Efficient and Flexible Multi-Factor Authentication Protocol Based on Fuzzy Extractor of Administrator’s Fingerprint and Smart Mobile Device
Abstract
:1. Introduction
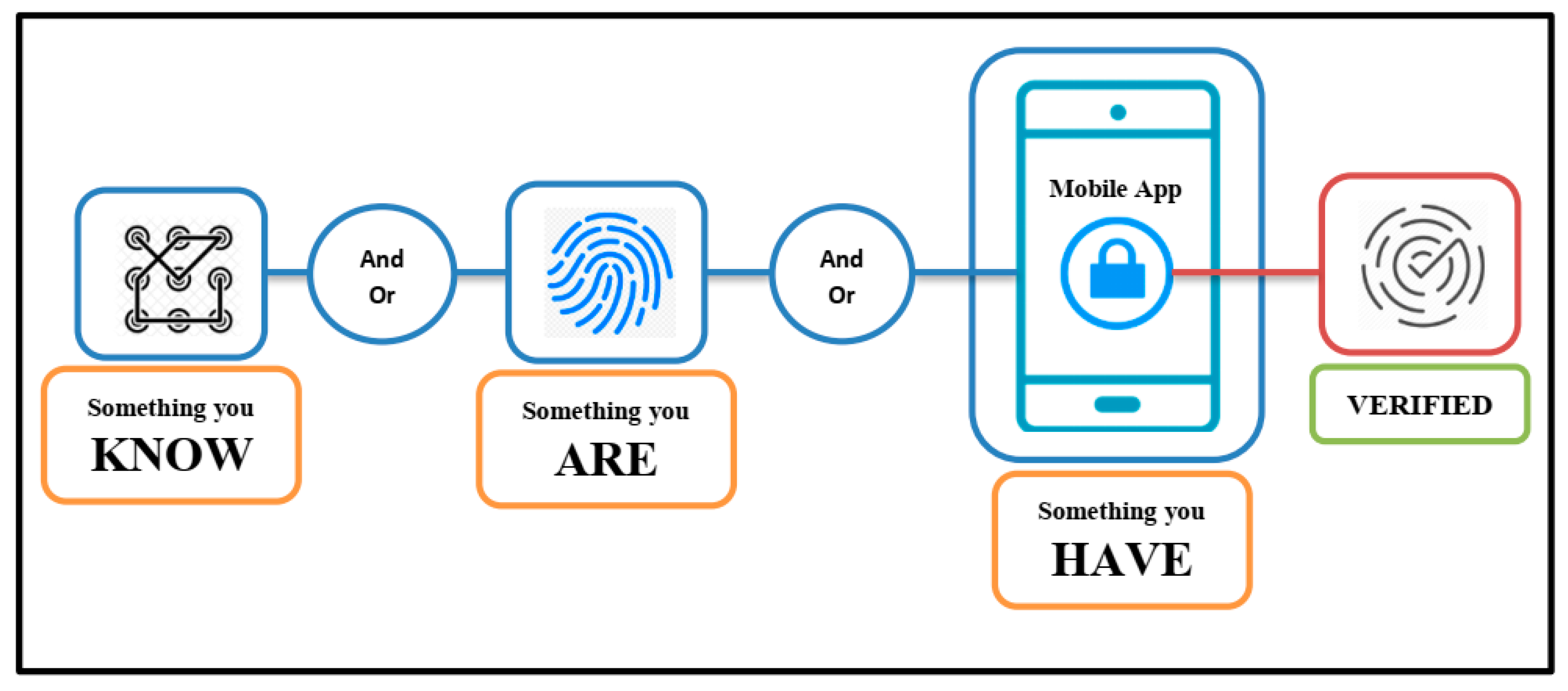
- We design a secure and robust protocol for authenticating the legal administrator that can play the main role for management of IoT devices in future work or server–client systems. This work has positive features such as mutual authentication, once-secure session key for each login phase, the anonymity of password and biometric, unlinkability, and security against a stolen smart mobile device and online change of password.
- We propose an MFA protocol based on a fuzzy extractor of the user’s fingerprint, smart mobile phone and an encrypted-credential file that keeps our main factors in safe mode against malicious attacks.
- We present a security analysis of our work, and we have noted that our protocol resists the replay attacks, man-in-the-middle attacks, insider attacks, offline dictionary attacks, eavesdropping and traffic attacks.
- Consequently, we prove the proposed protocol on standard and strong security proof tool AVISPA.
- We present the comparative analysis of our proposed protocol with other related work based on security analyses and resisting well-known attacks.
2. Related Work
3. Symbols Used and Cryptography Concepts
3.1. Symbols Used
3.2. Cryptography Concepts
- The decisional Diffie–Hellman () key exchange protocol [34]: A and B agree on a finite cyclic group and choose a generator from them. They then choose randomly , ∊ [1, ||] and exchange and . The secret key is . To break the protocol, a passive eavesdropper, i.e., attacker (Eve), must compute the DDH function, defined as (, ) = .
- Fuzzy Extractor: The fuzzy extractor is a cryptography method for securely authenticating using biometric. Suppose a finite set is a metric space with a distance function along with an error limit, , calculated using error correction codes (Hamming distance, set difference metric, edit distance metric, etc.) [35,36]. The fuzzy extractor contains two operations i.e., Generator () and Reproduction (), with the following features:
- ○
- The operation takes a biometric ∊ of user as input and outputs a secret string ∊ , and a public string ∊ , i.e., Gen() = (,).
- ○
- The operation takes a noisy biometric ∊ of user and the public string as input and reproduces the secret string ∊ as an output, i.e., (, ) = if and only if dis (, ) ≤ .
- Hash function (MD5) [37]: The cryptographic hash function is MD5 (message digest 5). MD5 generates a 128-bit message digest of the input, which is expressed as a 32-digit hexadecimal number. MD5 hash outputs are unique even if the size of the input is different.
- Encryption/Decryption by AES algorithm [38]: The input and output for the AES algorithm contain sequences of 128 bits (digits with values of 0 or 1). These sequences are referred to as blocks and the number of bits they contain as their length. The cipher key for the AES algorithm is a sequence of 128, 192 or 256 bits. Other input, output and cipher key lengths are not permitted by this standard.
4. Our Proposed Protocol
4.1. Registration Phase
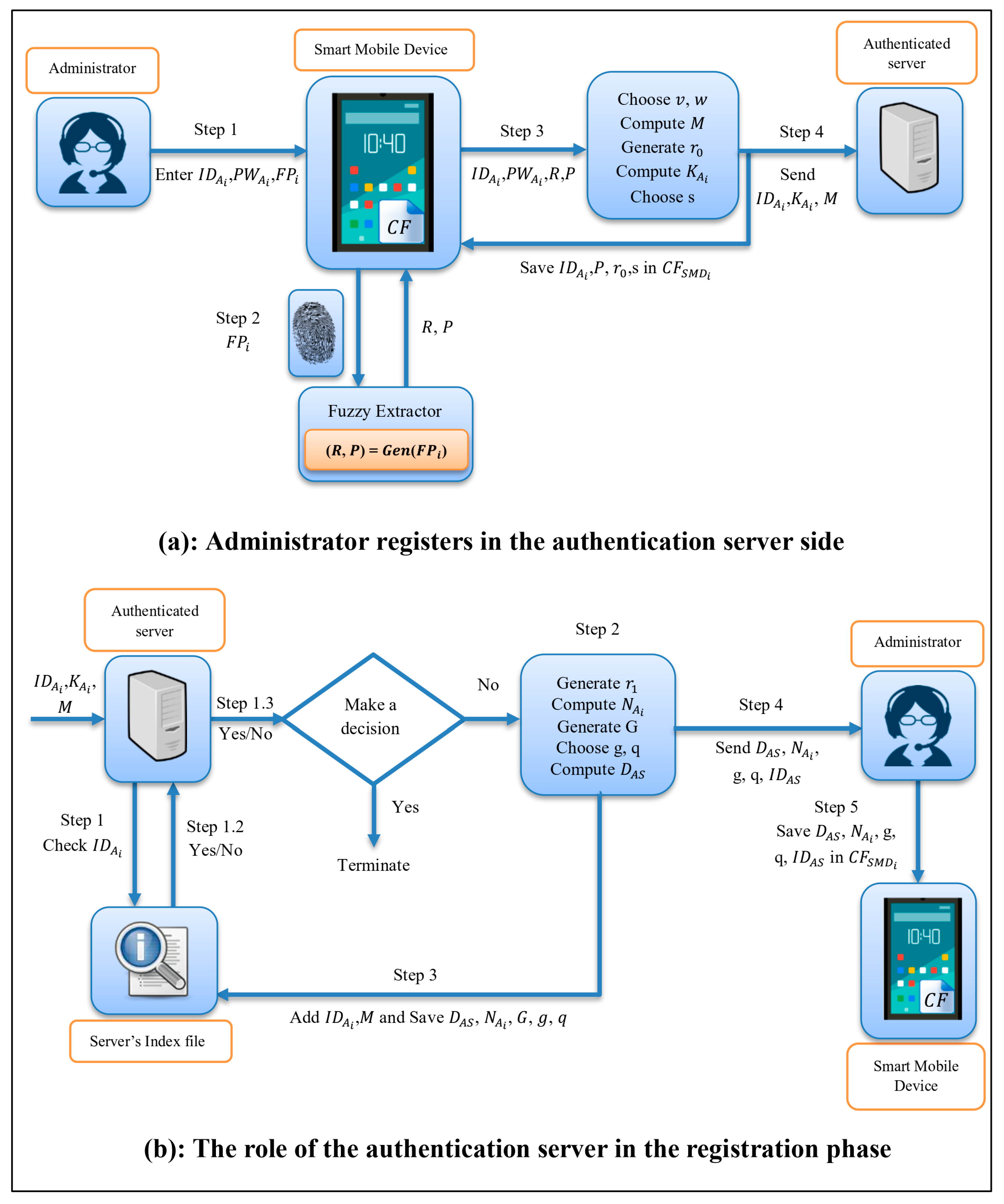
- should be registered into , they depend on their to complete this process via mobile apps, and this step can be described in the following points:
- enters their Username (), Password (), and Fingerprint () by using a mobile app.
- After that, applies the generator function of the fuzzy extractor to extract (,) from , (,) = ().
- chooses two large prime integer numbers , ϵ and computes = * .
- generates a random integer number ϵ , computes a secret parameter = ((,), , ) and chooses a private key () (note: is used with things and users).
- After that, creates a Credential file () to save the main parameters (, , , , , ) into secretly based on = .
- uses their to send a message = (, , ) to (see Figure 3a).
- checks the identity of in Index File () and compares (receiving) ≟ (existing) in ; if the result is equal, has been registered in the system. Otherwise, they create a new record to save of in .
- ○
- generates a random integer number ϵ , computes = h(, , ), and adds (, ) to ’s record in , where contains sensitive information used in the next phases by .
- ○
- Based on the decisional Diffie–Hellman () assumption, generates a group () and chooses a generator from the group and a large prime number (), computes = mod and saves (, , , ) in .
- sends = (, , , , ), to (see Figure 3b).
4.2. Login Phase
- They enter Identity (), Password (), and Fingerprint () by using a mobile device to allow them to use the important parameters inside .
- applies the reproduction function of the fuzzy extractor to calculate = (,).
- decrypts = to allow to use the important parameters inside .
- verifies the authority of based on extracting important parameters from the above steps and as follows:
- ○
- computes = ((, ), , ), = mod .
- ○
- After that, compares (computing) ≟ (existing) in the credential file; if the result is false, they terminate the login phase. Otherwise, performs the following steps:
- generates a random integer number ϵ , computes = (||||).
- computes ASCII code for , = , = mod , and = (||).
- They send = (, (||), , ) to .
- checks time stamp − ≤ ; if the equivalent condition is not fulfilled, aborts the authentication phase. Otherwise, compares ≟ ; if they match, calculates the following steps, otherwise terminates the authentication phase.
- ○
- computes = h (||||) and applies ASCII code for , = .
- ○
- computes = mod , the session key = mod , = (||), and encrypts (||) by using :
- Finally, sends = (, , ) to .
- They check − ≤ ; if not equal, they abort the authentication phase. Otherwise, they verify (from ) ≟ (from ); if not equal, they terminate the authentication phase. Otherwise, they implement these steps (see Figure 5):
- ○
- computes the session key = mod , from decrypts by using to retrieve (, ) = ().
- ○
- After that, checks if (from decrypted ) ≟ (from ) and (from decrypted ) ≟ (existing); if not equal, they terminate the process, otherwise they compute = (||) and encrypt (||) by using :
- Finally, sends to .
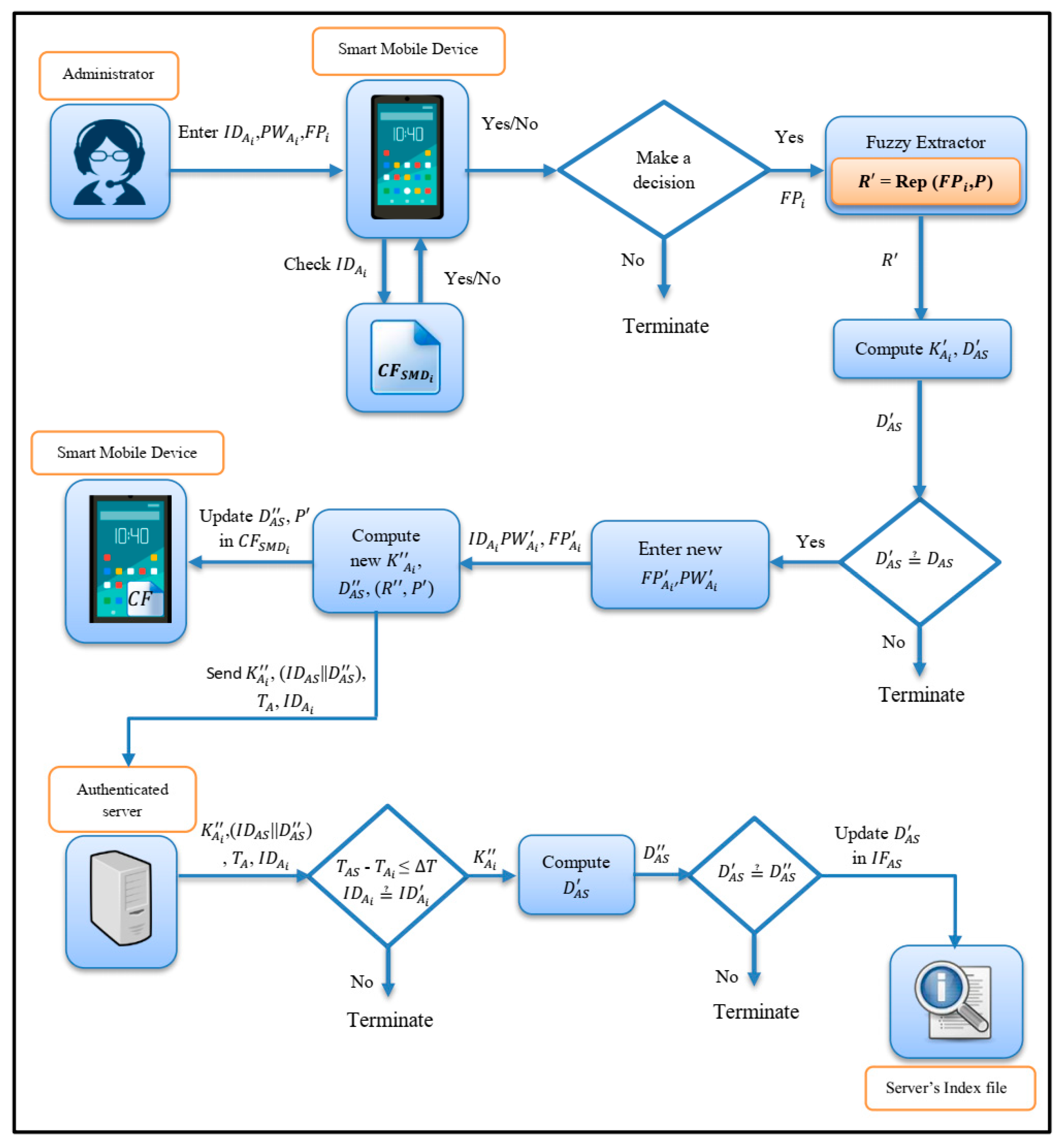
4.3. Change Password Phase
- enters the specified , , using to log into the system.
- computes = (, ), and decrypts = to allow to use important parameters inside .
- checks of with the value stored in when is correcting, they compute = ((, ), , ), = mod and compare ≟ (existing) in ; if not equal, they terminate the password change request, otherwise they go to the next steps.
- enters the new fingerprint () and new Password () into , which computes the new values (, ) = (), = ((,), , ), = mod .
- Eventually, updates the values (,) in , encrypts = , and sends = (,(||),,).
- AS checks − ≤ , (from ) ≟ (from ); if not equal, they terminate the request.
- AS computes new = mod , and checks (computing) ≟ (from ); if the equation is not equal, the process ends. Otherwise, they update the value of in with .
5. Security Analysis
- checks the validity of ’s parameters (, , and ) by applying the fuzzy extractor function to compute = mod .
- Then, compares ≟ (existing in the credential file); if the result is false, is not authorized and terminates the login phase. Otherwise, computes = mod , = (||).
- They send = ((||), , ) to .
- checks time stamp − ≤ ; if so, they compare ≟ , and, if not a match, they ensure the is not authorized. Otherwise, they compute the following steps:computes = mod , the session key = mod , and = (||), and encrypts (||) by using :
- sends = (, , ) to .
- They check − ≤ and (from ) ≟ (from ); if the results are not equal, they know the is unauthorized and terminate the authentication phase. Otherwise, they implement these steps:decrypts by using to retrieve (, ) = (). After that, checks (from decrypted ) ≟ (from ), (from decrypted ) ≟ (existing); if the results are equal, they terminate the process, otherwise they compute = (||) and encrypt (||) by using :
- sends to as a second factor.
- applies the generation function of the fuzzy extractor on , extracts the main values (, ) = (), generates a random integer number ϵ , and computes = ((,), , ).
- Administrator’s parameters (, ) are not saved in and while each pair of (, ) is saved in and other parameters (, , , and ) are saved as anomalous elements in to check the validity of in the login and authentication phases (where = h(, , ), = mod ). Assuming an attacker has the ability to access the main parameters (, , , , and ), the attacker cannot know the details of or as these parameters have been saved in an anomalous way and they fail to use it again to login instead of . □
- generates a random integer number ϵ and computes = (||||).
- computes ASCII code for , = , = mod , and = (||). □
- sends = ((||), , ) to .
- sends = (, , ) to .
- sends = (||) to .
6. Experimental Results
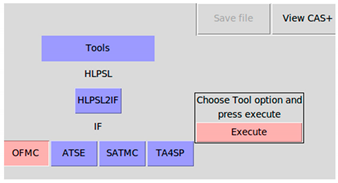
The AVISPA Tool
- On-the-fly model-checker (OFMC)
- Constraint-logic based attack searcher (CL-AtSe)
- SAT-based model-checker (SATMC)
- Tree automata based on automatic approximation for the analysis of security protocols (TA4SP)
- Transitions are defined as steps. The first basic role starts with a statement containing the beginning. This status only changes after receiving a message.
- Composed Roles contain one or more basic roles to implement together and denote the sessions involved in the protocol (see Table 4).
- Environment contains all sessions; the attacker may perform some roles as an authorized user (see Table 5).
- Security Goal defines the security objective of the protocol. Some of the goals used in this section include:
- Secret (SK’, sk, {Adm,AS}): It specifies that the information (SK’) is secretly shared with Adm and AS.
- Witness (Adm, AS, admin_authserver_ra, Ra2’): It represents the weak authenticity of Adm by AS and Adm is the witness for the data Ra2’. The identity of this goal is represented as admin_authserver_ra in the goal section.
- Request (Adm, AS, admin_authserver_m, M6’): It represents the strong authenticity of Adm by AS on M6’ with an identity admin_authserver_m.
- Summary: It specifies the security reliability of the protocol regarding safe, unsafe or inconclusive.
- Details: The output determines the environment and context under which the protocol is claimed to be safe, unsafe or inconclusive.
- Protocol: The name of the protocol required for documentation is written here.
- Goal: This section represents the specified security goal of the protocol.
- Backend: This section denotes one of the four back-ends.
7. Comparison with Other Related Works
7.1. Security Features
7.2. Performance Comparisons
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Baran, P. On Distributed Communications Networks. IEEE Trans. Commun. 1964, 12, 1–9. [Google Scholar] [CrossRef]
- Licklider, J.C.R. Memorandum for Members and Affiliates of the Intergalactic Computer Network; Technical Report; Advanced Research Projects Agency: Washington, DC, USA, 1963. [Google Scholar]
- Hsu, C.-L.; Lu, H.-P.; Hsu, H.-H. Adoption of the mobile Internet: An empirical study of multimedia message service (MMS). Omega 2007, 35, 715–726. [Google Scholar] [CrossRef]
- Atzori, L.; Iera, A.; Morabito, G. The Internet of Things: A Survey. Comput. Netw. 2010, 54, 2787–2805. [Google Scholar] [CrossRef]
- Gubbi, J.; Buyya, R.; Marusic, S.; Palaniswami, M. Internet of Things (IoT): A Vision, Architectural Elements, and Future Directions. Future Gener. Comput. Syst. 2013, 29, 1645–1660. [Google Scholar] [CrossRef]
- Mohsin, J.K.; Han, L.; Hegarty, R.; Hammoudeh, M. Two Factor vs Multi-factor, an Authentication Battle in Mobile Cloud Computing Environments. In Proceedings of the International Conference on Future Networks and Distributed Systems, Cambridge, UK, 19–20 July 2017. [Google Scholar]
- Konoth, R.K.; van der Veen, V.; Bos, H. How Anywhere Computing Just Killed Your Phone-Based Two-Factor Authentication; Springer: Berlin/Heidelberg, Germany, 2016. [Google Scholar]
- Kim, J.-J.; Hong, S.-P. A Method of Risk Assessment for Multi-Factor Authentication. J. Inf. Process. Syst. 2011, 7, 187–198. [Google Scholar] [CrossRef] [Green Version]
- Wang, D.; Wang, P. Offline Dictionary Attack on Password Authentication Schemes Using Smart Cards. Lect. Notes Comput. Sci. 2015, 7807, 221–237. [Google Scholar]
- Althobaiti, O.; Al-rodhaan, M.; Al-dhelaan, A. An Efficient Biometric Authentication Protocol for Wireless Sensor Networks. Int. J. Distrib. Sens. Netw. 2013, 9, 407971. [Google Scholar] [CrossRef]
- Boneh, D. The Decision Diffie-Hellman Problem. In Proceedings of the International Algorithmic Number Theory Symposium, Portland, OR, USA, 21–25 June 1998. [Google Scholar]
- Choi, Y.; Lee, Y.; Won, D. Security Improvement on Biometric Based Authentication Scheme for Wireless Sensor Networks Using Fuzzy Extraction. Int. J. Distrib. Sens. Netw. 2016, 12, 8572410. [Google Scholar] [CrossRef]
- Park, Y.; Park, Y. Three-factor user authentication and key agreement using elliptic curve cryptosystem in wireless sensor networks. Sensors 2016, 16, 2123. [Google Scholar] [CrossRef]
- Ndibanje, B.; Lee, H.-J.; Lee, S.-G. Security Analysis and Improvements of Authentication and Access Control in the Internet of Things. Sensors 2014, 14, 14786–14805. [Google Scholar] [CrossRef] [Green Version]
- Sun, J.; Zhang, R. TouchIn: Sightless two-factor authentication on multi-touch mobile devices. In Proceedings of the 2014 IEEE Conference on Communications and Network Security, San Francisco, CA, USA, 29–31 October 2014; pp. 436–444. [Google Scholar]
- Bruun, A.; Jensen, K.; Kristensen, D.; Nv, D.-R. Usability of Single- and Multi-Factor Authentication Methods on Tabletops: A Comparative Study. In Proceedings of the 5th IFIP WG 13.2 International Conference on Human-Centered Software Engineering, HCSE 2014, Paderborn, Germany, 16–18 September 2014; Springer: Berlin/Heidelberg, Germany, 2014. [Google Scholar]
- Ometov, A.; Bezzateev, S.; Mäkitalo, N.; Andreev, S.; Mikkonen, T.; Koucheryavy, Y. Multi-Factor Authentication: A Survey. Cryptography 2018, 2, 1. [Google Scholar] [CrossRef]
- Meixner, G. Automotive User Interfaces; Springer: Cham, Switzerland, 2017. [Google Scholar]
- Hwang, M.-S.; Li, L.-H. A new remote user authentication scheme using smart cards. IEEE Trans. Consum. Electron. 2000, 46, 28–30. [Google Scholar] [CrossRef]
- Khan, S.H.; Akbar, M.A.; Shahzad, F.; Farooq, M.; Khan, Z. Secure biometric template generation for multi-factor authentication. Pattern Recognit. 2015, 48, 458–472. [Google Scholar] [CrossRef] [Green Version]
- Acharya, S.A.S. Two Factor Authentication Using Smartphone Generated One Time Password. IOSR J. Comput. Eng. 2013, 11, 85–90. [Google Scholar] [CrossRef]
- Chen, X.; Tian, J.; Su, Q.; Yang, X.; Wang, F.-Y. A Secured Mobile Phone Based on Embedded Fingerprint Recognition Systems. In Proceedings of the IEEE International Conference on Intelligence and Security Informatics, ISI 2005, Atlanta, GA, USA, 19–20 May 2005; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3495, pp. 549–553. [Google Scholar]
- Derawi, M.O.; Yang, B.; Busch, C. Fingerprint Recognition with Embedded Cameras on Mobile Phones. In Proceedings of the Third International ICST Conference on Security and Privacy in Mobile Information and Communication Systems, MobiSec 2011, Aalborg, Denmark, 17–19 May 2011; Springer: Berlin/Heidelberg, Germany, 2012; Volume 94, pp. 136–147. [Google Scholar]
- Sin, S.W.; Zhou, R.; Li, D.; Isshiki, T.; Kunieda, H. Narrow Fingerprint Sensor Verification with Template Updating Technique. IEICE Trans. Fundam. Electron. Commun. Comput. Sci. 2012, 95, 346–353. [Google Scholar] [CrossRef]
- Ravi, H.; Sivanath, S.K. A novel method for touch-less finger print authentication. In Proceedings of the 2013 IEEE International Conference on Technologies for Homeland Security (HST), Waltham, MA, USA, 12–14 November 2013; pp. 147–153. [Google Scholar]
- Dhillon, P.K.; Kalra, S. Secure multi-factor remote user authentication scheme for Internet of Things environments. Int. J. Commun. Syst. 2017, 30, e3323. [Google Scholar] [CrossRef]
- Shrestha, B.; Tamrakar, S.; Mohamed, M.; Saxena, N. Theft-Resilient Mobile Wallets: Transparently Authenticating NFC Users with Tapping Gesture Biometrics. In Proceedings of the 32nd Annual Conference on Computer Security Applications, Los Angeles, CA, USA, 5–8 December 2016; pp. 265–276. [Google Scholar]
- Buschek, D.; De Luca, A.; Alt, F. Improving Accuracy, Applicability and Usability of Keystroke Biometrics on Mobile Touchscreen Devices. In Proceedings of the 33rd Annual ACM Conference on Human Factors in Computing Systems—CHI ’15, Seoul, Korea, 18–23 April 2015; pp. 1393–1402. [Google Scholar]
- Buriro, A.; Crispo, B.; Del Frari, F.; Wrona, K. Touchstroke: Smartphone User Authentication Based on Touch-Typing Biometrics. In Proceedings of the ICIAP 2015 International Workshops on New Trends in Image Analysis and Processing, Genoa, Italy, 7–11 September 2015; Springer: Cham, Switzerland, 2015; Volume 9281, pp. 27–34. [Google Scholar]
- Belk, M.; Fidas, C.; Germanakos, P.; Samaras, G. Computers in Human Behavior The interplay between humans, technology and user authentication: A cognitive processing perspective. Comput. Human Behav. 2017, 76, 184–200. [Google Scholar] [CrossRef]
- Michelin, R.A.; Zorzo, A.F.; Campos, M.B.; Neu, C.V.; Orozco, A.M.S. Smartphone as a biometric service for web authentication. In Proceedings of the 11th International Conference for Internet Technology and Secured Transactions (ICITST), Barcelona, Spain, 5–7 December 2016; pp. 405–408. [Google Scholar]
- Jeong, Y.; Park, J.S.; Park, J.H. An efficient authentication system of smart device using multi factors in mobile cloud service architecture. Int. J. Commun. Syst. 2015, 28, 659–674. [Google Scholar] [CrossRef]
- Sun, J.; Zhong, Q.; Kou, L.; Wang, W.; Da, Q.; Lin, Y. A lightweight multi-factor mobile user authentication scheme. In Proceedings of the IEEE INFOCOM 2018—IEEE Conference on Computer Communications, Honolulu, HI, USA, 15–19 April 2018; pp. 831–836. [Google Scholar]
- Whitfield, D.; Martin, E.H. New Directions in Cryptography. IEEE Trans. Inf. Theory 1976, 22, 644–654. [Google Scholar]
- Dodis, Y.; Reyzin, L.; Smith, A. Fuzzy Extractors: How to Generate Strong Keys from Biometrics and Other Noisy Data. Inf. Secur. Appl. 2004, 3027, 523–540. [Google Scholar]
- Dodis, Y.; Ostrovsky, R.; Reyzin, L.; Smith, A. Fuzzy Extractors: How to Generate Strong Keys from Biometrics and other Noisy Data. SIAM J. Comput. 2008, 38, 97–139. [Google Scholar] [CrossRef]
- Sagar, F.A. Cryptographic Hashing Functions—MD5. Available online: http://cs.indstate.edu/~fsagar/doc/ paper.pdf (accessed on 7 September 2019).
- Announcing the Advanced Encryption Standard (AES); Federal Information Processing Standards (FIPS); National Institute of Standards and Technology: Gaithersburg, MD, USA, 2001.
- Pfitzmann, A.; Hansen, M. Anonymity, Unlinkability, Unobservability, Pseudonymity, and Identity Management—A Consolidated Proposal for Terminology. Available online: http://citeseerx.ist.psu.edu/viewdoc/summary?doi=10.1.1.153.6354 (accessed on 7 September 2019).
- Maurya, A.K.; Sastry, V.N. Fuzzy Extractor and Elliptic Curve Based Efficient User Authentication Protocol for Wireless Sensor Networks and Internet of Things. Information 2017, 8, 136. [Google Scholar] [CrossRef]
- The AVISPA Team. HLPSL Tutorial 2006. Available online: http://www.avispa-project.org/package/tutorial.pdf (accessed on 7 September 2019).
- The AVISPA Team. AVISPA v1. 0 User Manual 2006. Available online: http://www.avispa-project.org/package/user-manual.pdf (accessed on 7 September 2019).
- León, O.; Hernández-Serrano, J.; Soriano, M. A secure and effective biometric-based user authentication scheme for wireless sensor networks using smart card and fuzzy extractor. Int. J. Commun. Syst. 2010, 23, 633–652. [Google Scholar]
- Moon, J.; Lee, D.; Lee, Y.; Won, D. Improving Biometric-Based Authentication Schemes with Smart Card Revocation/Reissue for Wireless Sensor Networks. Sensors 2017, 17, 940. [Google Scholar] [CrossRef] [PubMed]




| Symbol | Description |
|---|---|
| Authenticated Server. | |
| The administrator of a system. | |
| Smart mobile device. | |
| The number of administrators. | |
| Identity of administrators. | |
| Identity of an authenticated server. | |
| The password of an administrator. | |
| Fingerprint of administrators. | |
| , , | Random integer number. |
| Set of integer numbers within range . | |
| Secret information of Fuzzy Extractor. | |
| Public Reproduction parameter of Fuzzy Extractor. | |
| Secret parameter of Administrator. | |
| Generator function of Fuzzy extractor. | |
| Reproduction function of Fuzzy extractor. | |
| Hash function. | |
| Encryption function. | |
| Decryption function. | |
| Index file of an administrator. | |
| Credential file of Smart mobile device. | |
| Contain sensitive information. | |
| The private key of an administrator. | |
| , , | Large prime integer numbers. |
| Group of DDH. | |
| The generator of the group. | |
| A large prime number. | |
| Time of an administrator. | |
| Time of an authenticated server. | |
| A secret number of an administrator. | |
| A secret number of an authenticated server. | |
| Timestamp. | |
| Session key | |
| || | Concatenation operation. |
| The inverse of Concatenation operation. | |
| * | Multiplication operation. |
| role admin () Adm,AS: agent, S: symmetric_key, H,Gen,Rep,Mul,DDH,ASCII,Enc,Dec: hash_func, SND,RCV: channel(dy)) played_by Adm def= local State: nat, Das,Das1,FP,FP1,G,G1,Ha,Has,Ias,IDa,IDas,Ja,Ka,Ka1,M,M6,Na,Pas,PFP,PWa,Q,Ra1,Ra2,Ras1,RFP,RFP1,Ta,Ta1,Tas,Ua,V,Va,Vas,W,Xa,Xas,Ya,Yas: text, SK: message const admin_authserver_sk,authserver_admin_sk,authserver_admin_ra,admin_authserver_ra,adminv,authsv: protocol_id init State:= 0 transition 0.State = 0 /\ RCV(start) =|> State’:= 2 /\ V’:= new() /\ W’:= new() /\ M’:= Mul(V’.W’) /\ Ra1’:= new() /\ RFP’:= Gen(FP) /\ Ka’:= H(H(RFP’,Ra1’),IDa,PWa) /\ S’:= new() /\ secret(S’,adminv,Adm) /\ SND(IDa,Ka’,M’) 2.State = 2 /\ RCV(Na’,Das’,G1’,Q’,IDas’) =|> State’: = 4 /\ RFP1’: = Rep(FP1.PFP) /\ Ka1’: = H(H(RFP1’, Ra1),IDa,PWa) /\ Das1’: = DDH (exp (G1’, Ka1’). Q’) /\ Ra2’: = new () /\ Xa’: = new () /\ secret(Xa’, adminv,Adm) /\ Ta’: = new () /\ Ha’: = h (Ta’.IDa.Ra2’) /\ Ya’: = ASCII(Ha’) /\ Va’: = exp(DDH(exp(G1’,Ya’).Q’),Xa’) /\ secret (Va’,adminv,Adm) /\ Ua’: = (Va’.Das’) /\ witness (Adm,AS,admin_authserver_ra,Ra2’) /\ SND ((IDas’.Ra2’),Ua’,Ta’) 4.State = 4 /\ RCV(Ias’,Pas’,Tas’) =|> State’:= 6 /\ Ta1’:= new() /\ Vas’:= Mul(Pas’.Na) /\ SK’:= DDH(exp(Vas’,Xa),Q) /\ Ja’:= (IDas.Das) /\ M6’:= {IDa.Ja’}_SK’ /\ secret(SK’,sk,{Adm,AS}) /\ request(Adm,AS,admin_authserver_m,M6’) /\ SND(M6) /\ request(Adm,AS,admin_authserver_sk,SK’) end role |
| role authserver () Adm,AS: agent, S: symmetric_key, H,Gen,Rep,Mul,DDH,ASCII,Enc,Dec: hash_func, SND,RCV: channel(dy)) played_by AS def= local State: nat, Das,Das1,FP,FP1,G,G1,Ha,Has,Ias,IDa,IDas,Ja,Ka,Ka1,M,M6,Na,Pas,PFP,PWa,Q,Ra1,Ra2,Ras1,RFP,RFP1,Ta,Ta1,Tas,Ua,V,Va,Vas,W,Xa,Xas,Ya,Yas: text, SK: message const admin_authserver_sk, authserver_admin_sk, admin_authserver_m, authserver_admin_m, authserver_admin_ra, admin_authserver_ra, adminv, authsv: protocol_id init State:= 1 transition 1.State = 1 /\ RCV(IDa,Ka’,M’) =|> State’:= 3 /\ Ras1’: = new() /\ Na’: = H(Ras1’.IDa.Ka’) /\ G’: = new() /\ G1’: = new() /\ Q’: = new() /\ Das’: = DDH(exp(G1’,Ka’).Q’) /\ secret(Ras1’,authsv,AS) /\ SND(Na’,Das’,G1’,Q’,IDas) 3.State = 3 /\ RCV((IDas’.Ra2’),Ua’,Ta’) =|> State’: = 5 /\ Tas’: = new() /\ request (Adm,AS,authserver_admin_ra,Ra2’) /\ Has’: = h(Ta’.IDa.Ra2’) /\ Yas’: = ASCII(Has’) /\ Xas’: = new() /\ Vas’: = exp(DDH(exp(G1,Yas’).Q),Xas’) /\ secret(Xas’,authsv,AS) /\ Va’: = Mul(Ua’.Das) /\ SK’: = DDH(exp(Va’,Xas’).Q) /\ Pas’: = (Vas’.Na) /\ Ias’: = {IDa.Pas’}_SK’ /\ secret(SK’,sk,{AS,Adm}) /\ SND (Ias’,Pas’,Tas’) /\ witness(AS,Adm,authserver_admin_sk,SK’) 5.State =5 /\ RCV(M6’) =|> State’: = 7 /\ SK’: = DDH(exp(Va,Xas).Q) /\ request(AS,Adm,authserver_admin_m,M6’) /\ IDas’: = {M6’}_SK end role |
| role session () Adm,AS:agent, S: symmetric_key, H,Gen, Rep, Mul, DDH, ASCII, Enc, Dec: hash_func) def= local SAdm, RAdm, SAS, RAS: channel(dy) composition admin(Adm,AS,S,H,Gen,Rep,Mul,DDH,ASCII,Enc,Dec,SAdm,RAdm) /\ authserver (Adm,AS,S,H,Gen,Rep,Mul,DDH,ASCII,Enc,Dec,SAS,RAS) end role |
| role environment () def= const admin_authserver_m,authserver_admin_m, adminv,authsv,sk, authserver_admin_ra,admin_authserver_ra, admin_authserver_sk,authserver_admin_sk: protocol_id, adm, as: agent, sadminas,sias,sadmini: symmetric_key, h,gen, rep,mul,ddh,ascii,enc,dec: hash_func intruder_knowledge = {adm,as,h,gen,rep,mul,ddh,ascii,enc,dec,sias,sadmini} composition session(adm,as,sadminas,h,gen, rep,mul,ddh,ascii,enc,dec) /\ session(i,as,sias,h,gen, rep,mul,ddh,ascii,enc,dec) /\ session(adm,i,sadmini,h,gen, rep,mul,ddh,ascii,enc,dec) end role |
| goal secrecy_of sk,adminv,authsv authentication_on admin_authserver_m,authserver_admin_m,authserver_admin_ra,admin_authserver_ra,admin_authserver_sk,authserver_admin_sk end goal environment() |
| Using OFMC BACKEND | Using CL-ATSE BACKEND |
|---|---|
| SUMMARY SAFE DETAILS BOUNDED_NUMBER_OF_SESSIONS PROTOCOL /home/span/span/testsuite/results/testify GOAL as specified BACKEND OFMC COMMENTS STATISTICS parseTime: 0.00 s searchTime: 0.16 s visitedNodes: 12 nodes depth: 4 plies | SUMMARY SAFE DETAILS BOUNDED_NUMBER_OF_SESSIONS TYPED_MODEL PROTOCOL home/span/span/testsuite/results/test.if GOAL As Specified BACKEND CL-AtSe STATISTICS Analysed: 0 states Reachable: 0 states Translation: 0.04 s Computation: 0.00 s |
 |  |
| Security Feature | [12] | [13] | [40] | [43] | [44] | Our Protocol | |
|---|---|---|---|---|---|---|---|
| 1 | Provides mutual authentication. | Yes | Yes | Yes | Yes | Yes | Yes |
| 2 | Provides a once secure session key. | Yes | Yes | Yes | Yes | Yes | Yes |
| 3 | Provides anonymity of password and biometric. | Yes | Yes | Yes | Yes | Yes * | Yes |
| 4 | Provides unlinkability. | No | No | No | No | No | Yes |
| 5 | Secure against Stolen Smart Mobile Device. | No | No | No | No | No | Yes |
| 6 | Resistant to replay attacks. | Yes | No | Yes | Yes | Yes | Yes |
| 7 | Resistant to Man-in-the-middle attacks. | No | No | Yes | No | No | Yes |
| 8 | Resistant to eavesdropping and traffic attacks. | No | No | Yes | No | No | Yes |
| 9 | Resistant to an offline dictionary attack. | Yes | Yes | Yes | Yes | Yes | Yes |
| 10 | Resistant to an insider attack. | Yes | Yes | Yes | Yes | Yes | Yes |
| 11 | Provides an online change password. | No | No | Yes | No | Yes | Yes |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Mohammed, A.J.; Yassin, A.A. Efficient and Flexible Multi-Factor Authentication Protocol Based on Fuzzy Extractor of Administrator’s Fingerprint and Smart Mobile Device. Cryptography 2019, 3, 24. https://doi.org/10.3390/cryptography3030024
Mohammed AJ, Yassin AA. Efficient and Flexible Multi-Factor Authentication Protocol Based on Fuzzy Extractor of Administrator’s Fingerprint and Smart Mobile Device. Cryptography. 2019; 3(3):24. https://doi.org/10.3390/cryptography3030024
Chicago/Turabian StyleMohammed, Alzahraa J., and Ali A. Yassin. 2019. "Efficient and Flexible Multi-Factor Authentication Protocol Based on Fuzzy Extractor of Administrator’s Fingerprint and Smart Mobile Device" Cryptography 3, no. 3: 24. https://doi.org/10.3390/cryptography3030024
APA StyleMohammed, A. J., & Yassin, A. A. (2019). Efficient and Flexible Multi-Factor Authentication Protocol Based on Fuzzy Extractor of Administrator’s Fingerprint and Smart Mobile Device. Cryptography, 3(3), 24. https://doi.org/10.3390/cryptography3030024





