Enhancing Security and Privacy in Healthcare Systems Using a Lightweight RFID Protocol
Abstract
:1. Introduction
2. Related Work
3. Proposed Lightweight RFID Protocol
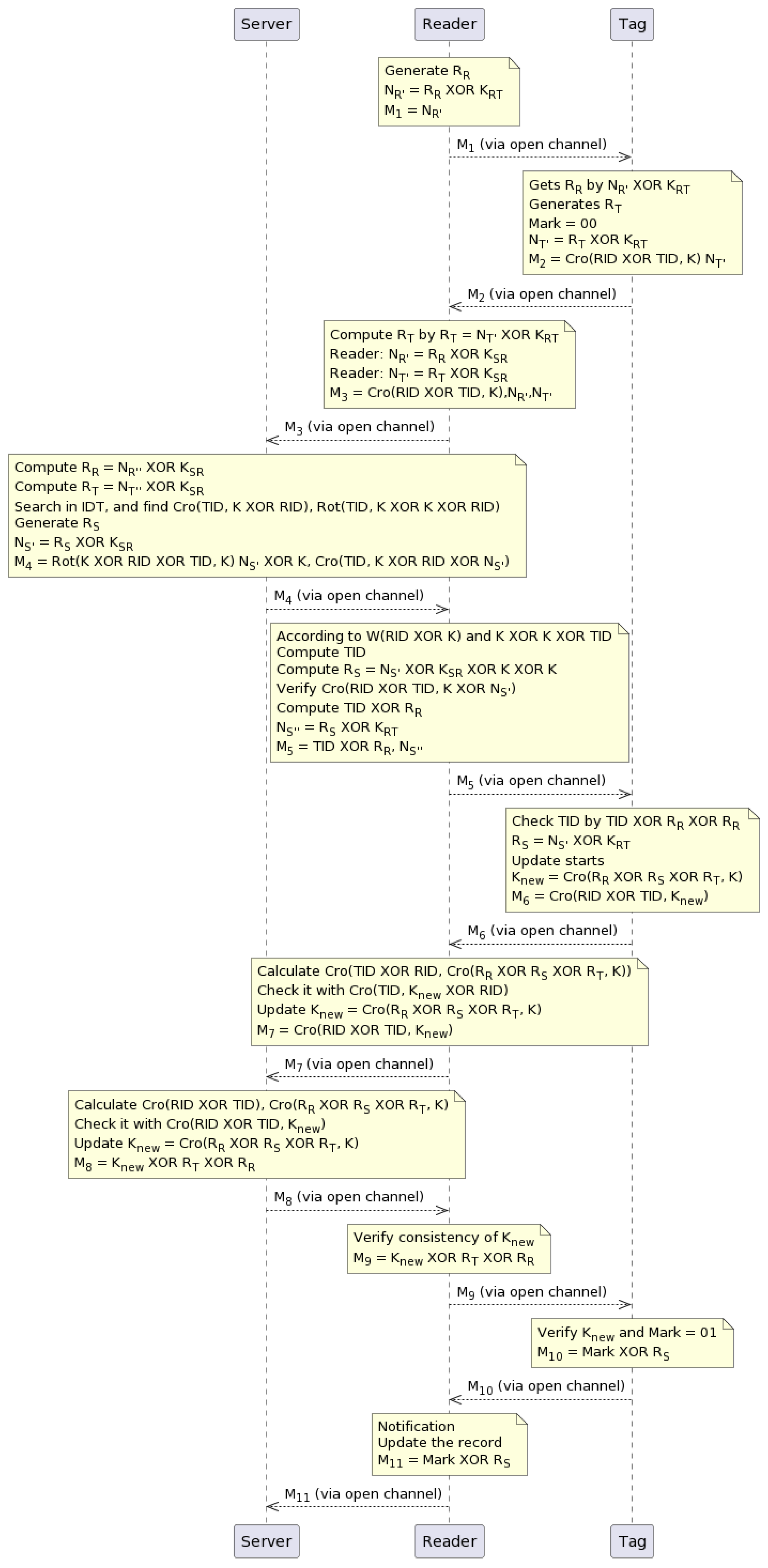
- Step 1:
- The scheme involves the reader and tag exchanging random numbers. The is a random number generated by a reader, and it is encrypted with a preshared key between the reader and tag. The resulting value is stored by the reader in , which is a message sent through a public channel to the tag.
- Step 2:
- The tag decrypts the random number by computing , where is a preshared key among the tag and reader. The tag generates its random number and sets a mark value of 00, thus indicating the start of the session. The tag then encrypts its random number with and stores the result in as . The tag also calculates and stores it in , which is sent to the reader through a public channel.
- Step 3:
- The reader decrypts the tag’s random number by computing , where is the value received in . The reader then encrypts the tag’s nonce and the reader’s nonce using a preshared key between the server and reader. This results in and (the double primes indicate the second encryption). The reader then calculates and stores it along with and in , which is sent directly to the server.
- Step 4:
- The server attains the random numbers of the reader and tag by decrypting them with as and , respectively. The server searches the ID table for the index corresponding to the value received in , which is . The protocol stops if the index value does not match an index in . If the index value matches an index in , a random number is produced by the server, which then encrypts it with and stores the result in . The server then calculates , , and and stores all three values in , which is sent to the reader through a public channel.
- Step 5:
- The reader checks the and obtains as follows. First, it computes the hamming weight of , which is denoted by . Then, it computes . Using these values, it obtains and as and , respectively. The reader then compares the received value with the calculated value to verify. If they match, it stores and in and forwards to the tag through a public channel.
- Step 6:
- The tag first obtains a random number . Then, it performs an XOR operation between the and the previously received , which is denoted as . Next, it checks if . After that, it updates the session number K by acquiring three random numbers: and . Specifically, K is replaced with , where . Remember that K is the default value mutually exchanged by the reader, tag, and server in the first session. Before initiating the next phase, the tag stores in and is shared with the reader.
- Step 7:
- The K in the server and reader is updated. Since some of the parameters are already calculated and present in the reader and server, such as and K, they take advantage of this fact and execute to obtain . They then compare it with the received from the tag, which is denoted as M7= . If they match, the reader updates . After this step, some verification operations are performed for the consistency of in the tag, reader, and server. Finally, the reader shares M7 with the server.
- Step 8:
- The server calculates and and checks them with ; after that, it updates and stores in M8. The server sends M8 to the reader via an insecure channel.
- Step 9:
- The reader verifies the consistency of and calculates , , and ; it then stores them in as . The reader also sends them to the tag, but it stores them within before sending them to the tag. Thus, is sent to the tag through a public channel.
- Step 10:
- In addition, both the reader and tag perform the same operations to confirm by obtaining it with the help of the operation , and they validate it against the previous value that was calculated before. If the verification process does not encounter any problems and is smooth, the value is set to 01, thereby indicating that the synchronization regarding K is completed.
- Step 11:
- The reader receives a notification from the tag to update the record. The reader stores mark value XOR with in M11; it then forwards to the server, which means the value is 01 at the server side. A new record , is produced and added to the index table IDT. The tag then sets the value to 10 after receiving a notification that the data has finished updating. The proposed authentication protocol is completed.
4. Computation Cost Comparison
5. Security Analysis
5.1. Automated ProVerif Security Proof
- Query 1 tests the event injection for the server. It checks if the ProVerif response confirms that the connection on the server is successfully opened and closed. The query result indicates that the event injection from end_S(IDS[]) to start_S(IDS[]) is true, meaning that the server’s communication channel is functioning correctly.
- Query 2 tests the event injection for the reader. It verifies if the ProVerif response confirms that the connection on the reader is successfully opened and closed. The query result indicates that the event injection from end_R(IDR[]) to start_R(IDR[]) is true, thereby indicating that the reader’s communication channel is functioning correctly.
- Query 3 focuses on the event injection for the tag. It checks if the ProVerif response confirms that the connection on the tag is successfully opened and closed. The query result indicates that the event injection from end_T(IDT[]) to start_T(IDT[]) is true, thus implying that the tag’s communication channel is functioning correctly.
- Query 4 examines the security/strength of the secret key KNEW by checking if it is susceptible to an attacker. The ProVerif response indicates that KNEW is secure, given that the result of not attacker(KNEW[]) is true. Therefore, the secret key KNEW is deemed secure, and an attacker cannot intercept it from the public channel.
5.2. BAN Logic Security Proof
- Goal 1:
- Goal 2:
- Goal 3:
- Goal 4:
- Goal 5:
5.2.1. Idealized Form
- M1:
- M2:
- M3:
- M4:
- M5:
- M6:
- M7:
- M8:
5.2.2. Assumption
- A 1:
- A 2:
- A 3:
- A 4:
- A 5:
- A 6:
- A 7:
5.2.3. Idealized form Verification
- V 1: , which demonstrates that only the reader and the server (as well as any other entities that they believe know the value of K) can access S. Combining this with the message seeing rule, P < (X, Y) |- P < X, we obtain
- V 2: , where Cro is a cryptographic function, and are identifiers, and K is the shared secret key.
- V 3:
- V 4:
- V 5:Hence, according to the above proof process, the first goal (Goal 1) has been achieved. Similarly, we can compute the message sent to the reader from the server as
- V 6: , namely, the Goal 2.By the same procedure, we can compute Goals 3 and 4. According to (A 1, A 2, A 3) and the process of front demonstration, we can obtain . Moreover, we combine secret rules and message keys. Given and , we can see that
- V 7:Hence, all the protocol goals have been proved to secure the proposed scheme logically.
5.2.4. Goals
- The server believes that and share a secret parameter ;
- believes in and also believes that and share the secret value ;
- believes that shares the secret key of with ;
- believes in and also believes that shares a secret key with .
6. Informal Security Analysis
7. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Lee, I.; Lee, K. The Internet of Things (IoT): Applications, investments, and challenges for enterprises. Bus. Horizons 2015, 58, 431–440. [Google Scholar] [CrossRef]
- Mahmood, K.; Arshad, J.; Chaudhry, S.A.; Kumari, S. An enhanced anonymous identity-based key agreement protocol for smart grid advanced metering infrastructure. Int. J. Commun. Syst. 2019, 32, 16. [Google Scholar] [CrossRef]
- Vijayakumar, P.; Obaidat, M.S.; Azees, M.; Islam, S.H.; Kumar, N. Efficient and Secure Anonymous Authentication with Location Privacy for IoT-Based WBANs. IEEE Trans. Ind. Inform. 2020, 16, 2603–2611. [Google Scholar] [CrossRef]
- Mishra, D.; Rana, S. A provably secure content distribution framework for portable DRM systems. J. Inf. Secur. Appl. 2021, 61, 102928. [Google Scholar] [CrossRef]
- Gao, M.; Lu, Y. URAP: A new ultra-lightweight RFID authentication protocol in passive RFID system. J. Supercomput. 2022, 78, 10893–10905. [Google Scholar] [CrossRef]
- Shariq, M.; Singh, K.; Maurya, P.K.; Ahmadian, A.; Taniar, D. AnonSURP: An anonymous and secure ultralightweight RFID protocol for deployment in internet of vehicles systems. J. Supercomput. 2022, 78, 8577–8602. [Google Scholar] [CrossRef]
- An, Y.; Zhang, Y.; Cao, W.; Tong, Z.; He, Z. A Lightweight and Practical Anonymous Authentication Protocol Based on Bit-Self-Test PUF. Electronics 2022, 11, 772. [Google Scholar] [CrossRef]
- Rana, S.; Mishra, D. Secure and ubiquitous authenticated content distribution framework for IoT enabled DRM system. Multimed. Tools Appl. 2020, 79, 20319–20341. [Google Scholar] [CrossRef]
- Chander, B.; Gopalakrishnan, K. A secured and lightweight RFID-tag based authentication protocol with privacy-preserving in Telecare medicine information system. Computer Commun. 2022, 191, 425–437. [Google Scholar] [CrossRef]
- Chen, Y.; Chou, J.S.; Lin, C.F.; Wu, C.L. A Novel RFID Authentication Protocol based on Elliptic Curve Cryptosystem. IACR Cryptol. EPrint Arch. 2011, 2011, 381. [Google Scholar]
- Bilal, Z.; Masood, A.; Kausar, F. Security analysis of ultra-lightweight cryptographic protocol for low-cost RFID tags: Gossamer protocol. In Proceedings of the 2009 International Conference on Network-Based Information Systems, Indianapolis, IN, USA, 19–21 August 2009; pp. 260–267. [Google Scholar]
- Abughazalah, S.; Markantonakis, K.; Mayes, K. Secure improved cloud-based RFID authentication protocol. In Data Privacy Management, Autonomous Spontaneous Security, and Security Assurance; Springer: Berlin/Heidelberg, Germany, 2015; pp. 147–164. [Google Scholar]
- Xie, W.; Xie, L.; Zhang, C.; Zhang, Q.; Tang, C. Cloud-based RFID authentication. In Proceedings of the 2013 IEEE International Conference on RFID (RFID), Penang, Malaysia, 30 April–2 May 2013; pp. 168–175. [Google Scholar]
- Fan, K.; Jiang, W.; Li, H.; Yang, Y. Lightweight RFID Protocol for Medical Privacy Protection in IoT. IEEE Trans. Ind. Inform. 2018, 14, 1656–1665. [Google Scholar] [CrossRef]
- Kaul, S.D.; Awasthi, A.K. RFID authentication protocol to enhance patient medication safety. J. Med. Syst. 2013, 37, 9979. [Google Scholar] [CrossRef]
- Chou, J.S. An efficient mutual authentication RFID scheme based on elliptic curve cryptography. J. Supercomput. 2014, 70, 75–94. [Google Scholar] [CrossRef]
- Liao, Y.P.; Hsiao, C.M. A secure ECC-based RFID authentication scheme integrated with ID-verifier transfer protocol. Ad Hoc Netw. 2014, 18, 133–146. [Google Scholar] [CrossRef]
- Zhao, Z. A secure RFID authentication protocol for healthcare environments using elliptic curve cryptosystem. J. Med. Syst. 2014, 38, 46. [Google Scholar] [CrossRef]
- Peeters, R.; Hermans, J. Attack on Liao and Hsiao’s Secure ECC-Based RFID Authentication Scheme Integrated with ID-Verifier Transfer Protocol. Cryptology ePrint Archive. 2013. Available online: https://eprint.iacr.org/2013/399.pdf (accessed on 15 March 2023).
- Farash, M.S.; Nawaz, O.; Mahmood, K.; Chaudhry, S.A.; Khan, M.K. A provably secure RFID authentication protocol based on elliptic curve for healthcare environments. J. Med. Syst. 2016, 40, 165. [Google Scholar] [CrossRef]
- Srivastava, K.; Awasthi, A.K.; Kaul, S.D.; Mittal, R. A hash based mutual RFID tag authentication protocol in telecare medicine information system. J. Med. Syst. 2015, 39, 153. [Google Scholar] [CrossRef] [PubMed]
- Li, C.T.; Weng, C.Y.; Lee, C.C. A secure RFID tag authentication protocol with privacy preserving in telecare medicine information system. J. Med. Syst. 2015, 39, 77. [Google Scholar] [CrossRef]
- Jin, C.; Xu, C.; Zhang, X.; Li, F. A secure ECC-based RFID mutual authentication protocol to enhance patient medication safety. J. Med. Syst. 2016, 40, 12. [Google Scholar] [CrossRef] [PubMed]
- Prakash Pokala, J.; Reddy, M.C.; Bapana, S.; Vorugunti, C.S. A secure RFID protocol for telecare medicine information systems using ECC. In Proceedings of the 2016 International Conference on Wireless Communications, Signal Processing and Networking (WiSPNET), Chennai, India, 23–25 March 2016; pp. 2295–2300. [Google Scholar]
- Zhou, Z.; Wang, P.; Li, Z. A quadratic residue-based RFID authentication protocol with enhanced security for TMIS. J. Ambient Intell. Humaniz. Comput. 2019, 10, 3603–3615. [Google Scholar] [CrossRef]
- Safkhani, M.; Vasilakos, A. A new secure authentication protocol for telecare medicine information system and smart campus. IEEE Access 2019, 7, 23514–23526. [Google Scholar] [CrossRef]
- Zheng, L.; Song, C.; Cao, N.; Li, Z.; Zhou, W.; Chen, J.; Meng, L. A new mutual authentication protocol in mobile RFID for smart campus. IEEE Access 2018, 6, 60996–61005. [Google Scholar] [CrossRef]
- Chen, X.; Geng, D.; Zhai, J.; Liu, W.; Zhang, H.; Zhu, T. Security analysis and enhancement of the most recent RFID protocol for telecare medicine information system. Wirel. Pers. Commun. 2020, 114, 1371–1387. [Google Scholar] [CrossRef]
- Shariq, M.; Singh, K.; Maurya, P.K.; Ahmadian, A.; Ariffin, M.R.K. Urasp: An ultralightweight rfid authentication scheme using permutation operation. Peer- Netw. Appl. 2021, 14, 3737–3757. [Google Scholar] [CrossRef]
- Xiao, L.; Xie, S.; Han, D.; Liang, W.; Guo, J.; Chou, W.K. A lightweight authentication scheme for telecare medical information system. Connect. Sci. 2021, 33, 769–785. [Google Scholar] [CrossRef]

| Notations | |||
|---|---|---|---|
| Notation | Description | Notation | Description |
| Random Nonce of Reader | Random Number of Server | ||
| Random Number of Tag | Tag ID | ||
| Reader ID | Preshared Key between and | ||
| Preshared Key between and | ⊕ | The XOR Operation | |
| K | Current Session Number | Next Session Number | |
| Cross Operation | Rotation Operation, | ||
| Status of Last Session | Random number of Reader xor with | ||
| Random number of Tag xor with | Random number of server xor with | ||
| Random number of Tag xor with | Random number of server xor with | ||
| Schemes | Cost |
|---|---|
| Kaul et al. [15]. | |
| Chien Protocol [10]. | |
| Gossamer Protocol [11]. | |
| Xie Protocol [13]. | |
| Sarah Protocol [12]. | |
| Fan Protocol [14]. | |
| Proposed Scheme |
| Query | ProVerif Response |
|---|---|
| Query inj-event(end_S(IDS[])) ==>inj-event(start_S(IDS[])) Completing… Starting query inj-event(end_S(IDS[])) ==>inj-event(start_S(IDS[])) | inj-event(end_S(IDS[])) ==>inj-event(start_S(IDS[])) is true. |
| Query inj-event(end_R(IDR[])) ==>inj-event(start_R(IDR[])) Completing… Starting query inj-event(end_R(IDR[])) ==>inj-event(start_R(IDR[])) | inj-event(end_S(IDR[])) ==>inj-event(start_S(IDR[])) is true. |
| Query inj-event(end_T(IDT[])) ==>inj-event(start_T(IDT[])) Completing… Starting query inj-event(end_T(IDT[])) ==>inj-event(start_T(IDT[])) | inj-event(end_T(IDT[])) ==>inj-event(start_T(IDT[])) is true. |
| Query not attacker(KNEW[]) Completing… Starting query not attacker(KNEW[]) | not attacker(KNEW[]) is true. |
| Notations | Description |
|---|---|
| Q believing in X | |
| Q sees which is X | |
| Q believes T’s action. E.g., | |
| means Q believes T believes X is true | |
| Q once says X | |
| Q has full jurisdiction beyond X | |
| X is updated and fresh | |
| Combine conditions C by the use of k | |
| Carry out hash operation on C; use X | |
| Message of hash X with a key K | |
| Q and T used to interact using the shared key k | |
| with each other | |
| Session key used one time in the | |
| current section | |
| Rule of Message-Meaning | |
| Rule of Concatenation-Freshness | |
| Rule of Verification-Nonce | |
| Rule of Jurisdiction |
| Security Criteria | Description |
|---|---|
| Tag Anonymity (R1) | Tag anonymity ensures privacy and prevents unauthorized tracking by concealing the identity of the tag or device that transmits information in a system or protocol. |
| Reply Attack (R2) | A malicious actor intercepts and retransmit legitimate data or actions to deceive a system, thereby compromising its integrity and security. |
| Synchronization Attack (R3) | It occurs when an attacker manipulates the coordination among the different entities to disrupt normal operations or gain unauthorized access. This attack compromises the targeted system’s integrity, availability, or confidentiality by exploiting timing or communication dependencies. |
| Forward Secrecy (R4) | A security vulnerability where the exposure of a long-term secret key does not compromise the privacy of previous communications. This ensures that historical data remains safeguarded, even if the private key is compromised. |
| Mutual Authentication (R5) | Mutual authentication is a security measure where both parties involved in a communication process verify each other’s identities, thereby establishing trust and preventing unauthorized access or impersonation. This ensures that the reader, tag and server confirm each other’s authenticity before establishing a connection. |
| DoS Attack (R6) | An adversary inundates a target system or network with high requests or traffic, thus resulting in service disruption or unavailability for legitimate users. The goal is to deplete system resources and impede its ability to handle legitimate requests. |
| Impersonation Attack (R7) | It occurs when an attacker assumes a false identity by posing as a legitimate user or entity in a cybersecurity breach. By exploiting this deception, the attacker aims to gain unauthorized access, deceive others, and potentially engage in malicious actions such as manipulating or stealing sensitive information while bypassing security measures. |
| Insider Attacker (R8) | It occurs within an organization and involves trusted individuals such as employees or contractors with authorized access. Leveraging their privileged positions, these attacks target system compromises, data theft, or infrastructure damage, thus posing significant risks due to the insider’s knowledge and authorized access. |
| Formal Verification (R9) | Formal verification means the proposed scheme security test uses well-known automated tools such as ProVerif. It also test the correctness of the proposed scheme using BAN Logics. |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Khan, M.A.; Ullah, S.; Ahmad, T.; Jawad, K.; Buriro, A. Enhancing Security and Privacy in Healthcare Systems Using a Lightweight RFID Protocol. Sensors 2023, 23, 5518. https://doi.org/10.3390/s23125518
Khan MA, Ullah S, Ahmad T, Jawad K, Buriro A. Enhancing Security and Privacy in Healthcare Systems Using a Lightweight RFID Protocol. Sensors. 2023; 23(12):5518. https://doi.org/10.3390/s23125518
Chicago/Turabian StyleKhan, Muhammad Ayaz, Subhan Ullah, Tahir Ahmad, Khwaja Jawad, and Attaullah Buriro. 2023. "Enhancing Security and Privacy in Healthcare Systems Using a Lightweight RFID Protocol" Sensors 23, no. 12: 5518. https://doi.org/10.3390/s23125518
APA StyleKhan, M. A., Ullah, S., Ahmad, T., Jawad, K., & Buriro, A. (2023). Enhancing Security and Privacy in Healthcare Systems Using a Lightweight RFID Protocol. Sensors, 23(12), 5518. https://doi.org/10.3390/s23125518








