A Small Subgroup Attack on Bitcoin Address Generation
Abstract
1. Introduction
2. Preliminaries
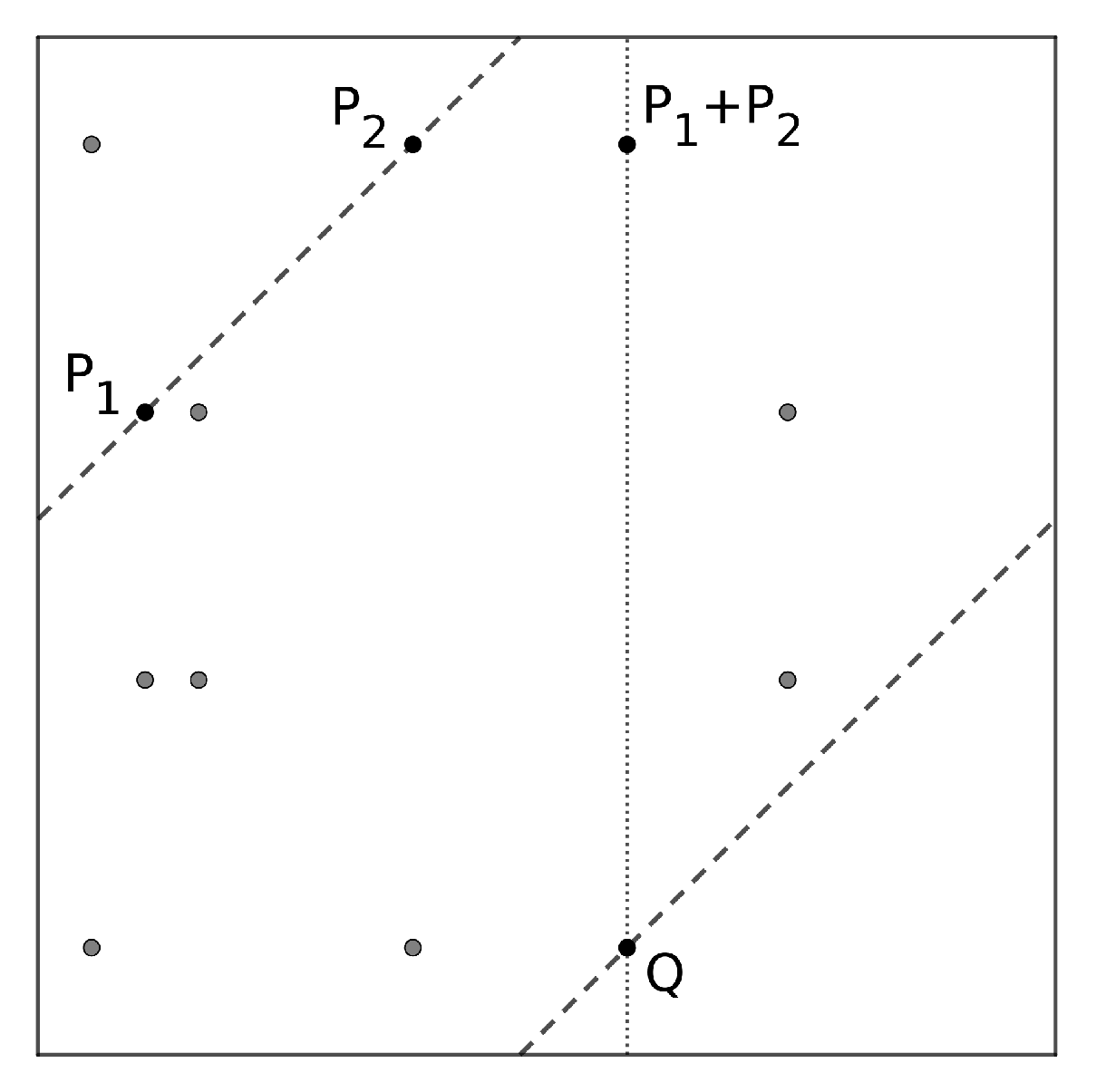
2.1. Elliptic Curve Discrete Logarithm Problem
2.2. The Bitcoin Address Generation
2.2.1. Public Key Generation
2.2.2. Address Generation
3. A Small Subgroup Attack
3.1. Subgroup Detection
3.2. Subgroup Inspection
- 1PSRcasBNEwPC2TWUB68wvQZHwXy4yqPQ3,
- 1B5USZh6fc2hvw2yW9YaVF75sJLcLQ4wCt,
- 1EHNa6Q4Jz2uvNExL497mE43ikXhwF6kZm,
- 1JPbzbsAx1HyaDQoLMapWGoqf9pD5uha5m.
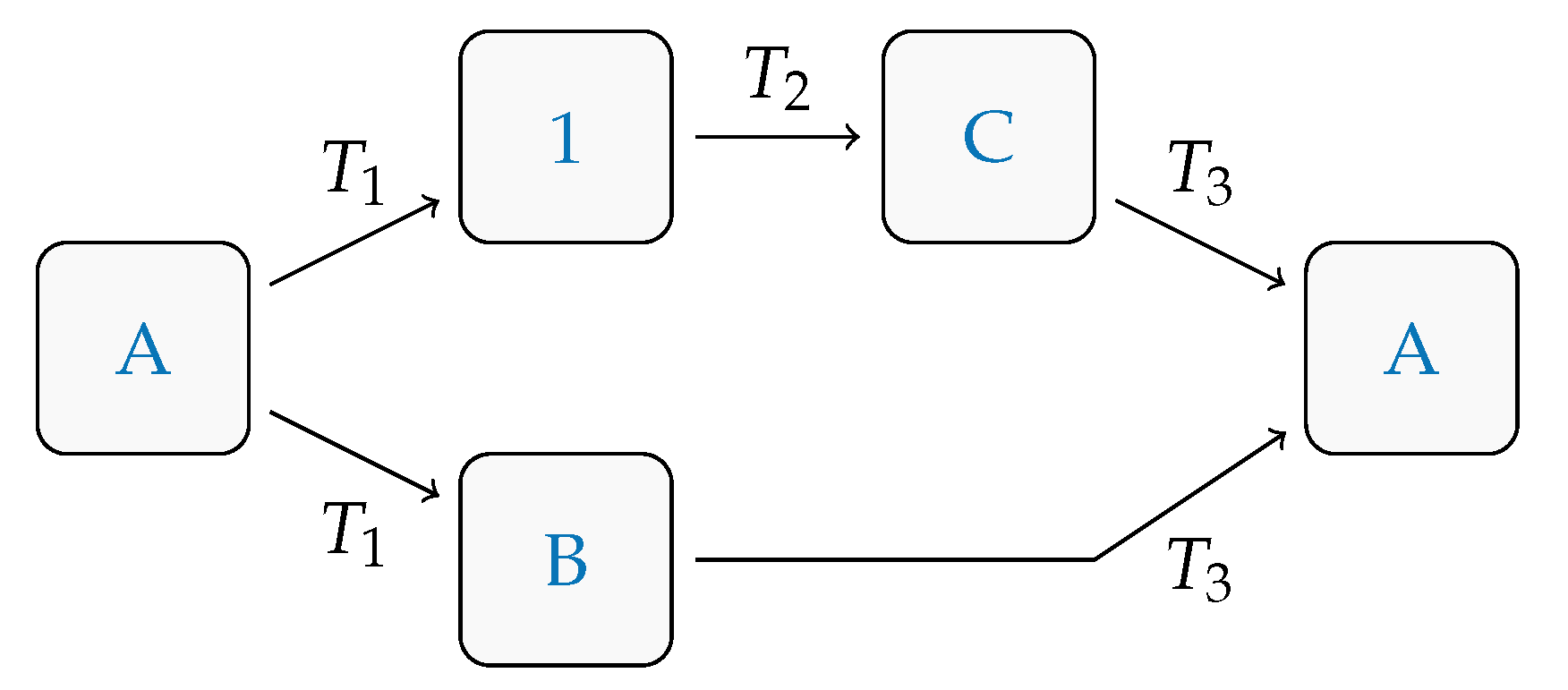
- A.
- 1FCuka8PYyfMULbZ7fWu5GWVYiU88KAU9W,
- B.
- 1NChjA8s5cwPgjWZjD9uu12A5sNfoRHhbA,
- C.
- 1695755gMv3fJxYVCDitMGaxGu7naSXYmv,
- T1.
- 69ad7033376cea2bbea01e7ef76cc8d7bc028325e9179b2231ca1076468c1a1e,
- T2.
- 1dd5c256a1acc81ea4808a405fd83586ea03d8b58e29a081ebf3d0d95e77bf63,
- T3.
- b722c77dcdd13c3616bf0c4437f2eb63d96346f74f4eeb7a1e24c1a9711fc101.
4. Discussion and Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. 2008. Available online: https://bitcoin.org/bitcoin.pdf (accessed on 5 May 2020).
- Narayanan, A.; Bonneau, J.; Felten, E.; Miller, A.; Goldfeder, S. Bitcoin and Cryptocurrency Technologies: A Comprehensive Introduction; Princeton University Press: Princeton, NJ, USA, 2016; Available online: https://press.princeton.edu/books/hardcover/9780691171692/bitcoin-and-cryptocurrency-technologies (accessed on 5 May 2020).
- Chen, W.; Xu, Z.; Shi, S.; Zhao, Y.; Zhao, J. A Survey of Blockchain Applications in Different Domains. In Proceedings of the 2018 International Conference on Blockchain Technology and Application ICBTA 2018, Xi’an China, 10–12 December 2018; Association for Computing Machinery: New York, NY, USA, 2018; pp. 17–21. [Google Scholar] [CrossRef]
- Blockchains: The Great Chain of Being Sure about Things. The Economist. 2015. Available online: https://www.economist.com/briefing/2015/10/31/the-great-chain-of-being-sure-about-things (accessed on 5 July 2020).
- Alharby, M.; Aldweesh, A.; van Moorsel, A. Blockchain-based Smart Contracts: A Systematic Mapping Study of Academic Research. In Proceedings of the 2018 International Conference on Cloud Computing, Big Data and Blockchain (ICCBB) 2018, Fuzhou, China, 15–17 November 2018. [Google Scholar] [CrossRef]
- Eyal, I. Blockchain Technology: Transforming Libertarian Cryptocurrency Dreams to Finance and Banking Realities; IEEE: Piscataway, NJ, USA, 2017; pp. 38–49. [Google Scholar] [CrossRef]
- Foodchain. Available online: https://food-chain.it/ (accessed on 5 June 2020).
- Chowdhury, M.J.M.; Colman, A.; Kabir, M.A.; Han, J.; Sarda, P. Blockchain as a Notarization Service for Data Sharing with Personal Data Store. In Proceedings of the 2018 17th IEEE International Conference on Trust, Security and Privacy in Computing and Communications/12th IEEE International Conference on Big Data Science and Engineering (TrustCom/BigDataSE), New York, NY, USA, 1–3 August 2018. [Google Scholar] [CrossRef]
- Lin, I.C.; Liao, T.C. A Survey of Blockchain Security Issues and Challenges. Netw. Secur. 2017, 19, 653–659. [Google Scholar] [CrossRef]
- Meneghetti, A.; Sala, M.; Taufer, D. A Survey on PoW-based Consensus. Ann. Emerg. Technol. Comput. AETiC 2020, 4, 8–18. [Google Scholar] [CrossRef]
- Lim, C.H.; Lee, P.J. A Key Recovery Attack on Discrete Log-Based Schemes Using a Prime Order Subgroup. In Annual International Cryptology Conference; Springer: Berlin/Heidelberg, Germany, 1998; pp. 249–263. [Google Scholar] [CrossRef]
- Sogiorno, D. Una Famiglia di Chiavi Deboli Nel Bitcoin, CRYPTANALYSIS: A Key Tool in Securing and Breaking Ciphers. 2020. Available online: http://www.decifris.it/2020/crittanalisi2020.html (accessed on 5 May 2020).
- Galbraith, S.D.; Gaudry, P. Recent progress on the elliptic curve discrete logarithm problem. Des. Codes Cryptogr. 2016, 78, 51–72. [Google Scholar] [CrossRef]
- Silverman, J.H. The Arithmetic of Elliptic Curves; Springer: Berlin/Heidelberg, Germany, 1986. [Google Scholar]
- Lidl, R.; Niederreiter, H. Finite Fields; Cambridge University Press: Cambridge, UK, 1996. [Google Scholar] [CrossRef]
- Vo, S.C. A Survey of Elliptic Curve Cryptosystems, Part I: Introductory. In NASA Advanced Supercomputing Division; NAS Technical Report—NAS-03-012; 2003. Available online: https://www.nas.nasa.gov/assets/pdf/techreports/2003/nas-03-012.pdf (accessed on 18 May 2020).
- Certicom Research. SEC 2: Recommended Elliptic Curve Domain Parameters. 2000. Available online: http://www.secg.org/sec2-v2.pdf (accessed on 18 May 2020).
- Penard, W.; van Werkhoven, T. On the Secure Hash Algorithm Family, Cryptography in Context. Chapter 1. 2007. Available online: https://www.staff.science.uu.nl/~tel00101/liter/Books/CrypCont.pdf (accessed on 18 May 2020).
- Dobbertin, H.; Bosselaers, A.; Preneel, B. RIPEMD-160: A Strengthened Version of RIPEMD. In International Workshop on Fast Software Encryption; Springer: Berlin/Heidelberg, Germany, 1996; pp. 71–82. [Google Scholar] [CrossRef]
- Antonopoulos, A.M. Base58 and Base58Check Encoding. In Mastering Bitcoin; O’Reilly: Sevastopol, CA, USA, 2015; Available online: https://www.oreilly.com/library/view/mastering-bitcoin-2nd/9781491954379/ch04.html#base58 (accessed on 20 May 2020).
- Blockchain.com. Available online: https://www.blockchain.com/explorer?view=btc (accessed on 20 May 2020).

© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Sala, M.; Sogiorno, D.; Taufer, D. A Small Subgroup Attack on Bitcoin Address Generation. Mathematics 2020, 8, 1645. https://doi.org/10.3390/math8101645
Sala M, Sogiorno D, Taufer D. A Small Subgroup Attack on Bitcoin Address Generation. Mathematics. 2020; 8(10):1645. https://doi.org/10.3390/math8101645
Chicago/Turabian StyleSala, Massimiliano, Domenica Sogiorno, and Daniele Taufer. 2020. "A Small Subgroup Attack on Bitcoin Address Generation" Mathematics 8, no. 10: 1645. https://doi.org/10.3390/math8101645
APA StyleSala, M., Sogiorno, D., & Taufer, D. (2020). A Small Subgroup Attack on Bitcoin Address Generation. Mathematics, 8(10), 1645. https://doi.org/10.3390/math8101645





