A Novel Detection and Identification Mechanism for Malicious Injection Attacks in Power Systems
Abstract
:1. Introduction
2. Related Works
- How to address the limitation caused by precomputed threshold;
- How to cut down the effect of model error and external disturbance.
- A novel detection model is developed based on the UIOs and cosine similarity theorem. By designing the UIOs to handle the effect of model error and external disturbance, the accuracy of state estimation can be improved. By using the principle of cosine similarity matching, the limitation caused by the precomputed detection threshold can be addressed.
- An observer combination-based attack identification framework is proposed. By introducing the observer combination strategy, the influence caused by the injected FDI attacks can quickly be identified and eliminated.
3. Problem Description
3.1. Three-Phase Voltage-Based Power State Model
3.2. Problem Formulation
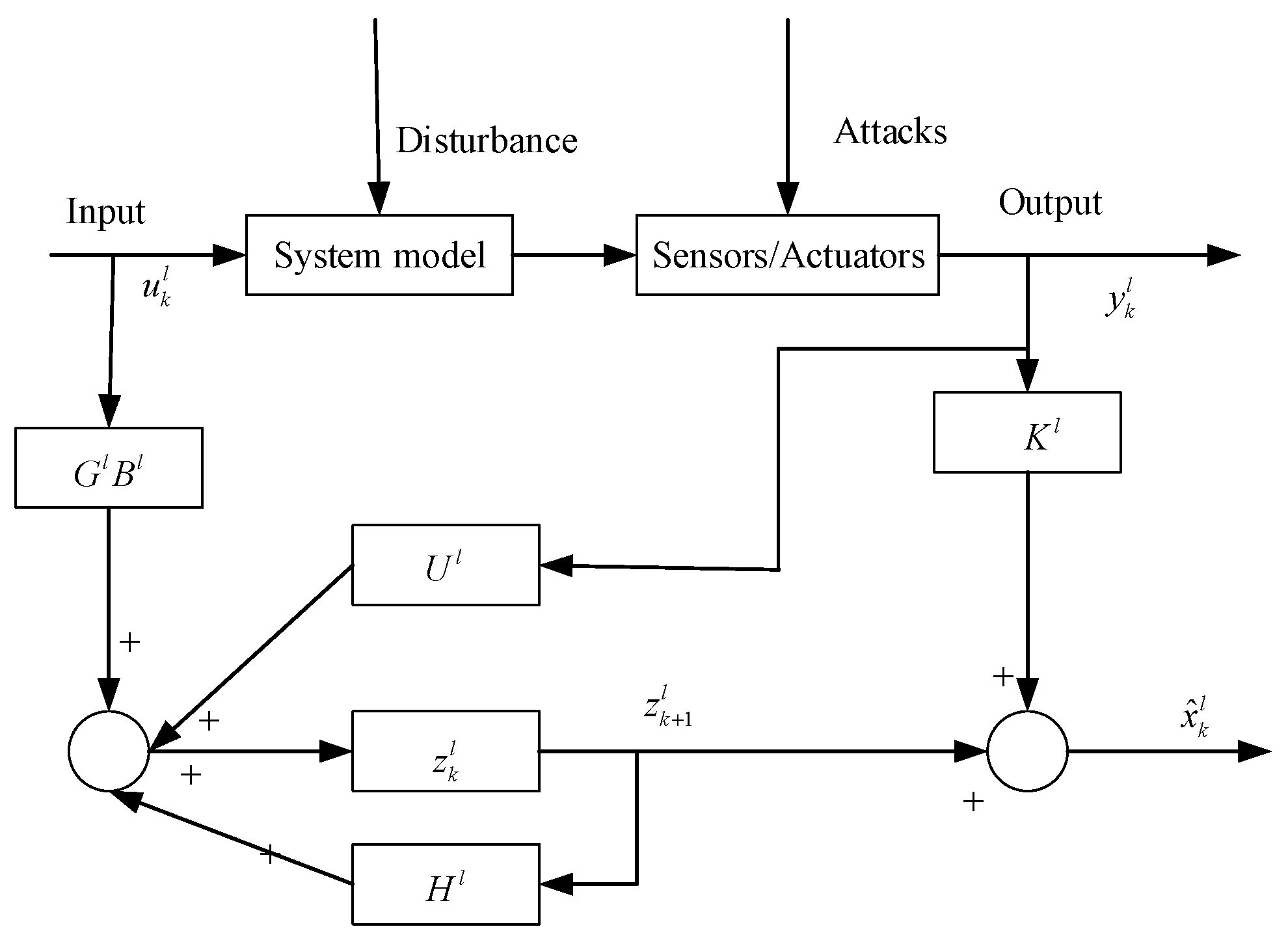
4. Detection and Identification Mechanism for FDI Attacks
4.1. UIO-Based State Estimation
4.2. Cosine Similarity Theorem-Based Detection Method
| Algorithm 1: Cosine similarity theorem-based detection algorithm against FDI attacks |
| 1. ; 2. ; 3. ; 4. 5. ; 6. ; 7. 8. 9. |
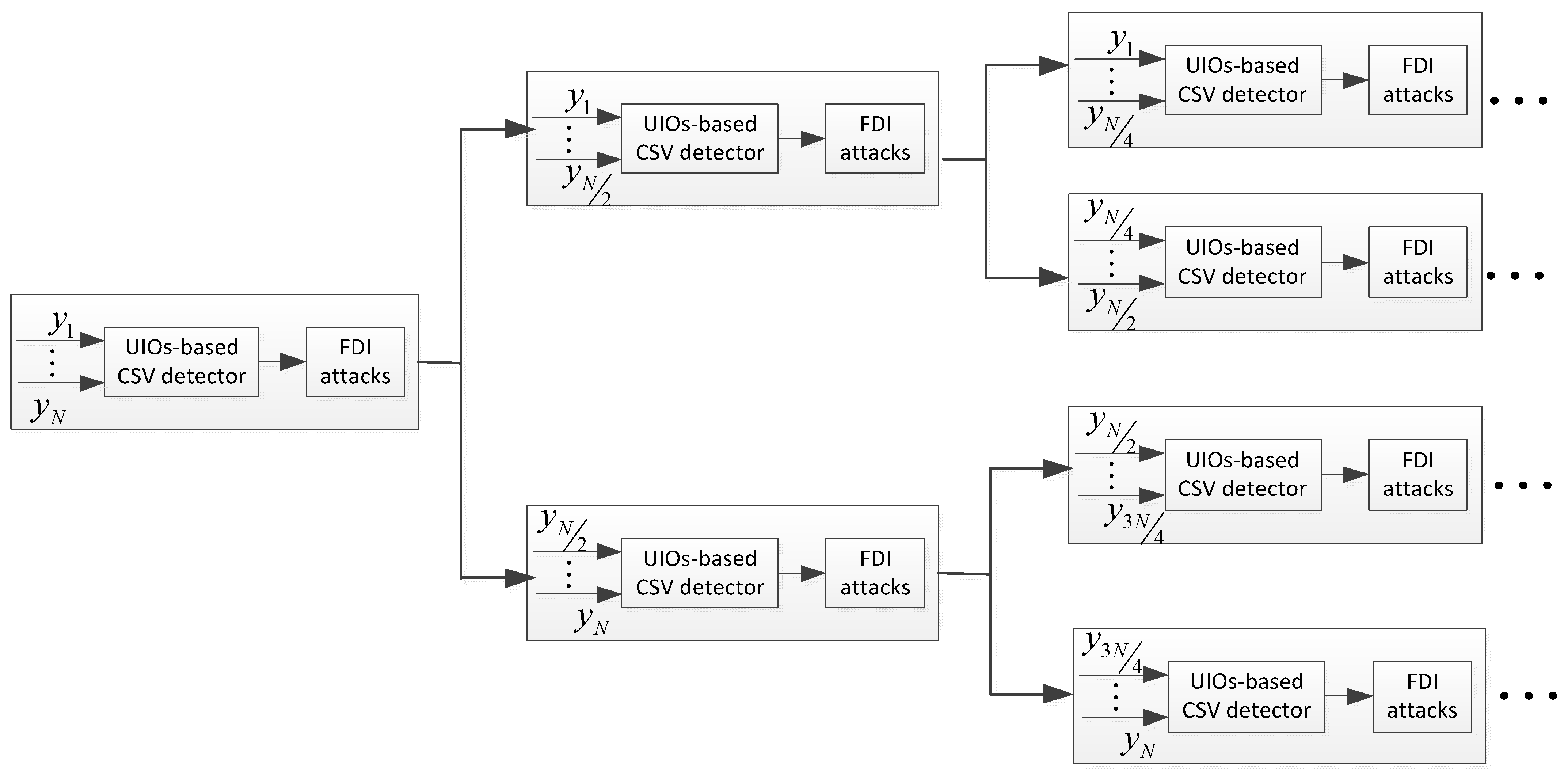
4.3. Observer Combination-Based Identification Method
| Algorithm 2: Observer combination-based attack identification |
| 1. 2. 3. ; 4. 5. 6. ; 7. 8. Else no attacks; 9. Repeat steps 5–7; 10. Output: the attacked nodes. |
5. Results
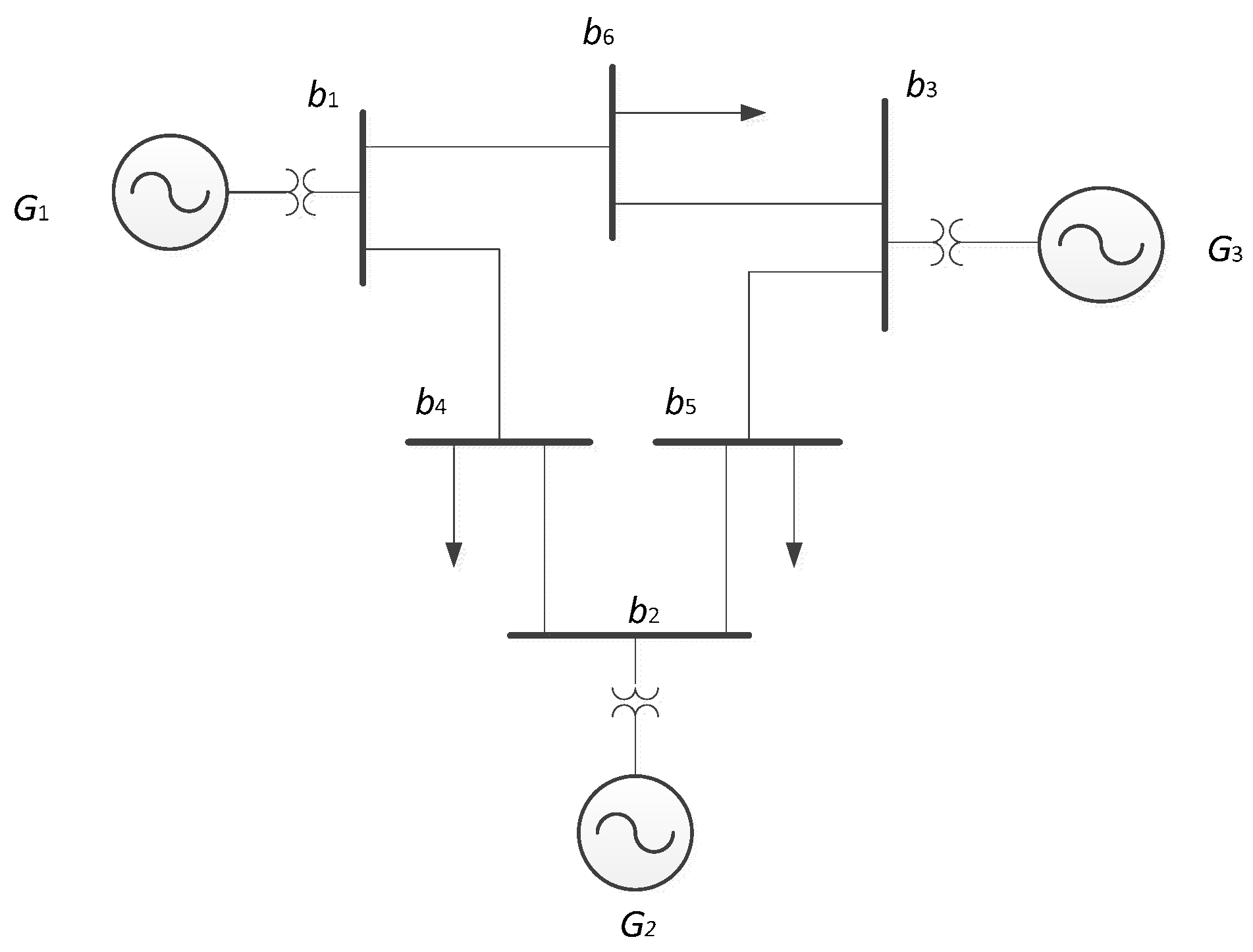
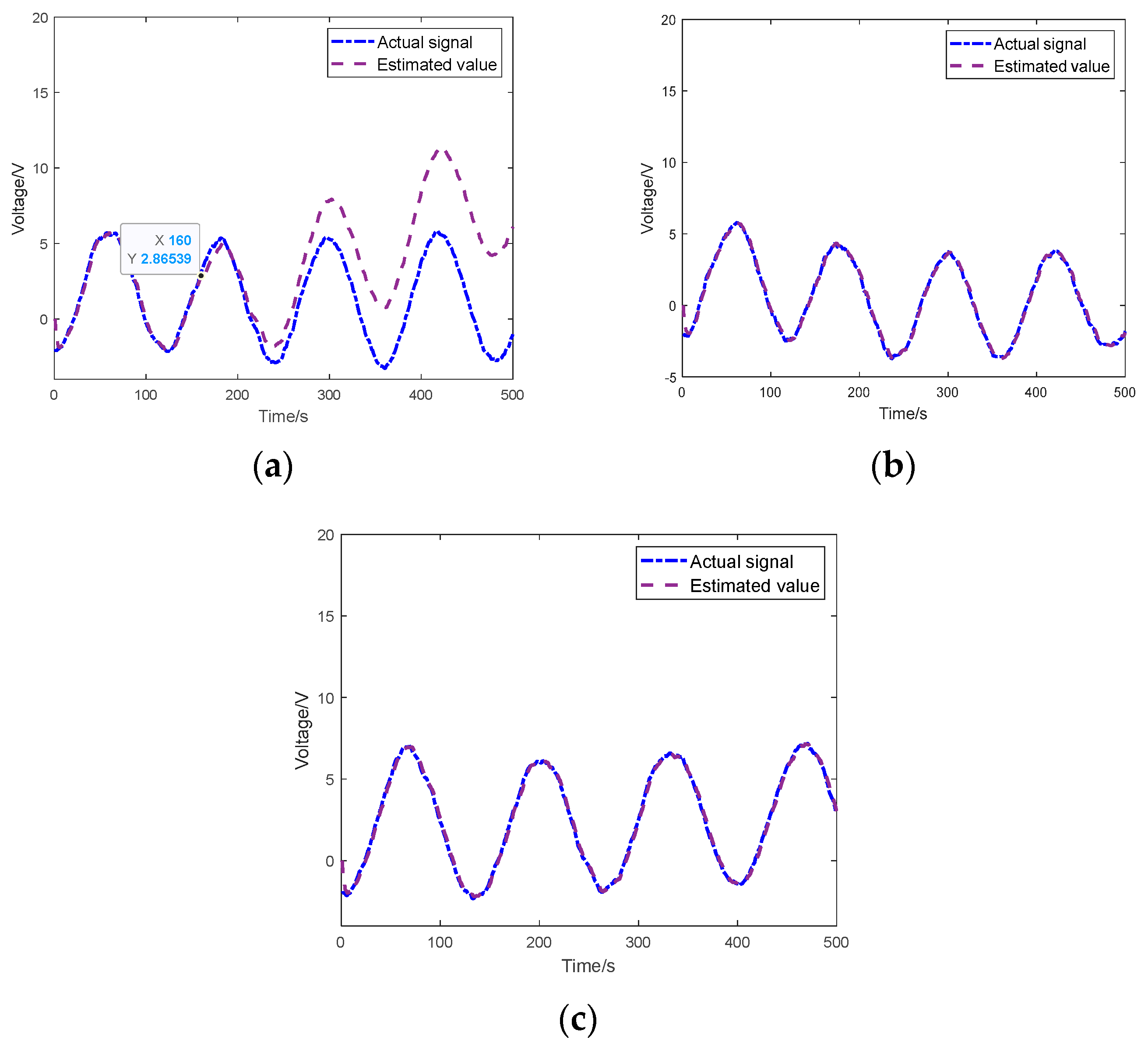
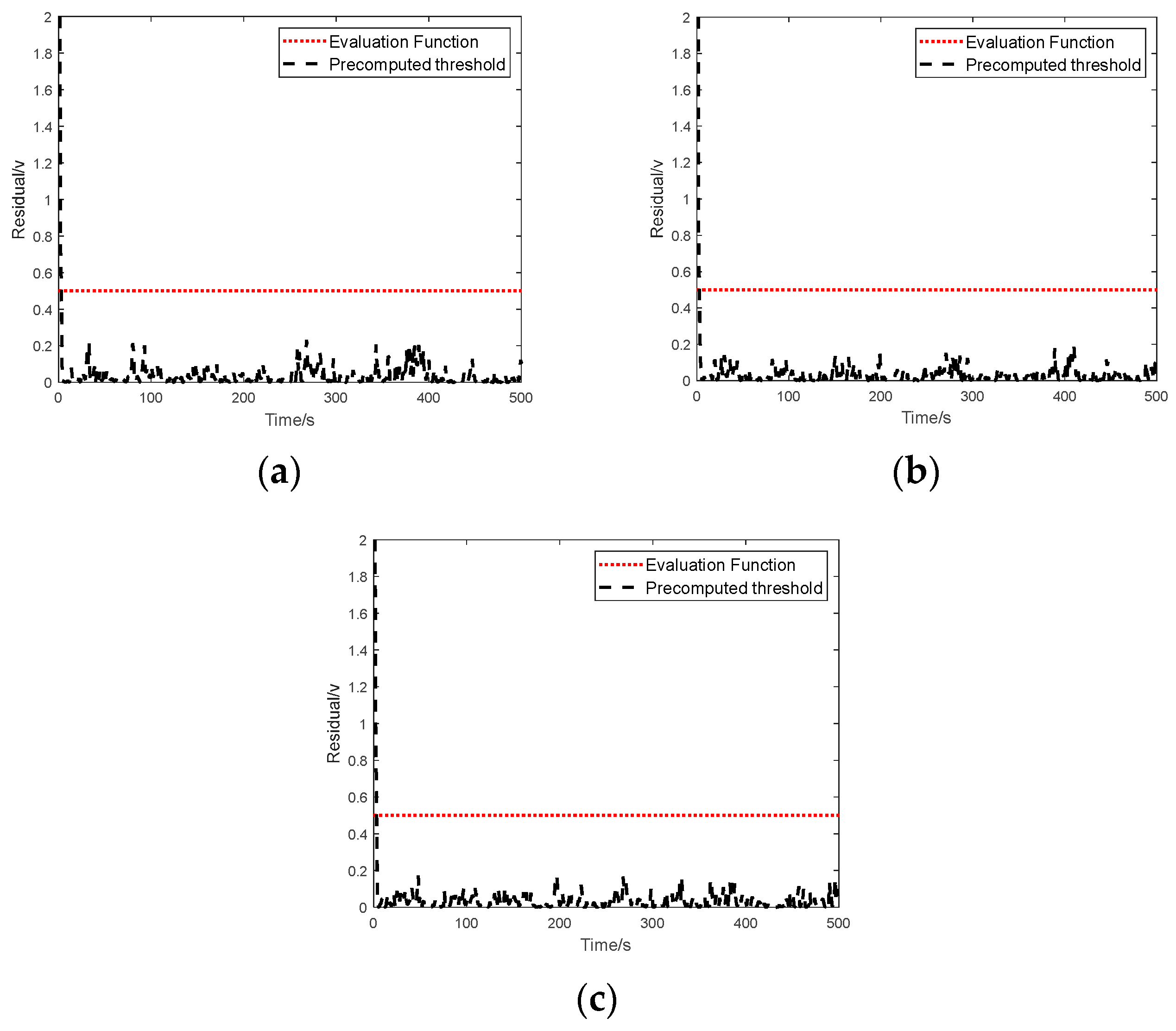
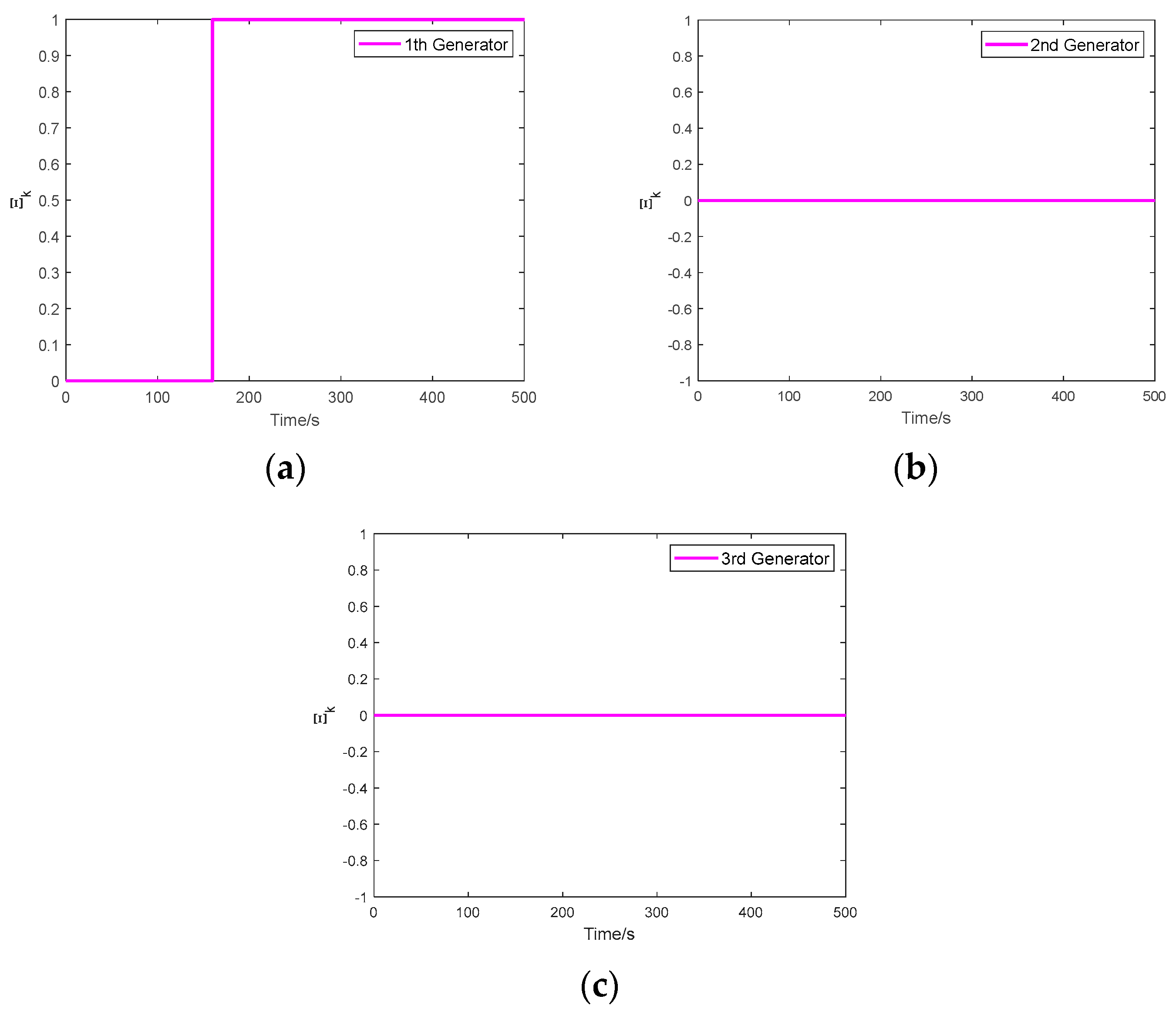
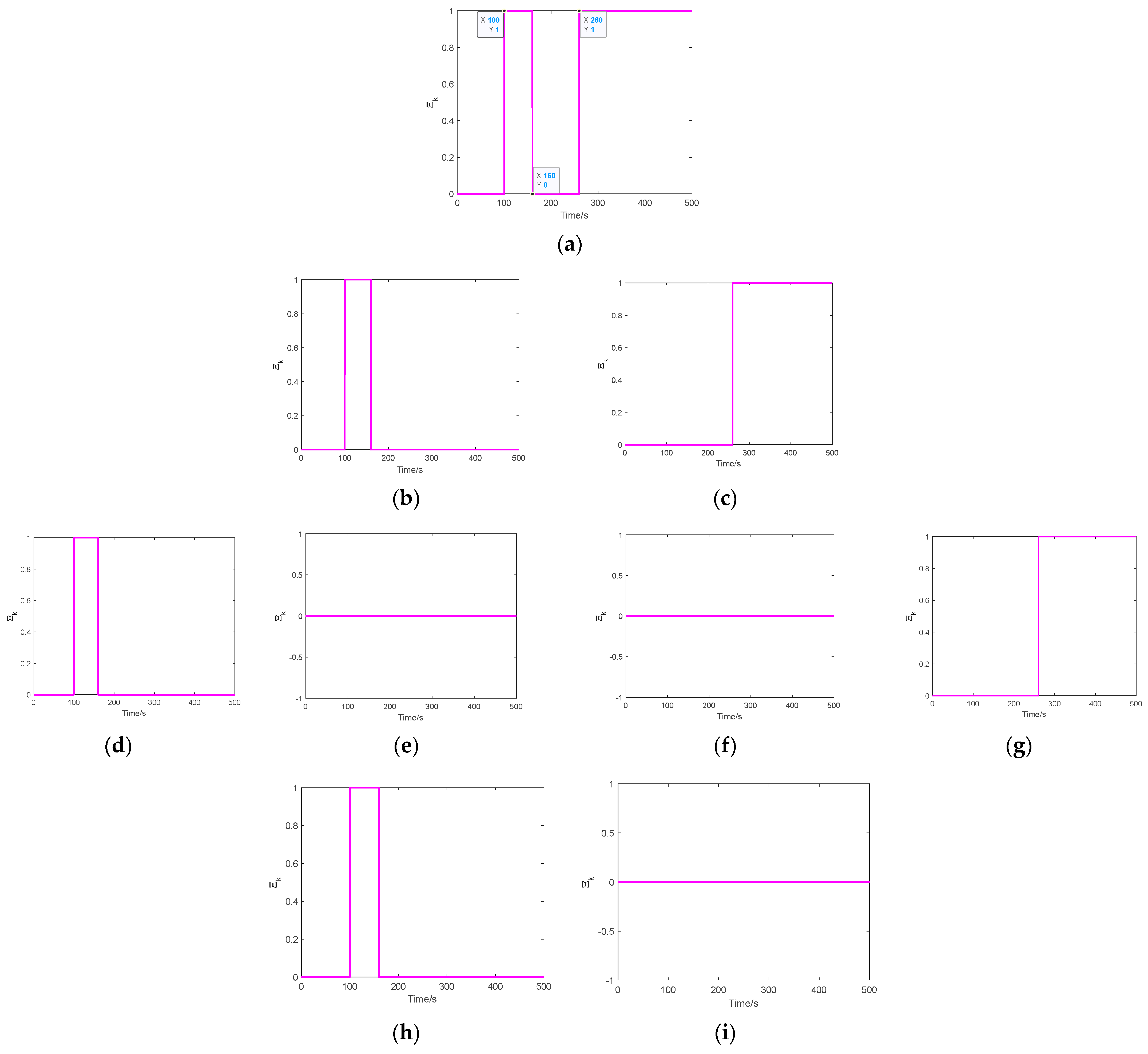
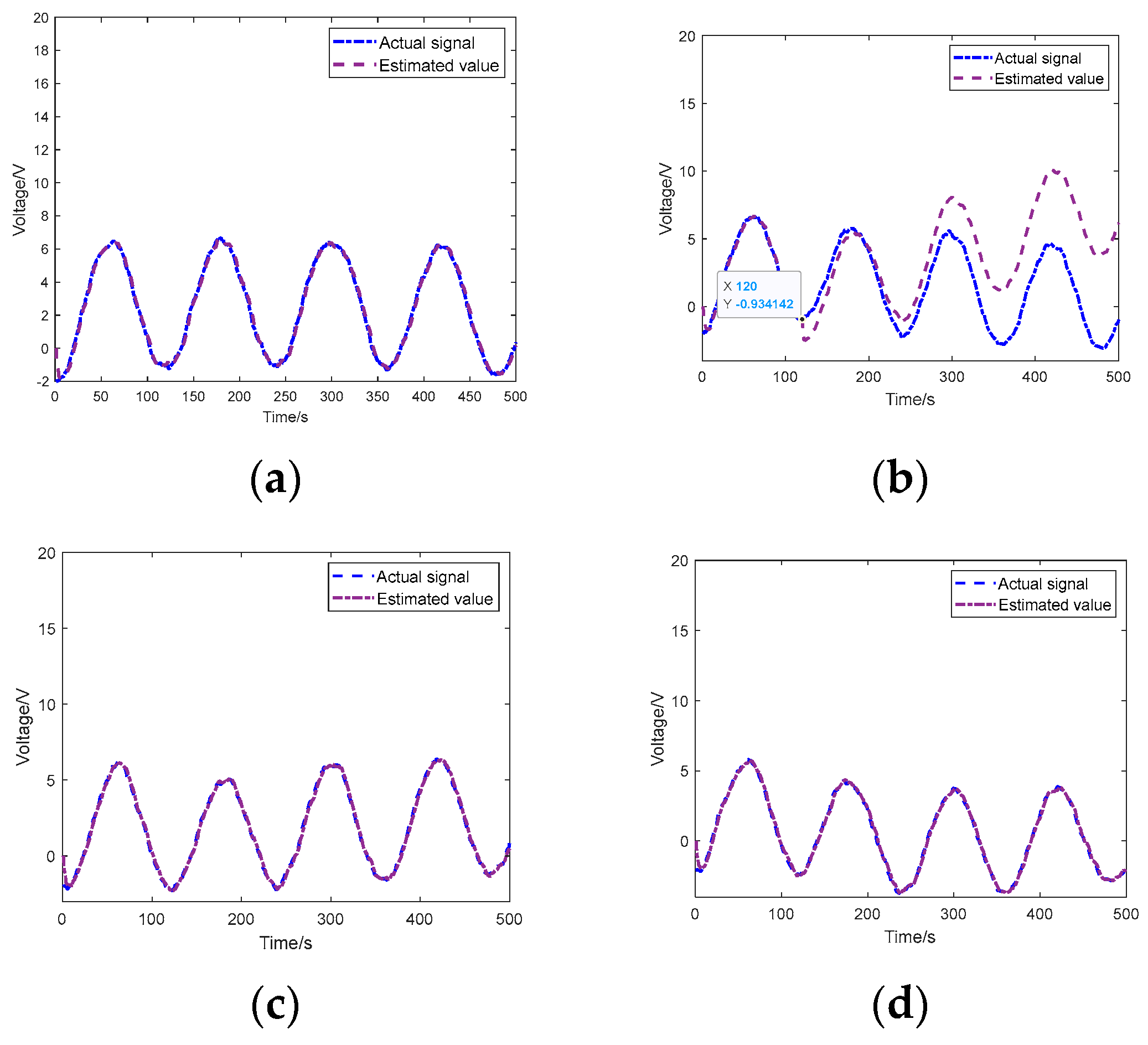
5.1. Case 1: Detection of One FDI Attack on an IEEE 6-Bus Power System
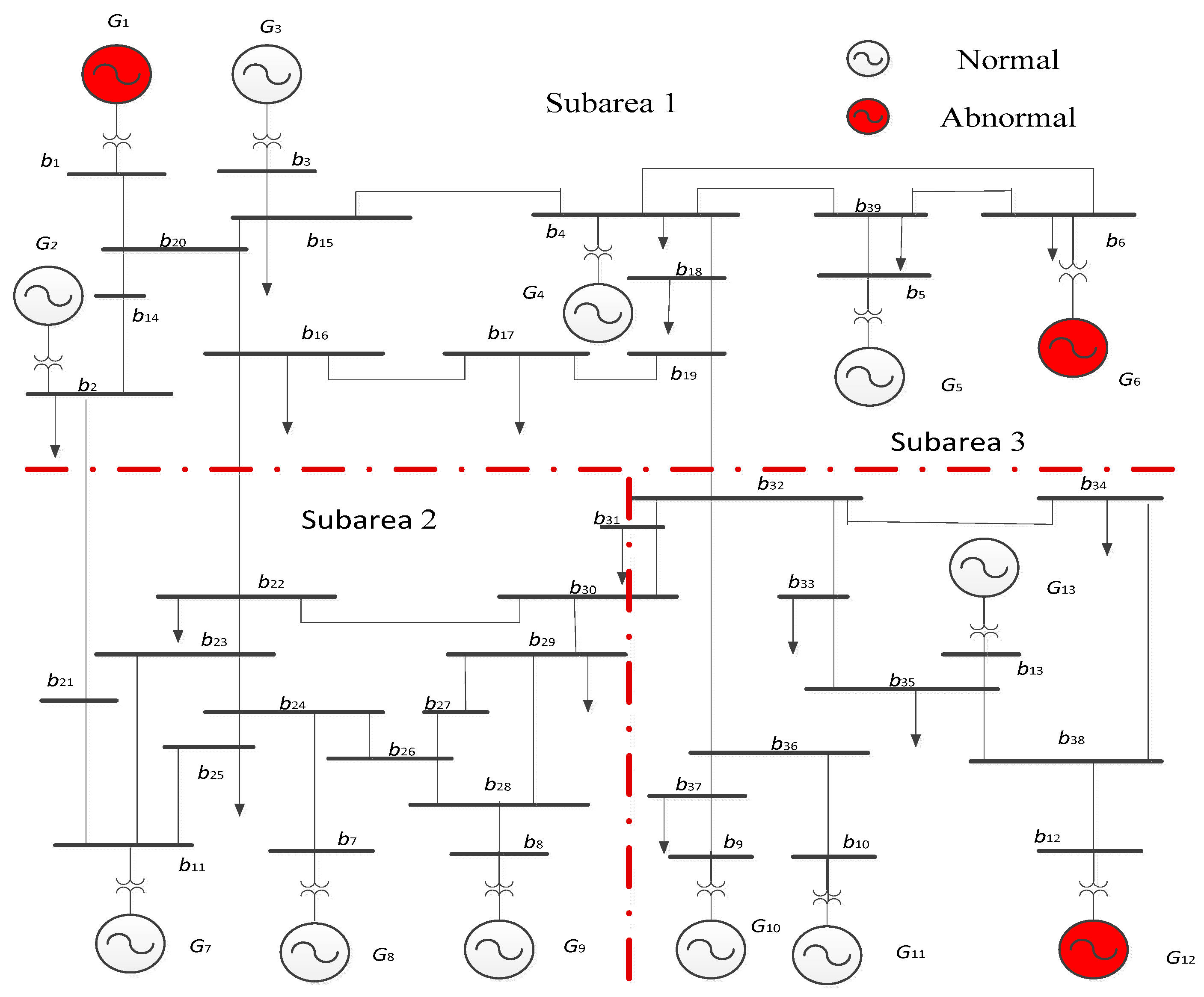
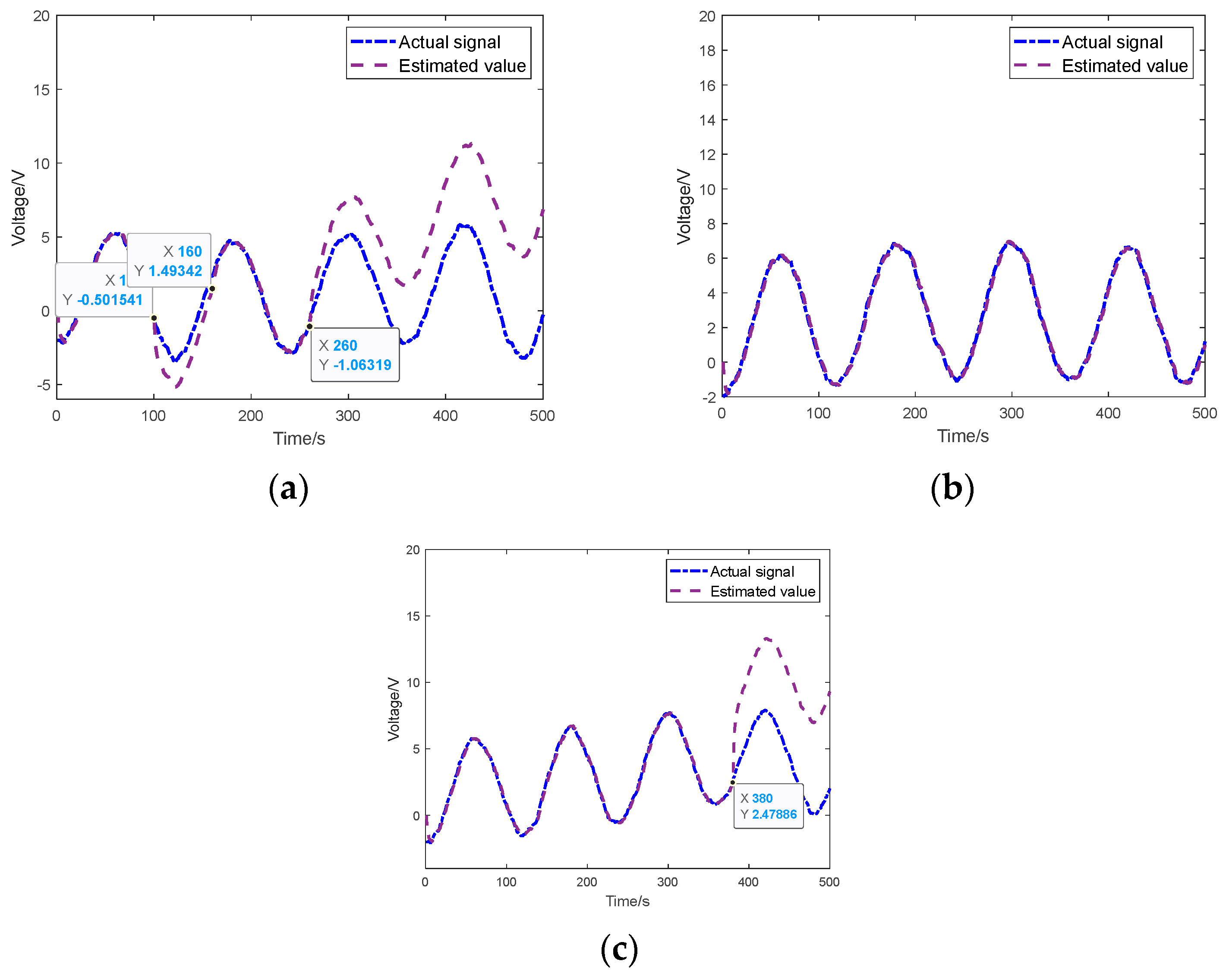
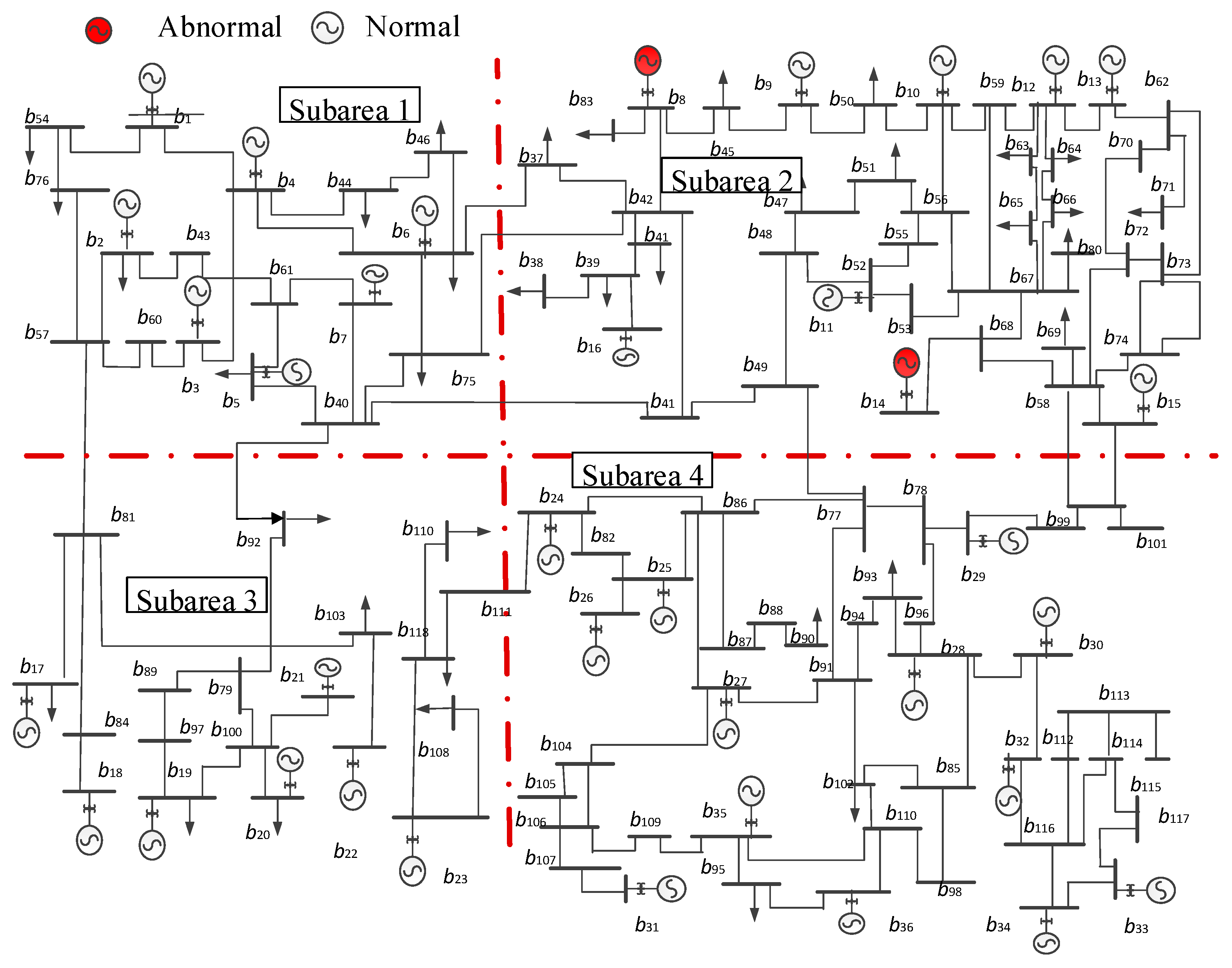
5.2. Case 2: Detection and Identification of Multiple FDI Attacks on an IEEE 39-Bus Power System
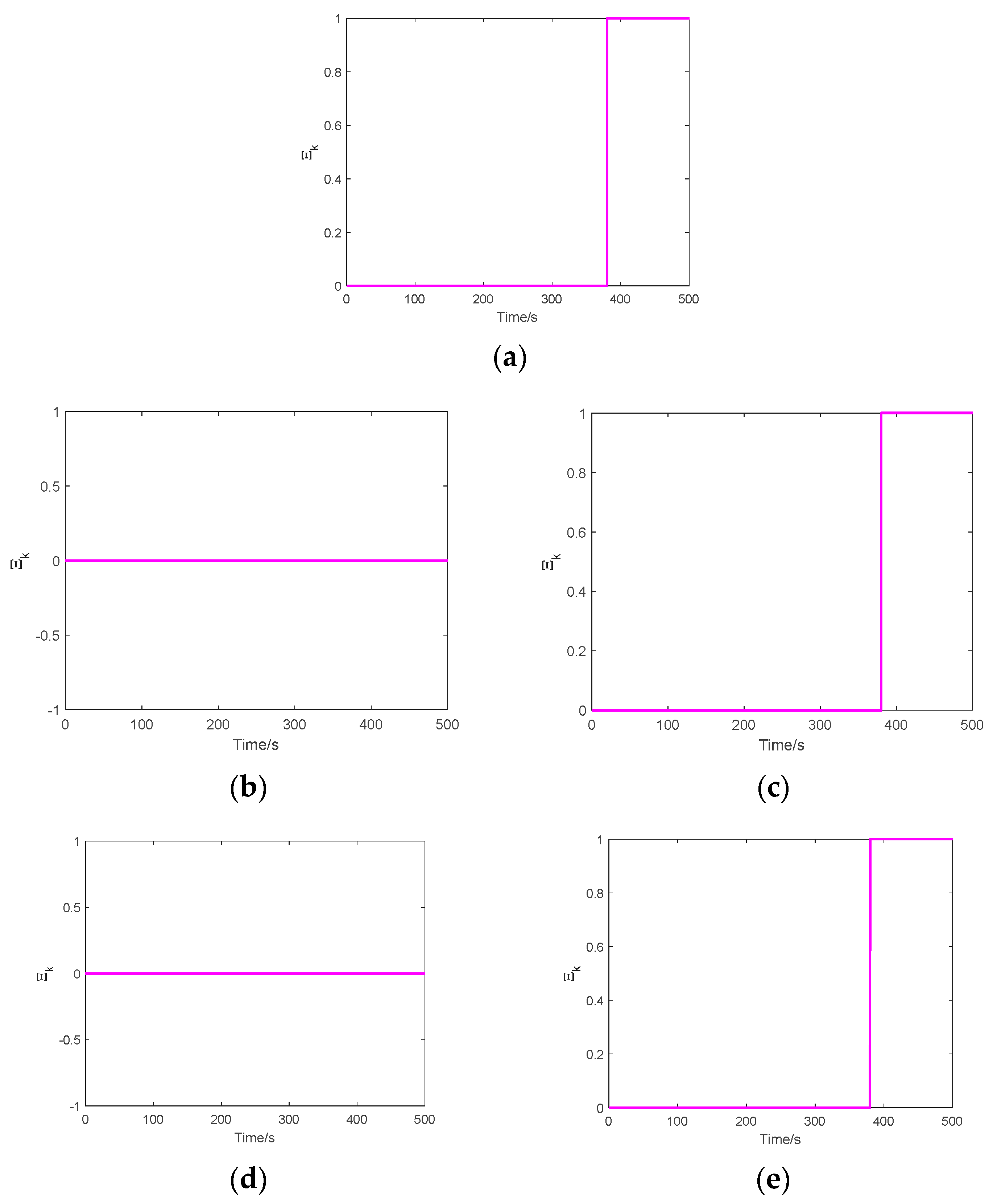
5.3. Case 3: Detection and Identification of Multiple FDI Attacks on IEEE 118-Bus Power System
6. Conclusions and Discussion
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Nomenclature
| Definition of all parameters | |
| amplitude of the three-phase voltage | |
| angular frequency | |
| angular phase | |
| voltage signal of the 1st generator | |
| voltage signal of the 2nd generator | |
| voltage signal of the 3rd generator | |
| model error and external disturbance, which is norm-bounded | |
| observation matrix of appropriate dimensions | |
| constant matrix of appropriate dimensions | |
| output residual | |
| measurement output | |
| the precomputed detection threshold | |
| output residual under FDI attacks | |
| measurement output under FDI attacks | |
| state estimation under FDI attacks | |
| increment of state caused by the attack | |
| attack-selected matrix of appropriate dimensions | |
| constant matrix of appropriate dimensions | |
| constant matrix of appropriate dimensions | |
| state vector of UIO | |
| estimation value of | |
| designed system parameter matrix | |
| constant matrix of appropriate dimensions | |
References
- Oyewole, P.A.; Jayaweera, D. Power System Security with Cyber-Physical Power System Operation. IEEE Access 2020, 8, 179970–179982. [Google Scholar] [CrossRef]
- Wang, C.; Jiang, C.; Wang, J.; Shen, S.; Guo, S.; Zhang, P. Blockchain-aided network resource orchestration in intelligent Internet of Things. IEEE Internet Things J. 2023, 10, 6151–6163. [Google Scholar] [CrossRef]
- Lau, P.; Wang, L.; Liu, Z.; Wei, W.; Ten, C.-W. A Coalitional Cyber-Insurance Design Considering Power System Reliability and Cyber Vulnerability. IEEE Trans. Power Syst. 2021, 36, 5512–5524. [Google Scholar] [CrossRef]
- Ashok, A.; Govindarasu, M.; Wang, J. Cyber-Physical Attack-Resilient Wide-Area Monitoring, Protection, and Control for the Power Grid. Proc. IEEE 2017, 105, 1389–1407. [Google Scholar] [CrossRef]
- Das, L.; Munikoti, S.; Natarajan, B.; Srinivasan, B. Measuring smart grid resilience: Methods challenges and opportunities. Renew. Sustain. Energy Rev. 2021, 130, 109918. [Google Scholar] [CrossRef]
- Liu, S.; Mashayekh, S.; Kundur, D.; Zourntos, T.; Butler-Purry, K. A framework for modeling cyber physical switching attacks in smart grid. IEEE Trans. Emerg. Top. Comput. 2014, 1, 273–285. [Google Scholar] [CrossRef]
- Saini, A.; Bhui, P.; Singh, A.K.; Haq, F.U.; Kotakonda, C. Impact of False Data Injection Attacks in Wide Area Damping Control. In Proceedings of the 2022 22nd National Power Systems Conference (NPSC), New Delhi, India, 17–19 December 2022; pp. 218–223. [Google Scholar]
- Xiao, M.; Wu, J.; Long, C.; Li, S. Construction of false sequence attack against PLC based power control system. In Proceedings of the 2016 35th Chinese Control Conference (CCC), Chengdu, China, 27–29 July 2016; pp. 10090–10095. [Google Scholar]
- Yu, X.; Xue, Y. Smart grids: A cyber-physical systems perspective. Proc. IEEE 2016, 104, 1058–1070. [Google Scholar] [CrossRef]
- Du, D.; Zhu, M.; Li, X.; Fei, M.; Bu, S.; Wu, L.; Li, K. A Review on Cybersecurity Analysis, Attack Detection, and Attack Defense Methods in Cyber-physical Power Systems. J. Mod. Power Syst. Clean Energy 2023, 11, 727–743. [Google Scholar] [CrossRef]
- Shukla, R.M.; Sengupta, S. A novel machine learning pipeline to detect malicious anomalies for the Internet of Things. Internet Things 2022, 20, 100603. [Google Scholar] [CrossRef]
- Gaggero, G.B.; Caviglia, R.; Armellin, A.; Rossi, M.; Girdinio, P.; Marchese, M. Detecting Cyberattacks on Electrical Storage Systems through Neural Network Based Anomaly Detection Algorithm. Sensors 2022, 22, 3933. [Google Scholar] [CrossRef]
- Mashima, D.; Cárdenas, A.A. Evaluating Electricity Theft Detectors in Smart Grid Networks. In Research in Attacks, Intrusions, and Defenses. RAID 2012; Balzarotti, D., Stolfo, S.J., Cova, M., Eds.; Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2012; Volume 7462. [Google Scholar] [CrossRef]
- Gaggero, G.B.; Rossi, M.; Girdinio, P.; Marchese, M. Detecting System Fault/Cyberattack within a Photovoltaic System Connected to the Grid: A Neural Network-Based Solution. J. Sens. Actuator Netw. 2020, 9, 20. [Google Scholar] [CrossRef]
- Gunduz, H.; Jayaweera, D. Modern power system reliability assessment with cyber-intrusion on heat pump systems. IET Smart Grid 2020, 3, 561–571. [Google Scholar] [CrossRef]
- Zhang, J.; Wang, X. Low-complexity quickest change detection in linear systems with unknown time-varying pre- and post-change distributions. IEEE Trans. Inf. Theory 2021, 67, 1804–1824. [Google Scholar] [CrossRef]
- Nawaz, R.; Akhtar, R.; Shahid, M.A.; Qureshi, I.M.; Mahmood, M.H. Machine learning based false data injection in smart grid. Int. J. Electr. Power Energy Syst. 2021, 130, 106819. [Google Scholar] [CrossRef]
- Punmiya, R.; Choe, S. Energy theft detection using gradient boosting theft detector with feature engineering-based preprocessing. IEEE Trans. Smart Grid 2019, 10, 2326–2329. [Google Scholar] [CrossRef]
- Gallo, A.J.; Turan, M.S.; Boem, F.; Parisini, T.; Ferrari-Trecate, G. A Distributed Cyber-Attack Detection Scheme with Application to DC Microgrids. IEEE Trans. Autom. Control 2020, 65, 3800–3815. [Google Scholar] [CrossRef]
- Lv, Y.W.; Yang, G.H. An adaptive cubature Kalman filter for nonlinear systems against randomly occurring injection attacks. Appl. Math. Comput. 2022, 418, 126834. [Google Scholar] [CrossRef]
- Živković, N.; Sarić, A.T. Detection of false data injection attacks using unscented Kalman filter. J. Mod. Power Syst. Clean Energy 2018, 6, 847–859. [Google Scholar] [CrossRef]
- Liu, Y.; Xue, W.; He, S.; Cheng, L. Stealthy False Data Injection Attacks against Extended Kalman Filter Detection in Power Grids. In Proceedings of the 2021 8th International Conference on Information, Cybernetics, and Computational Social Systems (ICCSS), Beijing, China, 10–12 December 2021; pp. 459–464. [Google Scholar]
- Xiahou, K.; Liu, Y.; Wu, Q.H. Decentralized Detection and Mitigation of Multiple False Data Injection Attacks in Multiarea Power Systems. IEEE J. Emerg. Sel. Top. Ind. Electron. 2022, 3, 101–112. [Google Scholar] [CrossRef]
- Kazemi, Z.; Safavi, A.A.; Naseri, F.; Urbas, L.; Setoodeh, P. A secure hybrid dynamic-state estimation approach for power systems under false data injection attacks. IEEE Trans. Ind. Inform. 2020, 16, 7275–7286. [Google Scholar] [CrossRef]
- Wang, H.; Ruan, J.; Zhou, B.; Li, C.; Wu, Q.; Raza, M.Q.; Cao, G.Z. Dynamic data injection attack detection of cyber physical power systems with uncertainties. IEEE Trans. Ind. Inform. 2019, 15, 5505–5518. [Google Scholar] [CrossRef]
- Manandhar, K.; Cao, X.; Hu, F.; Liu, Y. Detection of faults and attacks including false data injection attack in smart grid using Kalman filter. IEEE Trans. Control Netw. Syst. 2014, 1, 370–379. [Google Scholar] [CrossRef]
- Tan, R.; Nguyen, H.H.; Foo, E.Y.; Yau, D.K.; Kalbarczyk, Z.; Iyer, R.K.; Gooi, H.B. Modeling and mitigating impact of false data injection attacks on automatic generation control. IEEE Trans. Inf. Forensics Secur. 2017, 12, 1609–1624. [Google Scholar] [CrossRef]
- Luo, X.; Zhu, M.; Wang, X.; Guan, X. Detection and isolation of false data injection attack via adaptive Kalman filter bank. J. Control Decis. 2022, 1–13. [Google Scholar] [CrossRef]
- Venkateswaran, S.; Kravaris, C. Linear Unknown Input Observers for Sensor Fault Estimation in Nonlinear Systems. IFAC-PapersOnLine 2023, 56, 61–66. [Google Scholar] [CrossRef]
- Pipeleers, G.; Vandenberghe, L. Generalized KYP Lemma with Real Data. IEEE Trans. Autom. Control 2011, 56, 2942–2946. [Google Scholar] [CrossRef]
- Pertew, A.M.; Marquez, H.J.; Zhao, Q. H∞ observer design for lipschitz nonlinear systems. IEEE Trans. Autom. Control 2006, 51, 1211–1216. [Google Scholar] [CrossRef]
- Zhang, Z.H.; Yang, G.H. Event-triggered fault detection for a class of discrete-time linear systems using interval observers. ISA Trans. 2017, 68, 160–169. [Google Scholar] [CrossRef]
- Gerhat, B. Schur complement dominant operator matrices. J. Funct. Anal. 2023, 286, 110195. [Google Scholar] [CrossRef]
- Chow, J.; Kokotovic, P. Time scale modeling of sparse dynamic networks. IEEE Trans. Autom. Control 2003, 30, 714–722. [Google Scholar] [CrossRef]

| Category | Approach | Advantages | Disadvantages |
|---|---|---|---|
| Data-driven methods | [11,12,13,14,15,16,17,18] |
|
|
| Model-based methods | [19,20,21,22,23,24,25] |
|
| System | Detection Time (s) | Identification Time (s) |
|---|---|---|
| 6-bus | 0.8 | 1.2 |
| 39-bus | 1.5 | 3.8 |
| 118-bus | 2.2 | 4.5 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Zhang, H.; Wang, X.; Ban, L.; Sun, M. A Novel Detection and Identification Mechanism for Malicious Injection Attacks in Power Systems. Symmetry 2023, 15, 2104. https://doi.org/10.3390/sym15122104
Zhang H, Wang X, Ban L, Sun M. A Novel Detection and Identification Mechanism for Malicious Injection Attacks in Power Systems. Symmetry. 2023; 15(12):2104. https://doi.org/10.3390/sym15122104
Chicago/Turabian StyleZhang, Hongfeng, Xinyu Wang, Lan Ban, and Molin Sun. 2023. "A Novel Detection and Identification Mechanism for Malicious Injection Attacks in Power Systems" Symmetry 15, no. 12: 2104. https://doi.org/10.3390/sym15122104
APA StyleZhang, H., Wang, X., Ban, L., & Sun, M. (2023). A Novel Detection and Identification Mechanism for Malicious Injection Attacks in Power Systems. Symmetry, 15(12), 2104. https://doi.org/10.3390/sym15122104







