Optimal Resource Allocation for 5G Network Slice Requests Based on Combined PROMETHEE-II and SLE Strategy
Abstract
1. Introduction
- A mathematical model is introduced for network slicing that takes operational constraints and security considerations into account when assigning nodes and connecting them.
- The prepared node importance rank array (NIRA) was used to allocate NSR nodes in physical and logical networks, and the SLE approach was utilized to connect the network slice request (NSR) nodes. NIRA preparation takes into account node information such as the node capacity, nearby line bandwidth, degree of the node, and the node’s proximity centrality.
- A PROMETHEE-II multi-criteria approach is suggested for NIRA preparation, and an SLE algorithm is provided for NSR node link creation. The SLE approach generates the shortest path array (SPA) for NSR nodes, guaranteeing that all possible connections are installed and increasing the acceptance percentage.
- The proposed PROMETHEE-SLE approach was evaluated on a small-world network to confirm that the infrastructure is slicing-friendly, and the results were also compared to those obtained from a scale-free physical infrastructure.
2. Related Works
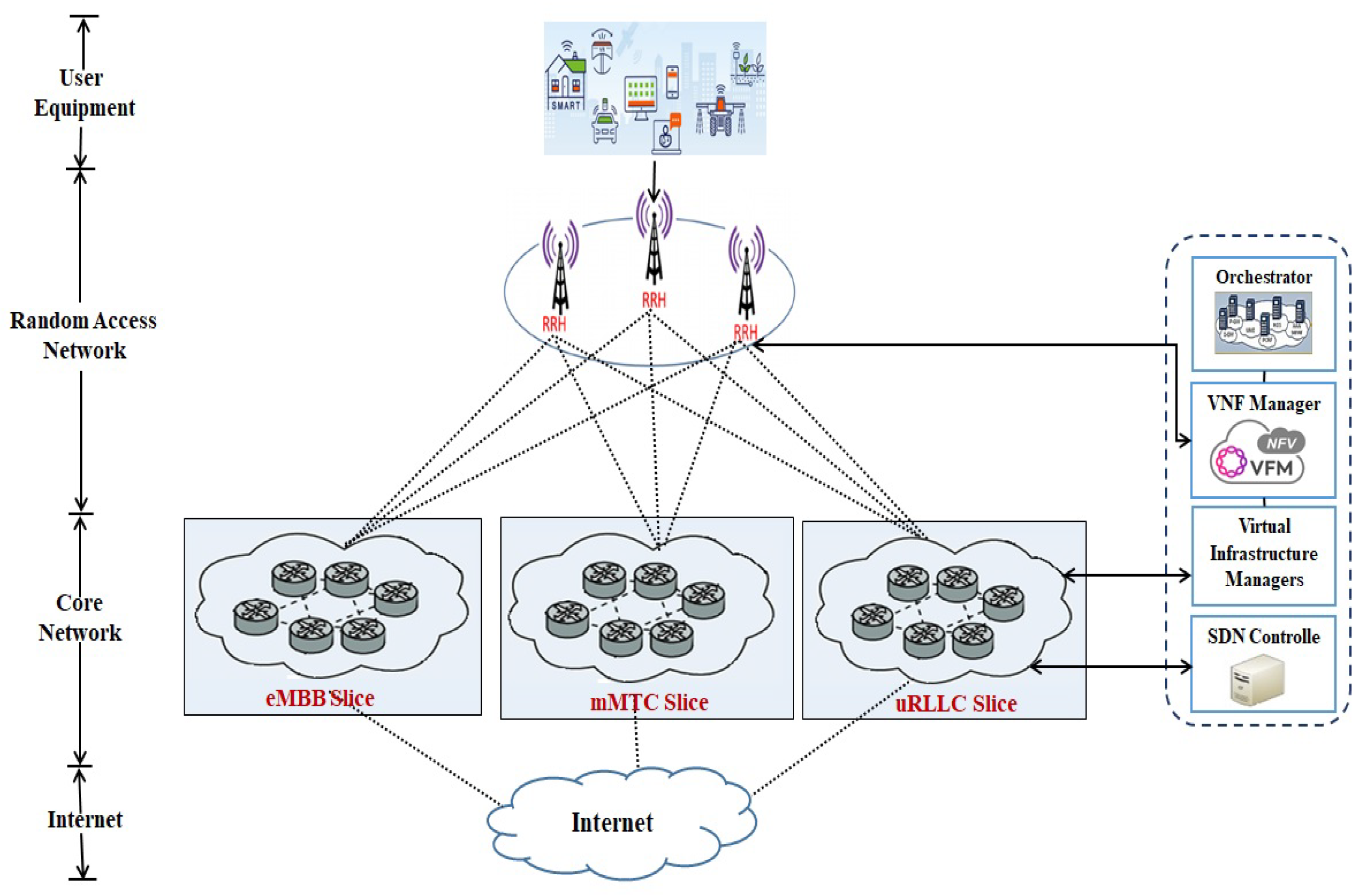
3. Proposed System Model
3.1. Physical Infrastructure Model
3.2. NSR Model
3.3. NSR Deployment Strategy
- NSR Acceptance Ratio (NAR): This metric provides the direct measurement of the adapted network slicing technique on the given physical infrastructure. It is measured by taking the ratio between successfully completed NSRs and unsuccessful NSRs for a given time , which is expressed aswhere and are served and unserved NSR at time t, respectively.
- Resource Efficiency (RE): This metric is measured by calculating the achieved revenue and the investment cost made for providing the physical infrastructure. The revenue can be determined from the CPU capacity of nodes and link bandwidth requested for the NSRs. The investment cost is estimated from the physical infrastructure for the case. The expression for calculating RE is given bywhere is the revenue of NSR at time t, is the utilized physical infrastructure for the NSR at time t, and are the requested numbers of CPU and BW of NSR at time t, and is the length of the shortest path for NSR at time t.
- Problem Formulation: It is understandable that effective network slicing results in the maximum utilization of physical network resources while minimizing slice provisioning costs [27]. As a result, the problem of minimizing the cost of slice provisioning is formulated using the integer linear programming model in conjunction with the necessary constraints as shown below.is a binary variable, where indicates that is served onto , and is otherwise 0. indicates whether the link hosts the request link : the value will be 1 if the link exists; otherwise, it will be 0. Network providers use some additional resources to ensure the security level of nodes. Along with CPU capacity and bandwidth, we also considered the link capacity, delay rate, and jitter resources to improve the allocation of resources and accuracy of node slice creation. Constraint (7) guarantees that each request node is allocated onto the physical node. Constraint (8) ensures that the physical node can only host one node from the same request. The CPU capacity is represented in constraint (9). Constraint (10) ensures the security constraints of each node. Constraint (11) indicates the flow passing through physical nodes. Constraint (12) guarantees that the bandwidth requested by the NSR link should not exceed the available bandwidth in the physical link. The objective of this work was to improve the use of resources and the adoption rate of network slicing. Physical infrastructure restrictions were kept in mind as part of this solution method. Every NSR requirement is guaranteed to be within the stated limits given below:where and are the minimum and maximum number of nodes per NSR, respectively, and are the minimum and maximum number of BW per NSR, respectively, and are the minimum and maximum number of CPUs per node per NSR, respectively, and are the minimum and maximum life time per NSR, respectively, and and are the minimum and maximum security level per node per NSR, respectively. The limitations specified in Equations (12)–(16) correspond to the NSR limits on the node count, bandwidth, CPU capacity, security level, and life duration. Constraint (17) ensures that the NSR’s lifetime does not exceed the overall transmission time interval .
3.4. Factors for Node Importance Calculation
- Node Capacity Factor (NCF): The availability of the number of CPUs on the node is used to determine the capacity of the node. A node with a higher number of CPUs may give service to a greater number of NSRs. As a result, a node with a large number of CPUs should be given a better ranking in the NIRA system. The value of the factor is updated immediately upon the accomplishment of each NSR as below:where is the available CPU capacity of the node of physical infrastructure at time t, and is the requested CPU capacity of the node of the NSR received at time t.
- Node Topology Factor (NTF) and Node Bandwidth Factor (NBF): In both cases, the number of adjacent connections present with the physical node determines the NTF and NBF. The total number of adjacent connections of a node is represented by NTF, whereas the total number of adjacent links bandwidth is represented by NBF. Any node with a greater NTF and NBF is given a higher priority in the NIRA. Each NSR results in an update of the factors. The equations for updating the factors are shown below:where is the total nodes present in the network, is 1 if the node has a connection with node and unserved at time t, and 0 otherwise, is the available bandwidth of the link connecting node i and node j of physical infrastructure at time t, and is the requested bandwidth of the link connecting node i and node j of the NSR at time t.
- Node Closeness Centrality Factor (NCCF): Using the factors NCF, NTF, and NBF, we may learn about the node’s local information. A node’s strength in a network should be measured by how much it can influence the shortest path. A node’s global relevance is determined by its shortest route information, which is provided by NCCF. Therefore, the closer a node is to other nodes, the greater its centrality. Listed below is the NCCF equation at time t.where is the shortest path length between node i and j.
4. Proposed Strategies for NSR Deployment
4.1. PROMETHEE-II Strategy for NIRA Preparation
| Algorithm 1: Node allocation through PROMETHEE-II |
| Input: Output: for each node of do Calculate for Physical infrastructure using PROMETHEE-II end for for each node of do Calculate Prepare for NSR using PROMETHEE-II end for Set allocationTrack=0 for each node of do if is not empty then for each node of do if and then node Allocation to Update and of and Update else Move to next node end if end for else if allocationTrack= then Return NSR node allocation unsuccessful else Return NSR node allocation success end if end for return |
4.2. SLE Strategy for SPA Preparation
| Algorithm 2: SLE for SPA preparation |
|
4.3. Hybrid PROMETHEE-II and SLE Approach for Deployment
| Algorithm 3: NSR deployment through hybrid PROMETHEE-II and SLE |
|
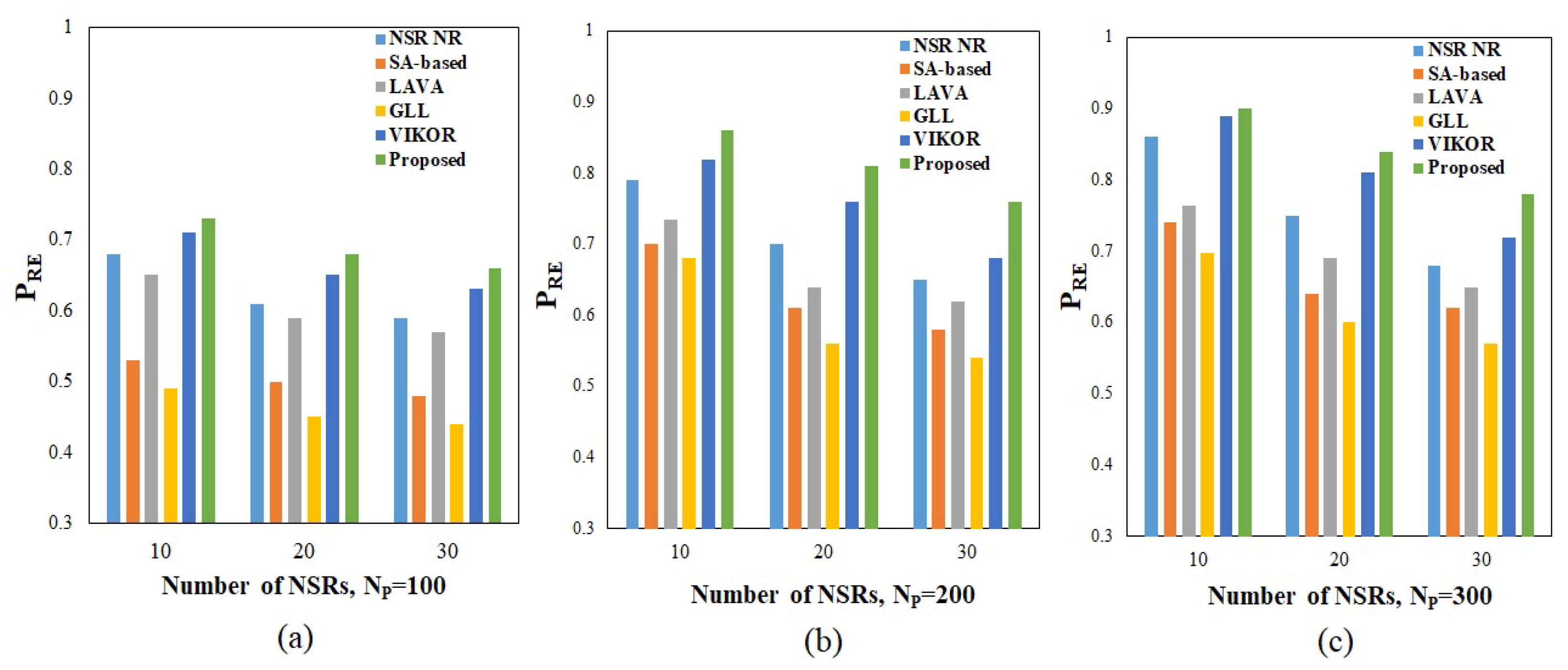
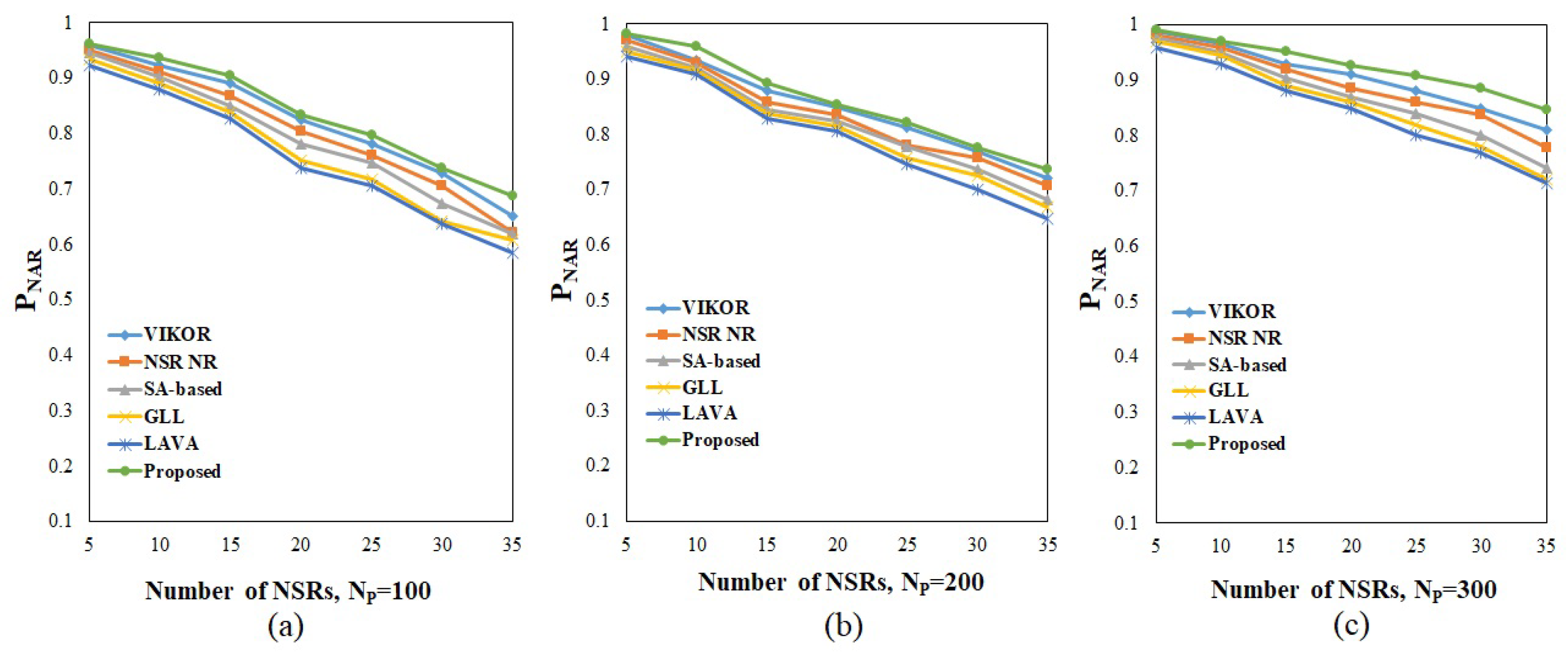
5. Simulation Results and Discussions
5.1. Implementation of Proposed Algorithm for NSR Resource Allocation
5.2. Implementation of the Algorithm under Different Physical Infrastructure Networks
6. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- 5G PPP Architecture Working Group. View on 5G Architecture: Version 2.0. 2017, pp. 1–117. Available online: https://discovery.ucl.ac.uk/id/eprint/10043680 (accessed on 31 January 2018).
- Alliance, N. Description of network slicing concept. NGMN 5G P 2016, 1, 1–11. [Google Scholar]
- Zhang, H.; Liu, N.; Chu, X.; Long, K.; Aghvami, A.H.; Leung, V.C. Network slicing based 5G and future mobile networks: Mobility, resource management, and challenges. IEEE Commun. Mag. 2017, 55, 138–145. [Google Scholar] [CrossRef]
- Study on Management and Orchestration of Network Slicing for Next Generation Network; 3GPP: Sophia Antipolis, France, 2018.
- Nojima, D.; Katsumata, Y.; Shimojo, T.; Morihiro, Y.; Asai, T.; Yamada, A.; Iwashina, S. Resource isolation in RAN part while utilizing ordinary scheduling algorithm for network slicing. In Proceedings of the 2018 IEEE 87th Vehicular Technology Conference (VTC Spring), Porto, Portugal, 3–6 June 2018; pp. 1–5. [Google Scholar]
- Parsaeefard, S.; Dawadi, R.; Derakhshani, M.; Le-Ngoc, T. Joint user-association and resource-allocation in virtualized wireless networks. IEEE Access 2016, 4, 2738–2750. [Google Scholar] [CrossRef]
- Tang, L.; Zhang, X.; Xiang, H.; Sun, Y.; Peng, M. Joint resource allocation and caching placement for network slicing in fog radio access networks. In Proceedings of the 2017 IEEE 18th International Workshop on Signal Processing Advances in Wireless Communications (SPAWC), Sapporo, Japan, 3–6 July 2017; pp. 1–6. [Google Scholar]
- Bega, D.; Gramaglia, M.; Banchs, A.; Sciancalepore, V.; Samdanis, K.; Costa-Perez, X. Optimising 5G infrastructure markets: The business of network slicing. In Proceedings of the IEEE INFOCOM 2017-IEEE Conference on Computer Communications, Atlanta, GA, USA, 1–4 May 2017; pp. 1–9. [Google Scholar]
- Sama, M.R.; An, X.; Wei, Q.; Beker, S. Reshaping the mobile core network via function decomposition and network slicing for the 5G Era. In Proceedings of the 2016 IEEE Wireless Communications and Networking Conference, Doha, Qatar, 3–6 April 2016; pp. 1–7. [Google Scholar]
- Bari, F.; Chowdhury, S.R.; Ahmed, R.; Boutaba, R.; Duarte, O.C.M.B. Orchestrating virtualized network functions. IEEE Trans. Netw. Serv. Manag. 2016, 13, 725–739. [Google Scholar] [CrossRef]
- Riggio, R.; Bradai, A.; Harutyunyan, D.; Rasheed, T.; Ahmed, T. Scheduling wireless virtual networks functions. IEEE Trans. Netw. Serv. Manag. 2016, 13, 240–252. [Google Scholar] [CrossRef]
- Ordonez-Lucena, J.; Ameigeiras, P.; Lopez, D.; Ramos-Munoz, J.J.; Lorca, J.; Folgueira, J. Network slicing for 5G with SDN/NFV: Concepts, architectures, and challenges. IEEE Commun. Mag. 2017, 55, 80–87. [Google Scholar] [CrossRef]
- Herker, S.; Khan, A.; An, X. Survey on survivable virtual network embedding problem and solutions. In Proceedings of the International Conference on Networking and Services, ICNS, Lisbon, Portugal, 24–29 March 2013; pp. 99–104. [Google Scholar]
- Leconte, M.; Paschos, G.S.; Mertikopoulos, P.; Kozat, U.C. A resource allocation framework for network slicing. In Proceedings of the IEEE INFOCOM 2018-IEEE Conference on Computer Communications, Honolulu, HI, USA, 16–19 April 2018; pp. 2177–2185. [Google Scholar]
- Kaloxylos, A. A survey and an analysis of network slicing in 5G networks. IEEE Commun. Stand. Mag. 2018, 2, 60–65. [Google Scholar] [CrossRef]
- Subedi, P.; Alsadoon, A.; Prasad, P.; Rehman, S.; Giweli, N.; Imran, M.; Arif, S. Network slicing: A next generation 5G perspective. EURASIP J. Wirel. Commun. Netw. 2021, 2021, 1–26. [Google Scholar] [CrossRef]
- Chowdhury, M.; Rahman, M.R.; Boutaba, R. Vineyard: Virtual network embedding algorithms with coordinated node and link mapping. IEEE/ACM Trans. Netw. 2011, 20, 206–219. [Google Scholar] [CrossRef]
- Duan, Q.; Wang, S.; Ansari, N. Convergence of networking and cloud/edge computing: Status, challenges, and opportunities. IEEE Netw. 2020, 34, 148–155. [Google Scholar] [CrossRef]
- Guan, W.; Wen, X.; Wang, L.; Lu, Z.; Shen, Y. A service-oriented deployment policy of end-to-end network slicing based on complex network theory. IEEE Access 2018, 6, 19691–19701. [Google Scholar] [CrossRef]
- Aarts, E.; Korst, J. Simulated Annealing and Boltzmann Machines: A Stochastic Approach to Combinatorial Optimization and Neural Computing; Wiley-Interscience series in discrete mathematics and optimization; John Wiley and Sons, Inc.: New York, NY, USA, 1989. [Google Scholar]
- Yu, C.; Hou, W.; Guan, Y.; Zong, Y.; Guo, P. Virtual 5G network embedding in a heterogeneous and multi-domain network infrastructure. China Commun. 2016, 13, 29–43. [Google Scholar] [CrossRef]
- Mijumbi, R.; Serrat, J.; Gorricho, J.L.; Bouten, N.; De Turck, F.; Davy, S. Design and evaluation of algorithms for mapping and scheduling of virtual network functions. In Proceedings of the 2015 1st IEEE Conference on Network Softwarization (NetSoft), London, UK, 13–17 April 2015; pp. 1–9. [Google Scholar]
- Cao, H.; Yang, L.; Zhu, H. Novel node-ranking approach and multiple topology attributes-based embedding algorithm for single-domain virtual network embedding. IEEE Internet Things J. 2017, 5, 108–120. [Google Scholar] [CrossRef]
- Tang, L.; Tan, Q.; Shi, Y.; Wang, C.; Chen, Q. Adaptive virtual resource allocation in 5G network slicing using constrained Markov decision process. IEEE Access 2018, 6, 61184–61195. [Google Scholar] [CrossRef]
- Ma, T.; Zhang, Y.; Wang, F.; Wang, D.; Guo, D. Slicing Resource Allocation for eMBB and URLLC in 5G RAN. Wirel. Commun. Mob. Comput. 2020, 1–11. [Google Scholar] [CrossRef]
- Faisal, A.R.; Hashim, F.; Noordin, N.K.; Ismail, M.; Jamalipour, A. Efficient beamforming and spectral efficiency maximization in a joint transmission system using an adaptive particle swarm optimization algorithm. Appl. Soft Comput. 2016, 49, 759–769. [Google Scholar] [CrossRef]
- Li, X.; Guo, C.; Gupta, L.; Jain, R. Efficient and secure 5G core network slice provisioning based on VIKOR approach. IEEE Access 2019, 7, 150517–150529. [Google Scholar] [CrossRef]
- Abidi, M.H.; Alkhalefah, H.; Moiduddin, K.; Alazab, M.; Mohammed, M.K.; Ameen, W.; Gadekallu, T.R. Optimal 5G network slicing using machine learning and deep learning concepts. Comput. Stand. Interfaces 2021, 76, 103518. [Google Scholar] [CrossRef]
- Wang, H.; Wu, Y.; Min, G.; Miao, W. A graph neural network-based digital twin for network slicing management. IEEE Trans. Ind. Inform. 2020, 18, 1367–1376. [Google Scholar] [CrossRef]
- Barabási, A.L.; Albert, R. Emergence of scaling in random networks. Science 1999, 286, 509–512. [Google Scholar] [CrossRef]
- Dong, Z.; Wang, Z.; Xie, W.; Emelumadu, O.; Lin, C.; Rojas-Cessa, R. An experimental study of small world network model for wireless networks. In Proceedings of the 2015 36th IEEE Sarnoff Symposium, Newark, NJ, USA, 20–22 September 2015; pp. 70–75. [Google Scholar]
- Guennebaud, G.; Jacob, B. Eigen. Version 3. 2010. Available online: http://eigen.tuxfamily.org (accessed on 31 January 2018).
- Gao, L.; Li, P.; Pan, Z.; Liu, N.; You, X. Virtualization framework and VCG based resource block allocation scheme for LTE virtualization. In Proceedings of the 2016 IEEE 83rd Vehicular Technology Conference (VTC Spring), Nanjing, China, 15–18 May 2016; pp. 1–6. [Google Scholar]
- Olya, M.H. Applying Dijkstra’s algorithm for general shortest path problem with normal probability distribution arc length. Int. J. Oper. Res. 2014, 21, 143–154. [Google Scholar] [CrossRef]
- Brans, J.; Mareschal, B. Multiple Criteria Decision Analysis: State of the Art Surveys; Figueira, Springer: New York, NY, USA, 2005; Volume 78. [Google Scholar]



| Ref. No. | Objectives | Node Provisioning for NSR Nodes | Link Provisioning for NSR Nodes | Physical Network | Resource | Security Issues |
|---|---|---|---|---|---|---|
| [17] | Slice acceptance ratio and revenue-to-cost ratio | Deterministic and random rounding | Deterministic and random rounding | Scale-free | Bandwidth and CPU capacity | Not considered |
| [19] | Acceptance ratio and resource efficiency | Acceptance ratio and resource efficiency | k shortest path Floyd algorithm | Scale-free | Bandwidth and CPU capacity | Not considered |
| [20] | Acceptance ratio and resource efficiency | Simulated annealing | Simulated annealing | Scale-free | Bandwidth and CPU capacity | Not considered |
| [21] | Acceptance ratio and resource efficiency | LAVA approach | LAVA approach | Scale-free | Bandwidth and CPU capacity | Not considered |
| [22] | Acceptance ratio and resource efficiency | GLL approach | GLL approach | Scale-free | Bandwidth and CPU capacity | Not considered |
| [23] | Slice acceptance ratio and revenue-to-cost ratio | Greedy node mapping | Dijkstra’s algorithm | Scale-free | Bandwidth and CPU capacity | Considered |
| [24] | Resource utilization and outage probability and resource efficiency | Markov decision process | Markov decision process | Scale-free NOMA | Power and subcarrier | Considered |
| [25] | Spectral efficiency and reliability | JSPA | JSPA | Scale-free OFDMA | Power and subcarrier | Not considered |
| [26] | Spectral efficiency and reliability | APSO | APSO | Scale-free OFDMA | Power and subcarrier | Not considered |
| [27] | Slice acceptance ratio and revenue-to-cost ratio | Node ranking using VIKOR | k shortest path algorithm | Scale-free | Bandwidth and CPU capacity | Considered |
| [28] | Slice classification accuracy | DBN and NN, GS-DHOA for weight function adjustments | DBN and NN, GS-DHOA for weight function adjustments | - | Performance dataset consists of network features | Considered |
| [29] | Latency and training loss | GNN model with DT | GNN model with DT | - | Performance dataset consists of network features | Considered |
| Proposed | Acceptance ratio and resource efficiency | Node ranking using PROMETHEE II | SPA formation through Dijkstra’s algorithm | Small-world network and scale-free network | Bandwidth and CPU capacity | Considered |
| . | . | . | . | . |
| . | . | . | . | . |
| Definitions | Descriptions | Range |
|---|---|---|
| The distribution of available security level of a node in real number | (0–1) | |
| The distribution of CPU for each node in unit | U[30, 60] | |
| The distribution of bandwidth of each links in unit | U[30, 60] | |
| L | The distribution of length of the links | U[1, 5] |
| The total number of NSRs arrived in the time frame | U[5, 35] | |
| The distribution of nodes for each NSR | U[10, 30] | |
| The distribution of CPU requirement | U[5, 25] | |
| The distribution of bandwidth requirement | U[5, 25] | |
| The distribution of required security level of a node in real number | (0–0.5) | |
| The time duration of each NSR | T[10, 40] |
| Model | 100 Nodes | 200 Nodes | 300 Nodes | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| BW Utilized | CPU Served | BW Utilized | CPU Served | BW Utilized | CPU Served | ||||||||
| NSRs | Min | Max | Min | Max | Min | Max | Min | Max | Min | Max | Min | Max | |
| SFN | 10 | 2328 | 4351 | 2212 | 4133 | 2605 | 4875 | 2501 | 4680 | 3123 | 5859 | 2967 | 5566 |
| 20 | 4086 | 7653 | 3882 | 7270 | 4729 | 8852 | 4540 | 8498 | 5601 | 10508 | 5321 | 9983 | |
| 30 | 7927 | 9908 | 7531 | 9413 | 9544 | 11,925 | 9162 | 11,448 | 10,626 | 13,275 | 10,095 | 12,611 | |
| SWN | 10 | 2921 | 5476 | 2775 | 5202 | 3440 | 6450 | 3302 | 6192 | 3605 | 6754 | 3425 | 6416 |
| 20 | 5448 | 10,200 | 5176 | 9690 | 6484 | 12,156 | 6225 | 11,670 | 6720 | 12,600 | 6384 | 11,970 | |
| 30 | 11,880 | 14,852 | 11,286 | 14,109 | 13,680 | 17,102 | 13,133 | 16,418 | 14,049 | 17,554 | 13,347 | 16,676 | |
| Model | 100 Nodes | 200 Nodes | 300 Nodes | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| BW Utilized | CPU Served | BW Utilized | CPU Served | BW Utilized | CPU Served | ||||||||
| NSRs | |||||||||||||
| SFN | 10 | 2406 | 914 | 2286 | 868 | 2811 | 1045 | 2699 | 1003 | 3321 | 1957 | 3155 | 1859 |
| 20 | 6243 | 2431 | 5931 | 2309 | 7368 | 2692 | 7073 | 2584 | 7862 | 3164 | 7468 | 3006 | |
| 30 | 8683 | 5292 | 8248 | 5027 | 9321 | 7018 | 8948 | 6737 | 9813 | 7738 | 9322 | 7351 | |
| SWN | 10 | 4812 | 1827 | 4571 | 1736 | 5622 | 2089 | 5397 | 2005 | 6642 | 3914 | 6310 | 3718 |
| 20 | 10,486 | 8861 | 9862 | 8618 | 11,736 | 8384 | 11,147 | 8169 | 11,723 | 8328 | 10,937 | 8012 | |
| 30 | 13,365 | 10,584 | 12,497 | 10,055 | 15,641 | 11,035 | 14,895 | 10,874 | 17,625 | 12,476 | 16,644 | 10,702 | |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Venkatapathy, S.; Srinivasan, T.; Jo, H.-G.; Ra, I.-H. Optimal Resource Allocation for 5G Network Slice Requests Based on Combined PROMETHEE-II and SLE Strategy. Sensors 2023, 23, 1556. https://doi.org/10.3390/s23031556
Venkatapathy S, Srinivasan T, Jo H-G, Ra I-H. Optimal Resource Allocation for 5G Network Slice Requests Based on Combined PROMETHEE-II and SLE Strategy. Sensors. 2023; 23(3):1556. https://doi.org/10.3390/s23031556
Chicago/Turabian StyleVenkatapathy, Sujitha, Thiruvenkadam Srinivasan, Han-Gue Jo, and In-Ho Ra. 2023. "Optimal Resource Allocation for 5G Network Slice Requests Based on Combined PROMETHEE-II and SLE Strategy" Sensors 23, no. 3: 1556. https://doi.org/10.3390/s23031556
APA StyleVenkatapathy, S., Srinivasan, T., Jo, H.-G., & Ra, I.-H. (2023). Optimal Resource Allocation for 5G Network Slice Requests Based on Combined PROMETHEE-II and SLE Strategy. Sensors, 23(3), 1556. https://doi.org/10.3390/s23031556






