A Reliable and Privacy-Preserving Vehicular Energy Trading Scheme Using Decentralized Identifiers
Abstract
1. Introduction
1.1. Motivation
1.2. Contributions
- •
- We propose a reliable and privacy-preserving vehicular energy trading scheme using decentralized identifiers (DIDs) and verifiable credential (VC) technologies. The energy purchaser’s DID is not revealed during the authentication process at the reservation phase. Additionally, completed transaction information is not recorded in a public ledger but in VCs.
- •
- In order to ensure reliability in energy trading, the initial VC shared during the reservation phase is incomplete. When the transaction parties successfully perform the energy trade, the signature of the CS is added to the VC, and it becomes valid.
- •
- We analyze the proposed scheme using an ROR model and AVISPA simulation for demonstrating it resists malicious attacks and attains security features.
- •
- We compare the performance and security features of the proposed scheme and related works to showcase the security and efficiency of our approach.
2. Related Work
2.1. Decentralized Energy Trading System for Electric Vehicles
- •
- Elimination of single points of failure: In a centralized system, all information is processed through a central authority, creating a vulnerability. Blockchain decentralizes transaction processing, reducing the risk of system-wide failure due to a single compromised node.
- •
- Data integrity and immutability: Blockchain records transactions in a manner that ensures data cannot be tampered with. This immutability is crucial for maintaining accurate and trustworthy records in EV energy trading systems, which allows for robust auditing and accountability.
- •
- Enhanced security through decentralization: By distributing transactions across a network of nodes, blockchain-based systems are inherently more secure against cyber-attacks. Encrypted data and consensus-based verification methods provide additional layers of protection.
- •
- Increased trust and transparency: In a blockchain-based system, all participants can view the transaction history, which enhances transparency. This transparency builds trust among users, as they can independently verify the accuracy and legitimacy of transactions.
2.2. Privacy Protection and Reliability Research for Decentralized Energy Trading Systems
3. Preliminaries
3.1. Elliptic Curve Cryptosystem (ECC)
- Elliptic curve discrete logarithm problem (ECDLP): given a base point G and point , it is difficult to find the in probability polynomial time.
- Elliptic curve decisional Diffie–Hellman problem (ECDDHP): given a base points G and two points and , it is difficult to compute in probability polynomial time.
3.2. Elliptic Curve Pedersen Commitment
- Setup: Let G be a random generator point on and be a chosen generator point, where . The trusted authority publishes .
- Commit: The committer creates a commitment C; are random numbers, and , where represents a dedicated value created by the committer.
- Open: To confirm the authenticity of C, the committer reveals x and r, and the verifier checks if .
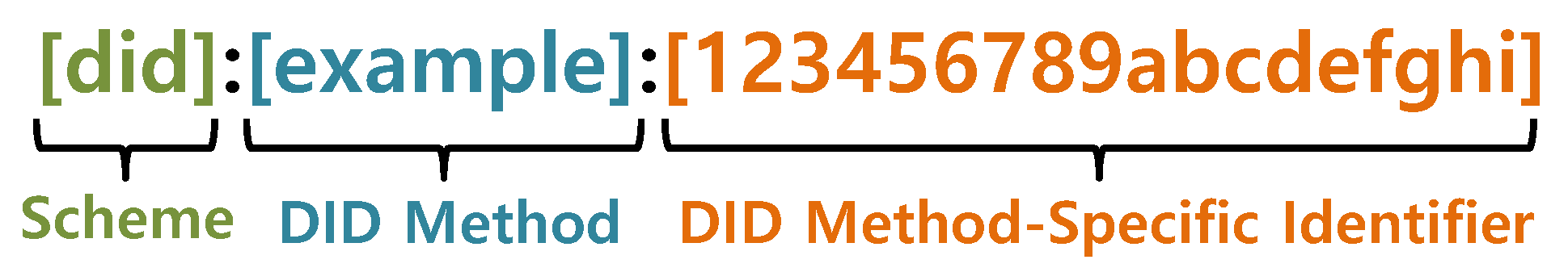
3.3. Decentralized Identifiers (DIDs)
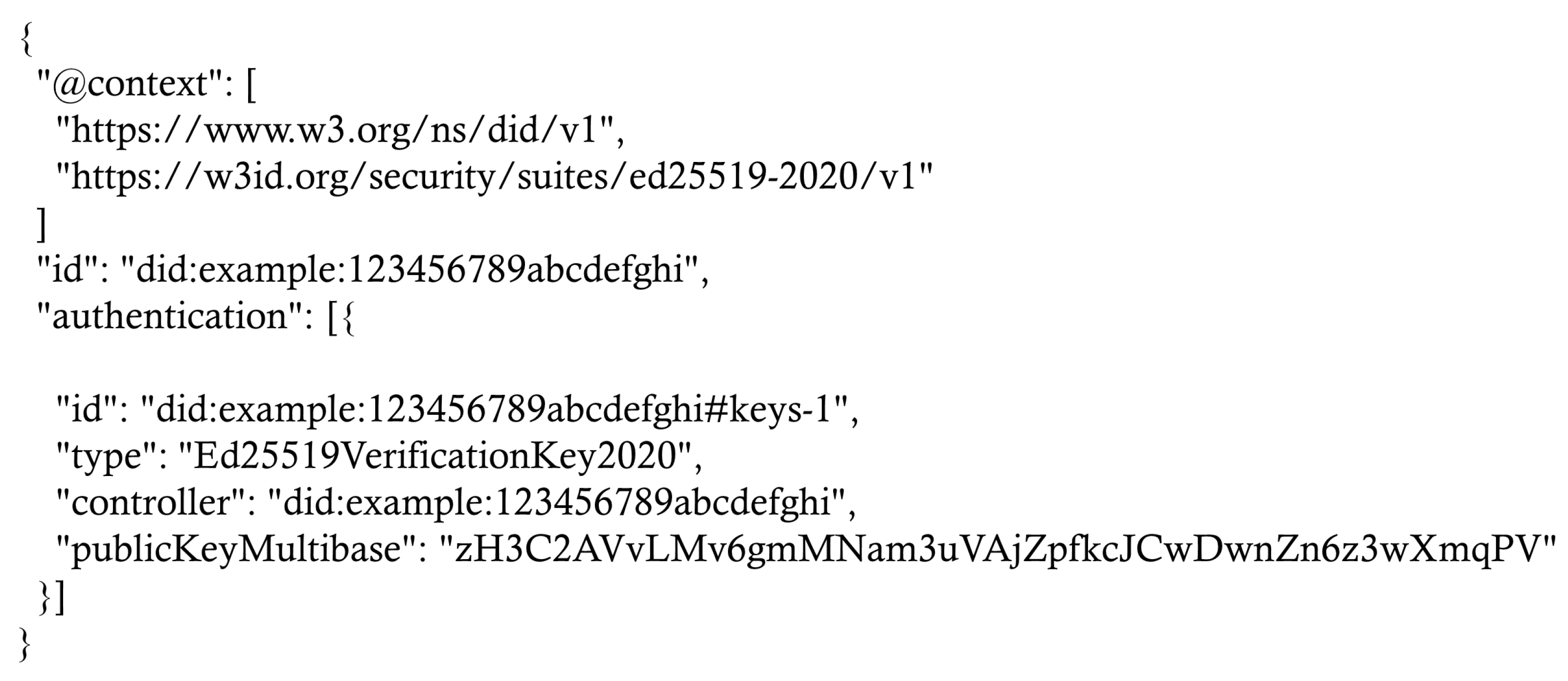
3.4. Verifiable Credentials (VCs)
4. Proposed Model
- Electric vehicles (EVs): EVs embedded with OBU devices can communicate with external entities through dedicated short range communication (DSRC) or wireless access in vehicular environment (WAVE) and store data securely. Bidirectional EVs can purchase energy (charge) from electric vehicle supply equipment (EVSE) and sell energy to external loads (discharge). In this paper, we refer to the first vehicle as the energy purchaser and the second vehicle as the energy seller.Energy seller (ES): To sell surplus energy, the ES generates a bid containing the selling price, transaction time, energy volume, and other relevant information; then, it sends it to other EVs via the RSU. When the ES receives a message from an EP seeking to reserve an energy transaction, it verifies the message and shares the incomplete credentials and session key with the EP. Subsequently, the ES transfers energy and commitment to the promised CS according to the credential information and then completes the credentials by adding the signature received from the CS.Energy purchaser (EP): After selecting the optimal bid price, the EP sends a reservation message to the ES to plan energy trading. In the reservation phase, the EP shares incomplete credentials and a session key with the ES. When the EP arrives at the promised CS, the EP proves its commitment to the ES using the session key. If the proof is correct, the ES gets the energy stored in the CS.In this paper, RSU only provides a wide range of wireless communication services to EVs.
- Smart charging stations (CSs): CSs are equipped with battery energy storage and a communication module for EV charging services. The CS receives the commitment and energy from the ES and stores it. The stored energy is passed on to the EP, who proves the same commitment. CSs are a type of semi-trusted authority. Even if the charging station is attacked by a malicious attacker, there is no advantage to the attacker because the charging station does not have specific information about the energy trading.
- Blockchain: The proposed energy trading system utilizes a public blockchain. Public blockchains are fully decentralized infrastructures, allowing all nodes on the network to easily participate without the intervention of a trusted authority and preventing single points of failure. To ensure that all participants in the system agree on a single source of truth, consensus algorithms are employed. In our system, this source comprises DID documents rather than energy trading information between EVs.
5. Proposed Scheme
5.1. Initialization Phase
5.2. DID Generation Phase
5.3. Submitting Bids Phase
- Step 1: user enters identity and password and computes , , , . Then, verifies whether . If it matches, generates a random number and a current timestamp and computes , , signature , and a bid to sell surplus energy, where denote an amount of energy to sell, a selling price, an expiration time for the transaction, respectively. propagates .
- Step 2: checks the freshness of timestamp and uses to retrieve the corresponding DID document. Then, computes and checks whether . It is essential for to select the best bid and, at the same time, check the validity of the bid.
5.4. Reservation Phase
- Step 1: inputs and and then computes , , , . checks . If it is valid, generates a random number and a timestamp and computes , , , , , . Then, sends to .
- Step 2: checks the timestamp and computes , . Then, retrieves ’s document using to obtain and computes , . verifies the signature through .
- Step 3: When and select the optimal charging station for energy trading, generates a temporary credential recording a signature and information about the negotiated transaction and sends encrypted with to .
- Step 4: decrypts the using and verifies the signature of recorded in . After that, adds payment information and a signature to . Then, sends encrypted with to and stores .
- Step 5: decrypts using and verifies the signature of recorded in . Then, stores .
5.5. Charging Phase
5.5.1. Discharging
- Step 1: generates an and a timestamp . Next, computes , , , , , and sends to
- Step 2: checks the freshness of the and calculates , . If matches, generates and sends to .
- Step 3: calculates and verifies using ’s public key. If the signature is valid, records in and transmits vehicular energy and to .
- Step 4: stores in a database and energy in battery storage.
5.5.2. Charging
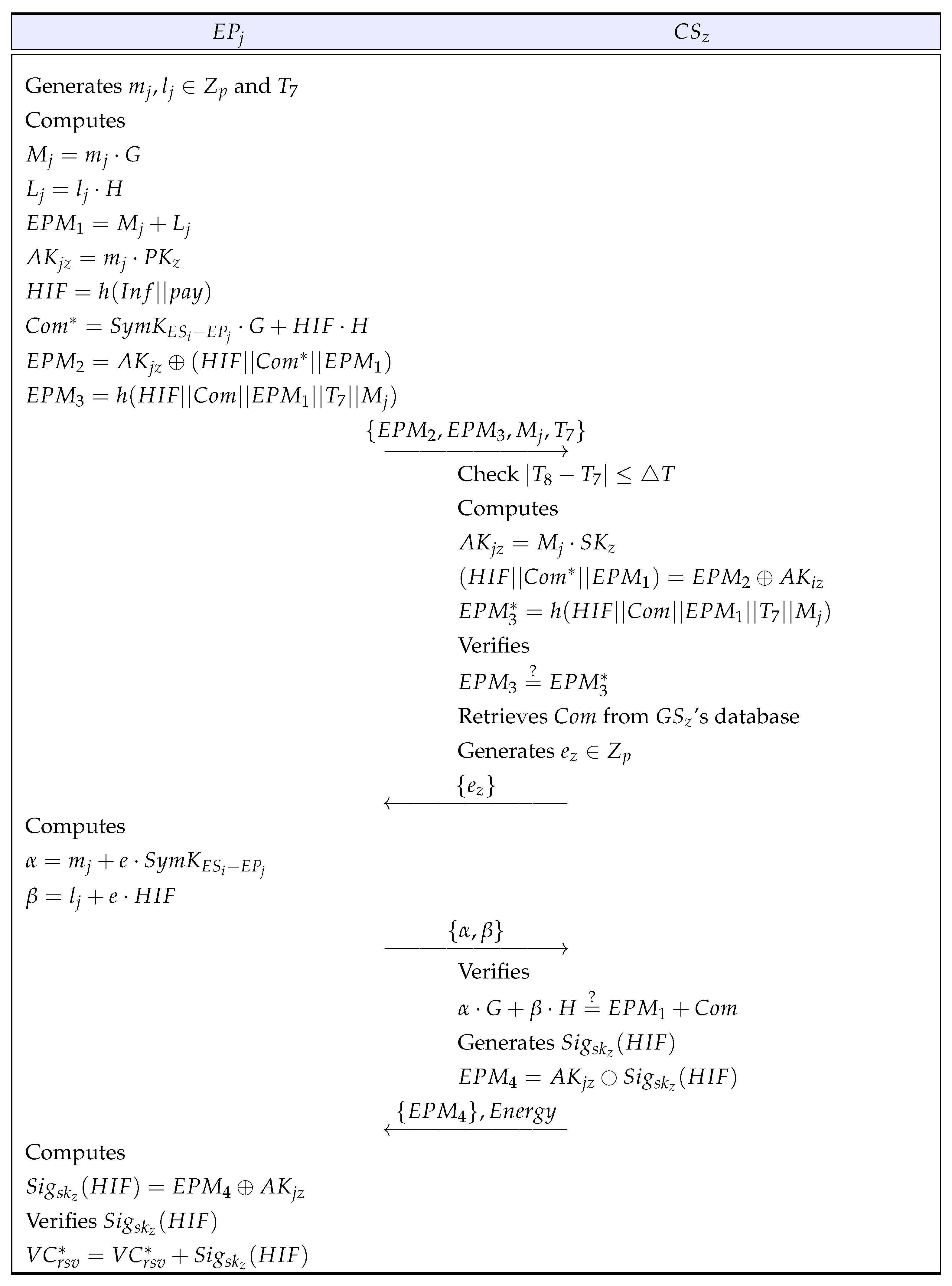
- Step 1: generates random numbers , and timestamps and computes , , , , , , , . Then, sends to .
- Step 2: After receiving the message from , verifies the freshness of the message. calculates , , and checks whether is correct. If it is correct, retrieves and sends a random number to .
- Step 3: computes , and submits to
- Step 4: If is correct, generates , and transfers to .
- Step 5: calculates and verifies using ’s public key. If the signature is valid, records in .
6. Security Analysis
6.1. Informal Analysis
- Impersonation attack: Malicious attackers can attempt to impersonate a legitimate vehicle. However, as mentioned in Section 3.1, due to ECDLP and ECDDHP, attackers find it challenging to compute the vehicle’s private key and session key , making it difficult to impersonate a legitimate vehicle. Therefore, the proposed scheme is secure against an impersonation attack.
- Replay attack: Attackers can intercept messages transmitted over a public channel and resend or delay them to obtain sensitive information or to execute other security attacks. However, since messages transmitted over the public channel include timestamps and random numbers, recipients can verify the freshness of the message. Therefore, the proposed scheme is secure against replay attacks.
- Man-in-the-middle (MITM) attack: Attackers can participate in communication between two legitimate vehicles during the reservation phase to collect valuable information about the users and to later attempt to forge messages using this information. However, due to the use of one-way hash functions, random numbers, and timestamps, the integrity and freshness of the message is ensured. Additionally, since signatures are generated using private keys , attackers cannot create valid authentication messages. Therefore, the proposed scheme is secure against a man-in-the-middle attack.
- Confidentiality: In the proposed scheme, the DID of the energy purchaser is not exposed in order to conceal transactions between the energy seller and purchaser. However, the DID of the energy seller is exposed to publicly verify the legitimacy of the seller and invoices. Additionally, the charging station, which manages the energy received from the energy seller, provides energy only to vehicles that present the correct commitment , thus not requiring information about the energy purchaser. Moreover, only the parties involved in the energy transaction possess verifiable credentials to prove their participation.
- Reliability: To ensure the reliability of energy transactions between two vehicles in the proposed scheme, both vehicles share verifiable credentials during the reservation phase. These credentials are not valid until they obtain the signature from the charging station. As both vehicles successfully delegate and accept energy through the charging station, they can complete their credentials by obtaining the signature value from the charging station. Therefore, the proposed scheme provides reliability to energy traders so that they can proceed with the normal energy trading process.
- Mutual authentication: and authenticate each other. authenticates by checking whether is correct during the reservation phase. authenticates by verifying whether is correct during the submitting bids phase. Therefore, the proposed scheme ensures mutual authentication.
6.2. Formal Analysis
6.2.1. ROR model
- Game 0: is considered to be ’s real attacks in our proposed scheme. picks a random bit c at the beginning of . Then, we obtain the following equation:
- Game 1: indicates that executes an eavesdropping attack, in which the transmitted messages are intercepted between and . For this game, executes a query to obtain the communicated messages. After the end of this game, carries out , and queries to compromise session key . To derive , needs the short-term secret values and and private keys and . Hence, ’s probability of winning by eavesdropping on the messages does not increase. Therefore, we obtain the result as follows:
- Game 2: is considered to be active/passive attacks by executing and queries to find hash collision. can intercept the transmitted messages from the submitting bids phase to the reservation phase. The intercepted messages are safeguarded by the collision-resistant one-way hash function . Furthermore, tries to derive by using intercepted messages. However, needs to break the ECDDHP (defined in Section 3.1) in polynomial time t, which is a computationally infeasible problem for to derive . By applying the ECDDHP and the birthday paradox result, we obtain the inequality
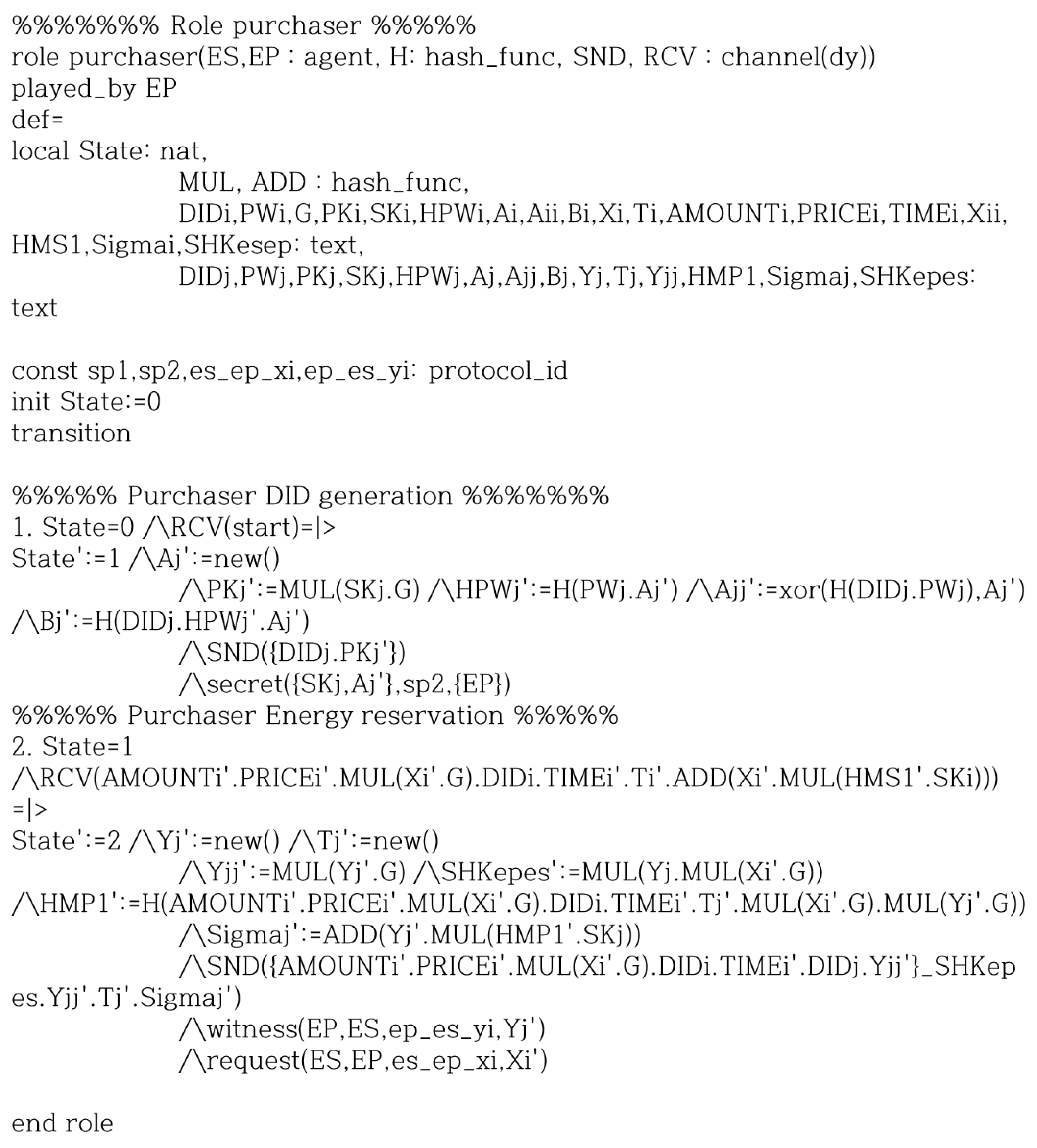
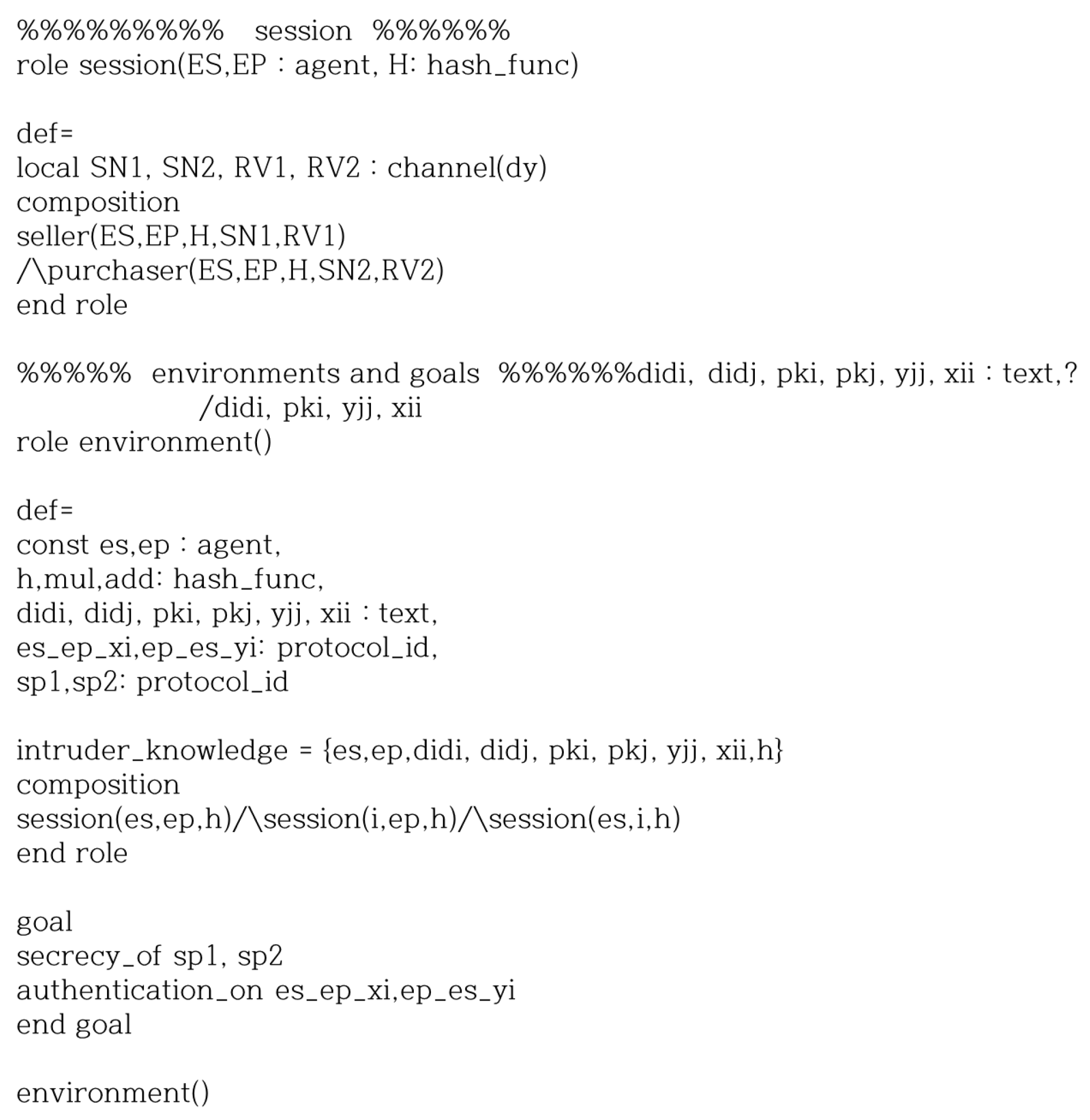
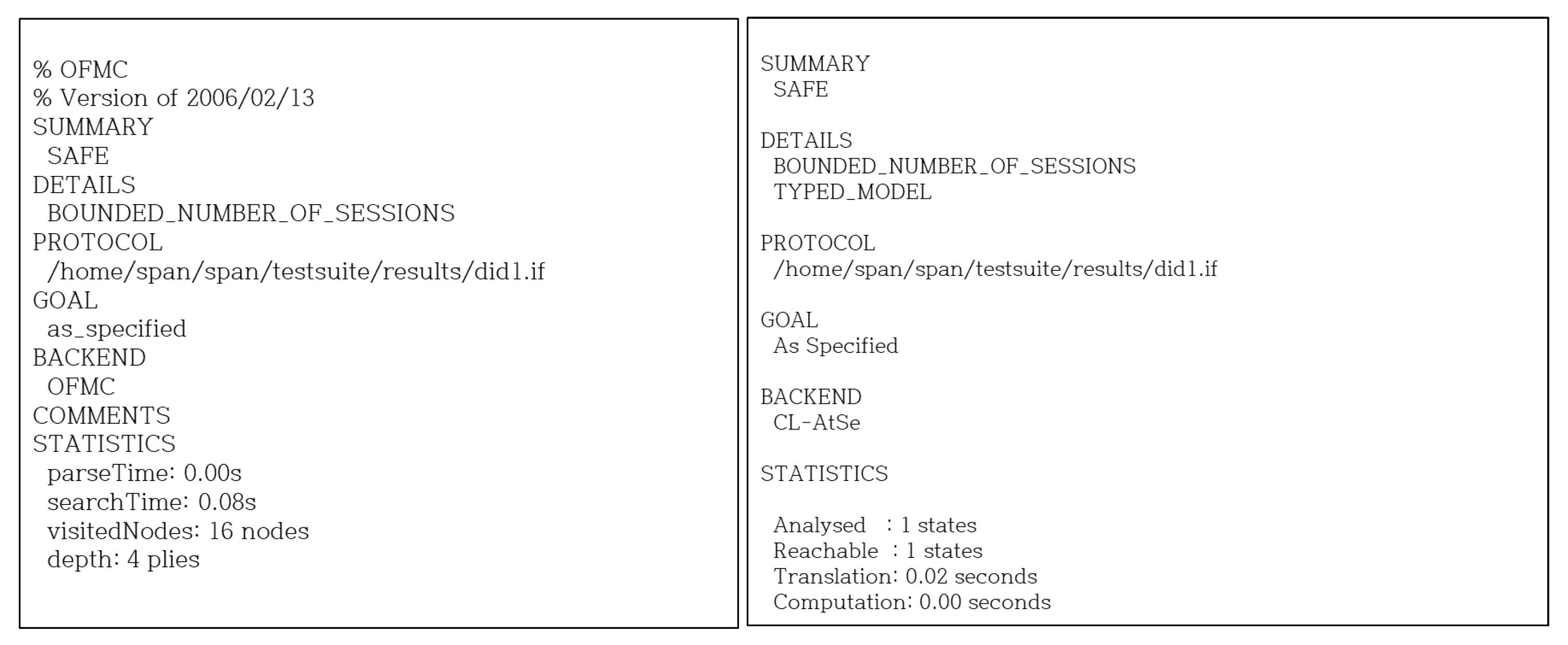
6.2.2. AVISPA Simulation
7. Performance Analysis
7.1. Security Features
7.2. Computation Cost Analysis
7.3. Communication Cost Analysis
8. Conclusions
Author Contributions
Funding
Data Availability Statement
Conflicts of Interest
References
- Global EV Outlook: Understanding the Electric Vehicle Landscapeto. 2020. Available online: https://www.ourenergypolicy.org/wp-content/uploads/2013/09/GlobalEVOutlook_2013.pdf (accessed on 8 April 2024).
- Electric Car Demand Growing, Global Market Hits 740,000 Units. Available online: https://cleantechnica.com/2015/03/28/ev-demand-growing-global-market-hits-740000-units/ (accessed on 8 April 2024).
- Mouli, G.R.C.; Kefayati, M.; Baldick, R.; Bauer, P. Integrated PV charging of EV fleet based on energy prices, V2G and offer of reserves. IEEE Trans. Smart Grid 2019, 10, 1313–1325. [Google Scholar] [CrossRef]
- Zhong, W.; Xie, K.; Liu, Y.; Yang, C.; Xie, S. Topology-aware vehicle-to-grid energy trading for active distribution systems. IEEE Trans. Smart Grid 2019, 10, 2137–2147. [Google Scholar] [CrossRef]
- Alvaro-Hermana, R.; Fraile-Ardanuy, J.; Zufiria, P.J.; Knapen, L.; Janssens, D. Peer to peer energy trading with electric vehicles. IEEE Intell. Transp. Syst. Mag. 2016, 8, 33–44. [Google Scholar] [CrossRef]
- Shurrab, M.; Singh, S.; Otrok, H.; Mizouni, R.; Khadkikar, V.; Zeineldin, H. An efficient vehicle-to-vehicle (V2V) energy sharing framework. IEEE Internet Things J. 2021, 9, 5315–5328. [Google Scholar] [CrossRef]
- Umesh, B.S.; Khadkikar, V.M.; Zeineldin, H.; Singh, S.; Otrok, H.; Mizouni, R. Direct electric vehicle to vehicle (V2V) power transfer using on-board drivetrain and motor windings. IEEE Trans. Ind. Electron. 2021, 69, 10765–10775. [Google Scholar]
- Global EV Outlook. 2020. Available online: https://www.iea.org/reports/global-ev-outlook-2020 (accessed on 8 April 2024).
- Electric Vehicle Market by Component, Vehicle (Passenger Cars, CV), Propulsion (BEV, PHEV, FCEV), Vehicle Drive Type (FWD, RWD, AWD), Vehicle Top Speed (<125 mph, >125 mph), Charging Point, Vehicle Class, V2G, Region-Global Forecast 2030. Available online: https://www.marketsandmarkets.com/Market-Reports/electric-vehicle-market-209371461.html (accessed on 8 April 2024).
- Chekired, D.A.; Khoukhi, L.; Mouftah, H.T. Fog-computing-based energy storage in smart grid: A cut-off priority queuing model for plug-in electrified vehicle charging. IEEE Trans. Ind. Inform. 2020, 16, 3470–3482. [Google Scholar] [CrossRef]
- Zhang, P.; Qian, K.; Zhou, C.; Stewart, B.G.; Hepburn, D.M. A methodology for optimization of power systems demand due to electric vehicle charging load. IEEE Trans. Power Syst. 2012, 27, 1628–1636. [Google Scholar] [CrossRef]
- Chen, J.; Zhang, Y.; Su, W. An anonymous authentication scheme for plug-in electric vehicles joining to charging/discharging station in vehicle-to-Grid (V2G) networks. China Commun. 2015, 12, 9–19. [Google Scholar] [CrossRef]
- Yan, Q.; Zhang, B.; Kezunovic, M. Optimized operational cost reduction for an EV charging station integrated with battery energy storage and PV generation. IEEE Trans. Smart Grid 2019, 10, 2096–2106. [Google Scholar] [CrossRef]
- Li, Z.; Kang, J.; Yu, R.; Ye, D.; Deng, Q.; Zhang, Y. Consortium blockchain for secure energy trading in industrial Internet of Things. IEEE Trans. Ind. Informat. 2018, 14, 3690–3700. [Google Scholar] [CrossRef]
- Aggarwal, S.; Kumar, N.; Gope, P. An efficient blockchain-based authentication scheme for energy-trading in V2G networks. IEEE Trans. Ind. Informat. 2020, 17, 6971–6980. [Google Scholar] [CrossRef]
- Li, D.; Yang, Q.; An, D.; Yu, W.; Yang, X.; Fu, X. On location privacy-preserving online double auction for electric vehicles in microgrids. IEEE Internet Things J. 2019, 6, 5902–5915. [Google Scholar] [CrossRef]
- Yucel, F.; Akkaya, K.; Bulut, E. Efficient and privacy preserving supplier matching for electric vehicle charging. Ad Hoc Netw. 2019, 90, 101730. [Google Scholar] [CrossRef]
- Tandon, R.; Gupta, P.K. SV2VCS: A secure vehicle-to-vehicle communication scheme based on lightweight authentication and concurrent data collection trees. J. Ambient Intell. Human. Comput. 2021, 12, 9791–9807. [Google Scholar] [CrossRef]
- He, Y.; Zhang, C.; Wu, B.; Geng, Z.; Xiao, K.; Li, H. A trusted architecture for EV shared charging based on blockchain technology. High-Confid. Comput. 2021, 1, 100001. [Google Scholar] [CrossRef]
- Huang, X.; Xu, C.; Wang, P.; Liu, H. LNSC: A security model for electric vehicle and charging pile management based on blockchain ecosystem. IEEE Access 2018, 6, 13565–13574. [Google Scholar] [CrossRef]
- Kang, J.; Yu, R.; Huang, X.; Maharjan, S.; Zhang, Y.; Hossain, E. Enabling localized peer-to-peer electricity trading among plug-in hybrid electric vehicles using consortium blockchains. IEEE Trans. Ind. Informat. 2017, 13, 3154–3164. [Google Scholar] [CrossRef]
- Kim, M.; Lee, J.; Oh, J.; Park, K.; Park, Y.; Park, K. Blockchain based energy trading scheme for vehicle-to-vehicle using decentralized identifiers. Appl. Energy 2022, 322, 119445. [Google Scholar] [CrossRef]
- Sun, G.; Dai, M.; Zhang, F.; Yu, H.; Du, X.; Guizani, M. Blockchain-enhanced high-confidence energy sharing in internet of electric vehicles. IEEE Internet Things J. 2020, 7, 7868–7882. [Google Scholar] [CrossRef]
- Son, S.; Lee, J.; Kim, M.; Yu, S.; Das, A.K.; Park, Y. Design of blockchain-based lightweight V2I handover authentication protocol for VANET. IEEE Trans. Netw. Sci. Eng. 2022, 9, 1346–1358. [Google Scholar] [CrossRef]
- Blockchain GDPR Privacy by Design. Available online: https://blockchain.ieee.org/images/files/pdf/blockchain-gdpr-privacy-by-design.pdf (accessed on 8 April 2024).
- Bernabe, J.B.; Canovas, J.L.; Hernandez-Ramos, J.L.; Moreno, R.T.; Skarmeta, A. Privacy-preserving solutions for blockchain: Review and challenges. IEEE Access 2019, 7, 164908–164940. [Google Scholar] [CrossRef]
- Zhang, H.; Wang, J.; Ding, Y. Blockchain-based decentralized and secure keyless signature scheme for smart grid. Eenrgy 2019, 180, 955–967. [Google Scholar] [CrossRef]
- Guan, Z.; Si, G.; Zhang, X.; Wu, L.; Guizani, N.; Du, X.; Ma, Y. Privacy-preserving and efficient aggregation based on blockchain for power grid communications in smart communities. IEEE Commun. Mag. 2018, 56, 82–88. [Google Scholar] [CrossRef]
- Aitzhan, N.Z.; Svetinovic, D. Security and privacy in decentralized energy trading through multi-signatures, blockchain and anonymous messaging streams. IEEE Trans. Dependable Secur. Comput. 2018, 15, 840–852. [Google Scholar] [CrossRef]
- Kumari, A.; Gupta, R.; Tanwar, S.; Tyagi, S.; Kumar, N. When blockchain meets smart grid: Secure energy trading in demand response management. IEEE Netw. 2020, 34, 299–305. [Google Scholar] [CrossRef]
- Gai, K.; Wu, Y.; Zhu, L.; Qiu, M.; Shen, M. Privacy-preserving energy trading using consortium blockchain in smart grid. IEEE Trans. Ind. Inform. 2019, 15, 3548–3558. [Google Scholar] [CrossRef]
- Guan, Z.; Lu, X.; Yang, W.; Wu, L.; Wang, N.; Zhang, Z. Achieving efficient and Privacy-preserving energy trading based on blockchain and ABE in smart grid. J. Parallel Distrib. Comput. 2021, 147, 34–45. [Google Scholar] [CrossRef]
- Xia, S.; Lin, F.; Chen, Z.; Tang, C.; Ma, Y.; Yu, X. A bayesian game based vehicle-to-vehicle electricity trading scheme for blockchain-enabled internet of vehicles. IEEE Trans. Veh. Technol. 2020, 69, 6856–6868. [Google Scholar] [CrossRef]
- Baza, M.; Sherif, A.; Mahmoud, M.M.E.A.; Bakiras, S.; Alasmary, W.; Abdallah, M.; Lin, X. Privacy-preserving blockchain-based energy trading schemes for electric vehicles. IEEE Trans. Veh. Technol. 2021, 70, 9369–9384. [Google Scholar] [CrossRef]
- Li, M.; Hu, D.; Lal, C.; Conti, M.; Zhang, Z. Blockchain-enabled secure energy trading with verifiable fairness in industrial internet of things. IEEE Trans. Ind. Informat. 2020, 16, 6564–6574. [Google Scholar] [CrossRef]
- Yahaya, A.S.; Javaid, N.; Almogren, A.; Ahmed, A.; Gulfam, S.M.; Radwan, A. A two-stage privacy preservation and secure peer-to-peer energy trading model using blockchain and cloud-based aggregator. IEEE Access 2021, 9, 143121–143137. [Google Scholar] [CrossRef]
- Cui, J.; Wu, D.; Zhang, J.; Xu, Y.; Zhong, H. An efficient authentication scheme based on semi-trusted authority in VANETs. IEEE Trans. Veh. Technol. 2019, 68, 2972–2986. [Google Scholar] [CrossRef]
- Chai, H.; Leng, S.; He, J.; Zhang, K.; Cheng, B. Cyberchain: Cybertwin empowered blockchain for lightweight and privacy-preserving authentication in internet of vehicles. IEEE Trans. Veh. Technol. 2022, 71, 4620–4631. [Google Scholar] [CrossRef]
- Cani, A.S.; Bertino, E.; Yuan, D.; Meng, K.; Dong, Z.Y. SPrivAD: A secure and privacy-preserving mutually dependent authentication and data access scheme for smart communities. Comput. Secur. 2022, 115, 102610. [Google Scholar]
- Decentralized Identifiers (DIDs) v1.0 Core Architecture, Data Model, and Representations. Available online: https://www.w3.org/TR/2021/PR-did-core-20210803/ (accessed on 8 April 2024).
- Verifiable Credentials Data Model 1.0 Expressing Verifiable Information on the Web. Available online: https://www.w3.org/TR/2021/REC-vc-data-model-20211109/ (accessed on 8 April 2024).
- Automated Validation of Internet Security Protocols and Applications. Available online: http://www.avispa-project.org/ (accessed on 8 April 2024).






| Query | Description |
|---|---|
| Under this query, performs an eavesdropping attack between and over a public channel. | |
| Under this query, can send the messages to the participant and get the response message accordingly. | |
| Under this query, compromises a current session key between and . | |
| An unbiased coin c is tossed prior to the start of the game, and the result is used to decide the output of the query. If receives , the session key among and is fresh. If receives , the session key is not fresh; otherwise, obtains a null value (⊥). |
| Security and Function Properties | Xia et al. [33] | Baza et al. [34] | Li et al. [35] | Yahaya et al. [36] | Proposed |
|---|---|---|---|---|---|
| ∘ | ∘ | ∘ | ∘ | ∘ | |
| ∘ | ∘ | ∘ | ∘ | ∘ | |
| ∘ | ∘ | ∘ | ∘ | ∘ | |
| ∘ | × | × | ∘ | ∘ | |
| − | ∘ | ∘ | ∘ | ∘ | |
| ∘ | ∘ | ∘ | ∘ | ∘ | |
| × | × | × | × | ∘ | |
| − | × | × | − | ∘ |
| Notation | Depiction | Computation Cost |
|---|---|---|
| one-way hash function | 0.003 ms | |
| point addition operation on elliptic curve | 0.013 ms | |
| scalar point multiplication operation on elliptic curve | 2.373 ms | |
| exponentiation operation on elliptic curve | 0.819 ms | |
| bilinear pairing operation | 6.575 ms | |
| symmetric key encryption (e.g., AES-256) | 0.001 ms | |
| symmetric key decryption | 0.001 ms | |
| asymmetric key encryption (e.g., RSA) | 0.304 ms | |
| asymmetric key decryption | 2.405 ms | |
| signature generation | 0.173 ms | |
| signature verification | 4.194 ms |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2024 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Kim, M.; Park, K.; Park, Y. A Reliable and Privacy-Preserving Vehicular Energy Trading Scheme Using Decentralized Identifiers. Mathematics 2024, 12, 1450. https://doi.org/10.3390/math12101450
Kim M, Park K, Park Y. A Reliable and Privacy-Preserving Vehicular Energy Trading Scheme Using Decentralized Identifiers. Mathematics. 2024; 12(10):1450. https://doi.org/10.3390/math12101450
Chicago/Turabian StyleKim, Myeonghyun, Kisung Park, and Youngho Park. 2024. "A Reliable and Privacy-Preserving Vehicular Energy Trading Scheme Using Decentralized Identifiers" Mathematics 12, no. 10: 1450. https://doi.org/10.3390/math12101450
APA StyleKim, M., Park, K., & Park, Y. (2024). A Reliable and Privacy-Preserving Vehicular Energy Trading Scheme Using Decentralized Identifiers. Mathematics, 12(10), 1450. https://doi.org/10.3390/math12101450








