Abstract
The integrity protection of digital signals is an important task in modern applications. We propose DIPS (Data Integrity Protection of Signals), a fragile watermarking algorithm aiming to protect the integrity of sampled signals like images composed of pixels or sampled audio signals that can be divided into block units. The present paper starts with two works that propose fragile watermarking algorithms yielding high-quality watermarked objects, identifies their security vulnerabilities, and finally defines a method that embeds a compressed Message Authentication Code of each block into the LSBs of the block samples. As it modifies 2 bits per block at most, the introduced distortion is extremely low, thus resulting in a very high objective quality (). Experimental results confirming this characteristic are reported on real sampled signals such as speech, images, and ECG signals.
1. Introduction
Digital watermarking is a branch of the data-hiding field that refers to a collection of methods, techniques, and algorithms with the purpose to embed data, i.e., the watermark, into digital objects to satisfy specific application requirements like copyright protection, origin tracking, integrity protection, and tamper detection [1].
Watermarking takes place in two distinct phases. The embedding phase, performed once, stores the watermark into the cover (i.e., original) object (using a secret key for the security of the whole method) and the extraction/verification phase (run every time the application is required to check a desired property of the object such as integrity or ownership) that extracts the watermark and controls its characteristics (like correlation or areas of difference from the expected).
Watermark embedding obviously requires the alteration of the digital object. The watermark data may be stored directly in the representation domain of the digital object like pixels or audio samples; in that case, it is said to be stored in the spatial or time domains. Nonetheless, before embedding the object may be transformed into another domain, like the Fourier transform domain or the singular value decomposition domain, where the watermark is stored just before inverse transforming the data to obtain the original domain; in this case, the watermarking algorithm is said to operate in the transformed domain.
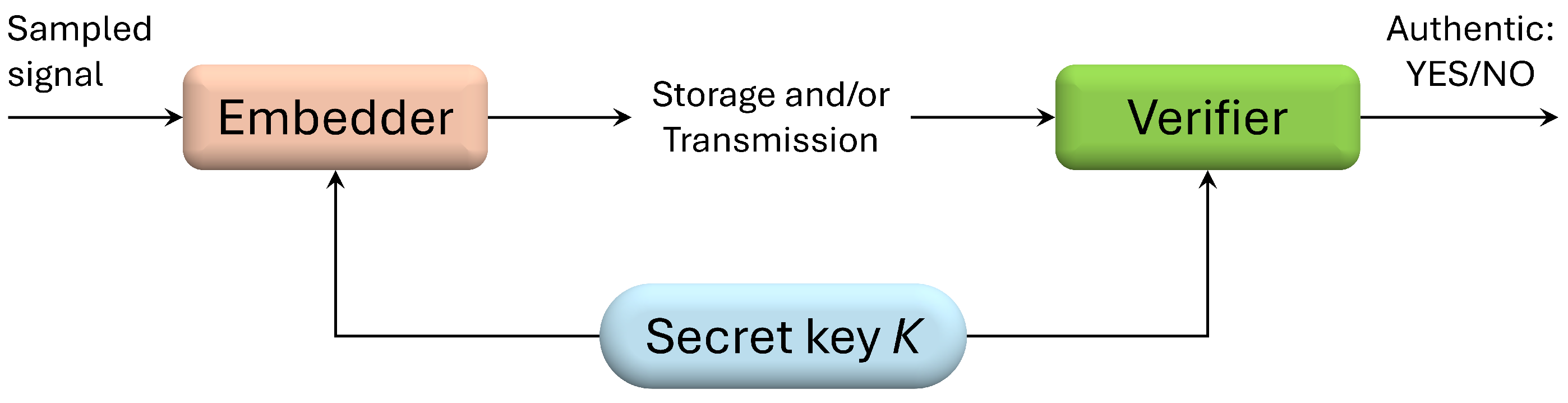
The properties of a watermark depend on its field of application. For example, copyright protection requires that the watermark be robust, that is, it must be able to resist intentional attacks aimed at its removal. On the contrary, tamper detection uses fragile watermarks that are (locally) modified at any minimal alteration of the digital object: the portions where the recovered and expected watermarks differ reveal changes (intentional or not) undergone by the digital object. Thus, in the context of fragile watermarking, the embedded fragile watermark is used as a mean to verify the integrity of the digital object, identifying (i.e., localizing) altered parts of the object if any tampering took place. The tampering attack may take place during the storage or transmission phases of the watermarked object (see Figure 1).
Figure 1.
A high-level schema of the embedding and verification procedures.
Given that the watermark embedding operation alters the cover object producing a watermarked object, watermarking algorithms may be reversible or non-reversible depending on the possibility of recovering the digital object from the watermarked one during the extraction/verification phase. In some application contexts, the cover object is available during the verification step, while in others, the watermarked object is the only data available. In the first case, the algorithm may be referred to as non-blind, whereas in the second case, the algorithm is said to be blind.
Digital steganography is another branch of data hiding, where the objective is not only to embed and hide data into a digital entity but also conceal this embedding in such a way that it should not be possible to (mathematically) prove that some data has been stored. Steganography has partially different constraints and other fields of application, and the algorithm proposed in this paper does not deal with them. Nonetheless, embedding in the LSBs of signal samples is one of the techniques used due to the low amount of noise introduced and the consequent reduction in detectability (see, for example, [2,3]).
Digital watermarking algorithms have been developed for various types of digital object, such as images [4,5], videos [6], audio [7,8], neural networks [9,10], and 3D models [11,12]. In this paper, we build upon the algorithm in [4], later improved in [13], developed for the integrity protection of digital images and provide a solution to a security issue we discovered. Specifically, we demonstrate a possible attack on the method and present a solution that introduces minimal error, as two bits per block at most are changed. Finally, we apply the improved algorithm to the fragile watermarking of audio, images, and ECG signals.
The paper is structured as follows: the next section discusses related work, and the proposed algorithm is presented in Section 3. Section 4 reports the experimental results of applying the method to a set of audio, image, and electrocardiogram files. Finally, Section 5 discusses the relevant aspects of the work, and conclusions are drawn in Section 6. Section 7 summarizes the symbols and variables used in this paper for readability, and Appendix A presents a formal proof that only two bit changes are needed to insert the watermark.
2. Related Work
Our proposed improvement stores the fragile watermark in the LSBs of a signal’s samples. This signal could be, for example, an image, a sound, or a physical quantity sampled in time. Many works that embed data in the LSBs of samples have been published (see, for example, [8,14,15]). As already said, the developed algorithm works on sampled data and corrects a security flaw present in previously published papers [4,13]. Given that this problem is more evident on samples having a large bit depth, we implemented, tested, and compared our proposal mainly on audio files. In particular, we worked on non-compressed audio files (wave format) and evaluated the characteristics with respect to the works [8,16,17,18].
In [8], a fragile watermarking algorithm for audio files based on hashes is proposed. The file is divided into 256 contiguous, non-overlapping blocks, and for each block (not considering the LSBs), a (synchronization) hash is computed, compressed to R bits, and stored into the block’s LSBs. After that, a main hash (SHA-256) with a length of 256 bits is computed on the whole file (excluding the LSBs) and is stored in the LSBs at one bit per block; in addition, an area of LSBs is left free to save a third hash of all the LSBs (excluding those in the area itself). In this way, all the parts of the file are hashed. We will make an extensive comparison of the quality of the watermarked files produced by this method and our algorithm.
The method introduced in [16] operates by using Quantization Index Modulation to embed a fragile watermark (a bit string obtained from a secret text in UTF-8 format permuted and transformed with an Orthogonal Variable Spreading Factor code) into the approximation coefficients of the Discrete Wavelet Transform of the host signal. The method shows the maximum sensitivity to tampering with highest quality of 69.7 dB and typical of 50.86 dB on the tested audio files. Ref. [18] proposes an algorithm for the tamper detection of audio files containing speech data. The file is divided in frames, each one containing a spoken word: a watermark depending on the signal and the frame position is generated, encrypted and stored in each frame at sampling points chosen with a key. The bits are then embedded into the singular values of the SVD (Singular Value Decomposition) computed on the detail coefficients of the Discrete Wavelet Transform. The paper reports experimental results at an average of 61.15 dB.
Ref. [17] presents a method that can be used for the robust and fragile blind watermarking of audio files. The fragile watermark is saved into the second- and third-level detail sub-bands of the Lifting Wavelet Transform (LWT), whilst the robust watermark is embedded into the LWT third-level approximation coefficients. Also, the method saves a compressed version of the signal along with the watermark for recovering purposes in case of tampering. Due to the large amount of information saved for recovering objectives, the is 35.75 dB for fragile watermarked files and even lower ( dB) when the robust watermark is added.
The above mentioned papers will be used to perform some comparisons with our proposal, but the objective of the present paper is the improvement in security of the fragile watermarking algorithms proposed in [4,13]. Therefore, we will briefly present these two works in the following.
In [4], Lin et al. present a fragile watermarking algorithm for images. The method uses keys and authentication data to produce a watermark bit string to protect the integrity of an image. The image is divided in blocks of pixels , and the algorithm stores watermark bits by altering in each block at maximum one pixel by ±1 using the following embedding function:
If the value to be embedded is u, then a pixel is incremented or decremented by 1 to change the sum in Equation (1) by . As reported in [4], the false-negative probability of the method is for every block.
The problem with this algorithm is that if a pixel already has the maximum (respectively minimum) value and if an increment (respectively decrement) of 1 is required, the operation cannot be performed because it would result in an overflow or, if modular arithmetic is used, the introduced error produces a visible alteration (and a reduced Peak Signal-to-Noise Ratio ()).
This problem is solved in [13]. It focuses on watermark embedding and covers all possible combinations of pixel values. This includes situations where a pixel with a value of 0 must be decremented, or a pixel with the maximum value must be incremented. The idea is to eventually alter more than one pixel: if the increment (respectively decrement) is not possible, then a decrement (respectively increment) is performed on the selected pixel and the embedding process is repeated. It is also shown that this iteration comes to an end and the watermark is finally embedded. In this case, it is recognized that the object quality is slightly reduced due to the fact that more than one pixel modification of ±1 is performed.
Nonetheless, due to the use of the modulo operation, the formula in Equation (1) cannot detect modifications of magnitude to one or more pixels s: in fact, for every ,
When block sizes are small relative to the pixel range , , certain pixel modifications may remain undetected. While this is negligible for smaller bit depths, applying the method to high-resolution images or 16-bit audio files necessitates larger blocks to prevent such attacks. Consequently, this creates a trade-off where the required block size may be too large to allow for precise localization of tampered samples.
This issue is also due to the way in which the watermark string is computed in the mentioned papers: even though the string is derived from a secret key and it is made dependent on the object content, but it is not enough to overcome the mentioned problem. In this paper, we propose to make the watermark completely dependent on the content of the block in which it is embedded and, in doing so, it does not suffer the attack previously discussed.
Moreover, in order to prove that Data Integrity Protection of Signals (DIPS) solves the aforementioned problem, we will present experimental results on audio files whose samples are represented with a large bit depth (usually 16 bits). The method works on any kind of sampled data and this will be shown by applying the proposed solution to images and ECG signals.
3. The DIPS Algorithm
In order to overcome security issues, DIPS makes use of Message Authentication Codes (MACs). A Message Authentication Code (MAC) is a computer security primitive used to verify the integrity and authenticity of digital data. Essentially, a MAC M is a short digest, depending on a secret symmetric (i.e., shared among authorized entities) key K, computed on a bit string representing the digital object O to protect: M is attached to O and can be used by those having access to K to check the integrity of O by computing its MAC and checking if . Only the entities who possess the key K can generate the correct MAC and/or verify it. Cryptographic properties guarantee that attackers, not knowing the secret key K, cannot alter O and generate a new valid MAC. Being based on a symmetric secret key, a MAC cannot guarantee the non-repudiation property, which is the ability to prove to a third party the origin of an object from an entity. In that case, digital signatures are needed [19,20]. A MAC can be computed with many techniques, with the most widely used being through a cryptographic hash function, like HMAC [21] and KMAC [22], or with a block cipher, like CMAC [23]. For an introduction and insights on MACs and digital signatures, see [24].
In particular, the basic idea is to store in a block of samples a fragile watermark made of a Message Authentication Code (MAC) of the block itself. To minimize the noise, or error, introduced by this embedding, the MAC will be stored into the Least Significant Bits (LSBs) of the samples. The embedding function will be the one expressed by Equation (1): given that the MAC will be computed on the most significant part of the samples (i.e., the block samples without the LSBs), the only part that can be modified for watermark embedding are the LSBs. This changes the possibility of incrementing or decrementing a sample value: the only permissible changes will be to 0 with a LSB valued at 1, which will decrement the modulo sum in Equation (1) by i (for the i-th sample), or to 1 with a LSB valued at 0 incrementing the modulo sum in Equation (1) by i.
DIPS performs the following steps:
- Choose a secret symmetric key K to be used for the computation of the MAC.
- For every block, compute the MAC of its samples (without the LSBs) using the key K and the block position (in order to avoid copy and paste attacks) as seeds. If the MAC used has length bits, compress it to obtain bits: KMAC may produce a MAC of any desired length, whereas HMAC, based on SHA-256, requires a reduction from 256 to bits. This can be done by splitting the 256 bits into blocks of bits and XORing them (the last block being ) in length. Let m denote the resulting MAC: being a string of bits, it can be interpreted as an integer value .
- Compute the block value v using Equation (1) and evaluate the difference , then modify the LSBs of some samples to make , i.e. . To this end, if , then changing it to 1 will increase v by i (modulo ); on the contrary, changing from 1 to 0 will decrease v by i or increase it by (which is also modulo in this case).
The algorithm to find the correct and minimal (in terms of number of LSBs) modification was developed and implemented in MATLAB R2023b (more details on the pseudocode presented in Algorithm 1 may be provided upon request to the corresponding author.). The developed procedure has a recursive component and is capable of changing an increasing number of LSBs from 1 to a pre-defined maximum; we provide a high-level description of this in Algorithm 1. The implemented procedure was used to watermark a large number of blocks (see Section 4), and we empirically verified that the maximum number of changed LSBs is 2. We provide a formal proof of this property in Appendix A.
Algorithm 1 embeds a fragile watermark in a block of samples. Firstly, the modulo sum v in Equation (1) and a -bits MAC of the samples (without the LSBs) are computed. If these two values differ, then some of the LSBs are modified to increase the sum (1) by the amount so that the MAC is stored; this is performed with a recursive function as can be seen in the second part of Algorithm 1. Note that the watermark embedding is based on the formula in Equation (1) with a slight variation as in Equation (3): it is applied to the LSBs only, following this consideration. A flip (i.e., a NOT operation) of an LSB modifies the sum by an amount corresponding to the weight (from 1 to ) assigned to that position, and the sample is not involved in the embedding of the difference between the present sum value and the desired one. Given that the MAC depends on the sample values amended from the LSBs, the embedding function can be applied to the LSBs only (see Equation (3)).
The array contains in position i the index of the sample (from 1 to ) whose LSB, if modified, will alter the sum (3) by i. Note that entries will not refer to any sample; thus, not all possible differences can be compensated by altering only one LSB.
| Algorithm 1 Fragile watermarking of a block B of size samples. Input: B and its position P, MAC key K, . Output: watermarked block B |
function embedWatermark()
function findChange()
|
The recursive function builds a list of LSB modifications (i.e., a list of LSBs to which apply the NOT operator) to add the required difference to the sum in Equation (3). If the modification can be obtained by changing one LSB not already used, it is added to the list of required changes (the complexity of this operation is ); otherwise, for all the possible changes not already used, the change is added to the list of changes, and the function is recursively called to find the necessary changes for the remaining part . In this case, the complexity becomes where N is the block length. Thus, if the function is recursively called C times, then the complexity is . If the function returns a non-empty list, then a set of LSBs to obtain the value has been found. Otherwise, the change is discarded and the next change is tested.
According to the proof in Appendix A, confirmed by the set of experiments we performed on a large number of blocks of various sizes (see Section 4), we found that , the maximum allowed recursion depth, may be set to 2.
A change to any bit of the block (LSBs included) will be detected as a modification to the watermark computed with Equation (3):
A consideration is required at this point: as with the original paper [4], this algorithm embeds a watermark of bits. Therefore, a modification to the block could result in a false negative (i.e., undetected tampered block) with probability .
4. Experimental Results
In this section, we report the test results of DIPS applied to a set of audio files in wave format, PNG color images, and raw ECG signals. Moreover, we provide a performance comparison with a recently published fragile watermarking algorithm for audio signals [8] and up-to-date quality results on images. The measures used in these evaluations and comparisons are the and .
The and values resulting from the watermarked object are computed with the well-known formulas:
and
where is the average power of the signal (i.e., the average of the squared samples), is the maximum possible excursion of the samples, with being d the bit depth, and is the mean squared error between the original and the watermarked object.
Assuming that a maximum of 2 LSBs are changed in each block (this is based on the proof provided in the Appendix A, confirmed by our set of experiments, that any difference between the MAC value and the sum in Equation (3) can be compensated with 0, 1, or 2 LSB flips), then the , so it is possible to compute the minimum theoretic , according to the following equation:
Table 1 reports minimum values for two different bit depths and block sizes , with n in the range [6, 16].

Table 1.
Minimum for different block sizes and sample’s bit depth d, computed considering a maximum of 2 LSB flips.
We evaluated DIPS performances on a set of 100 audio files available from [25]: the wave file sizes vary between 10 MB and 20 MB and incorporate recorded mono audio of time duration between 110 s and 220 s sampled at a frequency of 44,100 Hz with 16 bits per sample. These audio files contain voice recordings of males and females reading a text. The test results are reported in Table 2: for every block size analyzed, the block time length is derived and the average (with standard deviation) and minimal and values obtained from the tested files are reported.

Table 2.
and performance comparison for different block sizes of audio files (time duration refers to a frequency sampling of 44,100 Hz, the samples bit depth is 16). The mean ± standard deviation and, in parentheses, the minimum value of the statistics over the 100 files are reported for each block size .
As observed, the values are higher than the theoretical minimum (see Equation (6) and Table 1) because not all blocks had a modification of 2 LSBs. In fact, on the tested files, almost all blocks are needed to change the LSBs to store the MAC, and approximately half of the blocks had 1 LSB modified and the other half had 2 LSBs flipped. No blocks required more than 2 changes (also see the proof in Appendix A).
For comparison, we present the results of the DIPS algorithm against those of a recently published work for the fragile watermarking of audio files [8]. In that paper, the authors proposed a procedure based on hashes: the audio file is divided into 256 blocks and each one (LSBs excluded) is protected with a hash of S bits in length stored in the LSBs of the block. Then, a hash of 256 bits computed on the whole file (excluding the LSBs) is distributed over the blocks, at one bit per block, and one more hash (LSB seal hash) is used to authenticate the LSBs of the samples in the file. The paper reports results for , thus, 9 watermark bits are stored in each block, with an exception made for the block also storing the seal hash. The paper shows the performance for some audio files of different time durations sampled at 44,100 Hz. From this, we infer the block size given that [8] splits the file into 256 blocks. Even if a precise comparison is difficult due to unavailability of the audio files they used and the different constraints on the block sizes in DIPS, we collected in Table 3 the and values of some files from [8], given that they have a similar block size to DIPS.

Table 3.
Comparison of objective quality performance between DIPS and [8]. The value in parentheses refers to the of a second file having the same time duration.
To analyze the comparison in Table 3, some considerations are in order. First of all, both algorithms change LSBs only. Secondly, for a fixed number of potentially changeable LSBs, the bigger the block, the smaller the (m.s.) error and thus the larger the . The algorithm in [8] reports results embedding 9 bits per block, thus changing, on average, bits (LSBs) per block. DIPS instead modifies, at most, 2 LSBs to embed 9 bits per block. Consequently, it has higher performance in terms of . On the contrary, performances are comparable: the DIPS algorithm has better results in some cases and less in others, but this fact depends upon the average power of the host signal (which is apparently smaller for the audio files we used) and the slightly different block sizes.
As a last consideration, we report the fact that [8] is able to detect a modification to the audio file (even without block localization), reserving one watermark bit per block to store a file hash. This can also be provided by DIPS with a small modification: just define blocks of samples, compute the MAC of each block, and store it as previously done; then, after having zeroed the LSBs of the ()-th sample of each block, compute a MAC of the whole file and store it one bit per block in the LSBs of the ()-th samples. With this modification, the localization capability is the same and the tamper detection is 100%. By using the same kind of idea, one can embed a digital signature covering the whole watermarked file (excluding only the LSBs devoted to carrying the digital signature itself). This would also add a feature of non-repudiation. It is up to the application to choose which method to use depending on its needs. In any case, the objective of our paper is to present a security improvement with respect to the methods in [4,13], which work on the authentication of single blocks of samples.
Moreover, we report in Table 4 a comparison of the quality of the watermarked files produced by DIPS with the other audio watermarking algorithms previously presented [8,16,17,18]. As it can be observed, the proposed improvement in security also has as side effect of reducing the noise introduced by the fragile watermarking process with respect to other methods developed for audio files. Nonetheless, we remark on the fact that the proposed solution can be applied to other file formats composed of samples and whose application field is resilient to a minimal modification of some samples’ Least Significant Bits. In order to show this, we also report further experiments on images and signals.

Table 4.
Objective quality comparison of the watermarked files produced by DIPS and by [8,16,17,18].
A second set of experiments were performed on 500 color images of pixels [26]. Table 5 reports quality of watermarked images in terms of and . Again, the quality is higher than the minimum values reported in Table 1. For a comparison on this dataset, see [27].

Table 5.
PSNR and SNR performance comparison for different block sizes of color images. The mean ± standard deviation and, in parentheses, the minimum value of the statistics over the 500 files are reported for each block size .
Finally, we tested DIPS on a set of ECG signals taken from [28]. This data is related to a project for the implementation of technologies for 5P-Medicine related to cardiovascular diseases. It includes ECG data acquired from 219 individuals seated for 30 s and standing for 30 s. We only used the data related to the ECG sensors in millivolts (mV). As shown in Table 6, the quality results are better than the minimum reported in Table 1 as well.

Table 6.
PSNR and SNR performance comparison for different block sizes of electrocardiograms. The mean ± standard deviation and, in parentheses, the minimum value of the statistics over the 219 files are reported for each block size .
5. Discussion
In this section, we will argue about some relevant issues that DIPS faces and solves.
- Quality. First of all, to the best of our knowledge, DIPS obtains the best quality in terms of and with respect to any published method when applied to audio signals and images (concerning ECG signals, we did not find any paper that presents watermarking of such signals). Note that any other objective quality measure would result in a value that is definitely better than most other methods, as DIPS only modifies at most 2 LSBs per block. This advantage is even more evident for high bit-depth signals. For instance, the Structural Similarity Index () for the color images in our experiments is always >0.998, with 1 being the best value.
- Attacks. It should be pointed out that we presented a simplified version of DIPS in order to focus the attention on the method itself. This simplified version is prone to a very simple attack: as the value v in Equation (1) can be obtained in several different ways, an attacker might change a proper set of LSBs and obtain the same value v, and such tampering would go undetected. To solve this issue, DIPS actually scrambles the positions of the LSBs according to the secret key when computing the sum. Another solution would be to add a digital signature computed (with a private key) on the watermarked object and insert it into a set of LSBs reserved for it. In order to prevent cut-and-paste attacks, the MAC of a block also contains the position of the block in the watermarked signal.
- Capacity and localization. There is a strong correlation between payload capacity and localization ability of DIPS. The larger the block size, the coarser the localization and the smaller the total payload capacity. Anyway, there is also a limit on the minimum size of a block that depends on how much one wants to compress the MAC: the smaller the MAC, the higher the probability of not detecting a tampered block. In particular, in order to insert a watermark of bits, the block must consists of at least samples. As in the original algorithm [4], with a block size of samples, the probability of missing the detection of a single tampered block is . This can be acceptable in many application contexts because the probability of missing the tampering of at least one of k blocks is , which rapidly decreases for increasing k and n: for example, with a block size of samples , the probability of missing the tampering of at least one of tampered blocks is , i.e., less than .
- Security. The security of the method lies in the secrecy of the symmetric key K used to compute the MACs of the various blocks and, obviously, on the mathematical security of the used MAC algorithms (which is guaranteed for the MAC methods previously cited): anyone who knows the key K can verify the integrity of a file as well as generate the authentication information for that file.
- Data hiding. DIPS can also be used as a data-hiding method to securely transfer secret messages between parties: as the payload capacity can be varied according to the block size, DIPS can carry bits, where is the total number of blocks.
Finally, we remark the security improvement over the algorithms proposed in [4,13] and the applicability of DIPS to any object resilient to minimal LSB modifications and whose structure can be interpreted as a sequence of samples.
6. Conclusions
This paper presented DIPS (Data Integrity Protection of Signals) a security improvement to an integrity protection watermarking algorithm developed for blocks of samples [4,13]. The paper builds upon two previously published works, identifies a security vulnerability present in them, and finally proposes an embedding method that stores a Message Authentication Code of each block into the LSBs of the block itself by modifying at most two LSBs per block. The watermarked objects show a very high quality, improving the state-of-the-art quality as shown for real-world signals. Finally, it is worth mentioning that the proposed solution has a wide range of applications, namely to all files composed of samples, like audio, images, or ECG signals, and whose applications tolerate very small changes to some sample LSBs.
7. Notation and Nomenclature
This section is aimed at summarizing the notation of the variables used throughout the paper and the nomenclature of functions and data structures used in the algorithms.
7.1. Notation
In this paper, we will write the following:
- for the set of positive integers;
- Scalar values with italics uppercase and lowercase letters from the Latin alphabet, eventually with a subscript, e.g., .
7.2. Nomenclature
Table 7 lists the meaning of some terms, variables and functions used throughout the paper.

Table 7.
Meaning of some terms used in the paper.
Author Contributions
All the authors gave the same contribution in all aspects of this paper. All authors have read and agreed to the published version of the manuscript.
Funding
This work has been supported by the Italian Ministero dell’Università e della Ricerca.
Data Availability Statement
Conflicts of Interest
The authors declare no conflicts of interest.
Abbreviations
The following abbreviations are used in this manuscript:
| CMAC | Cipher-based Message Authentication Code |
| DIPS | Data Integrity Protection of Signals |
| DWT | Discrete Wavelet Transform |
| ECG | Electrocardiogram |
| HMAC | Hash-based Message Authentication Code |
| KMAC | KECCAK Message Authentication Code |
| LSB | Least Significant Bit |
| MAC | Message Authentication Code |
| MSE | Mean Squared Error |
| PSNR | Peak Signal-to-Noise Ratio |
| SNR | Signal-to-Noise Ratio |
| SSIM | Structural Similarity Index |
| SVD | Singular Value Decomposition |
Appendix A
In this section, we will prove the following theorem:
Theorem A1.
Let . Given the sum
where are binary weights, and its corresponding modulo value , then any desired value can be obtained from a suitable displacement value d by changing (i.e., flipping, or negating) at maximum two weights , with .
Proof.
To change v into , it is necessary to identify a set of indexes for which negating the corresponding binary weights results in a modification of d, with .
The flipping, or negation, of a binary weight can be obtained with or, equivalently, . Flipping a weight adds a to s, conversely negating a weight subtracts a from s.
To prove the theorem, it must be shown that, from any value d, there exists at least one index a or pair of indices such that flipping the corresponding weight or weights , the required displacement d is obtained through one of the following operations: or .
The proof is given into two parts, A and B, depending on the sign of d.
- Case A: d > 0
In this case, the condition can be achieved with one of the following subcases:
- Addition: If there exist such that and , set and .
- Example (): if , choosing results in the new sum .
- Substitution: If there exist such that with and , set and .
- Example (): if , and the new sum is .
- Subtraction: If there exist such that (that is, ) and , set and .
- Example (): if and removing and gives the new sum .
- Complementary substitution: If there exist such that with and , set and .
- Example (): if and the new sum is .
- Case B: d < 0
In this case, the value is obtained through an analogous logic:
- 5.
- Subtraction: If there exist such that and , set and .
- Example (): if , choosing results in the new sum , or choosing gives the sum .
- 6.
- Substitution: If there exist such that and and , set and .
- Example (): if , and , the new sum is .
- 7.
- Addition: If there exist such that and and , set and .
- Example (): if , and , the new sum is .
- 8.
- Complementary substitution: If there exist such that (equivalently, ) with and , set and .
- Example (): if and the new sum is .
Given that the set I contains all integers from 0 to , then the interval is covered by all possible sums and differences of two distinct elements of I. Thus, for any displacement d, there must exist at least one pair satisfying one of the above subcases, showing that any value m can be obtained by flipping at most two weights. □
References
- Cox, I.; Miller, M.; Bloom, J.; Fridrich, J.; Kalker, T. Digital Watermarking and Steganography, 2nd ed.; Morgan Kaufmann: San Francisco, CA, USA, 2007. [Google Scholar]
- Mielikainen, J. LSB Matching Revisited. IEEE Signal Process. Lett. 2006, 13, 285–287. [Google Scholar] [CrossRef]
- Li, X.; Yang, B.; Cheng, D.; Zeng, T. A Generalization of LSB Matching. IEEE Signal Process. Lett. 2009, 16, 69–72. [Google Scholar] [CrossRef]
- Lin, P.Y.; Lee, J.S.; Chang, C.C. Protecting the Content Integrity of Digital Imagery with Fidelity Preservation. ACM Trans. Multimed. Comput. Commun. Appl. 2011, 7, 1–20. [Google Scholar] [CrossRef]
- Wan, W.; Wang, J.; Zhang, Y.; Li, J.; Yu, H.; Sun, J. A comprehensive survey on robust image watermarking. Neurocomputing 2022, 488, 226–247. [Google Scholar] [CrossRef]
- Asikuzzaman, M.; Pickering, M.R. An Overview of Digital Video Watermarking. IEEE Trans. Circuits Syst. Video Technol. 2017, 28, 2131–2153. [Google Scholar] [CrossRef]
- Arnold, M. Audio watermarking: Features, applications and algorithms. In Proceedings of the 2000 IEEE International Conference on Multimedia and Expo. ICME2000. Proceedings. Latest Advances in the Fast Changing World of Multimedia (Cat. No.00TH8532), New York, NY, USA, 30 July–2 August 2000; Volume 2, pp. 1013–1016. [Google Scholar] [CrossRef]
- AlSabhany, A.A.; Ali, A.H.; Alsaadi, M. A lightweight fragile audio watermarking method using nested hashes for self-authentication and tamper-proof. Multimed. Tools Appl. 2024, 83, 89135–89149. [Google Scholar] [CrossRef]
- Botta, M.; Cavagnino, D.; Esposito, R. NeuNAC: A novel fragile watermarking algorithm for integrity protection of neural networks. Inf. Sci. 2021, 576, 228–241. [Google Scholar] [CrossRef]
- Trias, C.D.S.; Mitrea, M.; Tartaglione, E.; Fiandrotti, A.; Cagnazzo, M.; Chaudhuri, S. A hitchhiker’s guide to white-box neural network watermarking robustness. In Proceedings of the 2023 11th European Workshop on Visual Information Processing (EUVIP), Gjovik, Norway, 11–14 September 2023; pp. 1–6. [Google Scholar]
- Vasc, B.; Raveendran, N.; Vasic, B. Neuro-OSVETA: A Robust Watermarking of 3D Meshes. arXiv 2023, arXiv:2304.10348. [Google Scholar] [CrossRef]
- Wang, Y.; Liu, J.; Yang, Y.; Ma, D.; Liu, R. 3D model watermarking algorithm robust to geometric attacks. IET Image Process. 2017, 11, 822–832. [Google Scholar] [CrossRef]
- Botta, M.; Cavagnino, D.; Pomponiu, V. Protecting the Content Integrity of Digital Imagery with Fidelity Preservation: An Improved Version. ACM Trans. Multimed. Comput. Commun. Appl. 2014, 10, 1–5. [Google Scholar] [CrossRef]
- Kim, C.; Yang, C.N. Self-Embedding Fragile Watermarking Scheme to Detect Image Tampering Using AMBTC and OPAP Approaches. Appl. Sci. 2021, 11, 1146. [Google Scholar] [CrossRef]
- Li, P.; Cao, W.; Yu, T. Improved LSB substitution based semi-blind fragile watermarking for high-accuracy tamper localization. J. Inf. Secur. Appl. 2026, 97, 104330. [Google Scholar] [CrossRef]
- Renza, D.; Ballesteros L., D.M.; Lemus, C. Authenticity verification of audio signals based on fragile watermarking for audio forensics. Expert Syst. Appl. 2018, 91, 211–222. [Google Scholar] [CrossRef]
- Hu, H.T.; Lee, T.T. Hybrid Blind Audio Watermarking for Proprietary Protection, Tamper Proofing, and Self-Recovery. IEEE Access 2019, 7, 180395–180408. [Google Scholar] [CrossRef]
- Zhou, S.; Song, M.; Qian, Q.; Liao, W.; Gong, X. GRACED: A Novel Fragile Watermarking for Speech Based on Endpoint Detection. Secur. Commun. Networks 2022, 2022, 9496748. [Google Scholar] [CrossRef]
- Yang, X.; Wang, W.; Tian, T.; Wang, C. Cryptanalysis and Improvement of a Blockchain-Based Certificateless Signature for IIoT Devices. IEEE Trans. Ind. Inform. 2024, 20, 1884–1894. [Google Scholar] [CrossRef]
- Hauer, E.; Dittmann, J.; Steinebach, M. Digital signatures based on invertible watermarks for video authentication. In Proceedings of the IFIP International Conference on Communications and Multimedia Security; Springer: Berlin/Heidelberg, Germany, 2005; pp. 277–279. [Google Scholar]
- Krawczyk, H.; Bellare, M.; Canetti, R. HMAC: Keyed-Hashing for Message Authentication. In RFC 2104; RFC Editor: Marina del Rey, CA, USA, 1997. [Google Scholar] [CrossRef]
- Kelsey, J.; Chang, S.j.; Perlner, R. SHA-3 Derived Functions: cSHAKE, KMAC, TupleHash, and ParallelHash; Technical Report SP 800-185; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2016. [CrossRef]
- Dworkin, M. Recommendation for Block Cipher Modes of Operation: The CMAC Mode for Authentication; Technical Report SP 800-38B; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2005. [CrossRef]
- Schneier, B. Applied Cryptography, 2nd ed.; Wiley: London, UK, 1996. [Google Scholar]
- Mysore, G.J. Can we Automatically Transform Speech Recorded on Common Consumer Devices in Real-World Environments into Professional Production Quality Speech?—A Dataset, Insights, and Challenges. IEEE Signal Process. Lett. 2015, 22, 1006–1010. [Google Scholar] [CrossRef]
- Olmos, A.; Kingdom, F. Fred Kingdomś Laboratory, McGill Vision Research. Available online: http://tabby.vision.mcgill.ca/ (accessed on 3 March 2026).
- Botta, M.; Cavagnino, D.; Pomponiu, V. A modular framework for color image watermarking. Signal Process. 2016, 119, 102–114. [Google Scholar] [CrossRef]
- Pires, I.; Pinto, R.; Silva, P.; Garcia, N.M. ECG data related to 30-s seated and 30-s standing for 5P-medicine project. In Mendeley Data V2; Elsevier: Amsterdam, The Netherlands, 2022. [Google Scholar] [CrossRef]
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.