A Privacy-Preserving Polymorphic Heterogeneous Security Architecture for Cloud–Edge Collaboration Industrial Control Systems
Abstract
1. Introduction
- A privacy-preserving polymorphic heterogeneous security architecture for cloud–edge collaboration ICSs is proposed. Based on the DHR architecture, this framework integrates privacy-preserving mechanisms and closed-loop feedback control to address hardware and software homogeneity, singularity, and vulnerabilities in industrial control systems.
- Based on the proposed architecture, this paper presents a novel privacy-preserving arbitration mechanism that dynamically balances privacy protection with operational efficiency. The scheme introduces a privacy budget parameter that adaptively adjusts the proportion of protected output bits based on real-time threat assessment and arbitration error rates, enabling edge-level preliminary consistency checking while maintaining cloud-level verification capabilities. This adaptive approach leverages the natural advantages of cloud–edge collaboration to ensure data confidentiality while preserving functional correctness and system availability in multi-executor environments.
- To address the challenges of limited heterogeneous resources and underlying homogeneous risks in cloud–edge collaboration ICSs, this paper introduces credibility and heterogeneity metrics and designs a hybrid event-time triggered scheduling strategy based on these metrics for executor management. Simulation-based validation conducted on a natural gas pipeline pressure control system demonstrates that the proposed security architecture significantly strengthens system resilience against false data injection and privacy attacks, thereby confirming the effectiveness of our methodology.
2. Related Work
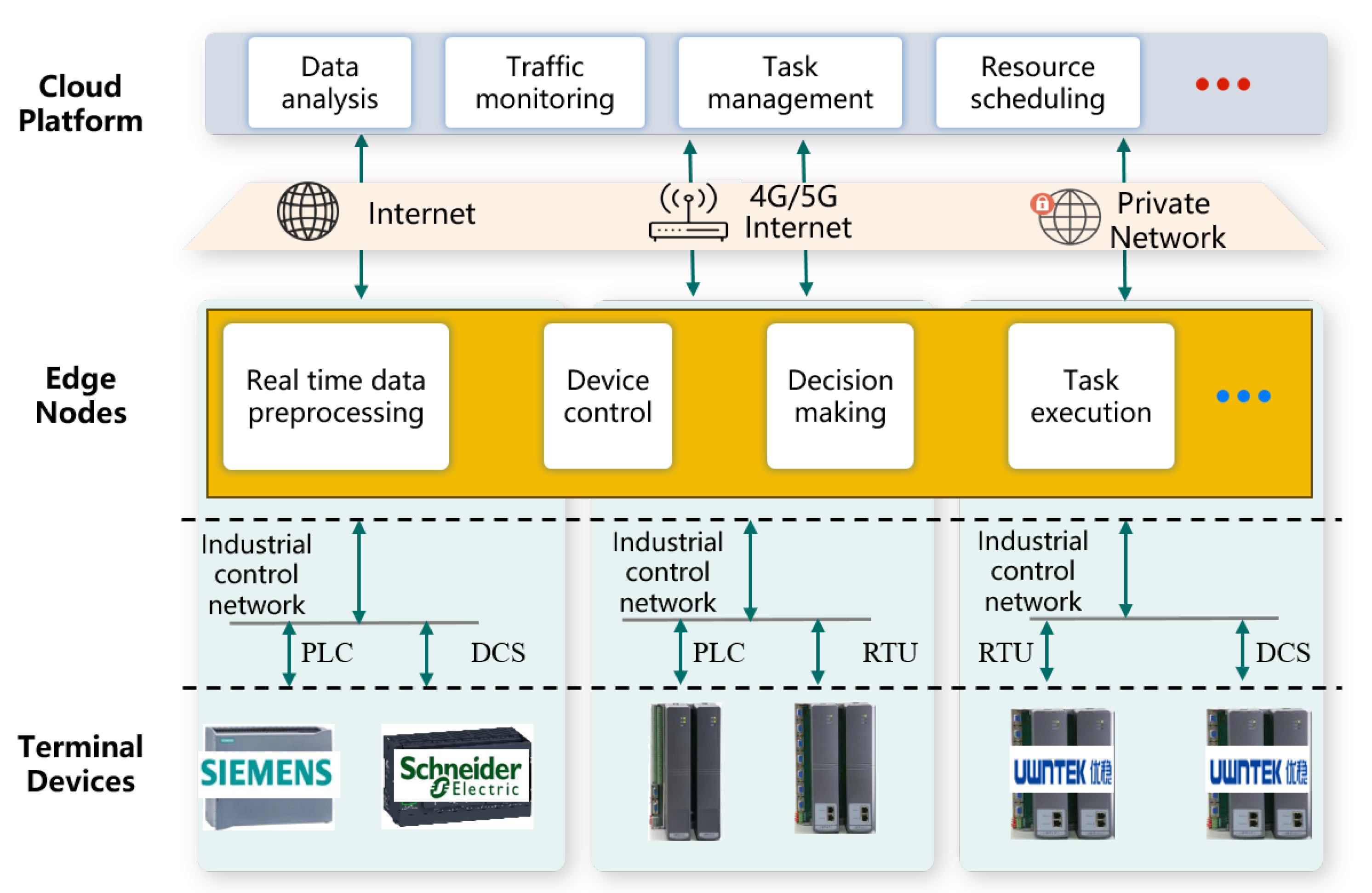
2.1. Cloud–Edge Collaboration ICS Architecture and Security Challenges
2.2. Defense Mechanisms in Cloud–Edge Collaboration ICSs
2.3. Research on Dynamic Heterogeneous Redundancy Architecture
3. System Model
3.1. Proposed Polymorphic Heterogeneous Security Architecture
3.2. Threat Model and Security Assumptions
3.2.1. Attacker Capabilities and Objectives
- Availability Attacks: Adversaries may exploit unknown vulnerabilities within executors to manipulate their operational behavior, causing them to produce erroneous computation results or control outputs. The ultimate objective of such attacks is to compromise system availability by inducing inconsistent or harmful control actions. The attacker possesses the capability to infiltrate individual executors but faces the challenge of compromising a sufficient number of heterogeneous executors simultaneously to overcome the arbitration mechanism.
- Privacy Attacks: We assume sophisticated adversaries can mount side-channel attacks, memory analysis techniques, or advanced persistent threats (APTs) against the arbitration and scheduling module. While unable to alter the module’s functionality, these attacks aim to extract sensitive information processed during arbitration, potentially exposing proprietary algorithms, control parameters, operational data, or system state information that could be leveraged for future attacks.
3.2.2. Component Trust Assumptions
- Trusted Components: We consider both the input agent and output agent as trusted entities within our security model. This assumption is justified by their functional simplicity, uncomplicated structure, and amenability to hardened implementation through specialized hardware or formal verification methodologies. Additionally, these components can be subjected to rigorous physical isolation and strict access control mechanisms, further reinforcing their trustworthiness. The operational simplicity of these agents permits exhaustive security verification, significantly reducing the attack surface.
- Untrusted Components: Each executor within the heterogeneous executor set is considered potentially compromised. We assume that executors may contain unknown vulnerabilities or undocumented backdoors that have not yet been identified or patched. However, we establish that executors operate within strict isolation boundaries, preventing lateral movement or cross-contamination between execution environments.
- Semi-trusted Components: The arbitration and scheduling module is classified as semi-trusted. While we assume it executes its designated algorithms faithfully and performs arbitration functions according to specification, we acknowledge inherent privacy vulnerabilities in its operation. Since this module necessarily processes outputs from all executors and makes critical system decisions, its complexity exceeds that of the input/output agents, making it difficult to implement through pure hardware solutions or to verify exhaustively.
3.3. Design Goals
- Security: Our primary security objective is to ensure system availability and output integrity with high probability even in the presence of adversarial attacks targeting individual executors. The architecture must guarantee that compromised executors cannot persistently produce erroneous outputs without detection, thereby preventing attacks from propagating to physical control processes or upstream analytical systems. Specifically, the system should maintain correct operation as long as a threshold number of executors remain uncompromised and automatically identify and isolate compromised executors through behavioral analysis and output comparison.
- Privacy: The architecture must protect sensitive operational data, proprietary algorithms, and system parameters from adversaries capable of monitoring the arbitration process or conducting side-channel attacks. Even if an attacker successfully infiltrates the arbitration module, they should be unable to extract the exact values of executor outputs or internal system states, thus preserving the confidentiality of critical industrial information. Privacy protection should extend to both the content of individual executor outputs and the aggregate results of the arbitration process.
- Efficiency: While enhancing security and privacy, the architecture must maintain reasonable operational efficiency without introducing prohibitive computational or communication overhead. The additional resources required for maintaining multiple heterogeneous executors, performing privacy-preserving arbitration, and executing dynamic scheduling should be proportionate to the security gains achieved.
4. Privacy and Security Enhanced Methods
4.1. Privacy-Preserving Arbitration Mechanism
4.1.1. Exact Voting Arbitration
4.1.2. Basic Homomorphic Encryption-Based Scheme
- Each online heterogeneous executor computes its output and encrypts it using the public key of the intended recipient (such as the cloud platform), producing ciphertext .
- The executors transmit their encrypted outputs to the arbitration and scheduling module.
- The arbitration and scheduling module performs homomorphic subtraction operations between each pair of encrypted outputs, generating difference ciphertexts:where ⊖ represents the homomorphic subtraction operation.
- The arbitration and scheduling module transmits these difference ciphertexts to the cloud platform.
- The cloud platform decrypts each difference ciphertext using its private key :
- The cloud platform evaluates the consistency of executor outputs:
- The cloud platform sends the consistency evaluation results back to the arbitration and scheduling module.
- For consistent outputs identified by the cloud platform, the arbitration and scheduling module performs homomorphic addition of the corresponding ciphertexts to generate an aggregated result:where is the set of executors with consistent outputs and ⨁ represents the homomorphic addition operation.
- The cloud platform decrypts the aggregated result and computes the final output:
4.1.3. Communication-Optimized Scheme
4.1.4. Adaptive Privacy Budget Scheme
- Each executor computes its output and separates it into two parts: (first bits) and (remaining bits).
- The executor computes a hash of the visible portion, , and sends both this hash and the encrypted complete output to the arbitration and scheduling module.
- The module compares hashes of visible portions to make preliminary consistency determinations:
- Based on local consistency checks, the module initiates the homomorphic encryption-based scheme for final verification.
4.2. Credit-Heterogeneity-Based Executor Scheduling Strategy
4.2.1. Quantification of Executor Heterogeneity and Credibility
4.2.2. Executor Scheduling Algorithm
- Generate a random number , where m is the number of online executors;
- Sort the m executors in descending order by their online runtime, and take the k executors with the longest runtime offline for cleansing;
- Select k executors from the standby pool to bring online, maximizing the objective function , where represents the set of candidate executors for scheduling, is the aggregate heterogeneity vector, and is the aggregate credibility vector.
- Calculate the total credibility for each set of executors producing different outputs usingwhere represents the common-mode vulnerability factor:
- Compare the total credibility of different output groups, and take offline the executor set with lower total credibility for cleansing.
4.2.3. Dynamic Updates to Credibility and Heterogeneity
5. Security and Privacy Analysis
5.1. Security
5.2. Privacy
- : The first bits, which are hashed and sent in the clear;
- : The remaining bits, which remain fully encrypted.
6. Experimental Evaluation and Results
6.1. Experimental Setup
6.2. Comparative Analysis of Defense Strategies
6.3. Performance Evaluation of Privacy-Preserving Arbitration
6.4. Executor Scheduling Algorithm Performance Analysis
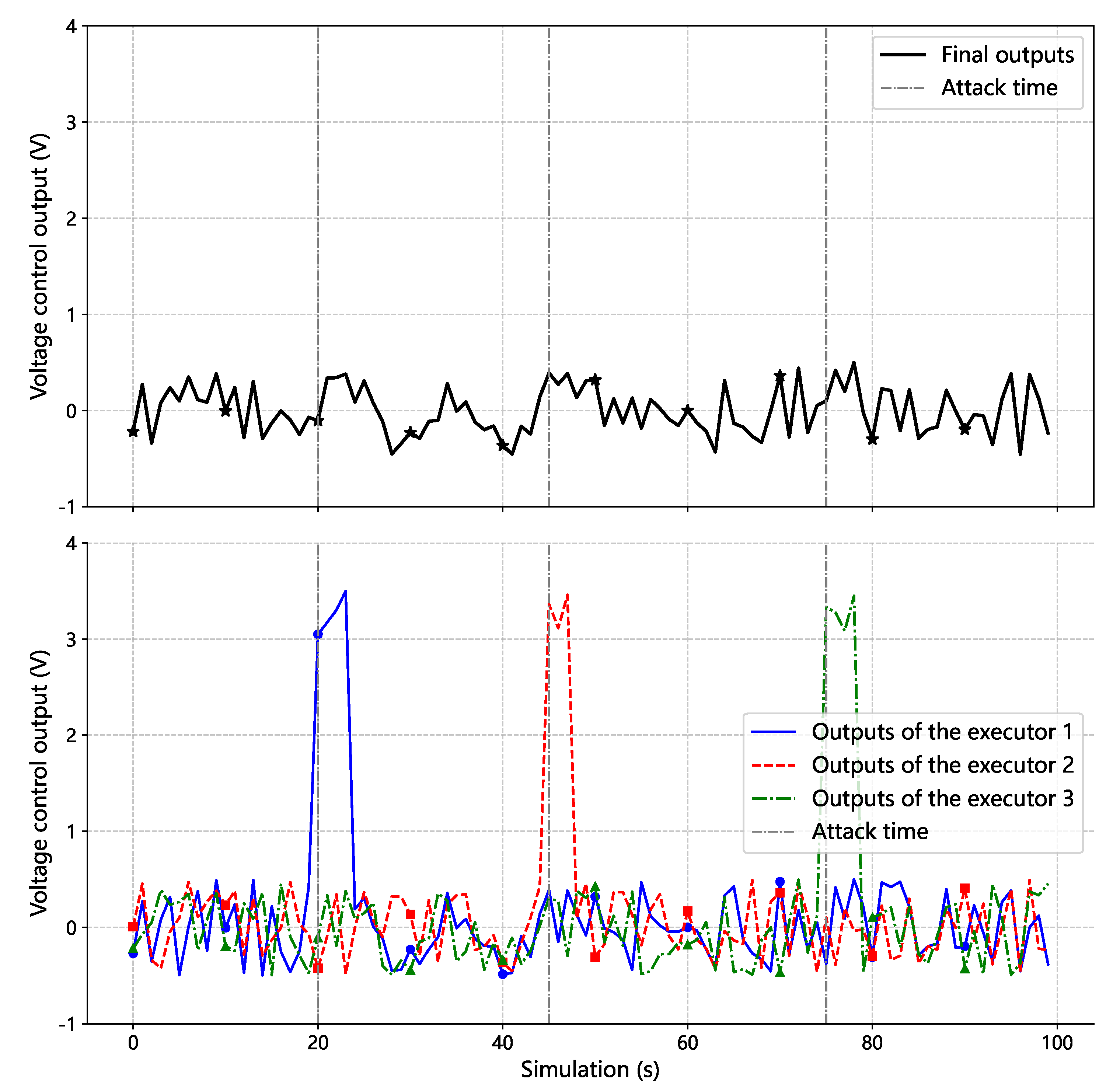
6.5. Validation in Smart Grid Voltage Control Systems
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Alrumaih, T.N.; Alenazi, M.J. CGAAD: Centrality-and graph-aware deep learning model for detecting cyberattacks targeting industrial control systems in critical infrastructure. IEEE Internet Things J. 2024, 11, 24162–24182. [Google Scholar] [CrossRef]
- Dritsas, E.; Trigka, M. A survey on the applications of cloud computing in the industrial internet of things. Big Data Cogn. Comput. 2025, 9, 44. [Google Scholar] [CrossRef]
- Kaneko, Y.; Yokoyama, Y.; Monma, N.; Terashima, Y.; Teramoto, K.; Kishimoto, T.; Saito, T. A microservice-based industrial control system architecture using cloud and MEC. In Proceedings of the Edge Computing–EDGE 2020: 4th International Conference, Held as Part of the Services Conference Federation, SCF 2020, Proceedings 4, Honolulu, HI, USA, 18–20 September 2020; Springer: Berlin/Heidelberg, Germany, 2020; pp. 18–32. [Google Scholar]
- Zhao, B.; Gao, Q.; Li, Y.; Lü, J.; Zhang, K. Cooperative security analysis of industry cloud control systems under false data injection attacks. IEEE Trans. Syst. Man Cybern. Syst. 2024, 54, 3124–3133. [Google Scholar] [CrossRef]
- Bala, M.I.; Chishti, M.A. Survey of applications, challenges and opportunities in fog computing. Int. J. Pervasive Comput. Commun. 2019, 15, 80–96. [Google Scholar] [CrossRef]
- Nain, G.; Pattanaik, K.; Sharma, G. Towards edge computing in intelligent manufacturing: Past, present and future. J. Manuf. Syst. 2022, 62, 588–611. [Google Scholar] [CrossRef]
- Li, P.; Xia, J.; Wang, Q.; Zhang, Y.; Wu, M. Secure architecture for Industrial Edge of Things (IEoT): A hierarchical perspective. Comput. Netw. 2024, 251, 110641. [Google Scholar] [CrossRef]
- Yang, X.; Esquivel, J.A. Lstm network-based adaptation approach for dynamic integration in intelligent end-edge-cloud systems. Tsinghua Sci. Technol. 2024, 29, 1219–1231. [Google Scholar] [CrossRef]
- Yang, T.; Jiang, X.; Li, W.; Liu, P.; Wang, J.; Hao, W.; Yang, Q. Cloud-edge collaborative data anomaly detection in industrial sensor networks. PLoS ONE 2025, 20, e0324543. [Google Scholar] [CrossRef] [PubMed]
- Qi, L.; Zhang, X.; Chen, H.; Bian, N.; Ma, T.; Yin, J. A Novel Distributed Orchestration Engine for Time-Sensitive Robotic Service Orchestration Based on Cloud-Edge Collaboration. IEEE Trans. Ind. Inform. 2025, 21, 3943–3954. [Google Scholar] [CrossRef]
- Huang, K.; Wang, Q.; Chen, Z.; Yang, C.; Gui, W. Secure Cloud-Edge Collaborative Method for Dynamic Industrial Process Monitoring Using Self-Updating Dictionary Learning. IEEE Trans. Autom. Sci. Eng. 2025, 22, 14170–14182. [Google Scholar] [CrossRef]
- Alzu’Bi, A.; Alomar, A.; Alkhaza’Leh, S.; Abuarqoub, A.; Hammoudeh, M. A review of privacy and security of edge computing in smart healthcare systems: Issues, challenges, and research directions. Tsinghua Sci. Technol. 2024, 29, 1152–1180. [Google Scholar] [CrossRef]
- Wu, J. Cyberspace Mimic Defense; Springer: Berlin/Heidelberg, Germany, 2020. [Google Scholar]
- Wang, Y.; Fang, L.; Hu, B.; Ge, G.; Zhou, X.; Zhang, W. Overview of research on cloud-edge-end collaboration technology of industrial control system. In Proceedings of the 2023 International Conference on Electronics, Computers and Communication Technology, Guilin, China, 17–19 November 2023; pp. 169–174. [Google Scholar]
- Al-Yarimi, F.A.; Salah, R.; Mohamoud, K. Blockchain-driven secure data sharing framework for edge computing networks. Tsinghua Sci. Technol. 2025, 30, 978–997. [Google Scholar] [CrossRef]
- Al-Hawawreh, M.; Hossain, M.S. Digital twin-driven secured edge-private cloud Industrial Internet of Things (IIoT) framework. J. Netw. Comput. Appl. 2024, 226, 103888. [Google Scholar] [CrossRef]
- Jiang, Y.; Wu, S.; Ma, R.; Liu, M.; Luo, H.; Kaynak, O. Monitoring and defense of industrial cyber-physical systems under typical attacks: From a systems and control perspective. IEEE Trans. Ind. Cyber-Phys. Syst. 2023, 1, 192–207. [Google Scholar] [CrossRef]
- Lian, Z.; Shi, P.; Chen, M. A Survey on Cyber-Attacks for Cyber-Physical Systems: Modeling, Defense and Design. IEEE Internet Things J. 2025, 12, 1471–1483. [Google Scholar] [CrossRef]
- Choi, W.; Pandey, S.; Kim, J. Detecting Cybersecurity Threats for Industrial Control Systems using Machine Learning. IEEE Access 2024, 12, 153550–153563. [Google Scholar] [CrossRef]
- Termanini, A.; Al-Abri, D.; Bourdoucen, H.; Al Maashri, A. Using machine learning to detect network intrusions in industrial control systems: A survey. Int. J. Inf. Secur. 2025, 24, 20. [Google Scholar] [CrossRef]
- Xu, C.; Du, X.; Li, L.; Li, X.; Yu, H. End-edge collaborative lightweight secure federated learning for anomaly detection of wireless industrial control systems. IEEE Open J. Ind. Electron. Soc. 2024, 5, 132–142. [Google Scholar] [CrossRef]
- Xue, Y.; Pan, J.; Geng, Y.; Yang, Z.; Liu, M.; Deng, R. Real-Time Intrusion Detection based on Decision Fusion in Industrial Control Systems. IEEE Trans. Ind. Cyber-Phys. Syst. 2024, 2, 143–153. [Google Scholar] [CrossRef]
- Huang, D.; Shi, X.; Zhang, W.A. False data injection attack detection for industrial control systems based on both time-and frequency-domain analysis of sensor data. IEEE Internet Things J. 2021, 8, 585–595. [Google Scholar] [CrossRef]
- Mokhtari, S.; Yen, K.K. False Data Injection Attack Detection, Isolation, and Identification in Industrial Control Systems Based on Machine Learning: Application in Load Frequency Control. Electronics 2024, 13, 3239. [Google Scholar] [CrossRef]
- Zhang, X.; Jiang, Z.; Ding, Y.; Ngai, E.C.; Yang, S.H. Anomaly detection using isomorphic analysis for false data injection attacks in industrial control systems. J. Frankl. Inst. 2024, 361, 107000. [Google Scholar] [CrossRef]
- Ma, Y.W.; Tsou, C.W. A novel passive-active detection system for false data injection attacks in industrial control systems. Comput. Secur. 2024, 145, 103996. [Google Scholar] [CrossRef]
- Sangoleye, F.; Johnson, J.; Tsiropoulou, E.E. Intrusion Detection in Industrial Control Systems based on Deep Reinforcement Learning. IEEE Access 2024, 12, 151444–151459. [Google Scholar] [CrossRef]
- Thiyagarajan, K.; Hammad, I. Anomaly Detection in Air-Gapped Industrial Control Systems of Nuclear Power Plants. In Proceedings of the 2024 Cyber Awareness and Research Symposium (CARS), Grand Forks, ND, USA, 28–29 October 2024; IEEE: New York, NY, USA, 2024; pp. 1–6. [Google Scholar]
- Benka, D.; Horváth, D.; Špendla, L.; Gašpar, G.; Strémy, M. Machine Learning-Based Detection of Anomalies, Intrusions and Threats in Industrial Control Systems. IEEE Access 2025, 13, 12502–12514. [Google Scholar] [CrossRef]
- Zhao, J.; Jin, Z.; Zeng, P.; Sheng, C.; Wang, T. An Anomaly Detection Method for Oilfield Industrial Control Systems Fine-Tuned Using the Llama3 Model. Appl. Sci. 2024, 14, 9169. [Google Scholar] [CrossRef]
- Ekrad, K.; Leclerc, S.; Johansson, B.; Vadillo, I.A.; Mubeen, S.; Ashjaei, M. Real-Time Fault Diagnosis of Node and Link Failures for Industrial Controller Redundancy. In Proceedings of the 2024 IEEE 29th International Conference on Emerging Technologies and Factory Automation (ETFA), Padova, Italy, 10–13 September 2024; IEEE: New York, NY, USA, 2024; pp. 1–4. [Google Scholar]
- Qin, X.; Jiang, F.; Dong, C.; Doss, R. A hybrid cyber defense framework for reconnaissance attack in industrial control systems. Comput. Secur. 2024, 136, 103506. [Google Scholar] [CrossRef]
- Sharma, R. Enhancing Industrial Automation and Safety Through Real-Time Monitoring and Control Systems. Int. J. Smart Sustain. Intell. Comput. 2024, 1, 1–20. [Google Scholar] [CrossRef]
- Chaves, A.; Rice, M.; Dunlap, S.; Pecarina, J. Improving the cyber resilience of industrial control systems. Int. J. Crit. Infrastruct. Prot. 2017, 17, 30–48. [Google Scholar] [CrossRef]
- Ma, R.; Cheng, P.; Zhang, Z.; Liu, W.; Wang, Q.; Wei, Q. Stealthy attack against redundant controller architecture of industrial cyber-physical system. IEEE Internet Things J. 2019, 6, 9783–9793. [Google Scholar] [CrossRef]
- Rajput, P.H.N.; Doumanidis, C.; Maniatakos, M. ICSPatch: Automated Vulnerability Localization and Non-Intrusive Hotpatching in Industrial Control Systems using Data Dependence Graphs. In Proceedings of the 32nd USENIX Security Symposium (USENIX Security 23), Anaheim, CA, USA, 9–11 August 2023; pp. 6861–6876. [Google Scholar]
- Zhang, X.; Li, J.; Wu, J.; Chen, G.; Meng, Y.; Zhu, H.; Zhang, X. Binary-Level Formal Verification Based Automatic Security Ensurement for PLC in Industrial IoT. IEEE Trans. Dependable Secur. Comput. 2025, 22, 2211–2226. [Google Scholar] [CrossRef]
- Chavez, A.R. Moving target defense to improve industrial control system resiliency. In Industrial Control Systems Security and Resiliency: Practice and Theory; Springer: Berlin/Heidelberg, Germany, 2019; pp. 143–167. [Google Scholar]
- Zhou, Y.; Cheng, G.; Ouyang, Z.; Chen, Z. Resource-efficient low-rate DDoS mitigation with moving target defense in edge clouds. IEEE Trans. Netw. Serv. Manag. 2025, 22, 168–186. [Google Scholar] [CrossRef]
- Etxezarreta, X.; Garitano, I.; Iturbe, M.; Zurutuza, U. Low delay network attributes randomization to proactively mitigate reconnaissance attacks in industrial control systems. Wirel. Netw. 2024, 30, 5077–5091. [Google Scholar] [CrossRef]
- Wu, X.; Wang, M.; Shen, J.; Gong, Y. Towards Double-Layer Dynamic Heterogeneous Redundancy Architecture for Reliable Railway Passenger Service System. Electronics 2024, 13, 3592. [Google Scholar] [CrossRef]
- Dai, Z.; Leeke, M.; Ding, Y.; Yang, S.h. A heterogeneous redundant architecture for industrial control system security. In Proceedings of the 2022 IEEE 27th Pacific Rim International Symposium on Dependable Computing (PRDC), Beijing, China, 28 November–1 December 2022; IEEE: New York, NY, USA, 2022; pp. 89–97. [Google Scholar]
- Dai, W.; Li, S.; Lu, L.; Ye, Y.; Meng, F.; Zhang, D. Research on Application of Mimic Defense in Industrial Control System Security. In Proceedings of the 2021 IEEE 2nd International Conference on Information Technology, Big Data and Artificial Intelligence (ICIBA), Chongqing, China, 17–19 December 2021; IEEE: New York, NY, USA, 2021; Volume 2, pp. 573–577. [Google Scholar]
- Sun, C.; Chen, G.; Sun, X.; Li, Q.; Lv, P.; Dai, H. An Architecture for Industrial Control Mimic Systems Based on Component and Multi-Level 2-Mode Judgment Algorithm. In Proceedings of the 2024 10th IEEE International Conference on High Performance and Smart Computing (HPSC), New York, NY, USA, 10–12 May 2024; IEEE: New York, NY, USA, 2024; pp. 77–82. [Google Scholar]
- Quan, G.; Yao, Z.; Si, X.; Zhu, W.; Chen, L. A data sharing model for blockchain trusted sensor leveraging mimic hash mechanism. Electronics 2024, 13, 1495. [Google Scholar] [CrossRef]
- Shao, S.; Gu, T.; Nie, Y.; Ji, Z.; Wu, F.; Ba, Z.; Ji, Y.; Ren, K.; Sun, G. An Active Defense Adjudication Method Based on Adaptive Anomaly Sensing for Mimic IoT. IEEE Trans. Serv. Comput. 2025, 18, 57–71. [Google Scholar] [CrossRef]
- Huang, Z.; Yuan, Y.; Fu, J.; He, J.; Zhu, H.; Cheng, G. Location-Aware Measurement for Cyber Mimic Defense: You Cannot Improve What You Cannot Measure. Appl. Sci. 2023, 13, 9213. [Google Scholar] [CrossRef]
- Yu, Z.; Kong, X.; Miao, X.; Cao, Y.; Huang, W.; Du, J. HSelect: Effective Selection of Heterogeneous Software for Common Mode Failure Mitigation. In Proceedings of the 2025 4th International Symposium on Computer Applications and Information Technology (ISCAIT), Xi’an, China, 21–23 March 2025; IEEE: New York, NY, USA, 2025; pp. 1876–1880. [Google Scholar]
- Shao, S.; Ji, Y.; Zhang, W.; Liu, S.; Jiang, F.; Cao, Z.; Wu, F.; Zeng, F.; Zuo, J.; Zhou, L. A DHR executor selection algorithm based on historical credibility and dissimilarity clustering. Sci. China Inf. Sci. 2023, 66, 212304. [Google Scholar] [CrossRef]
- Tang, Z.; Guo, X.; Chen, L. Mimic Scoring Voting Algorithm Based on Historical Confidence and Heterogeneity. In Proceedings of the 2021 IEEE 6th International Conference on Signal and Image Processing (ICSIP), Nanjing, China, 22–24 October 2021; IEEE: New York, NY, USA, 2021; pp. 1145–1149. [Google Scholar]
- Zhang, J.Z.; Yu, Y.; Wang, H.; Zhang, Z.L. Research on a Polymorphic Multi-Mode Decision Algorithm Based on AdaBoost. In Proceedings of the 2023 15th International Conference on Communication Software and Networks (ICCSN), Shenyang, China, 21–23 July 2023; IEEE: New York, NY, USA, 2023; pp. 477–483. [Google Scholar]
- Sinaga, K.P.; Yang, M.S. A Globally Collaborative Multi-View k-Means Clustering. Electronics 2025, 14, 2129. [Google Scholar] [CrossRef]
- Domingo-Ferrer, J. A provably secure additive and multiplicative privacy homomorphism. In Proceedings of the International Conference on Information Security, Sao Paulo, Brazil, 30 September–2 October 2002; Springer: Berlin/Heidelberg, Germany, 2002; pp. 471–483. [Google Scholar]
- Savvides, S.; Khandelwal, D.; Eugster, P. Efficient confidentiality-preserving data analytics over symmetrically encrypted datasets. Proc. VLDB Endow. 2020, 13, 1290–1303. [Google Scholar] [CrossRef]
- Alhashimi, A.; Nolte, T.; Papadopoulos, A.V. Enhancing Sensor Attack Detection and Mitigating Sensor Compromise Impact in a Switching-Based Moving Target Defense. In Proceedings of the 2024 European Control Conference (ECC), Stockholm, Sweden, 25–28 June 2024; IEEE: New York, NY, USA, 2024; pp. 2560–2567. [Google Scholar]
- Qin, X.; Doss, R.; Jiang, F.; Qin, X.; Long, B. Securing ICS networks: SDN-based Automated Traffic Control and MTD Defensive Framework against DDoS attacks. Comput. Commun. 2025, 241, 108252. [Google Scholar] [CrossRef]









| Work | Methodology | Privacy Protection | Application Domain |
|---|---|---|---|
| Sun et al. [44] | Multi-level 2-mode judgment algorithm | Not addressed | Industrial applications (real-time constraints) |
| Shao et al. [46] | Active defense arbitration with adaptive anomaly sensing | Not addressed | Mimic IoT |
| Huang et al. [47] | Location-aware metrics (common-mode index, transfer probability) | Not addressed | General DHR systems |
| Yu et al. [48] | HSelect approach with file/block-level code change detection | Not addressed | N-versioning systems |
| Shao et al. [49] | Historical credibility and dissimilarity clustering (HCDC) | Not addressed | General DHR systems |
| Tang et al. [50] | Mimic scoring voting algorithm with heterogeneity measures | Not addressed | General DHR systems with limited executors |
| Zhang et al. [51] | Polymorphic multi-mode decision with AdaBoost classifiers | Not addressed | General DHR systems |
| Our Work | Privacy-preserving arbitration with a hybrid event–time triggered scheduling strategy | Adaptive privacy budget allocation mechanism | Cloud–edge collaboration ICS |
| Method | Failures | MTTR (min) | MTBF (min) | Availability (%) |
|---|---|---|---|---|
| Static redundancy | 2 | 44.92 | 75.08 | 62.57 |
| Moving target defense | 2 | 16.17 | 103.83 | 86.53 |
| Proposed method | 0 | 0.00 | 240.00 | 100.00 |
| Detection Rate (%) | Average (%) | Best Cases (%) | Worst Cases (%) |
|---|---|---|---|
| 99.9 | 99.9945 | 100.0000 | 95.0000 |
| 95.4 | 99.7790 | 100.0000 | 90.0000 |
| 92.9 | 99.6735 | 100.0000 | 90.0000 |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2025 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Niu, Y.; Han, X.; He, C.; Wang, Y.; Cao, Z.; Zhou, D. A Privacy-Preserving Polymorphic Heterogeneous Security Architecture for Cloud–Edge Collaboration Industrial Control Systems. Appl. Sci. 2025, 15, 8032. https://doi.org/10.3390/app15148032
Niu Y, Han X, He C, Wang Y, Cao Z, Zhou D. A Privacy-Preserving Polymorphic Heterogeneous Security Architecture for Cloud–Edge Collaboration Industrial Control Systems. Applied Sciences. 2025; 15(14):8032. https://doi.org/10.3390/app15148032
Chicago/Turabian StyleNiu, Yukun, Xiaopeng Han, Chuan He, Yunfan Wang, Zhigang Cao, and Ding Zhou. 2025. "A Privacy-Preserving Polymorphic Heterogeneous Security Architecture for Cloud–Edge Collaboration Industrial Control Systems" Applied Sciences 15, no. 14: 8032. https://doi.org/10.3390/app15148032
APA StyleNiu, Y., Han, X., He, C., Wang, Y., Cao, Z., & Zhou, D. (2025). A Privacy-Preserving Polymorphic Heterogeneous Security Architecture for Cloud–Edge Collaboration Industrial Control Systems. Applied Sciences, 15(14), 8032. https://doi.org/10.3390/app15148032






