Deep Q-Learning-Based Neural Network with Privacy Preservation Method for Secure Data Transmission in Internet of Things (IoT) Healthcare Application
Abstract
:1. Introduction
- Constructing a systematic framework using the deep Q-learning method for processing patient data, which further reduces traffic in a network.
- Adoptingciphertext-policy attribute-based privacy preservation (CPABPP) for generating both a public key (PK) and a master key (MK).
2. Related Works
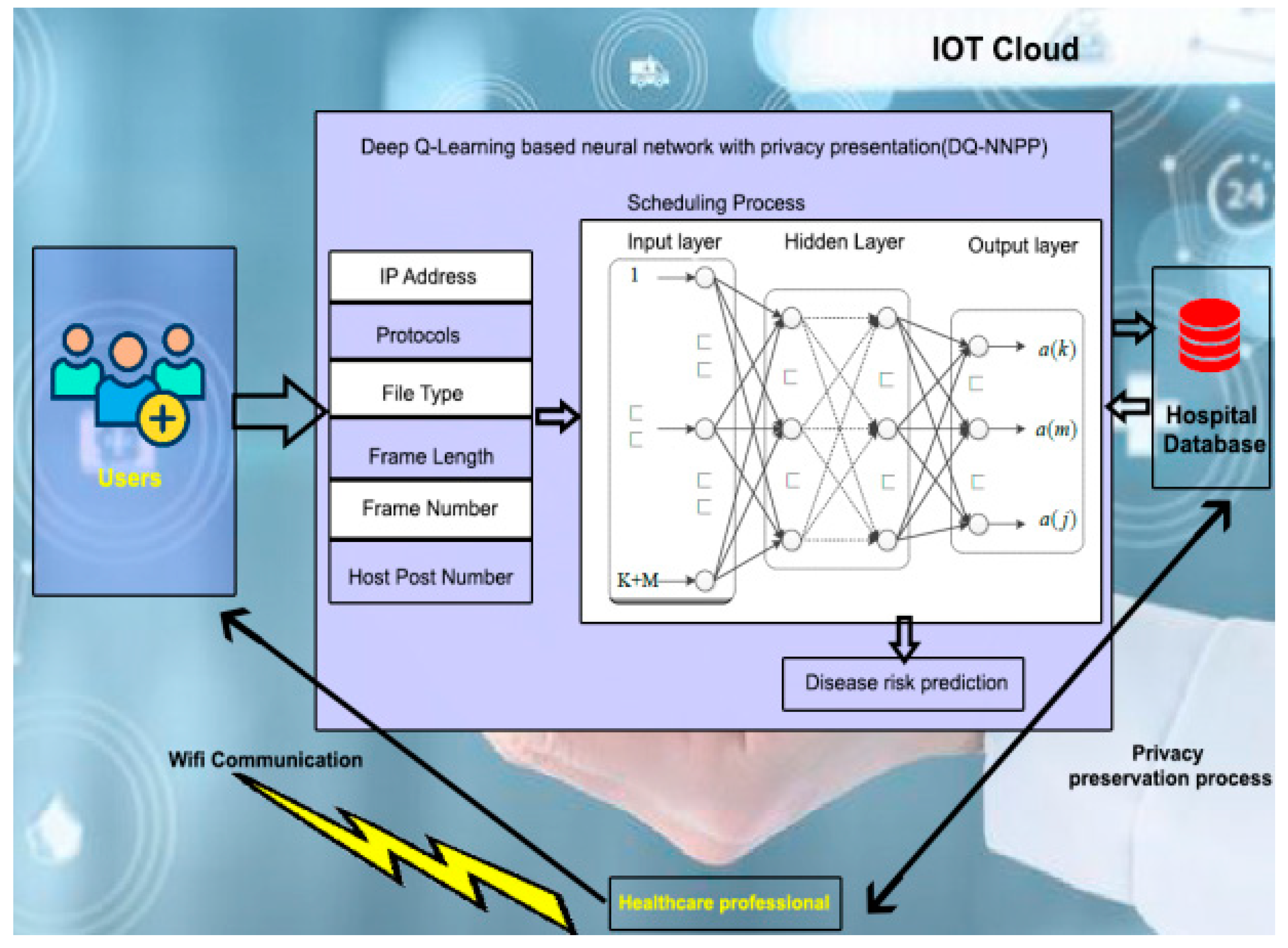
3. System Model
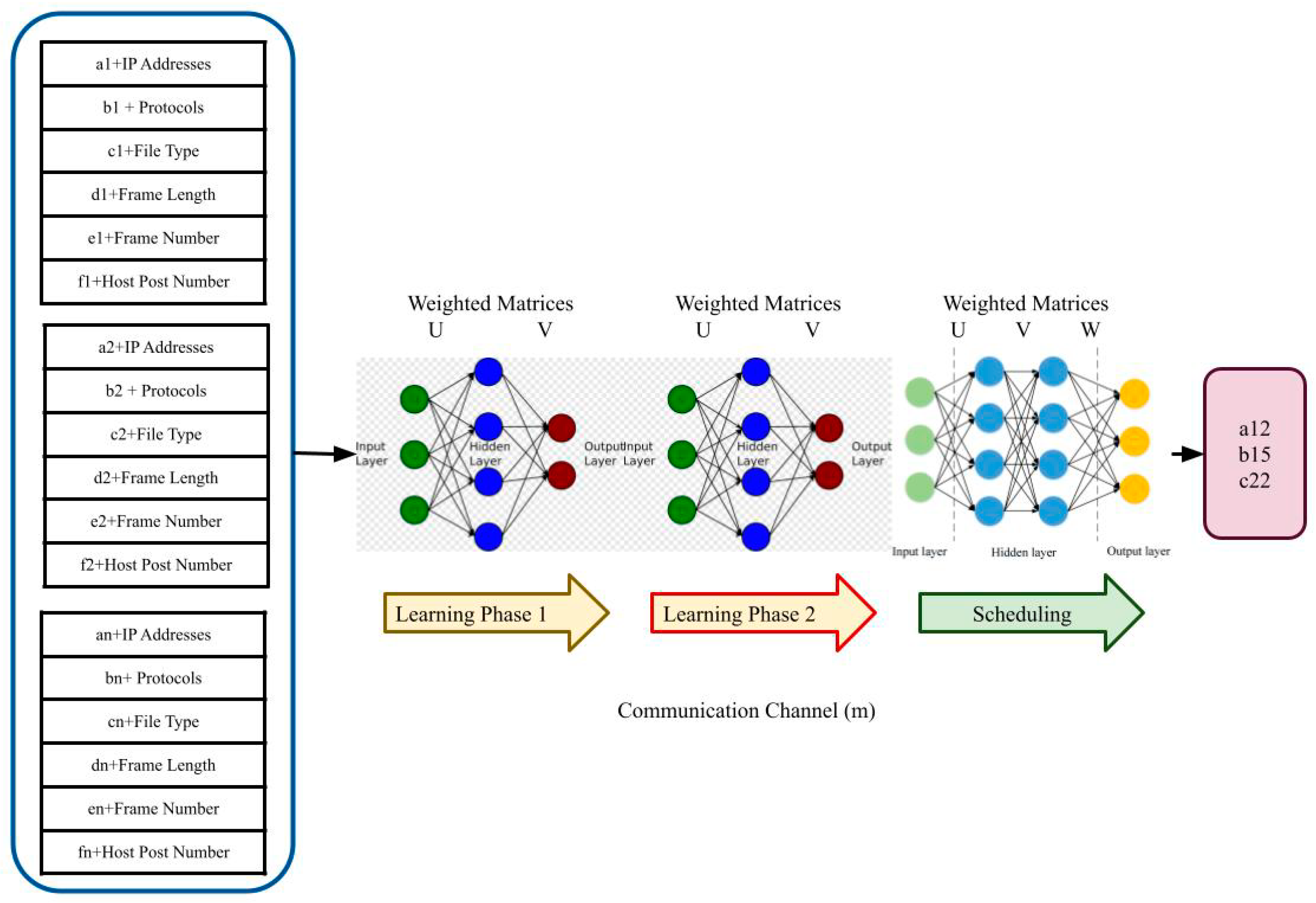
3.1. Deep Q-Learning-Based Scheduling and Data Transmission
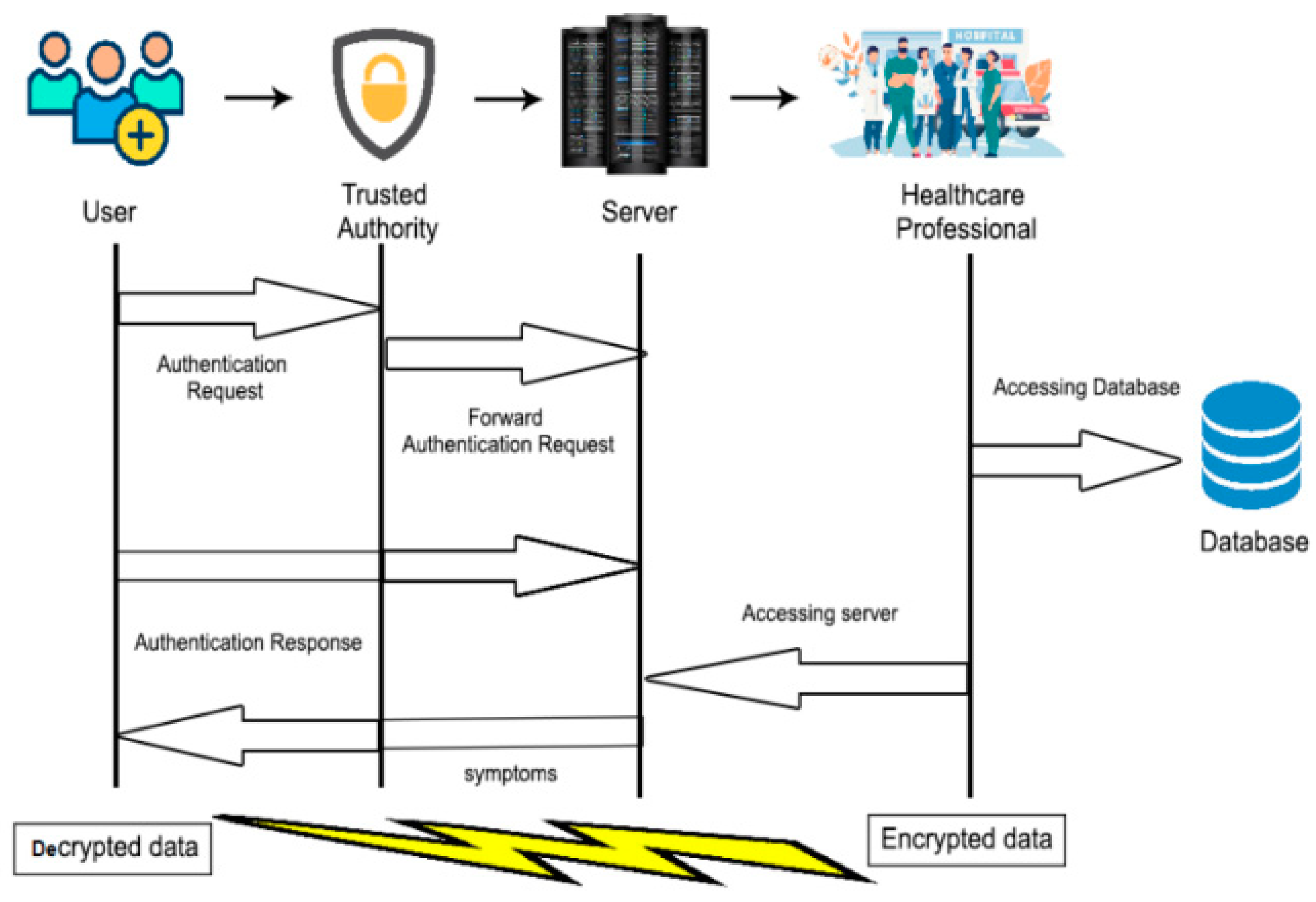
System Model for Security
- TA generates the parameters and deals with registration.
- Hospitals supply patients’ medical information to the servers.
- The userqueries the doctors with the source and destination stage.
- Interaction between servers generates a portion of the clinical pathway, which in turn is returned to the user. Multiple interactions are allowed to occur with other interactions instead of between the hospital and user, thereby effectively reducing the local communication overhead and computational cost. In this model, the data (k = 1, 2, 3, …, m) of medical datasets include details of the patients, such as name, age, gender, expenses, other indices, medication, and the time of appointments. These details are shared and protected by the ciphertext-policyattribute-based privacy preservation approach. On the basis of these privacy policies, the server creates an integrated directional connected network.
3.2. Key Generation on Ciphertext-PolicyAttribute-Based Privacy Preservation (CPABPP)
| Algorithm 1 Algorithm for generating subkeys |
| 1: Input—plain text |
| 2: Output—subkeys |
| 3: Strings(x) = P1, P2, P3…Pn |
| 4: if |
| 5: A = P1(XOR) P2 |
| 6: (n = P1; n + 1 > P1) |
| 7: B = P2(XOR) P3 |
| 8: (P2 = n; P2 < n + 1) |
| 9: C = P3(XOR) P4 |
| 10: (n = P1; n + 1 > P1) |
| 11: N = Pn(XOR) Pn |
| 12: (P1 = n; P1 < n + 1) |
| 13: end if |
| 14: Y*Z* (A mod E) = K1 |
| 15: X*Z*(B mod F) = K2 |
| 16: Y*X*(C mod G) = K3 |
| 17: α2 (Y*Z*(A mod E)) = βK1 |
| 18: α2 (X*Z*(B mod F)) = βK2 |
| 19: α2 (Y*X*(C mod G)) = βK3 |
| 20: end |
Encryption Process
4. Performance Analysis
5. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Buttyan, L.; Hubaux, J.P. Privacy protection. In Security and Cooperation in Wireless Networks: Thwarting Malicious and Selfish Behavior in the Age of Ubiquitous Computing; Cambridge University Press: New York, NY, USA, 2008; pp. 237–254. [Google Scholar]
- Ramos, J.L.H.; Bernabe, J.B.; Skarmeta, A.F. Towards Privacy-preserving data sharing in smart environments. In Proceedings of the IEEE 8th International Conference on Innovative Mobile and Internet Services in Ubiquitous Computing, Birmingham, UK, 2–4 July 2014; pp. 334–339. [Google Scholar]
- Gue, X.; Duan, X.; Gao, H.; Huang, A.; Jiao, B. An ECG Monitoring and Alarming System Based on Android Smart Phone. Commun. Netw. 2013, 5, 584–589. [Google Scholar] [CrossRef]
- Sonar, K.; Upadhyay, H. A Survey: DDOS Attack on Internet of Things. Int. J. Eng. Res. Dev. 2014, 10, 58–63. [Google Scholar]
- Miao, Y.; Ma, J.; Liu, X.; Wei, F.; Liu, Z.; Wang, X.A. m2-ABKS: Attribute-Based Multi-Keyword Search over Encrypted Personal Health Records in Multi-Owner Setting. J. Med. Syst. 2016, 40, 68. [Google Scholar] [CrossRef] [PubMed]
- Huang, M.; Liu, A.; Wang, T.; Huang, C. Green data gathering under delay differentiated services constraint for internet of things. Wirel. Commun. Mob. Comput. 2018, 2018, 9715428. [Google Scholar] [CrossRef] [Green Version]
- Rahim, R.; Murugan, S.; Mostafa, R.R.; Dubey, A.; Regin, K.; Kulkarni, R.; Dhanalakshmi, V. Detecting the Phishing Attack Using Collaborative Approach and Secure Login through Dynamic Virtual Passwords. Webology 2020, 17, 524–535. [Google Scholar] [CrossRef]
- Tang, J.; Liu, A.; Zhao, M.; Wang, T. An Aggregate Signature Based Trust Routing for Data Gathering in Sensor Networks. Secur. Commun. Netw. 2018, 2018, 6328504. [Google Scholar] [CrossRef]
- Al-Qatf, M.; Lasheng, Y.; Al-Habib, M.; Al-Sabahi, K. Deep Learning Approach Combining Sparse Autoencoder with SVM for Network Intrusion Detection. IEEE Access 2018, 6, 52843–52856. [Google Scholar] [CrossRef]
- Otoum, S.; Kantarci, B.; Mouftah, H.T. On the Feasibility of Deep Learning in Sensor Network Intrusion Detection. IEEE Netw. Lett. 2019, 1, 68–71. [Google Scholar] [CrossRef]
- Ahamad, D.; Alam Hameed, S.; Akhtar, M. A multi-objective privacy preservation model for cloud security using hybrid Jaya-based shark smell optimization. J. King Saud Univ.-Comput. Inf. Sci. 2020. [Google Scholar] [CrossRef]
- Deebak, B.D.; Al-Turjman, F.; Aloqaily, M.; Alfandi, O. An Authentic-Based Privacy Preservation Protocol for Smart e-Healthcare Systems in IoT. IEEE Access 2019, 7, 135632–135649. [Google Scholar] [CrossRef]
- Wang, K.; Chen, C.-M.; Tie, Z.; Shojafar, M.; Kumar, S.; Kumari, S. Forward Privacy Preservation in IoT enabled Healthcare Systems. IEEE Trans. Ind. Inform. 2022, 18, 1991–1999. [Google Scholar] [CrossRef]
- Kwabena, O.A.; Qin, Z.; Zhuang, T.; Qin, Z. Mscryptonet: Multi-scheme privacy-preserving deep learning in cloud computing. IEEE Access 2019, 7, 29344–29354. [Google Scholar] [CrossRef]
- Keshavarzian, A.; Sharifian, S.; Seyedin, S. Modified deep residual network architecture deployed on serverless framework of IoT platform based on human activity recognition application. Futur. Gener. Comput. Syst. 2019, 101, 14–28. [Google Scholar] [CrossRef]
- Zhang, C.; Zhu, L.; Xu, C.; Lu, R. PPDP: An efficient and privacy-preserving disease prediction scheme in cloud-based e-Healthcare system. Futur. Gener. Comput. Syst. 2018, 79, 16–25. [Google Scholar] [CrossRef]
- Veeramakali, T.; Siva, R.; Sivakumar, B.; Mahesh, S.P.; Krishnaraj, N. An intelligent internet of things-based secure healthcare framework using blockchain technology with an optimal deep learning model. J. Super Comput. 2021, 77, 1–21. [Google Scholar] [CrossRef]
- Hui, H.; Zhou, C.; Xu, S.; Lin, F. A novel secure data transmission scheme in industrial internet of things. China Commun. 2020, 17, 73–88. [Google Scholar] [CrossRef]
- Liang, W.; Tang, M.; Long, J.; Peng, X.; Xu, J.; Li, K.-C. A Secure FaBric Blockchain-Based Data Transmission Technique for Industrial Internet-of-Things. IEEE Trans. Ind. Inform. 2019, 15, 3582–3592. [Google Scholar] [CrossRef]
- Abirami, P.; Bhanu, S.V. Enhancing cloud security using crypto-deep neural network for privacy preservation in trusted environment. Soft Comput. 2020, 24, 18927–18936. [Google Scholar] [CrossRef]
- Zhang, L.; Shi, Y.; Chang, Y.-C.; Lin, C.-T. Hierarchical Fuzzy Neural Networks with Privacy Preservation for Heterogeneous Big Data. IEEE Trans. Fuzzy Syst. 2020, 29, 46–58. [Google Scholar] [CrossRef]
- Bi, H.; Liu, J.; Kato, N. Deep Learning-based Privacy Preservation and Data Analytics for IoT Enabled Healthcare. IEEE Trans. Ind. Inform. 2021. [Google Scholar] [CrossRef]
- Zhu, J.; Song, Y.; Jiang, D.; Song, H. A new deep-Q-learning-based transmission scheduling mechanism for the cognitive Internet of Things. IEEE Internet Things J. 2017, 5, 2375–2385. [Google Scholar] [CrossRef]
- Yang, L.; Yu, K.; Yang, S.X.; Chakraborty, C.; Lu, Y.; Guo, T. An Intelligent Trust Cloud Management Method for Secure Clustering in 5G enabled Internet of Medical Things. IEEE Trans. Ind. Inform. 2021. [Google Scholar] [CrossRef]
- Liu, J.; Liu, H.; Chakraborty, C.; Yu, K.; Shao, X.; Ma, Z. Cascade Learning Embedded Vision Inspection of Rail Fastener by Using a Fault Detection IoT Vehicle. IEEE Internet Things J. 2021. [Google Scholar] [CrossRef]
- Guesmi, R. A novel design of Chaos based S-Boxes using genetic algorithm techniques. In Proceedings of the 2014 IEEE/ACS 11th International Conference on Computer Systems and Applications (AICCSA), Doha, Qatar, 10–13 November 2014. [Google Scholar]
- Qin, Q.; Jin, B.; Liu, Y. A Secure Storage and Sharing Scheme of Stroke Electronic Medical Records Based on Consortium Blockchain. BioMed Res. Int. 2021, 2021, 6676171. [Google Scholar] [CrossRef] [PubMed]

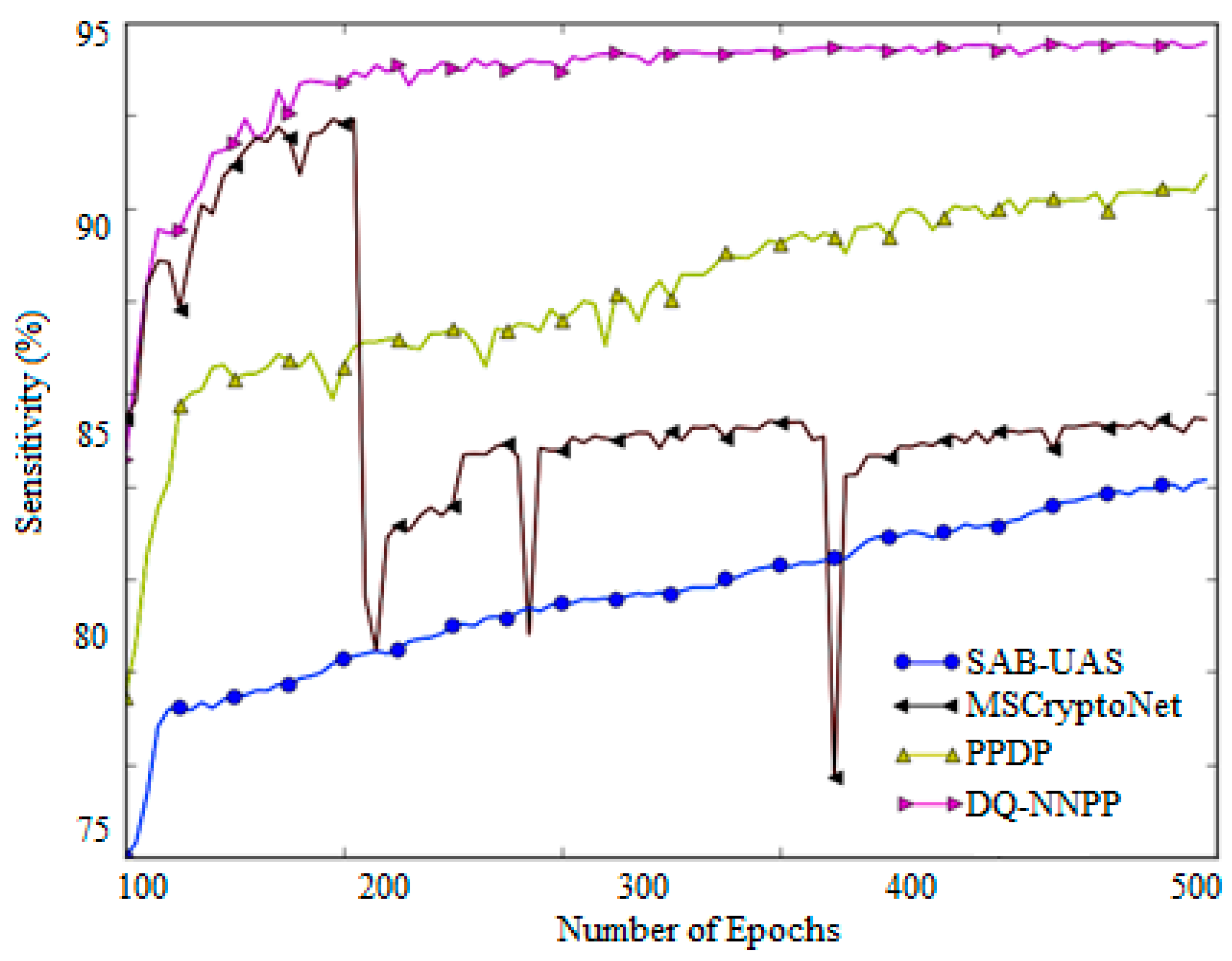
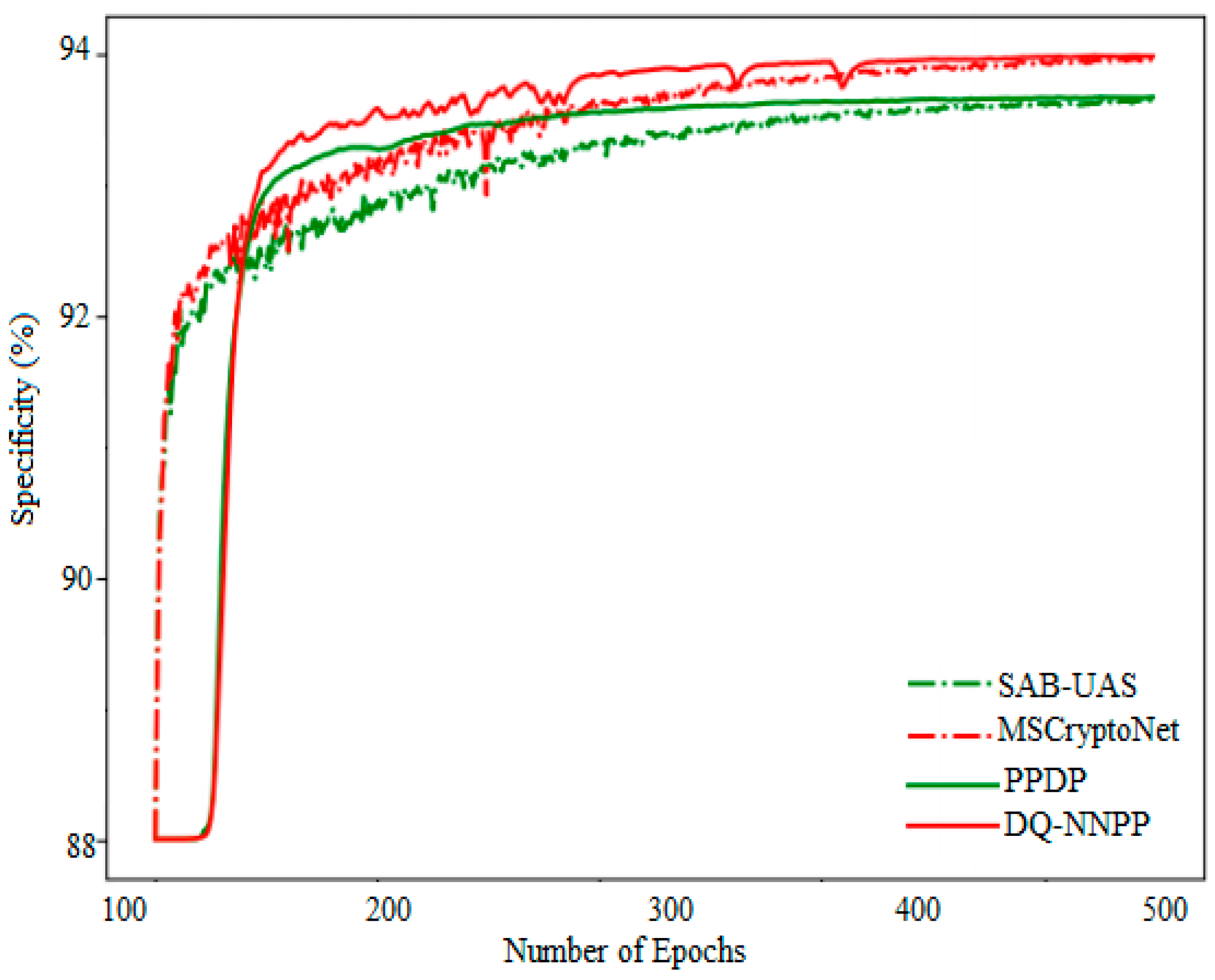

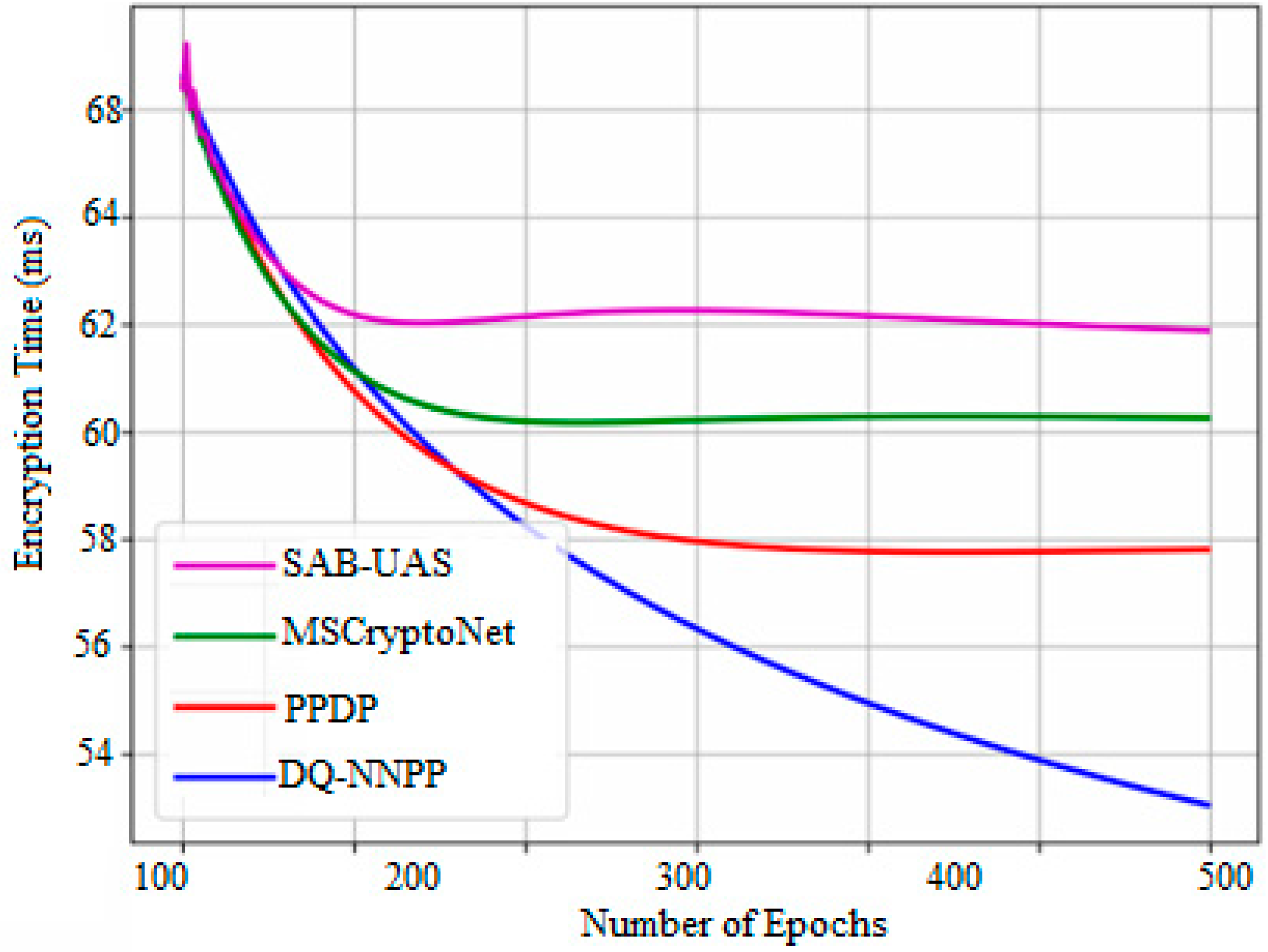
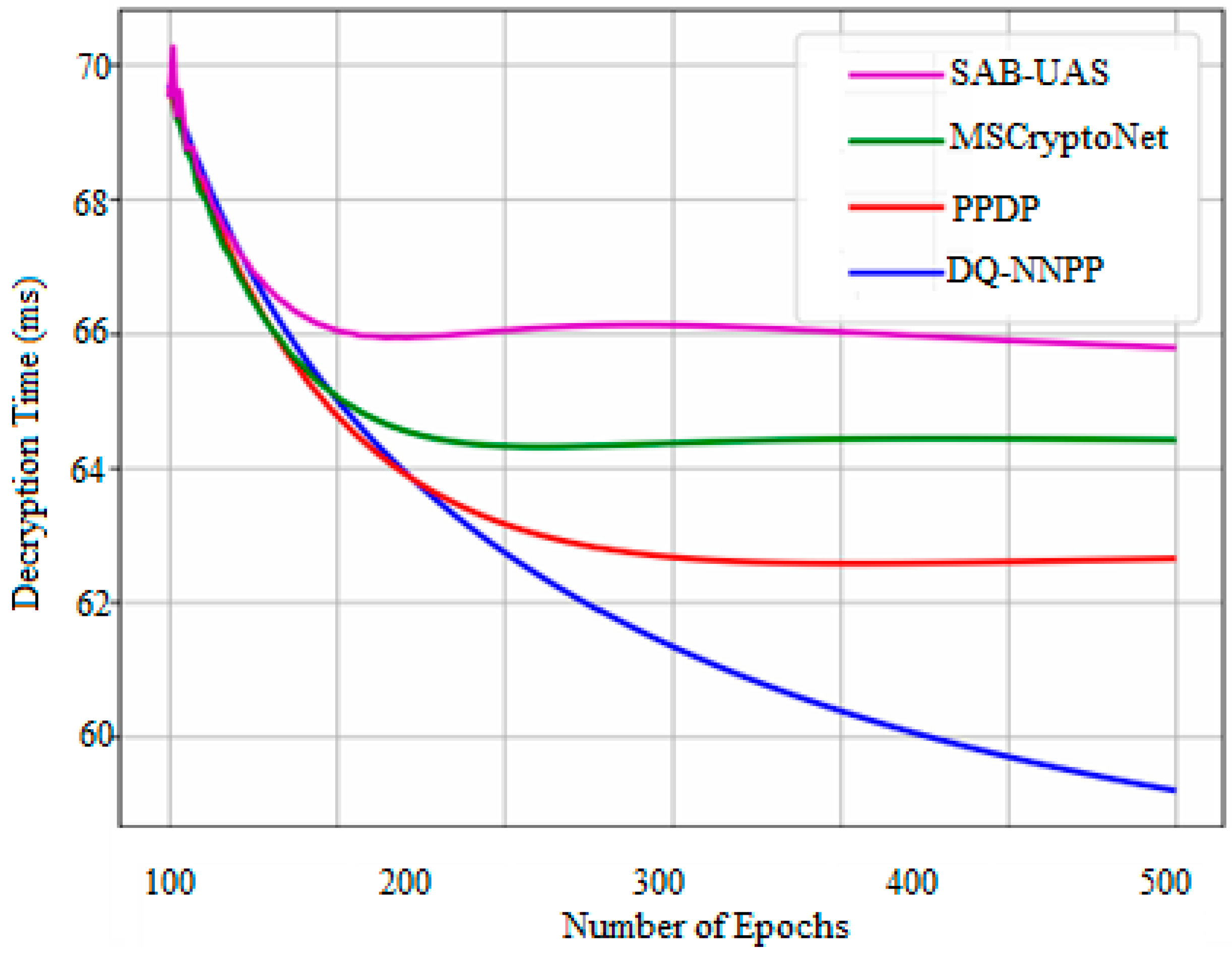
| Parameters | SAB-UAS [12] | MSCryptoNet [14] | PPDP [16] | DQ-NNPP (Proposed) |
|---|---|---|---|---|
| Accuracy (%) | 92.02 | 94.3 | 93.04 | 93.74 |
| Sensitivity (%) | 79.4 | 84.72 | 86.42 | 92 |
| Specificity (%) | 90.7 | 91.44 | 91.58 | 92.1 |
| Communication Overhead (%) | 64.62 | 65.24 | 66.76 | 67.08 |
| Encryption time (ms) | 64 | 62.2 | 60.52 | 58.72 |
| Decryption time (ms) | 67.48 | 66.58 | 64.74 | 62.72 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kathamuthu, N.D.; Chinnamuthu, A.; Iruthayanathan, N.; Ramachandran, M.; Gandomi, A.H. Deep Q-Learning-Based Neural Network with Privacy Preservation Method for Secure Data Transmission in Internet of Things (IoT) Healthcare Application. Electronics 2022, 11, 157. https://doi.org/10.3390/electronics11010157
Kathamuthu ND, Chinnamuthu A, Iruthayanathan N, Ramachandran M, Gandomi AH. Deep Q-Learning-Based Neural Network with Privacy Preservation Method for Secure Data Transmission in Internet of Things (IoT) Healthcare Application. Electronics. 2022; 11(1):157. https://doi.org/10.3390/electronics11010157
Chicago/Turabian StyleKathamuthu, Nirmala Devi, Annadurai Chinnamuthu, Nelson Iruthayanathan, Manikandan Ramachandran, and Amir H. Gandomi. 2022. "Deep Q-Learning-Based Neural Network with Privacy Preservation Method for Secure Data Transmission in Internet of Things (IoT) Healthcare Application" Electronics 11, no. 1: 157. https://doi.org/10.3390/electronics11010157
APA StyleKathamuthu, N. D., Chinnamuthu, A., Iruthayanathan, N., Ramachandran, M., & Gandomi, A. H. (2022). Deep Q-Learning-Based Neural Network with Privacy Preservation Method for Secure Data Transmission in Internet of Things (IoT) Healthcare Application. Electronics, 11(1), 157. https://doi.org/10.3390/electronics11010157







