Practically Feasible Robust Quantum Money with Classical Verification
Abstract
:Featured Application
Abstract
1. Introduction
2. Materials and Methods
2.1. Definitions for Private Quantum Money
- 1.
- The bank algorithm produces a quantum note $ = (ρ, s.n.) where ρ is a quantum state of the note and s.n. is the classical serial number of the note.
- 2.
- Verification is a protocol with classical communication that is run on the note $, between the noteholder H who claims to possess the note $ and the bank. The output of the protocol is a bit declared by the bank to denote whether the note is valid or not. We denote this final bit as which is 1 when the bank validates the note and 0 otherwise.
- Correctness: The scheme is correct if, for every honest holder H, it holds that
- Unforgeability: the scheme is unforgeable if for any quantum adversary who possesses m notes, has interacted a finitely bounded number of times with the bank and has managed to produce notes , it holds that,
- 1.
- The bank algorithm produces a quantum note $ = ρ where ρ is a quantum state of the note.
- 2.
- Verification is a protocol with classical communication that is run on the note $, between the noteholder H who claims to possess the note $ and the bank. The output of the protocol is a bit declared by the bank to denote whether the note is valid or not. We denote this final bit as which is 1 when the bank validates the note and 0 otherwise.
- Correctness: the scheme is correct if, for every honest holder H, it holds that
- Unforgeability: the scheme is unforgeable if for any quantum adversary who possesses the note $, has interacted a finitely bounded number of times with the bank and has managed to produce two notes and , it holds that,
2.2. Tools for the Money Scheme
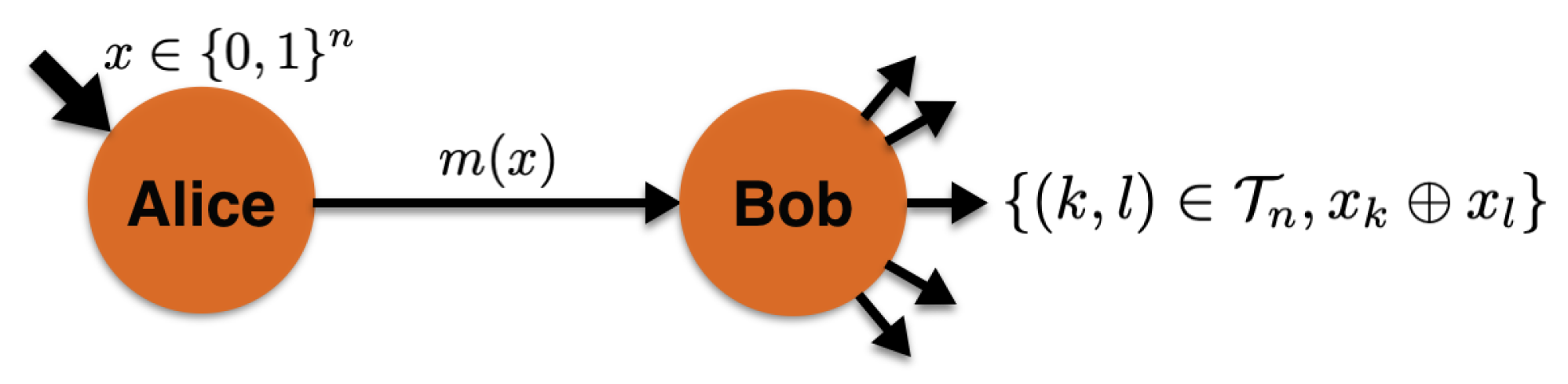
2.2.1. Sampling Matching Problem
2.2.2. Sampling Matching Scheme with Single-Photon States
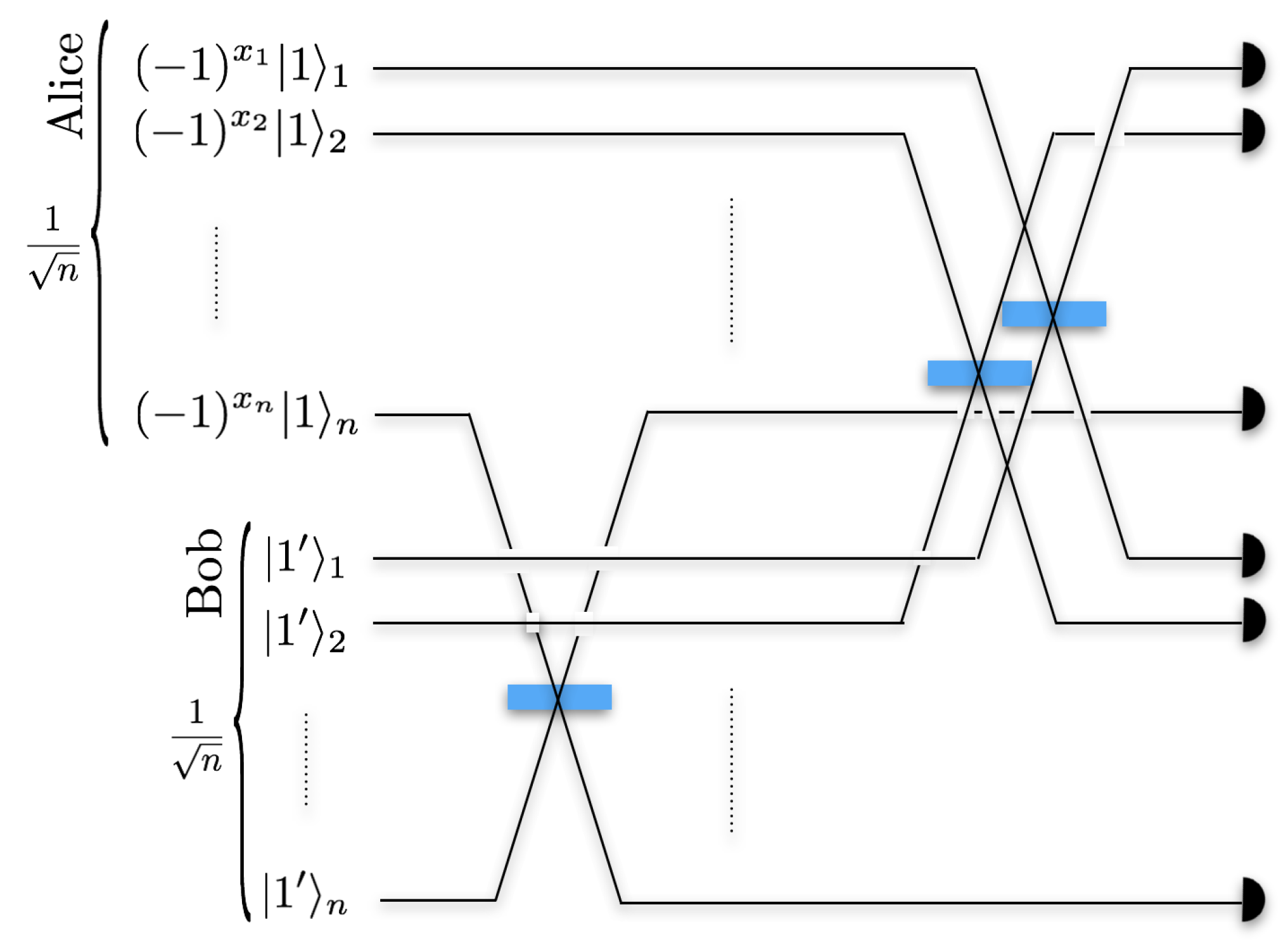
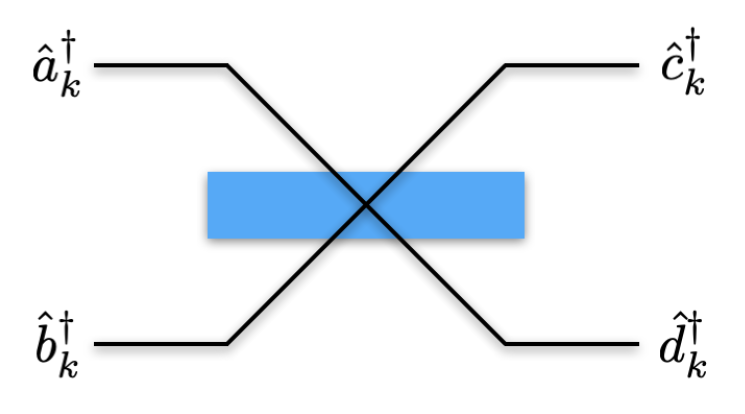
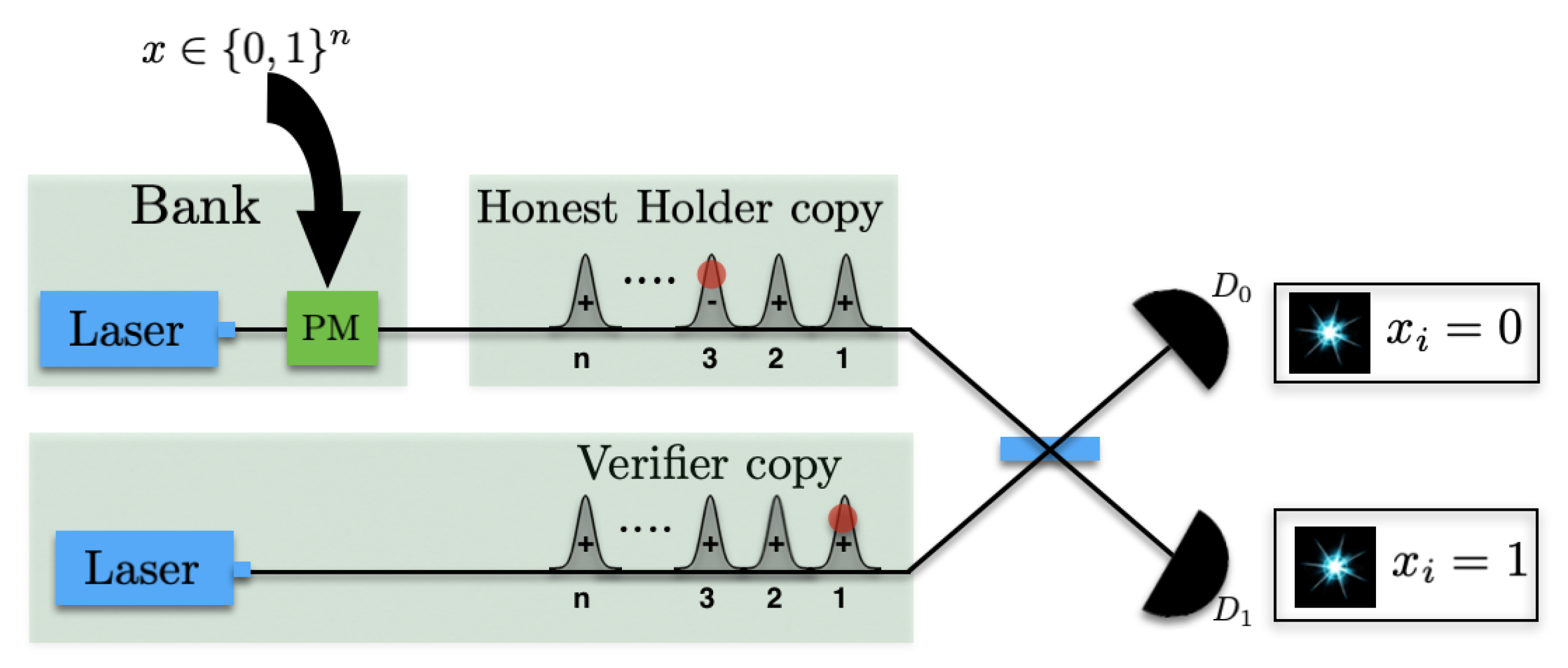
- Simultaneous single-photon clicks in or , for two distinct modes , implies .
- Simultaneous single-photon clicks in or , for two distinct modes , implies .
- Two photons in the same mode or does not reveal the parity outcome for Bob and hence results in inconclusive outcome.
3. Results
3.1. Private Quantum Money Scheme
- Note verification procedure requiring a single round classical communication between the local verifier and the bank,
- Fixed verification circuit for a given input size of the note,
- Multiple note re-usability, meaning the same note can be reused by the holder a number (linear in the size of the note) of times,
- Unconditional security against any adversary trying to forge the banknote while tolerating a noise of up to .
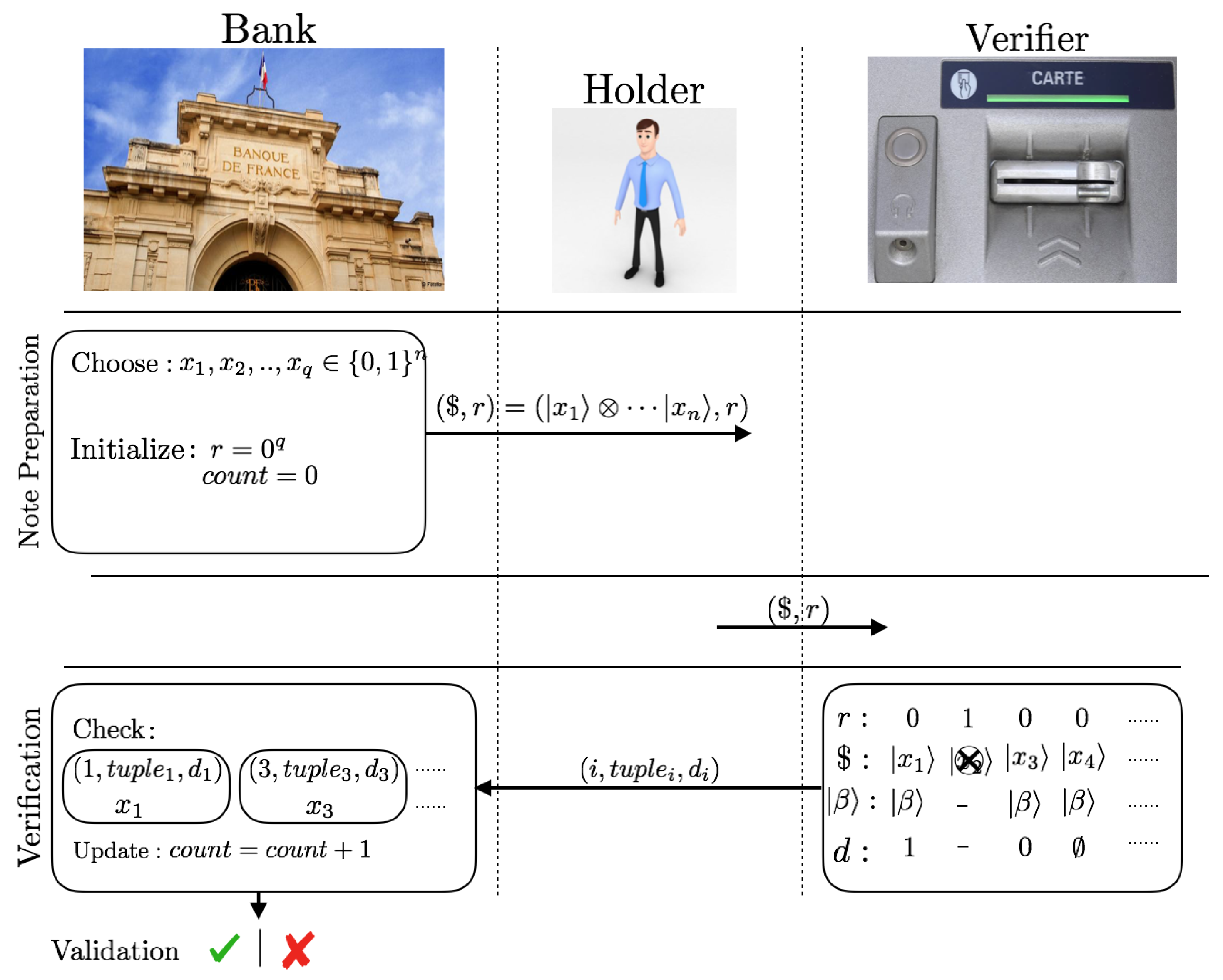
3.1.1. Note Preparation Phase
- The bank independently and uniformly randomly chooses q n-bit binary strings
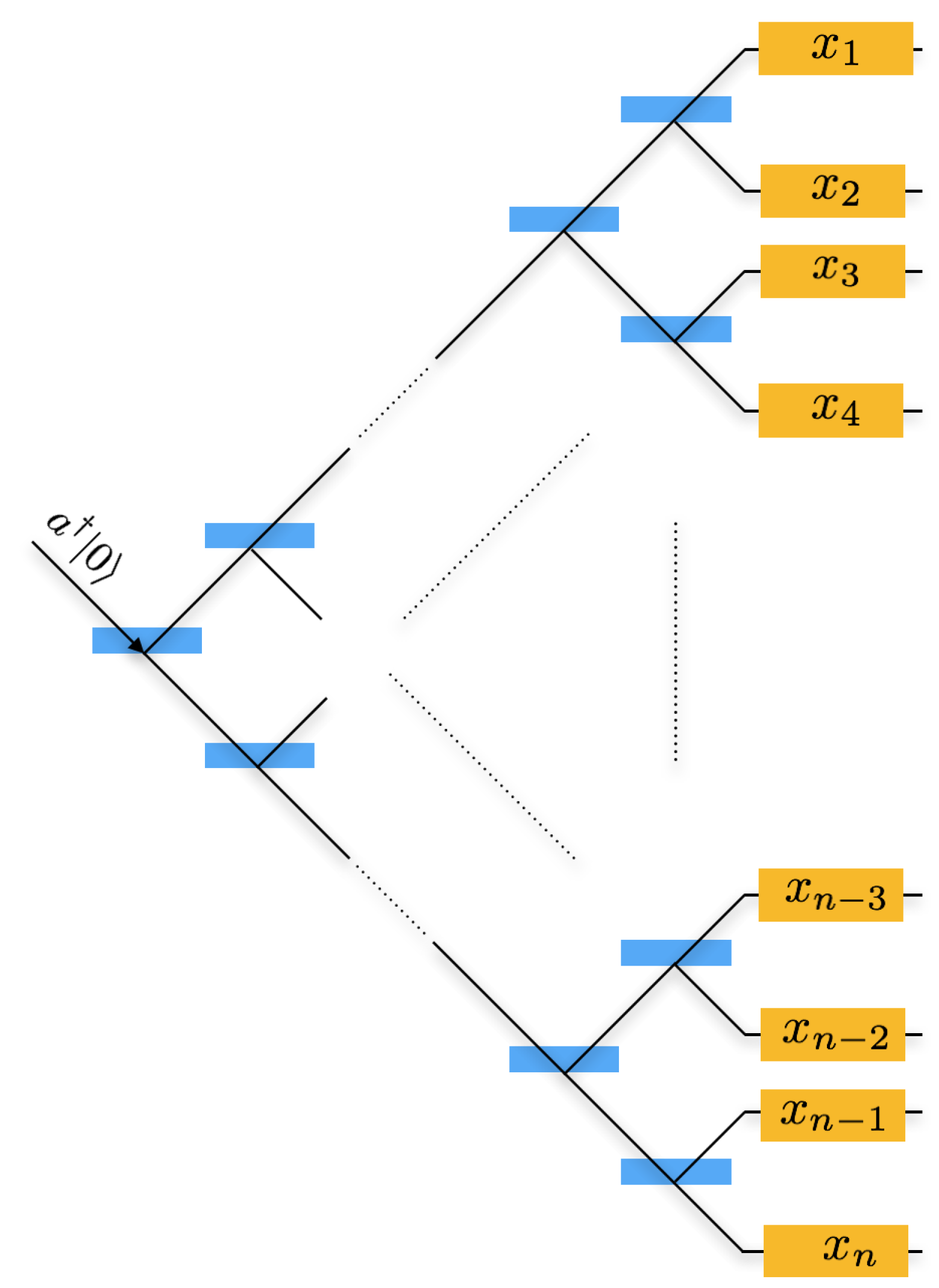
- The bank encodes each binary string into the single-photon state in superposition over n modes,where is the k-th bit value of string and is the creation operator for the mode k with . The note is a combination of all the q copies of the single-photon state .
- The bank creates a classical binary register r and initializes it to . This register keeps the track of positions j where the states have been used for the verification.
- The bank creates a counter variable count and initializes it to 0. This keeps a track of the number of verification attempts.
- The bank sends the quantum note ($, r) to the holder.
3.1.2. Verification Phase
Local testing
- The holder gives the note if the holder is honest) to Ver.
- Ver checks for the number of times the note has been re-used by verifying that the hamming distance of r register , where T is a predefined maximum number of copies in the note that are allowed for verification. If , the note is rendered useless.
- Ver uniformly and randomly selects a subset copies from the states marked . All the corresponding L copies in the r register are then marked to 1.
- For each chosen copy , Ver prepares his local coherent state and runs the SM scheme (Section 2.2.2).
- jVer first checks if he gets two photon clicks in all the chosen L copies. If not, he rejects (this is a check against all those attacks where the adversary removes the single-photon state and introduces either vacuum or a multi-photon state).
- Ver counts the number of successful copies , where he obtains two single-photon clicks in two different modes. For these copies he outputs the parity outcome where the clicks have been obtained in modes k and l. For the rest of the copies, he sets .
- Ver checks if , where is the minimum number of copies that will locally guarantee his acceptance of the note, where is the desired security factor. Here is the expected number of copies where the honest noteholder obtains two single-photon clicks in two different modes when Ver runs the SM scheme.
- Ver proceeds to the classical communication step with the bank only when the note passes this test.
Communication with the bank
- Ver forwards the outcomes for each to the bank through a classical authenticated channel.
- The bank checks if , otherwise the verification attempt is rendered invalid. Here is the ceiling function.
- For each copy with , the bank compares the parity value with the secret string . He validates the note if the number of correct outcomeswhere is the expected number of copies that give the correct parity outcome when the noteholder is honest, and is a positive constant whose optimal value is determined by the forging probability (Section 3.3).
- The bank updates the count by 1.
3.2. Correctness
3.3. Unforgeability of Banknotes
3.4. Quantum Money Scheme with Coherent states
3.4.1. Description of the Money Scheme
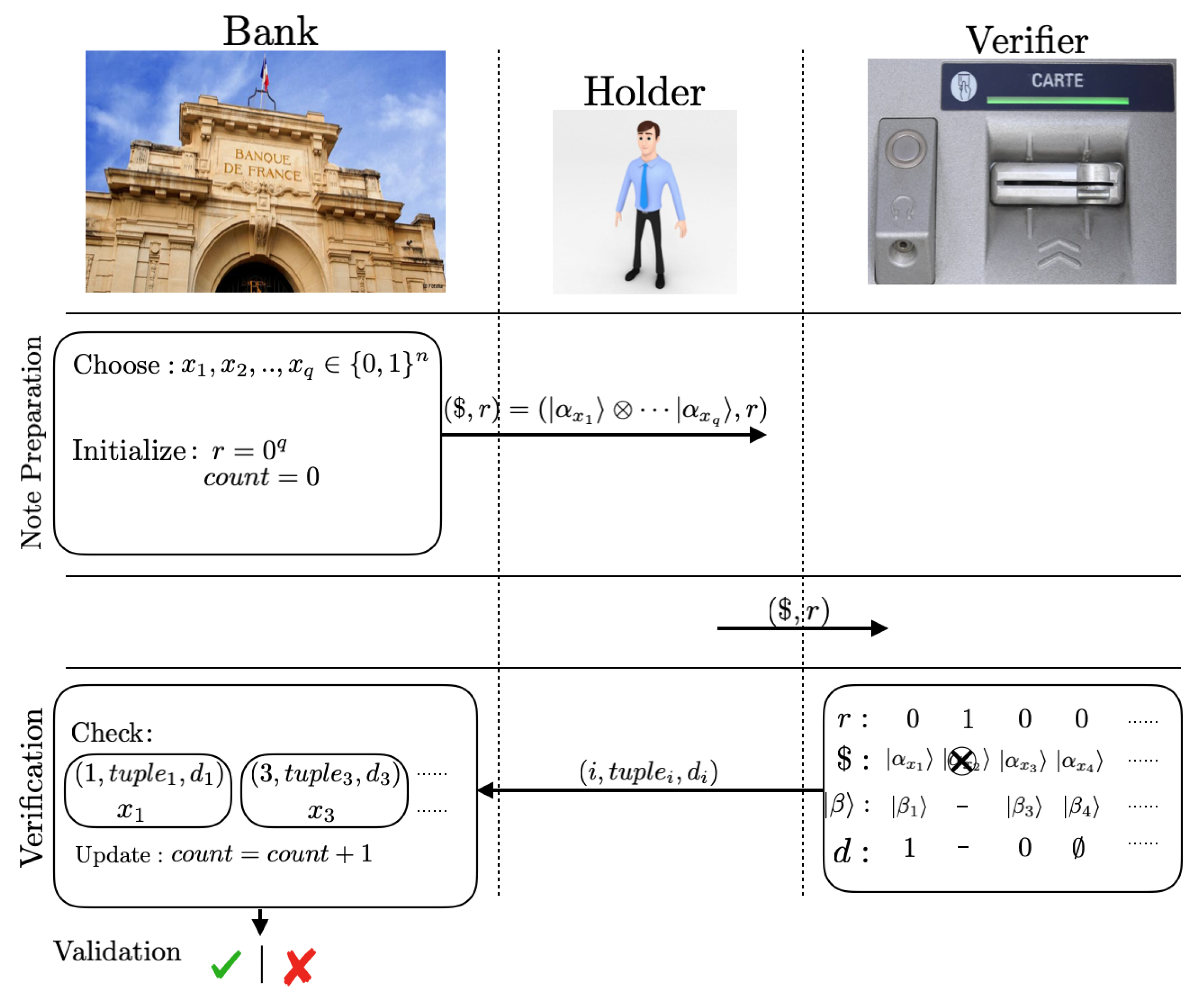
3.4.2. Note Preparation Phase
- The bank independently and randomly chooses qn-bit binary strings
- The bank encodes each the binary string into the phase randomized coherent state , with an average photon number 1,where is the kth bit value of string . The coherent state is a sequence of n coherent pulses in n modes. The note is a combination of all the q copies of the coherent state .
- The bank creates a classical binary register r and initializes it to . This register keeps the track of positions j where the states have been used for the verification.
- The bank creates a counter variable count and initializes it to 0. This keeps a track of the number of verification attempts.
- The bank sends the quantum note ($, r) to the holder.
3.4.3. Verification Phase
Local testing
- The holder gives the note if the holder is honest) to Ver.
- Ver checks the re-usability of the note by verifying that the hamming distance of r register , where T is a predefined maximum number of copies in the note that are allowed for verification. If , the note is rendered useless and must be returned to the bank.
- Ver uniformly and randomly selects a subset copies from the states marked . He marks all the corresponding copies in the r register to 1.
- For each copy , Ver prepares his local coherent state and runs the SM scheme (Figure 6).
- Ver counts the number of successful copies , where he obtains exactly two single-photon clicks in two different time modes. For these copies he outputs the parity outcome where the clicks have been obtained in times modes k and l. For the rest of the copies, he sets .
- Ver checks if , where is the minimum number of copies that will locally guarantee his acceptance of the note, where is the security factor. Here is the expected number of copies where the honest noteholder obtains exactly two single-photon clicks when Ver runs the SM scheme.
- Ver proceeds to the communication with the bank only when the note passes this test.
Communication with the bank
- 8.
- Ver forwards the outcomes to the bank.
- 9.
- The bank checks if , otherwise he renders the verification attempt as invalid.
- 10.
- For each copy with , the bank compares the parity value with the secret string . He validates the note if the number of correct outcomeswhere is the expected number of copies that give the correct parity outcome when the noteholder is honest, and is a positive constant.
- 11.
- The bank updates the count by 1.
4. Discussion
Funding
Acknowledgments
Conflicts of Interest
Abbreviations
| SM | sampling matching |
| HM | hidden matching |
| SDP | semi-definite programming |
References
- Wiesner, S.S. Wiesner, Sigact News 15, 78 (1983). Sigact News 1983, 15, 78. [Google Scholar] [CrossRef]
- Wootters, W.K.; Zurek, W.H. A single quantum cannot be cloned. Nature 1982, 299, 802–803. [Google Scholar] [CrossRef]
- Bennett, C.H.; Brassard, G. Quantum cryptography: Public key distribution and coin tossing. Theor. Comput. Sci. 2014, 560, 7–11. [Google Scholar] [CrossRef]
- Gottesman, D.; Chuang, I. Quantum digital signatures. arXiv 2001, arXiv:quant-ph/0105032. [Google Scholar]
- Ambainis, A. A new protocol and lower bounds for quantum coin flipping. J. Comput. Syst. Sci. 2004, 68, 398–416. [Google Scholar] [CrossRef]
- Broadbent, A.; Fitzsimons, J.; Kashefi, E. Universal blind quantum computation. In Proceedings of the 2009 50th Annual IEEE Symposium on Foundations of Computer Science, Atlanta, GA, USA, 24–27 October 2009; pp. 517–526. [Google Scholar]
- Crépeau, C.; Gottesman, D.; Smith, A. Secure multi-party quantum computation. In Proceedings of the Thiry-Fourth Annual ACM Symposium on Theory of Computing, Montreal, QC, Canada, 19–21 May 2002; pp. 643–652. [Google Scholar]
- Broadbent, A.; Schaffner, C. Quantum cryptography beyond quantum key distribution. Des. Codes Cryptogr. 2016, 78, 351–382. [Google Scholar] [CrossRef]
- Lutomirski, A. An online attack against Wiesner’s quantum money. arXiv 2010, arXiv:1010.0256. [Google Scholar]
- Brodutch, A.; Nagaj, D.; Sattath, O.; Unruh, D. An adaptive attack on Wiesner’s quantum money. arXiv 2014, arXiv:1404.1507. [Google Scholar]
- Gavinsky, D. Quantum money with classical verification. In Proceedings of the 2012 IEEE 27th Annual Conference on Computational Complexity (CCC), Porto, Portugal, 26–29 June 2012; pp. 42–52. [Google Scholar]
- Georgiou, M.; Kerenidis, I. New constructions for quantum money. In Proceedings of the 10th Conference on the Theory of Quantum Computation, Communication and Cryptography (TQC 2015), Brussels, Belgium, 20–22 May 2015; Volume 44. [Google Scholar]
- Amiri, R.; Arrazola, J.M. Quantum money with nearly optimal error tolerance. Phys. Rev. A 2017, 95, 062334. [Google Scholar] [CrossRef]
- Gavinsky, D.; Kempe, J.; Kerenidis, I.; Raz, R.; De Wolf, R. Exponential separations for one-way quantum communication complexity, with applications to cryptography. In Proceedings of the Thirty-Ninth Annual ACM Symposium on Theory of Computing, San Diego, CA, USA, 11–13 June 2007; pp. 516–525. [Google Scholar]
- Arrazola, J.M.; Karasamanis, M.; Lütkenhaus, N. Practical quantum retrieval games. Phys. Rev. A 2016, 93, 062311. [Google Scholar] [CrossRef]
- Pastawski, F.; Yao, N.Y.; Jiang, L.; Lukin, M.D.; Cirac, J.I. Unforgeable noise-tolerant quantum tokens. Proc. Natl. Acad. Sci. USA 2012, 109, 16079–16082. [Google Scholar] [CrossRef]
- Aaronson, S.; Christiano, P. Quantum money from hidden subspaces. In Proceedings of the Forty-Fourth Annual ACM Symposium on Theory of Computing, New York, NY, USA, 19–22 May 2012; pp. 41–60. [Google Scholar]
- Farhi, E.; Gosset, D.; Hassidim, A.; Lutomirski, A.; Shor, P. Quantum money from knots. In Proceedings of the 3rd Innovations in Theoretical Computer Science Conference, Cambridge, MA, USA, 8–10 January 2012; pp. 276–289. [Google Scholar]
- Moulick, S.R.; Panigrahi, P.K. Quantum cheques. Quantum Inf. Process. 2016, 15, 2475–2486. [Google Scholar] [CrossRef]
- Radian, R.; Sattath, O. Semi-Quantum Money. arXiv 2019, arXiv:1908.08889. [Google Scholar]
- Bozzio, M.; Orieux, A.; Vidarte, L.T.; Zaquine, I.; Kerenidis, I.; Diamanti, E. Experimental investigation of practical unforgeable quantum money. npj Quantum Inf. 2018, 4, 5. [Google Scholar] [CrossRef]
- Guan, J.Y.; Arrazola, J.M.; Amiri, R.; Zhang, W.; Li, H.; You, L.; Wang, Z.; Zhang, Q.; Pan, J.W. Experimental preparation and verification of quantum money. Phys. Rev. A 2018, 97, 032338. [Google Scholar] [CrossRef]
- Kumar, N.; Kerenidis, I.; Diamanti, E. Experimental demonstration of quantum advantage for one-way communication complexity surpassing best-known classical protocol. Nat. Commun. 2019, 10, 1–10. [Google Scholar] [CrossRef]
- Ben-David, S.; Sattath, O. Quantum tokens for digital signatures. arXiv 2016, arXiv:1609.09047. [Google Scholar]
- Goldreich, O. The Foundations of Cryptography, Volume 2, Chapter Encryption Schemes; Cambridge University Press: Cambridge, UK, 2004. [Google Scholar]
- Upfal, E.; Mitzenmacher, M. Probability and Computing: Randomized Algorithms and Probabilistic Analysis; Cambridge University Press: Cambridge, UK, 2005. [Google Scholar]
- Bar-Yossef, Z.; Jayram, T.S.; Kerenidis, I. Exponential separation of quantum and classical one-way communication complexity. In Proceedings of the Thirty-Sixth Annual ACM Symposium on Theory of Computing, Chicago, IL, USA, 13–15 June 2004; pp. 128–137. [Google Scholar]
- Molina, A.; Vidick, T.; Watrous, J. Optimal counterfeiting attacks and generalizations for Wiesner’s quantum money. In Proceedings of the Conference on Quantum Computation, Communication, and Cryptography, Tokyo, Japan, 17–19 May 2012; pp. 45–64. [Google Scholar]
- Croke, S.; Kent, A. Security details for bit commitment by transmitting measurement outcomes. Phys. Rev. A 2012, 86, 052309. [Google Scholar] [CrossRef]
- Jamiołkowski, A. Linear transformations which preserve trace and positive semidefiniteness of operators. Rep. Math. Phys. 1972, 3, 275–278. [Google Scholar] [CrossRef]
- Yao, A.C. Lower bounds by probabilistic arguments. In Proceedings of the 24th Annual Symposium on Foundations of Computer Science (sfcs 1983), Tucson, AZ, USA, 7–9 November 1983; pp. 420–428. [Google Scholar]
- Holevo, A.S. Information-theoretical aspects of quantum measurement. Probl. Peredachi Informatsii 1973, 9, 31–42. [Google Scholar]
- Lvovsky, A.I.; Sanders, B.C.; Tittel, W. Optical quantum memory. Nat. Photonics 2009, 3, 706. [Google Scholar] [CrossRef]
- Julsgaard, B.; Sherson, J.; Cirac, J.I.; Fiurášek, J.; Polzik, E.S. Experimental demonstration of quantum memory for light. Nature 2004, 432, 482. [Google Scholar] [CrossRef] [PubMed]
- Fleischhauer, M.; Lukin, M.D. Quantum memory for photons: Dark-state polaritons. Phys. Rev. A 2002, 65, 022314. [Google Scholar] [CrossRef]
- Kozhekin, A.; Mølmer, K.; Polzik, E. Quantum memory for light. Phys. Rev. A 2000, 62, 033809. [Google Scholar] [CrossRef]
- Arrazola, J.M.; Diamanti, E.; Kerenidis, I. Quantum superiority for verifying NP-complete problems with linear optics. npj Quantum Inf. 2018, 4, 56. [Google Scholar] [CrossRef]
© 2019 by the author. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kumar, N. Practically Feasible Robust Quantum Money with Classical Verification. Cryptography 2019, 3, 26. https://doi.org/10.3390/cryptography3040026
Kumar N. Practically Feasible Robust Quantum Money with Classical Verification. Cryptography. 2019; 3(4):26. https://doi.org/10.3390/cryptography3040026
Chicago/Turabian StyleKumar, Niraj. 2019. "Practically Feasible Robust Quantum Money with Classical Verification" Cryptography 3, no. 4: 26. https://doi.org/10.3390/cryptography3040026
APA StyleKumar, N. (2019). Practically Feasible Robust Quantum Money with Classical Verification. Cryptography, 3(4), 26. https://doi.org/10.3390/cryptography3040026




