Abstract
Healthcare is now an important part of daily life because of rising consciousness of health management. Medical professionals can know users’ health condition if they are able to access information immediately. Telemedicine systems, which provides long distance medical communication and services, is a multi-functional remote medical service that can help patients in bed in long-distance communication environments. As telemedicine systems work in public networks, privacy preservation issue of sensitive and private transmitted information is important. One of the means of proving a user’s identity are user-controlled single sign-on (UCSSO) authentication scheme, which can establish a secure communication channel using authenticated session keys between the users and servers of telemedicine systems, without threats of eavesdropping, impersonation, etc., and allow patients access to multiple telemedicine services with a pair of identity and password. In this paper, we proposed a smartcard-based user-controlled single sign-on (SC-UCSSO) for telemedicine systems that not only remains above merits but achieves privacy preservation and enhances security and performance compared to previous schemes that were proved with BAN logic and automated validation of internet security protocols and applications (AVISPA).
1. Introduction
Healthcare is now an important part of daily life because of rising consciousness of health management. People can check up health conditions by themselves, such as heartbeat rate, quality of sleep, amount of exercise, and so on, by supporting wearable technology, including smart phone, smart watch, smart bracelet, etc., which measures biodata and assists self-health management. Currently, biodata is only transferred to a smartphone and analyzed by applications on a smart phone, without being transferred to other outside systems [1]. Medical professionals can know users’ health conditions, if medical professionals are able to access the information immediately [1].
Telemedicine systems provide long distance medical communication and services through which patient and medical professionals can communicate online, and patient benefits from being supported with ambulatory care or other medical services, even in remote areas [1,2,3,4]. Telemedicine systems allow health related data and image to be reliably transmitted from one point to another [1]. Many researchers focused on monitoring patient’s health with specific diseases using telemedicine, such as diabetes and Parkinson’s disease, and telemedicine systems can help a patient recover from illness through this way [5,6,7,8]. In other words, telemedicine can help patients improve their quality of life [1]. Moreover, telemedicine systems can provide better solutions in emergency situations and serious disease monitoring [1,8,9,10]. Telemedicine systems are implemented with wireless communication environments, such as Wi-Fi, Internet of Things (IoT), and fifth generation (5G), to achieve long distance medical communication and services [8,11]. The sensors, such as wearable devices, for example, gather measured data, and measured data are then transmitted through gateways, 5G base stations, and core networks. After this, data is stored or analyzed by applications in back-end servers or cloud servers.
Telemedicine systems are implemented with wireless communication environments, which means data are transmitted through public networks. The patient sends healthcare-related information through public networks when using telemedicine technology, and the transmitted information is important, sensitive, and private [1]. Security issues related to data transmission were discussed, such as eavesdropping, man-in-the-middle (MITM) attack, data tempering attack, message modification attack, data interception attack, etc. [12] Although the Health Insurance Portability and Accountability Act (HIPAA), General Data Protection Regulation (GDPR), and Safe Harbor Laws have regulations that provide privacy of personal information, technical support is still not enough [12,13,14].
Security issues exist in multi-server environments when applying conventional password-based authenticated key exchange schemes. Users have to maintain pairs of identifiers and passwords that increase computational cost and security risks. Moreover, a trustworthy third party is required, while users utilize a single pair of identity and password in multi-server telemedicine systems. However, a malicious third party is able to impersonate users to access other services, with knowledge of shared keys. The same can be proved if a malicious server exists. In terms of performance, the cost of establishing a session key for users is related to the number of servers in conventional schemes. A single sign-on (SSO) mechanism can overcome the above issues that allow users a single action to achieve authentication with a single pair of identity and password, rather than with multiple passwords [15,16,17].
In the proposed scheme, we apply a user-controlled SSO (UCSSO) authenticated key agreement. The key allows patients access to services in multi-server telemedicine systems with a user-defined password, and establishes a secret shared key among servers for securing subsequent communications and designing a smartcard-based user-controlled single sign-on (SC-UCSSO) scheme that can be applied in 5G-IoT multi-server telemedicine systems. The patients has data ownership as they can control and decide the data’s destination and time of transmission. The proposed scheme establishes a secure communication channel using authenticated session keys between patients and services, while meeting general security requirements. Moreover, computational complexity is better than the compared previous schemes. We sketch the remaining organization of paper below. We introduce telemedicine systems and the Chebyshev chaotic maps in Section 2. We introduce our scheme in Section 3, and security and performance analysis are detailed in Section 4 and Section 5. We present our results of implementation in Section 6. Finally, the conclusion is drawn in Section 7.
2. Related Works
2.1. Telemedicine Systems
Telemedicine systems is a technology of electronic message and telecommunication related to healthcare [1,18]. The National Health Services (NHS) of United Kingdom defines changes to NHS service model as “out of hospital care”, “reducing emergency hospital services”, “personalized care”, “digitally enables care”, and “integrated care systems models”, which can correspond to the features of telemedicine systems [19,20]. Thanks to the IoT technology, which enable medical professionals to monitor patients who are outside of medical institutes in real-time, medical professionals can know users’ health condition, if they are able to view the information immediately [1,20]. In other words, telemedicine systems with IoT can enhance functions of patient’s health monitor and proactive and preventive healthcare interventions [20].
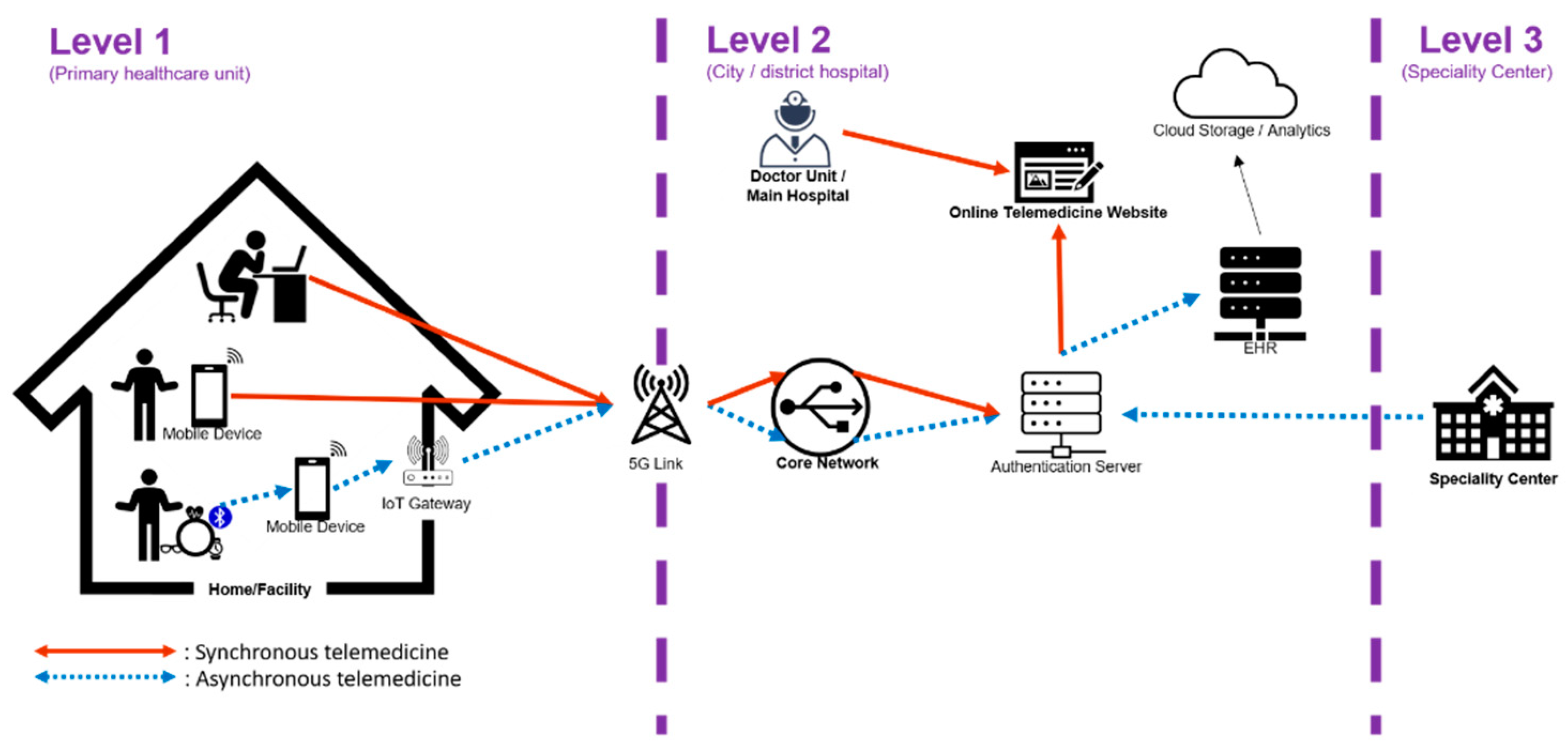
A general telemedicine system can be divided into three level [21]. Level 1 (primary healthcare unit) consists of users with webcam, smart phone, or wearable devices, which is enables communications of measured biodata through wireless communications, including radio frequency identification (RFID), near field communication (NFC), Bluetooth, Wi-Fi, Zigbee, etc. [20]. Measured biodata are transmitted to the user’s smartphone without being transferred to other systems [1]. Level 2 (city or district hospital) is clinic or local hospital that the patient might visit before being transferred to a large hospital or medical center. Level 3 (specialty center) takes part in telemedicine in case of a rare disease or an incurable disease [21]. Figure 1 illustrates a general telemedicine system including two scenarios—asynchronous telemedicine and synchronous telemedicine [21,22]. Asynchronous telemedicine allows patients to decide a proper time to send medical image and health record to medical service providers for detailed examination. Synchronous telemedicine, also called synchronous video conferencing or interactive telemedicine, provides real-time communication between patient and medical professional [22].

Figure 1.
A general telemedicine system with asynchronous and synchronous telemedicine.
2.2. Medical Privacy
Telemedicine systems have many challenges, such as infrastructure, connections, professional requirements, data management, and real-time monitoring [23,24]. Medical privacy is of the utmost importance, and damage of medical privacy not only brings huge economic losses and losses of credibility to hospitals and other related institutions but does potential harm to patients and endangers lives of patients [24,25]. Unfortunately, thus far, healthcare-related industries did not achieve users’ expectations [24]. Trust management (TM) is important for allowing reliable data collection and transmission, to provide qualified services and enhance user privacy and information security [26]. Gambetta first defined two widely accepted definitions of trust called reliability trust and decision trust [26,27]. Recently, researchers had discussions about TM of IoT [28,29,30,31,32]. Fortino et al. summarized and discussed main trust concepts, including behavior trust, reputation, honesty, and accuracy [26].
As we mentioned, telemedicine is implemented in public networks, so privacy preservation is one of notable security issues, which has caught researchers’ attention. Mishra et al. [33] and Renuka et al. [34] utilized a biometric feature to design authentication schemes for telemedicine systems. Zriqat and Altamimi discussed issues through data collection, data transmission, and data storage and access level [12]. Dharminder et al. discussed authorized access to healthcare services [35]. Zhang et al. [36], Zhang et al. [37], and Sureshkumar et al. [38] designed authentication and key agreement for telemedicine system. Baker et al. [8], Guo et al. [39], and Anwar et al. [11] focused on telemedicine using IoT, blockchain, and 5G technology and proposed framework or scheme. In summary, three keys to the question must be solved for assuring telemedicine environments. First, image storage should be highly efficient. Second, transmitting sensitive image should satisfy confidence, integrity, and accessibility. Finally, encryption progress should be efficient, especially for the end-point.
3. Proposed Scheme
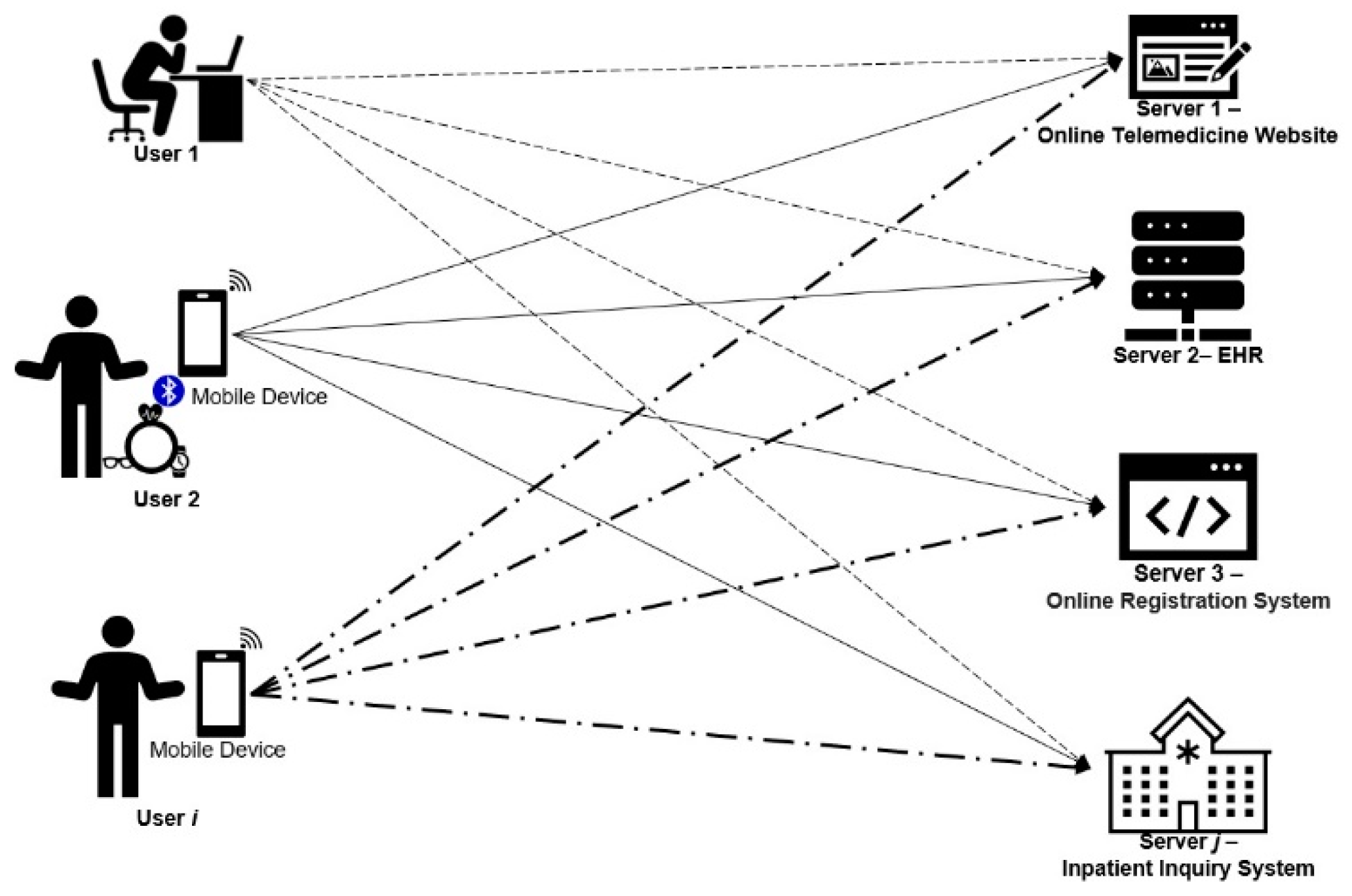
In the proposed system, there are i users and j servers. User can use a smartcard or a smart token to log in to whichever server user wishes to access, as shown in Figure 2. The proposed scheme includes four phases—system initialization phase, registration phase, authenticated key exchange phase, and offline password change phase. In the system initialization phase, Server generates essential parameters and functions for the whole scheme. User becomes a legitimate member in the system through the registration phase. In the authenticated key exchange phase, User and server authenticate each other and establish a session key for symmetric encryption for communication and transmitted measured biodata. The proposed scheme provides offline password change phase such that user can change the password periodically, without the participation of server . Notations are defined in Table 1.

Figure 2.
System structure of the proposed scheme.

Table 1.
Notations of the proposed scheme.
3.1. Preliminary
We briefly introduce Chebyshev chaotic maps in this section. The chaotic system has properties that can correspond to the cryptosystem’s properties. First, the result is unpredictable if small changes in initial values occur [40,41,42]. Second, the chaotic system is a complex oscillation [40,41,42]. Third, the chaotic system shows qualitative change of character of solutions [40,41,42]. The above features can correspond to confusion and diffusion of the cryptosystem, which was discussed for decades [24,40,41,42,43,44,45,46,47,48,49,50]. Mathematical definitions of the Chebyshev chaotic maps are introduced as below [24,46,47,48,49,50].
- Polynomials of Chebyshev chaotic maps is formed as in x of degree n.
- If , polynomials of the Chebyshev chaotic maps is formed as . However, results of the Chebyshev chaotic maps are 1 and x when n is 0 and 1, respectively.
- If and , , which is the so-called semi-group property.
- Zhang [51] proved that semi-group property can hold if Chebyshev polynomials are extended on interval . In the situation, polynomials of Chebyshev chaotic maps become where , , and N is a large prime number, and .
- Even only with the knowledge of x and y, n is computationally infeasible to be obtained such that , which is the so-called Chaotic maps-based discrete logarithm problem (CMDLP).
- Even only with the knowledge of (x , ), is computationally infeasible to be obtained, which is the so-called Chaotic maps-based Diffie-Hellman problem (CMDHP).
The proposed scheme applies the extended Chebyshev chaotic maps, which satisfies the above definitions.
3.2. System Initialization Phase
User sets up smartcard by entering an identifier and password in the system initialization phase. Server sets up the system’s parameters by performing the following steps.
- Step 1.
- Server generates a secret value , a big prime p, and a random number .
- Step 2.
- Server choses a symmetric encryption algorithm , a symmetric decryption algorithm , a collision-resistance one-way hash function H(.), and a collision-resistance secure one-way chaotic hash function (.).
3.3. Registration Phase
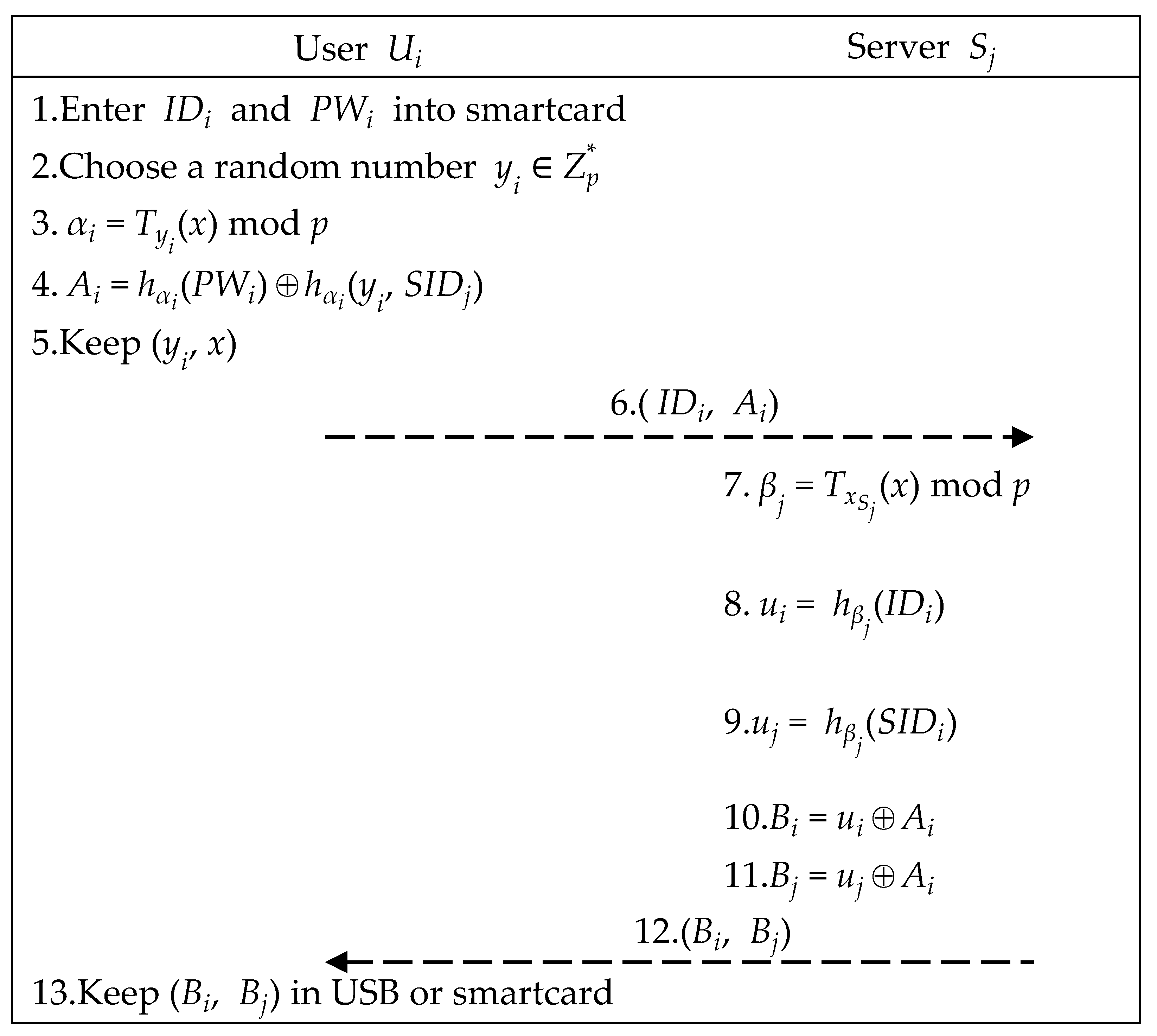
User and server perform the following steps to complete the registration phase to become a legitimate member, as illustrated in Figure 3.

Figure 3.
Registration phase of the proposed scheme.
- Step 1.
- User enters and .
- Step 2.
- User uses the smartcard to choose a random number After that, smartcard computes ( ) as below. Finally, smartcard stores and sends (, ) to server .
- Step 3.
- After receiving (, ), server computes elements below. Then, server returns (, ) to user .
- Step 4.
- Upon receiving (, ), user stores (, ) in USB or smartcard.
3.4. Authenticated Key Exchange Phase
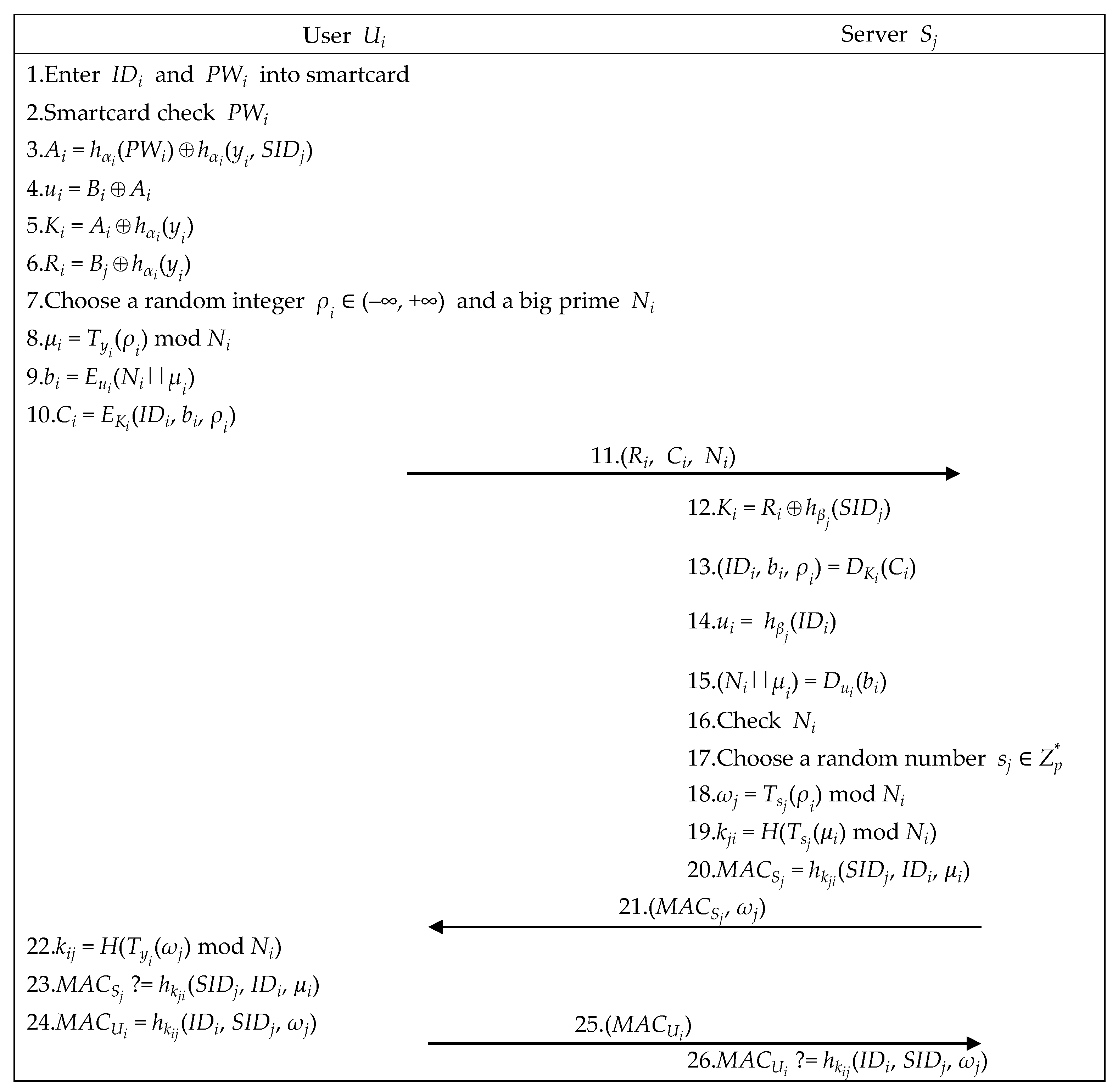
To complete the mutual authentication and session key confirmation and obtain the remote server’s services, user , user ’s smartcard, and a server perform the following steps, as illustrated in Figure 4.

Figure 4.
The authenticated key exchange phase of the proposed scheme.
- Step 1.
- User enters and .
- Step 2.
- Smartcard checks , utilizes (, x) to compute , retrieves (, ) to recover , and computes (, ), as below.
- Step 3.
- Smartcard chooses integer and a big prime to compute (, , ) as below, and sends (, , ) to server .
- Step 4.
- After receiving (, , ), server computes the equations below. If server can decrypt successfully, server successfully authenticates user .
- Step 5.
- For establishing a shared session key, server chooses a random number , utilizes , , and retrieved from Step 4 to compute , , and , and sends to user .
- Step 6.
- Upon receiving , user ’s smartcard computes and checks whether is correct. If it holds, the mutually shared session key is correct. Then, user Ui’s smartcard computes and sends it to server .
- Step 7.
- Upon receiving , server checks whether is correct. If it holds, the shared session key confirmation is complete.
3.5. Offline Password Change Phase
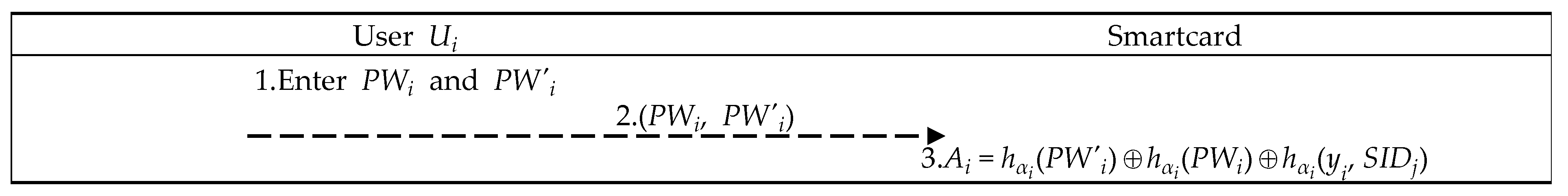
User and smartcard cooperatively perform the following steps to complete the password changing process, as illustrated in Figure 5.

Figure 5.
Offline password change phase of the proposed scheme.
- Step 1.
- User enters PIN to start smartcard and inputs old and new .
- Step 2.
- Smartcard updates and stores it.
4. Security Analysis
We apply BAN logic [52] and AVISPA tool [53] for formal security proof. We also present informal security proof, which proves that the proposed scheme can achieve some security requirements.
4.1. Formal Security Proof Using BAN Logic
This subsection describes the logical analyses of the proposed scheme by using the logical tool defined by Burrows et al. [52]. The process of proof in this section is similar with some schemes, because these schemes, including the proposed scheme, aim to prove that the principles in schemes can believe the established session keys. The notations used in the BAN logic [52] analysis are defined in Table 2.

Table 2.
Notations of BAN logic [52] used in analyzing the proposed scheme.
4.1.1. Initial Assumptions
Making initial assumptions is necessary for ensuring success of scheme and establishing the foundation of logical proof [52]. Initial assumptions of the proposed scheme are listed below.
- A1. : P can read from channel .
- A2. : P believes that P and Q can write on .
- A3. : P believes that Q only says what it believes.
- A4. : P believes that is fresh.
- A5. : P believes that a is P’s extended chaotic maps-based Diffie-Hellman secret [24,49].
4.1.2. Inference Rules
The purpose of inference rules is analyzing belief, which pays attention to beliefs of principals in authentication and key agreement schemes, in order to verify message, freshness, and trustworthiness of origin of scheme [52,54,55,56,57]. We apply the seeing rules, interpretation rules, freshness rules, and the rationality rules for logical proof.
The seeing rules define that if a principle sees a formula, the principle also sees its components with knowing necessary keys. We apply S1 and S2 as below.
- S1. : If P receives and reads X via C, then P believes that X has arrived on C and P sees X.
- S2. : If P sees a hybrid message (X, Y), then P sees X and Y separately.
The interpretation rules define that a principle can believe some hybrid facts by logical reasoning. We apply I1, I2, and I3, as below.
- I1. : If P believes that C can only be written by P and Q, then P believes that if P receives X via C, then Q said X.
- I2. : If P believes that Q said a hybrid message (X, Y), then P believes that Q has said X and Y separately.
- I3. : If P believes that a is P’s extended chaotic maps-based Diffie-Hellman secret and is extended chaotic maps-based Diffie-Hellman component from Q, then P believes that is symmetric key shared between P and Q.
The freshness rules define that if one part of a formula is fresh, the entire formula must be fresh. We apply F1 and F2 as below.
- F1. : If P believes that another Q said X and P also believes that X is fresh, then P believes that Q recently said X.
- F2. : If P believes that a part of a mixed message X is fresh, then it believes that the whole message (X, Y) is fresh.
The rationality rules define that a principle can only believe what it believes. We have R1 as below.
- R1. : If P believes that implies and P believes that is true, then P believes that is true.
4.1.3. Goals
Goals are what schemes must achieve, and goals are required while designing schemes. The goals of the proposed scheme are listed below.
- Goal 1. : User believes that is a symmetric key shared between participants and .
- Goal 2. : Server believes that is a symmetric key shared between participants and .
- Goal 3. : User believes that believes is a symmetric key shared between and .
- Goal 4. : Server believes that believes is a symmetric key shared between and .
4.1.4. Proof
The proposed scheme can be normalized as Steps 1 and 2.
- Step 1.
- Step 2.
Equation (26) means user believes that is its extended chaotic maps-based Diffie-Hellman secret. Equation (27) means user believes that is the extended chaotic maps-based Diffie-Hellman component from server . To accomplish Goal 1 (User believes that is a symmetric key shared between participants user and server ), Equations (25) and (26) must hold, because of the interpretation rule (I3) and assumption (A5).
The meaning of Equation (28) is described below. The first fact is that server once said that (x) mod p is the extended chaotic maps-based Diffie-Hellman public component from server , is encrypted by and . The second fact is that server once said that (x) mod p is the extended chaotic maps-based Diffie-Hellman public component from server . In Equation (29), user believes that the first fact implies the second fact. Equation (28) means that user believes that server once said that is the extended chaotic maps-based Diffie-Hellman public component from server . Next, to accomplish Equation (27), Equations (28) and (29) must hold because of assumption (A3) and the rationality rule (R1).
To accomplish Equation (29), Equation (30) must hold, which means that user believes that , which is that the extended chaotic maps-based Diffie-Hellman public component from server is fresh because of freshness rules (F1) and (F2), and assumption (A4).
Equation (31) means that user can read from the channel . Equation (32) means that user believes that user and server can write messages on channel . Equation (33) means that user Ui sees and believes that is in the channel , which is the extended chaotic maps-based Diffie-Hellman public component from server . To accomplish Equation (30), we have Equations (31)–(33) that must hold because of the interpretation rules (I1), the seeing rules (S1), (S2), assumptions (A1) and (A2). By using the interpretation rules (I3), our proposed scheme realizes that Goal 1 is achieved. Similarly, we ensured that the proposed scheme realizes Goal 2 by using the same arguments of Goal 1.
The meaning of Equation (34) is described below. The first fact is that server once said that is the symmetric key shared between and . The second fact is that server believes that is the symmetric key shared between and . In Equation (35), user believes that the first fact implies the second fact. To accomplish the Goal 3, we have Equations (34) and (35), which must hold because of the rationality rule (R1) and assumption (A3).
Equation (36) means that user believes symmetric key is fresh. To accomplish Equation (35), Equation (36) must hold because of the freshness rules (F1) and (F2) and assumption (A4).
Equation (37) means that user sees and believes that is in the channel . To accomplish Equation (36), Equations (31), (32) and (37) must hold because of the interpretation rule (I1), the assumptions (A1) and (A2), and the seeing rules (S1) and (S2). Thus, the proposed scheme realizes that Goal 3 is achieved. Similarly, using the same arguments of Goal 3, the proposed scheme realizes Goal 4.
Therefore, the proposed scheme realizes Goals 1, 2, 3, and 4.
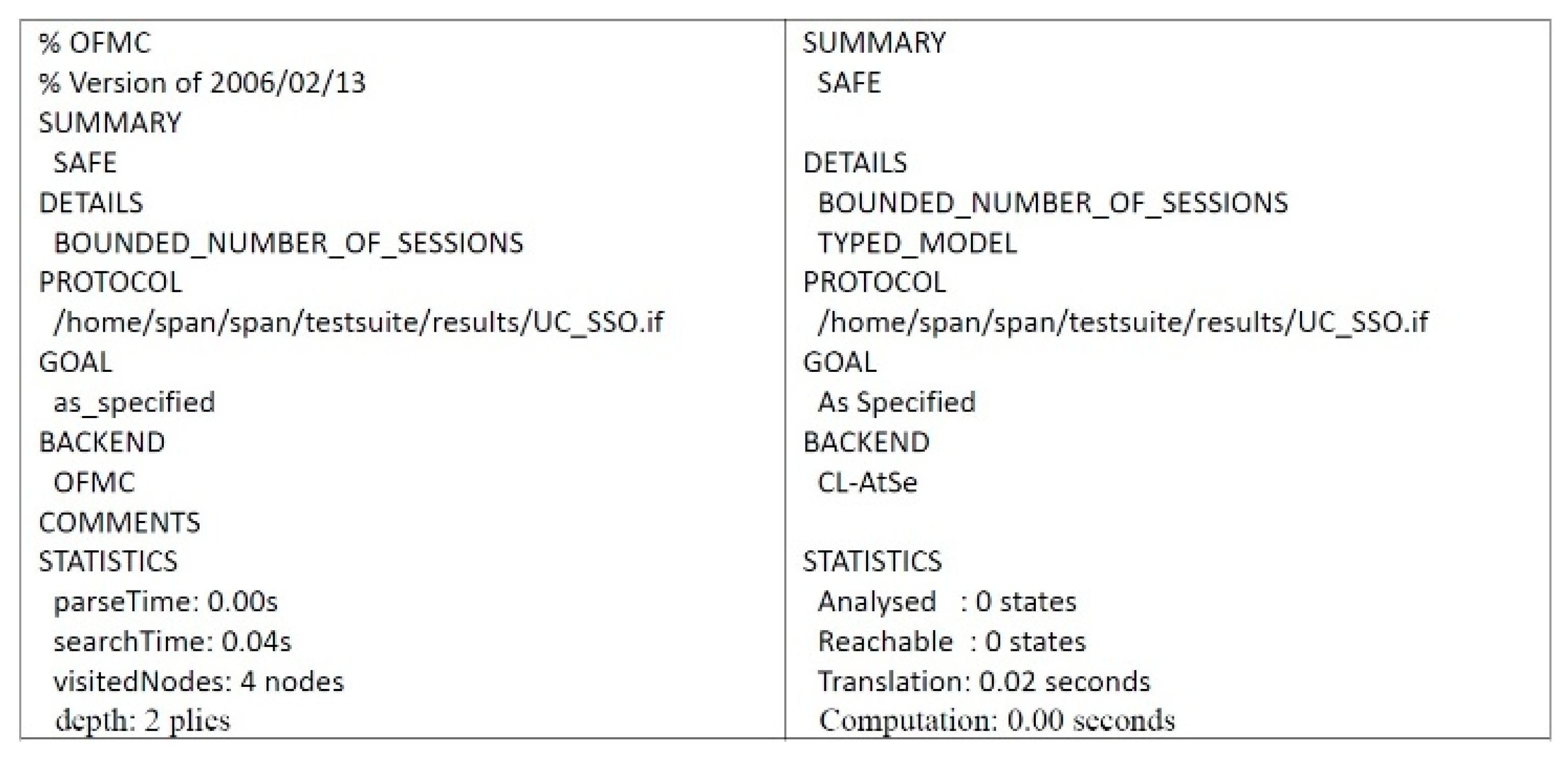
4.2. Formal Security Proof Using AVISPA
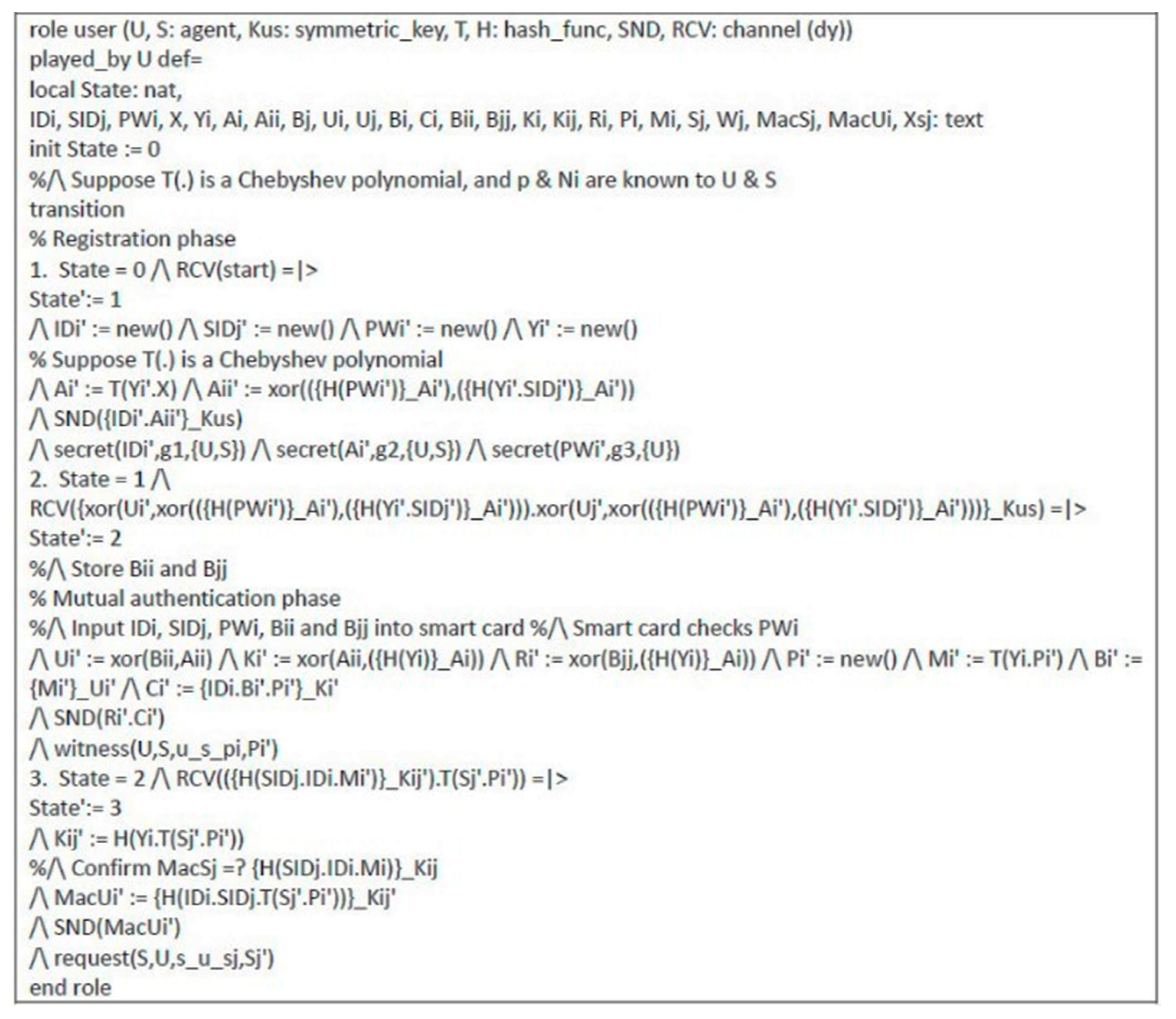
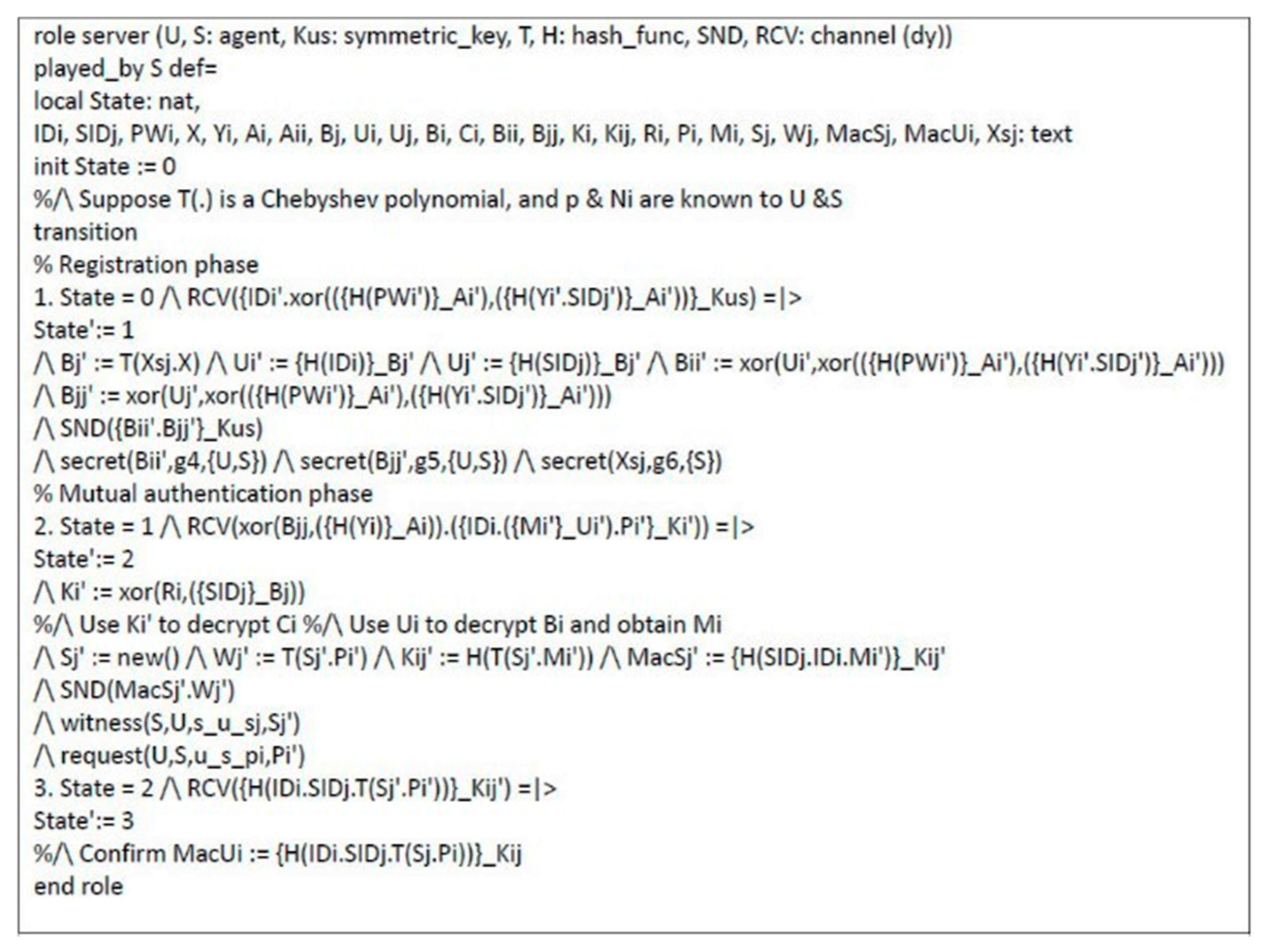
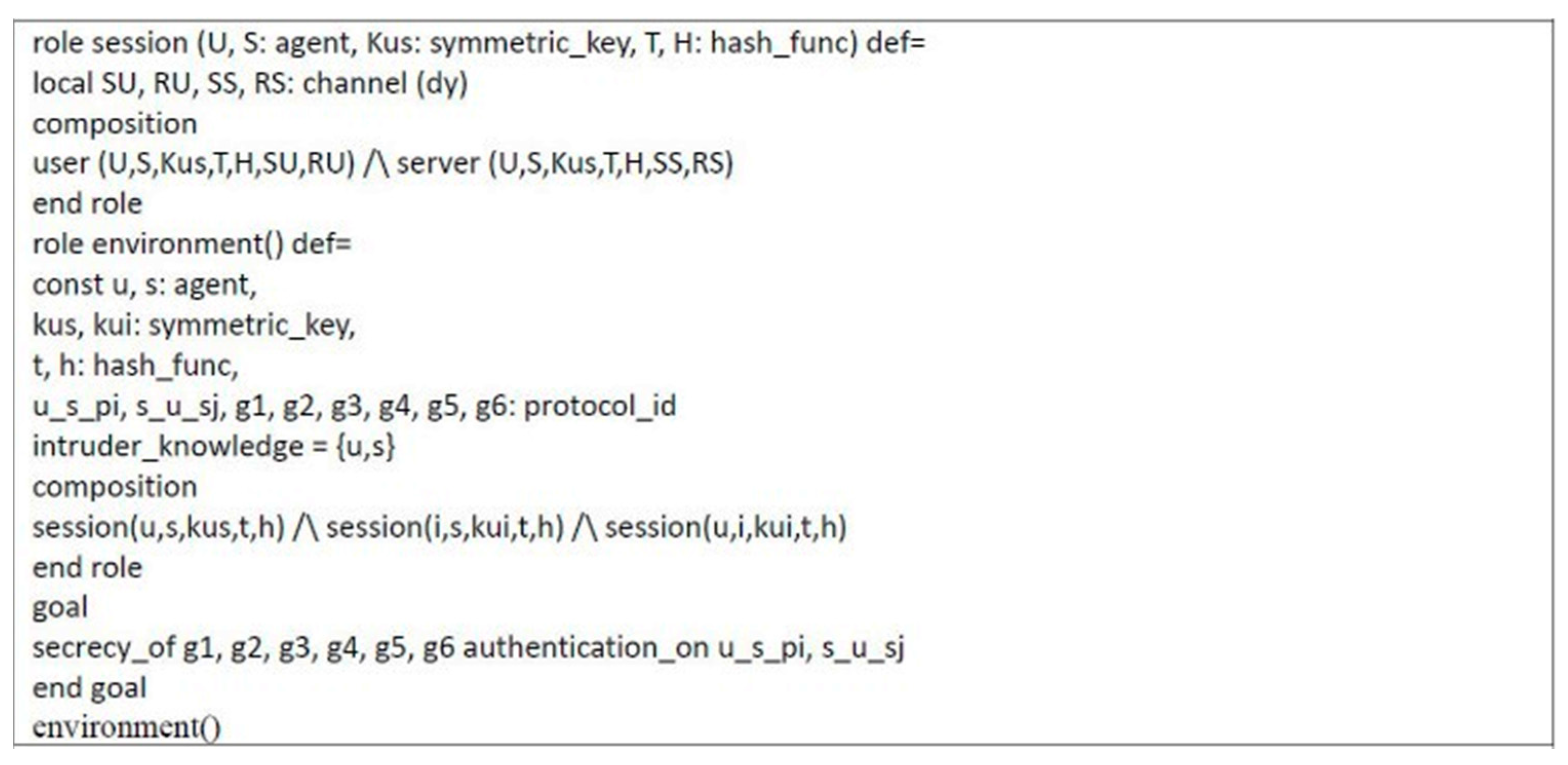
Automated validation of internet security protocols and applications (AVISPA) is a high-level language tool for security protocols, and it provides automatic analysis techniques through its back-ends, called on-the-fly model-checker (OFMC), constraint logic based attack searcher (CL-AtSe), SAT-based model-checker (SATMC), and tree automata based on automatic approximations for the analysis of security protocols (TA4SP) [53,58,59,60]. The AVISPA tool executes a simulated protocol through high-level protocol specification language (HLPSL) [61]. We used the AVISPA tool to verify the proposed scheme. The HLPSL specification of user U and server S are shown in Figure 6 and Figure 7, respectively. The session role, environment role, and goals are also specified in HLPSL, shown in Figure 8. Figure 9 shows the results and proves that the proposed scheme is safe.

Figure 6.
HLPSL specification of user.

Figure 7.
HLPSL specification of server.

Figure 8.
HLPSL specification of session role, environment role, and goals.

Figure 9.
Results of AVISPA.
4.3. Informal Security Proof
We present theoretical analyses that proved that proposed scheme could achieve security requirements.
4.3.1. Preventing MITM Attack
In order to prevent MITM attack, user and server can confirm whether the message is resent, modified, and replaced, by checking information through message authentication codes and . User verifies at Step 6, and server verifies at Step 7 in the authenticated key exchange phase of the proposed scheme. In this way, the adversary cannot modify message authentication codes and without session key .Thus, the proposed scheme can prevent MITM attack.
4.3.2. Key Confirmation
User can check session key by , and server can also check session key through in the proposed scheme. As a result, the proposed scheme achieves key confirmation.
4.3.3. Preventing Key-Compromise Impersonation and Server Spoofing Attacks
User ’s random number is stored in a smartcard, which is hard to obtain information. The adversary must have user ’s smartcard and correct password if they want to impersonate a legitimate user. The number of attempts that a password can be entered is limited; if the number of attempts to enter a password exceeds the allowable number of attempts, the smartcard will get locked. On the other hand, the adversary cannot obtain due to not knowing , and afterwards the process cannot be completed by adversary. As a result, the proposed scheme can prevent key-compromise impersonation and server spoofing attacks.
4.3.4. Mutual Authentication
In the authenticated key exchange phase of the proposed scheme, server encrypts from user to message authentication code with session key and sends to user . In Step 6, user uses from server to obtain session key and verify . Server verifies message authentication code sent by user in Step 7. and are included in session keys that only two parties of communication have, so only user and server can verify each other.
4.3.5. User Anonymity
User ’s identity is protected by being encrypted in with , before being sent. Server must obtain by computing . The adversary cannot obtain even with and because only server has knowledge of secret . The adversary cannot obtain without and decrypting ; thus, the adversary cannot obtain . As a result, the proposed scheme provides user anonymity during communication.
4.3.6. Resistant to Bergamo et al.’s Attack
Bergamo et al.’s attack is based on [62]. (i) The adversary is able to obtain related elements (x, , , ); and (ii) several Chebyshev polynomials pass through the same point due to periodicity of the cosine function. In the proposed scheme, the adversary is unable to obtain any related elements (x, , , ) as these are encrypted in transmitted messages where only user and server can retrieve decryption key. Moreover, the proposed protocol utilizes the extended Chebyshev polynomials, in which the periodicity of the cosine function is avoided by extending the interval of x to [51]. As a result, the proposed scheme can resist the attack proposed by Bergamo et al. [62].
5. Performance Analysis
We present relevant security requirements and computational complexity comparison.
5.1. Comparisons of Security Requirements
Table 3 shows comparisons of security requirements that were presented in the schemes designed by Wang and Zhao [63], Yoon and Jeon [46], Lin [48], Lin and Zhu [64], Lee et al. [49], Madhusudhan et al. [65], Sureshkumar et al. [38], and us. Wang and Zhao’s [63], Lin’s [48], and Lin and Zhu’s schemes [64] are not secure against key-compromise impersonation attack, since the transmitted messages can be replayed by an adversary. Wang and Zhao’s [63], Madhusudhan et al.’s [65], and Sureshkumar et al.’s [38] scheme cannot prevent server spoofing attack. Our scheme is secure against both key-compromise impersonation attack and server spoofing attack. Furthermore, our scheme provides user anonymity, which Wang and Zhao’s [63], Yoon and Jeon’s [46], and Madhusudhan et al.’s [65] scheme do not. Our scheme can also prevent MITM attack, which Wang and Zhao’s [63], Yoon and Jeon’s [46], and Madhusudhan et al.’s [65] scheme cannot. Furthermore, our scheme ensures that users and servers use the same shared key in a session via key confirmation, which is not present in Wang and Zhao’s [63], Yoon and Jeon’s [46], Lin’s [48], Lin and Zhu’s [64], Lee et al.’s [49], Madhusudhan et al.’s [65], and Sureshkumar et al.’s [38] scheme. Moreover, our scheme can prevent DoS attacks, which Wang and Zhao’s [63], Yoon and Jeon’s [46], Lin’s [48], and Madhusudhan et al.’s [65] scheme cannot.

Table 3.
Comparisons of Security Requirements.
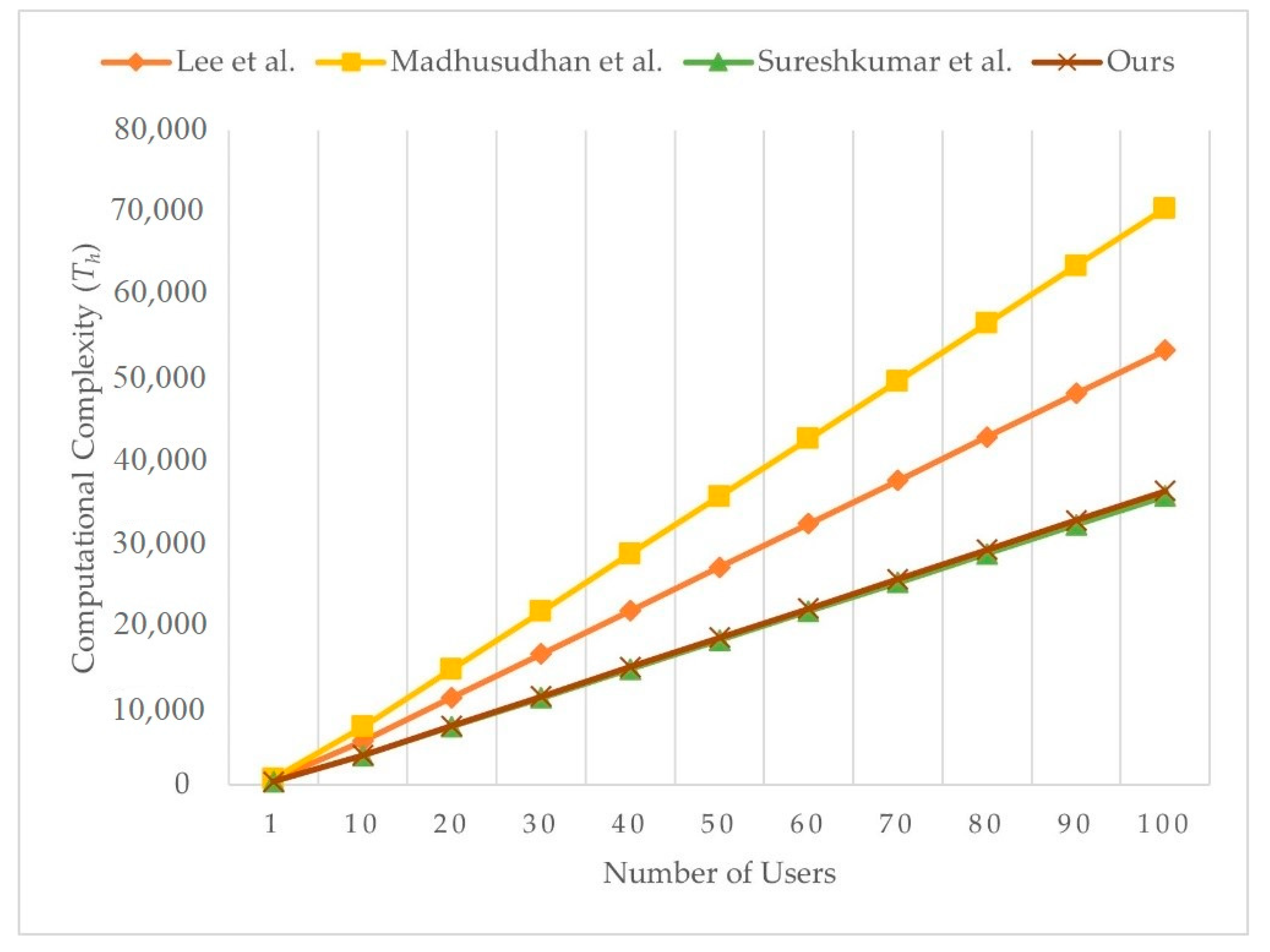
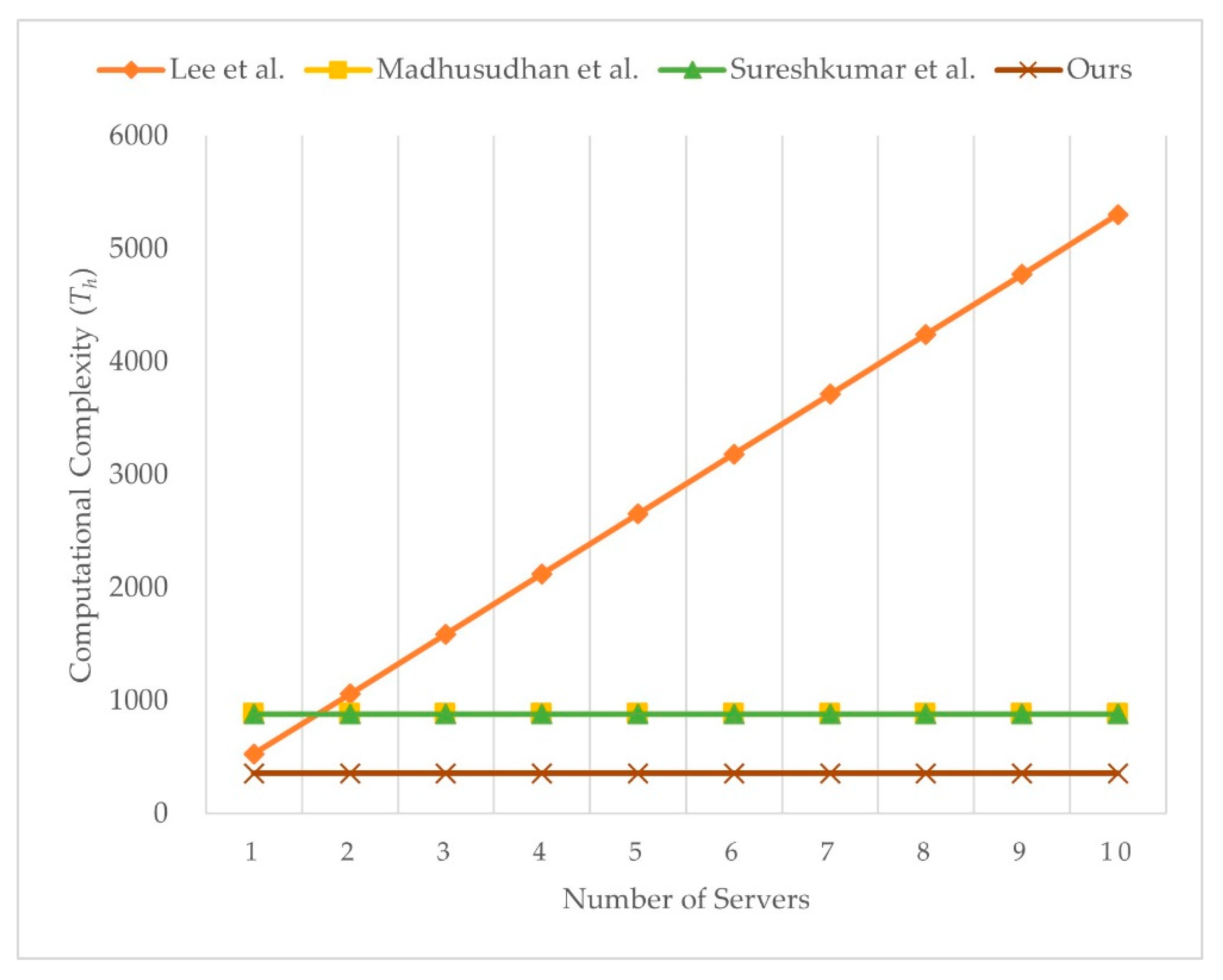
5.2. Comparisons of Computational Complexity
We present the computational complexity comparison with Lee et al.’s [49], Madhusudhan et al.’s [65], and Sureshkumar et al.’s [38] scheme, as shown in Table 4. We ignore the time taken for computing XOR operations because the value is too low to influence result. Although our scheme needs more one-way hash function operations than Lee et al.’s [49] scheme and more symmetry encryption operations than Lee et al.’s [49], Madhusudhan et al.’s [65], and Sureshkumar et al.’s [38] scheme, our scheme allows key confirmation. Even so, our scheme has the less overall computational cost than Lee et al.’s [49], Madhusudhan et al.’s [65], and Sureshkumar et al.’s [38] scheme. Users in our scheme can enjoy telemedicine services witha lower computational cost. As a result, our scheme is more efficient than Lee et al.’s [49], Madhusudhan et al.’s [65], and Sureshkumar et al.’s [38]. Figure 10 illustrates the computational complexity of the server with varying number of users, and Figure 11 illustrates the computational complexity of user with varying number of servers. The computational complexity of user in Lee et al.’s scheme [49] is related to the number of servers. Computational complexity of user in Madhusudhan et al.’s [65], Sureshkumar et al.’s [38], and the proposed scheme is not related to number of servers, and the proposed scheme shows the least computational complexity among the compared schemes.

Table 4.
Comparisons of Computational Complexity.

Figure 10.
Computational complexity of server with varying number of users.

Figure 11.
Computational complexity of user with varying number of servers.
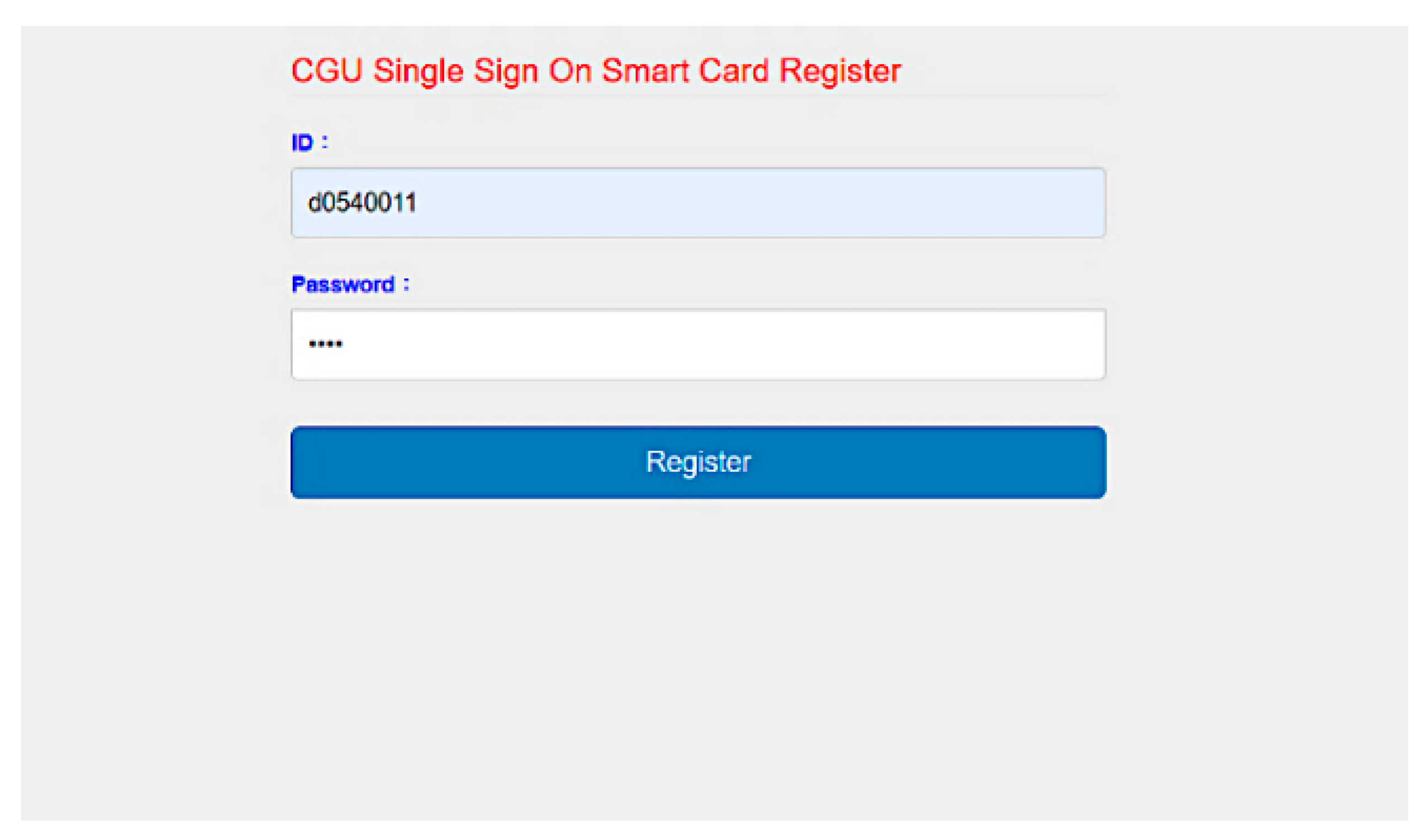
6. Implementation
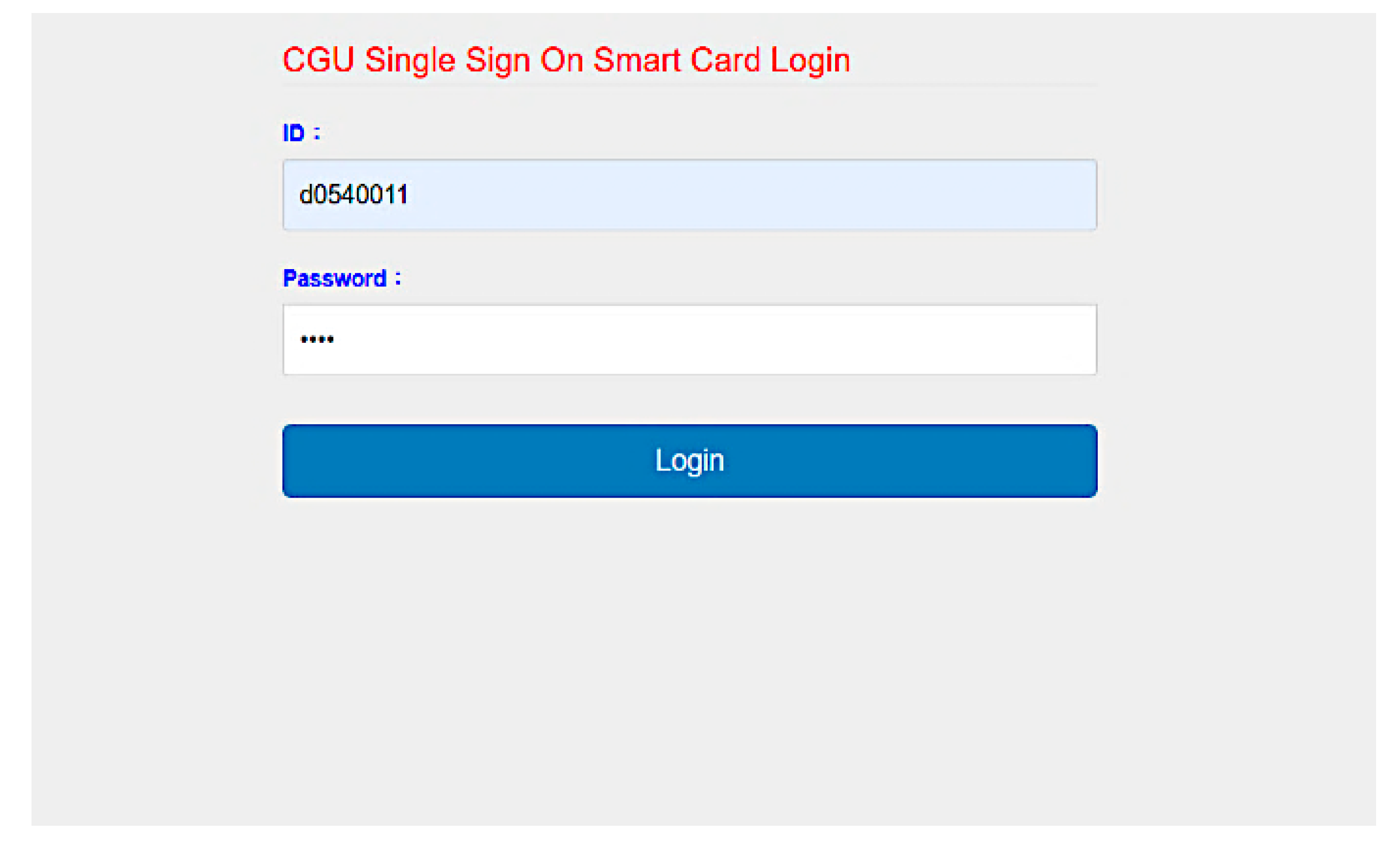
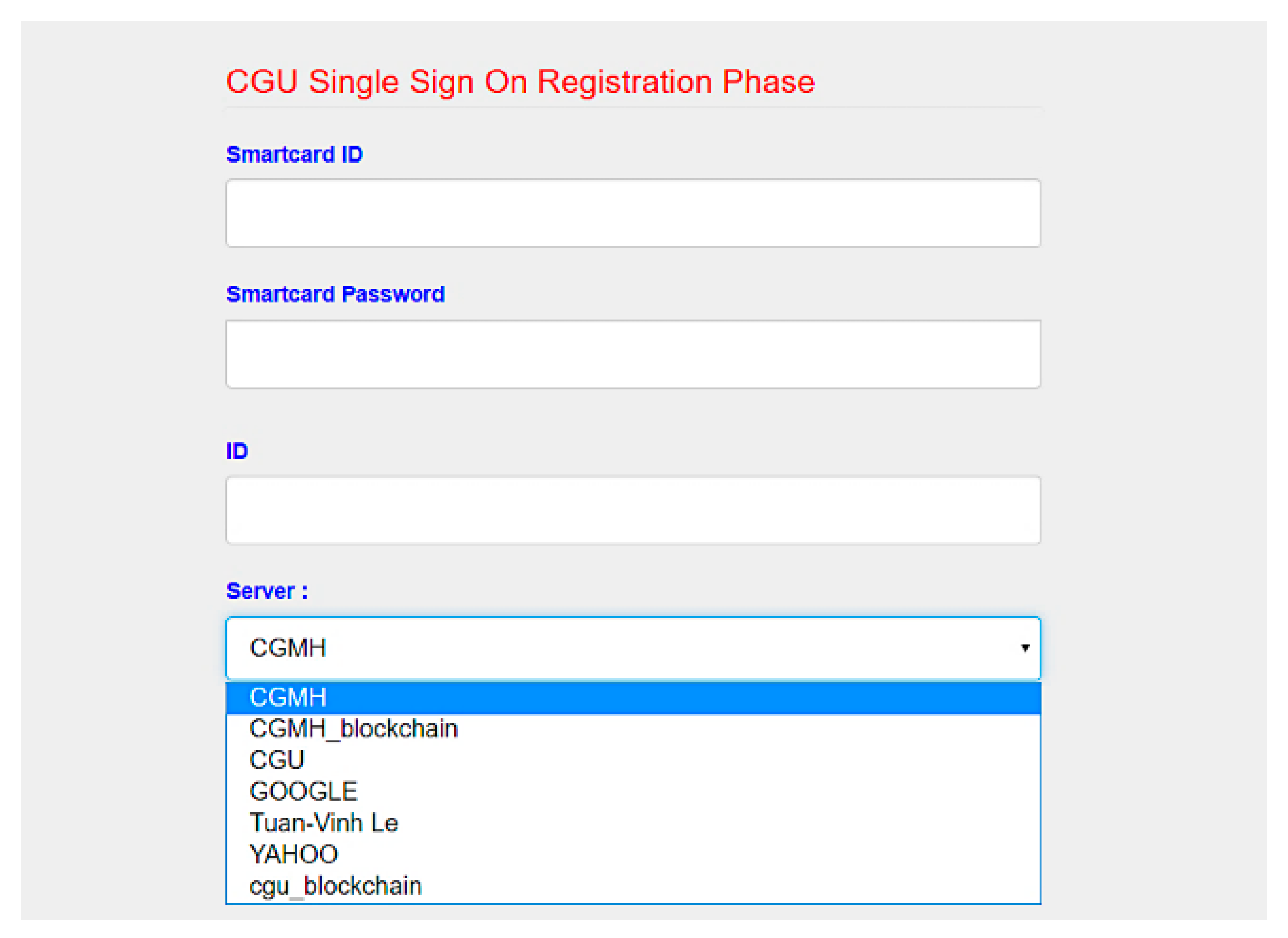
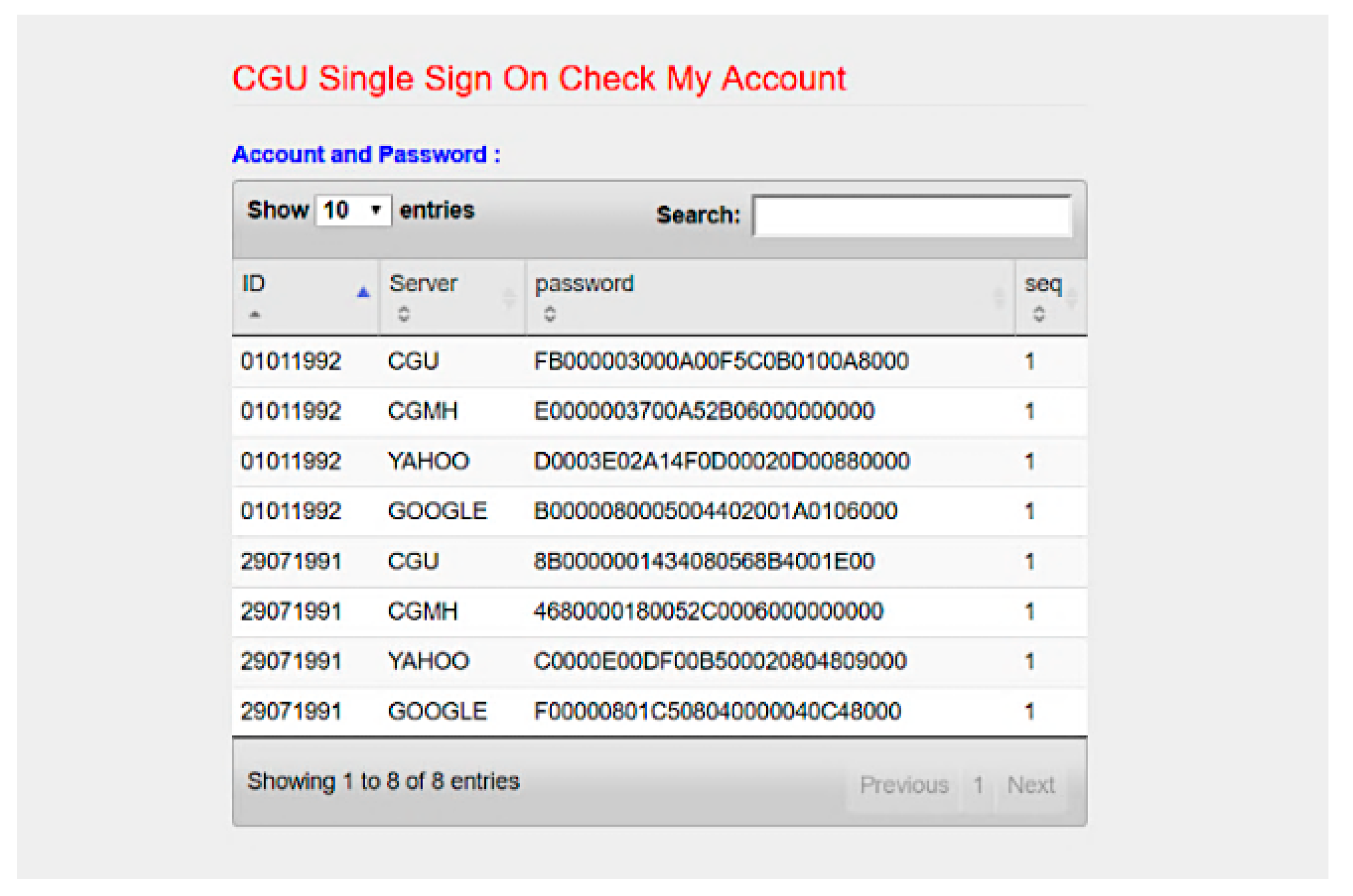
We developed SC-UCSSO system using the proposed scheme, in a multi-function smart token, as shown in Figure 12, which supports the public key infrastructure and the X.509 certificate. A user can insert a smart token to a computer or a laptop and insert the smartcard shown in Figure 13 into a smart token, in order to use the system. Figure 14 and Figure 15 show the registration and login interfaces. Figure 16 shows that the user can login to multiple services, which implies that the proposed system can be used in multi-server environments. The proposed system also provides account checking (Figure 17) to manage the user’s accounts. The user can login to the online telemedicine website using a computer, laptop, smartphone, or any wireless devices that has a webcam with a smart token and a smartcard in synchronous telemedicine scenario. The channel of online video consult between the patient and medical professional is protected by the session key generated by the proposed scheme. In asynchronous telemedicine, the measured biodata is transmitted to a smartphone using Bluetooth, and the user can decide when to send data to the designed server of telemedicine systems. The user logins with smart token and smartcard, before sending data. Transmitted measured data between smartphone and servers would be protected by the session key generated through the proposed scheme. The user has data ownership because the user can control data’s destination and the time of being transmitted. Once data are sent by user, the privacy of user would be protected because the transmission channel is secure with the session key.

Figure 12.
Multi-function smart token.

Figure 13.
Smartcard.

Figure 14.
Interface of registration.

Figure 15.
Interface of login.

Figure 16.
Interface of choosing services.

Figure 17.
Interface of account checking.
7. Discussion
We give a discussion for brief review, real-life scenario, and limitations of this research.
Telemedicine systems work in public networks, where privacy preservation issue of users and sensitive and private transmitted information is important [1]. Security issues related to data transmission are discussed, such as eavesdropping, MITM attack, data tempering attack, message modification attack, data interception attack, etc. [12] Although regulations, such as HIPAA, GDPR, Safe Harbor Laws, etc., were developed, technical support is still not enough [12,13,14]. We proposed an SC-UCSSO for the 5G-IoT telemedicine systems, which can be applied in the 5G-IoT telemedicine multi-server environments. Security of the proposed scheme was proved by BAN logic, AVISPA tool, and theoretical analyses. The proposed scheme achieved general security requirements, such as preventing MITM attack, preventing key-compromise impersonation, and server spoofing attacks, and user anonymity, key confirmation, and mutual authentication. Moreover, the proposed scheme overcomes the drawbacks of the compared previous schemes, such as stolen-verification table attack, clock synchronization problem, and DoS attack, as shown in Table 3 in the previous section. The proposed scheme applies the extended Chebychev chaotic maps that can resist Bergamo et al.’s attack [62]. Performance of the proposed scheme is also compared with Lee et al.’s [49], Madhusudhan et al.’s [65], and Sureshkumar et al.’s [38] scheme by analyzing the computational complexity of each scheme, and the results showed that the proposed scheme was less expensive (719) in total than Lee et al.’s [49] (), Madhusudhan et al.’s [65] (1588), and Sureshkumar et al.’s [38] scheme (1235), as shown in Table 4.
We give four possible real-life scenarios of telemedicine systems in 5G-IoT environments that can apply the proposed scheme.
- Scenario 1:
- Patient inserts smartcard (e.g., health insurance card or smartcard, as in Figure 13) into measurement devices that include a smartcard reader, such as sphygmomanometer or blood-glucose meter, before measuring biodata. Once a patient inserts smartcard, the authenticated key agreement phase of the proposed scheme is activated, and measured biodata can be transmitted securely to server as it is encrypted by the session key.
- Scenario 2:
- Patient’s wearable healthcare device (e.g., sensors, smart watch, etc.) transmits the measured biodata to the related mobile application (APP) on a smartphone, through data synchronization via Bluetooth, NFC, RFID, etc. If the patient wants to transmit the measured biodata to server, the patient can use a smartphone with a smartcard adopter, such as the smart token in Figure 13. Once a patient inserts the smartcard, the authenticated key agreement phase of proposed scheme is activated, and the measured biodata can be securely transmitted to server as it is encrypted by the session key.
- Scenario 3:
- Patient’s measured biodata are recorded or stored in storage at home. If the patient wants to transmit the measured biodata to server, the patient can use the smartcard with a reader. Once a patient inserts the smartcard, the authenticated key agreement phase of proposed scheme is activated, and the measured biodata can be transmitted securely to server as it is encrypted by the session key.
- Scenario 4:
- If a medical professional would like to access the measured biodata on server, the medical professional has to use the smartcard (e.g., healthcare certification IC card [66]) with a reader. Once a medical professional inserts smartcard, the authenticated key agreement phase of proposed scheme is activated, and the measured biodata can be securely transmitted as it is encrypted by the session key.
Scenario 1 to 3 allow the patient to decide the data’s destination and time of transmission.
This research has limitations. We only give a software security analysis, but hardware security and availability are other aspects of security in telemedicine systems, such as electromagnetic interference (EMI), which might affect the functions on wearable devices. Although there are already measurement devices with a smartcard reader on the market, we did not evaluate the hardware’s effects with the proposed scheme. We assumed that the users (patient/medical professional) have a smartcard (health insurance card/ healthcare certification IC card) and proposed a smartcard-based scheme, but authentication could be achieved in many ways, such as three-factor authentication, two-step verification, fast identity online (FIDO), etc., which can be related to works in the future.
8. Conclusions
Telemedicine systems is a multi-functional remote medical service that can help patients in bed in long-distance communication environments [1,2,3,4]. As telemedicine systems work in public networks, privacy preservation issue of sensitive and private transmitted information is important. [1]. We proposed a SC-UCSSO for 5G-IoT telemedicine systems, which could achieve some general security requirements, such as preventing MITM attack, preventing key-compromise impersonation and server spoofing attacks, provide user anonymity, and overcomes the drawbacks of the previous schemes compared herein. The proposed scheme establishes a secure communication channel using the authenticated session keys between patients and services of telemedicine systems, without threats of eavesdrop, impersonation, etc., and allow patient access to multiple telemedicine services, with a pair of identity and password. Formal security analysis using BAN logic [52] and the AVISPA tool [67] was given. We also gave a performance analysis and proved that the proposed scheme is more efficient than previous compared schemes, and computational complexity of the user in proposed scheme was not related to the number of servers. Moreover, the proposed scheme is suitable for asynchronous and synchronous telemedicine, and patients have data ownership because the user can control and decide data’s destination and time of transmission.
Author Contributions
Conceptualization, T.-W.L. and C.-L.H.; methodology, T.-W.L.; formal analysis, T.-W.L. and T.-V.L.; informal analysis, T.-W.L.; software implementation, B.-Y.H.; writing—original draft preparation, T.-W.L.; writing—review and editing, C.-L.H. and C.-F.L.; supervision, C.-L.H.; funding acquisition, C.-L.H. All authors have read and agreed to the published version of the manuscript.
Funding
This research was funded by Ministry of Science and Technology, Taiwan, grant number MOST107-2221-E-182-006 and MOST 108-2221-E-182-011, Healthy Aging Research Center, Chang Gung University, Taiwan, grant number EMRPD1K0461 and EMRPD1I0481, and Chang Gung University, Taiwan, grant number PARPD3K0011 and SCRPD3H0011.
Institutional Review Board Statement
Not applicable.
Informed Consent Statement
Not applicable.
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Garai, Á.; Péntek, I.; Adamkó, A. Revolutionizing Healthcare with IoT and Cognitive, Cloud-Based Telemedicine. Acta Polytech. Hung. 2019, 16, 163–181. [Google Scholar] [CrossRef]
- Fong, B.; Fong, A.C.M.; Li, C.K. Telemedicine Technologies: Information Technologies in Medicine and Telehealth; John Wiley and Sons: New York, NY, USA, 2010. [Google Scholar] [CrossRef]
- Ryu, S. History of Telemedicine: Evolution, Context, and Transformation. Healthc. Inform. Res. 2010, 16, 65–66. [Google Scholar] [CrossRef]
- Abderrahim, A.; Ibtissam, F.; Habiba, C.; Hicham, E.A.; Nabil, H. AES-PRESENT: A New Secure Iot-Based Scheme for Telemedicine and E-Health Systems. ARPN J. Eng. Appl. Sci. 2018, 13, 9554–9559. [Google Scholar]
- Fan, Y.J.; Yin, Y.H.; Xu, L.D.; Zeng, Y.; Wu, F. IoT-Based Smart Rehabilitation System. IEEE Trans. Ind. Inform. 2014, 10, 1568–1577. [Google Scholar] [CrossRef]
- Pasluosta, C.F.; Gassner, H.; Winkler, J.; Klucken, J.; Eskofier, B.M. An Emerging Era in the Management of Parkinson’s Disease: Wearable Technologies and the Internet of Things. IEEE J. Biomed. Health Inform. 2015, 19, 1873–1881. [Google Scholar] [CrossRef] [PubMed]
- Chang, S.; Chiang, R.; Wu, S.; Chang, W. A Context-Aware, Interactive M-Health System for Diabetics. IT Prof. 2016, 18, 14–22. [Google Scholar] [CrossRef]
- Baker, S.B.; Xiang, W.; Atkinson, I. Internet of Things for Smart Healthcare: Technologies, Challenges, and Opportunities. IEEE Access 2017, 5, 26521–26544. [Google Scholar] [CrossRef]
- Sarkar, S.; Misra, S. From Micro to Nano: The Evolution of Wireless Sensor-Based Health Care. IEEE Pulse 2016, 7, 21–25. [Google Scholar] [CrossRef]
- Yin, Y.; Zeng, Y.; Chen, X.; Fan, Y. The Internet of Things in Healthcare: An Overview. J. Ind. Infor. Integr. 2016, 1, 3–13. [Google Scholar] [CrossRef]
- Anwar, S.; Prasad, R. Framework for Future Telemedicine Planning and Infrastructure Using 5G Technology. Wirel. Pers. Commun. 2018, 100, 193–208. [Google Scholar] [CrossRef]
- Zriqat, I.a.A.; Altamimi, A.M. Security and Privacy Issues in Ehealthcare Systems: Towards Trusted Services. Int. J. Adv. Comput. Sci. Appl. 2016, 7, 229–236. [Google Scholar]
- The 104th United States Congress, Health Insurance Portability and Accountability Act of 1996. Public Law 104-191. United States Statut. Large. 1996, 110, 1936–2103. Available online: https://pubmed.ncbi.nlm.nih.gov/16477734/ (accessed on 19 April 2021).
- Note on Proposal for a Regulation of the European Parliament and of the Council on the Protection of Individuals with Regard to the Processing of Personal Data and on the Free Movement of Such Data (General Data Protection Regulation): 2012/0011 (Cod). Council of the European Union. 2013. Available online: https://lobbyplag.eu/governments/assets/pdf/CD-16140_14-C1.pdf (accessed on 20 April 2021).
- Lee, T.F. Provably Secure Anonymous Single-Sign-on Authentication Mechanisms Using Extended Chebyshev Chaotic Maps for Distributed Computer Networks. IEEE Syst. J. 2018, 12, 1499–1505. [Google Scholar] [CrossRef]
- Liu, X.; Liu, J.; Wang, W.; Zhu, S. Android Single Sign-on Security: Issues, Taxonomy and Directions. Future Gener. Comput. Syst. 2018, 89, 402–420. [Google Scholar] [CrossRef]
- Zakaria, N.H.; Zainul, M.F.; Katuk, N.; Tahir, H.M.; Omar, M.N. An Evaluation of Page Token in Openid Single Sign on (SSO) to Thwart Phishing Attack. J. Telecommun. Elect. Comput. Eng. 2018, 10, 19–23. [Google Scholar]
- Marciniak, R. Role of New It Solutions in the Future of Shared Service Model. Pollack Period. 2013, 8, 187–194. [Google Scholar] [CrossRef]
- National Health Service. The NHS Long Term Plan. National Health Service. Available online: https://www.longtermplan.nhs.uk/wp-content/uploads/2019/08/nhs-long-term-plan-version-1.2.pdf (accessed on 8 April 2021).
- Philip, N.Y.; Rodrigues, J.J.P.C.; Wang, H.; Fong, S.J.; Chen, J. Internet of Things for in-Home Health Monitoring Systems: Current Advances, Challenges and Future Directions. IEEE J. Sel. Areas Commun. 2021, 39, 300–310. [Google Scholar] [CrossRef]
- Pramanik, P.K.D.; Pareek, G.; Nayyar, A. Security and Privacy in Remote Healthcare: Issues, Solutions, and Standards. In Telemedicine Technologies: Big Data, Deep Learning, Robotics, Mobile and Remote Applications for Global Healthcare; Elsevier: Amsterdam, The Netherlands, 2019; pp. 201–225. [Google Scholar] [CrossRef]
- Devaraj, S.J. Emerging Paradigms in Transform-Based Medical Image Compression for Telemedicine Environment. In Telemedicine Technologies: Big Data, Deep Learning, Robotics, Mobile and Remote Applications for Global Healthcare; Academic Press: Cambridge, MA, USA, 2019; pp. 15–29. [Google Scholar] [CrossRef]
- Rao, K. The Path to 5G for Health Care. Available online: https://futurenetworks.ieee.org/images/files/pdf/applications/5G--Health-Care030518.pdf (accessed on 8 April 2021).
- Lin, T.W.; Hsu, C.L. FAIDM for Medical Privacy Protection in 5G Telemedicine Systems. Appl. Sci. 2021, 11, 1155. [Google Scholar] [CrossRef]
- Fan, K.; Jiang, W.; Li, H.; Yang, Y. Lightweight RFID Protocol for Medical Privacy Protection in IoT. IEEE Trans. Ind. Inform. 2018, 14, 1656–1665. [Google Scholar] [CrossRef]
- Fortino, G.; Fotia, L.; Messina, F.; Rosaci, D.; Sarné, G.M.L. Trust and Reputation in the Internet of Things: State-of-the-Art and Research Challenges. IEEE Access 2020, 8, 60117–60125. [Google Scholar] [CrossRef]
- Gambetta, D. Can We Trust Trust? In Trust: Making and Breaking Cooperative Relations; Gambetta, D., Ed.; Blackwell: Oxford, UK, 1988; pp. 213–237. [Google Scholar]
- Yan, Z.; Zhang, P.; Vasilakos, A.V. A Survey on Trust Management for Internet of Things. J. Netw. Comput. Appl. 2014, 42, 120–134. [Google Scholar] [CrossRef]
- Sharma, A.; Pilli, E.S.; Mazumdar, A.P.; Gera, P. Towards Trustworthy Internet of Things: A Survey on Trust Management Applications and Schemes. Comput. Commun. 2020, 160, 475–493. [Google Scholar] [CrossRef]
- Ud Din, I.; Guizani, M.; Kim, B.S.; Hassan, S.; Khan, M.K. Trust Management Techniques for the Internet of Things: A Survey. IEEE Access 2019, 7, 29763–29787. [Google Scholar] [CrossRef]
- Guo, J.; Chen, I.R.; Tsai, J.J.P. A Survey of Trust Computation Models for Service Management in Internet of Things Systems. Comput. Commun. 2017, 97, 1–14. [Google Scholar] [CrossRef]
- Abdelghani, W.; Zayani, C.A.; Amous, I.; Sèdes, F. Trust Management in Social Internet of Things: A Survey. In Lecture Notes in Computer Science (Including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); Springer: Berlin, Germany, 2016; Volume 9844, pp. 430–441. [Google Scholar]
- Mishra, D.; Mukhopadhyay, S.; Kumari, S.; Khan, M.K.; Chaturvedi, A. Security Enhancement of a Biometric Based Authentication Scheme for Telecare Medicine Information Systems with Nonce. J. Med. Syst. 2014, 38, 41. [Google Scholar] [CrossRef]
- Renuka, K.; Kumari, S.; Li, X. Design of a Secure Three-Factor Authentication Scheme for Smart Healthcare. J. Med. Syst. 2019, 43, 133. [Google Scholar] [CrossRef]
- Dharminder, D.; Mishra, D.; Li, X. Construction of RSA-Based Authentication Scheme in Authorized Access to Healthcare Services: Authorized Access to Healthcare Services. J. Med. Syst. 2020, 44, 6. [Google Scholar] [CrossRef]
- Zhang, L.; Luo, H.; Zhao, L.; Zhang, Y. Privacy Protection for Point-of-Care Using Chaotic Maps-Based Authentication and Key Agreement. J. Med. Syst. 2018, 42, 250. [Google Scholar] [CrossRef] [PubMed]
- Zhang, Q.; Zhang, Q.; Gan, Y.; Wang, R.; Tan, Y.A. A Dynamic and Cross-Domain Authentication Asymmetric Group Key Agreement in Telemedicine Application. IEEE Access 2018, 6, 24064–24074. [Google Scholar] [CrossRef]
- Sureshkumar, V.; Amin, R.; Obaidat, M.S.; Karthikeyan, I. An Enhanced Mutual Authentication and Key Establishment Protocol for TMIS Using Chaotic Map. J. Inf. Secur. Appl. 2020, 53, 102539. [Google Scholar] [CrossRef]
- Guo, R.; Shi, H.; Zheng, D.; Jing, C.; Zhuang, C.; Wang, Z. Flexible and Efficient Blockchain-Based ABE Scheme with Multi-Authority for Medical on Demand in Telemedicine System. IEEE Access 2019, 7, 88012–88025. [Google Scholar] [CrossRef]
- Kocarev, L. Chaos-Based Cryptography: A Brief Overview. IEEE Circuits Syst. Mag. 2001, 1, 6–21. [Google Scholar] [CrossRef]
- Kocarev, L.; Lian, S. Chaos-Based Cryptography—Theory, Algorithms and Applications; Springer: Berlin, Germany, 2011; Volume 354. [Google Scholar]
- Solev, D.; Janjic, P.; Kocarev, L. Introduction to Chaos. In Studies in Computational Intelligence; Springer: Berlin, Germany, 2011; Volume 354, pp. 1–25. [Google Scholar]
- Dachselt, F.; Schwarz, W. Chaos and Cryptography. IEEE Trans. Circuits Syst. I Fundam. Theory Appl. 2001, 48, 1498–1509. [Google Scholar] [CrossRef]
- Kocarev, L.; Tasev, Z. Public-Key Encryption Based on Chebyshev Maps. In Proceedings of the 2003 International Symposium on Circuits and Systems, Bangkok, Thailand, 25–28 May 2003; pp. III28–III31. [Google Scholar]
- Mishkovski, I.; Kocarev, L. Chaos-Based Public-Key Cryptography. In Studies in Computational Intelligence; Springer: Berlin, Germany, 2011; Volume 354, pp. 27–65. [Google Scholar]
- Yoon, E.J.; Jeon, I.S. An Efficient and Secure Diffie–Hellman Key Agreement Protocol Based on Chebyshev Chaotic Map. Commun. Nonlinear Sci. Numer. Simul. 2011, 16, 2383–2389. [Google Scholar] [CrossRef]
- Yoon, E.J.; Yoo, K.Y. Cryptanalysis of Group Key Agreement Protocol Based on Chaotic Hash Function. IEICE Trans. Inf. Syst. 2011, E94-D, 2167–2170. [Google Scholar] [CrossRef]
- Lin, H.Y. Improved Chaotic Maps-Based Password-Authenticated Key Agreement Using Smart Cards. Commun. Nonlinear Sci. Numer. Simul. 2015, 20, 482–488. [Google Scholar] [CrossRef]
- Lee, T.F.; Hsiao, C.H.; Hwang, S.H.; Lin, T.H. Enhanced Smartcard-Based Password-Authenticated Key Agreement Using Extended Chaotic Maps. PLoS ONE 2017, 12, e0181744. [Google Scholar] [CrossRef]
- Lin, T.W.; Hsu, C.L. Anonymous Group Key Agreement Protocol for Multi-Server and Mobile Environments Based on Chebyshev Chaotic Maps. J. Supercomput. 2018, 74, 4521–4541. [Google Scholar] [CrossRef]
- Zhang, L. Cryptanalysis of the Public Key Encryption Based on Multiple Chaotic Systems. Chaos Solitons Fractals 2008, 37, 669–674. [Google Scholar] [CrossRef]
- Burrows, M.; Abadi, M.; Needham, R. A Logic of Authentication. ACM Trans. Comput. Syst. (TOCS) 1990, 8, 18–36. [Google Scholar] [CrossRef]
- Mishkovski, I.; Kocarev, L. Chaos-Based Public-Key Cryptography. In Chaos-Based Cryptography: Theory, Algorithms and Applications; Kocarev, L., Lian, S., Eds.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 27–65. [Google Scholar] [CrossRef]
- Amin, R.; Islam, S.H.; Biswas, G.P.; Khan, M.K.; Kumar, N. A Robust and Anonymous Patient Monitoring System Using Wireless Medical Sensor Networks. Future Gener. Comput. Syst. 2018, 80, 483–495. [Google Scholar] [CrossRef]
- Han, L.; Tan, X.; Wang, S.; Liang, X. An Efficient and Secure Three-Factor Based Authenticated Key Exchange Scheme Using Elliptic Curve Cryptosystems. Peer-to-Peer Netw. Appl. 2018, 11, 63–73. [Google Scholar] [CrossRef]
- Liu, B.; Yang, B.; Su, X. An Improved Two-Way Security Authentication Protocol for RFID System. Information 2018, 9, 86. [Google Scholar] [CrossRef]
- Tan, Z. Secure Delegation-Based Authentication for Telecare Medicine Information Systems. IEEE Access 2018, 6, 26091–26110. [Google Scholar] [CrossRef]
- Armando, A.; Basin, D.; Boichut, Y.; Chevalier, Y.; Compagna, L.; Cuellar, J.; Drielsma, P.H.; Heám, P.C.; Kouchnarenko, O.; Mantovani, J.; et al. The AVISPA Tool for the Automated Validation of Internet Security Protocols and Applications. In Proceedings of the Lecture Notes in Computer Science, Edinburgh, UK, 6–10 July 2005; pp. 281–285. [Google Scholar]
- Sutrala, A.K.; Das, A.K.; Kumar, N.; Reddy, A.G.; Vasilakos, A.V.; Rodrigues, J.J.P.C. On the Design of Secure User Authenticated Key Management Scheme for Multigateway-Based Wireless Sensor Networks Using ECC. Int. J. Commun. Syst. 2018, 31, e3514. [Google Scholar] [CrossRef]
- Alshahrani, M.; Traore, I. Secure Mutual Authentication and Automated Access Control for IoT Smart Home Using Cumulative Keyed-Hash Chain. J. Inf. Secur. Appl. 2019, 45, 156–175. [Google Scholar] [CrossRef]
- Oheimb, D.v. The High-Level Protocol Specification Language HLPSL Developed in the EU Project AVISPA. In Proceedings of the APPSEM 2005 Workshop, Frauenchiemsee, Germany, 12–15 September 2005. [Google Scholar]
- Bergamo, P.; D’Arco, P.; De Santis, A.; Kocarev, L. Security of Public-Key Cryptosystems Based on Chebyshev Polynomials. IEEE Trans. Circuits Syst. I Regul. Papers 2005, 52, 1382–1393. [Google Scholar] [CrossRef]
- Wang, X.; Zhao, J. An Improved Key Agreement Protocol Based on Chaos. Commun. Nonlinear Sci. Numer. Simul. 2010, 15, 4052–4057. [Google Scholar] [CrossRef]
- Lin, N.; Zhu, H.F. Enhancing the Security of Chaotic Maps-Based Password-Authenticated Key Agreement Using Smart Card. J. Inf. Hiding Multimed. Signal Process. 2017, 8, 1273–1282. [Google Scholar]
- Madhusudhan, R.; Nayak, C.S. A Robust Authentication Scheme for Telecare Medical Information Systems. Multimed. Tools Appl. 2019, 78, 15255–15273. [Google Scholar] [CrossRef]
- Healthcare Certification Authority. Available online: https://hca.nat.gov.tw/Default.aspx (accessed on 8 September 2020).
- AVISPA: Automated Validation of Internet Security Protocols and Applications. Available online: http://www.avispa-project.org/ (accessed on 30 May 2020).
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).