Abstract
We propose an ultra-lightweight cryptographic scheme called “Small Lightweight Cryptographic Algorithm (SLA)”. The SLA relies on substitution–permutation network (SPN). It utilizes 64-bit plaintext and supports a key length of 80/128-bits. The SLA cipher includes nonlinear layers, XOR operations, and round permutation layers. The S-box serves to introduce nonlinearity in the entire scheme design. It plays a vital role in increasing the complexity and robustness of the design. The S-box can thwart attacks such as linear and differential attacks. The scheme makes it possible to breed many active S-boxes in a short number of rounds, hindering analytical attacks on the cipher. When compared to other currently used ciphers, SLA has a higher throughput. Additionally, we demonstrate the SLA’s performance as an ultra-lightweight compact cipher, and its security analysis. The SLA cipher’s design is well suited for applications where small-scale embedded system dissipation is critical. The SLA algorithm is implemented using Python.
1. Introduction
The current significant advancement in the network of intelligent objects is the Internet of Things (loT). It has various uses, such as radiation monitoring in nuclear power plants, smart cities, smart homes and smart environments in general, animal tracking, health monitoring, and many more applications. The main issues in IoT applications are energy management, IPv6 adoption, standardization, and security [1].
Any wireless cryptographic scheme has serious data security challenges. A cryptographic method is a crucial component of network security. For IoT systems, “Lightweight Cryptography (LWC)” is most suited. Lightweight cryptography is a protocol designed for use in constrained environments such as sensor networks, meters, healthcare, the Internet of Things, cyber-physical systems, intelligent energy systems, indicators, custom controls, etc. [2]. In addition, formal methods on IoT application layer protocols for improving security and detecting security issues remain an open challenge.
The motivation for developing SLA includes the following. Major standards organizations closely follow lightweight cryptographic development. Several lightweight cryptographic methods have been standardized by The International Organization for Standards (ISO) and the International Electro-technical Commission (IEC). These standard bodies are also reviewing more algorithms to include in their standards. Recently, the National Institute of Standards and Technology (NIST) made public its lightweight algorithms portfolio requirements [3]. This announcement came after the Institute held two workshops on lightweight cryptography [4,5].
Enforcing security against attacks on IoT systems is a challenging task. Once the required features of an IoT system have been added, cryptographic engineering aims to harmonize conflicting requirements to create secure yet usable embedded IoT systems. The field of LWC for IoT applications combines cryptography, computer science, and electrical engineering. Solutions to IoT security problems are converging on cryptographic engineering. This paper attempts to reconcile these conflicting requirements. In this paper, we propose a new lightweight cryptographic scheme built from finite fields, using their underlying mathematical structure. In general, this choice does not influence the security of the scheme, but influences the performance of the resulting implementation. This approach has become a major design trend in cryptography, due to the increasing importance of small-scale embedded IoT devices. In a lightweight cryptographic scheme, the construction of a strong non-linear S-box (confusion layer) uses Galois field multiplication which meets cryptographic properties, and provides a novel method to construct diffusion layers by 32-bit binary matrix. The resulting proposed SLA scheme provides a sufficient security level against most of the well-known attacks on block ciphers, such as linear and differential cryptanalysis.
2. Related Work
A significant number of authors, in the current literature, have undertaken investigations into how to improve IoT security and privacy. This section derives input from current solutions for small cryptographic algorithms. They also discussed how to enhance the level of security for the IoT.
In [6] a new variant lightweight cryptography algorithm for the Internet of Things is proposed, which is called New Variant Lightweight Cryptography (NVLC). The main idea of the design of NVLC is to use a 4-bit S-box with a lower signal delay in comparison to an 8-bit S-box. Additionally, it used the Whitening key idea at the beginning and end of encryption to raise the difficulty of key search and the difficulty of attacking the cipher. However, the encryption methods investigated the goal of a high level of security in the low-resource device for NVLC block cipher design.
SFN [7], a new lightweight algorithm, employs a 96-bit key on a 64-bit block. The novel idea of the design is to use a different encryption method that takes both SP network structure and Feistel network structure to encrypt. Involution related properties of the nonlinear and linear components are employed into the design of SP network structure. The modified SP network structure enables the encryption and decryption program or circuit to work as the Feistel network structure. The encryption method satisfies the security requirements of different user levels. It gave a good performance in hardware at 1876 GEs.
A study in [8] proposed a simplified new version of the round function of the original SIMON by reducing its impact by changing the shift numbers, so the first rotation is removed to enhance the speed of SIMON and execution time.
The Feistel scheme is used to encrypt the lightweight block cipher LiCi [9]. LiCi has a 128-bit key, a 64-bit block, and 31 rounds. The LiCi design uses the substitution layer derived from the Karnaugh Map that applies 4 × 4 S-boxes, which has been employed to reduce the logic gates of the S-box, and use circular shift by (3, 7). The encryption method offers good performance, both on hardware at 1153 GEs and on software platforms.
BORON, a low-power cipher proposed in [10], boasts being ultra-weight and compact. It works with 128/80-bit keys and 64-bit plaintext over the SP network. Their methods used for encryption gave excellent performance of 1939 GEs in a small area. It performs efficiently on both hardware and software platforms.
In [11], a family of low energy block ciphers called Midori is proposed, which is composed of two variants: Midori64 and Midori128. The design of Midori is to make use of cell-permutation layers 4 × 4 involutory Binary MDS matrix to optimize diffusion speed, and two types bijective 4-bit S-boxes. The encryption methods satisfy the optimization goal of low energy for block cipher design.
The study in [12] presented Simeck, a lightweight block cipher designed from components of other ciphers, SIMON and Speck. The study proved the ability to design ciphers that have less power consumption and are relatively smaller in area.
The RECTANGLE algorithm [13] proposed new design criteria for the RECTANGLE S-box. The main idea of the design of RECTANGLE makes use of the bit-slice style in a lightweight manner, and was introduced for speeding up the software speed in the design of the DES and Serpent block cipher [14,15]. It offers a very low cost in hardware but also is very competitive in software speed.
In [16], a lightweight, versatile block cipher called TWINE is proposed. The global structure of TWINE is a type-2 generalized Feistel structure (GFS). A round function of TWINE consists of a non-linear single 4-bit S-box rather than multiple ones, which can contribute to smaller (serialized) hardware and software implementations and different block shuffle from the original (cyclic shift), which can greatly improve the diffusion speed of type-2 GFS. Despite the fact that bit-shifting operations are often used in the diffusion layer of many lightweight block ciphers (e.g., PRESENT and NOEKEON), they actually lose their efficiency in software implementations. Therefore, (PRESENT-like and NOEKEON-like) diffusion techniques [17,18] are not an option for TWINE.
Bogrof et al. [19] presented PRINCE, which provides a new dimension to lightweight cryptography by achieving low latency. It also focuses on hardware implementation. It utilized a 128 bits key and was comprised of 64 bits block with 12 rounds. The S-box of this cipher was non-linear i.e., Feistel structure. The main advantage of the Feistel structure is that the same program code can be used for the encryption and decryption process. It also helps in reducing memory usage. The cipher can however be susceptible to related-key attacks if the Feistel structure uses alternating keys. Some other noteworthy mentions from this generation are Humming-Bird, KASUMI, and Piccolo
In [20], a symmetric cryptographic algorithm, KLEIN, which has the benefit of better performance of software on legacy sensor platforms, is proposed. The fact that it uses a 4-bit S-box permutation via the algebraic normal form (ANF), rather than an 8-bit S-box, whether implemented in hardware or software, results in a tiny hardware implementation. KLEIN’s design increases the available options of lightweight block ciphers for low-resource applications.
In [21], Leander et al. proposed a family of new lightweight variants of DES (data encryption standard), which are called DESL/DESX/DESXL (the lightweight modified versions of the well-known DES). The main idea of the new variants of DES is to use just one S-box recursively, instead of eight different S-boxes, to minimize the hardware implementation.
mCrypton [22] is designed by following the overall architecture of Crypton [23], but with redesign and simplifications of each component function to enable much more compact implementation in both hardware and software.
Based on the state of current small cypher results, it is essential to provide not only a small cypher footprint to fit into small memories, but also to enhance speed and cryptographic strength by making it difficult for linear and differential cryptanalysis.
3. Block Cipher SLA
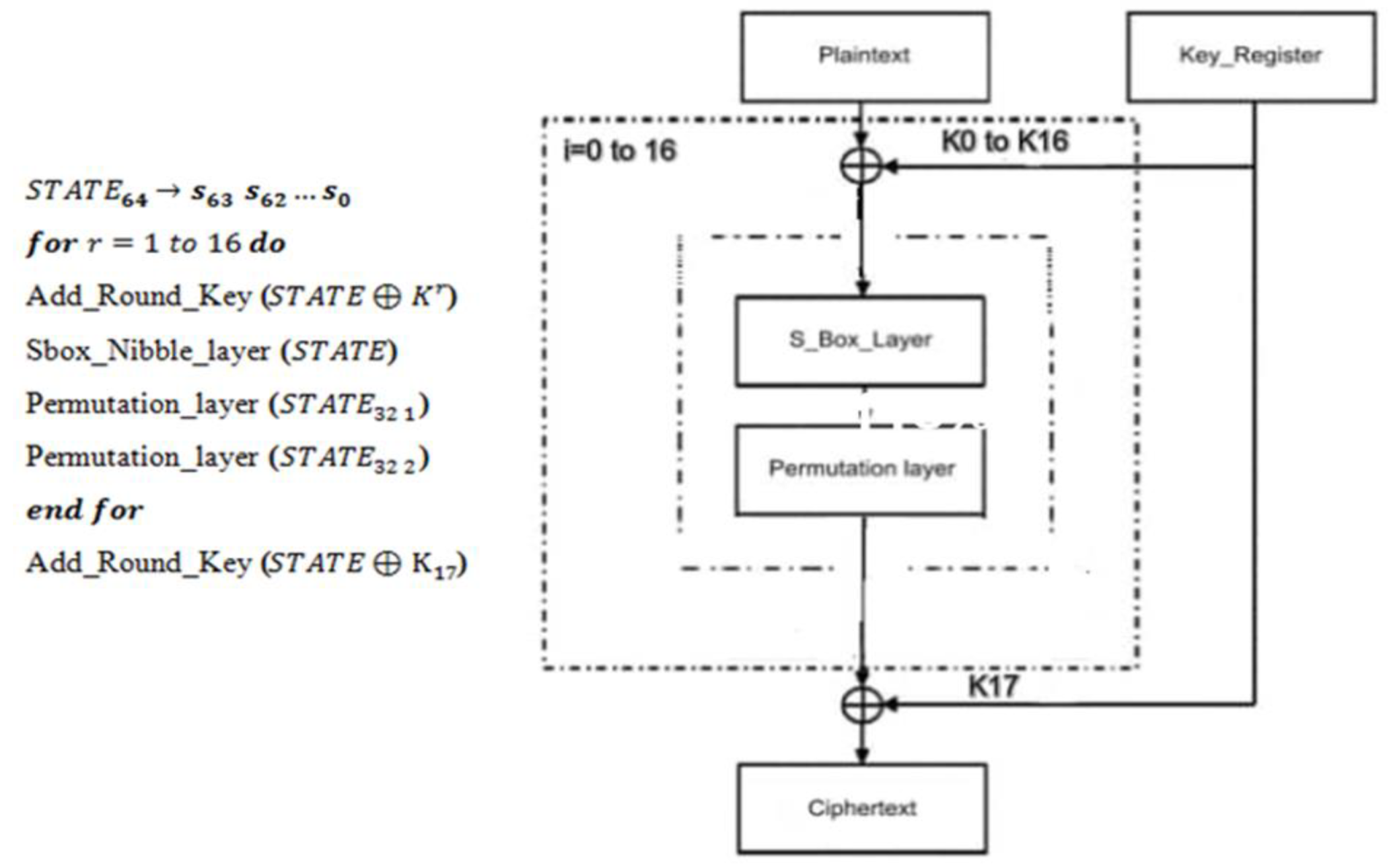
To ensure difficulty in differential and linear cryptanalysis, SLA uses a substitution–permutation network [24], having 16 rounds with 16 keys. The block size is 64 bits with an 80- and 128-bit key size. The block diagram of the SLA cipher is shown in Figure 1, and Figure 2 shows the detailed SLA block cipher.
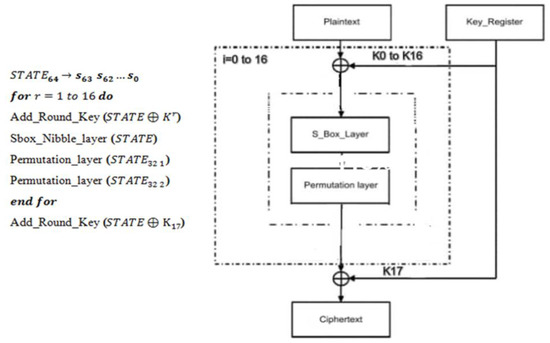
Figure 1.
SLA Block diagram.
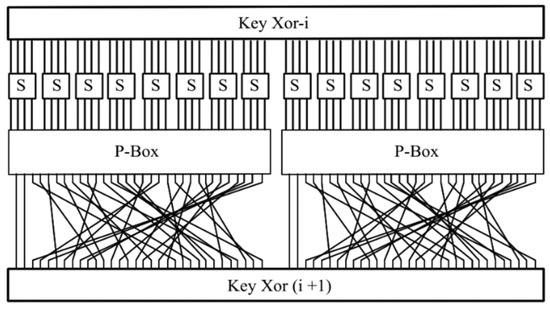
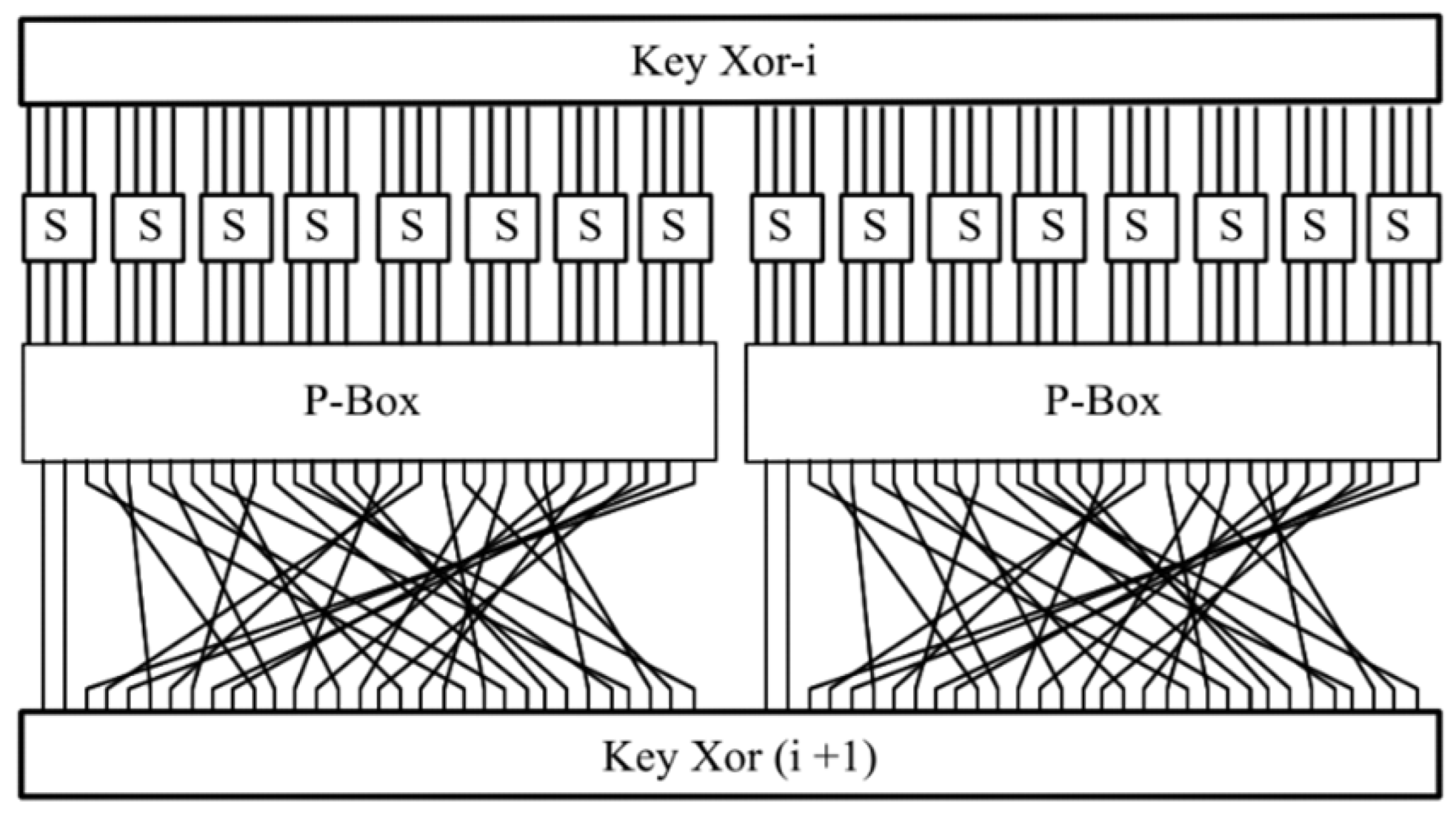
Figure 2.
SLA Block cipher.
Each of the sixteen rounds includes an eXclusive OR (‘XOR’) logic operation to obtain new keys for . They are produced by the 80/128-bit key register. Finally, one additional key will then be produced and XOR-ed to obtain the ultimate ciphertext. The confusion layer represents a non-linear substitution (box) table. The diffusion layer represents one of the durable layers between extant LWC schemes. Figure 2 depicts the block cipher, including pseudocode, with each phase.
3.1. Add_Round_Key
The Add_Round_Key performs an eXclusive OR (‘’) on a 64-bit plaintext and with a 64-bit sub-key produced from the 80/128-bit key register. defines sub-keys for , and the actual output is given as
3.2. Substitution Box (S-Box_Nibble Layer)
The single S-box used in our scheme is S-box. The substitution layer is represented in a hexadecimal form in Table 1. Values in Table 1 are readily implemented using a table of sixteen four-bit values. This is a direct result of the search for a lightweight cryptographic algorithm.

Table 1.
A Sbox_Nibble Layer of our scheme.
3.3. Permutation Layer
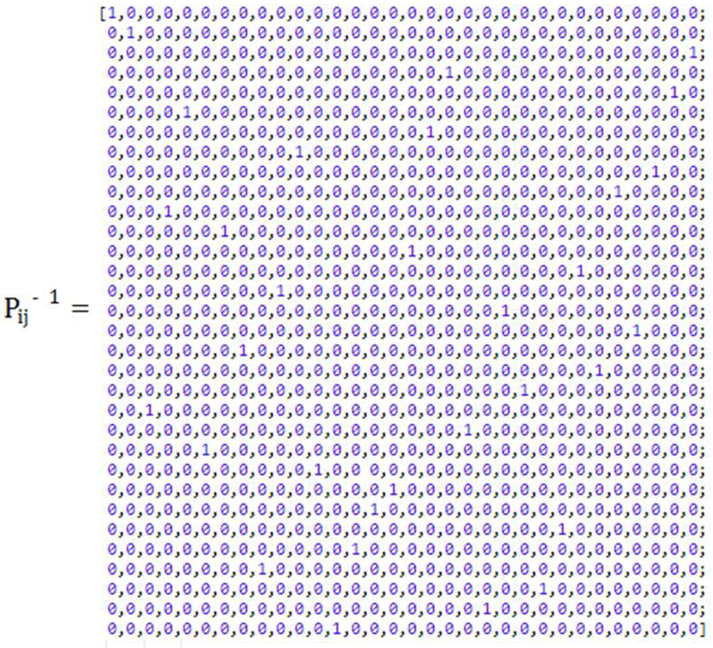
The permutation layer creates a mixed 32-bit output from a 32-bit input. At the 32-bit number bit position, a 32-bit-sized bit is replaced by bit x. The diffusion function can be expressed as a bit permutation level of 1-bit words using the equations below. Appendix A contains a 32 by 32 one-to-one permutation matrix and its inverse. The permutation matrix performs the binary permutation operation in (1) as
The reason for using a one-to-one permutation matrix is to scramble the key. The desire is to rearrange the values in the key so that it looks like someone knows the original key. In a one-to-one permutation matrix, the values of the key do not change; the values only change position. A one-to-one permutation matrix is very fast because one-to-one swapping of the position is fast. For example, if the RaspberryPi device tests a 10 × 10 number, it takes more time to perform 10 multiplications by 10 in the microcontroller; however, a one-to-one permutation matrix is very fast.
Algorithm 1 summarizes the encryption process outlined in Section 3.1, Section 3.2 and Section 3.3.
| Algorithm 1 Encryption |
| Input: Plaintext Output: Ciphertext = 0 16 // S-box // High 32-bit P-box // Low 32-bit P-box |
3.4. Key Schedule of 80- and 128-Bit Key Size
The key scheduling algorithm is one of the most crucial parts of any cryptographic scheme; it determines the cipher’s intricacy. Cryptography has undoubtedly evolved since the days of Kerckhoff. The key schedule of SLA is inspired by the key schedule of PRESENT [17]. No attacks have been reported to date on the PRESENT scheme key scheduling. The SLA scheme key scheduling has a total of 16 sub-keys with a 64-bit key size.
- Scheduling of 80-bit key
The key register KEY contains the 80-bit key provided by the user, specified as . From round , the 64-bit sub-keys least significant bit (LSB), obtained in (2):
The register KEY is updated after obtaining the 64-bit key in (3–5):
For 0 to 16 rounds, five bits of the round counter are XOR-ed with the five bits of key register KEY, i.e., from to .
- 2.
- Scheduling of 128-bit key
The key register KEY contains the 128-bit key provided by the user, specified as . From the round , 64-bit sub-keys least significant bit (LSB), obtained in (6):
The register KEY is updated after obtaining the 64-bit key obtained in (7–10):
3.5. The Decryption Process
The decryption process is the reverse of the encryption procedure. Each layer is reversible. The subkeys are generated in reverse order by the key schedule by using the transformation round keys. The decryption process involves the same number of rounds of encryption, where its processes are performed in each round. They are, however, the reverse of each other. In the add_round_key layer, the inverse is achieved by XORing the same round key to the block. In the S-box, and in the permutation layer, the inverse function is used in the decryption process, using the result that
4. Evaluation of SLA Scheme
4.1. Security Evaluation
- Linear cryptanalysis
Linear cryptanalysis [25,26] is one of the most widely used techniques for breaking block ciphers. To evaluate the difficulty of the linear cryptanalysis of the SLA scheme, we present a minimal bound on the number of so-called “active” S-boxes defined in a linear characteristic. Table 3 presents the linear characteristic for the SLA scheme, and Table 4 shows the minimal number of active S-boxes in the linear characteristic.
Theorem 1.
For sixteen rounds of SLA, it features 48 active S-boxes, and a maximum probabilistic bias linear characteristic is.
Theorem 1 is formally proved in Appendix C.
Walsh transform. The Walsh transform of the Boolean function with is defined as
The Walsh coefficient of at point is denoted by the value , and the Walsh spectrum of is denoted by the multiset consisting of all Walsh coefficients of .
Walsh transform. The bias (aka, correlation or imbalance) of a Boolean function with is defined as
- 2.
- Differential Cryptanalysis
Differential cryptanalysis [26,27] is the main form of attack on symmetric block ciphers. Differential paths are formed by considering the differences between inputs and outputs with a high probability for each round. The S-box where the differences between the inputs or the outputs are nonzero is called the active S-box. SLA presents a minimal bound on the number of so-called “active” S-boxes defined in a differential characteristic to assess the hardness of the SLA scheme differential cryptanalysis.
Appendix E shows the linear/differential relations SLA scheme S-box. Table 5 shows the differential characteristics SLA scheme, and Table 6 shows the minimal number of active S-boxes in the differential characteristic.
Theorem 2.
For sixteen rounds of SLA, it features 48 active S-boxes, and a maximum probabilistic differential characteristic for the sixteen rounds is .
Theorem 2 is formally proved in Appendix D.
Autocorrelation. The autocorrelation transform taken concerning to , of Boolean function with is denoted by and defined as (14):
Differential uniformity. Given differential uniformity for any vectorial Boolean function for any into , we defined in (15):
Then, the differential spectrum of is the multi-set , and its maximum (16):
- 3.
- Algebraic degree. An algebraic degree of a vectorial Boolean function is the number of variables in the longest item of its ANF, denoted by [28].
Nonlinearity. The nonlinearity of Boolean function is defined as the Hamming distance between and the set of all affine functions (or linear) [29] in (17)
- 4.
- Nonlinearity. The nonlinearity of the vectorial Boolean function is the minimal of all component functions of [28], and the Walsh spectrum is used to calculate it in the manner outlined below in (18):
- 5.
- Correlation Immunity. The correlation immunity of a Boolean function is defined as a measurement of how uncorrelated outputs are with a certain subset of its inputs. If is balanced, and , then so-called [30]. This criterion is from the Walsh spectrum in the manner outlined in (19):
- 6.
- Balancedness. The vectorial Boolean function is balanced if its outputs are distributed uniformly over . According to the Walsh Spectrum, this property is evaluated as follows [31]:
- 7.
- Algebraic immunity. Algebraic immunity of a Boolean function is defined as the least degree of all annihilators of or is designated by notation [32,33,34].
- 8.
- Global avalanche criterion (GAC). The global avalanche criterion is presented through two indicators [35].
First, the , denoted by .
Second, the , denoted by .
When cryptographic functions have achieved low values of both indicators, they reach the best diffusion.
- 9.
- Propagation criterion. The propagation criterion of vectorial Boolean function satisfies the This property is from the Walsh spectrum in the manner outlined below [36,37]:
- 10.
- Linear potential. The linear potential of a vectorial Boolean function is a metric of linearity that fulfills [38]. Therefore, the upper bound is met when is linear or affine, whereas the tight bound holds if and only if exhibits maximal nonlinearity ( is bent), and it is defined as
- 11.
- Differential potential. The differential potential of a vectorial Boolean function is a gauge of resistance to differential attack where and the lower bound is valid if is bent and the upper bound is met when is linear or affine, and it is defined as
- 12.
- Fixpoints and negated-fixpoints. A vectorial Boolean function represents the fixpoints of , that is, and negated-fixpoints of , that is
4.2. The Effect of the Avalanche
A cipher with a strong avalanche effect has a better chance of resisting most possible attacks, since even minor input changes have a big impact on the output. In SLA, by changing just one bit in the plaintext/key bits of the input in SLA, the output was observed. It was observed that more than half of the ciphertext bits are impacted by a single bit change in the SLA cipher’s key. Tables 8 and 9 show the effect of the avalanche. This is the intended outcome in the design of SLA in this paper [39].
4.3. Performance Evaluations
Here, we analyzed the performance of SLA further. Based on the AMD Ryzen 45500U processor with 64-bit 4 GHz, Table 10 provides a thorough comparison between SLA and other contenders.
4.4. Results
An analysis of the probabilistic linear relations shows that the nonlinearity property (item in Table 2) is four, while the highest value for a Sbox_Nibble is six. The linear potential (item in Table 2) is 0.25 over the best known for a Sbox_Nibble with four input variables, which is 0.0625. The findings demonstrate that a 4 × 4 Sbox_Nibble Layer offers good resistance to linear attacks.

Table 2.
Comparison with Respect to Cryptographic Criteria of Sbox_Nibble Layer for our design Approach and Mini AES.
Investigation and analysis of the probabilistic differential relations of SLA were undertaken to establish its resistance to probabilistic differential attacks. The result shows that the linearity distance Sbox_Nibble (item in Table 2) is two over a maximal value of four. The differential potential (item in Table 2) is identical to 0.25 over the best known for a Sbox_Nibble with four input variables, which is 0.0625. These findings demonstrate that Sbox_Nibble has the best defense against differential attacks.
The robustness of our S-box design compared to the Mini AES S-box is shown in Table 2. For a 4 × 4 S-box, the Mini AES does not provide effective defense against linear attacks. In addition, it does not exhibit the best defense against differential attacks.
The algebraic degree of the Mini AES S-box is two. This number is too low for immunity against high order differential attacks. Consequently, algebraic attacks can be efficiently executed if a multivariate algebraic equations system is solved. The S-box Mini AES’s reaches the upper bound of 16 and its is close to 4096, hence its inability to achieve a great diffusion. Table 2 provides an overview of the findings for these criteria.
The range of values accepted by the Walsh transform of the Sbox_Nibble are 8, 4, 0, −4, and −8.
The range of values accepted by the linear profile are 64, 16, and 0; the range of values accepted by the differential profile are 1, 024, 512, and 0; finally, the autocorrelation has three levels: 8, 0, and −8.
The results of the linear characteristic and the differential characteristic SLA scheme are shown in Table 3 and Table 4.

Table 3.
Linear Characteristics for the SLA scheme.

Table 4.
Minimal Number of Active S-boxes from the Linear Characteristics.
The results of the minimal number of active S-boxes in the linear and differential characteristics are shown in Table 5 and Table 6.

Table 5.
Differential Characteristics for the SLA scheme.

Table 6.
Minimal Number of Active S-boxes in the Differential Characteristics.
The comparison of the linear and differential attack of SLA with the other algorithms is shown in Table 7. The results show that 16 rounds of SLA are secure enough against differential and linear attacks.

Table 7.
Comparison of Linear and Differential Attacks.
By changing just one bit in the input plaintext/key bits, the output seen in Table 8 and Table 9 is produced. Each time a bit in the key is changed when using the SLA scheme; over half of the ciphertext bits are also changed.

Table 8.
The Effect of the Avalanche on SLA-80.

Table 9.
The Effect of the Avalanche on SLA-128.
The SLA scheme is designed in such a way that it provides optimum performance. The performance of SLA and relevant LWC algorithms in software on AMD Ryzen 45500U processor are shown in Table 10. Interestingly, the execution times of SLA are small, typically less than 0.000659451 s for all of them, which would fit quite well in current IoT devices. They also require little power to process. SIMON and CLEFIA have the highest execution times of 0.02201274 s and 0.022619188 s, respectively. SLA has the highest throughput of 97,050.44167 kilobytes per second. This performance can further be improved by using faster processors in IoTs.

Table 10.
The Performance of SLA and Relevant LWC Algorithms in Software.
In the autocorrelation coefficients, the for Sbox_Nibble is 8, and for the is 640. These results show that Sbox_Nibble obtains a reasonably acceptable diffusion since its is closer to the lower bound and is 0 compared to the upper bound, where 16 is. Similarly, the has theoretical bounds of 256 and 4096, and is extremely close to the 256 lower bound.
When the cryptographic functions attain lower bound for both indicators, the ideal diffusion will be attained. The nibble S-box is represented using the algebraic normal form (ANF):
These forms show that Sbox_Nibble, when compared with others with a maximum algebraic immunity of 2, has an algebraic immunity degree of 3, which is sufficiently high to protect it from higher-order differential attacks. As a result, carrying out algebraic attacks through solving a multivariate algebraic equation system is difficult.
The cipher structure has no visible flaws such as the absence of fixpoints/negated-fixpoints. In addition, a low-level cryptographic algorithm with a rising number of fixpoints or negated-fixpoints lacks the required randomness, so it is not considered to be well designed.
5. Conclusions
This paper has presented SLA, a lightweight scheme. Because SLA is based on the SP-network, it is faster than the Feistel-based cipher. Additionally, the proposed SLA scheme employs a novel encryption method, including finite field multiplication, to construct nonlinear S-box (confusion layer) and the effective one-to-one matrix linear permutation (diffusion layer), which leads to satisfactory security requirements without losing performance efficiency on both execution time and throughput. We exploited properties related to the nonlinear and linear components to design SP network structure. As we designed the SLA, we researched the minimal numbers of active S-boxes and good S-boxes. We also researched the hamming weight calculation for LAT and DDT entries. The proposed SLA design has achieved a small execution time, high throughput, and high level of security. This makes it suitable for small-scale embedded environments such as RFID tags and wireless sensor nodes. Advanced attacks can be used to examine the SLA scheme further. We expect our results to be applied in other domains as well.
Author Contributions
Conceptualization, N.I. and J.A.; Methodology, N.I. and J.A.; Software, N.I.; Validation, N.I. and J.A.; Formal analysis, N.I. and J.A.; Investigation, J.A.; Data curation, N.I.; Writing—original draft, N.I.; Writing—review & editing, J.A.; Visualization, J.A.; Supervision, J.A. All authors have read and agreed to the published version of the manuscript.
Funding
This PhD study is self-funded with no external funding.
Institutional Review Board Statement
Reviewed by my PhD supervisor.
Informed Consent Statement
I Johnson Agbinya PhD Supervisor for Nahla Ibrahim consent and approve to publish this research output as a requirement for examination of her PhD thesis.
Data Availability Statement
Contact Nahla Ibrahim, nahla480@outlook.com.
Acknowledgments
The authors would like to express their thanks for the infinite grace of the Almighty God of essential importance. I solemnly offer my regards to His grace, which enabled peace and harmony for this work.
Conflicts of Interest
The authors declare no conflict of interest.
Appendix A. Bit Permutation Layer
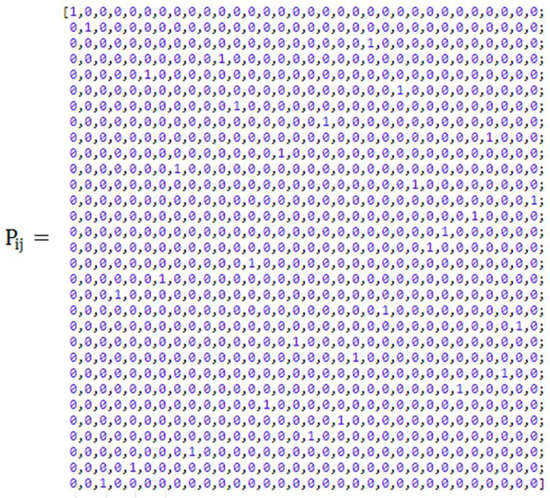
Figure A1.
32 by 32 one-to-one permutation matrix.
Figure A1.
32 by 32 one-to-one permutation matrix.
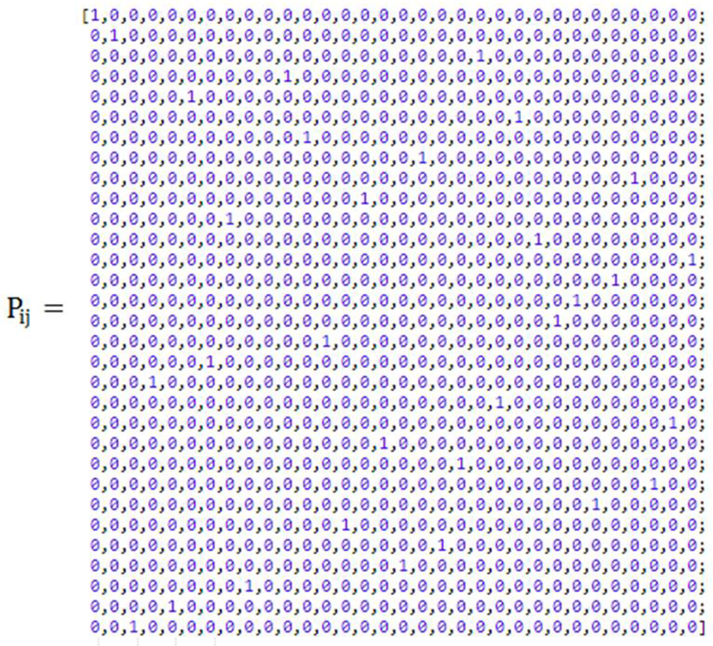
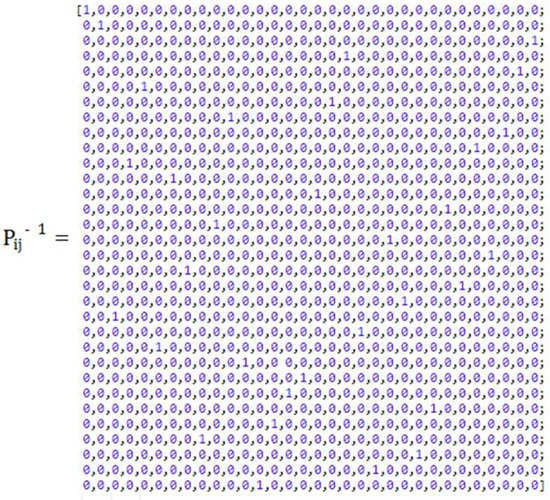
Figure A2.
Inverse of 32 by 32 one-to-one permutation matrix.
Figure A2.
Inverse of 32 by 32 one-to-one permutation matrix.
Appendix B. Test Vectors

Table A1.
Test Vector (for 80-bit key).
Table A1.
Test Vector (for 80-bit key).
| Plaintext | Key | Ciphertext |
|---|---|---|
| 0000 0000 0000 0000 | 0000 0000 0000 0000 0000 | 740434f796cff821 |
| FFFF FFFF FFFF FFFF FFFF | 475a92fa61af749c |

Table A2.
Test vector (for 128-bit key).
Table A2.
Test vector (for 128-bit key).
| Plaintext | Key | Ciphertext |
|---|---|---|
| 0000 0000 0000 0000 | 0000 0000 0000 0000 0000 0000 0000 0000 | 858f96a55cc4f107 |
| FFFF FFFF FFFF FFFF FFFF FFFF FFFF FFFF | 0937f4ef5c91acfa |
Appendix C
Proof of Theorem 1.
In cryptanalysis, the Matsui’s piling-up lemma is a principle used in linear cryptanalysis to construct linear relations to the action of block ciphers:
□
| Lemma (Pilling-up lemma) |
Let be the probability of a linear characteristic. The correlation of the linear characteristic over S-box is given by [45]. From the input–output correlation of S-box, it is straightforward that any linear characteristic over S-box has a correlation of at most . The best way to resist against linear cryptanalysis is to increase the number of active S-boxes in the cipher scheme.
The maximum probabilistic bias linear characteristic of SLA S-box equal to can be calculated similarly [18]. Therefore, the maximum probabilistic bias linear characteristic is estimated for three rounds as
When applied to sixteen rounds, the maximum probabilistic bias linear characteristic is estimated as
To determine the hardness of linear attack, compute the number of known plaintext as follows:
The number of known plaintext is specified for sixteen rounds of the SLA scheme as follows:
The available limit of known plaintext is . This number is lower than the desired number of known plaintext i.e., So, the full number of rounds of the SLA scheme demonstrate solid resilience to linear attacks.
Appendix D
Proof of Theorem 2.
The maximum probabilistic differential characteristic of SLA S-box is. Therefore, the maximum probabilistic differential characteristic for the sixteen rounds is . □
To determine the hardness of differential attack, compute the number of chosen plaintext as follows:
The number of chosen plaintext is , where and .
The number of chosen plaintext is , which exceeds the allowed bound . So, excellent defense against differential attacks is seen in the complete rounds of SLA. Table 7 presents linear and differential attack comparisons.
Appendix E. Differential and Linear Relations of SLA Sbox_Nibble

Table A3.
Differential relations of Sbox_Nibble.
Table A3.
Differential relations of Sbox_Nibble.
| a\b | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | a | b | c | d | e | f |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 16 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 2 | 2 | 2 | 2 | 0 | 0 | 4 | 2 | 0 | 0 | 0 | 2 | 0 | 0 | 0 |
| 2 | 0 | 2 | 0 | 0 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 0 | 4 | 0 | 0 | 2 |
| 3 | 0 | 0 | 2 | 0 | 2 | 2 | 2 | 0 | 4 | 0 | 0 | 2 | 0 | 0 | 2 | 0 |
| 4 | 0 | 4 | 0 | 2 | 0 | 2 | 0 | 0 | 2 | 0 | 2 | 2 | 0 | 0 | 0 | 2 |
| 5 | 0 | 0 | 4 | 2 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 2 | 2 | 2 | 0 | 2 |
| 6 | 0 | 0 | 0 | 2 | 4 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 0 |
| 7 | 0 | 0 | 0 | 4 | 2 | 0 | 0 | 2 | 0 | 2 | 0 | 2 | 0 | 0 | 2 | 2 |
| 8 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 4 |
| 9 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 2 | 0 | 2 | 0 | 2 | 0 | 4 | 2 |
| a | 0 | 2 | 0 | 2 | 0 | 0 | 4 | 0 | 2 | 2 | 0 | 0 | 0 | 2 | 2 | 0 |
| b | 0 | 2 | 2 | 0 | 0 | 0 | 2 | 2 | 0 | 2 | 4 | 2 | 0 | 0 | 0 | 0 |
| c | 0 | 0 | 2 | 2 | 0 | 4 | 0 | 0 | 0 | 2 | 2 | 0 | 2 | 0 | 2 | 0 |
| d | 0 | 2 | 2 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 4 | 2 | 2 |
| e | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 2 | 2 | 4 | 0 | 2 | 2 | 2 | 0 | 0 |
| f | 0 | 2 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 4 | 2 | 2 | 2 | 0 |

Table A4.
Linear relations of Sbox_Nibble.
Table A4.
Linear relations of Sbox_Nibble.
| a\b | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | a | b | c | d | e | f |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 16 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 0 | −4 | 0 | 2 | −2 | 2 | 2 | −2 | 2 | 2 | 2 | 0 | 0 | 0 | 4 |
| 2 | 0 | 2 | 0 | −2 | 2 | 4 | 2 | 0 | −2 | 0 | 2 | 0 | 4 | −2 | 0 | −2 |
| 3 | 0 | 2 | 0 | 2 | −4 | 2 | 0 | −2 | 0 | −2 | 4 | 2 | 0 | 2 | 0 | 2 |
| 4 | 0 | −4 | 2 | 2 | 2 | 2 | 4 | 0 | 2 | −2 | 0 | 0 | 0 | 0 | −2 | 2 |
| 5 | 0 | 0 | 2 | 2 | 0 | 0 | −2 | −2 | 0 | 4 | −2 | 2 | 4 | 0 | −2 | 2 |
| 6 | 0 | 2 | 2 | 4 | 0 | −2 | 2 | 0 | 0 | 2 | 2 | −4 | 0 | −2 | 2 | 0 |
| 7 | 0 | −2 | −2 | 0 | −2 | 4 | 0 | 2 | 2 | 4 | 0 | −2 | 0 | 2 | 2 | 0 |
| 8 | 0 | −2 | −2 | 4 | −2 | 0 | 0 | 2 | −4 | −2 | −2 | 0 | 2 | 0 | 0 | −2 |
| 9 | 0 | −2 | −2 | 0 | 0 | −2 | −2 | 0 | 2 | 0 | 4 | −2 | 2 | 0 | −4 | −2 |
| a | 0 | 0 | 2 | −2 | −4 | 0 | 2 | 2 | −2 | 2 | 0 | 0 | −2 | −2 | −4 | 0 |
| b | 0 | 0 | −2 | −2 | −2 | −2 | 4 | −4 | 0 | 0 | −2 | −2 | 2 | 2 | 0 | 0 |
| c | 0 | 2 | −4 | 2 | 0 | 2 | 0 | −2 | 2 | 0 | −2 | 0 | −2 | −4 | −2 | 0 |
| d | 0 | −2 | 0 | −2 | −2 | 0 | −2 | 0 | 0 | −2 | 0 | −2 | 2 | −4 | 2 | 4 |
| e | 0 | 0 | 0 | 0 | 2 | 2 | −2 | −2 | −4 | 0 | 0 | −4 | −2 | 2 | −2 | 2 |
| f | 0 | −4 | 0 | 0 | 0 | 0 | 0 | −4 | −2 | 2 | 2 | 2 | −2 | −2 | 2 | −2 |
References
- Vinayaga Sundaram, B.; Ramnath, M.; Prasanth, M.; Varsha Sundaram, J. Encryption and Hash based Security in Internet of Things. In Proceedings of the ICSCN 2015, IEEE, Chennai, India, 26–28 March 2015; pp. 1–6. [Google Scholar] [CrossRef]
- Kumar, V.K.; Mascarenhas, S.J.; Kumar, S.; Rakesh, J.P.V. Design And Implementation of Tiny Encryption Algorithm. IJERA 2015, 5 Pt 2, 94–97. [Google Scholar]
- National Institute of Standards and Technology (NIST); Lightweight Cryptography. Available online: https://csrc.nist.gov/Projects/LightweightCryptography (accessed on 18 October 2018).
- National Institute of Standards and Technology (NIST); Lightweight Cryptography Workshop 2015. Available online: https://www.nist.gov/newsevents/events/2015/07/lightweight-cryptographyworkshop2015 (accessed on 23 September 2016).
- National Institute of Standards and Technology (NIST); Lightweight Cryptography Workshop 2016. Available online: https://www.nist.gov/newsevents/events/2016/10/lightweight-cryptography-workshop-2016 (accessed on 3 April 2017).
- Al-Rahman, S.A.; Sagheer, A.; Dawood, O. NVLC: New Variant Lightweight Cryptography Algorithm for Internet of Things. In Proceedings of the AICIS 2018, IEEE, Fallujah, Iraq, 20–21 November 2018; pp. 176–181. [Google Scholar] [CrossRef]
- Li, L.; Liu, B.; Zhou, Y.; Zou, Y. SFN: A new lightweight block cipher. In Proceedings of the MICPRO 2018, Opatija, Croatia, 21–25 May 2018; Elsevier: Amsterdam, The Netherlands, 2018; pp. 138–150. [Google Scholar] [CrossRef]
- Alassaf, N.; Gutub, A.; Parah, S.A.; Al Ghamdi, M. Enhancing speed of SIMON: A light-weight-cryptographic algorithm for IoT applications. In Multimedia Tools and Applications 2018; Springer: Berlin/Heidelberg, Germany, 2018; pp. 32633–32657. [Google Scholar] [CrossRef]
- Patil, J.; Bansod, G.; Kant, K.S. LiCi: A new ultra-lightweight block cipher. In Proceedings of the ICEI 2017, IEEE, Pune, India, 3–5 February 2017; pp. 40–45. [Google Scholar] [CrossRef]
- Bansod, G.; Pisharoty, N.; Patil, A. BORON: An ultra-lightweight and low power encryption design for pervasive computing. In FITEE 2017; Zhejiang University: Hangzhou, China; Springer: Berlin/Heidelberg, Germany, 2017; pp. 317–331. [Google Scholar] [CrossRef]
- Banik, S.; Bogdanov, A.; Isobe, T.; Shibutani, K.; Hiwatari, H.; Akishita, T.; Regazzoni, F. Midori: A Block Cipher for Low Energy. In ASIACRYPT 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 411–436. [Google Scholar] [CrossRef]
- Yang, G.; Zhu, B.; Suder, V.; Aagaard, M.D.; Gong, G. The Simeck Family of Lightweight Block Ciphers. In CHES 2015; Springer: Berlin/Heidelberg, Germany, 2015; pp. 307–329. [Google Scholar] [CrossRef]
- Zhang, W.; Bao, Z.; Lin, D.; Rijmen, V.; Yang, B.; Verbauwhede, I. RECTANGLE: A Bit-slice Lightweight Block Cipher Suitable for Multiple Platforms. In Science China Information Sciences 2015; Springer Nature: Berlin/Heidelberg, Germany, 2015; pp. 1–15. [Google Scholar] [CrossRef]
- Biham, E. A Fast New DES Implementation in Software. In FSE 1997; Biham, E., Ed.; Springer: Berlin/Heidelberg, Germany, 1997; pp. 260–272. [Google Scholar] [CrossRef]
- Anderson, R.; Biham, E.; Knudsen, L.R. Serpent: A Proposal for the Advanced Encryption Standard. NIST AES Propos. 1998, 174, 1–23. [Google Scholar]
- Suzaki, T.; Minematsu, K.; Morioka, S.; Kobayashi, E. TWINE: A Lightweight Block Cipher for Multiple Platforms. In SAC 2012; Springer: Berlin/Heidelberg, Germany, 2012; pp. 339–354. [Google Scholar] [CrossRef]
- Bogdanov, L.R.; Knudsen, G.; Leander, C.; Paar, A.; Poschmann, M.J.B.; Seurin, Y.; Vikkelsoe, C. PRESENT: An Ultra-Lightweight Block Cipher. In CHES 2007; Springer: Berlin/Heidelberg, Germany, 2007; pp. 450–466. [Google Scholar] [CrossRef]
- Daemen, J.; Peeters, M.; Van Assche, G.; Rijmen, V. The Noekeon Block Cipher. The NESSIE Proposal, 2000. First Open NESSIE Workshop, November. Available online: http://gro.noekeon.org/ (accessed on 23 September 2016).
- Borghof, J.; Canteaut, A.; Güneysu, T.; Kavun, E.B.; Knezevic, M.; Knudsen, L.R.; Leander, G.; Nikov, V.; Paar, C.; Rechberger, C.; et al. PRINCE—A low-latency block cipher for pervasive computing applications. In Proceedings of the ASIACRYPT 2012, Beijing, China, 2–6 December 2012; Springer: Berlin/Heidelberg, Germany, 2012; pp. 208–225. [Google Scholar] [CrossRef]
- Gong, Z.; Nikova, S.; Law, Y.W. KLEIN: A New Family of Lightweight Block Ciphers. In RFIDSec 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 1–18. [Google Scholar] [CrossRef]
- Leander, G.; Paar, C.; Poschmann, A.; Schramm, K. New Lightweight DES Variants. In FSE 2007; Springer: Berlin/Heidelberg, Germany, 2007; pp. 196–210. [Google Scholar] [CrossRef]
- Lim, C.H.; Korkishko, T. mCrypton—A Lightweight Block Cipher for Security of Low-Cost RFID Tags and Sensors. In WISA 2005; Song, J., Kwon, T., Yung, M., Eds.; Springer: Berlin/Heidelberg, Germany, 2005; pp. 243–258. [Google Scholar] [CrossRef]
- Lim, C.H. A revised version of crypton: Crypton v1.0. In FSE 1999; Knudsen, L.R., Ed.; Spinger: Berlin/Heidelberg, Germany, 1999; pp. 31–45. [Google Scholar] [CrossRef]
- Menezes, A.; van Oorschot, P.C.; Vanstone, S. The Handbook of Applied Cryptography; CRC Press: Boca Raton, FL, USA, 1996. [Google Scholar] [CrossRef]
- Matsui, M. Linear Cryptanalysis Method for DES Cipher. In EUROCRYPT 1993; Springer: Berlin/Heidelberg, Germany, 1993; pp. 386–397. [Google Scholar] [CrossRef]
- Heys, H.M. A tutorial on linear and differential cryptanalysis. Cryptologia 2001, 26, 189–221. [Google Scholar] [CrossRef]
- Biham, E.; Shamir, A. Differential Cryptanalysis of DES-like Cryptosystems. J. Cryptol. 1991, 4, 3–72. [Google Scholar] [CrossRef]
- Nyberg, K. On the construction of highly nonlinear permutations. In EUROCRYPT 1992; Springer: Berlin/Heidelberg, Germany, 1992; pp. 92–98. [Google Scholar] [CrossRef]
- Pieprzyk, J.; Finkelstein, G. Toward effective nonlinear cryptosystem design. IEE Proc. E-Comput. Digit. Tech. 1988, 135, 325–335. [Google Scholar] [CrossRef]
- Siegenthaler, T. Decrypting a class of stream ciphers using ciphertext only. IEEE Trans. Comput. 1985, 34, 81–85. [Google Scholar] [CrossRef]
- Pommerening, K. Linearitatsmafie fiir BOOLE sche Abbildungen; Technical Report 2005; Fachbereich Mathematik der Johannes-Gutenberg-Universitát: Mainz, Germany, 2005. [Google Scholar]
- Courtois, N. Fast algebraic attacks on stream ciphers with linear feedback. In CRYPTO 2003; Springer: Berlin/Heidelberg, Germany, 2003; pp. 176–194. [Google Scholar] [CrossRef]
- Courtois, N.; Meier, W. Algebraic attacks on stream ciphers with linear feedback. In EUROCRYPT 2003; Springer: Berlin/Heidelberg, Germany, 2003; pp. 345–359. [Google Scholar] [CrossRef]
- Faugére, J.-C.; Ars, G. An Algebraic Cryptanalysis of Nonlinear Filter Generators Using Grobner Bases. Technical Report 2003. INRIA 4739. Available online: https://hal.inria.fr/inria-00071848 (accessed on 1 February 2023).
- Zhang, X.-M.; Zheng, Y. GAC—The criterion for global avalanche characteristics of cryptographic functions. J. Univers. Comput. Sci. 1995, 1, 320–337. [Google Scholar] [CrossRef]
- Preneel, B.; Van Leekwijck, W.; Van Linden, L.; Govaerts, R.; Vandewalle, J. Propagation Characteristics of Boolean Functions. In EUROCRYPT 1990; Springer: Berlin/Heidelberg, Germany, 1990; pp. 161–173. [Google Scholar]
- Webster, A.F.; Tavares, S.E. On the Design of S-boxes. In Crypto ’85; Williams, H.C., Ed.; Springer: Berlin/Heidelberg, Germany, 1986; pp. 523–534. [Google Scholar] [CrossRef]
- Chabaud, F.; Vaudenay, S. Links between differential and linear cryptanalysis. In Advances in Cryptology (EUROCRYPT 1995); Springer: Berlin/Heidelberg, Germany, 1995; pp. 356–365. [Google Scholar] [CrossRef]
- Shi, Z.; Lee, R.B. Bit permutation instructions for accelerating software cryptography. In ASAP’00 2000; IEEE: Boston, MA, USA, 2000; pp. 138–148. [Google Scholar] [CrossRef]
- Álvarez-Cubero, J.A.; Zufiria, P.J. Algorithm 959: VBF: A Library of C++ Classes for Vector Boolean Functions in Cryptography. ACM Trans. Math. Softw. 2016, 42, 1–22. [Google Scholar] [CrossRef]
- Bansod, G.; Patil, A.; Sutar, S.; Pisharoty, N. ANU: An ultra-lightweight cipher design for security in IoT. Secur. Commun. Netw. 2016, 9, 4823–6411. [Google Scholar] [CrossRef]
- Kumar, M.; Pal, S.K.; Panigrahi, A. FeW: A lightweight block cipher. MATDER 2019, Turk. J. Math. Comput. Sci. 2019, 11, 58–73. [Google Scholar]
- Wu, W.; Zhang, L. L-block: A lightweight block cipher. In ACNS 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 327–344. [Google Scholar] [CrossRef]
- Shibutani, K.; Isobe, T.; Hiwatari, H.; Mitsuda, A.; Akishita, T.; Shirai, T. Piccolo: An Ultra-Lightweight Block cipher. In CHES 2011; Springer: Berlin/Heidelberg, Germany, 2011; pp. 342–357. [Google Scholar] [CrossRef]
- Matsui, M. New structure of block ciphers with provable security against differential and linear cryptanalysis. In FSE 1996; Gollmann, D., Ed.; Springer: Berlin/Heidelberg, Germany, 1996; pp. 205–218. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).