1. Introduction
The structure of conventional data compression methods for wireless visual sensor networks (WVSN) could be divided into two parts: the acquisition and the reduction [
1]. This means some redundant information must be captured before being removed, which leads to an unnecessary expense. Since a meaningful image always has a sparse representation under some basis, we might abandon the compression process by means of simply acquiring the useful information. Therefore, a promising technique called compressive sensing (CS) [
2] was proposed in 2006, and it was soon widely used for image compression in WVSN owing to its advantage of consumption reduction at sensor nodes [
3].
At present, the security of WVSN has been challenged by modified cracking methods [
4]. As a result, cryptosystems should be upgraded. Fortunately, chaotic systems offer good ideas to solve this problem due to their characteristics of deterministic randomness, initial value sensitivity, boundedness, etc. [
5,
6]. The most common way is encrypting images with measurement matrices generated by chaotic systems [
7,
8]. For instance, Huang’s work [
9] designed a Toeplitz matrix whose elements were produced by a two-dimensional generalized Arnold map, and then, it was employed to conduct the measurement operation. The work in [
10] also embedded a tent map into CS in a similar way. However, these methods were proven to be vulnerable against the chosen-plaintext attack (CPA) [
11]. Therefore, a great number of studies continued to seek further improvements based on this framework. Some researchers focused on expanding the space of parameter values, but their schemes of combining multiple chaotic systems [
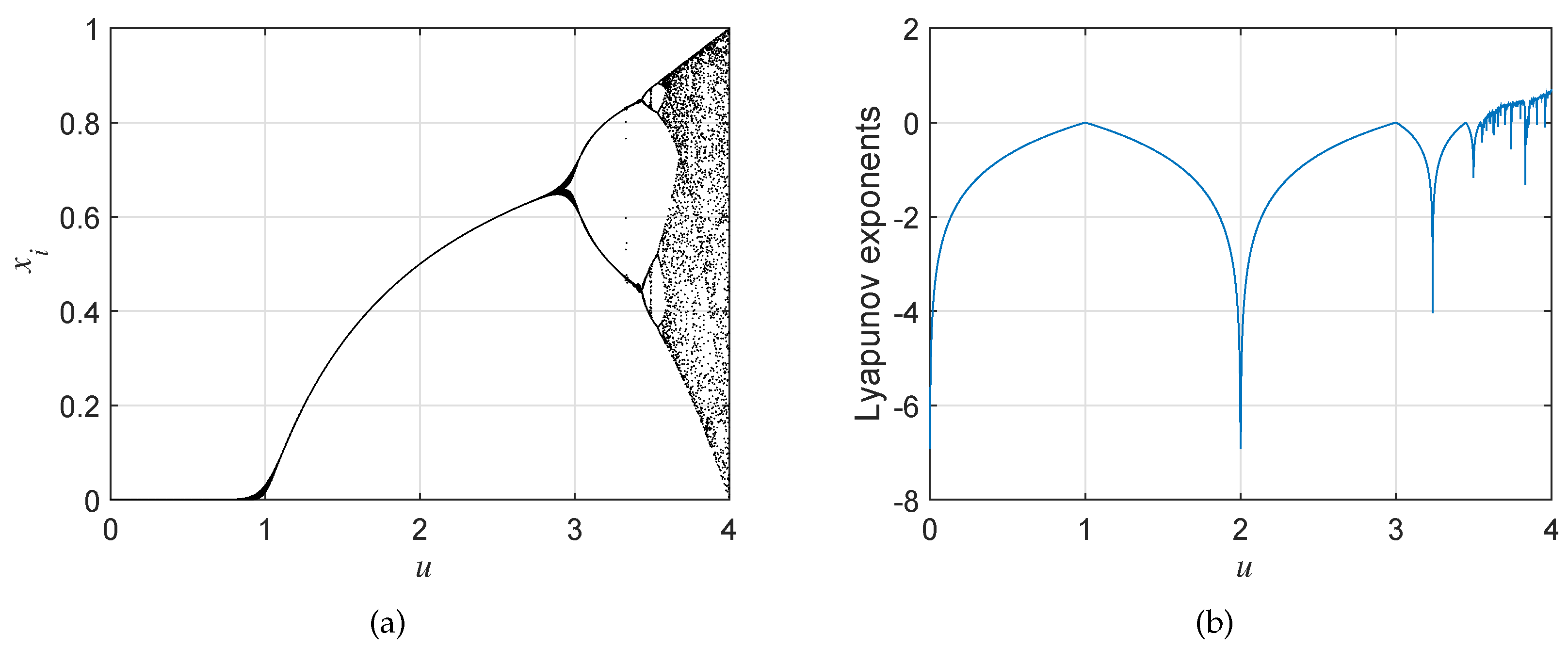
12] or modifying existing chaotic maps [
13,
14,
15] mostly had a few flaws of massive period windows or low Lyapunov exponents. More recently, CS and chaos have been mixed to build a complex structure to obtain extra security assurance. For example, Zhou et al. [
16] created a serial and parallel hybrid scheme, which was beneficial to apply mature encryption algorithms based on chaos. This measure indeed helped to enhance the security performance, but it was still vulnerable against CPA because the measurement process could be considered as a fixed linear projection. In fact, if a cryptosystem can resist CPA, it could be considered secure under all kinds of attacks like the chosen-ciphertext attack (CCA), etc. [
17]. Some recent algorithms based on chaos might tackle this problem, but they are inappropriate for wireless channels because of their poor robustness or high complexity [
6,
18,
19,
20]. For example, the scheme based on the orbit variation of the phase diagram [
6] could indeed resist CPA owing to the relevance between the encryption sequence and plaintext. However, the structure of cipher block chaining (CBC) would cause low performance in anti-jamming, which determines that the cryptosystem can only be used for lossless application. As a result, this article proposes a novel encryption scheme with desirable anti-interference performance based on CS and non-uniform quantization (NQ), which also achieves resisting CPA with less consumption [
6,
21,
22].
On account of the massive data acquired by sensor networks, another major issue in WVSN is the efficiency of communication [
23,
24,
25]. Zhang’s work [
7] claimed that its scheme could encrypt data and compress data simultaneously, but it neglected the fact that the space usage for each element in cipher data with no quantization was more than that in plain data. Therefore, the result of the compression ratio (CR) in [
7] was not accurate. To get a more precise result, we take into account the effect of data precision. Then, the formula of CR could be optimized from:
to:
where
and
are the number of pixels in a cipher image and the number of pixels in a plain image, respectively. Besides,
is the number of binary bits for each pixel in a cipher image, and
is the number of binary bits for each pixel in a plain image. For example,
and
of an eight-bit gray-scale image of size
are 262,144 and eight, respectively. As analyzed above, using CS alone is not enough to improve the efficiency in transmission. Therefore, the measurement result of a scene is usually quantized to be a sequence with finite data precision. To be specific, the size of data in a cipher image should be smaller than that in a plain image. The conventional method to solve this problem is applying uniform quantization (UQ) to the measurement result. However, the accuracy loss could not be neglected due to its irrational allocation of quantization resources. The quantization error in the centrally-distributed region would be large if consuming too much quantization resources in dealing with few values at the edge of the distribution region for measurement results, according to the characteristic that the pseudo-random measurement results are close to a Gaussian distribution [
26]. Since the importance of each element in the measurement results is equivalent, our idea is to design a self-adaptive NQ method to concentrate quantization resources in the centralized area of data. The performance of this scheme will be evaluated in
Section 4.2.
In conclusion, the main contributions of this work contain four aspects. First, the optimized logistic map (OLM) was designed to expand the parameter value space and eliminate the period windows in current chaotic systems. Second, our work modified the formula of CR by taking into account the limited data precision in cipher images, while most papers ignored this fact and calculated CR with the assumption of infinite data precision. Third, in order to maintain the ability of anti-interference while ensuring that the encryption framework based on CS can resist CPA, a self-adaptive NQ method was proposed. Ultimately, the performance of anti-jamming in the proposed cryptosystem was better than that in existing schemes according to the theories’ analysis and simulation results.
The rest of this paper is organized as follows. The preliminary knowledge and designed OLM are introduced in the next section. Then, in
Section 3, the framework and detailed steps of the proposed cryptosystem are illustrated. After that, simulation results and the corresponding theories’ analysis are described in detail in
Section 4. The last section concludes all work mentioned in this paper.
3. The Proposed Cryptosystem
In some recent studies about WVSN, the traditional charge coupled device (CCD) camera was replaced by a single pixel camera [
31], which contributes to consumption reduction in sensor nodes. Based on this, the framework proposed by this paper was designed as
Figure 3 shows. A chaotic sequence controlled by the secret key, as can be seen, was utilized to generate measurement matrix
for CS. After the measurement result
was obtained, an operation of NQ based on a parameter-variable non-linear transform was executed to get quantized data
. Then, another two chaotic sequences were utilized to confuse and substitute
separately, which helped to improve the security of cipher data
. In the decryption process, symbol “
” stands for an inverse operation. According to this scheme, the decryption part was simply an inverse operation of encryption one mentioned above, except for a reconstruction step. As a result, only the encryption process is elaborated in this section.
The encryption process could be divided into three steps:
Eventually, cipher image would be sent to the terminal user directly or through some medium nodes. Additive noise was drawn in the framework to model the interference in the wireless channel.
4. Simulation and Analysis
Although the scenarios at sensor nodes could be converted to plain images of various in sizes, gray-scale levels, and color patterns, they could all be separated easily [
6]. For simplicity, this paper assumed that all the plain and cipher images were eight-bit gray-scale. That is to say, all pixel values in this paper were unsigned integers in eight bits (UINT8) ranging from 0–255. Studies have proven that information of a meaningful image always has a sparse representation under some basis. Without loss of generality, the discrete cosine transformation (DCT) matrix was taken as the sparse basis
. Then, we assumed a vector
was the vectorized scene of size
at a sensor node, and it could be recovered precisely if measurement matrix
met the requirements proposed in
Section 2.1. The cyclic-structured chaotic matrix mentioned above was utilized to construct measurement matrix
. Since this work does not focus on the research of reconstruction, a commonly-used greedy algorithm called OMP was directly applied in the reconstruction process. In this section, some standard images are taken as examples to evaluate the performance of the security and anti-jamming of the proposed scheme.
4.1. Security Performance
4.1.1. Ability of Resisting CPA
Most cryptosystems could be simplified to:
where
is the element’s index in the vectorized cipher image associated with the
element in the vectorized plain image by the confusion operation. Besides,
,
,
, and
are the
element in the vectorized cipher image, the
element in the vectorized plain image, the
element in the chaotic encryption sequence, and a fixed function containing exclusive or (XOR) and modulus operations, respectively. For a certain secret key,
could be considered as an invariant, which causes the result that
only depends on
and
. Obviously, it could be cracked easily by CCA [
36] or CPA [
21].
On the basis of the theories analyzed in [
6], the most popular way to resist CPA and CCA is modifying the encryption sequence with the plain image as:
where
is a fixed non-linear function. According to this model, a tiny residual in the recovered image would cause a huge error in the generation of the encryption sequence, which greatly affects the anti-jamming performance of a cryptosystem.
Fortunately, CS could solve this problem ideally. The mathematical model of existing schemes based on CS is:
where
represents the
row and the
column element in measurement matrix
and
stands for the
element in the vectorized plain image. In Equation (
11), each pixel
in the vectorized plain image is influenced by all pixels in the corresponding cipher image, and each pixel in a cipher image is influenced by all pixels in the corresponding plain image. These characteristics could help to resist most cracking methods. For example, the work in [
36] obtained the starting point for CCA by analyzing matrix
, which revealed the causality relations between cipher pixels and plain pixels in the decryption process. However, all elements in matrix
would be “1” for methods based on CS, which causes a failure in pursuing breakthroughs with
. Furthermore, due to the fact that each element in the cipher image involves all information about the plain image, the anti-jamming performance of the cryptosystem based on Equation (
11) is better than those based on Equation (
10).
Nevertheless, this scheme could be cracked within limited steps by some differential cryptanalysis methods based on CPA [
21]. For example, with some plain images for which all elements are zeros, but only one element has a value of one, a cryptanalyst could acquire information about every column of measurement matrix
. This information could be accumulated and decomposed easily because of the linear relationship between the cipher image and the plain image. In conclusion, cryptosystems based on Equation (
11) are vulnerable against CPA.
In the proposed scheme, the encryption process has been modified to:
where
stands for a parameter-variable non-linear function, whose parameters are relevant to the statistical characteristics of plain image
. In other words, this scheme would alter the encryption model as soon as the plain image changes. Moreover, it converts the relationship between cipher images and plain images from linear to non-linear, which helps to resist differential cryptanalysis methods based on CPA.
4.1.2. Key Space and Key Sensitivity
The key space of a cryptosystem should be larger than
to resist a brute-force attack [
37]. In fact, this requirement is quite easy to be met by using various kinds of chaotic systems. For example, the parameter value
f and initial value
in an OLM could be taken as a secret key. Assume that the data type of the chaotic system is Float32 (32 binary bits); one OLM would require a key containing
bits. Hence, the three chaotic maps applied in
Figure 3 needed a total of
bits for secret key, which was big enough to meet the requirement of key space. Furthermore, the length of a key could be adjusted according to the practical situations by means of locking some parameters or replacing OLM with a more complicated chaotic system.
The key sensitivity of a cryptosystem requires that the cipher images encrypted with different secret keys should be different and that the decrypted images should be unrecognized with incorrect keys. This paper assumes that a tiny change of
in the initial value of OLM
has occurred. Then, the corresponding cipher image would be drastically changed as shown in
Figure 5. On the other hand, decryption is proven to fail in
Figure 6 with the hypothesis that the parameter value in OLM
contains an error of
. Therefore, for our scheme, images can only be reconstructed by correct secret keys.
4.1.3. Statistical Histogram
The statistical histograms of images could cause information disclosure to attackers, so cipher images should conceal this kind of information. As shown in
Figure 7, all encrypted images were alternated to be uniformly distributed by the substitution method shown in Equation (
8), and this was based on the pseudo-random sequence generated by OLM
.
4.1.4. Correlation Coefficients
Between two adjacent elements of a plain image, there always exists a strong correlation that is adverse to the security of the cryptosystem. As we know, the confusion process could eliminate this defect by randomly scrambling all elements of a image. To testify to the effect, the correlation of 4096 pairs selected by adjacent pixels in the vertical, horizontal, and diagonal directions, respectively, from the sample image of a baboon is drawn in
Figure 8. Furthermore, the corresponding coefficients were calculated by the formula [
34]:
where:
In this formula,
N is the number of pixel pairs selected, while
and
stand for the values of the
pixel pair. Besides,
represents the estimation of the mathematical expectations of
, and
is the variance of
. Furthermore,
returns the estimation of the covariance between
and
. The correlation of adjacent pixels was reduced significantly, according to
Figure 8 and
Table 1. Moreover, the performance of the proposed scheme is compared to related works in
Table 2, which helps to evaluate its performance objectively. As can be seen, the performance of the decorrelation by the proposed method was similar to those of existing works.
4.1.5. Differential Analysis
The number of pixels change rate (NPCR) and the unified average changing intensity (UACI) are the general indicators of cryptosystems in the assessment of the performance in resisting differential attacks. Their definitions could be expressed as:
and:
respectively. Here,
is the absolute value, and
n denotes the number of pixels. In addition,
and
represent the coherence of two cipher images in the location
and the pixel value of element
in Cipher Image 1, respectively. Specifically, the optimum values of NPCR and UACI in eight-bit gray-scale images of size
are
and
, respectively [
42]. This paper assumed two similar plain images with a difference of one bit encrypted to be cipher
and cipher
. Then, UACI could be obtained by Equation (
15). Besides, the corresponding matrix
should be calculated to get the result of NPCR. To be specific,
was set to zero as long as
was identical to
. Otherwise, it should be set to one.
The results of NPCR and UACI with the proposed scheme are listed in
Table 3. As this table shows, they were very close to the optimum values. Furthermore, the results of other works are compared with ours in
Table 4. It can be found that the NPCR and UACI of the proposed encryption scheme were acceptable, but worse than some current methods. The primary reason was that, CBC mode was discarded by this paper for the purpose of boosting anti-jamming performance. In fact, if there exists a higher demand for NPCR and UACI, designers could manage this by adding more rounds of confusion and substitution operations.
4.1.6. Randomness Analysis
Evaluating the randomness of cryptographic sequences generated by chaotic systems is necessary in designing encryption schemes. At present, most studies [
43,
44] utilized NIST SP 800-22 as their testing suite. It is a random number testing software approved by the National Institute of Standards (NIST). According to its requirements, the testing results’
p-values should be greater than the significance level
(
) if passing the corresponding tests. In this section, we construct a sample with a length of 4M bits by random parameters and initial states for implementing all 17 tests and list the results in
Table 5. Obviously, the proposed OLM could successfully pass NIST SP 800-22 tests.
4.1.7. Efficiency Analysis
Considering the parallel computing ability in the measurement process of CS, FPGA are preferred to be utilized as embedded processors in the front nodes. Although the hardware implementation has not been completed yet, theory analysis and simulation experiments can also evaluate the efficiency of the proposed scheme to some extent. According to the structure mentioned in
Section 3, the proposed scheme merely added an operation of non-linear transform, in contrast to existing methods based on CS. Therefore, the time and space complexity of the designed method was still
, where
is the number of pixels in a cipher image. The time consumption of the encryption and decryption process for the proposed method is listed in
Table 6 in seconds. Besides, the results of some related references are compared in
Table 7. Simulation results indicated that the efficiency of our scheme was high enough and approximate to other schemes. It is worth mentioning that the simulation experiments were performed on a Apple Laptop MD760 with the operating system Windows 7. In addition, MATLAB R2014b and plain images of size
were utilized.
4.1.8. Information Entropy
Information entropy
is taken as a statistical measure of uncertainty in communication theory [
47]. It could be expressed by:
where
s is a discrete random-variable and
is the probability density function of the occurrence of
. If every symbol has an equal probability (
), then the entropy
, and this is the ideal case. In the cryptosystem for images, the entropy of cipher images should be approximately eight. Simulation experiments were implemented, and the corresponding results are listed in
Table 8. It can be found that the information entropy in cipher images was very close to the ideal value, and this means the encryption scheme can resist entropy attack.
4.2. Anti-Jamming Performance
When calculating the CR and the peak signal-to-noise ratio (PSNR) of a recovered image, most people might neglect the fact that all image data have finite precision. Since all pixel values were assumed to be UINT8, the formula of CR could be simplified from Equation (
2) to Equation (
1) under this hypothesis. Besides, our paper calculates the PSNR of the reconstructed image in the traditional way by:
where
is the maximum value of elements in an image (
in this paper) and
is the mean squared error of the recovered image.
According to Equation (
12), the encryption model proposed depended on the statistical information of the plain image. Therefore, it was not sensitive to each element of the cipher image. As a result, the proposed scheme was more robust than the methods based on Equation (
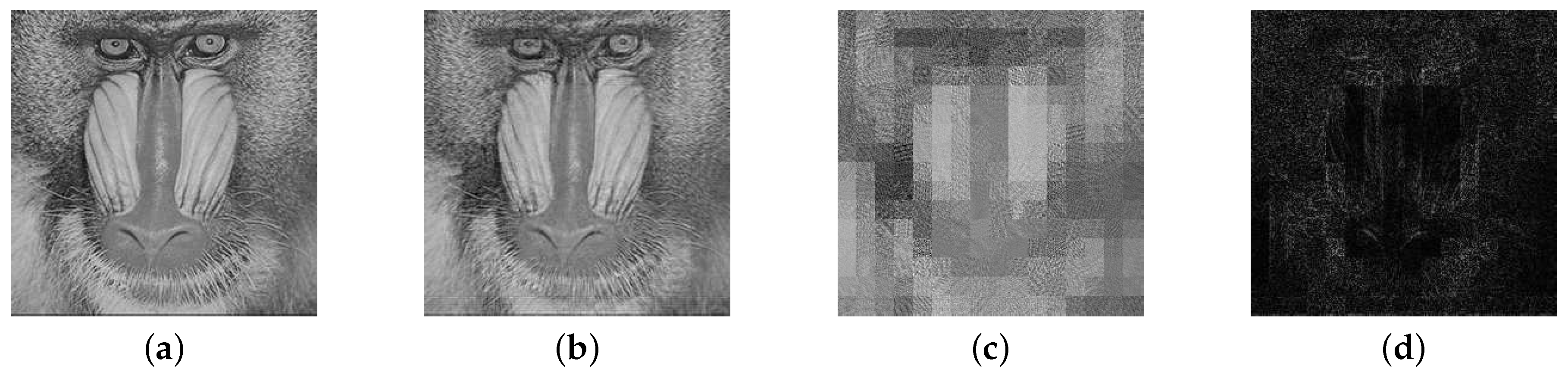
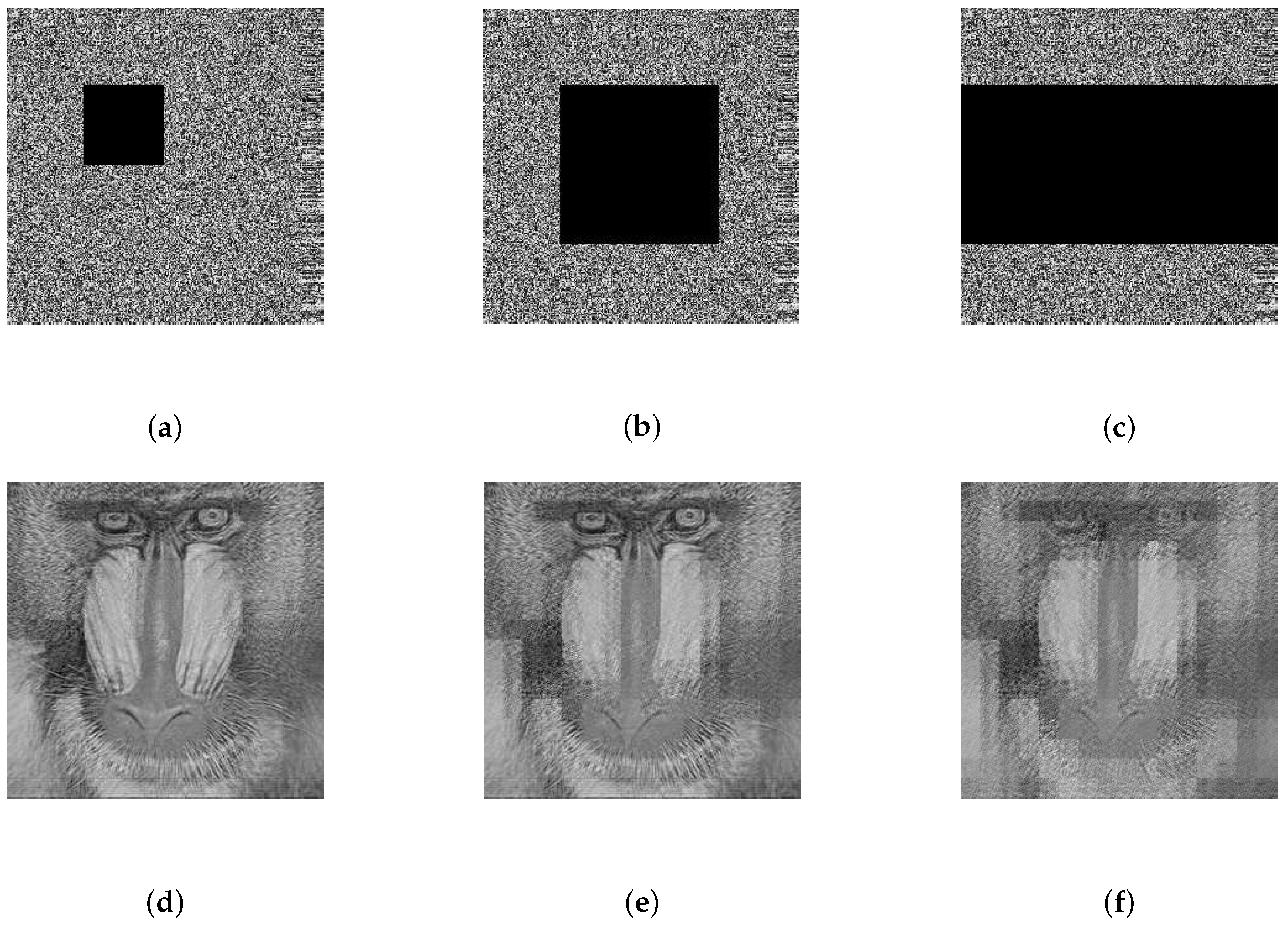
10) if the cipher image was altered. Since strong noise and severe data loss are major forms of interference in the wireless channel, this section simulates these situations to evaluate the anti-jamming performance of the proposed scheme. The image of the baboon was taken as an example to simulate
,
, or
occlusion in the corresponding cipher image, and it was also taken as an example to simulate zero-mean additive white Gaussian noise (AWGN) with standard deviations of 40, 60, or 80 in the corresponding cipher image. The results shown in
Figure 9a–f and
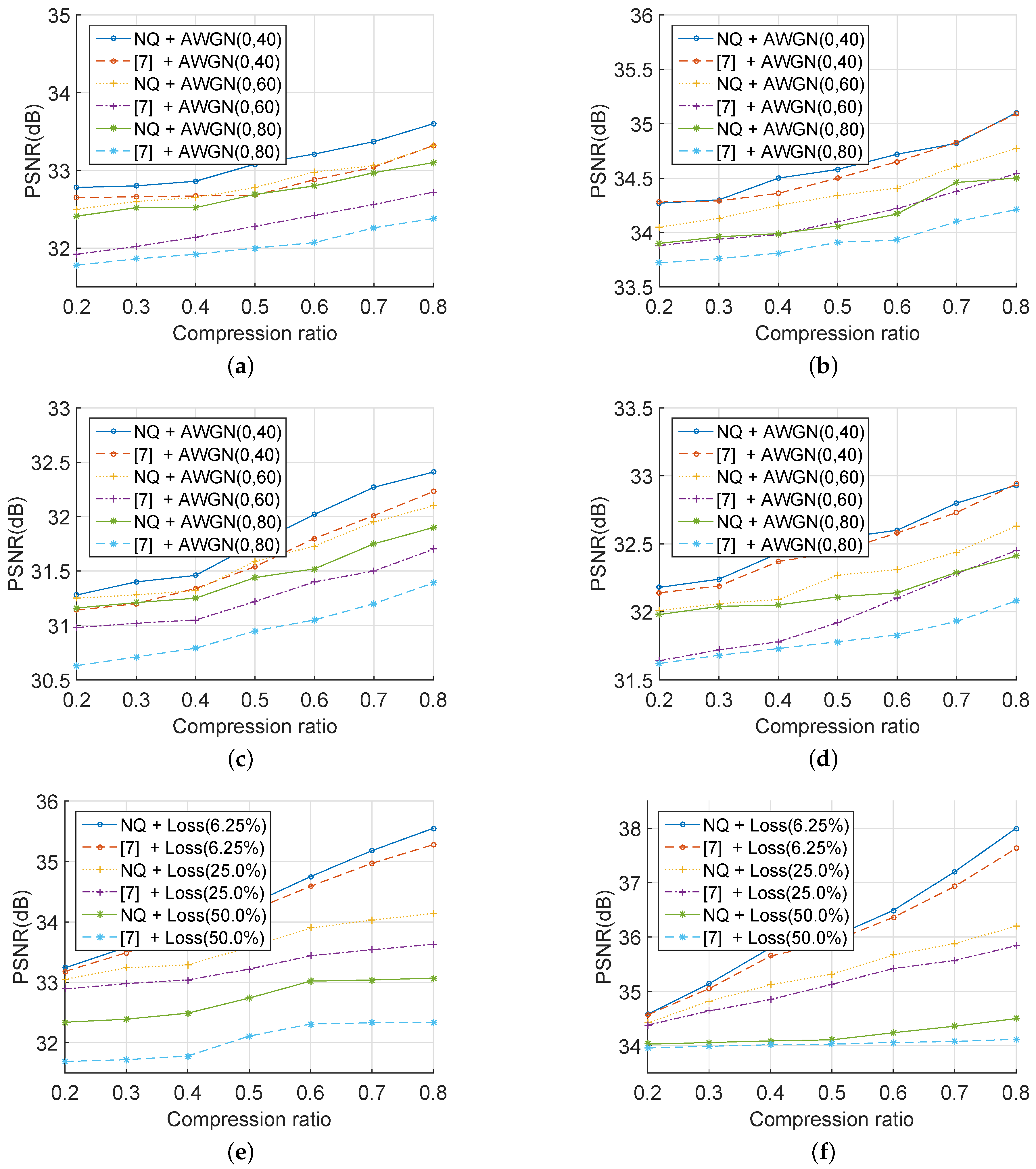
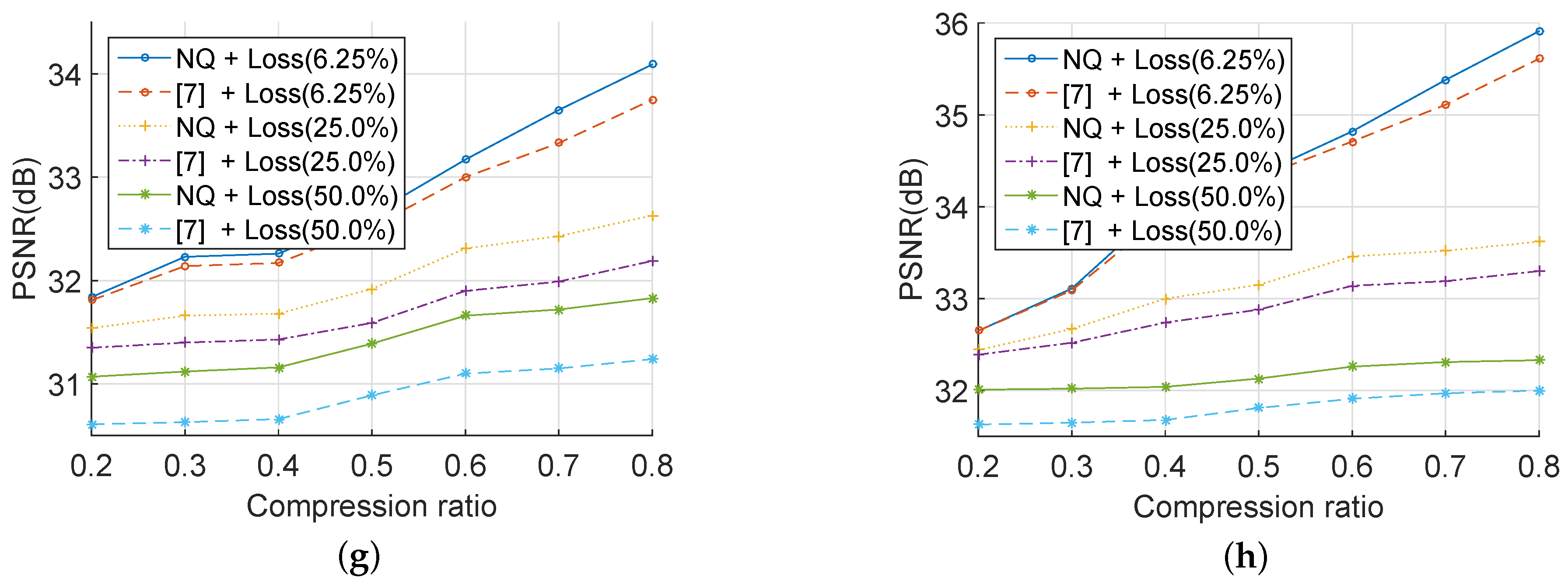
Figure 10a–c indicate that the proposed cryptosystem had satisfactory robustness.
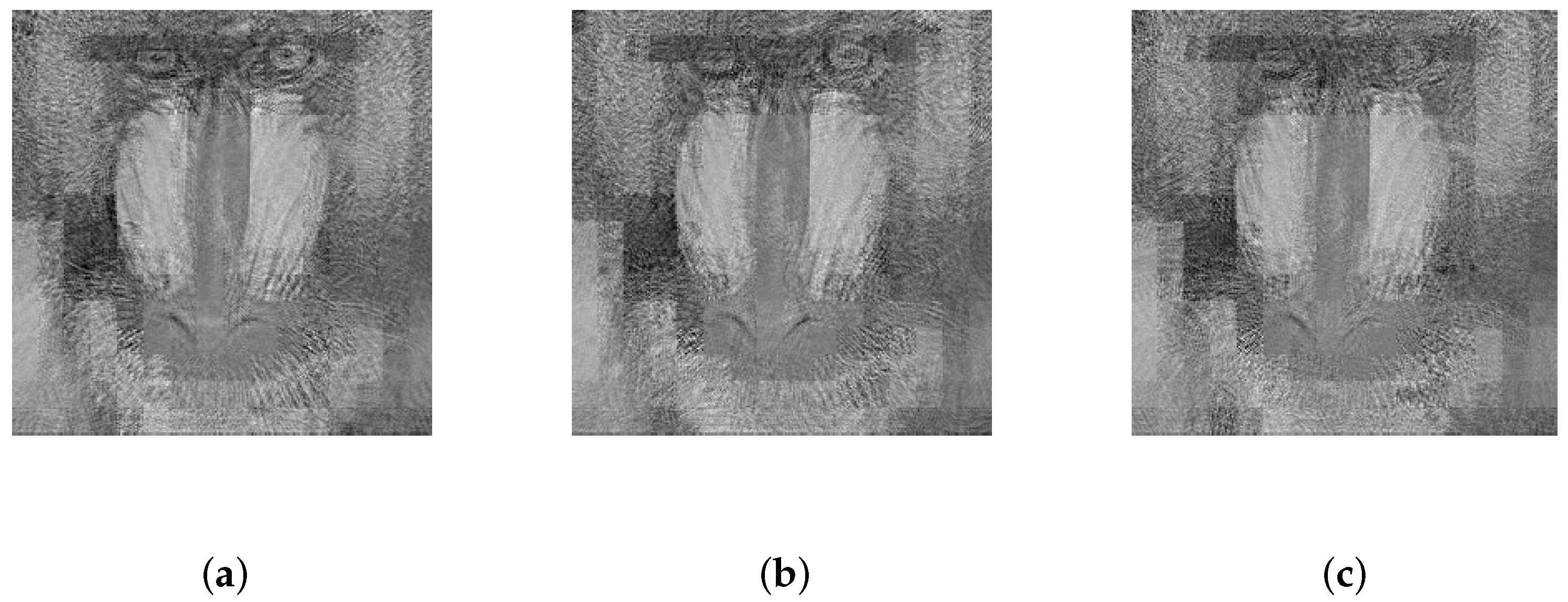
Then, with the same reconstruction algorithm and measurement matrix, the evaluation results were compared with those in [
7].
Figure 11 illustrates that the PSNR of a recovered image was positively related to the CR of the corresponding cipher image. In other words, the outcome depended on the number of rows in the measurement matrix
. As can be seen,
Figure 11a–d demonstrates that, under different compression ratios, the PSNR of recovered images with the proposed scheme was approximate to or higher than that with the method in [
7] under powerful AWGN. Besides,
Figure 11e–h shows that, in the situation of severe data loss, the PSNR of the decrypted images with the proposed scheme was better than that with the method in [
7]. All results in
Figure 11 were obtained by 100 Monte Carlo simulation experiments in MATLAB R2014b. In conclusion, the proposed scheme could help to improve the performance in adverse communication circumstances, such as in an intense AWGN environment or in a severe data loss situation.