Intercept-Resend Emulation Attacks against a Continuous-Variable Quantum Authentication Protocol with Physical Unclonable Keys
Abstract
1. Introduction
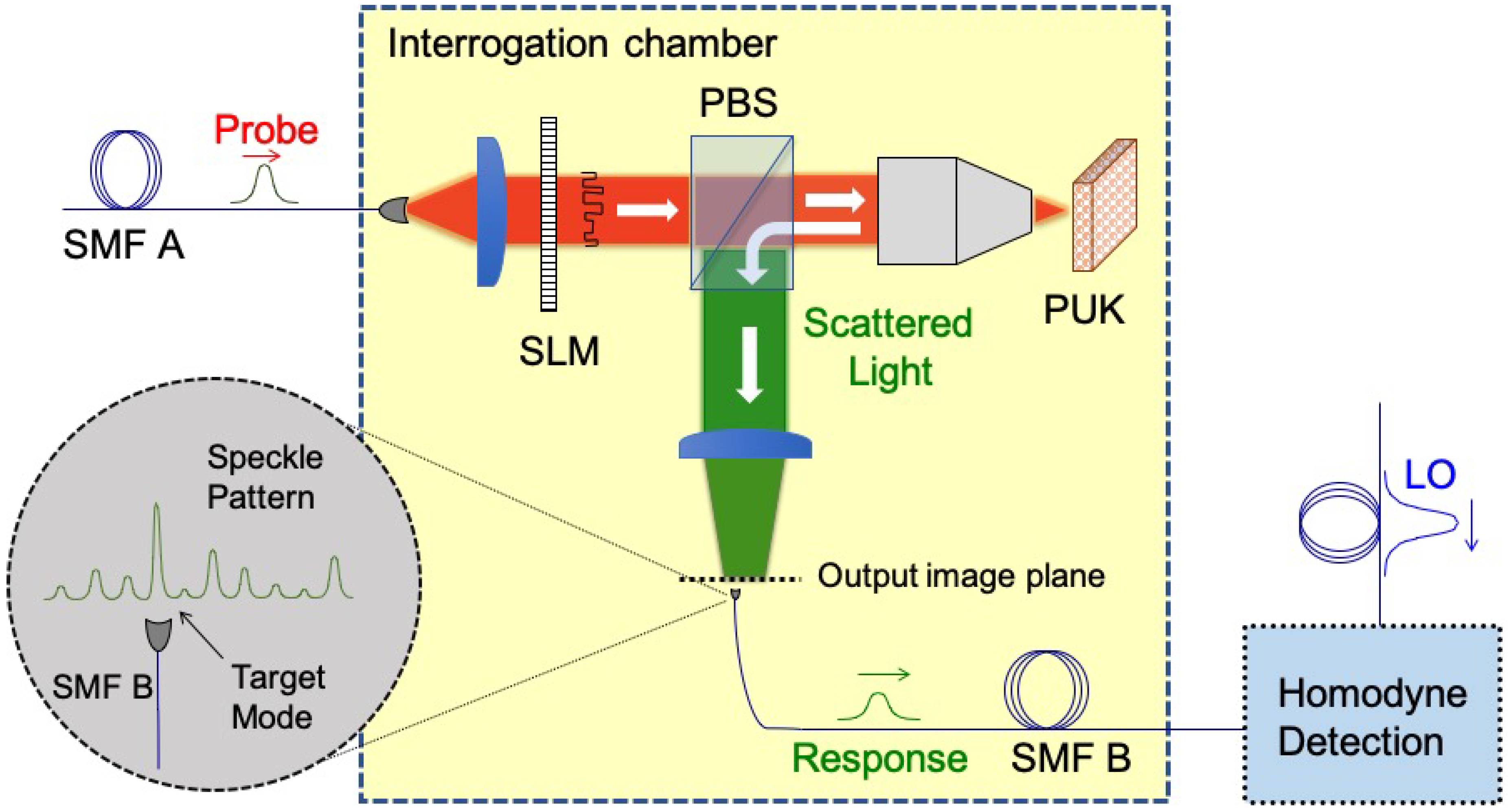
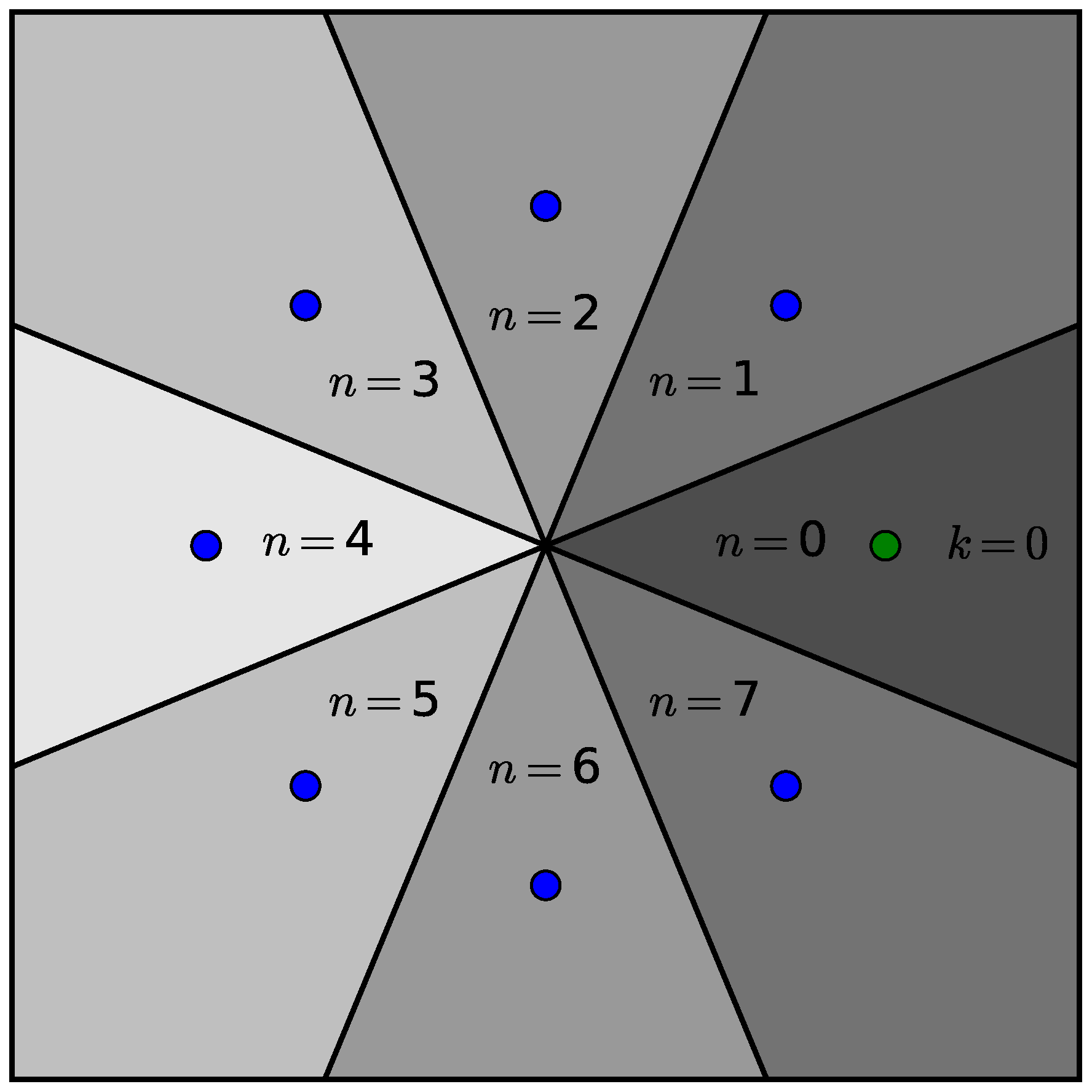
2. Authentication Scheme
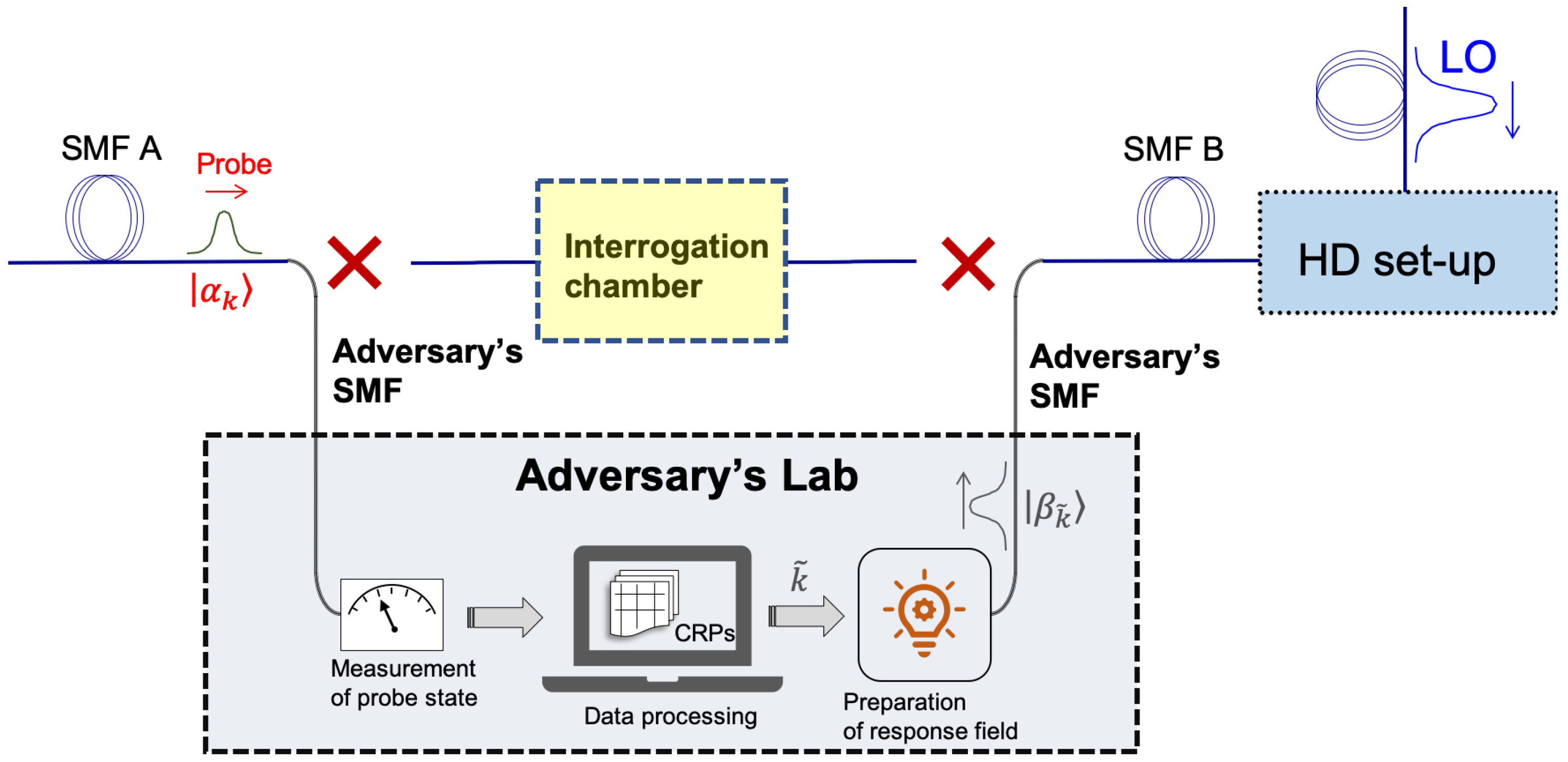
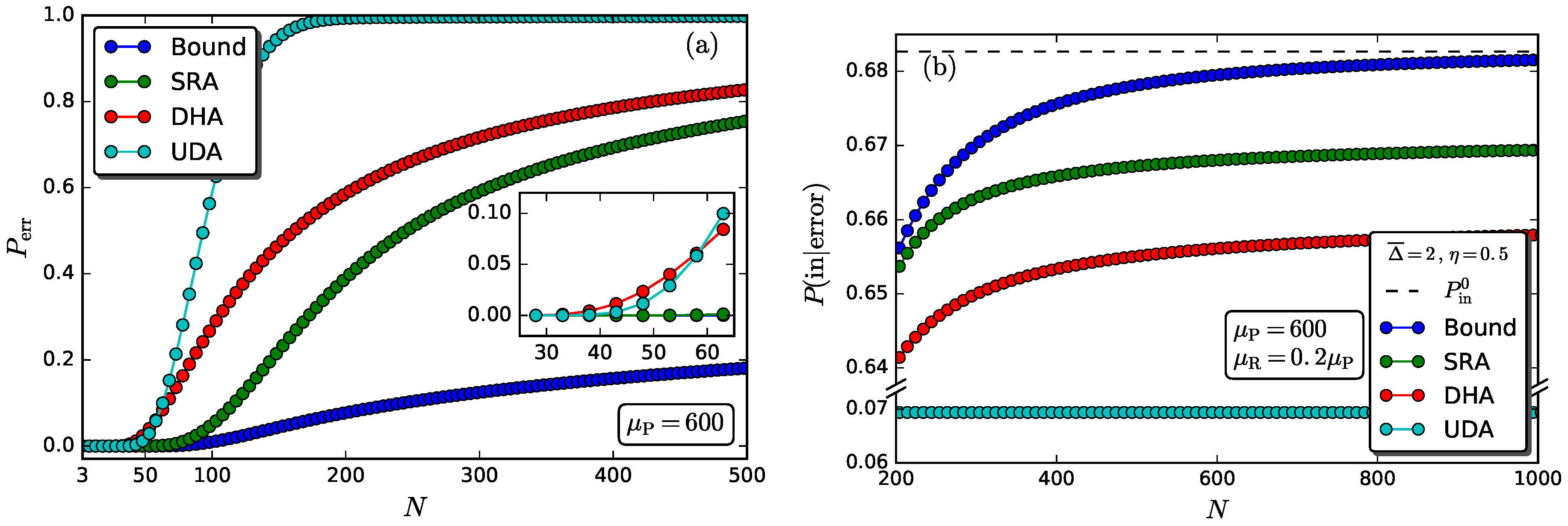
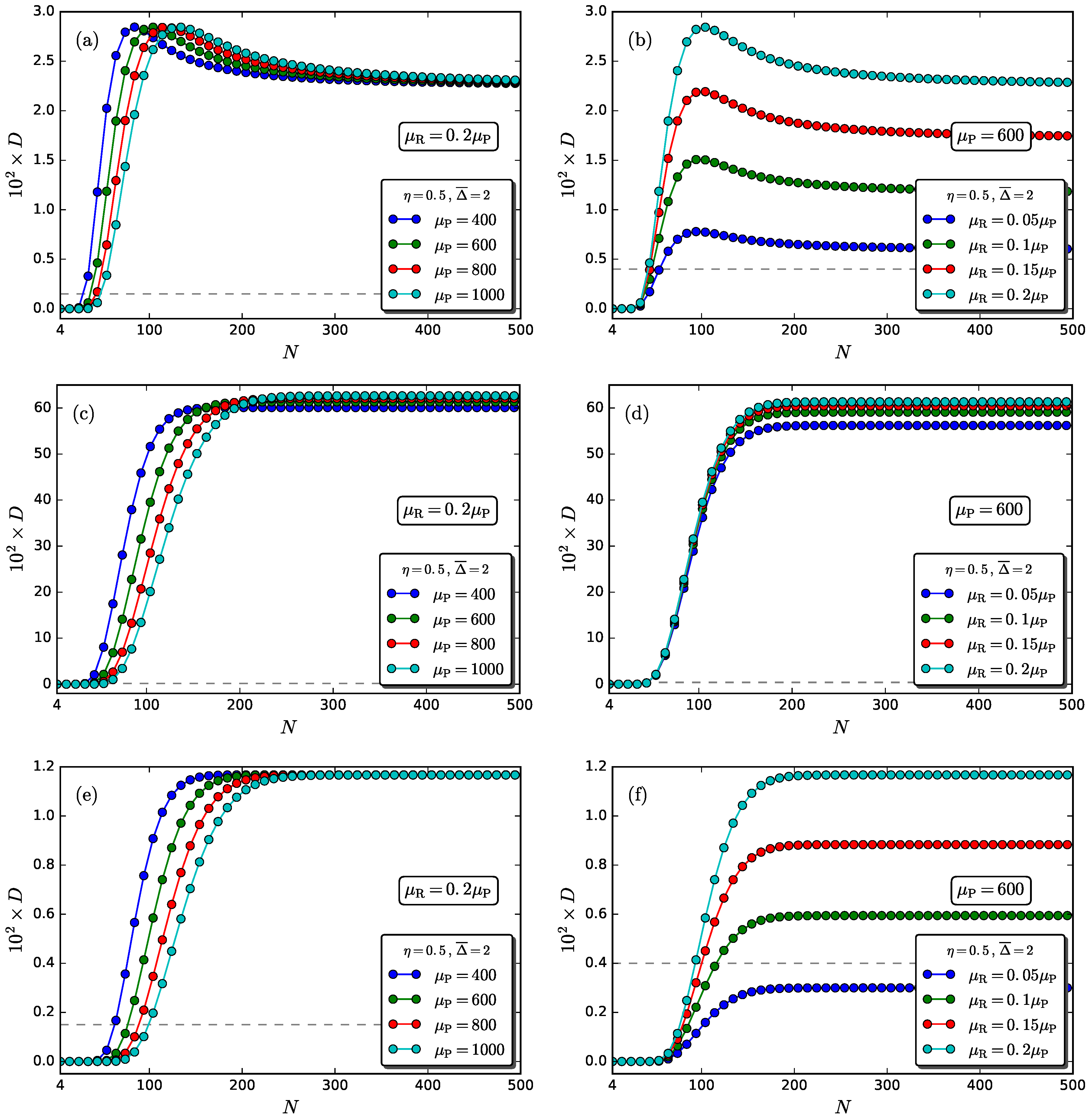
3. Intercept–Resend Emulation Attacks
3.1. Dual Homodyne–Detection Attack
3.2. Unambiguous State-Discrimination Attack
3.3. Minimum-Error State Discrimination Attack
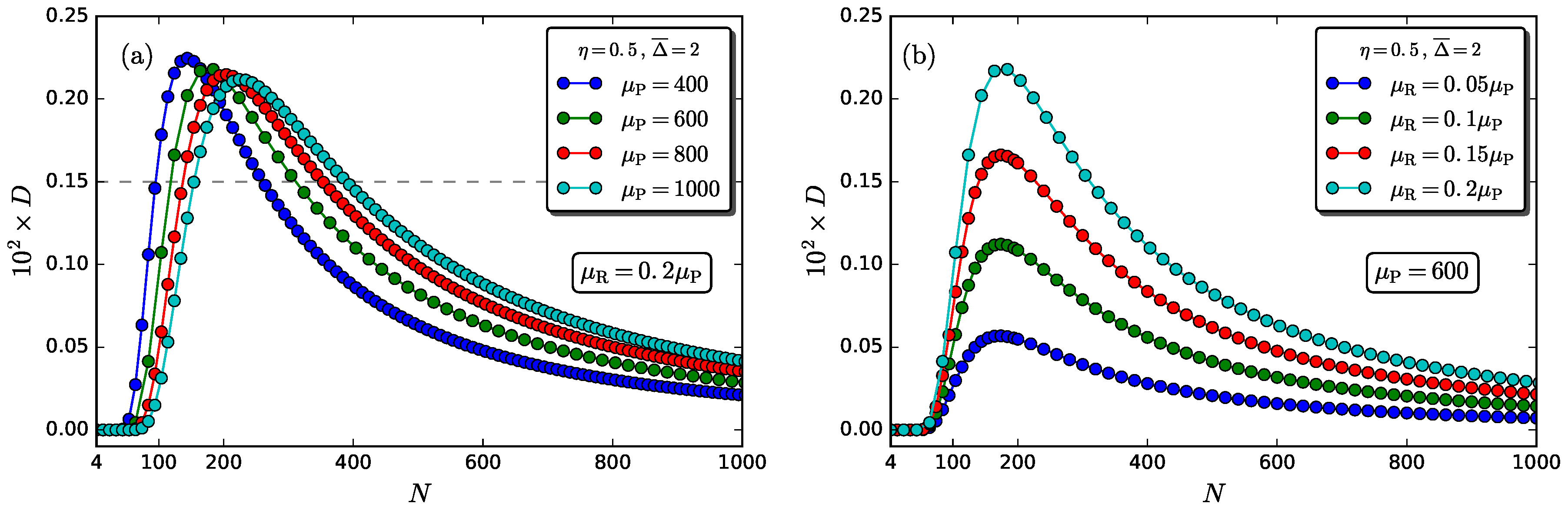
4. Numerical Results and Discussion
5. Concluding Remarks
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| PUK | Physical unclonable key |
| EAP | Entity authentication protocol |
| HD | Homodyne detection |
| LO | Local oscillator |
| SMF | Single mode fiber |
| SLM | Spatial light modulator |
| CRP | Challenge response pair |
| DHA | Dual-homodyne–detection attack |
| UDA | Unambiguous-state-discrimination attack |
| SRA | Square-root-measurement attack |
References
- Menezes, A.; van Oorschot, P.; Vanstone, S. Handbook of Applied Cryptography; CRC Press: Boca Raton, FL, USA, 1996. [Google Scholar]
- Martin, K.M. Everyday Cryptography: Fundamental Principles and Applications; Oxford University Press: Oxford, UK, 2012. [Google Scholar]
- Herder, C.; Yu, M.D.; Koushanfar, F.; Devadas, S. Physical Unclonable Functions and Applications: A Tutorial. Proc. IEEE 2014, 102, 1126–1141. [Google Scholar] [CrossRef]
- Rührmair, U.; Holcomb, D.E. PUFs at a Glance. In Proceedings of the Conference on Design, Automation and Test in Europe (DATE’14), Dresden, Germany, 24–28 March 2014. [Google Scholar]
- Daihyun, L.; Lee, J.W.; Gassend, B.; Suh, G.E.; van Dijk, M.; Devadas, S. Extracting secret keys from integrated circuits. IEEE Trans. Very Large Scale Integr. Syst. 2005, 13, 1200–1205. [Google Scholar] [CrossRef]
- Pappu, R.; Recht, B.; Taylor, J.; Gershenfeld, N. Physical one-way functions. Science 2002, 297, 2026–2030. [Google Scholar] [CrossRef] [PubMed]
- Maes, R. Physically Unclonable Functions: Constructions, Properties and Applications; Springer: New York, NY, USA, 2013. [Google Scholar]
- McGrath, T.; Bagci, I.E.; Wang, Z.M.; Roedig, U.; Young, R.J. A PUF taxonomy. Appl. Phys. Rev. 2019, 6, 011303. [Google Scholar] [CrossRef]
- Santikellur, P.; Bhattacharyay, A.; Chakraborty, R.S. Deep Learning Based Model Building Attacks on Arbiter PUF Compositions. Cryptology ePrint Archive, Report 2019/566. 2019. Available online: https://eprint.iacr.org/2019/566 (accessed on 24 October 2019).
- Khalafalla, M.; Gebotys, C. PUFs Deep Attacks: Enhanced modeling attacks using deep learning techniques to break the security of double arbiter PUFs. In Proceedings of the 2019 Design, Automation & Test in Europe Conference & Exhibition (DATE), Florence, Italy, 25–29 March 2019; pp. 204–209. [Google Scholar]
- Ganji, F.; Forte, D.; Seifert, J.P. PUFmeter a Property Testing Tool for Assessing the Robustness of Physically Unclonable Functions to Machine Learning Attacks. IEEE Access 2019, 7, 122513–122521. [Google Scholar] [CrossRef]
- Delvaux, J. Machine-Learning Attacks on PolyPUFs, OB-PUFs, RPUFs, LHS-PUFs, and PUF–FSMs. IEEE Trans. Inf. Forensics Secur. 2019, 14, 2043–2058. [Google Scholar] [CrossRef]
- Rührmair, U.; Hilgers, C.; Urban, S.; Weiershäuser, A.; Dinter, E.; Forster, B.; Jirauschek, C. Optical PUFs Reloaded. Cryptology ePrint Archive, Report 2013/215. 2013. Available online: https://eprint.iacr.org/2013/215 (accessed on 24 October 2019).
- Goorden, S.A.; Horstmann, M.; Mosk, A.P.; Škorić, B.; Pinkse, P.W.H. Quantum-secure authentication of a physical unclonable key. Optica 2014, 1, 421–424. [Google Scholar] [CrossRef]
- Nikolopoulos, G.M.; Diamanti, E. Continuous-variable quantum authentication of physical unclonable keys. Sci. Rep. 2017, 7, 46047. [Google Scholar] [CrossRef]
- Nikolopoulos, G.M. Continuous-variable quantum authentication of physical unclonable keys: Security against an emulation attack. Phys. Rev. A 2018, 97, 012324. [Google Scholar] [CrossRef]
- Vellekoop, I.M. Feedback-based wavefront shaping. Opt. Express 2015, 23, 12189–12206. [Google Scholar] [CrossRef]
- Mosk, A.P.; Lagendijk, A.; Lerosey, G.; Fink, M. Controlling waves in space and time for imaging and focusing in complex media. Nat. Photonics 2012, 6, 283. [Google Scholar] [CrossRef]
- Poppoff, S.K.; Lerosey, G.; Fink, M.; Boccara, A.C.; Gigan, S. Controlling light through optical disordered media: transmission matrix approach. New J. Phys. 2011, 13, 123021. [Google Scholar] [CrossRef]
- Defienne, H.; Barbieri, M.; Chalopin, B.; Chatel, B.; Walmsley, I.; Smith, B.; Gigan, S. Nonclassical light manipulation in a multiple-scattering medium. Opt. Lett. 2014, 39, 6090–6093. [Google Scholar] [CrossRef] [PubMed]
- Huisman, T.J.; Huisman, S.R.; Mosk, A.P.; Pinkse, P.W. Controlling single-photon Fock-state propagation through opaque scattering media. Appl. Phys. B 2014, 116, 603–607. [Google Scholar] [CrossRef][Green Version]
- Huisman, S.R.; Huisman, T.J.; Wolterink, T.A.W.; Mosk, A.P.; Pinkse, P.W.H. Programmable multiport optical circuits in opaque scattering materials. Opt. Express 2015, 23, 3102–3116. [Google Scholar] [CrossRef]
- Leonhardt, U.; Böhmer, B.; Paul, H. Uncertainty relations for realistic joint measurements of position and momentum in quantum optics. Opt. Commun. 1995, 119, 296–300. [Google Scholar] [CrossRef]
- Schleich, W.P. Quantum Optics in Phase Space; John Wiley & Sons: Hoboken, NJ, USA, 2011. [Google Scholar]
- Chefles, A.; Barnett, S.M. Optimum unambiguous discrimination between linearly independent symmetric states. Phys. Lett. A 1998, 250, 223–229. [Google Scholar] [CrossRef]
- Ivanovic, I.D. How to differentiate between non-orthogonal states. Phys. Lett. A 1987, 123, 257–259. [Google Scholar] [CrossRef]
- Peres, A. How to differentiate between non-orthogonal states. Phys. Lett. A 1988, 128, 19. [Google Scholar] [CrossRef]
- Dieks, D. Overlap and distinguishability of quantum states. Phys. Lett. A 1988, 126, 303–306. [Google Scholar] [CrossRef]
- Barnett, S.M.; Croke, S. Quantum state discrimination. Adv. Opt. Photonics 2009, 1, 238–278. [Google Scholar] [CrossRef]
- Weir, G. Optimal Discrimination of Quantum States. Ph.D. Thesis, University of Glasgow, Glasgow, UK, 2018. [Google Scholar]
- Izumi, S.; Takeoka, M.; Wakui, K.; Fujiwara, M.; Ema, K.; Sasaki, M. Optical phase estimation via the coherent state and displaced-photon counting. Phys. Rev. A 2016, 94, 033842. [Google Scholar] [CrossRef]
- Croal, C.; Peuntinger, C.; Heim, B.; Khan, I.; Marquardt, C.; Leuchs, G.; Wallden, P.; Andersson, E.; Korolkova, N. Free-Space Quantum Signatures Using Heterodyne Measurements. Phys. Rev. Lett. 2016, 117, 100503. [Google Scholar] [CrossRef] [PubMed]
- Van Enk, S. Unambiguous state discrimination of coherent states with linear optics: Application to quantum cryptography. Phys. Rev. A 2002, 66, 042313. [Google Scholar] [CrossRef]
- Horstmayer, R.; Judkewitz, B.; Vellekoop, I.M.; Assawaworrarit, S.; Yan, C. Physical key-protected one-time pad. Sci. Rep. 2013, 3, 3543. [Google Scholar] [CrossRef]
- Nikolopoulos, G.M. Optical scheme for cryptographic commitments with physical unclonable keys. Opt. Express 2019, 27, 29367–29379. [Google Scholar] [CrossRef]

| Identification Number | |||
|---|---|---|---|
| Challenge | Response | ||
| k | Phase mask | ||
| 0 | |||
| 1 | |||
| 2 | |||
| ⋮ | ⋮ | ⋮ | |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Fladung, L.; Nikolopoulos, G.M.; Alber, G.; Fischlin, M. Intercept-Resend Emulation Attacks against a Continuous-Variable Quantum Authentication Protocol with Physical Unclonable Keys. Cryptography 2019, 3, 25. https://doi.org/10.3390/cryptography3040025
Fladung L, Nikolopoulos GM, Alber G, Fischlin M. Intercept-Resend Emulation Attacks against a Continuous-Variable Quantum Authentication Protocol with Physical Unclonable Keys. Cryptography. 2019; 3(4):25. https://doi.org/10.3390/cryptography3040025
Chicago/Turabian StyleFladung, Lukas, Georgios M. Nikolopoulos, Gernot Alber, and Marc Fischlin. 2019. "Intercept-Resend Emulation Attacks against a Continuous-Variable Quantum Authentication Protocol with Physical Unclonable Keys" Cryptography 3, no. 4: 25. https://doi.org/10.3390/cryptography3040025
APA StyleFladung, L., Nikolopoulos, G. M., Alber, G., & Fischlin, M. (2019). Intercept-Resend Emulation Attacks against a Continuous-Variable Quantum Authentication Protocol with Physical Unclonable Keys. Cryptography, 3(4), 25. https://doi.org/10.3390/cryptography3040025






