CrossRef]
- Al-diabat, M. Detection and Prediction of Phishing Websites using Classification Mining Techniques. Int. J. Comput. Appl. 2016, 147, 5–11. [Google Scholar] [CrossRef]
- Almomani, A.; Alauthman, M.; Shatnawi, M.T.; Alweshah, M.; Alrosan, A.; Alomoush, W.; Gupta, B.B.; Gupta, B.B.; Gupta, B.B. Phishing Website Detection With Semantic Features Based on Machine Learning Classifiers: A Comparative Study. Int. J. Semant. Web Inf. Syst. 2022, 18, 1–24. [Google Scholar] [CrossRef]
- Alazaidah, R.; Al-Shaikh, A.; Almousa, M.; Khafajeh, H.; Samara, G.; Alzyoud, M.; Al-shanableh, N.; Almatarneh, S. Website Phishing Detection Using Machine Learning Techniques. J. Stat. Appl. Probab. 2024, 13, 119–129. [Google Scholar] [CrossRef]
- Mahajan, R.; Siddavatam, I. Phishing Website Detection using Machine Learning Algorithms. Int. J. Comput. Appl. 2018, 181, 45–47. [Google Scholar] [CrossRef]
- Khera, M.; Prasad, T.; Xess, L.; Singh, R.; Aiden, M.K. Malicious Website Detection using Machine Learning. Int. J. Eng. Res. Technol. (IJERT) 2022, 11, 19–27. [Google Scholar] [CrossRef]
- Lee, J.; Lim, P.; Hooi, B.; Divakaran, D.M. Multimodal Large Language Models for Phishing Webpage Detection and Identification. In Proceedings of the 2024 APWG Symposium on Electronic Crime Research (eCrime), Boston, MA, USA, 24–26 September 2024; pp. 1–13, Version Number: 1. [Google Scholar] [CrossRef]
- Syed, S.A. AI-Driven Detection of Phishing Attacks through Multimodal Analysis of Content and Design. Int. J. Innov. Res. Comput. Commun. Eng. 2024, 12, 9979–9987. [Google Scholar] [CrossRef]
- Trad, F.; Chehab, A. Large Multimodal Agents for Accurate Phishing Detection with Enhanced Token Optimization and Cost Reduction. In Proceedings of the 2024 2nd International Conference on Foundation and Large Language Models (FLLM), Dubai, United Arab Emirates, 26–29 November 2024; pp. 229–237. [Google Scholar] [CrossRef]
- Cao, T.; Huang, C.; Li, Y.; Wang, H.; He, A.; Oo, N.; Hooi, B. PhishAgent: A Robust Multimodal Agent for Phishing Webpage Detection. In Proceedings of the Thirty-Ninth AAAI Conference on Artificial Intelligence and Thirty-Seventh Conference on Innovative Applications of Artificial Intelligence and Fifteenth Symposium on Educational Advances in Artificial Intelligence (AAAI’25/IAAI’25/EAAI’25), Philadelphia, PA, USA, 25 February–4 March 2025; VAAAI Press: Washington, DC, USA, 2025; Volume 39, pp. 27869–27877. [Google Scholar] [CrossRef]
- Li, Y.; Huang, C.; Deng, S.; Lock, M.L.; Cao, T.; Oo, N.; Lim, H.W.; Hooi, B. KnowPhish: Large Language Models Meet Multimodal Knowledge Graphs for Enhancing Reference-Based Phishing Detection. In Proceedings of the 33rd USENIX Conference on Security Symposium (SEC ’24) USENIX Association, Philadelphia, PA, USA, 14–16 August 2024; pp. 793–810. [Google Scholar] [CrossRef]
- Alshingiti, Z.; Alaqel, R.; Al-Muhtadi, J.; Haq, Q.E.U.; Saleem, K.; Faheem, M.H. A Deep Learning-Based Phishing Detection System Using CNN, LSTM, and LSTM-CNN. Electronics 2023, 12, 232. [Google Scholar] [CrossRef]
- Aldakheel, E.A.; Zakariah, M.; Gashgari, G.A.; Almarshad, F.A.; Alzahrani, A.I.A. A Deep Learning-Based Innovative Technique for Phishing Detection in Modern Security with Uniform Resource Locators. Sensors 2023, 23, 4403. [Google Scholar] [CrossRef]
- Repository, U.M.L. PhiUSIIL Phishing URL Dataset. Available online: https://archive.ics.uci.edu/dataset/967 (accessed on 2 February 2025).
- Chiew, K.L.; Tan, C.L.; Wong, K.; Yong, K.S.; Tiong, W.K. A new hybrid ensemble feature selection framework for machine learning-based phishing detection system. Inf. Sci. 2019, 484, 153–166. [Google Scholar] [CrossRef]
- Shafin, S.S. An explainable feature selection framework for web phishing detection with machine learning. Data Sci. Manag. 2025, 8, 127–136. [Google Scholar] [CrossRef]
- Yoon, J.H.; Buu, S.J.; Kim, H.J. Phishing Webpage Detection via Multi-Modal Integration of HTML DOM Graphs and URL Features Based on Graph Convolutional and Transformer Networks. Electronics 2024, 13, 3344. [Google Scholar] [CrossRef]
- Asiri, S.; Xiao, Y.; Li, T. PhishTransformer: A Novel Approach to Detect Phishing Attacks Using URL Collection and Transformer. Electronics 2023, 13, 30. [Google Scholar] [CrossRef]
- Lin, Y.; Liu, R.; Divakaran, D.M.; Ng, J.Y.; Chan, Q.Z.; Lu, Y.; Si, Y.; Zhang, F.; Dong, J.S. Phishpedia: A Hybrid Deep Learning Based Approach to Visually Identify Phishing Webpages. In Proceedings of the 30th USENIX Security Symposium (USENIX Security 21), USENIX Association, Vancouver, BC, Canada, 11–13 August 2021; pp. 3793–3810. Available online: https://www.usenix.org/system/files/sec21-lin.pdf (accessed on 2 February 2025).
- Abdelnabi, S.; Krombholz, K.; Fritz, M. VisualPhishNet: Zero-Day Phishing Website Detection by Visual Similarity. In Proceedings of the ACM Conference on Computer and Communications Security (CCS), Virtual Event USA, 9–13 November 2020; ACM: New York, NY, USA, 2020. Available online: https://publications.cispa.de/articles/conference_contribution/VisualPhishNet_Zero-Day_Phishing_Website_Detection_by_Visual_Similarity/24613248 (accessed on 2 February 2025).
- Zhang, L.; Zhang, P.; Liu, L.; Tan, J. Multiphish: Multi-Modal Features Fusion Networks for Phishing Detection. In Proceedings of the ICASSP 2021—2021 IEEE International Conference on Acoustics, Speech and Signal Processing (ICASSP), Toronto, ON, Canada, 6–11 June 2021; pp. 3520–3524. [Google Scholar] [CrossRef]
- Salih, A.M.; Raisi-Estabragh, Z.; Galazzo, I.B.; Radeva, P.; Petersen, S.E.; Lekadir, K.; Menegaz, G. A Perspective on Explainable Artificial Intelligence Methods: SHAP and LIME. Adv. Intell. Syst. 2025, 7, 2400304. [Google Scholar] [CrossRef]
- Lim, B.; Huerta, R.; Sotelo, A.; Quintela, A.; Kumar, P. EXPLICATE: Enhancing Phishing Detection through Explainable AI and LLM-Powered Interpretability. arXiv 2025, arXiv:2503.20796. [Google Scholar] [CrossRef]
- Shendkar, B.D.; Chandre, P.R.; Madachane, S.S.; Kulkarni, N.; Deshmukh, S. Enhancing Phishing Attack Detection Using Explainable AI: Trends and Innovations. ASEAN J. Sci. Technol. Dev. 2024, 42, 8. [Google Scholar] [CrossRef]
- Galego Hernandes, P.R.; Floret, C.P.; Cardozo De Almeida, K.F.; Da Silva, V.C.; Papa, J.P.; Pontara Da Costa, K.A. Phishing Detection Using URL-based XAI Techniques. In Proceedings of the 2021 IEEE Symposium Series on Computational Intelligence (SSCI), Orlando, FL, USA, 4–7 December 2021; pp. 01–06. [Google Scholar] [CrossRef]
- Akhtar, H.M.U.; Nauman, M.; Akhtar, N.; Hameed, M.; Hameed, S.; Tareen, M.Z. Mitigating Cyber Threats: Machine Learning and Explainable AI for Phishing Detection. VFAST Trans. Softw. Eng. 2025, 13, 170–195. [Google Scholar] [CrossRef]
- Rashid, F.; Ranaweera, N.; Doyle, B.; Seneviratne, S. LLMs are One-Shot URL Classifiers and Explainers. Comput. Netw. 2024, 258, 170–195. [Google Scholar] [CrossRef]
- Feng, Z.; Guo, D.; Tang, D.; Duan, N.; Feng, X.; Gong, M.; Shou, L.; Qin, B.; Liu, T.; Jiang, D.; et al. CodeBERT: A Pre-Trained Model for Programming and Natural Languages. In Proceedings of the Findings of the Association for Computational Linguistics: EMNLP 2020, Online, 16–20 November 2020; pp. 1536–1547. [Google Scholar] [CrossRef]
- Moreau, L. AI Explainability with Grad-CAM: Visualizing Neural Network Decisions. 2025. Available online: https://www.edgeimpulse.com/blog/ai-explainability-with-grad-cam-visualizing-neural-network-decisions/ (accessed on 2 February 2025).
- Shrikumar, A.; Greenside, P.; Kundaje, A. Learning Important Features Through Propagating Activation Differences. In Proceedings of the 34th International Conference on Machine Learning—Volume 70 (ICML’17), JMLR.org, Sydney, Australia, 6–11 August 2017; pp. 3145–3153. Available online: https://dl.acm.org/doi/10.5555/3305890.3306006 (accessed on 19 December 2025).
- Nori, H.; Jenkins, S.; Koch, P.; Caruana, R. InterpretML: A Unified Framework for Machine LearningInterpretability. arXiv 2019, arXiv:1909.09223. Available online: https://api.semanticscholar.org/CorpusID:202712518 (accessed on 19 December 2025).
- Colhak, F.; Ecevit, M.I.; Dag, H. Transfer Learning for Phishing Detection: Screenshot-Based Website Classification. In Proceedings of the 2024 9th International Conference on Computer Science and Engineering (UBMK), Antalya, Turkiye, 26–28 October 2024; pp. 1–6. [Google Scholar] [CrossRef]
- Datasets, H. Combined BERT Phishing Dataset. Available online: https://huggingface.co/datasets/ealvaradob/phishing-dataset (accessed on 2 February 2025).
- Alexa Top 1 Million Sites. Available online: https://www.kaggle.com/datasets/cheedcheed/top1m (accessed on 14 November 2025).
- Mendoza Vega, D.O.; Diaz Mercado, D.O.; Cardenas, E.J.E. PhishFind: A Machine Learning-Based System for Real-Time Phishing Detection. In Proceedings of the 2025 8th International Conference on Systems Engineering—Cybersecurity & AI: Building a Reliable Digital Future (CIIS ’25), Lima, Peru, 1–3 October 2025; Association for Computing Machinery: New York, NY, USA, 2025; pp. 31–39. [Google Scholar] [CrossRef]
- Yuan, Y.; Hao, Q.; Apruzzese, G.; Conti, M.; Wang, G. “Are Adversarial Phishing Webpages a Threat in Reality?” Understanding the Users’ Perception of Adversarial Webpages. In Proceedings of the ACM Web Conference 2024, Singapore, 13–17 May 2024; pp. 1712–1723. [Google Scholar] [CrossRef]
- Akiba, T.; Sano, S.; Yanase, T.; Ohta, T.; Koyama, M. Optuna: A Next-generation Hyperparameter Optimization Framework. In Proceedings of the 25th ACM SIGKDD International Conference on Knowledge Discovery & Data Mining, Anchorage, AK, USA, 4–8 August 2019; pp. 2623–2631. [Google Scholar] [CrossRef]
- Prokhorenkova, L.; Gusev, G.; Vorobev, A.; Dorogush, A.V.; Gulin, A. CatBoost: Unbiased boosting with categorical features. In Advances in Neural Information Processing Systems; Curran Associates, Inc.: Red Hook, NY, USA, 2018; Volume 31. [Google Scholar]
- Tan, M.; Le, Q.V. EfficientNet: Rethinking Model Scaling for Convolutional Neural Networks. In Proceedings of the 36th International Conference on Machine Learning; ICML 2019, Long Beach, CA, USA, 9–15 June 2019; pp. 6105–6114. Available online: https://proceedings.mlr.press/v97/tan19a.html (accessed on 19 December 2025).
- Tekkali, C.G.; Natarajan, K. Transfer learning of pre-trained CNNs on digital transaction fraud detection. Int. J. Knowl.-Based Intell. Eng. Syst. 2024, 28, 571–580. [Google Scholar] [CrossRef]
- Cik, I.; Rasamoelina, A.D.; Mach, M.; Sincak, P. Explaining Deep Neural Network using Layer-wise Relevance Propagation and Integrated Gradients. In Proceedings of the 2021 IEEE 19th World Symposium on Applied Machine Intelligence and Informatics (SAMI), Herl’any, Slovakia, 21–23 January 2021; pp. 000381–000386. [Google Scholar] [CrossRef]
- Ali, A.; Schnake, T.; Eberle, O.; Montavon, G.; Müller, K.R.; Wolf, L. XAI for Transformers: Better Explanations through Conservative Propagation, 2022. In Proceedings of the 39th International Conference on Machine Learning, Baltimore, MD, USA, 17–23 July 2022; PMLR 162, pp. 1–17. Available online: https://proceedings.mlr.press/v162/ali22a/ali22a.pdf (accessed on 19 December 2025).
- Yang, A.; Yang, B.; Hui, B.; Zheng, B.; Yu, B.; Zhou, C.; Li, C.; Li, C.; Liu, D.; Huang, F.; et al. Qwen2 Technical Report. arXiv 2024, arXiv:2407.10671. [Google Scholar] [CrossRef]
- Colhak, F.; Ecevit, M.I.; Ucar, B.E.; Creutzburg, R.; Dag, H. Phishing Website Detection through Multi-Model Analysis of HTML Content. In Proceedings of International Conference on Theoretical and Applied Computing; Springer: Singapore, 2025; pp. 171–184. [Google Scholar] [CrossRef]
- Younis, E.M.G.; Zaki, S.M.; Kanjo, E.; Houssein, E.H. Evaluating Ensemble Learning Methods for Multi-Modal Emotion Recognition Using Sensor Data Fusion. Sensors 2022, 22, 5611. [Google Scholar] [CrossRef] [PubMed]
- Lutskovich, A.; Vasilyev, V.; Vulfin, A.; Kirillova, A.; Sulavko, A. Automated system for analyzing weakly structured threat intelligence data using large language models. Informatsionno-Upr. Sist. Inf. Control Syst. 2025, 2, 50–67. [Google Scholar] [CrossRef]
- Caruso, C.M.; Soda, P.; Guarrasi, V. MARIA: A multimodal transformer model for incomplete healthcare data. Comput. Biol. Med. 2025, 196, 110843. [Google Scholar] [CrossRef] [PubMed]
- Rahimi, F.; Tamantini, C.; Orlandini, A.; Fracasso, F.; Siciliano, R. Comparing Fusion Strategies for Multimodal Emotion Prediction Using Deep Physiological Features. In Proceedings of the Workshop on Social Robotics for Human-Centered Assistive and Rehabilitation Co-Located with International Conference on Social Robotics + AI (ICSR + AI 2025), CEUR-WS, Naples, Italy, 10–12 September 2025; pp. 56–64. Available online: https://ceur-ws.org/Vol-4067/paper9.pdf (accessed on 28 December 2025).
- Liang, Z.; Qu, A.; Shahbaba, B. Meta Fusion: A Unified Framework For Multimodality Fusion with Mutual Learning. arXiv 2025, arXiv:2507.20089. [Google Scholar] [CrossRef]
- Stahlschmidt, S.R.; Ulfenborg, B.; Synnergren, J. Multimodal deep learning for biomedical data fusion: A review. Briefings Bioinform. 2022, 23, bbab569. [Google Scholar] [CrossRef]
- Kalai, A.T.; Nachum, O.; Vempala, S.S.; Zhang, E. Why Language Models Hallucinate. arXiv 2025, arXiv:2509.04664. [Google Scholar] [CrossRef]
- Zhao, F.; Zhang, C.; Geng, B. Deep Multimodal Data Fusion. ACM Comput. Surv. 2024, 56, 216. [Google Scholar] [CrossRef]
- Belfedhal, A.E. Multi-Modal Deep Learning for Effective Malicious Webpage Detection. Rev. D’Intell. Artif. 2023, 37, 1005–1013. [Google Scholar] [CrossRef]
- Wang, C.; Zhang, M.; Shi, F.; Xue, P.; Li, Y. A Hybrid Multimodal Data Fusion-Based Method for Identifying Gambling Websites. Electronics 2022, 11, 2489. [Google Scholar] [CrossRef]
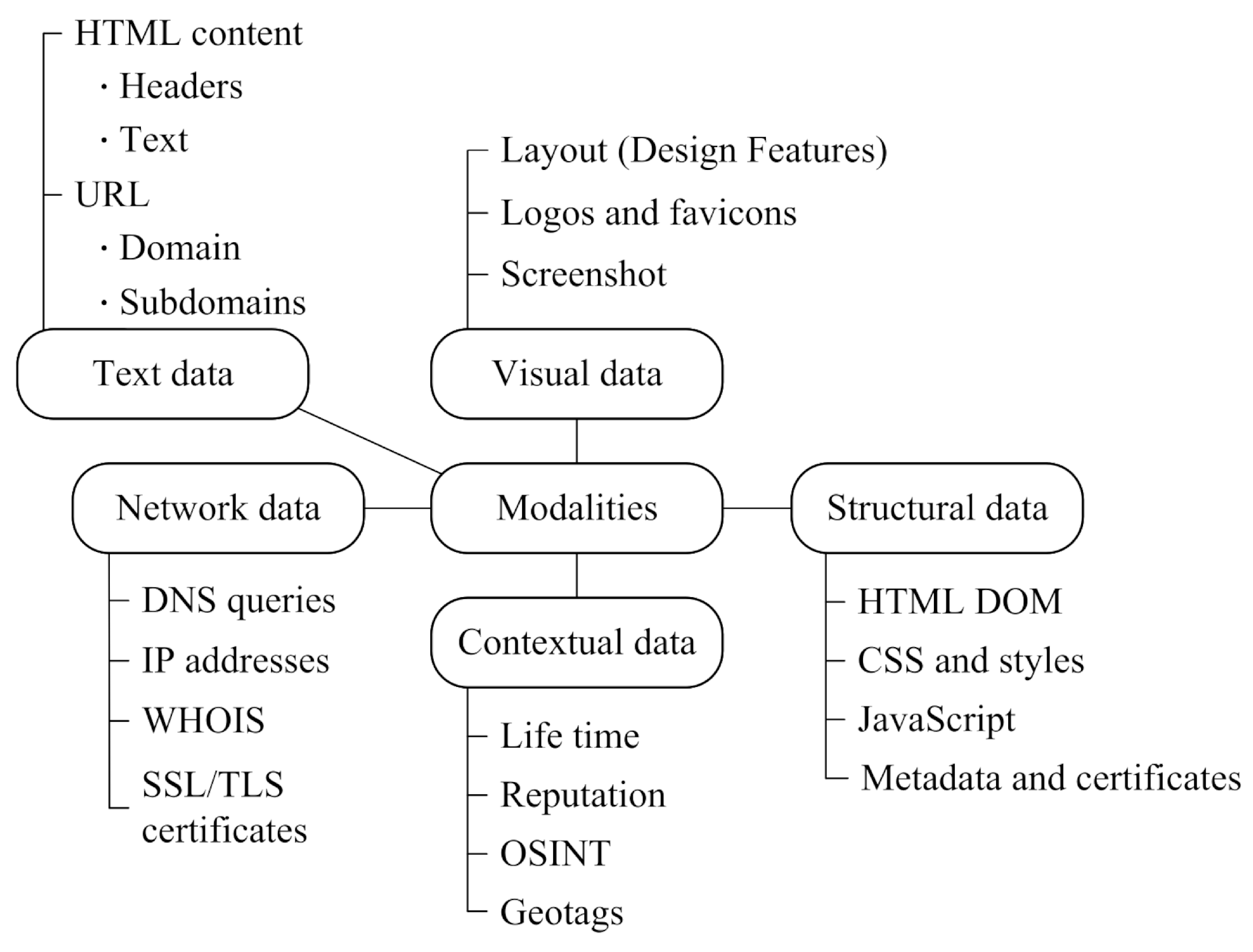









| Modality Type | Features | Extraction Methods |
|---|---|---|
| Text | URL, email body, HTML content, domain/subdomain | NLP, tokenization, embeddings (BERT, Word2Vec) |
| Visual | Page screenshots, logos, favicons, color schemes, layout | CNN, transfer learning (ResNet, VGG), object detection |
| Structural | HTML DOM, CSS, JavaScript, metadata, certificates | DOM parsing, graph analysis, feature extraction |
| Network | DNS queries, IP addresses, WHOIS, SSL certificates | Network analysis, OSINT, reputation services |
| Fusion Strategies | Advantages | Disadvantages | Examples of Systems |
|---|---|---|---|
| Early Fusion | – Accounting for low-level correlations – Simple architecture | – Loss of modality specificity – Training difficulty | MultiPhish [38] |
| Intermediate Fusion | – Balance of specificity and interaction – Mechanisms of attention | – Average learning difficulty | PhishTransformer [35] |
| Late Fusion | – Model specialization – Modularity – Parallelization | – Loss of intermodule connections | Yoon et al. [33] |
| Hybrid Fusion | – Maximum performance; adaptability | – High model complexity – Risk of overfitting | KnowPhish [28] |
| Method | Type of Explanation | Applicability | Clarity | Accuracy | Application in Phishing |
|---|---|---|---|---|---|
| SHAP | Global + Local | Model-agnostic | Average | High | XGBoost, RF—URL features |
| LIME | Local | Model-agnostic | Average | Average | Any models—URL, HTML |
| Grad-CAM | Local visual | CNN-specific | High | Average | ResNet, VGG—screenshots |
| DeepLIFT | Local | DNN-specific | Low | High | CNN, LSTM—all modalities |
| Explainable Boosting Machine (EBM) | Intrinsic | Special model | High | High | Email phishing |
| Attention Mechanisms | Intrinsic | Transformers | Average | Average | BERT, Transformers—text |
| LLM text | Post-processing | Any | Very high | High | All modalities with context |
| Level | Methods | Difficulty of Implementation | Cost of Inference | User-Friendliness | Application in Industrial Systems |
|---|---|---|---|---|---|
| Post hoc | LIME, SHAP, Grad-CAM, DeepLIFT | Average | Low | Technical | Wide |
| Intrinsic | Decision trees, EBM, logistic regression | Low | Very low | High | Moderate |
| Attention | Transformers, BERT family | High | Average | Average | Growing |
| LLM text | On-premises and cloud LLM | Very high | High | Very high | Experimental |
| Name | Year | Data Type | Volume | Balance of Classes (Phishing/Legitimate) | Sources | Peculiarities |
|---|---|---|---|---|---|---|
| PhiUSIIL | 2024 | URL + features | 235,795 URLs | 57%/43% | UCI ML Repository [31] | 48 features, focus on the latest threats |
| TR-OP | 2024 | Web pages | 10,000 | 50%/50% | USENIX Security | Manual validation, 440 brands [27] |
| Combined BERT | 2023 | Multimodal | 800 K+ URLs, 18 K emails, 6 K SMS | 52%/47% | HuggingFace | Cross-channel data [50] |
| PhishTank | Updates daily | URL | 1.5 M+ | Only phishing | UCI ML Repository | Community-driven, API access [31] |
| APWG | Quarterly | URL + reports | Varies | Only phishing | apwg trends report q4 2024 | Industrial standard [2] |
| MTLP | 2024 | Screenshots | 15,000 | 50%/50% | IEEE | Multitype logo phishing [49] |
| Alexa Top 1M | Archival | URL | 1,000,000 | 100% legitimate | Kaggle | Baseline of legitimate sites [51] |
| No. | Multimodal Component | Data Type | Extracted Features (In Brief) |
|---|---|---|---|
| 1 | URL | URL components and domain features | – URL structure and statistical features (length, special characters, presence of IP instead of domain); – Lexical features; – Syntactic features; – Phonetic features; – Semantic features; – SSL/TLS certificates |
| 2 | HTML | Source code of the main page of the target resource | – HTML components; – DOM structure; – JavaScript code; – CSS |
| 3 | Image | Image of the main page of the analyzed resource | – RGB image 600 × 600 pixels |
| 4 | Metadata | – WHOIS information (domain registration) – Domain analysis (age, registrar); – Reputation databases (VirusTotal, Google Safe Browsing) – Threat intelligence feeds (PhishTank, URLhaus, OpenPhish) |
| No. | Multimodal Component | Model Designation | Model Type |
|---|---|---|---|
| 1 | URL + Metadata | Using the Optuna framework [54], hyperparameters of the CatBoost model [55] are selected in k-cross-validation mode with k = 5. | |
| CNN1D for character-level URL analysis. | |||
| 2 | HTML | Fine-tuning of the CodeBERT model [45]. | |
| 3 | Image | Fine-tuning of the EfficientNet-B7 model [56,57]. | |
| 4 | Late binding | Late binding of trained models using weighted voting. |
| No. | Multimodal Component | Model Designation | Model | Formed Features of XAI |
|---|---|---|---|---|
| 1 | URL + Metadata | CatBoost | SHAP Values | |
| CNN1D | Grad-CAM, Integrated Gradients [58] | |||
| 2 | HTML | CodeBERT | Attention matrix [59] | |
| 3 | Image | EfficientNet-B7 | Grad-CAM |
| Metric | CatBoost | Random Forest | XGBoost |
|---|---|---|---|
| ROC-AUC | 0.924 | 0.915 | 0.918 |
| Accuracy | 0.910 | 0.890 | 0.900 |
| Recall | 0.880 | 0.850 | 0.860 |
| F1-score | 0.900 | 0.870 | 0.880 |
| Layers and Architecture Parameters | Description |
|---|---|
| Input layer—embedding | EMBED_DIM = 64 —converting characters to vector representation |
| CNN layers | Three parallel convolutional layers with kernels of sizes KERNEL_SIZES = , number of filters NUM_KERNELS = 64 |
| MaxPooling | Two layers |
| Output layer | Fully connected layer with sigmoid activation function |
| Loss function | Binary cross-entropy |
| Metrics | Accuracy, precision, recall, F1-score |
| Optimizer | Adam (LR = 0.001) |
| Data separation | The validation sample is 20% of the available data. |
| Regularization | Dropout (DROPOUT = 0.5) and early stopping (ReduceLROnPlateau). |
| Synthetic Link | http://paypa1-security.tk/login | ||
|---|---|---|---|
| features | Feature values | SHAP | Interpretation |
| domain_age_days | 3 | −0.450 | A critical feature of a phishing resource |
| is_suspicious_tld | 1 | −0.380 | An essential feature of a phishing resource |
| typosquatting_score | 0.75 | −0.315 | A critical feature of a phishing resource |
| Model | Synthetic Example of a Phishing URL | Description |
|---|---|---|
| Grad-CAM | http://paypa1-security.tk/login | The model focuses on the domain when deciding whether a resource belongs to a phishing resource. |
| Integrated Gradients | http://paypa1-security.tk/login +0.9 +0.7 +0.95 +0.6 | The model refines URL symbols and their significance coefficients based on their contributions to the resulting solution. |
| Parameter | Characteristic |
|---|---|
| GPU | 4 GPU Tesla V100 |
| GPU video memory capacity | 128 GB |
| CPU | Intel Xeon E5-2698 v4 2.2 GHz (20-core) |
| RAM capacity | 256GB RDIMM DDR4 |
| Model | Operation | Batch Performance Evaluation | Learning Mode/ Inference During Integration |
|---|---|---|---|
| HTML tokenization | 25–50 ms | GPU/GPU | |
| CodeBERT ONNX | 200 ms | GPU | |
| Attention extraction | 15–20 ms | GPU | |
| Feature extraction | Less than 8 ms per URL | GPU/CPU | |
| SHAP computation | Less than 12 ms per URL | GPU/CPU | |
| CatBoost C-compiled | Less than 8 ms per URL | GPU/CPU |
| Experiment | Model (Designation) | Model (Name) | Dataset | F1-Score |
|---|---|---|---|---|
| I | M1 | CatBoost | D1 (own dataset) | 0.900 |
| M3 | CodeBERT | 0.950 | ||
| M1 + M3 | CatBoost + CodeBERT + Voting Classifier | 0.972 |
| Model | Operation | Batch Performance Evaluation | Learning Mode/Inference During Integration |
|---|---|---|---|
| Tokenization | 3 ms | GPU/GPU | |
| CNN1D forward pass | 7 ms | GPU | |
| Grad-CAM + integrated gradients | 55 ms | GPU | |
| Screenshot capture | 250 ms | GPU/CPU | |
| Image preprocessing | 15 ms | GPU/CPU | |
| EfficientNet-B7 inference | 200 ms | GPU | |
| Grad-CAM computation | 150 ms | GPU | |
| Region analysis | 50 ms | GPU/CPU |
| Experiment | Model (Designation) | Model (Name) | Dataset | F1-Score |
|---|---|---|---|---|
| II | CNN1D | D2 (MTLP) | 0.914 | |
| EfficientNet-B7 | 0.932 | |||
| + | CNN1D + EfficientNet-B7 + Voting Classifier | 0.944 |
| Experiment | Model (Designation) | Model (Name) | Dataset | F1-Score |
|---|---|---|---|---|
| III | CatBoost + CodeBERT + CNN1D + EfficientNet-B7 + Voting Classifier | (own dataset) | 0.989 | |
| CatBoost + CodeBERT + CNN1D + EfficientNet-B7 + Voting Classifier | (MTLP) | 0.953 |
| № | Enhanced Attack Subclass | Decrease in Performance of Individual Models | Decrease in Performance Quality of Multimodal Model |
|---|---|---|---|
| 1 | URL obfuscation (the use of homoglyphs, the insertion of superfluous subdomains, the addition of suffixes or prefixes, and the substitution of domain names with IP addresses). | 2 | 1.5 |
| 2 | HTML obfuscation (the injection of “noise” into the DOM tree, the fragmentation of key strings, and the use of JavaScript-based encoding). | 4 | 2 |
| 3 | Visual camouflage (modifying the color scheme and non-essential template elements while preserving the fundamental structure of the login form). | 5 | 3 |
| Parameter | Explanation Subsystem without RAG | Explanation Subsystem with RAG |
|---|---|---|
| Distribution of points | 2 points — 3 scores; 3 points — 9 scores; 4 points — 66 scores; 5 points — 12 scores | 2 points — 0 scores; 3 points — 9 scores; 4 points — 54 scores; 5 points — 27 scores |
| Average points | 3.97 | 4.20 |
| Fleiss’s | 0.82 | 0.84 |
| Cronbach’s | 0.90 | 0.96 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Vulfin, A.; Sulavko, A.; Vasiliev, V.; Minko, A.; Kirillova, A.; Samotuga, A. A Multimodal Phishing Website Detection System Using Explainable Artificial Intelligence Technologies. Mach. Learn. Knowl. Extr. 2026, 8, 11. https://doi.org/10.3390/make8010011
Vulfin A, Sulavko A, Vasiliev V, Minko A, Kirillova A, Samotuga A. A Multimodal Phishing Website Detection System Using Explainable Artificial Intelligence Technologies. Machine Learning and Knowledge Extraction. 2026; 8(1):11. https://doi.org/10.3390/make8010011
Chicago/Turabian StyleVulfin, Alexey, Alexey Sulavko, Vladimir Vasiliev, Alexander Minko, Anastasia Kirillova, and Alexander Samotuga. 2026. "A Multimodal Phishing Website Detection System Using Explainable Artificial Intelligence Technologies" Machine Learning and Knowledge Extraction 8, no. 1: 11. https://doi.org/10.3390/make8010011
APA StyleVulfin, A., Sulavko, A., Vasiliev, V., Minko, A., Kirillova, A., & Samotuga, A. (2026). A Multimodal Phishing Website Detection System Using Explainable Artificial Intelligence Technologies. Machine Learning and Knowledge Extraction, 8(1), 11. https://doi.org/10.3390/make8010011






