Residual Energy Analysis in Cognitive Radios with Energy Harvesting UAV under Reliability and Secrecy Constraints
Abstract
1. Introduction
1.1. Contributions
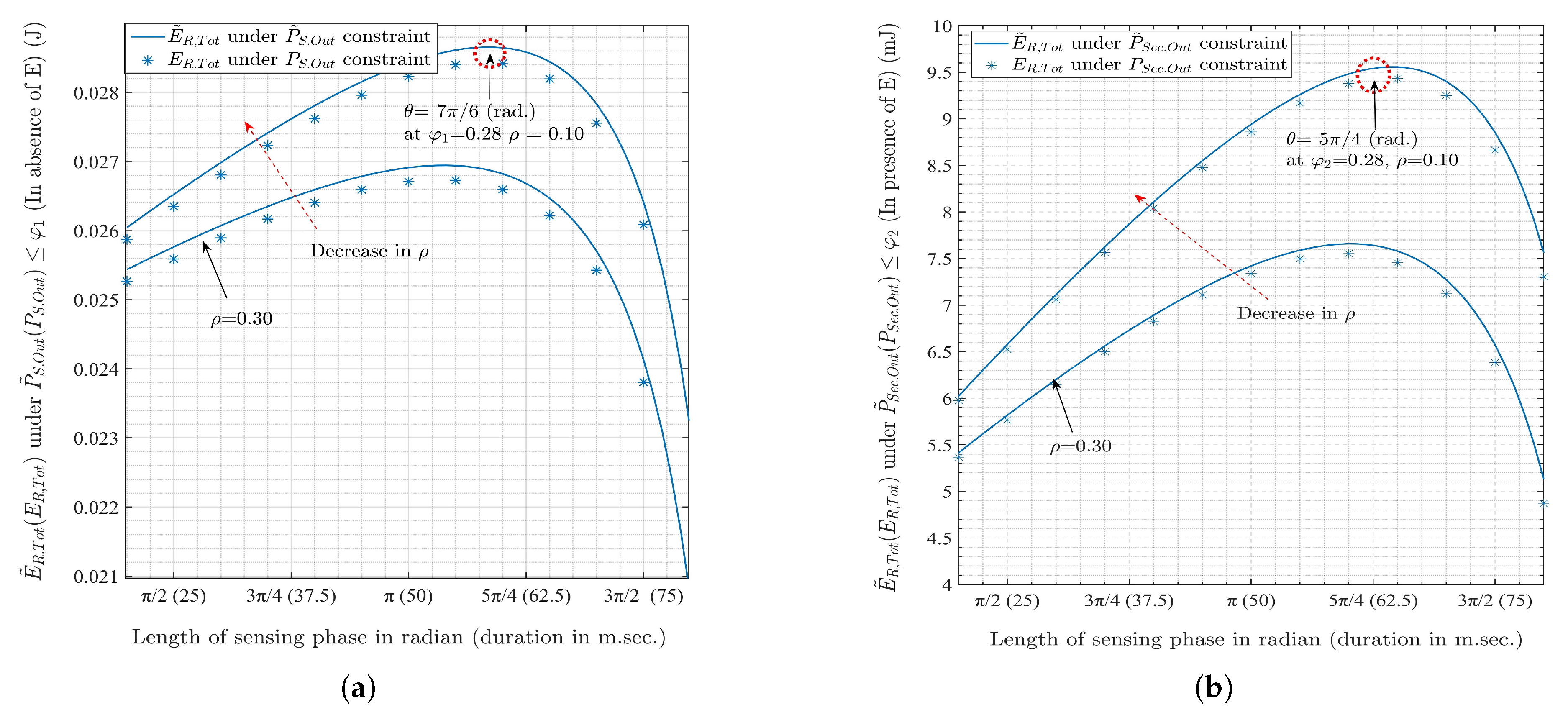
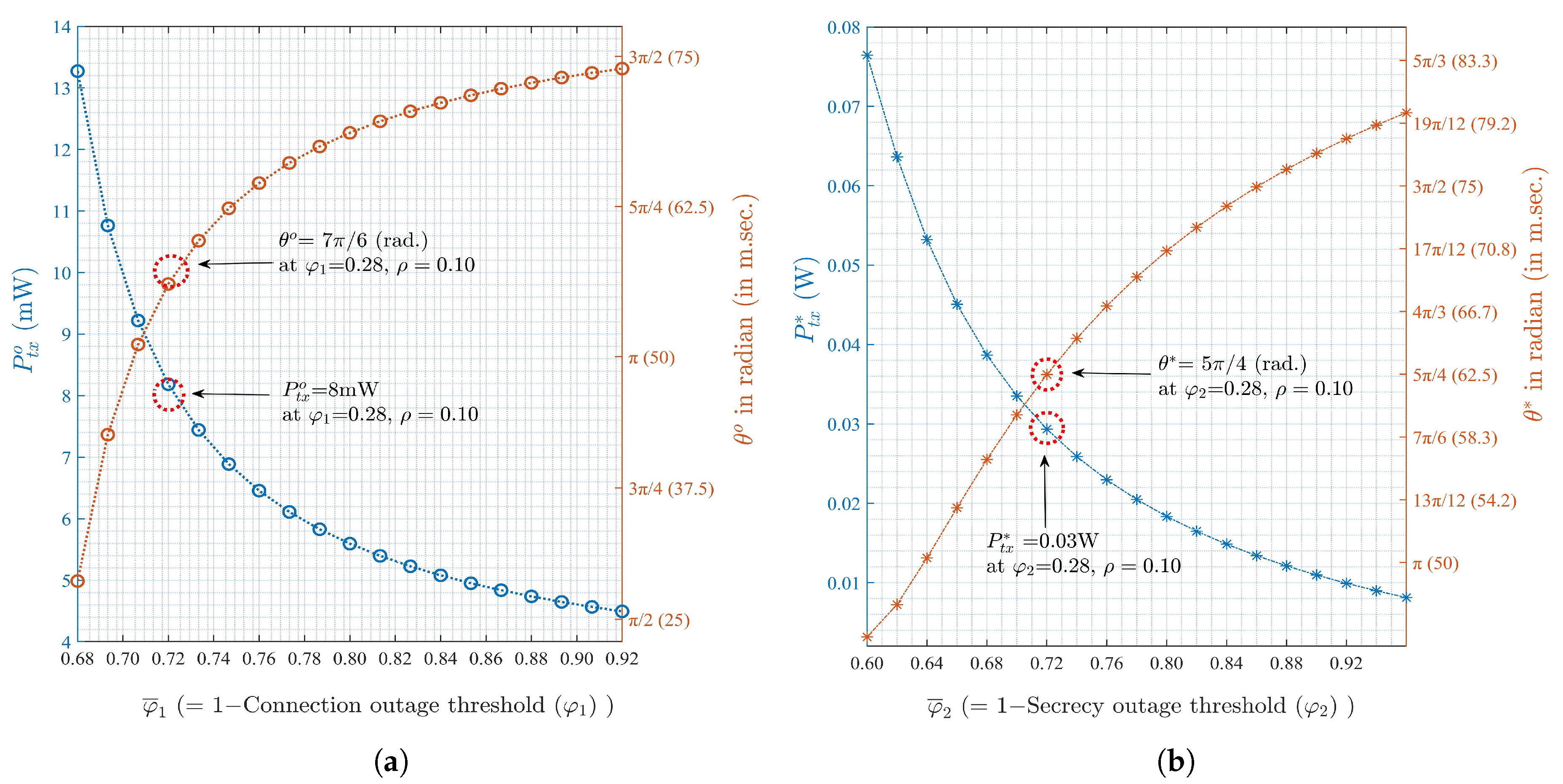
- We consider the energy management aspect of the energy harvesting CR-based UAV with limited-energy budget. The closed-form expressions of the total residual energy, connection outage probability, and secrecy outage probability are derived under a circular flight condition.
- We aim to extend the on-board battery life-time for UAV by maximizing the energy obtained through the EH and minimizing the transmission energy consumption. Thus, the optimal lengths of sensing phase and the transmit powers are obtained by solving the formulated optimization problems of maximum residual energy under the constraints of connection and secrecy outage probabilities with perfect sensing approximation.
- The analytical results are verified through the numerical simulations including imperfect sensing. Based on the results, we provide guidelines in designing an energy harvesting UAV-based CR system with the reliable and secure communications under scenarios without and with an eavesdropper, respectively.
1.2. Paper Organization
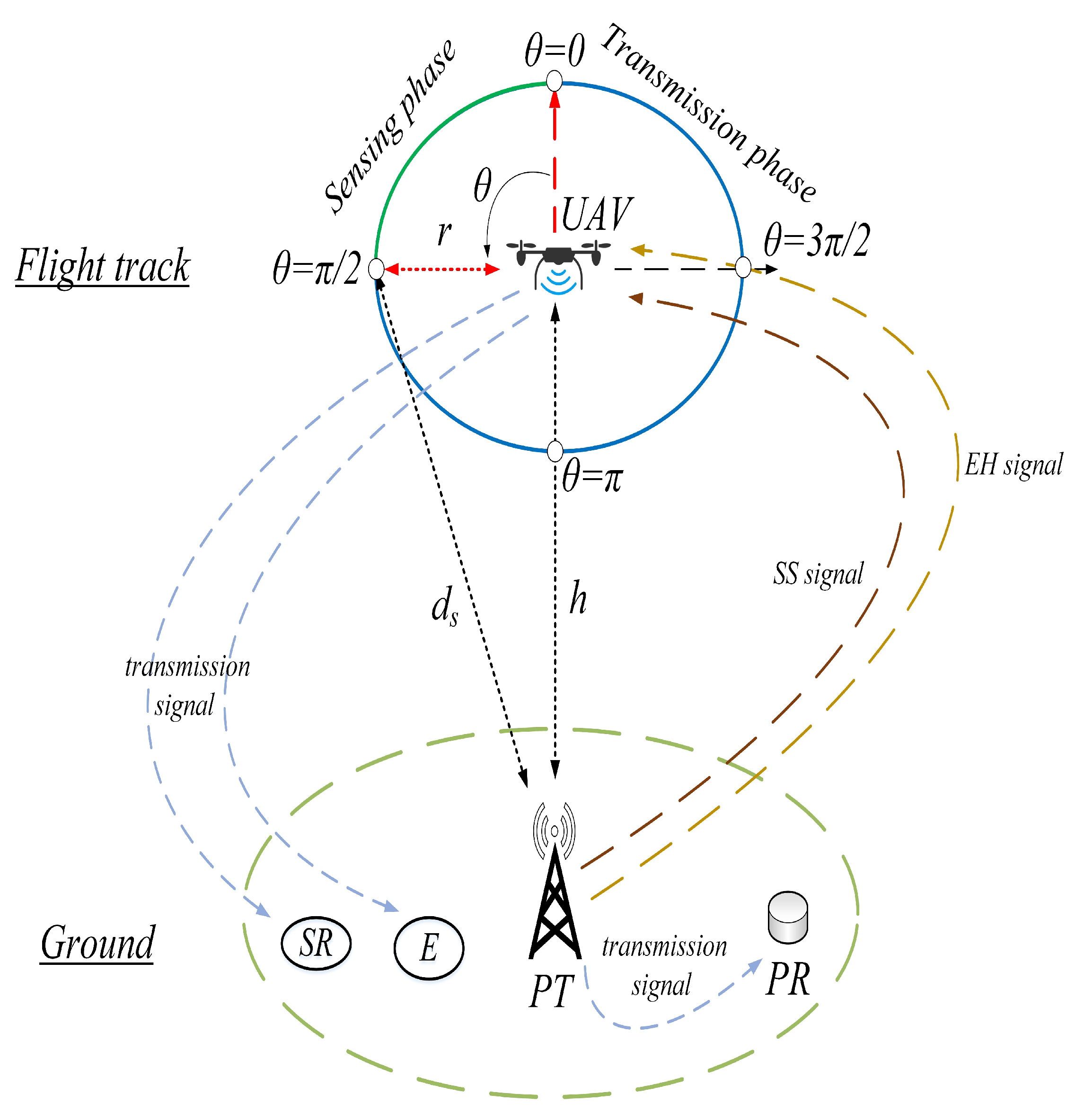
2. System Model
3. Sensing Procedure and Signal Modeling
4. Residual Energy Analysis
4.1. Sensing Phase
4.2. Transmission Phase
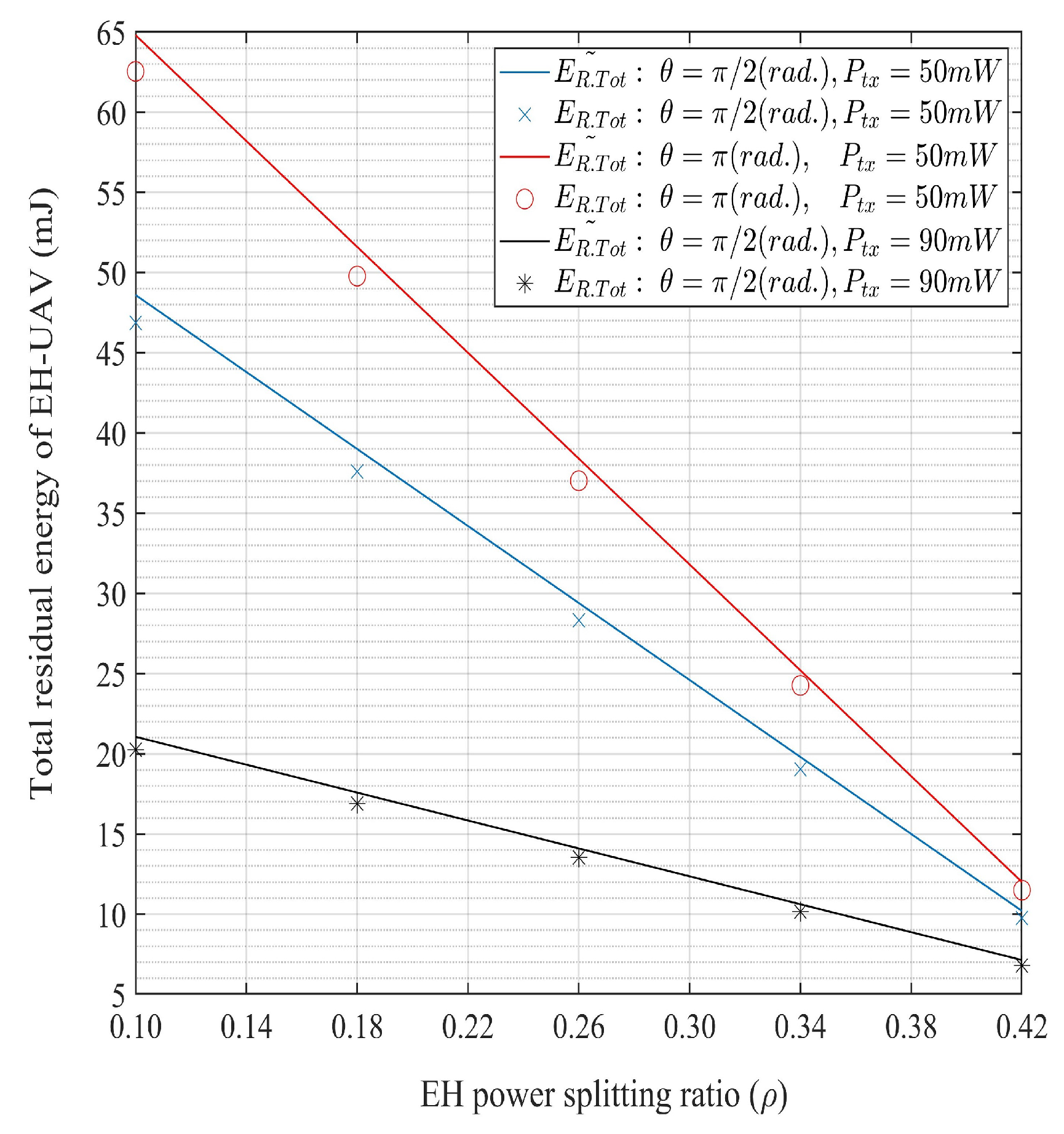
4.3. Total Residual Energy
5. Connection and Secrecy Outage Probabilities
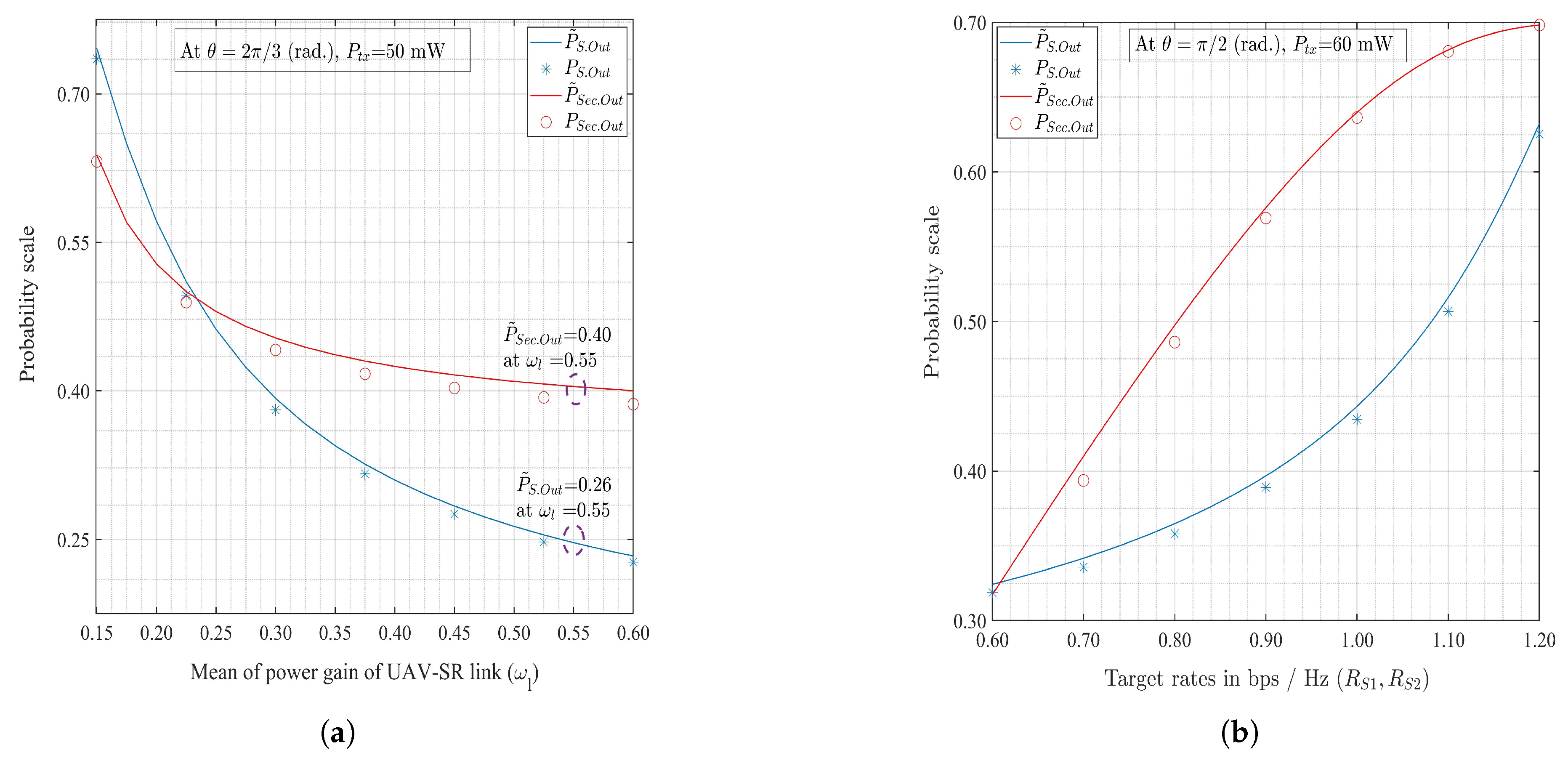
5.1. Connection Outage Probability
5.2. Secrecy Outage Probability
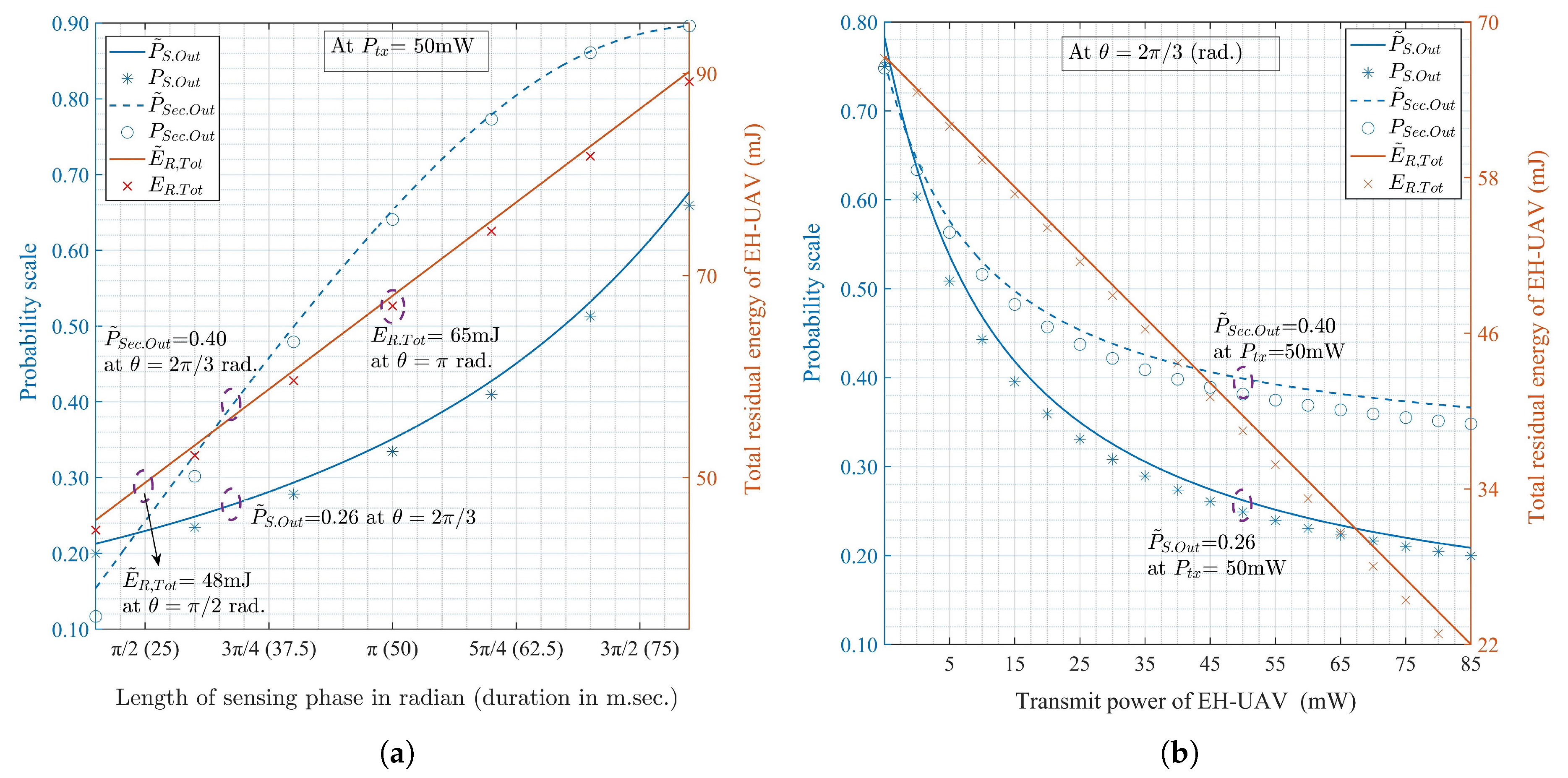
6. Maximization of Total Residual Energy
6.1. Residual Energy Maximization under Connection Outage Constraint
6.2. Residual Energy Maximization under Secrecy Outage Constraint
7. Numerical Results and Discussion
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Wang, D.; Chen, D.; Song, B.; Guizani, N.; Yu, X.; Du, X. From IoT to 5G I-IoT: The next generation IoT-based intelligent algorithms and 5G technologies. IEEE Commun. Mag. 2018, 56, 114–120. [Google Scholar] [CrossRef]
- Yu, H.; Lee, H.; Jeon, H. What is 5G? Emerging 5G mobile services and network requirements. Sustainability 2017, 9, 1848. [Google Scholar] [CrossRef]
- Yu, H. Optimal primary pilot power allocation and secondary channel sensing in cognitive radios. IET Communications 2016, 10, 487–494. [Google Scholar] [CrossRef]
- Salameh, H.A.B.; Almajali, S.; Ayyash, M.; Elgala, H. Spectrum assignment in cognitive radio networks for internet-of-things delay-sensitive applications under jamming attacks. IEEE Internet Things J. 2018, 5, 1904–1913. [Google Scholar] [CrossRef]
- Khalid, W.; Yu, H. Sensing and utilization of spectrum with cooperation interference for full-duplex cognitive radio networks. In Proceedings of the Eleventh International Conference on Ubiquitous and Future Networks (ICUFN), Zagreb, Croatia, 2–5 July 2019; pp. 598–600. [Google Scholar]
- Han, R.; Gao, Y.; Wu, C.; Lu, D. An Effective multi-objective optimization algorithm for spectrum allocations in the cognitive-radio-based internet of things. IEEE Access 2018, 6, 12858–12867. [Google Scholar] [CrossRef]
- Hu, F.; Chen, B.; Zhu, K. Full spectrum sharing in cognitive radio networks toward 5G: A survey. IEEE Access 2018, 6, 15754–15776. [Google Scholar] [CrossRef]
- Zhang, J.; Pan, G.; Wang, H.M. On physical-layer security in underlay cognitive radio networks with full-duplex wireless-powered secondary system. IEEE Access 2016, 4, 3887–3893. [Google Scholar] [CrossRef]
- Yu, H.; Lee, I.G. Physical layer security based on NOMA and AJ for MISOSE channels with an untrusted relay. Future Gener. Comput. Syst. 2020, 102, 611–618. [Google Scholar] [CrossRef]
- Tin, P.T.; Hung, D.; Nguyen, T.N.; Duy, T.T.; Voznak, M. Secrecy performance enhancement for underlay cognitive radio networks employing cooperative multi-hop transmission with and without presence of hardware impairments. Entropy 2019, 21, 217. [Google Scholar] [CrossRef]
- Rahman, M.A.; Lee, Y.D.; Koo, I. Joint relay selection and power allocation through a genetic algorithm for secure cooperative cognitive radio networks. Sensors 2018, 18, 3934. [Google Scholar] [CrossRef]
- Xiong, R.; Shan, F. DroneTank: Planning UAVs’ flights and sensors’ data transmission under energy constraints. Sensors 2018, 18, 2913. [Google Scholar] [CrossRef] [PubMed]
- Liu, X.; Guan, M.; Zhang, X.; Ding, H. Spectrum sensing optimization in an UAV-based cognitive radio. IEEE Access 2018, 6, 44002–44009. [Google Scholar] [CrossRef]
- Khalid, W.; Yu, H. Residual energy analysis with physical-layer security for energy-constrained UAV cognitive Radio Systems. In Proceedings of the 2020 International Conference on Electronics Information, and Communication (ICEIC), Barcelona, Spain, 19–22 January 2020; pp. 1–3. [Google Scholar]
- Zhang, F.; Jing, T.; Huo, Y.; Jiang, K. Outage probability minimization for energy harvesting cognitive radio sensor networks. Sensors 2017, 17, 224. [Google Scholar] [CrossRef] [PubMed]
- Banerjee, A.; Maity, S.; Roy, S. On residual energy maximization in energy harvesting cognitive radio network. In Proceedings of the 2017 IEEE Wireless Communications and Networking Conference (WCNC), San Francisco, CA, USA, 19–22 March 2017; pp. 1–6. [Google Scholar]
- Gao, Y.; He, H.; Deng, Z.; Zhang, X. Cognitive radio network with energy-harvesting based on primary and secondary user signals. IEEE Access 2018, 6, 9081–9090. [Google Scholar] [CrossRef]
- Werner, J.; Wang, J.; Hakkarainen, A.; Valkama, M.; Cabric, D. Primary user localization in cognitive radio networks using sectorized antennas. In Proceedings of the 2013 10th Annual Conference on Wireless On-demand Network Systems and Services (WONS), Banff, AB, Canada, 18–20 March 2013; pp. 155–161. [Google Scholar]
- Khalid, W.; Yu, H. Sum utilization of spectrum with spectrum handoff and imperfect sensing in interweave multi-channel cognitive radio networks. Sustainability 2018, 10, 1764. [Google Scholar] [CrossRef]
- Ozger, M.; Akan, O.B. On the utilization of spectrum opportunity in cognitive radio networks. IEEE Commun. Lett. 2016, 20, 157–160. [Google Scholar] [CrossRef]
- Khalid, W.; Yu, H. Spatial–temporal sensing and utilization in full duplex spectrum-heterogeneous cognitive radio networks for the internet of things. Sensors 2019, 19, 1441. [Google Scholar] [CrossRef]
- Khalid, W.; Yu, H. Optimal sensing performance for cooperative and non-cooperative cognitive radio networks. Int. J. Distrib. Sens. Networks 2017, 13, 1–9. [Google Scholar] [CrossRef]
- Ren, J.; Zhang, Y.; Zhang, N.; Zhang, D.; Shen, X. Dynamic channel access to improve energy efficiency in cognitive radio sensor networks. IEEE Trans. Wirel. Commun. 2016, 15, 3143–3156. [Google Scholar] [CrossRef]
- Xiang, Z.; Yang, W.; Cai, Y.; Ding, Z.; Song, Y. Secure transmission design in HARQ assisted cognitive NOMA networks. IEEE Trans. Inf. Forensics Secur. 2020, 15, 2528–2541. [Google Scholar] [CrossRef]
- Zhang, J.; Kundu, C.; Dobre, O.A.; Garcia-Palacios, E.; Vo, N. Secrecy performance of small-cell networks with transmitter selection and unreliable backhaul under spectrum sharing environment. IEEE Trans. Veh. Technol. 2019, 68, 10895–10908. [Google Scholar] [CrossRef]
- Xiang, Z.; Yang, W.; Pan, G.; Cai, Y.; Song, Y. Physical layer security in cognitive radio inspired NOMA network. IEEE J. Sel. Top. Signal Process. 2019, 13, 700–714. [Google Scholar] [CrossRef]
- Huynh, T.P.; Son, P.N.; Voznak, M. Secrecy performance of underlay cooperative cognitive network using non-orthogonal multiple access with opportunistic relay selection. Symmetry 2019, 11, 385. [Google Scholar] [CrossRef]
- Qin, M.; Yang, S.; Deng, H.; Lee, M.H. Enhancing security of primary user in underlay cognitive radio networks with secondary user selection. IEEE Access 2018, 6, 32624–32636. [Google Scholar] [CrossRef]

| Symbol | Description |
|---|---|
| 0.50 ( fair model of channel occupancy) | |
| 1.05 W | |
| 0.85 (interference probability to PT is 15% or less for the imperfect sensing) | |
| 0.95 | |
| 0.82 | |
| 0.55 | |
| 0.80 | |
| 0.10 | |
| h | 100m |
| 0.10 W | |
| 0.78 W | |
| 0.22 W | |
| 0.50 mW | |
| 50 kHz | |
| 0.30 bps/Hz | |
| 0.60 bps/Hz |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Khalid, W.; Yu, H.; Noh, S. Residual Energy Analysis in Cognitive Radios with Energy Harvesting UAV under Reliability and Secrecy Constraints. Sensors 2020, 20, 2998. https://doi.org/10.3390/s20102998
Khalid W, Yu H, Noh S. Residual Energy Analysis in Cognitive Radios with Energy Harvesting UAV under Reliability and Secrecy Constraints. Sensors. 2020; 20(10):2998. https://doi.org/10.3390/s20102998
Chicago/Turabian StyleKhalid, Waqas, Heejung Yu, and Song Noh. 2020. "Residual Energy Analysis in Cognitive Radios with Energy Harvesting UAV under Reliability and Secrecy Constraints" Sensors 20, no. 10: 2998. https://doi.org/10.3390/s20102998
APA StyleKhalid, W., Yu, H., & Noh, S. (2020). Residual Energy Analysis in Cognitive Radios with Energy Harvesting UAV under Reliability and Secrecy Constraints. Sensors, 20(10), 2998. https://doi.org/10.3390/s20102998






