1. Introduction
A wireless body area network (WBAN) is a wireless network of wearable computing devices including implanted devices embedded inside the body or attached on the skin, and accompanied devices which humans can carry by hand, in clothes pockets or in bags [
1,
2,
3,
4]. WBAN applications [
5,
6] are growing and becoming more indispensable in people’s lives due to the increasing accessability of network service and computing devices. Despite the great progress in networking and computing technology, security is one significant factor that influences users’ choice of WBAN applications, since such applications involve a lot of personal information and therefore are vulnerable to security issues.
IEEE Standard (Std) 802.15.6 [
7] is an international standard for wireless communication between nodes and hubs in WBANs. It provides strong security for communications that carry sensitive information. In the security services of this standard, the security association procedure activates a pre-shared or generates a new shared master key (MK) between a node and a hub. Several security association protocols suitable for a variety of use cases are provided in this standard. Among these protocols, password authenticated association [
8,
9] is a protocol for a node and a hub to generate a new shared MK from a pre-shared secret, i.e., the password. However, recent research shows that this protocol is vulnerable to several attacks, such as Man-in-the-Middle and impersonation attacks illustrated in [
10], and the off-line dictionary attack and there being a lack of forward secrecy, which are discussed in [
11,
12]. To eliminate these attacks, the authors in [
10] also proposes a modified version to this protocol.
In this paper, an improved password authenticated association protocol is proposed. In the rest of this paper, we denote this protocol by the
improved protocol, protocol in [
10] by the
modified protocol and protocol in the IEEE 802.15.6 standard by the
standard protocol. Compared with the modified protocol and the standard protocol, the improved protocol eliminates all the above attacks on one hand. Moreover, it alleviates computational burden on the node. Since the node usually has limited computational power compared with the hub, the improved protocol is meaningful in practise.
The remaining part of this paper is organized as follows:
Section 1 contains preliminaries and symbols that are useful in this paper. In
Section 3, we review the standard protocol and available attacks in literature. In
Section 4, the improved protocol is proposed and its security and performance are analyzed in
Section 5 and
Section 6, respectively.
Section 7 shows a use case of this improved protocol. Related works are provided in
Section 8. Finally,
Section 9 concludes this paper.
2. Preliminaries and Symbols
2.1. Elliptic Curve Public Key Cryptography
2.1.1. Elliptic Curve
The IEEE 802.15.6 password authenticated association protocol is based on the Diffie–Hellman key exchange [
13] employing the elliptic curve public key cryptography (ECC). An elliptic curve
E can be characterized by the following equation [
14,
15]:
where
is a point on the curve;
a and
b are coefficients;
p is an odd prime; and
is a prime finite field. For the choices of a suitable elliptic curve, the IEEE Std 802.15.6 suggests using Curve p-256 in FIPS Pub 186-3. Values of
a,
b,
p, the base point
and the order
r of
G are given in the standard.
2.1.2. Elliptic Curve Diffie–Hellman
Elliptic curve Diffie–Hellman (ECDH) is an anonymous key agreement protocol that allows two parties, each having an elliptic curve public-private key pair, to establish a shared secret over an insecure channel [
16]. Suppose
and
are private keys of two communicating parties A and B, respectively.
and
are random integers from the set
. The corresponding public keys
and
are computed as follows:
where × denotes scalar multiplication of
G by an integer. In the ECDH protocol, A and B exchange their public keys and compute
and
, respectively. The shares key is
, i.e., the
X coordinate of the point.
2.2. Password Authenticated Key Exchange
The password authenticated association protocol in the IEEE 802.15.6 standard is a variation of password authenticated key exchange (PAKE) [
8]. A PAKE protocol uses a pre-shared password for an authenticated key establishment. The password is usually short and easy for humans to remember, and is not stored directly in the memory of physical devices for security purpose. Instead, it is input by the users at the beginning of each run of the PAKE protocol.
2.3. Symbols
The association protocol is initiated by the node to generate a shared master key with the hub from a pre-shared password between them. We denote the node as the initiator and the hub as the responder. Some other symbols used in this paper are summarized in
Table 1.
3. IEEE 802.15.6 Password Authenticated Association Protocol
We review the IEEE 802.15.6 password authenticated association protocol, i.e., the standard protocol, and discuss its vulnerabilities in this section.
3.1. Description of the Standard Protocol
3.1.1. Set-Up
The initiator and the responder set up their private and public key as follows:
3.1.2. Master Key Generation
The initiator and the responder execute the following steps to generate a shared master key.
The initiator computes a password-scrambled public key
and sends it to the responder along with a nonce
and the identities
I and
R:
After receiving
, the responder sends the identities, a nonce and its public key back to the initiator:
The responder recovers
as follows:
The initiator and the responder compute the Diffie–Hellman key, respectively, through
The responder computes a message authentication code
and then sends the initiator
The initiator verifies the received
. If the verification succeeds, the initiator computes a message authentication code
and sends the responder
The responder verifies
. If the verification succeed, both parties compute and activate their new master key as follows:
3.2. Security Problems
The standard protocol uses the password to hide the public key of the initiator through
in the first step, so that only the responder can recover
from
. However, the protocol reveals
in
of step 4, which means an eavesdropper who intercepts
can acquire
. In this case, the password is no longer secret in the following runs of the protocol. This is the reason for the vulnerabilities of the standard protocol. Security problems and attacks to this standard protocol in literature are summarized as follows:
Impersonation attack. In [
10] the authors illustrate an initiator impersonation attack and a responder impersonation attack to the standard protocol. At the end of these attacks, the attackers successfully establish a master key with one side of the communicating parties, while the other side thinks it has the shared master key with the true participant.
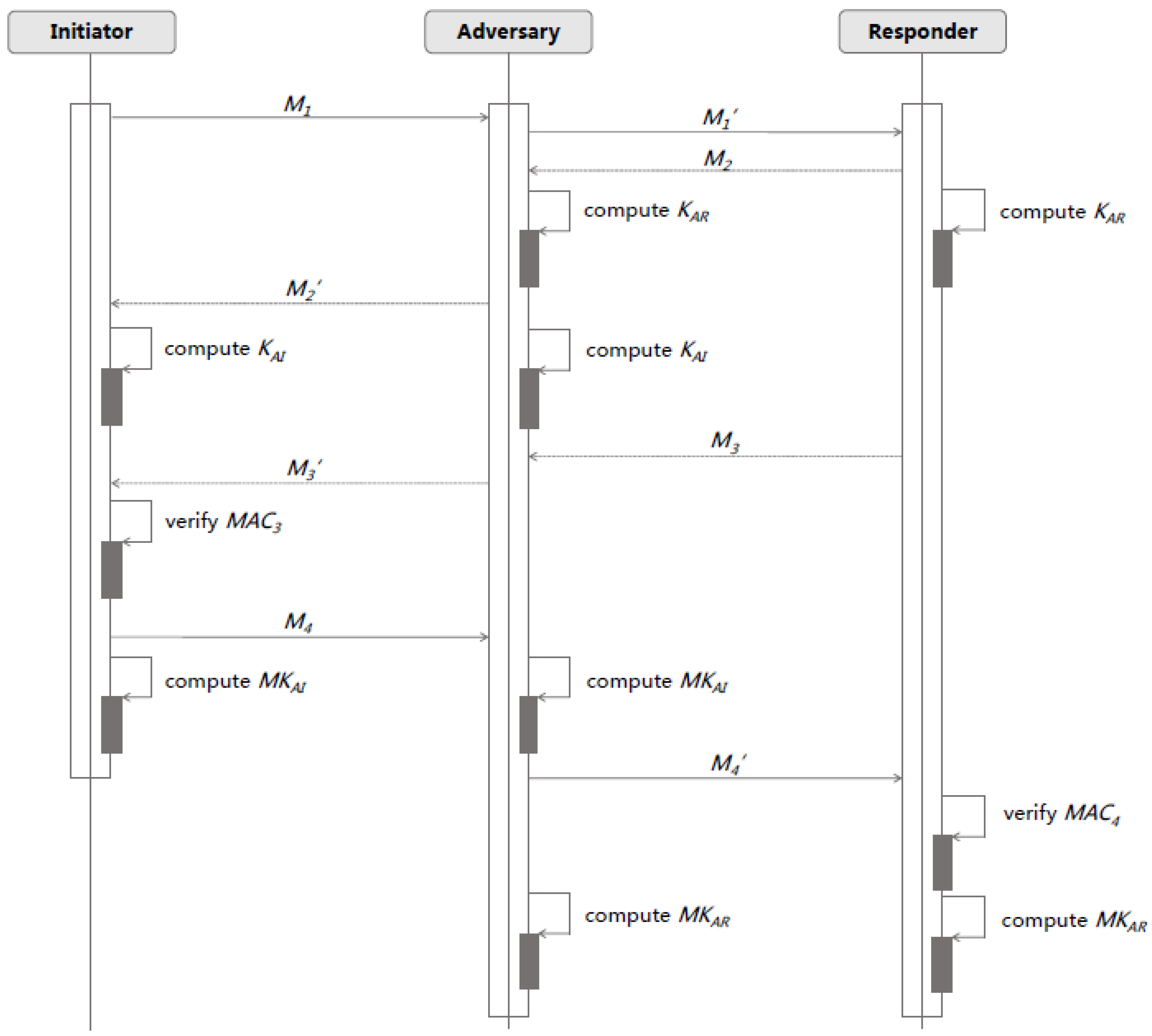
Man-in-the-Middle attack. In [
10], the authors show that an attacker breaks into the communication between the initiator and the responder and modifies the messages at his/her will. At last, the attacker shares two master keys with the initiator and the responder, respectively, while the initiator and the responder think they have a shared master key.
Figure 1 is a time-sequence diagram that illustrates the procedure of man-in-the middle attack against the protocol.
Off-line dictionary attack. The authors in [
11,
12] show that a dictionary attacker who eavesdrops messages between the initiator and the responder in a protocol run can obtain
and
and compute
from
. Then,
can be used as a verifier and the attacker can try probable
s from a dictionary of most probable passwords and check them using
.
Lack of forward secrecy. The author in [
11,
12] illustrates that if
has been compromised by an attacker, the attacker can acquire the Diffie–Hellman key
K through computing
and
from
since
,
and
are sent in the form of plaintext.
3.3. The Modified Protocol
The authors in [
10] propose a modified protocol to the standard protocol. Specifically, the modified protocol is similar to the standard one except that it does not send
in the clear in
. This modification solves most security problems as we mentioned in
Section 3.2, but it still fails to provide forward secrecy. We will compare security and performance of the two protocols with those of our new proposed protocol later in this paper.
4. The Improved Protocol
The improved protocol assumes that
and
can be reused in each round of protocol. This assumption is reasonable since, in the improved protocol, the temporary Diffie–Hellman key
K is derived from two random values chosen by the initiator and the responder, respectively, rather than their public and private keys. The improved protocol is described in detail as follows.
The initiator chooses a random value
and computes
and
Then, the initiator sends message
to the responder.
The responder chooses a random value
and computes
and
Then, the responder sends message
to the initiator
The responder recovers
as follows:
The initiator computes the Diffie–Hellman key through
The responder computes
K as follows
With the
K, the responder computes a message authentication code
and then sends the initiator
The initiator verifies the received
. If the verification succeeds, the initiator computes a message authentication code
and sends the responder
The responder verifies
. If the verification succeeds, both parties compute and activate their new master key as follows:
5. Security Analysis
In
Section 3.2, we listed all the attacks to the standard protocol, and in this section, we will prove the security of the improved protocol under all of these attacks.
5.1. Impersonation Attack
Proposition 1. Suppose the initiator and the responder have shared a password secretly, and an attacker is not able to impersonate the initiator to establish the master key with the responder.
Proof. Assume
is an attacker who attempts to impersonate the initiator and establish
with the responder.
attacks the protocol as follows:
initializes the protocol with the responder by sending the first message
as follows:
where
and
and
are random values generated by
.
After receiving
, the responder chooses a random value
and computes
and
. Then, the responder replies
with
:
The responder recovers
and computes
. Then, the responder computes
and sends the following message
to
:
At this step, needs to send the responder with , which should be equivalent with so that it can pass the verification at the beginning of the next step.
In step 4, in order to compute a valid , has to calculate K equals . However, without any of and , has no choice but to guess such a . The probability of guessing a valid is .
Alternatively, in the first piece of message , the adversary can send a intercepted in previous protocol runs instead of . In this case, K computed by the responder in step 3 equals , and . It is still infeasible for to compute the K since and are unknown to .
From the above analysis, now we can draw the conclusion that the probability for successfully impersonating the initiator and establishing a master key with the responder is , which is a minor value in a life circle of a normal node in WBAN applications. ☐
Proposition 2. Suppose the initiator and the responder have shared a password secretly, and an attacker is not able to impersonate the responder to establish the master key with the initiator.
Proof. Assume
is an attacker who intends to impersonate the responder and establish
with the initiator.
attacks the protocol as follows:
The is checked to be valid only if it equals . In order to generate a valid , can compute the CMAC output by inputting or guess the 64-bit result. To compute the CMAC output, has to calculate K that equals the K calculated by the initiator through . However, since is unknown to , it is infeasible for to acquire a valid K. Therefore, the adversary can only guess a valid with a successful probability at . Otherwise, the protocol will stop at the beginning of step 4 and the attack will fail.
☐
From Propositions 1 and 2, we can see impersonation attacks fail no matter if the attacker impersonates the initiator or the responder.
5.2. Man-in-the-Middle Attack
Proposition 3. Suppose the initiator and the responder have successfully shared a password , a Man-in-the-Middle attacker is not able to complete the improved protocol between the initiator and the responder without being detected.
Proof. Suppose
A is a Man-in-the-Middle attacker between the initiator and the responder.
A participants the improve protocol as follows:
The initiator sends
A with
which is the same with
in the improved protocol:
A replaces
with
and sends it to the responder:
The responder replies
A with
which is the same with
in the improved protocol:
A sends
to the initiator:
At this step, the Diffie–Hellman key between A and the initiator and between A and the responder are determined. Specifically, the initiator calculates , and the responder calculates .
The responder computes
and sends
A with
:
A should send the initiator with
where
The initiator verifies .
A should send the responder with
where
The responder verifies
Since A does not have any of , , , it is infeasible for A to compute and , and therefore A can not compute correct in step 3 and in step 4. Without valid and , the initiator will stop the protocol at the beginning of step 4, and the responder will stop at the beginning of step 5, which means A fails to establish an either with the initiator or the responder. ☐
5.3. Off-Line Dictionary Attack
Proposition 4. Suppose the initiator and the responder have successfully shared a password , and a passive eavesdropper who records one or more sessions of the improved protocol cannot eliminate a significant number of possible passwords.
Proof. In the improved protocol, values that are sent in the clear include I, R, , , , , , , and . In order to carry out an off-line dictionary attack, the adversary needs to acquire information that can help him to check possible passwords from a dictionary. Among all of these values sent in the clear, has a relationship only with through the equation . is kept secretly in the protocol, and , where is a random integer. Therefore, is a random value and is unknown to the adversary. The equation of and the value of do not give more information of to the attacker. Based on this acquired knowledge, the attacker is unable to eliminate possible passwords. ☐
According to Proposition 4, an off-line dictionary attack to the improved protocol is infeasible.
5.4. Forward Secrecy
Proposition 5. Suppose the initiator and the responder have successfully shared a password , and compromise of the long-term secret keys of a set of principals does not compromise the s established in previous runs of the improved protocol involving those principals.
Proof. The principals of this protocols are the initiator and the responder, and the long-term secret keys of these principals are the private keys and , the password and the public key that is masked during transmission. Assume the adversary A compromises these long-term secrets of the initiator and the responder, and then (s)he has , , and . In order to calculate an established in a previous run, A needs to compute from the formula where K is a necessary input in that run. Note that A can not use these values to run the protocol with the principals, since, in this case, the does not belong to a previous run but is established in the current run. Therefore, A has to compute K through , or . All three of the formulas require at least one of and . However, and are random values chosen by the initiator and the responder, respectively, in each run of the protocol, which means that these values change in every protocol run and are kept unknown to A. Without any of and , A fails to compromise the , although (s)he compromises all the long-term secret keys and values. ☐
From Proposition 5, we can see the improved protocol provides forward secrecy.
6. Performance
In order to observe the performance of the improved protocol, we evaluate the computation and communication cost theoretically. In addition, we also test the performance through a set of experiments.
6.1. Evaluation
The overall burden of the protocol contains three parts: communication cost, computation cost on the node and computation cost on the hub. For the communication cost, we count all of the pieces of messages transmitted between the node and the hub within a run of the protocol. In order to evaluate the computation cost, we count the number of cryptographic algorithm CMAC and scalar multiplication of an element from the ecliptic curve by an integer, since other operations such as addition and subtraction require minor computation cost.
Denote the cost of transmitting a piece of message by
, the cost of executing one CMAC algorithm by
, and the cost of executing the operation of scalar multiplication one time by
, and we compare the evaluated cost of the improved protocol with the modified protocol and the standard protocol in
Table 2.
From
Table 2, we can see that the improved protocol reduces computation cost on the node, while overall computation and communication cost does not increase. One time-consuming operation
is done by the hub on behalf of the node. Since the hub is more powerful compared with the node, the improved protocol is more affordable for WBAN applications.
6.2. Experiments
The improved protocol contains the algorithm of CMAC and ECC key-generation (generating a private key and using scalar multiplication to compute the public key). We test the runtime of these algorithms on the node through a set of experiments. In the experiments, we use Arduino Uno as the node, SHA-256 as the CMAC algorithms and the ATECC108A crypto chip from Atmel to execute the ECC key-generation. The elliptic curve is curve p-256 in Federal Information Processing Standards (FIPS) Pub 186-3. Description of the node is listed in
Table 3, and the results are summarized in
Table 4.
From
Table 4, we can see that the run-time of executing these algorithms is affordable for the node, which means that the improved protocol is suitable for WBAN applications.
7. Use Case
As described before, our improved protocol reduced the computational burden on one side of communication. This is a significant strength for some applications in wireless sensor networks. Here, we describe a smart lock system that uses our improved protocol to generate a master key. The specific system and the usage of the improved protocol are described as follows.
7.1. Smart Lock System
As is shown in
Figure 2, the smart lock system consists of a lock which is a physical host embedded with a computational device, and a phone which has installed a smart lock application. The aim of this system is using this phone application to securely lock or unlock the lock. Obviously, the computationally limited lock is the initiator and the relatively powerful phone is the responder. The smart lock system includes the following three phases, and our protocol is involved in the first phase.
Master Key Generation. The lock and the phone secretly input the short password and then execute our improved protocol. After this stage, a relatively long master key is shared by the lock and the phone.
Session Key Generation. With the master key, the lock and the phone execute the session key generation protocol (such protocols are available in literature) to generate their session key for this round of communication.
Secure Communication. The newly generated session key is used for this round of communication between the phone and the lock. We describe the steps as:
- (1)
The phone computes
and sends the request (
) with the
to the lock. Here,
P and
L denote the identity of the phone and the lock, and
denotes the value of counter.
- (2)
The lock verifies the . If the verification succeeds, the lock executes the request to lock or unlock; otherwise, it does not execute the request or responds with a failure message.
7.2. Analysis
The smart lock system is secure since the session key is kept secretly by the two participants. An adversary can not request the system to lock or unlock because they can not compute the correct without the session key. Therefore, the security of the session key is significant for the security of the whole system. Our improved protocol provides secure generation for the master key, which, in turn, guarantees the security of the session key.
Additionally, the device embedded in the lock is a less powerful device compared with a normal cell phone. Our password-based authenticated association protocol in the first phase reduces the computational cost of the lock, which makes the smart lock system more practicable.
8. Related Works
8.1. Comparison
In
Section 6.1, we compared the cost of the improved protocol with other related protocols in
Table 2. The comparison in terms of security of these protocols is listed in
Table 5, where
√ means being secure under the corresponding attacks or providing the corresponding security feature, while × means being insecure or not providing.
8.2. Password-Based Two-Party Key Exchange
Several password-based authenticated key exchange protocols have been proposed. In this subsection, we compare our improved protocol with three kinds of two-party key exchange protocols that are based on passwords.
8.2.1. Encrypted Key Exchange Using Diffie–Hellman
Diffie–Hellman-based Encrypted Key Exchange (EKE) protocols transmit the public keys encrypted using the password. The original protocol is proposed by Bellovin and Merritt in [
17]. Variants and extensions of this protocol have been proposed. Such protocols are proved to be secure in the random-oracle model. However, in practice, attacks against these protocols exist since the two parties are not able to verify the integrity of the received messages. If an attacker maliciously modifies the message, the two participants will generate different keys while they are not aware.
The IEEE Std password authenticate association protocol and our improved protocol are developed from these kinds of protocols. As in the IEEE std protocol and our improved protocol Hash-based Message Authenticated Code (HMAC) is used for verifying the integrity of messages transmitted between the two parties, the above attacks against the original Diffie–Hellman-based EKE protocols are eliminated.
8.2.2. RSA-Based Protocols
Rivest-Shamir-Adleman (RSA)-Based Protocols use the RSA algorithm as the basis of the password authentication key exchange scheme. In [
18], MacKenzie proposed a variant of RSA based open key exchange protocol called SNAPI (Secure Network Authentication with Password Information). Verification for the integrity of transmitted messages is involved in this protocol. However, this protocol is not suitable for wireless sensor networks since sensors are usually not powerful enough to run the RSA algorithm.
8.2.3. Protocols Using a Server Public Key
Some password-based authenticated key exchange protocols use a server public key in addition to the pre-shared password. Such protocols include the Gong-Lomas-Needham-Saltzer (GLNS) compact protocol proposed by Gong et al. in [
19], Gong’s Optimal GLNS nonce-based protocol in [
20], Kwon–Song Protocol in [
21] and Halevi–Krawczyk Protocol in [
22]. However, all four of the protocols used public key encryption, which is too high in computational cost for sensor devices. Moreover, the former two protocols need the participation of a server.
9. Conclusions
In low-power, low-complexity wireless sensor network applications such as WBANs, the communications security requirements mainly include authentication between participants, as well as confidentiality and integrity of transmitted messages. Mechanisms that aim to satisfy these requirements usually need a secret key to be held by participants. Therefore, key establishment and management are significant for security services in communications networks. The password authenticated association protocol is a scheme for the participants to generate a master key from a pre-shared password.
Considering the asymmetric power of the two participants in WBANs, we propose an improved password authenticated association protocol that reduces the computational cost on the less powerful participant of communication. The improved protocol can resist both impersonation attacks and Man-in-the-Middle attacks. A master key between the node and the hub will be established securely and efficiently through this protocol, and, afterwards, this is used for pairwise temporal key (PTK) creation, and the PTK is the key used in encryption and decryption process to provide authentication, confidentiality and integrity for communication.
The improved protocol requires one scalar multiplication and two HMAC computations on the nodes (i.e., the initiator). Since the computational costs of these algorithms are acceptable to devices with limited power in WBANs, the improved protocol is suitable for applications in WBANs.
Acknowledgments
This work has been supported by the Xi’an Jiaotong-Liverpool University research development fund projects RDF140243 and RDF150246, as well as by the Suzhou Science and Technology Development Plan under grant SYG201516, and Jiangsu Province National Science Foundation under grant BK20150376.
Author Contributions
Jie Zhang and Xin Huang attacked the standard protocol, and conceived and designed the improved protocol; Paul Craig and Alan Marshall analyzed the result; Jie Zhang wrote the paper; and Paul Craig and Alan Marshall modified the English language of the manuscript; Dawei Liu and Xin Huang contributed analysis tools.
Conflicts of Interest
The authors declare no conflict of interest.
Abbreviations
The following abbreviations are used in this manuscript:
| WBAN | Multidisciplinary Digital Publishing Institute |
| PTK | Pairwise Temporal Key |
| MAC | Message Authentication Code |
| EKE | Encrypted Key Exchange |
| SNAPI | Secure Network Authentication with Password Information |
| CMAC | Cypher-based message authentication code |
| SRAM | Static Random Access Memory |
| EEPROM | Electrically Erasable Programmable Read-Only Memory |
| SHA | Secure Hash Algorithm |
References
- Huang, X.; Chen, B.; Markham, A.; Wang, Q.; Yan, Z.; Roscoe, A.W. Human interactive secure key and identity exchange protocols in body sensor networks. Inf. Sec. 2013, 7, 30–38. [Google Scholar] [CrossRef]
- Huang, X.; Wang, Q.; Chen, B.; Markham, A.; Jäntti, R.; Roscoe, A.W.F. Body sensor network key distribution using human interactive channels. In Proceedings of the 4th International Symposium on Applied Sciences in Biomedical and Communication Technologies, Barcelona, Spain, 26–29 October 2011.
- Ullah, S.; Higgins, H.; Braem, B.; Latre, B.; Blondia, C.; Moerman, I.; Saleem, S.; Rahman, Z.; Kwak, K.S. A comprehensive survey of wireless body area networks. J. Med. Syst. 2012, 36, 1065–1094. [Google Scholar] [CrossRef] [PubMed]
- Movassaghi, S.; Abolhasan, M.; Lipman, J.; Smith, D.; Jamalipour, A. Wireless body area networks: A survey. IEEE Commun. Surv. Tutor. 2014, 16, 1658–1686. [Google Scholar] [CrossRef]
- Abdmeziem, M.R.; Tandjaoui, D. An end-to-end secure key management protocol for e-health applications. Comput. Electr. Eng. 2015, 44, 184–197. [Google Scholar] [CrossRef]
- Jovanov, E. Wireless technology and system integration in body area networks for m-health applications. In Proceedings of the 27th Annual International Conference of the Engineering in Medicine and Biology Society, Shanghai, China, 1–4 September 2005; pp. 7158–7160.
- IEEE Standards. IEEE Standard for Local and Metropolitan Area Networks-Part 15.6: Wireless Body Area Networks. 2012. Available online: http://standards.ieee.org/about/get/802/802.15.html (accessed on 29 February 2012).
- Boyd, C.; Mathuria, A. Protocols for Authentication and Key Establishment; Springer Science & Business Media: Berlin, Germany, 2013. [Google Scholar]
- Abdalla, M. Password-based authenticated key exchange: An overview. In Provable Security; Springer: Berlin, Germany, 2014; pp. 1–9. [Google Scholar]
- Huang, X.; Liu, D.; Zhang, J. An improved IEEE 802.15.6 password authenticated association protocol. In Proceedings of the 4th IEEE/CIC International Conference on Communications in China (ICCC 2015), Shenzhen, China, 2–4 November 2015.
- Toorani, M. Security analysis of the IEEE 802.15.6 standard. Int. J. Commun. Syst. 2016. [Google Scholar] [CrossRef]
- Toorani, M. On vulnerabilities of the security association in the IEEE 802.15. 6 standard. In Financial Cryptography and Data Security; Springer: Berlin/Heidelberg, Germany, 2015; pp. 245–260. [Google Scholar]
- Diffie, W.; Hellman, M.E. New directions in cryptography. IEEE Trans. Inf. Theory 1976, 22, 644–654. [Google Scholar] [CrossRef]
- Koblitz, N. Elliptic curve cryptosystems. Math. Comput. 1987, 48, 203–209. [Google Scholar] [CrossRef]
- Miller, V. Use of elliptic curves in cryptography. In Advances in Cryptology, CRYPTO85 Proceedings; Springer: Berlin/Heidelberg, Germany, 1986; pp. 417–426. [Google Scholar]
- Barker, E.; Chen, L.; Roginsky, A.; Smid, M. Recommendation for Pair-Wise Key Establishment Schemes Using Discrete Logarithm Cryptography; Technical Report; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2012. [Google Scholar]
- Bellovin, S.M.; Merritt, M. Encrypted key exchange: Password-based protocols secure against dictionary attacks. In Proceedings of the 1992 IEEE Computer Society Symposium on Research in Security and Privacy, Oakland, CA, USA, 4–6 May 1992; pp. 72–84.
- MacKenzie, P.; Patel, S.; Swaminathan, R. Password authenticated key exchange based on RSA. In Advances in Cryptology-Asiacrypt 2000; Springer: Berlin/Heidelberg, Germany, 2000; pp. 599–613. [Google Scholar]
- Gong, L.; Lomas, M.; Needham, R.M.; Saltzer, J.H. Protecting poorly chosen secrets from guessing attacks. IEEE J. Sel. Areas Commun. 1993, 11, 648–656. [Google Scholar] [CrossRef]
- Gong, L. Optimal authentication protocols resistant to password guessing attacks. In Proceedings of the 8th IEEE Computer Security Foundations Workshop, County Kerry, Ireland, 13–15 June 1995; pp. 24–29.
- Kwon, T.; Song, J. Efficient and secure password-based authentication protocols against guessing attacks. Comput. Commun. 1998, 21, 853–861. [Google Scholar] [CrossRef]
- Halevi, S.; Krawczyk, H. Public-key cryptography and password protocols. ACM Trans. Inf. Syst. Sec. (TISSEC) 1999, 2, 230–268. [Google Scholar] [CrossRef]
© 2016 by the authors; licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC-BY) license (http://creativecommons.org/licenses/by/4.0/).