1. Introduction
Many people are seriously injured or killed in road traffic accidents due to carelessness, traffic congestion, traffic violations, inadequate road information, increased population and lack of secure infrastructure. Therefore, reducing traffic congestion and enhancing road safety are the issues that many people are most concerned about. With the development of automotive technology and wireless communication technology, VANETs have aroused widespread interest. In VANET, smart vehicles equipped with the on-board device can be connected to each other and surrounding infrastructures easily [
1]. Any vehicle can send other nearby vehicles about the traffic and road conditions to warn of potential emergencies and traffic jams. In addition to helping prevent accidents, VANETs also provide convenience and business services that will help improve a driver’s experience [
2].
However, before taking this wonderful application into practice, several obstacles in VANETS need to be addressed: delay, service cost, security and privacy. It is worthwhile noting that security and privacy issues are becoming more and more import in many people’s lives [
3]. So far, the security issues of VANETs have been studied in detail, while the privacy issues still have many open questions [
4,
5,
6]. In the absence of privacy protection, the adversary can track the location of the target vehicle by collecting their routine information. Even worse, if a legitimate anonymous vehicle becomes malicious, there is no way to identify and revoke it. Thus, it is necessary to limit malicious vehicles, the privacy protection must be conditional for the vehicles which are able to be tracked and revoked if need. In addition, high mobility of vehicles and frequently changed topology are the other important characteristic of the vehicular network. Therefore, it is very challenging to design an efficient privacy preserving anonymous authentication scheme for VANETs.
In the past few years, many secure VANET schemes have been proposed, but there are still some unsolved problems. In [
7], it is stated that distributing and searching of a huge certificate revocation list (CRL) is inevitable. The overhead of authentication will increase linearly with the increase of CRLs. The higher overhead of identifying and revoking malicious vehicles makes group signature and identity-based signature (GSIS) [
8] and hybrid method [
9] unsuitable for real-time VANETs. Efficiency conditional privacy preservation (ECPP) [
10], proposed by Lu et al., is a relatively practical scheme which deals with the growing revocation list while achieving conditional traceability by the authorities, but it also suffers drawbacks: (1) It takes more latency time for sending and verifying the certificate and signature which are not efficient for the high speed movement of vehicles; (2) It needs large space to storage every vehicle’s temporary information to reveal the malicious vehicles when the tracking phases; (3) Vehicle will interact with infrastructure unit several times during short-time anonymous key generation.
To resolve these problems, we propose a more efficient conditional private preservation scheme based on ECPP. The main contributions of this paper include the following: (1) Reducing the storage space. When dispute occurs, the centralized Trusted Authority can decrypt the real identity of the rogue vehicles just by certification. So it does not need to storage temporary information, and that will save considerable storage space. (2) Lowering down half of the interaction steps during anonymous key generation phase. When vehicles move along the road, the speed is usually high, and it needs fast interaction. Fewer interaction steps help to increase the interaction speed (3) Decreasing the computational cost and communication overhead for sending and verifying the certificate and signature. The presented performance studies and comparisons with ECPP and other related schemes demonstrate that this scheme is effective and efficient.
The remainder of the paper is organized as follows. In
Section 2, the related work will be surveyed. In
Section 3, system model, desired requirements in VANETs will be described. We will also review the bilinear pairing techniques in
Section 4. The improved MECPP will be presented in
Section 5.
Section 6 will give security analysis about this protocol, followed by performance analysis in
Section 7. Finally, we conclude the paper in
Section 8. All the notations in the paper are defined in
Table 1.
2. Related Work
There have been many research works about anonymity authentication of VANETs in the last past years. In all existing works, pseudonym-based authentication schemes are the major approaches [
6,
7,
11,
12]. These pseudonym-based approaches can perfectly achieve privacy preservation, but the main limitation is that the TA is needed to keep the pseudonyms of each vehicle in storage space and required to change them in a frequent manner. To overcome this limitation, Ye et al. [
13] proposed a conditional privacy preserving authentication approach using anonymous certificates. However, it is not efficient because of frequent interactions with infrastructures. Lu et al. [
10] developed an efficient conditional privacy preservation scheme. This scheme can achieve perfect conditional privacy with bilinear pairing technology, but it still faces some limitation that takes more time with infrastructures and needs large storage space to save temporary messages.
Gamage et al. [
14] gave a privacy protection scheme for VANET based on an ID-based ring signature without tracking function, hence this scheme does not achieve conditional privacy. Then, Zhang et al. [
5] proposed another ID-based scheme named CPPA, but it is vulnerable to replay and non-repudiation attacks. To overcome the drawback of ID-based schemes, Shim improved a new efficient IBS scheme providing resistance against impersonation attack. However, it suffers to the modification attack which was demonstrated by Liu et al. [
15]. In 2015, Bayat et al. [
16] introduced an anonymous authentication scheme. High computational overhead is the main limitation of Bayat’s scheme. In 2018, Yang et al. [
4] proposed a message recovery authentication scheme based on certificateless signatures. This scheme achieves low communication costs and computation overhead without the bilinear pairing operations. However, this solution is one-way communication only from the vehicle to the RSU, and the vehicle cannot receive traffic information transmitted from the center.
Recently, Baker et al. [
17] proposed an energy efficient routing protocol for VANET, called GreeAODV, which focus on selecting the most efficient routing path between source and destination. It estimate the total power consumption and locate the lowest energy consumption route. In order to guarantee user satisfaction, a Trusted Third Party (TTP) cloud entity and Quality of Experience (QoE) game model has been proposed [
18]. TTPs, which provide an abstraction layer between the vehicular service users and providers, are well-known profitable commercial organizations that provide and sell service to users. TTPs thus will simplify the process of resource discovery and selection in a smart city. Based on a cluster-based Trusted Third Party (TTP) model, Ridhawi et al. [
19] propose a continuous availability scheme for diversified cloud services targeting vehicle cloud users. In this scheme, timely and successful receipt of information were used to reduce highway accidents by providing early warning messages to nearby and distant vehicles, thereby increasing response time to emergencies.
Other studies accessed the anomaly detection schemes which can be used for data analysis, monitoring the normal behavior of road-side infrastructures and protecting the vehicle from potential attack [
20]. Lazarevic et al. [
21] presented several anomaly detection schemes to identify possible network intrusions. Now black-hole attacks are one of the security threats that appear in the network. In [
22,
23], Otoum et al. gave a black-hole detection scheme which help in monitoring the different aspect of systems such as pressure and temperature. Very recently, Otoum et al. [
24] introduced an adaptively supervised and intrusion-aware data aggregation for wireless sensor clusters in critical infrastructures. This proposed scheme used an adaptive strategy to dynamically detect known and unknown intrusions, thus solving the intrusion problem.
3. System Model and System Security
In this section, we demonstrate the system model and the requirements of system security.
3.1. System Model
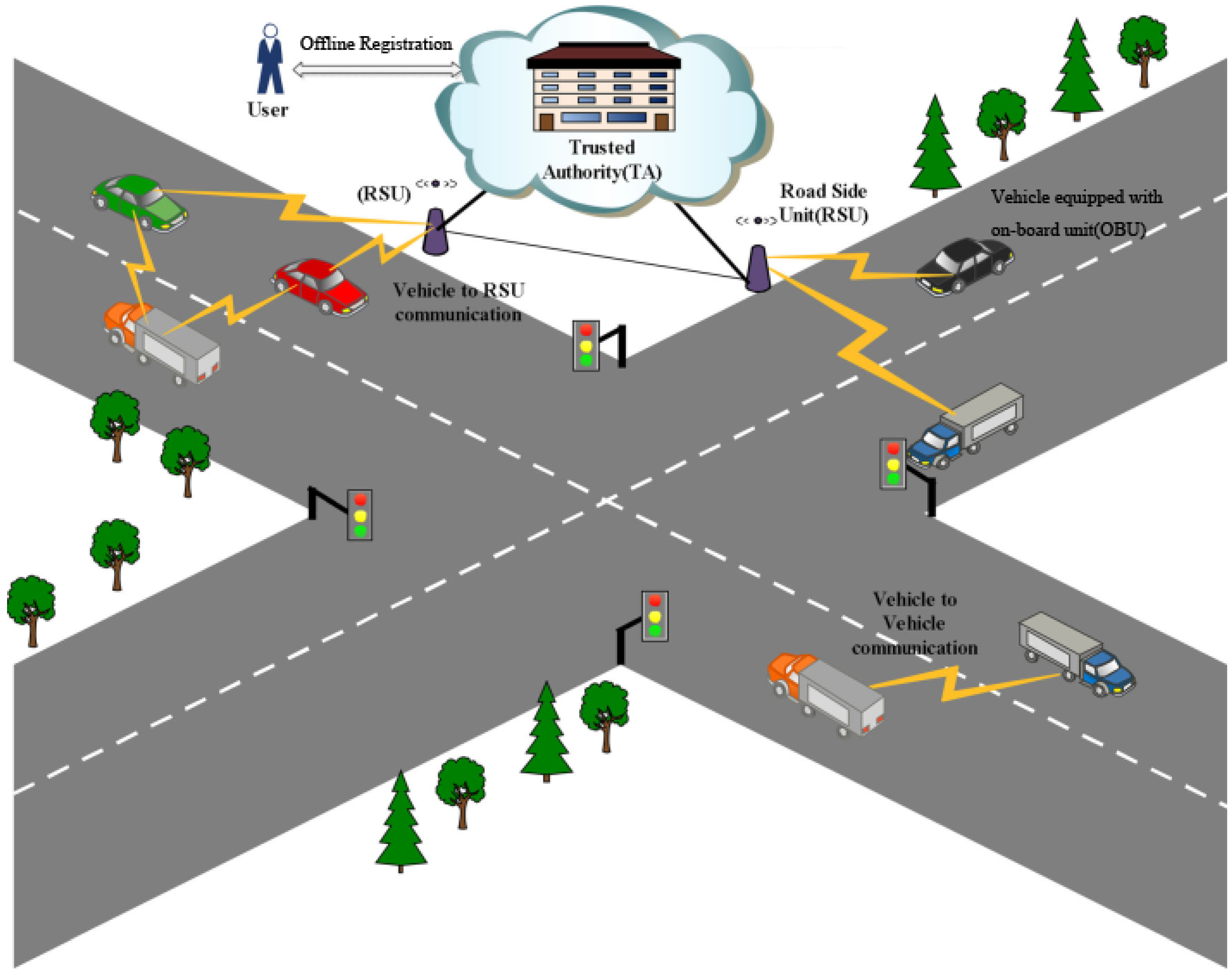
In this subsection, the system model of a single geographic region for the scheme is illustrated in
Figure 1.
System roles: VANETs generally consist of vehicles equipped with wireless communication devices, which are called On Board Unit (OBU), infrastructure units such as Road Side Units (RSUs) which are located on the roadside or at a street intersection providing wireless interfaces to vehicles within their radio coverage, and a centralized Trusted Authority (TA) which is responsible for the RSU and OBU Registration, and what is more, recovering the vehicle’s identity if it is necessary.
Channels: To secure the vehicular communications which are mainly used for civilian applications, we have been following assumptions about the channels:
OBU communicates with RSU or other OBU through wireless links, which is unsecured.
RSU is assumed to connect with the TA by wired links or any other creditable links with high bandwidth, low bit error rates and low delay.
3.2. System Security
In this subsection, we present the system assumption and the desired requirements for the proposed protocol.
3.2.1. Secure VANETs Assumption
All OBUs and RSUs are registered with the TA. The TA is not feasible to be compromised in the system and can be fully trusted by all parties.
RSUs are usually deployed in open unattended environments, which can be compromised by attackers or collude with each other. However, we assume that RSUs are monitored so that their compromise can be detected in a short time. As a result, at a given time slot, very few RSUs are compromised.
OBUs have limited computing power and storage space while TAs have greater computational power and enough hardware.
3.2.2. Desired Requirements
Anonymous Vehicle Authentication. The purpose of anonymous vehicle authentication is to verify a vehicle’s authentic and legitimate while without revealing the real ID of the vehicle.
Short-term Linkability. In some cases, like broadcasting road condition, applications require that a recipient can link two messages sent out by the same OBU in the short-term.
Long-term Unlinkability. In the long-term, messages from the same vehicle should not be able to be linked by attackers or eavesdroppers.
Traceability and Revocation. There must be a TA in VANETs which can trace the OBU that abuses the VANET. In addition, once the compromised OBU has been revealed, TA must revoke it immediately to prevent any further damage.
Non-repudiation. Both OBUs and RSUs should not deny their behaviors and must be responsible for the decision.
Efficiency. On the one hand, OBUs have resource-limited computing power to make VANETs economically viable. On the other hand, OBUs may move with the high speed. Suppose the application incorporates emergency information to be transferring to another vehicle, which has more probabilities to meet accident. This needs a quick response from the network to pass the information. A delay less than a second may cause severe damage and result in meaningless message. Therefore, the computation overhead and communication overhead at each vehicle must be as small as possible.
4. Preliminaries
Before presenting the scheme, we first review the pairing technique, state the definitions of the q-SDH assumption and weak chosen message attack.
4.1. Bilinear Pairing
Let
,
be the finite additive groups and
be the finite multiplicative group with same order
p where
, the bilinear pairing
satisfies the following properties [
25]:
Bilinearity: The mapping is said to be bilinear if the following relation holds: , , and .
Non-degeneracy: There exists such that is not the identity of .
Isomorphism: is an isomorphism from to , with
Computability: The bilinear map can be computed efficiently.
4.2. The Strong Diffie–Hellman Assumption
In this subsection, we state the strong Diffie–Hellman hardness assumption on which this scheme is based. Let be a generator of cyclic groups and be a generator of cyclic groups . and have the same prime order p.
q-Strong Diffie–Hellman Problem (q-SDH). Given a
-tuple
as input, output a pair
where
. An algorithm
A is said to have an advantage
in solving
q-SDH problem if
where the probability is over the random choice of
x in
and the random bits consumed by
A.
Definition 1. We say that the(q, t, ε)-SDH assumption holds in if no t-time algorithm has an advantage at least ε in solving the q-SDH problem in .
4.3. Weak Chosen Message Attacks
In this paper, we will prove the scheme existential unforgeability under a weak chosen message attack [
26], which need the adversary to submit all messages in advance and then are provided the public key and signatures. This notion is defined using the following game between a challenger and adversary
A:
Query: A list of messages were sent to challenger by the adversary A.
Response: The challenger runs algorithm to generate a public key and private key and then give A the public key and signatures for .
Output: Algorithm A wins the game if a pair is output, where:
M is not in , and
Definition 2. A forger -weakly breaks a signature scheme if A runs in time at most t, A makes at most signature queries, and has an advantage at least ε. A signature scheme is -existentially unforgeable under a weak chosen message attack if no forger -weakly breaks it.
5. The Improved More Efficient Protocol
The MECPP protocol includes four parts: system initialization, temporary anonymous key generation, safe message sending, and fast tracking algorithm.
5.1. System Initialization
First of all, The TA generates the system parameters for each and vehicle using the security parameter k. Then, it chooses a random number as its master key and computes as its public key. In addition, it selects two secure hash functions: f and h, where , and a secure symmetric encryption algorithm . Finally, TA publishes all public parameters .
5.1.1. OBU Registration Protocol
When an OBU register to the system with its identity , TA does the following:
Check the validity of the identity . If not valid, terminate the protocol;
Choose a fixed-length random number , compute the pseudo-id ;
Set .
Return to OBU the private key .
5.1.2. RSU Registration Protocol
When an RSU applies for registering, TA does:
Get a location information such that mod p, set ;
Return to RSU the location-awareness key , where the location-awareness key means it working at location ;
Subsequently, RSU itself picks a random number as the secret key which is used to encrypt OBU’s pseudo-id.
5.2. Temporary Anonymous Key Generation
In this part, we will describe how to generate the OBU temporary anonymous key.
Based on ECPP, we propose an improved protocol. First of all, the temporary anonymous information of OBU does not have to be stored by RSU. After mutual authentication, a random pseudo-id of OBU is generated by RSU, which is contained in the temporary certificate. When a dispute occurs, the real identity of the malicious vehicles could be recovered from temporary certification by RSU and TA together. The temporary anonymous key will be changed frequently. Therefore, that will help to save large storage spaces. Secondly, the interaction rounds are decreased to three times on the premise of mutual authentication in the scheme, while six times in ECPP. Because only valid RSU at location can decrypt the cipher text to get the pseudo-id , there is no risk in disclosing its pseudo-id to an attacker. It is more practical in the real world with fewer interactions. Finally, computation overhead is reduced because of less pairing operation and less point multiplication.
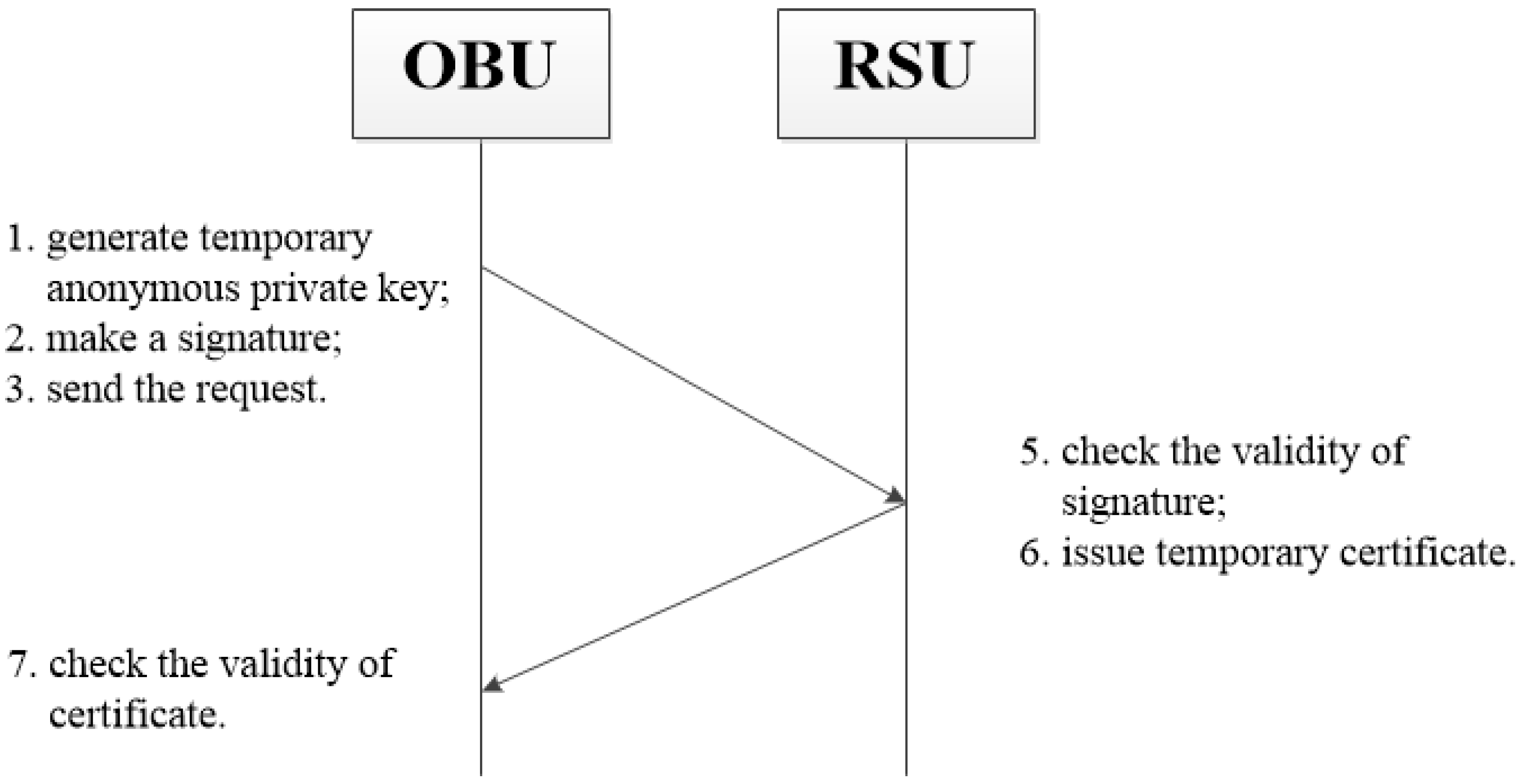
In
Figure 2, we describe the flowchart of temporary anonymous key generation. When the vehicle enters the area of the RSU, it firstly generates its temporary short-time anonymous private key. Then, the vehicle makes a signature as its proof and sends the request information to RSU. After receiving the request, the RSU checks the validity of signature at first. If it is valid, the OBU is authenticated. The RSU issues the temporary certificate and sends back to the vehicle. When receiving the certificate, the vehicle checks its validity. If valid, the RSU is also authenticated and the certificate is accepted. Next, we will give the detailed process of OBU temporary anonymous key generation in
Table 2.
Step 1. When an OBU goes into the location , it firstly computes and where is a random number. Then, the OBU chooses another random number as its temporary short-time anonymous private key, computes the corresponding temporary public key . At last, the OBU uses its private key to make a signature where is the current time-stamp, encrypts the signature as , and sends request information to the .
Step 2. After receiving the request,
computes
, and decrypts the cipher text
C with
. Then,
will check the validity of
and
. Either of them are invalid, the protocol aborts. Otherwise,
checks the equation
. If it holds, i.e., the OBU is authenticated, then
issues the certificate
, where
and
, the lifecycle of certification is based on time-stamp
; otherwise, the OBU fails the authentication since
Step 3. To verify
and the validity of certificate
, the OBU checks
. If it holds,
is valid and the RSU is also authenticated, because the adversary has no ability to recover the secret key
; Otherwise, the protocol aborts and the RSU cannot pass the authentication since
5.3. Safe Message Sending
5.4. Fast Tracking
Tracing operation is an essential issue for anonymous communication system. If a malicious vehicle makes a violation, the real identity of the signature should be revoked and transferred to the judiciary for punishment. When the TA receives the report:
step 1. The TA sends the tracing demand to the specified RSU according to the location information in .
step 2. The RSU returns the pseudo-id to TA by decrypting with security key .
step 3. The TA recovers the real identity by decrypting with master key u and then calculate . If , the and are valid and then broadcasts the pseudo-id to all RSUs. Then, the malicious vehicle cannot get temporary short-time anonymous key from the RSUs any more.
6. Security Analysis
In this section, we analyse the security of the proposed scheme. First, we will describe the provable security. Next we analyse more security requirements proposed in
Section 3.2.
6.1. Provable Security
1. Private Key Security. The TA use master key to allocate initial private keys to OBUs or RSUs during the registration stage. The security of private key is based on the
q-SDH [
27] hardness assumption. Even through several OBUs and RSUs are compromised, deducing the private keys of other OBUS and RSUs from the compromised private key is still computationally not feasible. It is still computationally not feasible to deduce other OBUs and RSUs’ private keys from the compromised private keys.
Lemma 1. If the q-SDH assumption holds in , then this scheme is secure against existential forgery under a chosen message attack.
Proof of Lemma 1. Assume A is a forger that -breaks the scheme and B is an attacker which solves the q-SDH problem in time with advantage by interacting with A. is an instance of the q-SDH problem, where for and for some unknown . For convenience, we set . Algorithm B’s goal is to produce a pair for some . It does so as follows:
Query: Algorithm A chooses a list of random pseudo-id , and requests for private key of , where . We may assume that .
Response:B must response with
’s public key and
’s private keys. Let
be the polynomial
. Expand
and write
where
. Compute:
Also, let
. The public key given to
A is
. Next, algorithm
B will generate private keys
for each
where
. To do so, let
be the polynomial
. We expand and write
. Compute
Observe that is a valid private key of under the public key . Algorithm B gives the private keys to A.
Output: Algorithm
A returns a forgery
such that
is a valid private key for
and
. In other words,
. Since
, we have that
and therefore
Using long division, we expand the polynomial
f as
for some polynimal
and some
. Then, computing as
Note that
, since
and
, as thus
does not divide
. Then, algorithm
B computes
and returns
as the solution to the
instance. ☐
2. Signature Security. The security of OBU’s signature is based on the discrete logarithm assumption. it is not feasible to output a forgery in polynomial time, which makes the scheme resistive to the impersonation attack and the bogus message spoofing attack.
Lemma 2. If the discrete logarithm assumption holds, then the signature is secure against existential forgery under an adaptively chosen message attack.
Proof of Lemma 2. We suppose that
A which is an adversary taking message
M and public key
Y as input has a non-negligible probability to output an existential forgery in polynomial time. Then,
A can get two forgeries for the same message according to the forking lemma [
28]. Let
and
are the two signature forgeries, respectively, where
mod
p and
mod
p. Then, we have the following equation.
As can be seen from the above, x can be computed successfully, but it contradicts the discrete logarithm assumption. Therefore, is difficult to be forged. ☐
6.2. Further Security Analysis of The Proposed Scheme
1. Mutual Authentication. The scheme realizes mutual authentication between the RSU and the OBU by the request-response protocol.
The RSU can quickly authenticate the OBU. In Step 2 of
Section 5.2, if the verification equation
holds, the OBU can be authenticated with pseudo-id
. Since the private key is secure according to
Lemma 1, therefore,
is unforgeable, and no adversary can launch an impersonation’s attack on the RSU.
The OBU can also efficiently authenticate the RSU at location . In Step 3 of
Section 5.2, if the equation
holds, the RSU is authenticated. Because the adversary is not feasible to recover the correct
without knowing the RSU’s private key
.
2. Anonymous Vehicle Authentication. The OBU’s identity can be kept perfectly anonymous in this protocol, since the real ID of OBU is not known to the RSU and other vehicles except the TA.
When the OBU requests for a short-time anonymous key, it sends to RSU the pseudo-id which is a random identity mark, and RSU does not know which it is.
When OBUs communicate each other, OBU uses a random pseudo-id to denote the identity, it is different with time going by and it has no means to other OBUs.
3. Short-term Linkability. Since the anonymous key is valid for a short time interval, any message signed by that key can be linked.
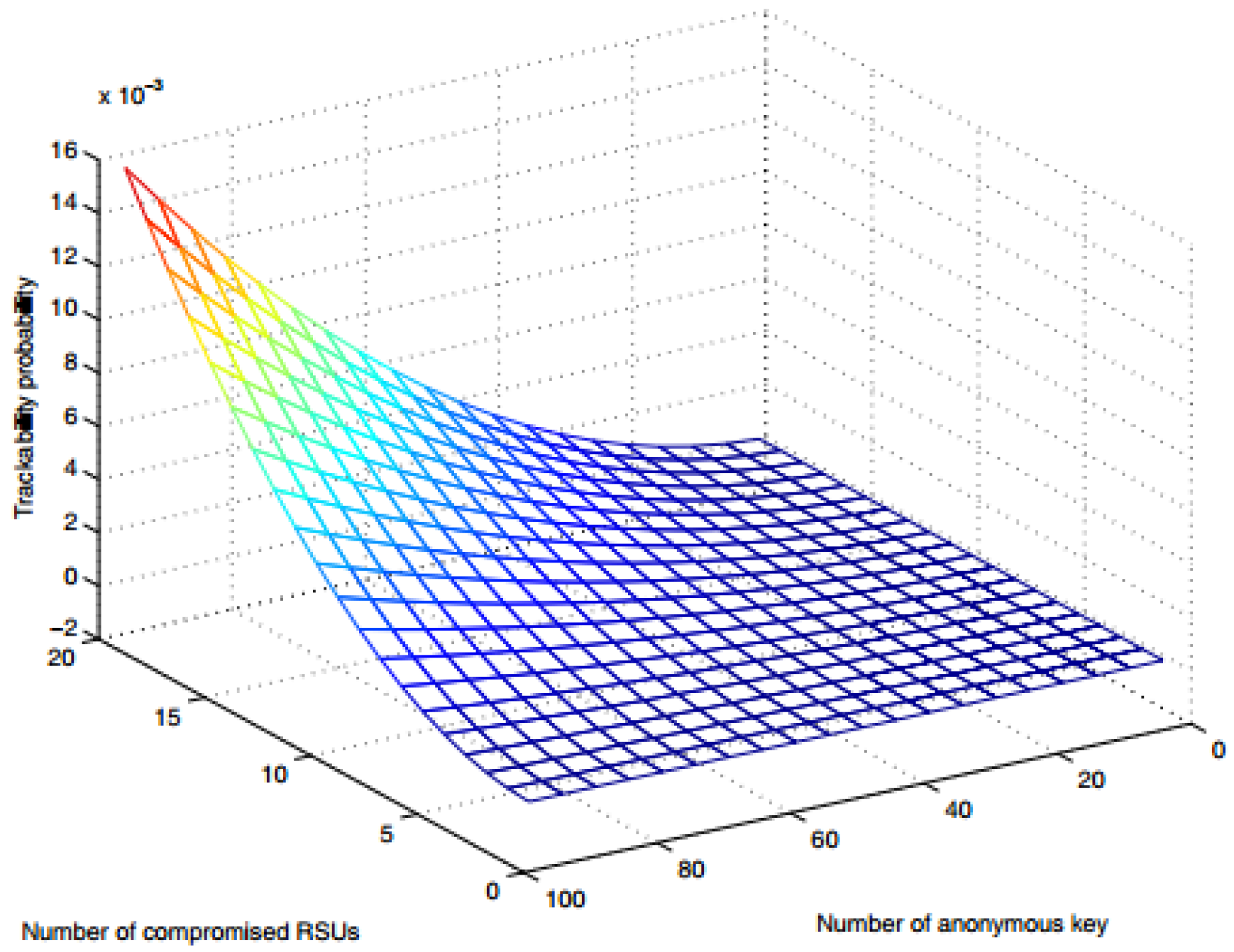
4. Long-term Unlinkability. In order to protect the privacy of the driver, we require that the information sent by the same vehicle be unlinkable in the long-term. We calculate the probability to quantify the risk that the victim OBU is tracked by some compromised RSUs. Here, we give some assumptions:
The RSUs may be compromised because of the insecure environment, but will be quickly rescued in the next period. We assume that the number of RSUs is , and that RSUs can be compromised. Then, the number of compromised RSUs is .
We assume that the number of anonymous keys that an OBU requests at some period is .
Let
represent the probability that exactly
i (
) among
anonymous keys are requested from different compromised RSUs, we have
. Then, the probability is
From
Figure 3 below, it can be seen that the tracking probability increases very slowly with the increase of the number of anonymous keys and the number of compromised RSUs. So it is long-term unlinkability.
6. Traceability. Even if the message does not contain identifying information about vehicles, by using the Fast Tracking algorithm described in
Section 5.4, the TA can recover the real identity of the malicious vehicle if required.
7. Non-repudiation. It is obvious that signature of OBU can provide the non-repudiation proof on the OBU’s temporary anonymous key requesting, while signature of RSU provide the non-repudiation proof on cert issue.
7. Performance Analysis
In this section, we compare the performance of the proposed protocol with other related schemes in terms of computational cost, communication overheads and storage overhead. To measure the effectiveness of the proposed scheme, we present the comparison results in different tables.
7.1. Computational Cost Analysis
We evaluate the computational cost for anonymous certificate and signature verification process with the prior related schemes such as ECPP [
10], Boneh Lynn Shacham (BLS) scheme [
29], group signature based (GSB) scheme [
8], certificateless aggregate signatures (CAS) [
30] and key-insulated pseudonym self delegation (KPSD) scheme [
31]. To facilitate analysis, the using notations are given in
Table 3, and the result was obtained on a 2.6-GHz computer with 8-GB installed memory, running Cygwin 1.7.35-15 [
32] with the gcc version 4.9.2 for the implementations.
The results of computation cost comparisons with ECPP, BLS, GSB, CAS, KPSD schemes are summarized in
Table 4. From
Table 4, it can be clearly observed that the proposed MECCP scheme takes less computational cost than others, because it takes only
,
and
for verifying a certificate and signature. Especially comparing with ECPP, the required execution time has been decreased by about
.
7.2. Communication Overheads Analysis
In this section, we discuss the communication cost of the proposed scheme with ECPP. To facilitate comparisons, we assume that the bit length of random number and time stamp are 4 bytes, the bit length of ID and PID are 20 bytes, the bit length of the elements in
and
are 20 bytes. Furthermore, assume that the bit length of the signature messages are all the same. In
Table 5, we summarize the communication overhead of sending the signature message between the proposed scheme and ECPP.
In the proposed scheme, the total size of the signature message is 20 + 4 + 20 + 4 + 20 + 20 + 20 = 108 bytes where , while the size of the signature message in ECPP is 24 + 20 + 4 + 20 + 20 + 20 + 4 + 4 + 4 = 120 bytes where .
Besides, the interaction steps during temporary anonymous key generation phase is three times while ECPP is six times.
From the analysis of communication cost above, it can be seen that the communication overhead has been reduced by about and the proposed scheme is more efficient than ECPP.
7.3. Storage Analysis
In this section, we analyse the storage cost between the proposed scheme and ECPP. To track the malicious vehicle, some information of vehicles should be saved by TA and RSU in ECPP. These will take a large of storage space especially the information of temporary anonymous keys, because the temporary anonymous keys of vehicles will be changed frequently to hide the real identity of vehicles. While in the proposed scheme, the real identity could be recovered by TA and RSU together from the certificate if necessary.
Table 6 shows the storage cost between the scheme and ECPP.
Considering that the temporary anonymous key will be changed frequently to secure the identity, it helps to save a large of storage space for RSU. In this sense, the MECPP protocol is more practical than ECPP.
8. Conclusions
In this paper, we proposed a new optimized protocol called MECPP based on ECPP for secure vehicular communications. The proposed MECPP scheme achieves mutual authentication between the RSUs and the vehicles in an anonymous manner before temporary certification. Particularly, the MECPP scheme not only provides the security and privacy protection to vehicles, but also provides a fast tracking mechanism to reveal the real identity of the malicious vehicles. In addition, the performance analysis section shows that the proposed scheme outperforms the ECPP scheme in terms of computational cost, communication overheads and storage overhead.
As future work, we propose to continue to optimize the latency, such as reducing communication overhead. Furthermore, we will aim to develop a new batch authentication scheme to simultaneously authenticate the vehicles in order to avoid the computation burden in large vehicular clouds.