Artificial Intelligence-Driven Composition and Security Validation of an Internet of Things Ecosystem
Abstract
1. Introduction
- Extension with metrics of the system composition and management procedures. This enables the calculation of the SPD for the currently composed system. Metrics are evolving as an integral characteristic of systems’ development as they are utilized for the comparison of the various possible system configurations, as well as, the impact quantification of the ongoing changes in the main setting.
- Verification that the various components can be composed into the examined system. This becomes imperative for heterogeneous environments (settings with different device types) and system-of-systems (a system comprised of many subsystems).
- Validation of properties that hold after the composition of two systems. This capability is useful in order to assure that the finally composed system fulfills the designed specifications and works correctly.
- Automated reactive strategies and moving-target defenses (MTDs). The IoT ecosystem is dominant by machine-to-machine (M2M) communications. Therefore, we need means to make the overall system self-adaptable to changes, failures, and/or other ongoing events. MTD is also such an approach in the cyber-security field [14]. MTDs include proactive altering of the system configuration, networking, and/or topology to increase the malicious effort for analyzing the system in normal operation, as well as, reactive operations to respond to specific types of ongoing attacks.
2. Related Work
2.1. System Composition
2.1.1. UML-Based Proposals
2.1.2. Logic-Based Proposals
2.2. Security Validation
2.3. Quantifying Security
2.4. Comparison
3. Materials and Methods
3.1. SPD Multi-Metric
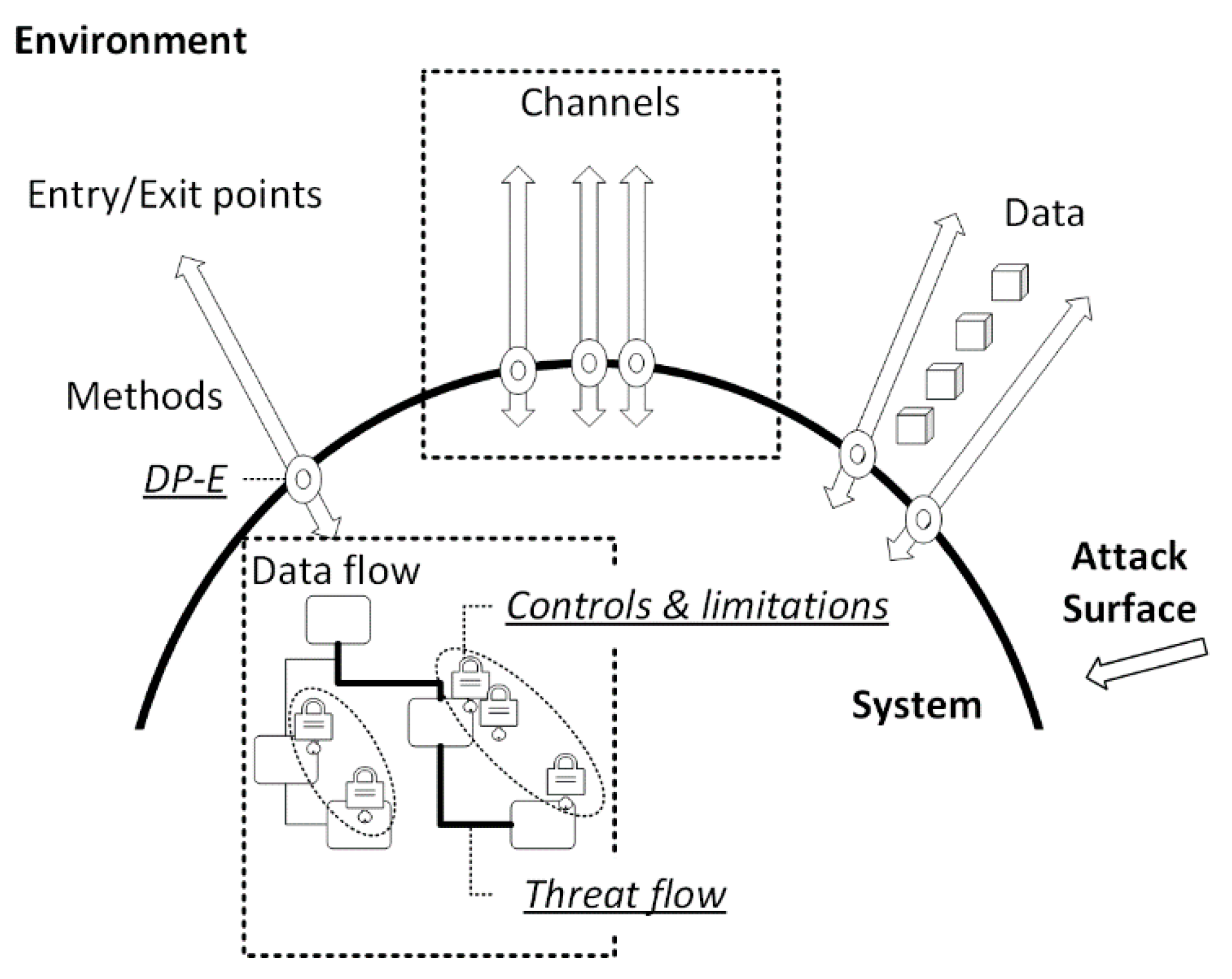
3.1.1. Attack Surface
3.1.2. Protection Level
- -
- Required time: The period that it takes (e.g., days or weeks) to detect and exploit a limitation.
- -
- Expertise: The technical knowledge and skills required (e.g., copy-cat, advanced, or expert).
- -
- Knowledge of the target: Familiarity with the victim’s system and operation (e.g., public, sensitive, or critical knowledge regarding some subsystems, etc.).
- -
- Window of opportunity: Hackers may need appreciable access to the system to successfully presume upon a threat while avoiding detection.
- -
- Resources: The required software, hardware, or other equipment (e.g., common or specialized resources).
3.1.3. Measurement
3.2. Medieval Castle Approach
- -
- AND-operation: 0 ≤ d ≤ dmin
- -
- OR-operation: dmax ≤ d ≤ 1
- -
- MEAN-operation: dmin ≤ d ≤ dmax
3.3. Composed SPD Multi-Metric
4. CompoSecReasoner
4.1. Attributes
4.2. Sources
4.3. Operations
4.3.1. Process Operation
| Algorithm 1: OperationEvaluation |
| Input: The operation identifier op. |
| Output: The operation’s <SPD>. |
| foreach timepoint ti in opdo |
| SequentialAttrs.Add(AttrWithMinSPDAtTi(op)); |
| end |
| foreach attribute attri in SequentialAttrsdo |
| attri.CoverMissingControlsFromAttr(attrii-1); |
| end |
| operationSPD = SequentialAttrs.getFinalAttr().EvaluateSPD(); |
| Return(operationSPD); |
4.3.2. Composition Operation
| Algorithm 2: OperationApplicabilityCheck |
| Input: The component C, the set of operations setop. |
| Output: TRUE/FALSE: checks if the operation can be performed or not. |
| foreach operation opi in opdo |
| opiAttrs = GetOperationAttrs(opi); |
| if (!ContainsAllAttrs(C, opiAttrs)) then |
| Return(FALSE); |
| end |
| end |
| Return(TRUE); |
4.4. System Components
- possess sources–processed data;
- deploy attributes–technologies and protocols;
- execute operations–series of attributes;
- contain sub-components–components of lower layers;
- offer specific SPD levels–based on the assessed metrics and their underlying sub-components.
| Algorithm 3:ComponentSPD |
| Input: The component C. |
| Output: The component’s <SPD>. |
| structuralSPD = MedievalCastleSPD(C); |
| constraintSPD = MinRelativeComponentSPD(C); |
| componentSPD = structuralSPD; |
| if (structuralSPD > constraintSPD) then |
| componentSPD = constraintSPD; |
| end |
| Return(componentSPD); |
4.5. Composition and Decomposition
| Algorithm 4: Composition |
| Input: The component C, a subcomponent subC. |
| Output:TRUE/FALSE: checks if the composition is performed or not. |
| currentSPD = C.SPD; |
| if(!C.ComplyWithFunctionalPre(subC) or !C.ComplyWithNonFunctionalPre(subC))then |
| Return(FALSE); //Composition is blocked |
| end |
| C.compose(subC); //Composition is performed |
| if (ComponentSPD(C) != currentSPD) then |
| Return(FALSE); //Composition is blocked |
| for each subcomponent of C do |
| ComponentSPD(subcomponent); |
| end |
| end |
| ComponentSPD(subC); |
| Return(TRUE); |
5. Compositions of SPD Metrics
5.1. Composition Verification Definitions
- (A)
- Assume QCompOp as the set of composition operations that all qcomp’s sub-components have to be capable to execute.
- (B)
- Assume QCompCons as a set of constraints along with the minimum SPD values that all qcomp’s sub-components have to satisfy.
- (C)
- A componentat the adjacent lower layers of qcomp, could be incorporated to qcomp if it can perform an operationand grantify all the constraints in QCompCons. The composition event is modelled as. After a successful composition at S’, it holds that. A component qcomp2 could be disintegrate from qcomp at any time-point. The decomposition event is modelled as. After a successful decomposition at S′, it holds that.
5.2. SPD Validation Definitions
- (A)
- Assume cons_comp_pre as the pre-conditions of this constraint at qcomp’s layer.
- (B)
- For a sub-layer i, assume cons_subcomp_pre_i as pre-conditions of this the constraint at sub-layer i.
- (C)
- the constraint cons holds iff qcomp fullfils cons_comp_pre and each sub-componentof sub-layer i fulfils the related cons_subcomp_pre_i.
- (D)
- if a sub-componentof sub-layer i violates the related cons_subcomp_pre_i, then disintegrate the sub-component:.
- (A)
- Assume mParam as the parameters of the system which influence m.
- (B)
- If the state of mParam changes, m’s SPD level is re-calculated:.
- (A)
- If the state of qcompsub changes, qcomp’s SPD level is re-calculated:.
- (B)
- If the state of qcomp changes, qcompsub’s SPD level is re-calculated:.
6. Implementation
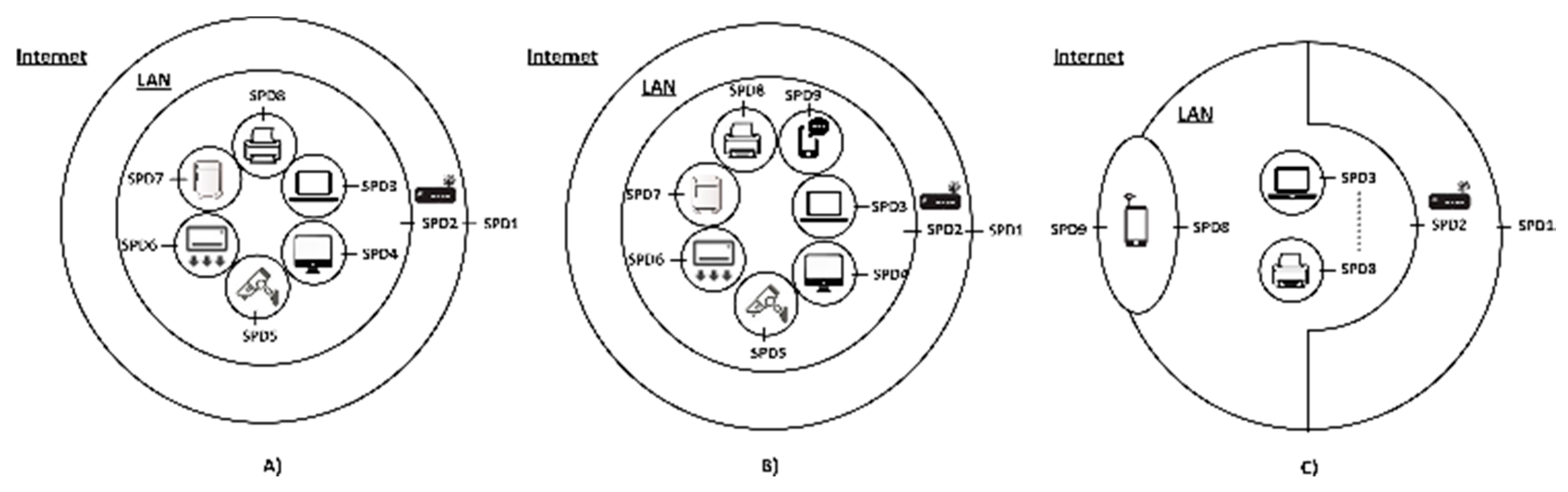
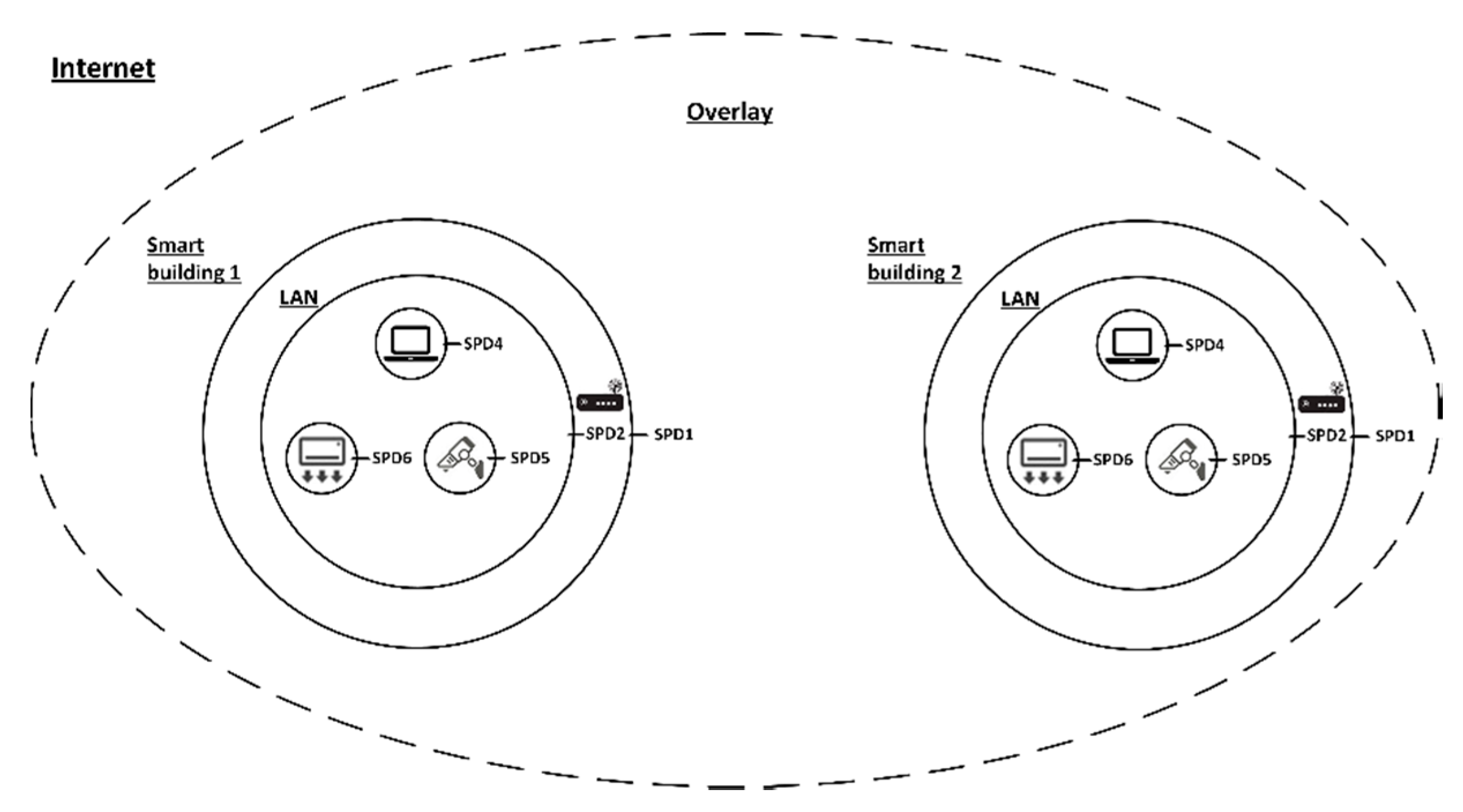
6.1. System Layers
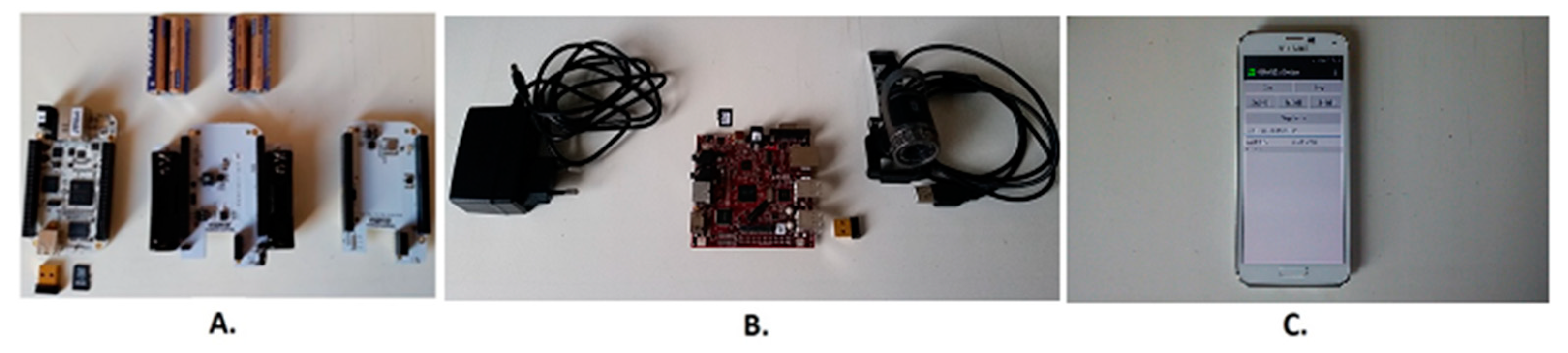
6.2. Motivating Example
6.3. Technical Details
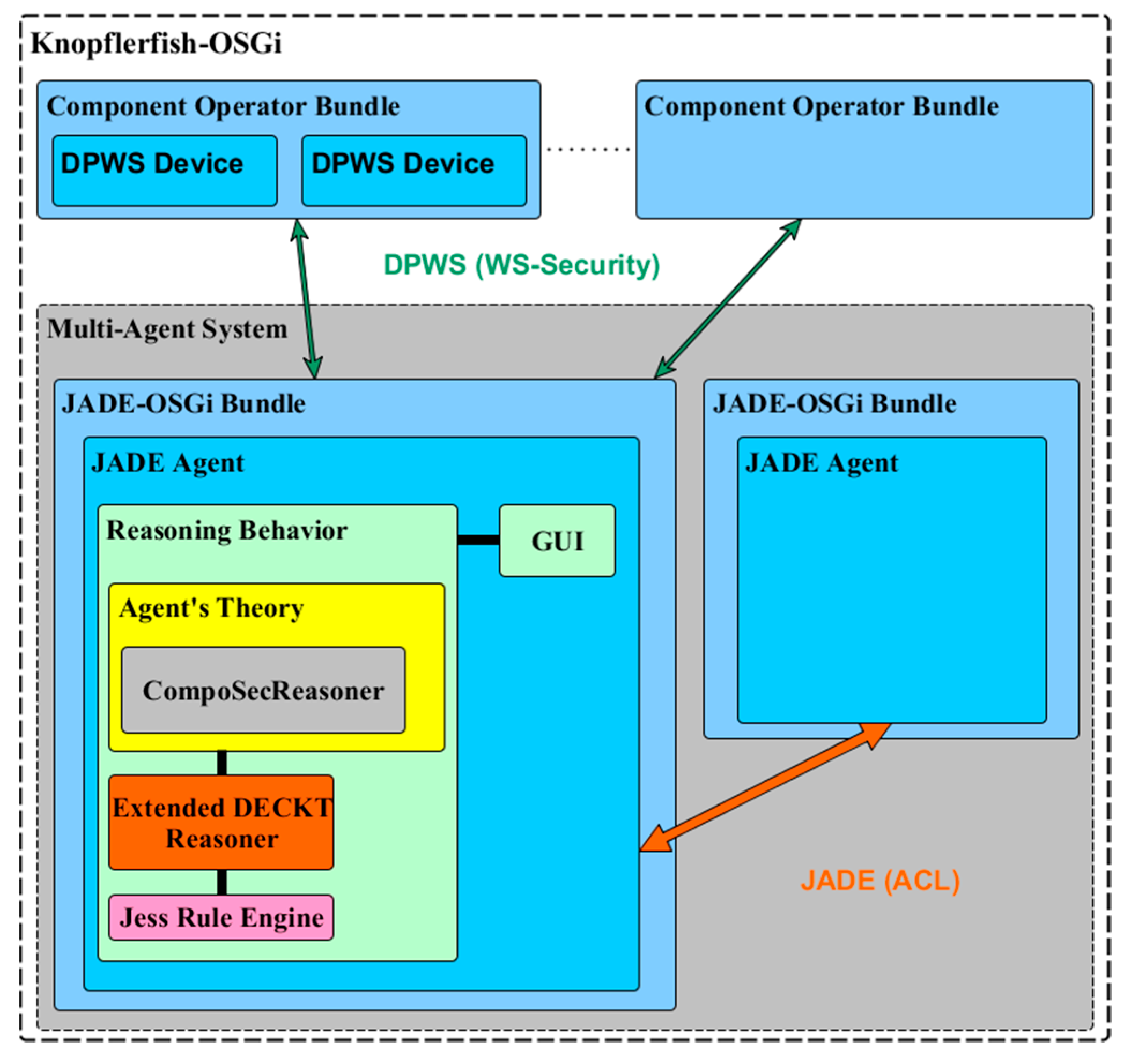
6.3.1. Reasoning System and Agent Technologies
6.3.2. Middleware and Service Platform
6.3.3. Platform Security Features
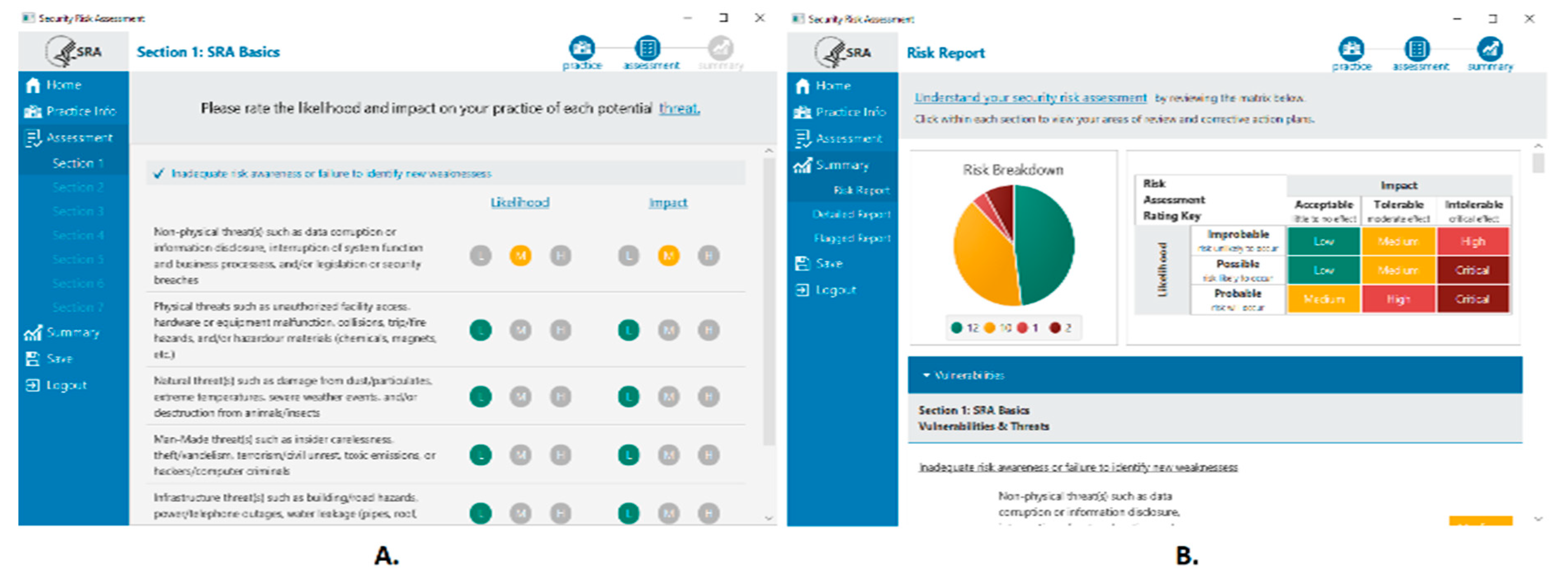
6.4. Demonstration
- Policy Enforcement Point (PEP): lays in the node layer imposing the access control at the device-end
- Policy administration Point (PAP): runs in middleware layer maintaining the access policies
- Policy Decision Point (PDP): also runs in the middleware, assessing the applicable policies which make the authorization decisions
- Policy Information Point (PIP): deployed in the middleware as the framework’s repository for the offered features
6.5. Levels of SPD
6.6. Composition and SPD Assessment
6.7. Reactive Strategies & MTDs
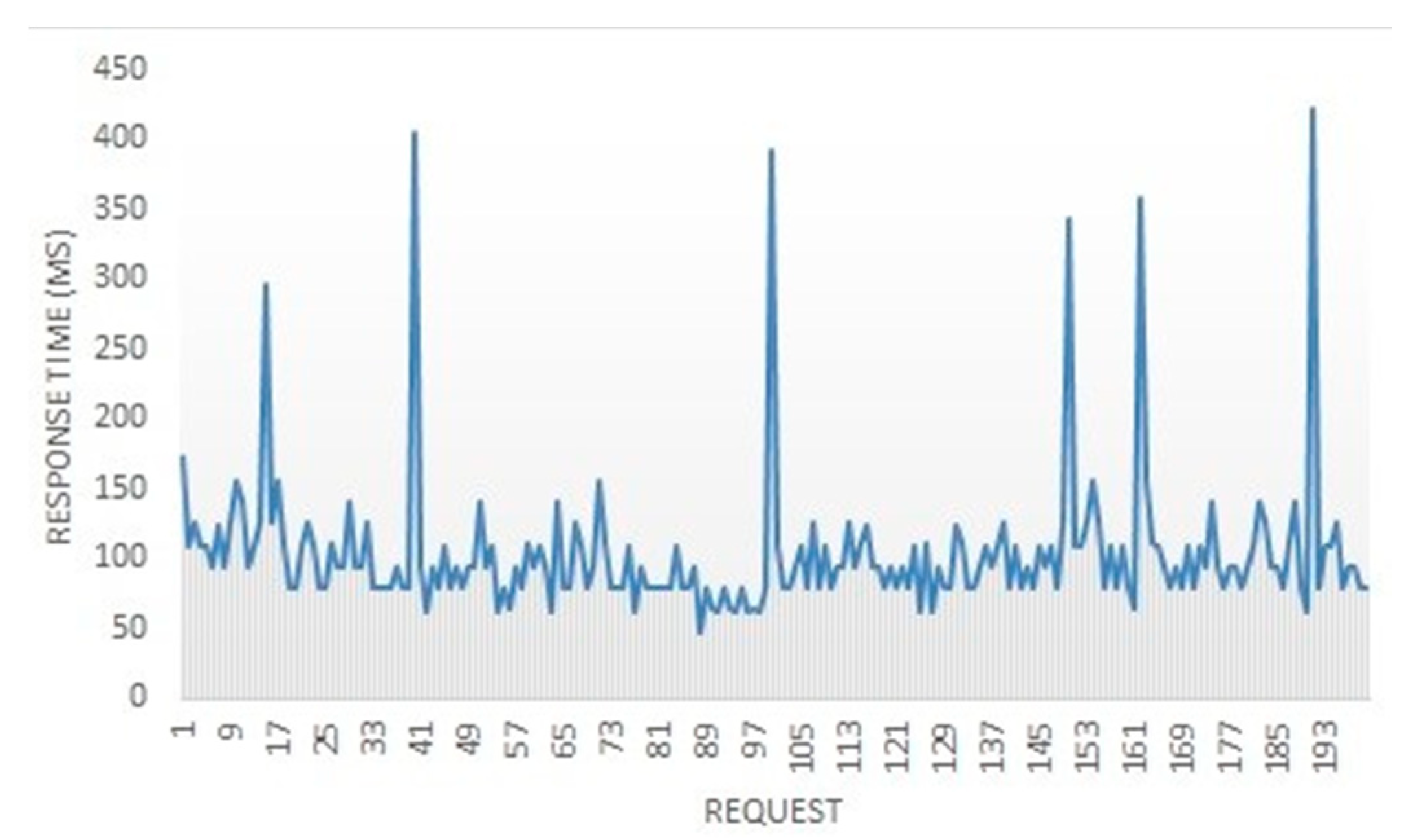
6.8. Performance Assessment
7. Discussion
7.1. Validation of the Derived SPD Values
7.2. Future Work
8. Conclusions
Author Contributions
Funding
Conflicts of Interest
Appendix A
| Control | Description |
|---|---|
| Interactive controls | |
| Security | |
| Authentication | Challenge of credentials based on authorization and identification |
| Resilience | Preserve protection in cases of failure or corruption |
| Subjugation | Assure that interactions happen based on a defined plan, removing liability and freedom of choice of the interacting entity in case of disclosure |
| Continuity | Preserve activity when failure or corruption occurs |
| Indemnification | Formal agreement between the asset owner and other interacting entities. May involve warnings as a precursor of public legislative protection and legal action |
| Privacy | |
| Consent | Freely given, informed, and specific agreement of the personal identifiable information (PII) principal for processing the PII. PII should not be shared or disclosed to third parties without consent from the PII principal |
| Opt-in | Policy or procedures under which the PII principal consents for the explicit processing actions of the PII, prior to relevant consent |
| Indentifiability | The ability to infer the identity of the PII principal, directly or indirectly, by a given set of PII. It may subsume complete indentifiability, pseudonymization or anonymity. |
| Notification | Inform the PII principals whose data is being gathered regarding such collection |
| Dependability | |
| Survivability | Available degraded operations that are useful and acceptable to users when a failure occurs for a specified period |
| Performability | Operations that assures how well the system will perform in the presence of faults for a specified period |
| Removal during use | Mechanisms that record and remove faults via the maintenance cycle after the production stage |
| Passive controls | |
| Security | |
| Confidentiality | Assurance that a processed asset is not known outside the interacting entities |
| Integrity | Assurance that the interacting entities know when an asset has been modified |
| Non-repudiation | Obstructs the interacting entities for denying their role in an occurred interaction |
| Alarm | Notification that an interaction is happening or has happened |
| Privacy | |
| Fairness | PII should be collected, used or disclosed for appropriate and limited purposes |
| Challenge compliance (accountability) | PII principals should be able to hold PII processors accountable for complying with all privacy controls |
| Retention | Insurance that PII which is no longer required, is not retained in order to limit unauthorized collection, usage and disclosure |
| Disposal | Mechanisms for the disposal or destruction of PII |
| Report | Report that an interaction regarding PII is occurring or has occurred |
| Break/incident response | Procedure for managing a breach concerning PII |
| Dependability | |
| Tolerance | Insurance that the needed functionality will be delivered in the presence of faults |
| Forecasting | Prediction of possible faults so that they can be removed or their effects can be circumvented |
| Prevention | Obstructs faults from being integrated into a system. It is achieved by using good implementation techniques and development techniques |
| Removal during development | Verification of a system in order to detect and remove faults before the system is put into production |
References
- Wang, C.; Zhao, Z.; Gong, L.; Zhu, L.; Liu, Z.; Cheng, X. A Distributed Anomaly Detection System for In-Vehicle Network Using HTM. IEEE Access 2018, 6, 9091–9098. [Google Scholar] [CrossRef]
- Hu, L.; Cheng, X.; Che, X. Survey of Grid Resource Monitoring and Prediction Strategies. Int. J. Intell. Inf. Process. 2010, 1, 78–85. [Google Scholar]
- Olszewski, R.; Pałka, P.; Turek, A.; Kietlinska, B.; Płatkowski, T.; Borkowski, M. Spatiotemporal Modeling of the Smart City Residents’ Activity with Multi-Agent Systems. Appl. Sci. 2019, 9, 2059. [Google Scholar] [CrossRef]
- Prasad, K.V.; Giuli, T.J.; Watson, D. The Case for Modeling Security, Privacy, Usability and Reliability (SPUR) in Automotive Software. Aswsd Springer Lncs 2008, 4922, 1–14. [Google Scholar]
- Shull, F.; Feldmann, R.L.; Seaman, C.; Regardie, M.; Godfrey, S. Fully Employing Software Inspections Data. Innov. Syst. Softw. Eng. A Nasa J. Springer 2012, 8, 243–254. [Google Scholar] [CrossRef][Green Version]
- Tabrizi, F.M.; Pattabiraman, K. Formal security analysis of smart embedded systems. In Proceedings of the Annual Computer Security Applications Conference (ACSAC), Los Angeles, CA, USA, 5–9 December 2016. [Google Scholar]
- Tabrizi, F.M.; Pattabiraman, K. A model for security analysis of smart meters. In Proceedings of the IEEE/IFIP 42nd International Conference on Dependable Systems and Networks Workshops (DSN-W), Boston, MA, USA, 25–28 June 2012. [Google Scholar]
- Rupp, A.; Baldimtsi, F.; Hinterwalder, G.; Paar, C. Cryptographic Theory Meets Practice: Efficient and Privacy-Preserving Payments for Public Transport. ACM Trans. Inf. Syst. Secur. (TISSEC) 2015, 17, 1–31. [Google Scholar] [CrossRef]
- Li, J.; Li, J.; Chen, X.; Liu, Z.; Jia, C. Privacy-preserving data utilization in hybrid clouds. Future Gener. Comput. Syst. 2014, 30, 98–106. [Google Scholar] [CrossRef]
- Jia, B.; Hao, L.; Zhang, C.; Huang, B. A Privacy-sensitive Service Selection Method Based on Artificial Fish Swarm Algorithm in the Internet of Things. Mob. Netw. Appl. 2020. [Google Scholar] [CrossRef]
- Avizienis, A.; Laprie, J.-C.; Randell, B.; Landwehr, C. Basic concepts and taxonomy of dependable and secure computing. IEEE Trans. Dependable Secur. Comput. (Tdsc) 2004, 1, 11–33. [Google Scholar] [CrossRef]
- Natella, R.; Cotroneo, D.; Madeira, H.S. Assessing dependability with software fault injection. Acm Comput. Surv. 2016, 48, 1–55. [Google Scholar] [CrossRef]
- Cinque, M.; Cotroneo, D.; Pecchia, A. Enabling effective dependability evaluation of complex systems via a rule-based logging framework. Int. J. Adv. Softw. 2009, 2, 323–336. [Google Scholar]
- Lei, C.; Zhang, H.-Q.; Tan, J.-L.; Zhang, Y.-C.; Liu, X.-H. Moving Target Defense Techniques: A Survey. Secur. Commun. Netw. 2018, 2018, 1–25. [Google Scholar] [CrossRef]
- JADE Framework. Available online: http://jade.tilab.com/ (accessed on 14 July 2020).
- OSGi Alliance. Available online: http://www.osgi.org/ (accessed on 14 July 2020).
- OASIS, DPWS. Available online: http://docs.oasis-open.org/ws-dd/dpws/1.1/os/wsdd-dpws-1.1-spec-os.pdf (accessed on 14 July 2020).
- Asghari, P.; Rahmani, A.M.; Javadi, H.H.S. Service composition approaches in IoT: A systematic review. J. Netw. Comput. Appl. 2018, 120, 61–77. [Google Scholar] [CrossRef]
- Aoudia, I.; Benharzallah, S.; Kahloul, L.; Kazar, O. Service composition approaches for internet of things: A review. Int. J. Commun. Netw. Distrib. Syst. 2019, 23, 194–230. [Google Scholar]
- UML. Available online: https://www.uml.org/ (accessed on 14 July 2020).
- Brambilla, M.; Fraternali, P. Interaction Flow Modeling Language: Model-Driven UI Engineering of Web and Mobile Apps with IFML; The MK/OMG Press: Burlington, MA, USA, 2014; pp. 1–422. [Google Scholar]
- Object Management Group (OMG), 1989–2020. Available online: https://www.omg.org/ (accessed on 14 July 2020).
- Brambilla1, M.; Umuhoza1, E.; Acerbis, R. Model-driven development of user interfaces for IoT systems via domain-specific components and patterns. J. Internet Serv. Appl. 2017, 8, 1–21. [Google Scholar]
- Souri, A.; Norouzi, M. A State-of-the-Art Survey on Formal Verification of the Internet of Things Applications. J. Serv. Sci. Res. 2019, 11, 47–67. [Google Scholar] [CrossRef]
- Sztipanovits, J.; Karsai, G. Model-integrated computing. IEEE Comput. 1997, 30, 110–112. [Google Scholar] [CrossRef]
- Kelly, S.; Tolvanen, J.-P. Domain-Specific Modeling: Enabling Full Code Generation; Wiley-IEEE Computer Society Pr.: Hoboken, NJ, USA, 2008; pp. 1–444. [Google Scholar]
- Society of Automotive Engineers (SAE), 1905–2020. Available online: https://www.sae.org/ (accessed on 14 July 2020).
- SAE. Architecture Analysis & Design Language. SAE Standard AS-5506. 2004. Available online: www.sae.org/standards/content/as5506c/ (accessed on 14 July 2020).
- Murugesan, A.; Whalen, M.W.; Rayadurgam, S.; Heimdahl, M.P.E. Compositional Verification of a Medical Device System. In Proceedings of the ACM SIGAda annual conference on High integrity language technology (HILT), Pittsburgh, PA, USA, 10–14 November 2013; pp. 51–64. [Google Scholar]
- Szemethy, T.; Karsai, G. Platform modeling and model transformation for analysis. J. Univers. Comput. Sci. 2004, 10, 1383–1406. [Google Scholar]
- Yamaoka, H.; Itakura, K.; Takahashi, E.; Nakagawa, G.; Michaelis, J.; Kanemasa, Y.; Ueki, M.; Matsumoto, T.; Take, R.; Tanie, S.; et al. Dracena: A Real-Time IoT Service Platform Based on Flexible Composition of Data Streams. In Proceedings of the IEEE/SICE International Symposium on System Integration, Paris, France, 14–16 January 2019; pp. 596–601. [Google Scholar]
- Incki, K.; Ari, I. A Novel Runtime Verification Solution for IoT Systems. IEEE Access 2018, 6, 13501–13512. [Google Scholar] [CrossRef]
- Shelby, Z.; Hartke, K.; Bormann, C. The Constrained Application Protocol (CoAP). Internet Eng. Task Force (IETF) RFC7252 2014. [Google Scholar] [CrossRef]
- Larson, B.R.; Chalin, P.; Hatcliff, J. BLESS: Formal Specification and Verification of Behaviors for Embedded Systems with Software. In Proceedings of the NASA Formal Methods Symposium, Moffett Field, CA, USA, 14–16 May 2013; pp. 276–290. [Google Scholar]
- Krishna, A.; Pallec, M.L.; Mateescu, R.; Noirie, L.; Salaun, G. IoT Composer: Composition and Deployment of IoT Applications. In Proceedings of the IEEE/ACM 41st International Conference on Software Engineering: Companion Proceedings (ICSE-Companion), Montreal, QC, Canada, 25–31 May 2019; pp. 19–22. [Google Scholar]
- Kushilevitz, E.; Lindell, Y.; Rabin, T. Information-theoretical secure protocols and security under composition. Slam J. Comput. 2010, 39, 2090–2112. [Google Scholar]
- de Albuquerque, J.P.; Krumm, H.; de Geus, P.L. Formal validation of automated policy refinement in the management of network security systems. Int. J. Inf. Secur. 2010, 9, 99–125. [Google Scholar] [CrossRef]
- Kidron, D.; Lindell, Y. Impossibility results for universal composability in public-key models and with fixed inputs. J. Cryptol. 2011, 24, 517–544. [Google Scholar] [CrossRef]
- Kulik, T.; Tran-Jørgensen, P.W.V.; Boudjadar, J.; Schultz, C. A Framework for Threat-driven Cyber Security Verification of IoT Systems. In Proceedings of the IEEE International Conference on Software Testing, Verification and Validation Workshops, Västerås, Sweden, 9–13 April 2018; pp. 89–97. [Google Scholar]
- Alloy Analyzer. Available online: https://alloytools.org/ (accessed on 14 July 2020).
- Eby, M. Integrating Security Modeling into Embedded System Design. Master’s Thesis, Vanderbilt University, Nashville, TN, USA, 2007. [Google Scholar]
- Bielova, N. A Theory of Constructive and Predictable Runtime Enforcement Mechanisms. Ph.D. Dissertation, University of Trento, Trento, Italy, November 2011. [Google Scholar]
- Savola, R.M.; Heinonen, P. A visualization and modeling tool for security metrics and measurements management. In Proceedings of the 2011 Information Security for South Africa, Johannesburg, South Africa, 15–17 August 2011; pp. 1–8. [Google Scholar]
- Ko, H.; Jin, J.; Keoh, S.L. Secure Service Virtualization in IoT by Dynamic Service Dependency Verification. IEEE Internet Things J. 2016, 3, 1006–1014. [Google Scholar] [CrossRef]
- Walter, M.; Trinitis, C. Quantifying the security of composed systems. In Proceedings of the International Conference on Parallel Processing and Applied Mathematics (PPAM’05), Poznan, Poland, 11–14 September 2005; Springer: Berlin/Heidelberg, Germany, 2006; pp. 1026–1033. [Google Scholar]
- Leuprecht, C.; Skillicorn, D.B.; Tait, V.E. Beyond the Castle Model of cyber-risk and cyber-security. Gov. Inf. Q. 2016, 33, 250–257. [Google Scholar] [CrossRef]
- Schannep, J.H.; Doukas, J.C.; Song, S.C. Advancing cybersecurity from Medieval Castles to STrategic Deterrence: A Systems Approach to cybersecurity. In Proceedings of the International Annual Conference of the American Society for Engineering Management, Coeur d’Alene, ID, USA, 17–20 October 2018; pp. 1–10. [Google Scholar]
- Theisen, C.; Munaiah, N.; Al-Zyoud, M.; Carver, J.C.; Meneely, A.; Williams, L. Attack surface definitions: A systematic literature review. Inf. Softw. Technol. 2018, 104, 94–103. [Google Scholar] [CrossRef]
- Younis, A.A.; Malaiya, Y.K.; Ray, I. Using Attack Surface Entry Points and Reachability Analysis to Assess the Risk of Software Vulnerability Exploitability. In Proceedings of the IEEE 15th International Symposium on High-Assurance Systems Engineering, Miami Beach, FL, USA, 9–11 January 2014; pp. 1–8. [Google Scholar]
- Theisen, C.; Murphy, B.; Herzig, K.; Williams, L. Risk-Based Attack Surface Approximation: How Much Data is Enough? In Proceedings of the IEEE/ACM 39th International Conference on Software Engineering: Software Engineering in Practice Track, Buenos Aires, Argentina, 20–28 May 2017; pp. 271–280. [Google Scholar]
- Yoon, C.; Lee, S.; Kang, H.; Park, T.; Shin, S.; Yegneswaran, V.; Porras, P.; Gu, G. Flow Wars: Systemizing the Attack Surface and Defenses in Software-Defined Networks. IEEE/Acm Trans. Netw. 2017, 25, 3514–3530. [Google Scholar] [CrossRef]
- Manadhata, P.K.; Wing, J.M. An attack surface metric. IEEE Trans. Softw. Eng. (Tse) 2010, 37, 371–386. [Google Scholar] [CrossRef]
- Howard, M.; Corporation, M. Determining Relative Attack Surface. U.S. Patent US 7299497 B2, 20 November 2007. [Google Scholar]
- Eguia, I.; Ser, J.D. A Meta-Heuristically Optimized Fuzzy Approach towards Multi-Metric Security Risk Assessment in Heterogeneous System of Systems. In Proceedings of the MeSeCC, Lisbon, Portugal, 7–9 January 2014. [Google Scholar]
- Chen, J. Dynamic Cyber Defence Framework. J. Inf. Warf. 2016, 15, 46–55. [Google Scholar]
- Albanese, M.; Battista, E.; Jajodia, S.; Casola, V. Manipulating the Attacker’s View of a System’s Attack Surface. In Proceedings of the IEEE Conference on Communications and Network Security, San Francisco, CA, USA, 29–31 October 2014; pp. 472–480. [Google Scholar]
- Savola, R.M.; Sihvonen, M. Metrics Driven Security Management Framework for E-Health Ecosystem Focusing on Chronic Diseases. In Proceedings of the International Conference on Management of Emergent Digital EcoSystems, Addis Ababa, Ethiopia, 28–31 October 2012; pp. 75–79. [Google Scholar]
- Krautsevich, L.; Martinelli, F.; Yautsiukhin, A. Formal approach to security metrics. What does “more secure” mean to you? ECSA 2010, 10, 162–169. [Google Scholar]
- Hatzivasilis, G. Multi-agent distributed epistemic reasoning in ambient intelligence environments. Master’s Thesis, University of Crete, Greece—FORTH-ICS, Heraklion, Greece, November 2011. [Google Scholar]
- Madl, G.; Abdelwahed, S. Model-based analysis of distributed real-time embedded system composition. In Proceedings of the 5th ACM international conference on Embedded software, EMSOFT’05, Jersey City, NJ, USA, 19–22 September 2005; pp. 371–374. [Google Scholar]
- Hatzivasilis, G.; Papaefstathiou, I.; Manifavas, C. Software Security, Privacy and Dependability: Metrics and Measurement. IEEE Softw. 2016, 33, 46–54. [Google Scholar] [CrossRef]
- ISECOM. Open Source Security Testing Methodology Manual. 1988–2015. Available online: https://www.isecom.org/OSSTMM.3.pdf (accessed on 14 July 2020).
- ISECOM. Common Criteria for Information Security Evaluation. 1996–2015. Available online: http://www.commoncriteriaportal.org (accessed on 14 July 2020).
- ISO/IEC. Code of Practice for Protection of Personally Identifiable Information (PII) in Public Clouds Acting as PII Processors. ISO/IEC 27018. 2014. Available online: http://www.iso.org/iso/catalogue_detail?csnumber=61498 (accessed on 14 July 2020).
- ISO/IEC. Privacy framework. ISO/IEC 29100. 2011. Available online: https://www.iso.org/obp/ui/#iso:std:iso-iec:29100:ed-1:v1:en (accessed on 14 July 2020).
- IEC. International Standard on Dependability. IEC 60300. 2017. Available online: https://tc56.iec.ch/dependability-standards/ (accessed on 14 July 2020).
- EU Funded Project—nSHIELD: New Embedded Systems arcHItecturE for Multi-Layer Dependable Solutions. Available online: https://artemis-ia.eu/project/34-nshield.html/ (accessed on 14 July 2020).
- Cesena, M. SHIELD Technology Demonstrators. In Measurable and Composable Security, Privacy, and Dependability for Cyberphysical Systems; CRC Press: Boca Raton, FL, USA, 2017; pp. 381–434. [Google Scholar]
- Muller, E.T. Commonsense Reasoning; Morgan Kaufmann Publishers: Burlington, MA, USA, 2010. [Google Scholar]
- Mantas, G.; Lymberopoulos, D.; Komninos, N. Security in smart home environment. In Wireless Technologies for Ambient Assisting Living and Healthcare: Systems and Applications; IGI Global: Hershey, PA, USA, 2010; pp. 170–191. [Google Scholar]
- Rantos, K.; Fysarakis, K.; Manifavas, C.; Askoxylakis, I. Policy-controlled authenticated access to LLN-connected healthcare resources. IEEE Syst. J. 2015, 12, 92–102. [Google Scholar] [CrossRef]
- Hatzivasilis, G.; Gasparis, E.; Theodoridis, A.; Manifavas, C. ULCL: An Ultra-Lightweight Cryptographic Library for embedded systems. In Proceedings of the MeSeCCS, Lisbon, Portugal, 7–9 January 2014; pp. 11–18. [Google Scholar]
- BeagleBone.org. BeagleBone Device Manual. Available online: http://beagleboard.org/static/beaglebone/a3/Docs/Hardware/BONE_SRM.pdf (accessed on 14 July 2020).
- Patkos, T.; Plexousakis, D. DECKT: Epistemic reasoning for ambient intelligence. In ERCIM News Magazine; ERCIM: Valbonne, France, 11 January 2011. [Google Scholar]
- FIPA. Available online: http://www.fipa.org/ (accessed on 14 July 2020).
- FIPA, ACL. Available online: http://en.wikipedia.org/wiki/Agent_Communication_Language (accessed on 14 July 2020).
- Makewave, Knopflerfish. Available online: http://www.knopflerfish.org/ (accessed on 14 July 2020).
- Strzałek, M.; Pałka, P. The issue of confidentiality, authentication, integrity and data non-repudiation in the multiagent systems. Studia Inform. 2012, 33, 217–227. [Google Scholar]
- Berstel, B. Extending the RETE algorithm for event management. In Proceedings of the IEEE 9th International Symposium on Temporal Representation and Reasoning, Manchester, UK, 7–9 July 2002; pp. 49–51. [Google Scholar]
- Malcolm, Y. A Federated Agent-Based Crowd Simulation Architecture. In Proceedings of the 21st European Conference on Modelling and Simulation (ECMS), Prague, Czech Republic, 4–6 June 2007; pp. 1–7. [Google Scholar]
- NIST. National Institute of Standards and Technology. USA, 1901–2020. Available online: https://www.nist.gov/ (accessed on 14 July 2020).
- TNIS. Common Vulnerability Scoring System (CVSS). NIST, 2019. Available online: https://www.first.org/cvss/ (accessed on 14 July 2020).
- NIST. CVSS Calculator. NIST, 2019. Available online: https://www.first.org/cvss/calculator/3.1 (accessed on 14 July 2020).
- Brian, A.; Fox, K.; Daniel, M. The Politics of the Health Insurance Portability and Accountability Act. Health Aff. 1997, 16, 146–150. [Google Scholar]
- TNIS; AHIPA. Security Risk Assessment Tool (SRA). NIST, 2019. Available online: https://www.healthit.gov/topic/privacy-security-and-hipaa/security-risk-assessment-tool (accessed on 14 July 2020).
- Manifavas, C.; Fysarakis, K.; Rantos, K.; Hatzivasilis, G. DSAPE—Dynamic Security Awareness Program Evaluation. In Proceedings of the International Conference on Human Aspects of Information Security, Privacy, and Trust, Heraklion, Crete, Greece, 22–27 June 2014; Volume 8533, pp. 258–269. [Google Scholar]
- Cotroneo, D.; Natella, R.; Rietrantuono, R.; Russo, S. A survey of software aging and rejuvenation studies. Acm J. Emerg. Technol. Comput. Syst. 2014, 10, 1–34. [Google Scholar] [CrossRef]
- Kapica, J.U.S. Exploits Iraq’s Aging Cryptography. Globe and Mail Update. 2013. Available online: http://www.theglobeandmail.com/technology/us-exploits-iraqs-aging-cryptography/article20448490/ (accessed on 14 July 2020).


| Feature | A | B | C | D | E | F | G | H | I | J | K |
|---|---|---|---|---|---|---|---|---|---|---|---|
| System composition | |||||||||||
| Dynamicity | Y | N | Y | Y | Y | Y | Y | Y | Y | N | N |
| Expressiveness generality | Y | Y | Y | Y | N | Y | Y | N | Y | N | N |
| Validation | |||||||||||
| Pre-composition | Y | Y | Y | Y | N | Y | Y | Y | Y | N | N |
| Post-composition | Y | N | N | N | Y | Y | Y | N | N | N | N |
| Evaluated Properties | |||||||||||
| Security | Y | N | N | N | N | N | N | Y | Y | Y | Y |
| Privacy | Y | N | N | N | N | N | N | N | N | N | N |
| Dependability | Y | P | P | P | Y | Y | Y | P | P | N | P |
| Artificial Intelligence | |||||||||||
| Distributed reasoning/processing | Y | N | N | Y | Y | Y | Y | N | Y | N | Y |
| Conflict resolution | Y | N | N | N | N | N | N | N | N | N | N |
| MTD | Y | N | N | N | N | N | Y | N | N | Y | Y |
| SPD Property | Damage Potential | Effort |
|---|---|---|
| Security | Privilege [62] -Root: 5 -Debugger: 4 -Authenticated user: 3 | Access rights [62] -Administrator: 4 -Authenticated user: 3 -Anonymous user: 1 -Unauthenticated user: 1 |
| Privacy | PII (personal identifiable information) type [64] -Sensitive personal data: 5 -Personal data: 4 -Statistical data:1 | PII actuator [64] -PII principal: 4 -Contracted PII processor: 3 -Third party: 2 |
| Dependability | Criticality [65] -Mission critical: 4 -Business critical: 3 -Business operational: 2 -Business supporting: 1 | Dependency level [65] -Coupling: 4 -Outgoing dependency: 3 -Incoming dependency: 2 -Independent operation: 1 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Hatzivasilis, G.; Papadakis, N.; Hatzakis, I.; Ioannidis, S.; Vardakis, G. Artificial Intelligence-Driven Composition and Security Validation of an Internet of Things Ecosystem. Appl. Sci. 2020, 10, 4862. https://doi.org/10.3390/app10144862
Hatzivasilis G, Papadakis N, Hatzakis I, Ioannidis S, Vardakis G. Artificial Intelligence-Driven Composition and Security Validation of an Internet of Things Ecosystem. Applied Sciences. 2020; 10(14):4862. https://doi.org/10.3390/app10144862
Chicago/Turabian StyleHatzivasilis, George, Nikos Papadakis, Ilias Hatzakis, Sotiris Ioannidis, and George Vardakis. 2020. "Artificial Intelligence-Driven Composition and Security Validation of an Internet of Things Ecosystem" Applied Sciences 10, no. 14: 4862. https://doi.org/10.3390/app10144862
APA StyleHatzivasilis, G., Papadakis, N., Hatzakis, I., Ioannidis, S., & Vardakis, G. (2020). Artificial Intelligence-Driven Composition and Security Validation of an Internet of Things Ecosystem. Applied Sciences, 10(14), 4862. https://doi.org/10.3390/app10144862






