Abstract
A Substitution box (S-box) is an important component used in symmetric key cryptosystems to satisfy Shannon’s property on confusion. As the only nonlinear operation, the S-box must be cryptographically strong to thwart any cryptanalysis tools on cryptosystems. Generally, the S-boxes can be constructed using any of the following approaches: the random search approach, heuristic/evolutionary approach or mathematical approach. However, the current S-box construction has some drawbacks, such as low cryptographic properties for the random search approach and the fact that it is hard to develop mathematical functions that can be used to construct a cryptographically strong S-box. In this paper, we explore the non-permutation function that was generated from the binomial operation of the power function to construct a cryptographically strong S-box. By adopting the method called the Redundancy Removal Algorithm, we propose some enhancement in the algorithm such that the desired result can be obtained. The analytical results of our experiment indicate that all criteria such as bijective, nonlinearity, differential uniformity, algebraic degree and linear approximation are found to hold in the obtained S-boxes. Our proposed S-box also surpassed several bijective S-boxes available in the literature in terms of cryptographic properties.
Keywords:
s-box; cryptographically strong s-box; binomial power function; non-permutation function; redundancy removal algorithm MSC:
11T71; 94A60; 68P25
1. Introduction
At a fundamental level, Claude Shannon’s properties of confusion and diffusion [1] often made for bench marking the security of a symmetric encryption. Confusion is defined as the complexity of the relationship between secret-key and cipher-text while diffusion is defined as the degree of influence of single input bit changed in the resulting ciphertext. To realize the confusion and diffusion of a symmetric encryption, several layers of substitution and permutation operation, called Substitution-Permutation Networks (SPNs), are applied. The substitution layer is a nonlinear operation used to improve the overall confusion of the encryption. On the contrary, the permutation layer is a linear operation that increases the measure of diffusion.
In symmetric encryption, the substitution layer is typically referred to as Substitution box (S-box). An S-box plays a crucial role against various cryptanalysis. Therefore, an S-box needs to be cryptographically strong by at least having high nonlinearity, low differential uniformity, a high algebraic degree and complex algebraic expression to resist cryptanalysis, such as differential attack first introduced by Biham and Shamir [2], linear attack described by Matsui [3], higher order differential attacks that were introduced by Lai [4] and Knudsen [5], interpolation attacks introduced by Jakobsen and Knudsen [6] and, lastly, algebraic attack introduced by Courtois and Pieprzyk [7]. As a result, research to improve the cryptographic properties of an S-box and its implementation efficiency can be found in the literature. To date, most published constructions of an S-box are based on the bijective functions of elements of four or eight bits.
1.1. Problem Statement
Over the last 20 years, there has been great progress in the field of nonlinear power functions which serve as an S-box. The most successful and widely used technique is the one adopted by the Advanced Encryption Standard (AES) [8] that makes use of the multiplicative inverse function over a finite field . Often, the cryptographic properties exhibited by AES’s S-box become a benchmark for other researchers to construct their S-boxes. This is because AES S-box is conjectured as having optimal cryptographic properties [9] with respect to resistance against linear, differential and algebraic attacks.
Nonlinearity, which is one of the cryptographic properties of S-box, remains a great challenge for future research. Among the main considerations in constructing a new S-box is the following question: Are there more optimal cryptographic properties than the one achieved by AES’s S-box? In other words, this question exclusively relates to the nonlinearity property achieved by an AES S-box. Although there were many new constructions proposed in the last 20 years, the cryptographic properties achieved by AES S-box remain unbeatable. Therefore, we aim to further explore the construction of an S-box.
Our main interest is the construction of bijective S-boxes when n is even, (i.e., n = 8). Most of our research relates to the non-permutation of binomial power functions over . The design criteria of an S-box are affected by resistance against the main attacks on block ciphers [10], as mentioned earlier. All these attacks contribute to the countermeasures of cryptographically strong S-boxes.
1.2. Contribution
Generally, S-box construction can be categorized into three generic methods which are random search, heuristic method and mathematical function approaches. There also exist S-box constructions that combine all or several of these generic methods to produce their desired result. In this paper, we are more interested in exploring and enhancing the S-box construction from a non-permutation power function as previously proposed by Mamadolimov et al. [11] and subsequently improved by Isa et al. [12]. Their method starts with the binomial operation of power functions over a finite field to select the initial S-box. The main criteria in selecting the initial S-box are that the S-box must exhibit optimal cryptographic properties, except balancedness. Then, using a heuristic algorithm known as the Redundancy Removal Algorithm, the final result with the permutation function is produced.
We improve the method by examining the properties exhibits from binomial power functions in more detail. This includes the main cryptographic properties (i.e., NL, DU and AD) and its redundant elements, since composition of two power functions are prone to produce a non-permutation power function [13]. From there, several other steps such as elements exchange and elements rotation are conducted to produce final S-box with desired cryptographically strong properties. The final S-box that we obtained exhibits better cryptographic properties compared to S-box with the same construction proposed by Mamadolimov et al. [11] and Isa et al. [12].
1.3. Organisation
The rest of the paper is organized as follows. In the second section, we discuss the security requirements for an S-box and the available S-box design methods in the literature. In the third section, we present some preliminaries and our proposed S-box construction. Following this, in the fourth section, we provide a discussion and comparative analysis between our findings and the S-boxes available in the literature. We conclude our paper in last section.
2. Security Requirement and S-Box Design Methods
2.1. S-Box Properties
An S-box plays a crucial role in resisting cryptanalysis. A cryptographically strong S-box is classified based on its exhibited cryptographic properties. Moreover, an S-box must exhibit high nonlinearity, low differential uniformity, a high algebraic degree and complex algebraic expression to resist cryptanalysis, such as linear [3], differential [2], algebraic [7] and interpolation [6] attacks. Therefore, a lot of research is still in place to investigate and strengthen the cryptographic properties of each S-box proposed.
There is also much research conducted in designing and constructing an S-box. Typically, the measurement of cryptographically strong S-box properties depends on assumptions. To avoid more confusion in determining a cryptographically strong S-box, Carlet takes responsibility by facilitating and simplifying the desired properties in designing good S-boxes [14]. In particular, the desired properties suggested by Carlet [14] and later followed by Piret et al. [15], are bench-marked against AES’s S-box. This is because AES’s S-box is already conjectured as having the optimal cryptographic properties [9].
Therefore, based on the suggestions made in [14,15], we set the desired values for each of the S-box properties to be considered cryptographically strong, as summarized in Table 1. The following subsections explain each property in detail.

Table 1.
Desired Value for Cryptographically Strong S-boxes.
Let be a finite field with elements, while is a finite field with elements. An S-box is a Boolean map:
where to are called as component functions of F.
2.1.1. Nonlinearity (NL)
Let be a nonzero element in and be a linear combination of the coordinate Boolean functions of F. The NL of an S-box, F, is the Hamming distance between the set of all affine functions over and the set of all non-constant linear combinations of component functions of F, as defined below:
Claude [14] suggested that the value of NL should be as close as possible to the best-known NL (i.e., ) to thwart linear cryptanalysis [3]. In our study, we set the minimum threshold for NL as 100 (i.e., ).
2.1.2. Differential Uniformity (DU)
By excluding the trivial entry case (i.e., ) from the difference distribution table, the largest value present in the table can determine the value of DU. The value of DU is defined as follows:
A smaller value of DU is preferable [14]. In our case, we determine that the value of DU must lie in the range of to resist differential cryptanalysis [2].
2.1.3. Algebraic Degree (AD)
is denoted from the number of variables in the largest monomial for the component function f of an S-box. Therefore, the AD of an S-box is determined by the maximum degree of all component functions, as follows:
The value of the AD of an S-box must be high [14] in order to resist higher order differential cryptanalysis [5]. In our study, we set .
2.1.4. Linear Approximation (LA)
The LA of an S-box is defined as follows:
where , and , are evaluated over . The operation denotes the inner product of vectors and input X of the S-box. denotes the product of vectors and output of the S-box.
By omitting the trivial case , the LA can be determined through the maximum entry in linear approximation table of the S-box. The lower value of LA is preferable in resistance against linear cryptanalysis [3]. Usually, the value of LA must be less than 28 (i.e., ).
2.1.5. Algebraic Complexity (AlC)
The Lagrange interpolation polynomial is the polynomial of degree that passes through n points and is given by:
where
The number of terms in determines whether an S-box has a simple or complex algebraic expression, thereby classifying whether the S-box has a low or high algebraic complexity. A complex AlC is needed to resist an interpolation attack [6] and other concerning algebraic attacks [7].
2.1.6. Fixed Points (Fp) and Opposite Fixed Points (OFp)
For an S-box, a fixed point is defined as . This mean if an input x is given, the output is also x. An opposite fixed point is defined as , where denotes the bit-wise complement of x. The number of and should be kept as low as possible to avoid any leakage in statistical cryptanalysis.
2.1.7. Balancedness
An n-variable Boolean function f is said to be balanced if , where is the Hamming weight of f for the n-variable. An S-box is called balanced if every value in occurs once. This implies that the function is bijective (also known as the permutation function).
2.2. S-Box Design Methods
In this section, we review several S-box constructions available in literature and classify them into three generic methods which are random generation, evolutionary or heuristic, and a mathematical function. In general, the classification of each S-box proposal is based on its construction. As an example, random methods that use a pseudo-random generator to generate a key and/or select a key randomly from its construction elements are categorized as a random generation approach. Likewise, using mathematical functions as the core of S-box construction will be categorized as a mathematical function approach. The S-box constructions that use neither a random generator nor mathematical function can be categorized as heuristic approaches. In addition, we also classify S-box constructions that use more than one generic method as a Combination Method.
The random generation approach is the simplest technique to construct an S-box; however, its disadvantage is that most of the final S-boxes generated do not achieve our desired value for cryptographically strong S-boxes, as stated in Table 1. Conversely, the mathematical function approach is the best technique with which to achieve the desired S-box properties; however, it is difficult to find this function. For the heuristic approach, the latest S-box construction proposals show an improvement compared to the early proposal in terms of its S-box properties. Therefore, nowadays, researchers focus their attention on exploring heuristic approaches to generate cryptographically strong S-boxes since the implementation of this approach is convenient in both hardware and software.
To facilitate the classification of S-box construction, we divide the S-box design methods into two subsections. The first subsection reviews the S-box constructions which are implemented in the block ciphers proposal, while the second subsection reviews other S-box constructions available in literature.
2.2.1. S-Boxes in Block Ciphers
Mathematical Function
The block ciphers SQUARE [16], BKSQ [17] and Rijndael [18,19] were developed by the same designer in the late 1990s. All S-boxes in these three block ciphers were constructed using similar transformations which take the multiplicative inverse over finite field , as suggested in [20]; then, an affine transformation over is applied to the output bits. Rijndael block cipher was then promoted as the Advanced Encryption Standard (AES) by the National Institute of Standards and Technology (NIST) in 2001 [8]. Following the same construction and transformations are the S-boxes used in block cipher Camellia [21], Mercy [22], ARIA [23], SMS4 [24] and BC2 [25]. The S-box in HyRAL [26] block cipher was also constructed based on multiplicative inverse over using the irreducible polynomial of with two transformations performed beforehand, namely affine transformation (i.e., ) and Gray code transformation (i.e., ). Therefore, HyRAL S-box is classified as a mathematical function approach.
Another block cipher proposed in 2010 is called PP-1 [27]. The S-box construction is classified as a mathematical function approach since they use a multiplicative inverse procedure over finite field, similar to AES but with a randomly chosen primitive polynomial (i.e., ). In the studies of Fuller et al. [28] for removing linear redundancy in S-boxes, they select several random pairs of S-box elements and rearrange four corresponding S-box entries in such a way that the S-box produced is an involution S-box.
Heuristic
CS-Cipher [29] and CRYPTON [30] block cipher use a 3-round Feistel cipher to generate S-box. In general, their S-box is constructed with concatenation of elements generated in and pre-determined parameters to produce S-box. Using the same construction is the S-box used in PICARO [15] block cipher. However, the S-box generated in PICARO is a non-bijective S-box. The ZORRO [31] block cipher proposed an improvement to PICARO’s S-box construction. They instantiate a 4-round Feistel network with a monomial generated in . Then, they add an 8-bit linear transformation at the end of each round and lastly, an affine transformation to remove the fixed point. Unlike PICARO, the final S-box of ZORRO is bijective but the construction classification technique is the same, i.e., a heuristic approach.
S-box used in Skipjack [32] and FOX [33] block ciphers are also classified as a heuristic approach. Although the real S-box construction in Skipjack is unknown, the research of Biryukov and Perrin [34] on the reverse-engineering of S-boxes, concludes that the Skipjack’s S-box construction is not the result of random generation. The method of S-box construction used in the FOX block cipher consists of a three-round Lai–Massey scheme to avoid a purely algebraic construction. The three rounds of the Lai–Massey scheme take three different small S-boxes as the round function F.
Random Generation
CHAIN [35] block ciphers generate their S-box using random generation while ANUBIS [36] block ciphers generate theirs using a pseudo-random number generator with consideration of the involution S-box as a result. An involution S-box is where the S-box has an inverse onto itself. Therefore, the same S-box can be used in encryption and decryption processes. The S-box used in KHAZAD [37] block ciphers is an improvement of ANUBIS’s S-box that uses linear shuffling. The same linear shuffling for S-box construction is also adopted in the ICEBERG [38] block cipher.
KAMKAR [39] block ciphers use a key-dependent S-box. KAMKAR uses two different generators of a quasi-random sequence of numbers to alternately trigger based on the scanned cipher key. Then, the generators are used to generate two random numbers and derive two integers between 0 and 255 to be used for swapping the location from the initial S-box. In KAMKAR, the initial S-box is fixed with a linear power function (i.e., x over ). The iteration continues until all bytes are scanned and swapped.
Combination Method
The Hierocrypt [40] block cipher uses two different S-boxes, namely a high-level S-box and lower-level S-box. For high-level S-box, the construction is based on bit permutation, followed by a power polynomial of over using the irreducible polynomial of . Lastly, an affine transformation over is applied on the output. The construction for a lower-level S-box is not described; therefore, we conclude that they used the heuristic approach for lower-level S-box. Using the same approach, the CLEFIA [41] block cipher employs two different S-boxes constructed using inverse function over and using four 4-bit random S-boxes for the second construction. Therefore, Hierocrypt’s and CLEFIA’s S-box construction are combination methods because they use the mathematical function approach for the first S-box and heuristic approach for the second S-box.
The KALYNA [42] block cipher adopted the S-box construction proposed by Kazymyrov et al. [43], which was constructed based on gradient descent. This S-box construction is basically an enhancement of the improved hill climbing method proposed by Gao et al. [44] in 2010. Generally, they generate an initial solution, S, which is a bijective S-box with a minimum value of DU based on function F. The function F is basically determined as an inverse function over finite field . Then, they randomly swap a number of values in S to generate as the final S-box. Therefore, we classify this construction as a combination method since they combine the mathematical function approach with the random generation approach.
2.2.2. Other S-Boxes Proposal
Aside from the S-boxes used in block ciphers, there exist a large number of S-box construction proposals in the literature. We have reviewed, analyzed and categorized all the S-box proposals that we have collected into random generation, heuristic, mathematical function and combination methods.
Random Generation
There are several S-box constructions that generate dynamic S-boxes which depend on a key. Among others are the proposal in [45,46,47,48]. In particular, their construction begins with an initial S-box, then a string of keys is generated to permute the content of the initial S-box. Thus, a new S-box is constructed. Various methods are used to generate the keys such as random generation, a pseudo-random number generator (PRNG) or a round key obtained from the RC4 algorithm [49].
Mamadolimov et al. [50] also proposed an S-box construction based on random generation. The initial S-box is represented as eight component functions. The first three component functions are deterministically constructed, such that the highest nonlinearity for each Boolean function is found. Then, the other five component functions are generated randomly to complete the S-box.
However, the S-box construction using random generation has received less attention among researchers. This might be because of the unfavorable cryptographic properties exhibited by this approach.
Heuristic
The heuristic approach has received more attention from researchers, especially on chaos-based S-box construction. This might be because chaos is a stochastic process in nonlinear dynamic systems, thus satisfying the need for nonlinearity in block ciphers. Among the popular chaotic maps used are the Chebyshev map [51,52], Baker map [53,54], Lorenz systems [55,56], logistic map [57,58], neural network [59,60], piecewise linear chaotic map [61,62], tent map [63,64] and Van Der Pol oscillator [65]. In general, chaos-based S-box construction starts with the selection of an initial value in selected chaotic map. Then, they iterate the chaotic map and use their defined technique to obtain an integer that lies between 0 and 255. This procedure is repeated to generate another integer until all 256 elements of the S-box are fulfilled.
Furthermore, there are several S-box proposals that we categorized as heuristic approaches, such as the S-box construction using hill climbing [43,66], Latin square [67], analytical approach [68], genetic algorithm [69,70], simulated annealing [71,72], cellular automata [73,74], ant colony optimization [75], artificial immune system [76] and bee waggle dance [77]. Nature-inspired systems, such as genetic algorithms, work in reverse, i.e., [70], gradient descent [43] (i.e., modified hill climbing), artificial immune system [76] and bee waggle dance [77] show encouraging developments in S-box construction using the heuristic approach.
Mathematical Function
The main criterion for categorizing S-box proposals as mathematical functions is that designers use the same transformation as AES [8]. This includes either revising the transformation [78,79,80] itself by using different irreducible polynomials or by adding another affine transformations [81,82,83,84] in their construction.
Moreover, some S-box proposals using mathematical functions other than AES were found in the literature, such as linear fractional transformation or projective general linear group [85,86,87], trace-representation polynomial function [88], gray code encode [89], semi-fields pseudo-extensions [90] and using finite field power functions [91]. All these S-box constructions provide encouraging results and can be categorized among cryptographically strong S-boxes.
Combination Method
Fuller et al. proposed 2-step tweaking [28] and 4-step tweaking [92] in order to avoid linear redundancy and preserve the involution properties of an S-box, respectively. We categorized their proposed techniques as a combination method since they used methods such as divide and swap in the tweaking of the initial S-box that was generated based on a multiplicative inverse function over . Mamadolimov et al. [11] and Isa et al. [12,93] also proposed an S-box construction using a combination method. In this proposal, they constructed an initial S-box based on the non-permutation power function followed by a heuristic approach, which is an algorithm to make the S-box bijective as a final result.
3. S-Box Construction
3.1. Preliminaries
Table 2 is an example of a non-permutation power function generated over finite field in . In this case, we use . We can extract the following information: (1) , (2) and (3) from Table 2.

Table 2.
over .
is a notation for Desired Element. A desired element only occurs once in a permutation function, such that a bijective S-box is achieved. From Table 2, only one element is found in the category, which is the element 0.
is a notation for Repeated Elements. The repeated elements were obtained from generated functions that occur more than once. From the analysis of Table 2, there are five elements that fall into this category, which are the elements 1, 8, A, C and F. All five repeated elements are found to be repeated three times.
denotes the Non-existent Elements which means that the elements are ’missing’ from the generated function. This happens because the element that should exist has been replaced by a repeated element. From Table 2, we can determine that there are a total of 10 elements that do not exist in over , which are 2, 3, 4, 5, 6, 7, 9, B, D and E.
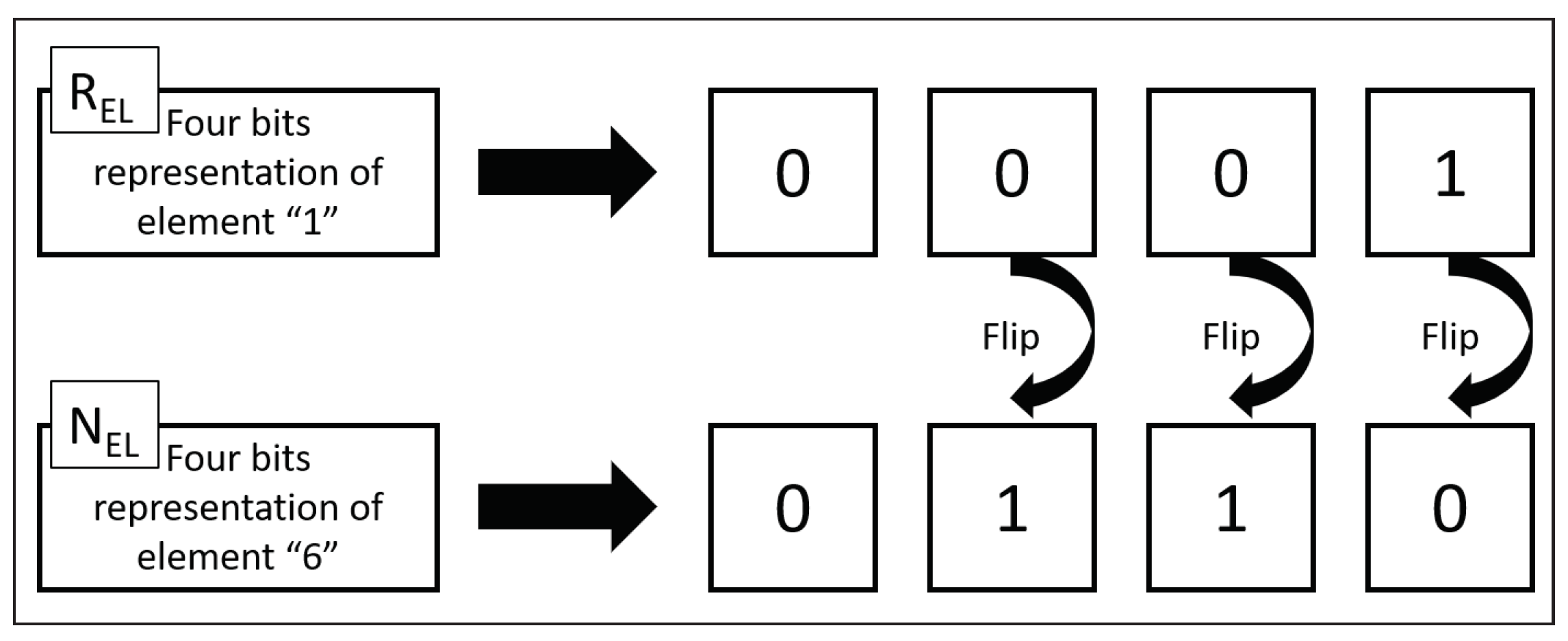
After these three group of elements are obtained, a Redundancy Analysis Table will be constructed. The Redundancy Analysis Table is a representation of bits error between all elements in compared to the elements in . Table 3 shows the redundancy analysis table of over the finite field . For example, there are 3 bits that needs to be changed to replace element 1 from with element 6 from , as illustrated in Figure 1. Likewise, the element F from has three options which only involve one bit change. The elements listed from are 7, B and E.

Table 3.
Redundancy Analysis Table for over .
Figure 1.
Bits Error Representation.
3.2. Our Proposed Construction
Let denote a power function in using the irreducible polynomial , where and . All power functions (i.e., ) can be classified into linearly non-equivalent functions using the squaring method [94], as shown in Table 4. The first column of Table 4 represents the powers d that are non-equivalent to each other. The second column lists all the equivalent power functions for each power d. For instance, the power function is equivalent to , as is the case with . Four more columns in Table 4 denote the values of NL, DU, AD and LA produced by the underlying power function. The column lists the number of non-existent elements, while the column lists the number of repeated elements in each of the involved power functions. The last column denotes whether the power function is a permutation or otherwise, based on the number given in columns and (i.e., label ‘Y’ is given when = = 0, otherwise label ‘N’ will be given).

Table 4.
Classification of linearly non-equivalent power function, based on maximum NL in .
Our construction starts with the generation of binomial power functions. and which are two different power functions selected over finite field is added to produce a new function (i.e., ). In total, there are possible combination of binomial power functions produced from this operation and none of them are permutation function. We analyzed its repeated elements () and non-existent elements (), then summarized the findings in Table 5.

Table 5.
Redundancy Analysis of Binomial Power Functions.
Table 5 lists the number of binomial power functions according to (, ) pairs. As an example, there are a total of 1024 binomial power functions that produce 15 non-existent elements over only one repeated element. In addition, there are a total of 576 generated binomial power functions that produce the same number of and , which are equal to 128. Other than that, we can categorize the generated binomial power functions into 130 groups based on (, ) pairs.
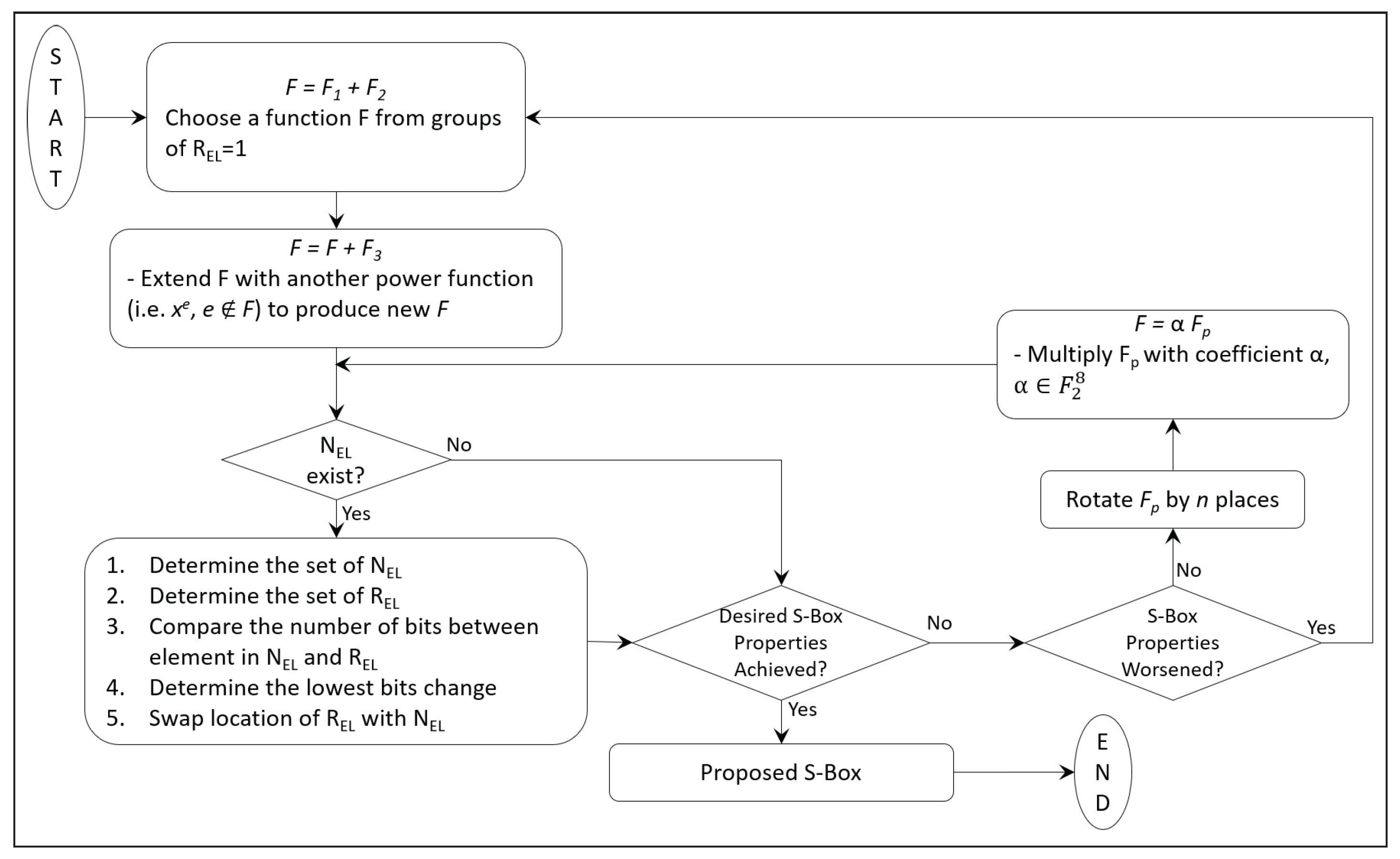
Overall, our proposed algorithm in constructing cryptographically strong S-boxes is illustrated in Figure 2, which is inspired by the S-box construction of Isa et al. [12]. Our initial S-box is selected from the groups of binomial power functions that produce only one (1) repeated element. This includes (, ) pairs of (15, 1), (17, 1), (51, 1) and (85, 1) from Table 5.
Figure 2.
S-box Optimization Algorithm.
In total, there are 1540 candidates that can be used for our initial S-box. However, this number of candidates can be minimized to 200 using the squaring method [94] because of its linearly non-equivalent properties, as shown in Table 6. The complete list of linearly non-equivalent binomial power functions that produces one repeated element from these four groups is included in Appendix A. In this study, we select and limit the selection of the initial S-box to only one repeated element to preserve the cryptographic properties of the newly generated function such that it is not compromised significantly.

Table 6.
Linearly Non-Equivalent Functions for = 1.
The construction continues with the addition of an S-box candidate with another power function (i.e., ), where the selection of a new power function must not include the previously selected power function. After a new function is generated, we extract the information of , and on the function, as described in Section 3.1. If contains no element, that means the function is already bijective. Then, we measure its cryptographic properties and store it as the proposed S-box if it exhibits the desired strong properties.
Otherwise, if contains any element, we construct a redundancy analysis table by determining all the elements in and groups of . Then, the bit errors rate between all elements in and all elements in are produced to complete the redundancy analysis table. The bit error rate is the number of bit errors per unit time. In this study, the bit errors range from a minimum of one (1) bit, up to the maximum of eight (8) bits since we construct an S-box.
From the redundancy analysis table, we identify one current ’smallest’ bit error. If there are several choices obtained from the table, the selection will be made randomly. Then, we determine the actual element of and that correspond with the selected smallest bit error. Next, the exact location of the selected is identified in function and lastly we swap the element with the previously selected (i.e., ). Similarly, the selection will be made randomly if more than one option of the identified is located. By selecting the smallest bit errors, we expect that the cryptographic properties of the newly generated function will not be compromised significantly.
After the swapping process, we measure the cryptographic properties of this newly generated function. We store it as the proposed S-box if it exhibits the desired strong properties. Otherwise, the function will be denoted as and rotated by n places. This rotation step that we proposed is operated based on circular rotation either column-wise (i.e., rotation of component function) or row-wise (i.e., rotation of elements in the function). The purpose of this step is to increase the algebraic expression (i.e., no. of terms (#term)) of the function while preserving its cryptographic properties. Current construction, which exhibits the algebraic expression with simple terms, might expose ciphers using the S-box to an interpolation attack [6]. From our observation, column-wise rotation does not impact the cryptographic properties of the function. However, different to row-wise rotation, the cryptographic properties might change significantly. Our analysis found that, for row-wise rotations of 64, 128 and 192 places, the cryptographic properties of the S-box can preserved.
Then, another round of iteration will be conducted in our algorithm. The next iteration contains a multiplication step of with a coefficient where ranges from 0 to 255; it then continues again with a redundancy analysis table. The stopping criteria that we fix in our iterations are based on the final S-box produced that meets our requirement or based on the cryptographic properties of that are found to worsen (i.e., the cryptographic properties exhibited are lower than the values stated in Table 1). In both cases, another set of will be selected for our next experiments.
Table 7 shows the optimal S-box obtained from the proposed method and is represented as hexadecimal. The first column in Table 7 denotes the first four bits, while the first row denotes the remaining four bits of the 8-bit input to the S-box. For instance, the input 71 gives the output CE, (i.e., F(71) = CE. For input 71, element 7 is selected from the first column while element 1 is selected from the first row). The cryptographic properties exhibited by this S-box meet all the desired values stated in Table 1.

Table 7.
Optimal S-box using Proposed Technique.
4. Discussion
Table 8 compares our obtained S-box with the existing cryptographically strong S-boxes available in literature, as discussed in the previous section. Only S-boxes that satisfy our prerequisite requirements are selected for comparison. The S-boxes were then arranged based on the optimal cryptographic properties exhibits by each S-box, starting with the highest NL, lowest DU, highest AD and, lastly, lowest LA. From there, we rank the S-boxes based on these four properties. Also included in Table 8 are the number of terms exhibited by an S-box and lastly the generic design method of each proposal.

Table 8.
S-Boxes Ranks.
In total, there are 39 S-boxes listed in Table 8 where we classify 16 ranks. The first rank is occupied by the AES S-box which was constructed using multiplicative inversion in . There are 13 others S-box construction that are similar to AES’s S-box construction; thus, they exhibit the same cryptographic properties as AES, which consists of (112, 4, 7, 16) for its (NL, DU, AD, LA), respectively. So far, this multiplicative inverse technique over finite field leads to the best-known cryptographic properties for an S-box.
Ranked second is the S-box construction proposed by Li et al. [91]. Their S-box construction exhibits cryptographic properties of (112, 4, 5, 16) for (NL, DU, AD, LA), respectively. Their S-box proposal is constructed in using Quadratic APN functions which are heuristically converted into an S-box as the final result.
There are also some authors that proposed several S-boxes such as Yang et al. [80], Kazymyrov et al. [43], Ivanov et al. [70] and Isa et al. in [12,77,93]. The S-box constructions proposed by Yang et al. [80] are ranked third, fourth and fifth and classified as mathematical functions-generated methods, as multiplicative inverse, addition and multiplication are only used in the algorithm. Ranked third and fifth are the S-boxes proposed by Ivanov et al. [70] that use the reversed genetic algorithm on the initial S-box that was generated beforehand using multiplicative inverse. Thus, we classify this algorithm as a combination method that lies between the mathematical function approach and heuristic approach. The third ranked S-box has the same nonlinearity as AES (i.e., NL = 112); however, the value for differential uniformity is slightly higher which is DU = 6. By the same S-box construction, Ivanov et al. [70] also produced S-boxes that are ranked seventh, ninth and tenth in Table 8.
We classify the S-box construction of Kazymyrov et al. [43] as random generation. This is because the S-box is constructed by randomly swapping two elements in an initial function. This step is repeated until their desired criteria are achieved. Their best proposed S-box is ranked eleventh with cryptographic properties of (104, 8, 7, 24), while the other one is ranked thirteenth.
Our proposed S-box construction is ranked sixth. The final S-box that we obtained exhibits cryptographic properties of (108, 4, 7, 20). The S-box also produces a complex algebraic expression of 255 terms. The best S-box by Isa et al. [93] shares the same rank of sixth, while the other two proposed S-boxes are ranked eighth and ninth with cryptographic properties of (108, 6, 4, 20) and (106, 6, 7, 22) for (NL, DU, AD, LA), respectively. However, their S-box, which can be constructed using simple algebraic expression (i.e., only three terms involved), might be vulnerable to an interpolation attack [6].
There are other S-boxes proposed by Isa et al. in [12,77] using the combination method. Ranked seventh, Isa et al. [77] used an algorithm called Bee Waggle Dance on the multiplicative inverse function. This construction produced an S-box with cryptographic properties of (108, 6, 7, 20). Ranked tenth is the construction of Isa et al. [12], who used an algorithm called the Redundancy Removal Algorithm on the non-permutation power function that exhibits cryptographic properties of (104, 6, 7, 24). Mamadolimov et al. [11] first introduced the original version of the Redundancy Removal Algorithm, which is ranked twelfth and has cryptographic properties of (102, 8, 7, 26). Empirically, our proposed construction, which is an inspired and enhanced version of the Redundancy Removal Algorithm, managed to obtain cryptographically strong S-boxes that compare well with and even outperform the originally proposed constructions [11,12].
From our observation, all the S-boxes listed in Table 8 are designed and constructed either through mathematical functions or through combination methods between mathematical functions and heuristic methods. So far, the best S-box that we found using random generation is the S-box proposed by Kazymyrov et al. [43], which is ranked eleventh. Nevertheless, this S-box exhibits DU = 8; thus, it fails to fulfill our cryptographically strong criteria. In fact, the S-boxes ranked from eleventh to sixteenth all fail to fulfill our prerequisite requirement for cryptographically strong S-boxes. The S-boxes are included in Table 8 for a comparative analysis.
The research results that are included in the comparative analysis are obtained by applying the security measurement using a mini-workstation with properties of Intel (R) Core (TM) i7-6600U CPU @ 2.60 GHz, 16 GB of RAM, 64-bit Operating System and pre-installed with MATLAB R2022a. All simulations were performed in MATLAB programming language, and no external embedded devices were involved. Since MATLAB is a high-level programming language, we did not conduct a computational complexity analysis of our S-box construction.
5. Conclusions
In this paper, we analyzed the cryptographic properties of binomial power functions. Through our observation of the redundancy table, we discover that all binomial power functions generated over a finite field are not bijective. We modify and enhance the method called the Redundancy Removal Algorithm to obtain cryptographically strong S-boxes. Our proposed S-box exhibits cryptographic properties of (108, 4, 7, 20) for (NL, DU, AD, LA), respectively; thus all our prerequisite requirements are fulfilled and the performance of the original algorithm proposed by Mamadolimov et al. and Isa et al. is surpassed.
From our comparative analysis, the mathematical function remains the best method to construct a cryptographically strong S-box. The production of a new mathematical function that can challenge multiplicative inversion is an interest of many researchers. However, recent research developments on combination methods of mathematical functions and the heuristic approach show an encouraging trend in the construction of a cryptographically strong S-box. As for random generation, this method is unfavorable since there are no recent developments driven by this approach.
In future work, our proposed S-box can be applied to a working encryption algorithm to analyze its efficiency and accuracy. To achieve this, we have to convert our script into a low-level programming language and implement it in an embedded device. We are also interested in categorizing our S-box collections based on equivalence classes. To the best of our knowledge, there are three types of equivalence classes in literature which are linear and affine equivalence, extended affine (EA-) equivalent and Carlet–Charpin–Zinoviev (CCZ-) equivalent.
Author Contributions
Conceptualization, S.A.A.S.J. and N.A.; methodology, H.I., S.M.A. and M.R.Z.; software, R.E. and N.A.; validation, H.I.; formal analysis, H.I.; investigation, H.I.; resources, H.I., S.A.A.S.J., R.E. and N.A.; data curation, H.I.; writing—original draft preparation, H.I.; writing—review and editing, M.R.Z., S.A.A.S.J., R.E., S.M.A. and N.A.; supervision, M.R.Z. and S.A.A.S.J. All authors have read and agreed to the published version of the manuscript.
Funding
The authors would like to acknowledge support from the Long Term Research Grant Scheme (LRGS) under grant number LRGS/1/2020/UM/01/5/4 (9012-00010) from the Ministry of Higher Education, Malaysia. R and N would also like to acknowledge support from Geran Penyelidikan Pengkomersialan MTUN 2020 9028-00023 provided by the Ministry of Higher Education of Malaysia (MOHE).
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
Abbreviations
The following abbreviations are used in this manuscript:
| SPNs | Substitution-Permutation Networks |
| S-box | Substitution box |
| NL | Nonlinearity |
| DU | Differential Uniformity |
| AD | Algebraic Degree |
| AES | Advanced Encryption Standard |
| LA | Linear Approximation |
| MDPI | Multidisciplinary Digital Publishing Institute |
| Desired Element | |
| Repeated Elements | |
| Non-Existent Elements |
Appendix A
Appendix A.1

Table A1.
Classification of Linearly Non-Equivalent Binomial Power Function with 15 to 1 Output.
Table A1.
Classification of Linearly Non-Equivalent Binomial Power Function with 15 to 1 Output.
| A | Linearly Equivalent Binomial Power Function to A |
|---|---|
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , | |
| , , |
Appendix A.2

Table A2.
Classification of Linearly Non-Equivalent Binomial Power Function with 17 to 1 Output.
Table A2.
Classification of Linearly Non-Equivalent Binomial Power Function with 17 to 1 Output.
| B | Linearly Equivalent Binomial Power Function to B |
|---|---|
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , |
Appendix A.3

Table A3.
Classification of Linearly Non-Equivalent Binomial Power Function with 85 to 1 Output.
Table A3.
Classification of Linearly Non-Equivalent Binomial Power Function with 85 to 1 Output.
| D | Linearly Equivalent Binomial Power Function to D |
|---|---|
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , |
Appendix A.4

Table A4.
Classification of Linearly Non-Equivalent Binomial Power Function with 51 to 1 Output.
Table A4.
Classification of Linearly Non-Equivalent Binomial Power Function with 51 to 1 Output.
| C | Linearly Equivalent Binomial Power Function to C |
|---|---|
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , | |
| , , , , , , |
References
- Shannon, C.E. Communication Theory of Secrecy Systems. Bell Syst. Tech. J. 1949, 28, 656–715. [Google Scholar] [CrossRef]
- Biham, E.; Shamir, A. Differential Cryptanalysis of DES-like Cryptosystems. In Advances in Cryptology—CRYPT0 ’90; Lecture Notes in Computer Science; Menezes, A.J., Vanstone, S.A., Eds.; Springer: Berlin/Heidelberg, Germany, 1991; Volume 537, pp. 2–21. [Google Scholar]
- Matsui, M. Linear Cryptanalysis Method for DES Cipher. In EUROCRYPT ’93; Lecture Notes in Computer Science; Helleseth, T., Ed.; Springer: Berlin/Heidelberg, Germany, 1994; Volume 765, pp. 386–397. [Google Scholar]
- Lai, X. Higher Order Derivatives and Differential Cryptanalysis. In Communications and Cryptography; The Springer International Series in Engineering and Computer Science; Blahut, R.E., Costello, D.J.J., Maurer, U., Mittelholzer, T., Eds.; Springer: New York, NY, USA, 1994; Volume 276, pp. 227–233. [Google Scholar]
- Knudsen, L.R. Truncated and Higher Order Differentials. In Fast Software Encryption; Lecture Notes in Computer Science; Preneel, B., Ed.; Springer: Berlin/Heidelberg, Germany, 1995; Volume 1008, pp. 196–211. [Google Scholar]
- Jakobsen, T.; Knudsen, L.R. The Interpolation Attack on Block Ciphers. In Fast Software Encryption; Lecture Notes in Computer Science; Biham, E., Ed.; Springer: Berlin/Heidelberg, Germany, 1997; Volume 1267, pp. 28–40. [Google Scholar]
- Courtois, N.T.; Pieprzyk, J. Cryptanalysis of Block Ciphers with Overdefined Systems of Equations. In ASIACRYPT 2002; Lecture Notes in Computer Science; Zheng, Y., Ed.; Springer: Berlin/Heidelberg, Germany, 2002; Volume 2501, pp. 267–287. [Google Scholar] [CrossRef]
- Federal Information Processing Standard (FIPS) 197; Advanced Encryption Standard. National Institute of Standards and Technology: Gaithersburg, MD, USA, 2001. [CrossRef]
- Dobbertin, H.; Daum, M.; Felke, P.; Lange, T.; Leander, G. S-Boxes and Filters. STORK Project, IST-2002-38273. 2002. Available online: http://www.stork.eu.org/papers/ (accessed on 20 July 2022).
- Carlet, C. Vectorial Boolean Functions for Cryptography; Cambridge University Press: Cambridge, UK, 2010; Chapter Boolean Models and Methods in Mathematics, Computer Science, and Engineering; pp. 398–470. [Google Scholar]
- Mamadolimov, A.; Isa, H.; Mohamad, M.S. Practical Bijective S-box Design. arXiv 2013, arXiv:1301.4723. [Google Scholar]
- Isa, H.; Jamil, N.; Z’aba, M.R. S-box Construction from Non-Permutation Power Functions. In Proceedings of the 6th International Conference on Security of Information and Networks, Aksaray, Turkey, 26–28 November 2013; ACM: New York, NY, USA, 2013; pp. 46–53. [Google Scholar]
- Roslan, M.F.; Seman, K.; Halim, A.; Sayuti, M. Current implementation of advance encryption standard (AES) S-Box. J. Fundam. Appl. Sci. 2017, 9, 518–542. [Google Scholar] [CrossRef]
- Carlet, C. On Known and New Differentially Uniform Functions. In Information Security and Privacy; Lecture Notes in Computer Science; Parampalli, U., Hawkes, P., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; Volume 6812, pp. 1–15. [Google Scholar]
- Piret, G.; Roche, T.; Carlet, C. PICARO—A Block Cipher Allowing Efficient Higher-Order Side-Channel Resistance. In Applied Cryptography and Network Security; Lecture Notes in Computer Science; Bao, F., Samarati, P., Zhou, J., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7341, pp. 311–328. [Google Scholar]
- Daemen, J.; Knudsen, L.; Rijmen, V. The Block Cipher SQUARE. In Fast Software Encryption; Lecture Notes in Computer Science; Biham, E., Ed.; Springer: Berlin/Heidelberg, Germany, 1997; Volume 1267, pp. 149–165. [Google Scholar]
- Daemen, J.; Rijmen, V. The Block Cipher BKSQ. In Smart Card Research and Applications; Lecture Notes in Computer Science; Quisquater, J.J., Schneier, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2000; Volume 1820, pp. 236–245. [Google Scholar]
- Daemen, J.; Rijmen, V. AES Proposal: Rijndael. NIST AES Proposal. 1999. Available online: https://csrc.nist.gov/projects/cryptographic-standards-and-guidelines/archived-crypto-projects/aes-development (accessed on 20 July 2022).
- Daemen, J.; Rijmen, V. The Block Cipher Rijndael. In Smart Card Research and Applications; Lecture Notes in Computer Science; Quisquater, J.J., Schneier, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2000; Volume 1820, pp. 277–284. [Google Scholar]
- Nyberg, K. Differentially Uniform Mappings for Cryptography. In Advances in Cryptology—EUROCRYPT ’93; Lecture Notes in Computer Science; Helleseth, T., Ed.; Springer: Berlin/Heidelberg, Germany, 1994; Volume 765, pp. 55–64. [Google Scholar]
- Aoki, K.; Ichikawa, T.; Kanda, M.; Matsui, M.; Moriai, S.; Nakajima, J.; Tokita, T. Camellia: A 128-Bit Block Cipher Suitable for Multiple Platforms—Design and Analysis. In Selected Areas in Cryptography; Lecture Notes in Computer Science; Stinson, D.R., Tavares, S., Eds.; Springer: Berlin/Heidelberg, Germany, 2001; Volume 2012, pp. 39–56. [Google Scholar]
- Crowley, P. Mercy: A Fast Large Block Cipher for Disk Sector Encryption. In Fast Software Encryption; Lecture Notes in Computer Science; Goos, G., Hartmanis, J., van Leeuwen, J., Schneier, B., Eds.; Springer: Berlin/Heidelberg, Germany, 2001; Volume 1978, pp. 49–63. [Google Scholar]
- Kwon, D.; Kim, J.; Park, S.; Sung, S.; Sohn, Y.; Song, J.; Yeom, Y.; Yoon, E.J.; Lee, S.; Lee, J.; et al. New Block Cipher: ARIA. In Information Security and Cryptology—ICISC 2003; Lecture Notes in Computer Science; Lim, J.I., Lee, D.H., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 2971, pp. 432–445. [Google Scholar]
- Diffie, W.; Ledin, G. SMS4 Encryption Algorithm for Wireless Networks. Cryptology ePrint Archive, Report 2008/329. 2008. Available online: http://eprint.iacr.org/ (accessed on 25 July 2022).
- Kurniawan, Y.; Mardiyanto, M.S.; Supriana, I.; Sutikno, S. The New Block Cipher: BC2. Int. J. Netw. Secur. 2009, 8, 16–24. [Google Scholar]
- Hirata, K. The 128-bit Block Cipher HyRAL (Hybrid Randomization Algorithm): Common Key Block Cipher. In Proceedings of the International Symposium on Intelligence Information Processing and Trusted Computing (IPTC), Wuhan, China, 28–29 October 2010; pp. 9–14. [Google Scholar]
- Bucholc, K.; Chmiel, K.; Grocholewska-Czuryło, A.; Idzikowska, E.; Janicka-Lipska, I.; Stokłosa, J. Scalable PP-1 Block Cipher. Int. J. Appl. Math. Comput. Sci. 2010, 20, 401–411. [Google Scholar] [CrossRef]
- Fuller, J.; Millan, W. Linear Redundancy in S-boxes. In Fast Software Encryption; Lecture Notes in Computer Science; Johansson, T., Ed.; Springer: Berlin/Heidelberg, Germany, 2003; Volume 2887, pp. 74–86. [Google Scholar]
- Stern, J.; Vaudenay, S. CS-Cipher. In Fast Software Encryption; Lecture Notes in Computer Science; Vaudenay, S., Ed.; Springer: Berlin/Heidelberg, Germany, 1998; Volume 1372, pp. 189–204. [Google Scholar]
- Lim, C.H. A Revised Version of CRYPTON: CRYPTON V1.0. In Fast Software Encryption; Lecture Notes in Computer Science; Knudsen, L., Ed.; Springer: Berlin/Heidelberg, Germany, 1999; Volume 1636, pp. 31–45. [Google Scholar]
- Gérard, B.; Grosso, V.; Naya-Plasencia, M.; Standaert, F.X. Block Ciphers That Are Easier to Mask: How Far Can We Go? In Cryptographic Hardware and Embedded Systems—CHES 2013; Lecture Notes in Computer Science; Bertoni, G., Coron, J.S., Eds.; Springer: Berlin/Heidelberg, Germany, 2013; Volume 8086, pp. 383–399. [Google Scholar]
- NIST. Skipjack and KEA Algorithm Specifications. 1998. Available online: https://csrc.nist.gov/Presentations/1998/Skipjack-and-KEA-Algorithm-Specifications/ (accessed on 20 July 2022).
- Junod, P.; Vaudenay, S. FOX: A New Family of Block Ciphers. In Selected Areas in Cryptography; Lecture Notes in Computer Science; Handschuh, H., Hasan, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2005; Volume 3357, pp. 114–129. [Google Scholar]
- Biryukov, A.; Perrin, L. On Reverse-Engineering S-Boxes with Hidden Design Criteria or Structure. In Advances in Cryptology – CRYPTO 2015; Lecture Notes in Computer Science; Gennaro, R., Robshaw, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2015; Volume 9215, pp. 116–140. [Google Scholar]
- Peyravian, M.; Coppersmith, D. A Structured Symmetric-key Block Cipher. Comput. Secur. 1999, 18, 134–147. [Google Scholar] [CrossRef]
- Barreto, P.S.L.M.; Rijmen, V. The ANUBIS Block Cipher. 2000. Available online: https://www.cosic.esat.kuleuven.be/nessie/workshop/ (accessed on 20 July 2022).
- Barreto, P.S.L.M.; Rijmen, V. The KHAZAD Legacy-Level Block Cipher. 2000. Available online: https://www.cosic.esat.kuleuven.be/nessie/workshop/ (accessed on 20 July 2022).
- Standaertt, F.X.; Piret, G.; Rouvroy, G.; Quisquater, J.J.; Legat, J.D. ICEBERG: An Involutional Cipher Efficient for Block Encryption in Reconfigurable Hardware. In Fast Software Encryption; Lecture Notes in Computer Science; Roy, B., Meier, W., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; Volume 3017, pp. 279–298. [Google Scholar]
- Elkamchouchi, H.M.; Makar, M.A. Kamkar Symmetric Block Cipher. In Proceedings of the Twenty-First National Radio Science Conference (NRSC), Cairo, Egypt, 18 March 2004; pp. C1–C18. [Google Scholar]
- Ohkuma, K.; Muratani, H.; Sano, F.; Kawamura, S. The Block Cipher Hierocrypt. In Selected Areas in Cryptography; Lecture Notes in Computer Science; Stinson, D., Tavares, S., Eds.; Springer: Berlin/Heidelberg, Germany, 2001; Volume 2012, pp. 72–88. [Google Scholar]
- Shirai, T.; Shibutani, K.; Akishita, T.; Moriai, S.; Iwata, T. The 128-Bit Blockcipher CLEFIA (Extended Abstract). In Fast Software Encryption: 14th International Workshop, FSE 2007, Luxembourg, Luxembourg, 26–28 March 2007; Revised Selected Papers; Springer: Berlin/Heidelberg, Germany, 2007; pp. 181–195. [Google Scholar]
- Oliynykov, R.; Gorbenko, I.; Kazymyrov, O.; Ruzhentsev, V.; Kuznetsov, O.; Gorbenko, Y.; Dyrda, O.; Dolgov, V.; Pushkaryov, A.; Mordvinov, R.; et al. A New Encryption Standard of Ukraine: The Kalyna Block Cipher; Cryptology ePrint Archive, Report 2015/650. 2015. Available online: https://eprint.iacr.org/2015/650 (accessed on 30 July 2022).
- Kazymyrov, O.; Kazymyrova, V.; Oliynykov, R. A Method for Generation of High-Nonlinear S-Boxes Based on Gradient Descent; Cryptology ePrint Archive, Report 2013/578. 2013. Available online: https://eprint.iacr.org/2013/578 (accessed on 30 July 2022).
- Gao, S.; Ma, W.; Feng, J.; Guo, N.; Yan, Y. Improved Hill-Climbing Methods in the Design of Bijective S-boxes. In Proceedings of the Sixth International Conference on Natural Computation (ICNC), Yantai, China, 10–12 August 2010; Volume 5, pp. 2378–2380. [Google Scholar]
- El-Ramly, S.H.; El-Garf, T.; Soliman, A.H. Dynamic Generation of S-boxes in Block Cipher Systems. In Proceedings of the Eighteenth National Radio Science Conference, Mansoura, Egypt, 27–29 March 2001; Volume 2, pp. 389–397. [Google Scholar]
- Kazlaukas, K.; Vaicekauskas, G.; Smaliukas, R. An Algorithm for Key-Dependent S-Box Generation in Block Cipher System. Informatica 2015, 26, 51–65. [Google Scholar] [CrossRef]
- Balajee, M.K.; Gnanasekar, J.M. Evaluation of Key Dependent S-Box based Data Security Algorithm using Hamming Distance and Balanced Output. TEM J. 2016, 5, 67–75. [Google Scholar]
- El-Latif, A.A.A.; Ramadoss, J.; Abd-El-Atty, B.; Khalifa, H.S.; Nazarimehr, F. A Novel Chaos-Based Cryptography Algorithm and Its Performance Analysis. Mathematics 2022, 10, 2434. [Google Scholar] [CrossRef]
- Gong, G.; Gupta, K.C.; Hell, M.; Nawaz, Y. Towards a General RC4-Like Keystream Generator. In Lecture Notes in Computer Science, Proceedings of Information Security and Cryptology: First SKLOIS Conference, CISC 2005, Beijing, China, 15–17 December 2005; Feng, D., Lin, D., Yung, M., Eds.; Springer: Berlin/ Heidelberg, Germany, 2005; Volume 3822, pp. 162–174. [Google Scholar]
- Mamadolimov, A.; Isa, H.; Ahmad, M.M.; Mohamad, M.S. Nonlinear Boolean Permutations. Pertanika J. Sci. Technol. 2011, 19, 1–9. [Google Scholar]
- Zhoua, Q.; Wong, K.; Liao, X.; Xiang, T.; Hu, Y. Parallel Image Encryption Algorithm based on Discretized Chaotic Map. Chaos 2008, 38, 1081–1092. [Google Scholar] [CrossRef]
- Xu, G.; Zhao, G.; Min, L. The Design of Dynamical S-boxes based on Discrete Chaos Map System. In Proceedings of the IEEE International Conference on Intelligent Computing and Intelligent Systems, Shanghai, China, 20–22 November 2009; Volume 2, pp. 473–478. [Google Scholar]
- Hung, P.A.; Klomkarn, K.; Sooraksa, P. Image Encryption based on Chaotic Map and Dynamic S-box. In Proceedings of the International Symposium on Intelligent Signal Processing and Communications Systems (ISPACS), Okinawa, Japan, 12–15 November 2013; pp. 435–439. [Google Scholar]
- Gondal, M.A.; Raheem, A.; Hussain, I. A Scheme for Obtaining Secure S-Boxes Based on Chaotic Baker’s Map. 3D Research 2014, 5, 17. [Google Scholar] [CrossRef]
- Khan, M.; Shah, T.; Mahmood, H.; Gondal, M.A.; Hussain, I. A Novel Technique for the Construction of Strong S-boxes based on Chaotic Lorenz Systems. Nonlinear Dyn. 2012, 70, 2303–2311. [Google Scholar] [CrossRef]
- Khan, M.; Shah, T.; Batool, S. A New Implementation of Chaotic S-boxes in CAPTCHA. Signal Image Video Process. 2015, 10, 293–300. [Google Scholar] [CrossRef]
- Hussain, I.; Shah, T.; Gondal, M.A.; Mahmood, H. An Efficient Approach for the Construction of LFT S-boxes using Chaotic Logistic Map. Nonlinear Dyn. 2013, 71, 133–140. [Google Scholar] [CrossRef]
- Ali, R.S.; Akif, O.Z.; Jassim, S.A.; Farhan, A.K.; El-Kenawy, E.S.M.; Ibrahim, A.; Ghoneim, M.E.; Abdelhamid, A.A. Enhancement of the CAST Block Algorithm Based on Novel S-Box for Image Encryption. Sensors 2022, 22, 8527. [Google Scholar] [CrossRef]
- Wang, Y.; Yang, L.; Li, M.; Song, S. A Method for Designing S-box based on Chaotic Neural Network. In Proceedings of the Sixth International Conference on Natural Computation (ICNC), Yantai, China, 10–12 August 2010; Volume 2, pp. 1033–1037. [Google Scholar]
- Noughabi, M.; Sadeghiyan, B. Design of S-boxes based on Neural Networks. In Proceedings of the International Conference on Electronics and Information Engineering (ICEIE), Kyoto, Japan, 1–3 August 2010; Volume 2, pp. V2-172–V2-178. [Google Scholar]
- Zaibi, G.; Kachouri, A.; Peyrard, F.; Fournier-Prunaret, D. On Dynamic Chaotic S-box. In Proceedings of the Global Information Infrastructure Symposium, Hammamet, Tunisia, 23–26 June 2009; pp. 1–5. [Google Scholar]
- Ahmad, M.; Rizvi, D.R.; Ahmad, Z. PWLCM-Based Random Search for Strong Substitution-Box Design. In Proceedings of the Second International Conference on Computer and Communication Technologies: IC3T 2015; Springer: New Delhi, India, 2016; Volume 1, pp. 471–478. [Google Scholar]
- Tang, G.; Liao, X. A Method for Designing Dynamical S-boxes based on Discretized Chaotic Map. Chaos Solitons Fractals 2005, 23, 1901–1909. [Google Scholar] [CrossRef]
- Rîncu, C.I.; Iana, V.G. S-box Design based on Chaotic Maps Combination. In Proceedings of the 10th International Conference on Communications (COMM), Bucharest, Romania, 29–31 May 2014; pp. 1–4. [Google Scholar]
- Anees, A.; Ahmed, Z. A Technique for Designing Substitution Box Based on Van der Pol Oscillator. Wirel. Pers. Commun. 2015, 82, 1497–1503. [Google Scholar] [CrossRef]
- Millan, W. How to Improve the Nonlinearity of Bijective S-boxes. In Information Security and Privacy; Lecture Notes in Computer Science; Boyd, C., Dawson, E., Eds.; Springer: Berlin/Heidelberg, Germany, 1998; Volume 1438, pp. 181–192. [Google Scholar]
- Wu, Y.; Noonan, J.P.; Agaian, S.S. Dynamic and Implicit Latin Square Doubly Stochastic S-boxes with Reversibility. In Proceedings of the IEEE International Conference on Systems, Man, and Cybernetics (SMC), Anchorage, AL, USA, 9–12 October 2011; pp. 3358–3364. [Google Scholar]
- Radhakrishnan, S.V.; Subramanian, S. An Analytical Approach to S-box Generation. Comput. Electr. Eng. 2013, 39, 1006–1015. [Google Scholar] [CrossRef]
- Picek, S.; Ege, B.; Batina, L.; Jakobovic, D.; Chmielewski, L.; Golub, M. On Using Genetic Algorithms for Intrinsic Side-channel Resistance: The Case of AES S-box. In Proceedings of the First Workshop on Cryptography and Security in Computing Systems, Vienna, Austria, 20 January 2014; ACM: New York, NY, USA, 2014; pp. 13–18. [Google Scholar]
- Ivanov, G.; Nikolov, N.; Nikova, S. Reversed Genetic Algorithms for Generation of Bijective S-Boxes with Good Cryptographic Properties. Cryptology ePrint Archive, Report 2014/801. 2014. Available online: https://eprint.iacr.org/2014/801 (accessed on 30 July 2022).
- Clark, J.A.; Jacob, J.L.; Stepney, S. The Design of S-boxes by Simulated Annealing. New Gen. Comput. 2005, 23, 219–231. [Google Scholar] [CrossRef]
- Kuznetsov, A.; Wieclaw, L.; Poluyanenko, N.; Hamera, L.; Kandiy, S.; Lohachova, Y. Optimization of a Simulated Annealing Algorithm for S-Boxes Generating. Sensors 2022, 22, 6073. [Google Scholar] [CrossRef]
- Szaban, M.; Seredynski, F. Cryptographically Strong S-Boxes based on Cellular Automata. In Cellular Automata; Lecture Notes in Computer Science; Umeo, H., Morishita, S., Nishinari, K., Komatsuzaki, T., Bandini, S., Eds.; Springer: Berlin/Heidelberg, Germany, 2008; Volume 5191, pp. 478–485. [Google Scholar]
- Szaban, M.; Seredynski, F. Designing Cryptographically Strong S-boxes with the use of Cellular Automata. Ann. UMCS Inf. 2009, 8, 27–41. [Google Scholar] [CrossRef]
- Ahmad, M.; Bhatia, D.; Hassan, Y. A Novel Ant Colony Optimization Based Scheme for Substitution Box Design. Procedia Comput. Sci. 2015, 57, 572–580. [Google Scholar] [CrossRef]
- Ivanov, G.; Nikolov, N.; Nikova, S. Cryptographically Strong S-Boxes Generated by Modified Immune Algorithm. In Cryptography and Information Security in the Balkans: Second International Conference, BalkanCryptSec 2015, Koper, Slovenia, 3–4 September 2015; Revised Selected Papers; Springer International Publishing: Cham, Switzerland, 2016; pp. 31–42. [Google Scholar]
- Isa, H.; Jamil, N.; Z’aba, M.R. Construction of Cryptographically Strong S-Boxes Inspired by Bee Waggle Dance. New Gen. Comput. 2016, 34, 221–238. [Google Scholar] [CrossRef]
- Sikdar, D. S-box Optimization Technique with a Primitive Irreducible Polynomial. Int. J. Emerg. Trends Technol. Comput. Sci. 2014, 3, 97–99. [Google Scholar]
- Khan, M.; Azam, N.A. S-Boxes based on Affine Mapping and Orbit of Power Function. 3D Research 2015, 6, 12. [Google Scholar] [CrossRef]
- Yang, M.; Wang, Z.; Meng, Q.; Han, L. Evolutionary Design of S-box with Cryptographic Properties. In Proceedings of the Ninth IEEE International Symposium on Parallel and Distributed Processing with Applications Workshops (ISPAW), Busan, Republic of Korea, 26–28 May 2011; pp. 12–15. [Google Scholar]
- Chun, Y.; Guo, Y. A Research and Improvement Based on Rijndael Algorithm. In Proceedings of the 1st International Conference on Information Science and Engineering (ICISE), Nanjing, China, 26–28 December 2009; pp. 1585–1588. [Google Scholar]
- Cui, J.; Huang, L.; Zhong, H.; Chang, C.; Yang, W. An Improved AES S-box and Its Performance Analysis. Int. J. Innov. Comput. Inf. Control 2011, 7, 2291–2302. [Google Scholar]
- Kumar, A.; Tiwari, N. AES Security Enhancement by Using Double S-Box. Int. J. Comput. Sci. Inf. Technol. 2012, 3, 3980–3984. [Google Scholar]
- Kapalova, N.; Sakan, K.; Algazy, K.; Dyusenbayev, D. Development and Study of an Encryption Algorithm. Computation 2022, 10, 198. [Google Scholar] [CrossRef]
- Hussain, I.; Shah, T.; Gondal, M.A.; Khan, M.; Khan, W.A. Construction of New S-box using a Linear Fractional Transformation. World Appl. Sci. J. 2011, 14, 1779–1785. [Google Scholar]
- Hussain, I.; Shah, T.; Gondal, M.A.; Khan, W.A.; Mahmood, H. A Group Theoretic Approach to Construct Cryptographically Strong Substitution Boxes. Neural Comput. Appl. 2013, 23, 97–104. [Google Scholar] [CrossRef]
- Hussain, I.; Shah, T.; Mahmood, H.; Gondal, M.A. A Projective General Linear Group based Algorithm for the Construction of Substitution Box for Block Ciphers. Neural Comput. 2013, 22, 1085–1093. [Google Scholar] [CrossRef]
- Jin, S.Y.; Baek, J.M.; Song, H.Y. Improved Rijndael-Like S-Box and Its Transform Domain Analysis. In Proceedings of the Sequences and Their Applications—SETA 2006: 4th International Conference, Beijing, China, 24–28 September 2006; Springer: Berlin/Heidelberg, Germany, 2006; pp. 153–167. [Google Scholar]
- Tran, M.T.; Bui, D.K.; Duong, A.D. Gray S-box for Advanced Encryption Standard. In Proceedings of the International Conference on Computational Intelligence and Security (CIS’08), Suzhou, China, 13–17 December 2008; Volume 1, pp. 253–258. [Google Scholar]
- Dumas, J.G.; Orfila, J.B. Generating S-Boxes from Semi-fields Pseudo-Extensions. arXiv 2014, arXiv:1411.2503. [Google Scholar]
- Li, Y.; Wang, M. Constructing Differentially 4-Uniform Permutations over GF(22m) from Quadratic APN Permutations over GF(22m+1). Des. Codes Cryptogr. 2014, 72, 249–264. [Google Scholar] [CrossRef]
- Fuller, J.; Millan, W.; Dawson, E. Multi-Objective Optimisation of Bijective S-boxes. New Gen. Comput. 2005, 23, 201–218. [Google Scholar] [CrossRef]
- Isa, H.; Jamil, N.; Z’aba, M.R. Improved S-Box Construction from Binomial Power Functions. Malays. J. Math. Sci. 2015, 9, 21–35. [Google Scholar]
- Aslan, B.; Sakalli, M.T.; Bulus, E. Classifying 8-Bit to 8-Bit S-Boxes based on Power Mappings from the Point of DDT and LAT Distributions. In Arithmetic of Finite Fields; Lecture Notes in Computer Science; von zur Gathen, J., Imaña, J.L., Koç, c.K., Eds.; Springer: Berlin/Heidelberg, Germany, 2008; Volume 5130, pp. 123–133. [Google Scholar]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).