Botnet Attack Detection Using Local Global Best Bat Algorithm for Industrial Internet of Things
Abstract
1. Introduction
- A novel meta-heuristic local-global best bat algorithm (LGBA) for optimization of the hyper-parameters of a neural network (LGBA-NN) is presented.
- The proposed LGBA-NN is tested on an N-BaIoT data set with extensive real-world traffic data with benign and malicious classes, achieving high performance.
2. Related Work
3. Material and Methods
3.1. Bat Algorithm
- Every micro bat estimates the distance within their surroundings and prey by utilizing its property of echolocation.
- Frequency of fixed range is utilized to find a micro bat’s velocity from location beside distinct loudness and distinct wavelength while searching for prey.
- Emission pulse rate can be utilized to adjust the frequency of its pulses while estimating distance among prey and microbat.
- Loudness will be migrated from a considerable positive value to a smaller value .
- N denotes the number of locations of the artificial bat.
- is used to denote minimum frequency, while is used to denote maximum frequency.
- Every bat’s velocity vector is represented by .
- Rate of loudness is denoted by .
- Pulse rate is denoted by .
- Every bat’s initial pulse rate is denoted by .
- and are two constants.
- £ is used to denote a range of bandwidth.
| Algorithm 1 Pseudo code for standard BA. |
|
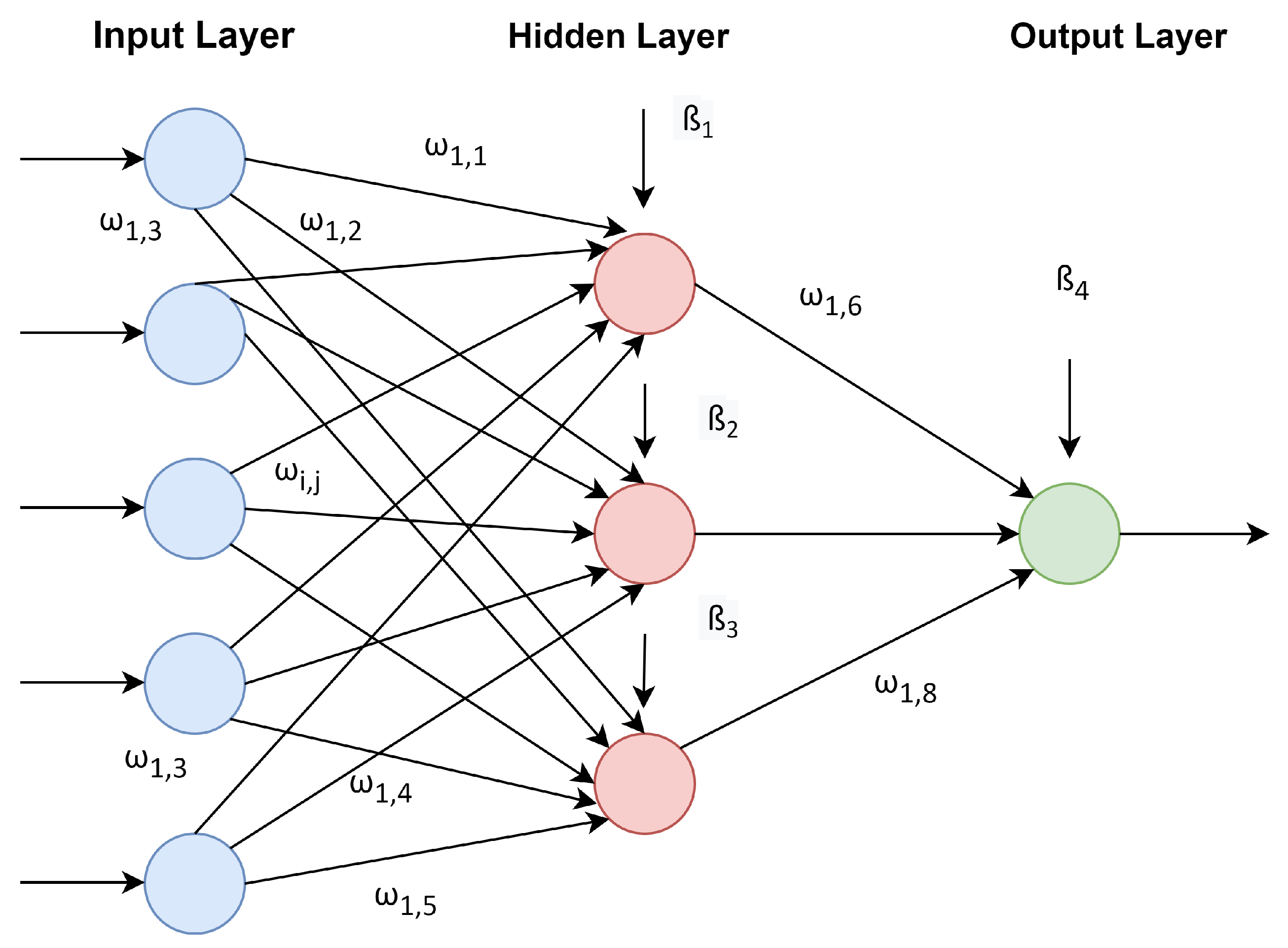
Deep Artificial Neural Networks (DNN)
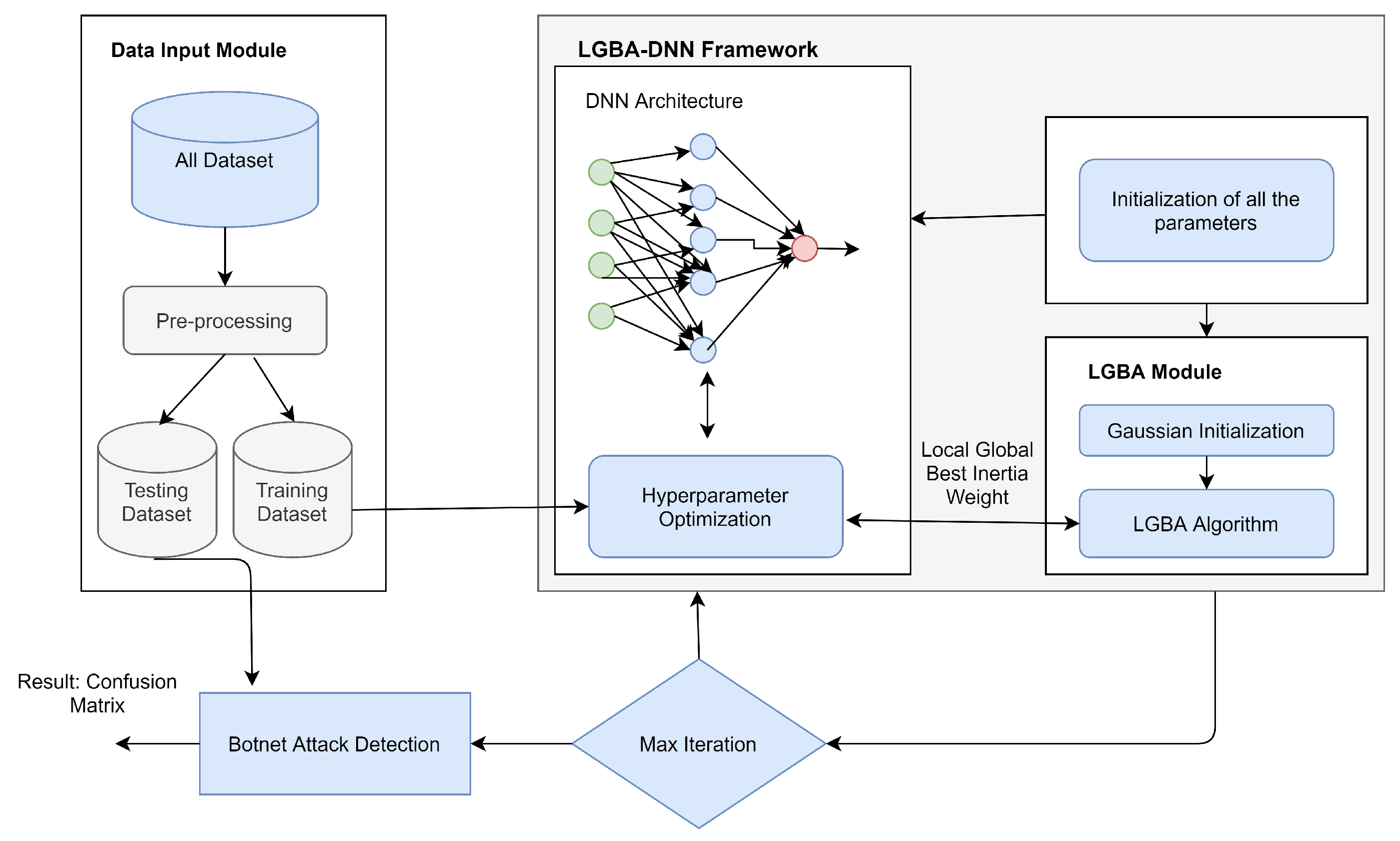
3.2. Local-Global Best Bat Algorithm (LGBA-NN)
3.2.1. Gaussian Distribution
3.2.2. LGBA-NN Steps
- Initialize the bat population using the Gaussian distribution over internal [0, 1]. The Gaussian density function ensures the diverse locations of each bat in the multidimensional search space. If any two corresponding vectors obtain the same initial solution, the Gaussian density function produces a diversity effect in the second generation. The following equation can be used to initialize the population using Gaussian distribution.where represents each individual gained initial location using Gaussian distribution over jth dimension. indicates the lower bound, which is set to 0, and shows the upper bound with 1 maximum value. represents the Gaussian density function used to generate random numbers following Gaussian distribution over the interval of [ ]. Normal distribution starts with a random guess if the bats have any prior knowledge about the solution. However, Gaussian distribution disregards previous experience about the solution. This phenomenon tends to produce a rich diversity in the initial solution of the population.
- The second modification includes the local-global best inertia weight to accelerate each bat’s velocity during the exploration process. In standard BA, the velocity of each bat is updated without inertia weight acceleration. In general, significant inertia weight is recommended for the initial stages of the quest process to improve global exploration (searching for new areas). However, the inertia weight is decreased for local exploration in the later stages (fine-tuning the current search area).The proposed local-global best inertia weight effect can be produced by taking a significant difference in local best solution of the current swarm with the global best solution of all multitude in the multidimensional search space. This phenomenon supports the convergence process to be robust enough in terms of exploration; if the current generation gained two same fitness values, the proposed inertia weight uses both solutions to decide the bat’s next location towards the global optimum. Local-global best inertia weight can be defined using the following equation.where indicates the local best solution of current swarm and expresses the global best solution of all the swarms in the population.LGBA-NN updates the bats velocity through following equation.is local-global best inertia weight; indicates the previous velocity of current individual, where is current position of bat; and expresses the global best solution of all swarms in the population. shows frequency of the ith bat in the multi-dimensional search space.
- In the third modification, we updated the local search mechanism, which uses the Gaussian density function and local-global best function to achieve better exploration during each generation. During the local searching process, each bat’s current fitness was evaluated and compared with each bat’s previous fitness; however, in standard BA, the local search mechanism missed the local and global best solution during the last generation. In the previous generation, if any bat has a global fitness greater than the global fitness of bats in the next generation, then the algorithm needs to retain the last global best fitness. We tackled this issue by introducing the Gaussian density function and local-global best function to achieve better exploration during each generation. Local-global best function retained the difference between previous local and global best. LGBA will check the difference between local and global best fitness; check if it is minimal, smaller than the current fitness; and retains the best optimum solution. LGBA uses the following equation to update the local search manner.where represents the accelerated sequence generated through Gaussian distribution, indicates the local-global best function retaining the difference between the previous local and global best, where is the scaling factor used to balance the exploitation during local search.The pseudo code for proposed LGBA-NN is given in Algorithm 2.
- In the last modification, LGBA is further employed in the neural network for hyperparameter tuning and weight optimization to classify ten different botnet attacks with an additional one benign target class. A weight is linked with each input signal following the optimal solution . The output signal is then fed to the classifier for the prediction. For weight optimization of LGBA-NN, we used the following equation.
| Algorithm 2 Pseudo code for the proposed LGBA-NN. |
|
3.3. Data Set Description
3.4. Evaluation Metrics
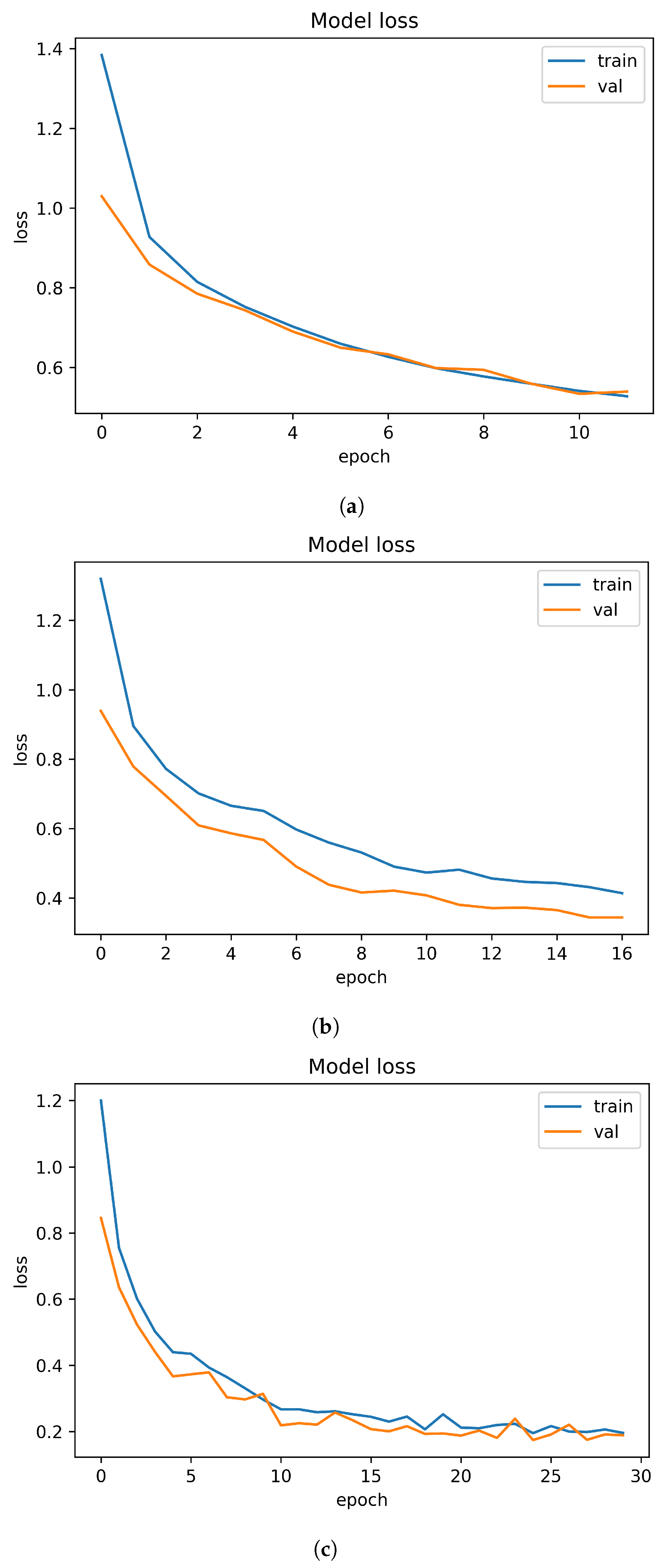
4. Results and Discussion
Analysis
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Vasilomanolakis, E.; Karuppayah, S.; Mühlhäuser, M.; Fischer, M. Taxonomy and Survey of Collaborative Intrusion Detection. ACM Comput. Surv. 2015, 47, 1–33. [Google Scholar] [CrossRef]
- Hussain, B.; Du, Q.; Sun, B.; Han, Z. Deep Learning-Based DDoS-Attack Detection for Cyber-Physical System over 5G Network. IEEE Trans. Ind. Inform. 2021, 17, 860–870. [Google Scholar] [CrossRef]
- de Assis, M.V.O.; Carvalho, L.F.; Rodrigues, J.J.P.C.; Lloret, J.; Proença, M.L., Jr. Near real-time security system applied to SDN environments in IoT networks using convolutional neural network. Comput. Electr. Eng. 2020, 86, 106738. [Google Scholar] [CrossRef]
- Manimurugan, S.; Al-Mutairi, S.; Aborokbah, M.M.; Chilamkurti, N.; Ganesan, S.; Patan, R. Effective attack detection in internet of medical things smart environment using a deep belief neural network. IEEE Access 2020, 8, 77396–77404. [Google Scholar] [CrossRef]
- Rehman Javed, A.; Jalil, Z.; Atif Moqurrab, S.; Abbas, S.; Liu, X. Ensemble Adaboost classifier for accurate and fast detection of botnet attacks in connected vehicles. Trans. Emerg. Telecommun. Technol. 2020. [Google Scholar] [CrossRef]
- Lee, S.; Abdullah, A.; Jhanjhi, N.; Kok, S. Classification of botnet attacks in IoT smart factory using honeypot combined with machine learning. PeerJ Comput. Sci. 2021, 7, 1–23. [Google Scholar] [CrossRef]
- Perez, M.G.; Celdran, A.H.; Ippoliti, F.; Giardina, P.G.; Bernini, G.; Alaez, R.M.; Chirivella-Perez, E.; Clemente, F.J.G.; Perez, G.M.; Kraja, E.; et al. Dynamic Reconfiguration in 5G Mobile Networks to Proactively Detect and Mitigate Botnets. IEEE Internet Comput. 2017, 21, 28–36. [Google Scholar] [CrossRef]
- Wei, W.; Woźniak, M.; Damaševičius, R.; Fan, X.; Li, Y. Algorithm Research of Known-plaintext Attack on Double Random Phase Mask Based on WSNs. J. Internet Technol. 2019, 20, 39–48. [Google Scholar]
- Yong, B.; Wei, W.; Li, K.; Shen, J.; Zhou, Q.; Wozniak, M.; Połap, D.; Damaševičius, R. Ensemble machine learning approaches for webshell detection in Internet of things environments. Trans. Emerg. Telecommun. Technol. 2020. [Google Scholar] [CrossRef]
- Chung, Y.Y.; Wahid, N. A hybrid network intrusion detection system using simplified swarm optimization (SSO). Appl. Soft Comput. 2012, 12, 3014–3022. [Google Scholar] [CrossRef]
- Ganapathy, S.; Kulothungan, K.; Muthurajkumar, S.; Vijayalakshmi, M.; Yogesh, P.; Kannan, A. Intelligent feature selection and classification techniques for intrusion detection in networks: A survey. EURASIP J. Wirel. Commun. Netw. 2013, 2013, 1–16. [Google Scholar] [CrossRef]
- Aburomman, A.A.; Reaz, M.B.I. Review of IDS development methods in machine learning. Int. J. Electr. Comput. Eng. (IJECE) 2016, 6, 2432–2436. [Google Scholar] [CrossRef]
- Bijalwan, A. Botnet Forensic Analysis Using Machine Learning. Secur. Commun. Netw. 2020, 2020, 9302318. [Google Scholar] [CrossRef]
- Alothman, Z.; Alkasassbeh, M.; Al-Haj Baddar, S. An efficient approach to detect IoT botnet attacks using machine learning. J. High Speed Netw. 2020, 26, 241–254. [Google Scholar] [CrossRef]
- Damasevicius, R.; Venckauskas, A.; Grigaliunas, S.; Toldinas, J.; Morkevicius, N.; Aleliunas, T.; Smuikys, P. Litnet-2020: An annotated real-world network flow dataset for network intrusion detection. Electronics 2020, 9, 800. [Google Scholar] [CrossRef]
- Mahmood, T.; Afzal, U. Security analytics: Big data analytics for cybersecurity: A review of trends, techniques and tools. In Proceedings of the 2013 2nd National Conference on Information Assurance (NCIA), Rawalpindi, Pakistan, 11–12 December 2013; pp. 129–134. [Google Scholar]
- Cozzi, E.; Vervier, P.A.; Dell’Amico, M.; Shen, Y.; Bilge, L.; Balzarotti, D. The Tangled Genealogy of IoT Malware. In Proceedings of the Annual Computer Security Applications Conference, Austin, TX, USA, 7–11 December 2020. [Google Scholar] [CrossRef]
- Kolias, C.; Kambourakis, G.; Stavrou, A.; Voas, J. DDoS in the IoT: Mirai and Other Botnets. Computer 2017, 50, 80–84. [Google Scholar] [CrossRef]
- Hoque, N.; Bhattacharyya, D.K.; Kalita, J.K. Botnet in DDoS Attacks: Trends and Challenges. IEEE Commun. Surv. Tutor. 2015, 17, 2242–2270. [Google Scholar] [CrossRef]
- McDermott, C.D.; Majdani, F.; Petrovski, A.V. Botnet Detection in the Internet of Things using Deep Learning Approaches. In Proceedings of the International Joint Conference on Neural Networks, Rio de Janeiro, Brazil, 8–13 July 2018; Volume 2018. [Google Scholar]
- Koroniotis, N.; Moustafa, N.; Sitnikova, E. Forensics and Deep Learning Mechanisms for Botnets in Internet of Things: A Survey of Challenges and Solutions. IEEE Access 2019, 7, 61764–61785. [Google Scholar] [CrossRef]
- Yerima, S.Y.; Alzaylaee, M.K.; Shajan, A.; Vinod, P. Deep learning techniques for android botnet detection. Electronics 2021, 10, 519. [Google Scholar] [CrossRef]
- Marir, N.; Wang, H.; Feng, G.; Li, B.; Jia, M. Distributed abnormal behavior detection approach based on deep belief network and ensemble svm using spark. IEEE Access 2018, 6, 59657–59671. [Google Scholar] [CrossRef]
- Azeez, N.A.; Ayemobola, T.J.; Misra, S.; Maskeliūnas, R.; Damaševičius, R. Network intrusion detection with a hashing based apriori algorithm using Hadoop MapReduce. Computers 2019, 8, 86. [Google Scholar] [CrossRef]
- Tuan, T.A.; Long, H.V.; Son, L.H.; Kumar, R.; Priyadarshini, I.; Son, N.T.K. Performance evaluation of Botnet DDoS attack detection using machine learning. Evol. Intell. 2020, 13, 283–294. [Google Scholar] [CrossRef]
- Kebande, V.R.; Venter, H.S. A cognitive approach for botnet detection using Artificial Immune System in the cloud. In Proceedings of the 2014 Third International Conference on Cyber Security, Cyber Warfare and Digital Forensic (CyberSec), Beirut, Lebanon, 29 April–1 May 2014; pp. 52–57. [Google Scholar]
- Da, K. A method for stochastic optimization. arXiv 2014, arXiv:1412.6980. [Google Scholar]
- Zeiler, M.D. Adadelta: An adaptive learning rate method. arXiv 2012, arXiv:1212.5701. [Google Scholar]
- Duchi, J.; Hazan, E.; Singer, Y. Adaptive subgradient methods for online learning and stochastic optimization. J. Mach. Learn. Res. 2011, 12, 2121–2159. [Google Scholar]
- Rauf, H.T.; Malik, S.; Shoaib, U.; Irfan, M.N.; Lali, M.I. Adaptive inertia weight Bat algorithm with Sugeno-Function fuzzy search. Appl. Soft Comput. 2020, 90, 106159. [Google Scholar] [CrossRef]
- Ullah, I.; Mahmoud, Q.H. A two-level flow-based anomalous activity detection system for IoT networks. Electronics 2020, 9, 530. [Google Scholar] [CrossRef]
- Dong, B.; Wang, X. Comparison deep learning method to traditional methods using for network intrusion detection. In Proceedings of the 2016 8th IEEE International Conference on Communication Software and Networks (ICCSN), Beijing, China, 4–6 June 2016; pp. 581–585. [Google Scholar]
- Folorunso, O.; Ayo, F.E.; Babalola, Y. Ca-NIDS: A network intrusion detection system using combinatorial algorithm approach. J. Inf. Priv. Secur. 2016, 12, 181–196. [Google Scholar] [CrossRef]
- Deng, L. A tutorial survey of architectures, algorithms, and applications for deep learning. APSIPA Trans. Signal Inf. Process. 2014, 3, e2. [Google Scholar] [CrossRef]
- Berman, D.S.; Buczak, A.L.; Chavis, J.S.; Corbett, C.L. A survey of deep learning methods for cyber security. Information 2019, 10, 122. [Google Scholar] [CrossRef]
- Yilmaz, S.; Sen, S. Early Detection of Botnet Activities Using Grammatical Evolution. In Applications of Evolutionary Computation; Springer International Publishing: Berlin/Heidelberg, Germany, 2019; pp. 395–404. [Google Scholar] [CrossRef]
- Yu, Y.; Long, J.; Liu, F.; Cai, Z. Machine learning combining with visualization for intrusion detection: A survey. In Proceedings of the International Conference on Modeling Decisions for Artificial Intelligence, Sant Julià de Lòria, Andorra, 19–21 September 2016; pp. 239–249. [Google Scholar]
- Ahmed, A.A.; Jabbar, W.A.; Sadiq, A.S.; Patel, H. Deep learning-based classification model for botnet attack detection. J. Ambient. Intell. Humaniz. Comput. 2020. [Google Scholar] [CrossRef]
- Alauthman, M.; Aslam, N.; Al-kasassbeh, M.; Khan, S.; Al-Qerem, A.; Raymond Choo, K. An efficient reinforcement learning-based Botnet detection approach. J. Netw. Comput. Appl. 2020, 150, 102479. [Google Scholar] [CrossRef]
- Mazini, M.; Shirazi, B.; Mahdavi, I. Anomaly network-based intrusion detection system using a reliable hybrid artificial bee colony and AdaBoost algorithms. J. King Saud Univ. Comput. Inf. Sci. 2019, 31, 541–553. [Google Scholar] [CrossRef]
- Asadi, M.; Jabraeil Jamali, M.A.; Parsa, S.; Majidnezhad, V. Detecting botnet by using particle swarm optimization algorithm based on voting system. Future Gener. Comput. Syst. 2020, 107, 95–111. [Google Scholar] [CrossRef]
- Al Shorman, A.; Faris, H.; Aljarah, I. Unsupervised intelligent system based on one class support vector machine and Grey Wolf optimization for IoT botnet detection. J. Ambient Intell. Humaniz. Comput. 2020, 11, 2809–2825. [Google Scholar] [CrossRef]
- Lin, K.C.; Chen, S.Y.; Hung, J.C. Botnet Detection Using Support Vector Machines with Artificial Fish Swarm Algorithm. J. Appl. Math. 2014, 2014, 1–9. [Google Scholar] [CrossRef]
- Rajagopal, S.; Kundapur, P.P.; Hareesha, K.S. A stacking ensemble for network intrusion detection using heterogeneous datasets. Secur. Commun. Netw. 2020, 2020, 4586875. [Google Scholar] [CrossRef]
- Elmasry, W.; Akbulut, A.; Zaim, A.H. Evolving deep learning architectures for network intrusion detection using a double PSO metaheuristic. Comput. Netw. 2020, 168, 107042. [Google Scholar] [CrossRef]
- Dwivedi, S.; Vardhan, M.; Tripathi, S. Defense against distributed DoS attack detection by using intelligent evolutionary algorithm. Int. J. Comput. Appl. 2020, 1–11. [Google Scholar] [CrossRef]
- Suhaimi, H.; Suliman, S.I.; Musirin, I.; Harun, A.; Mohamad, R.; Kassim, M.; Shahbudin, S. Network intrusion detection system using immune-genetic algorithm (IGA). Indones. J. Electr. Eng. Comput. Sci. 2020, 17, 1059–1065. [Google Scholar] [CrossRef][Green Version]
- Zhou, Y.; Mazzuchi, T.A.; Sarkani, S. M-AdaBoost—A based ensemble system for network intrusion detection. Expert Syst. Appl. 2020, 162, 113864. [Google Scholar] [CrossRef]
- Wu, Z.; Wang, J.; Hu, L.; Zhang, Z.; Wu, H. A network intrusion detection method based on semantic re-encoding and deep learning. J. Netw. Comput. Appl. 2020, 164, 102688. [Google Scholar] [CrossRef]
- Injadat, M.; Moubayed, A.; Nassif, A.B.; Shami, A. Multi-Stage Optimized Machine Learning Framework for Network Intrusion Detection. IEEE Trans. Netw. Serv. Manag. 2020. [Google Scholar] [CrossRef]
- Almomani, O. A Feature Selection Model for Network Intrusion Detection System Based on PSO, GWO, FFA and GA Algorithms. Symmetry 2020, 12, 1046. [Google Scholar] [CrossRef]
- Ahmad, Z.; Khan, A.S.; Shiang, C.W.; Abdullah, J.; Ahmad, F. Network intrusion detection system: A systematic study of machine learning and deep learning approaches. Trans. Emerg. Telecommun. Technol. 2020, 32. [Google Scholar] [CrossRef]
- Li, X.; Yi, P.; Wei, W.; Jiang, Y.; Tian, L. LNNLS-KH: A Feature Selection Method for Network Intrusion Detection. Secur. Commun. Netw. 2021, 2021, 8830431. [Google Scholar] [CrossRef]
- Selvakumar, B.; Muneeswaran, K. Firefly algorithm based feature selection for network intrusion detection. Comput. Secur. 2019, 81, 148–155. [Google Scholar] [CrossRef]
- Dong, Q.L.; He, S.N. Self-adaptive projection algorithms for solving the split equality problems. Fixed Point Theory 2017, 18, 191–202. [Google Scholar] [CrossRef]
- Sakr, M.M.; Tawfeeq, M.A.; El-Sisi, A.B. Network Intrusion Detection System based PSO-SVM for Cloud Computing. Int. J. Comput. Netw. Inf. Secur. 2019, 11, 22–29. [Google Scholar] [CrossRef]
- Salo, F.; Nassif, A.B.; Essex, A. Dimensionality reduction with IG-PCA and ensemble classifier for network intrusion detection. Comput. Netw. 2019, 148, 164–175. [Google Scholar] [CrossRef]
- Deng, L.; Li, D.; Yao, X.; Wang, H. RETRACTED ARTICLE: Mobile network intrusion detection for IoT system based on transfer learning algorithm. Clust. Comput. 2018, 22, 9889–9904. [Google Scholar] [CrossRef]
- Devan, P.; Khare, N. An efficient XGBoost–DNN-based classification model for network intrusion detection system. Neural Comput. Appl. 2020, 32, 12499–12514. [Google Scholar] [CrossRef]
- Magán-Carrión, R.; Urda, D.; Díaz-Cano, I.; Dorronsoro, B. Towards a Reliable Comparison and Evaluation of Network Intrusion Detection Systems Based on Machine Learning Approaches. Appl. Sci. 2020, 10, 1775. [Google Scholar] [CrossRef]
- Hajisalem, V.; Babaie, S. A hybrid intrusion detection system based on ABC-AFS algorithm for misuse and anomaly detection. Comput. Netw. 2018, 136, 37–50. [Google Scholar] [CrossRef]
- Kim, J.; Shim, M.; Hong, S.; Shin, Y.; Choi, E. Intelligent detection of iot botnets using machine learning and deep learning. Appl. Sci. 2020, 10, 7009. [Google Scholar] [CrossRef]
- De La Torre Parra, G.; Rad, P.; Choo, K.R.; Beebe, N. Detecting Internet of Things attacks using distributed deep learning. J. Netw. Comput. Appl. 2020, 163, 102662. [Google Scholar] [CrossRef]
- Soe, Y.N.; Feng, Y.; Santosa, P.I.; Hartanto, R.; Sakurai, K. Machine learning-based IoT-botnet attack detection with sequential architecture. Sensors 2020, 20, 4372. [Google Scholar] [CrossRef]
- Hosseini, S.; Nezhad, A.E.; Seilani, H. Botnet detection using negative selection algorithm, convolution neural network and classification methods. Evol. Syst. 2021. [Google Scholar] [CrossRef]
- Krich, S.I.; Weiner, I. Low-Sidelobe Antenna Beamforming Via Stochastic Optimization. IEEE Trans. Antennas Propag. 2014, 62, 6482–6486. [Google Scholar] [CrossRef]
- Yang, X.S. A New Metaheuristic Bat-Inspired Algorithm. In Proceedings of the Nature Inspired Cooperative Strategies for Optimization (NICSO 2010), Granada, Spain, 12–14 May 2010; Springer: Berlin/Heidelberg, Germany, 2010; pp. 65–74. [Google Scholar] [CrossRef]
- Meidan, Y.; Bohadana, M.; Mathov, Y.; Mirsky, Y.; Shabtai, A.; Breitenbacher, D.; Elovici, Y. N-BaIoT: Network-based Detection of IoT Botnet Attacks Using Deep Autoencoders. IEEE Pervasive Comput. 2018, 17, 12–22. [Google Scholar] [CrossRef]
| Ref | Data-Set | Methods | Evaluation Metrics | Accuracy |
|---|---|---|---|---|
| [44] | UNSW NB-15 | Ensemble approach using concept of stacking | Accuracy, recall, and precision | Gained 97% accuracy |
| [45] | Two common IDS data sets | Double Particle Swarm Optimization (PSO)-based algorithm | Accuracy, recall, precision, specificity | Increased DR by 4% to 6% |
| [46] | KDD Cup 99 and CIC-IDS 2017 | GOIDS | AUC, specificity, false-positive rate | Low false- positive rate. |
| [47] | Own collected | Immune Genetic Algorithm | Average standard deviation | 85% of prediction accuracy |
| [48] | AWID data | M-AdaBoost-A | TPR/FPR, macro precision | Showed highly accurate results |
| [49] | NSL-KDD | SRDLM | Accuracy, precision, recall, F1 | Attack detection over 99% |
| [50] | CICIDS 2017 | Multi-stage optimized ML-based NIDS | Accuracy, precision, recall /TPR, FAR/FPR | Detection accuracy over 99% |
| [51] | UNSW-NB15 | Feature selection model for NIDSs | TPR, TNR, FPR, FNR, accuracy, precision | Showed highly accurate results |
| [52] | CSE-CIC-IDS2018 | ML and DL-based NIDS. | Accuracy, precision, recall, FAR, TNR | Gained promising results |
| [53] | CICIDS2017, NSL-KDD | LNNLS-KH | FPR, DR | Ensured high detection accuracy |
| [54] | KDD CUP 99 | Data mining-based IDS | DR, FPR | Showed improved accuracy |
| [40] | NSL-KDD and ISCXIDS2012 | Anomaly network-based IDS (A-NIDS) | TP, FP, FN, TN | Gained enhanced detection accuracy |
| [55] | KDDTest + | Improved convolutional neural network (ICNN) | AC, TPR, FPR | Higher recall rate and lower FPR |
| [56] | NSL-KDD | Network intrusion detection system (NIDS) | FPR, FNR, TPR, TNR | Low false alarm rates (FARs) |
| [57] | ISCX 2012, and Kyoto 2006+. | Hybrid dimensionality reduction technique | AC, DR FAR, precision, F-measure | Gained enhanced detection accuracy |
| [58] | Public data sets | IoT-based IDS | FPR and DR | Obtained satisfactory results |
| [59] | NSL-KDD | XGBoost–DNN model | Recall, accuracy, precision | Showed useful outcomes |
| [60] | UGR’16 | ML-based NIDS | F1, precision, recall | Proved suitable for NID problems |
| [61] | NSL-KDD and UNSW-NB15 | Hybrid IDS | DA, DR, FNR, FPR, FAR | 0.01% FPR |
| [62] | N-BaIoT | CNN, RNN, and LSTM | F1 | 0.87 for 4 types of attack |
| [63] | PhishTank, OpenPhish, Curlie, N-BaIoT | Temporal LSTM | F1, accuracy | 94.80% accuracy |
| [64] | N-BaIoT | ANN, J48, Naïve Bayes | Accuracy | 99% |
| [65] | ISOT, ISCX | Artificial Immune System | Accuracy | 0.99 |
| Sr# | Target Class | Number of Instances |
|---|---|---|
| 1 | Mirai udpplain | 15,304 |
| 2 | Mirai udp | 15,625 |
| 3 | Mirai syn | 16,436 |
| 4 | Mirai scan | 14,517 |
| 5 | Mirai ack | 15,138 |
| 6 | Gafgyt udp | 15,602 |
| 7 | Gafgyt tcp | 15,676 |
| 8 | Gafgyt scan | 14,648 |
| 9 | Gafgyt junk | 15,449 |
| 10 | Gafgyt combo | 15,345 |
| 11 | Benign | 15,538 |
| 12 | Total | 7,062,606 |
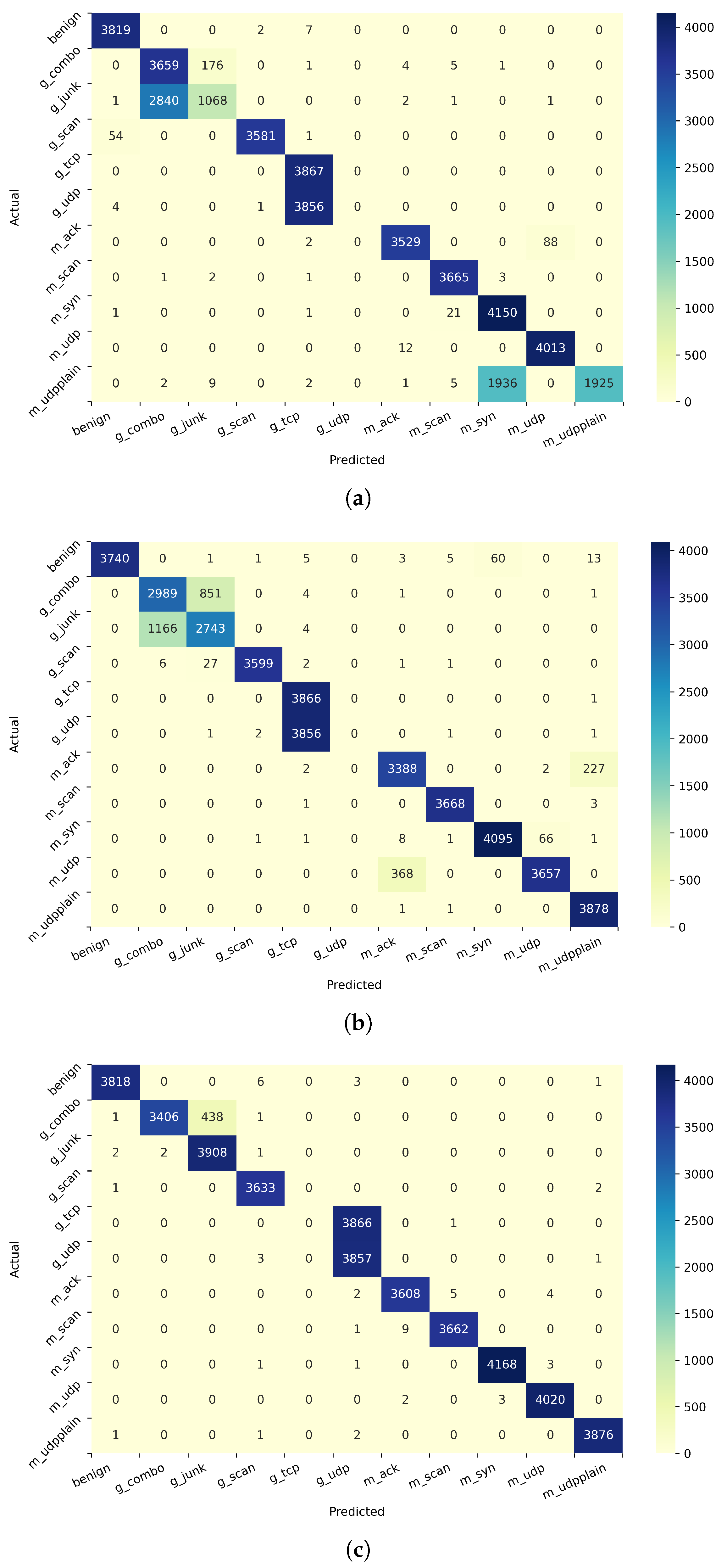
| Attack Type | Precision | Recall | F1-Score | Support |
|---|---|---|---|---|
| Benign | 0.9957 | 0.9724 | 0.9839 | 3882 |
| Gafgyt_combo | 0 | 0 | 0 | 3787 |
| Gafgyt_junk | 0.4977 | 0.9966 | 0.663898 | 3850 |
| Gafgyt_scan | 0.9975 | 0.9791 | 0.9882 | 3700 |
| Gafgyt_tcp | 0 | 0 | 0 | 3892 |
| Gafgyt_udp | 0.5089 | 0.9990 | 0.6743 | 4044 |
| Mirai_ack | 0.9974 | 0.3173 | 0.4814 | 3766 |
| Mirai_scan | 0.9806 | 0.9930 | 0.9868 | 3614 |
| Mirai_syn | 0.9885 | 0.9955 | 0.992068 | 4083 |
| Mirai_udp | 0.6545 | 0.9992 | 0.7909 | 3861 |
| Mirai_udpplain | 0.8714 | 0.9903 | 0.9271 | 3841 |
| Average | 0.6791 | 0.7510 | 0.6806 | 42,320 |
| Attack Type | Precision | Recall | F1-Score | Support |
|---|---|---|---|---|
| Benign | 0.9845 | 0.9976 | 0.9910 | 3828 |
| Gafgyt_combo | 0.5627 | 0.9513 | 0.7071 | 3846 |
| Gafgyt_junk | 0.8509 | 0.2729 | 0.4133 | 3913 |
| Gafgyt_scan | 0.9991 | 0.9848 | 0.9919 | 3636 |
| Gafgyt_tcp | 0.4997 | 1 | 0.666437 | 3867 |
| Gafgyt_udp | 0 | 0 | 0 | 3861 |
| Mirai_ack | 0.9946 | 0.9751 | 0.9847 | 3619 |
| Mirai_scan | 0.9913 | 0.9980 | 0.9947 | 3672 |
| Mirai_syn | 0.6814 | 0.9944 | 0.8087 | 4173 |
| Mirai_udp | 0.9783 | 0.9970 | 0.9875 | 4025 |
| Mirai_udpplain | 1 | 0.4961 | 0.663221 | 3880 |
| Average | 0.7733 | 0.7862 | 0.7432 | 42,320 |
| Attack Type | Precision | Recall | F1-Score | Support |
|---|---|---|---|---|
| Benign | 0.9856 | 0.9977 | 0.9916 | 3919 |
| Gafgyt_combo | 0 | 0 | 0 | 3854 |
| Gafgyt_junk | 0.4959 | 0.9984 | 0.662748 | 3840 |
| Gafgyt_scan | 0.9991 | 0.9866 | 0.9928 | 3594 |
| Gafgyt_tcp | 0.4908 | 1 | 0.658513 | 3823 |
| Gafgyt_udp | 0 | 0 | 0 | 3954 |
| Mirai_ack | 0.9676 | 0.9674 | 0.9675 | 3805 |
| Mirai_scan | 0.9994 | 1 | 0.999724 | 3628 |
| Mirai_syn | 1 | 0.9990 | 0.999523 | 4192 |
| Mirai_udp | 0.9921 | 0.9687 | 0.9803 | 3907 |
| Mirai_udpplain | 0.9877 | 0.9994 | 0.9935 | 3804 |
| Average | 0.7175 | 0.8080 | 0.7472 | 42,320 |
| Attack Type | Precision | Recall | F1-Score | Support |
|---|---|---|---|---|
| Benign | 1 | 0.9770 | 0.988372 | 3828 |
| Gafgyt_combo | 0.7183 | 0.7771 | 0.7465 | 3846 |
| Gafgyt_junk | 0.7571 | 0.7009 | 0.7279 | 3913 |
| Gafgyt_scan | 0.9988 | 0.9898 | 0.994336 | 3636 |
| Gafgyt_tcp | 0.4994 | 0.9997 | 0.6660 | 3867 |
| Gafgyt_udp | 0 | 0 | 0 | 3861 |
| Mirai_ack | 0.8986 | 0.9361 | 0.917039 | 3619 |
| Mirai_scan | 0.9975 | 0.9989 | 0.9982 | 3672 |
| Mirai_syn | 0.9855 | 0.98130 | 0.9834 | 4173 |
| Mirai_udp | 0.9817 | 0.9085 | 0.9437 | 4025 |
| Mirai_udpplain | 0.9401 | 0.9994 | 0.9688 | 3880 |
| Average | 0.7973 | 0.8417 | 0.8114 | 42,320 |
| Attack Type | Precision | Recall | F1-Score | Support |
|---|---|---|---|---|
| Benign | 0.987098 | 0.997699 | 0.99237 | 3911 |
| Gafgyt_combo | 0.989165 | 0.576276 | 0.72827 | 3802 |
| Gafgyt_junk | 0.705972 | 0.986229 | 0.822892 | 3776 |
| Gafgyt_scan | 0.942328 | 0.971896 | 0.956884 | 3665 |
| Gafgyt_tcp | 0 | 0 | 0 | 3903 |
| Gafgyt_udp | 0.498015 | 0.999486 | 0.664786 | 3891 |
| Mirai_ack | 0.967891 | 0.993147 | 0.980356 | 3794 |
| Mirai_scan | 0.974434 | 0.999727 | 0.986918 | 3660 |
| Mirai_syn | 0.979914 | 0.989377 | 0.984623 | 4142 |
| Mirai_udp | 0.999735 | 0.967444 | 0.983325 | 3901 |
| Mirai_udpplain | 0.993208 | 0.943484 | 0.967708 | 3875 |
| Average | 0.820524 | 0.855931 | 0.823409 | 42,320 |
| Attack Type | Precision | Recall | F1-Score | Support |
|---|---|---|---|---|
| Benign | 0.999741 | 0.987983 | 0.993827 | 3911 |
| Gafgyt_combo | 0.989529 | 0.546817 | 0.704388 | 3802 |
| Gafgyt_junk | 0.692265 | 0.981197 | 0.811788 | 3776 |
| Gafgyt_scan | 0.998088 | 0.997271 | 0.99768 | 3665 |
| Gafgyt_tcp | 0.498722 | 0.999744 | 0.665473 | 3903 |
| Gafgyt_udp | 0 | 0 | 0 | 3891 |
| Mirai_ack | 0.925917 | 0.991566 | 0.957617 | 3794 |
| Mirai_scan | 0.955103 | 0.999727 | 0.976906 | 3660 |
| Mirai_syn | 0.970912 | 0.958957 | 0.964897 | 4142 |
| Mirai_udp | 0.997233 | 0.923866 | 0.959148 | 3901 |
| Mirai_udpplain | 0.989022 | 0.999742 | 0.994353 | 3875 |
| Average | 0.818607 | 0.852457 | 0.819568 | 42,320 |
| Attack Type | Precision | Recall | F1-Score | Support |
|---|---|---|---|---|
| Benign | 0.9986 | 0.9973 | 0.9980 | 3828 |
| Gafgyt_combo | 0.9994 | 0.8855 | 0.9390 | 3846 |
| Gafgyt_junk | 0.8992 | 0.9987 | 0.9463 | 3913 |
| Gafgyt_scan | 0.9964 | 0.9991 | 0.9978 | 3636 |
| Gafgyt_tcp | 0 | 0 | 0 | 3867 |
| Gafgyt_udp | 0.4988 | 0.9989 | 0.6654 | 3861 |
| Mirai_ack | 0.9969 | 0.9969 | 0.99696 | 3619 |
| Mirai_scan | 0.9983 | 0.9972 | 0.9978 | 3672 |
| Mirai_syn | 0.9992 | 0.9988 | 0.9990 | 4173 |
| Mirai_udp | 0.9982 | 0.9987 | 0.9985 | 4025 |
| Mirai_udpplain | 0.9989 | 0.9989 | 0.9989 | 3880 |
| Average | 0.8523 | 0.9 | 0.8664 | 42,320 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alharbi, A.; Alosaimi, W.; Alyami, H.; Rauf, H.T.; Damaševičius, R. Botnet Attack Detection Using Local Global Best Bat Algorithm for Industrial Internet of Things. Electronics 2021, 10, 1341. https://doi.org/10.3390/electronics10111341
Alharbi A, Alosaimi W, Alyami H, Rauf HT, Damaševičius R. Botnet Attack Detection Using Local Global Best Bat Algorithm for Industrial Internet of Things. Electronics. 2021; 10(11):1341. https://doi.org/10.3390/electronics10111341
Chicago/Turabian StyleAlharbi, Abdullah, Wael Alosaimi, Hashem Alyami, Hafiz Tayyab Rauf, and Robertas Damaševičius. 2021. "Botnet Attack Detection Using Local Global Best Bat Algorithm for Industrial Internet of Things" Electronics 10, no. 11: 1341. https://doi.org/10.3390/electronics10111341
APA StyleAlharbi, A., Alosaimi, W., Alyami, H., Rauf, H. T., & Damaševičius, R. (2021). Botnet Attack Detection Using Local Global Best Bat Algorithm for Industrial Internet of Things. Electronics, 10(11), 1341. https://doi.org/10.3390/electronics10111341







