Abstract
Eavesdropping attack is one of the most serious threats in industrial crowdsensing networks. In this paper, we propose a novel anti-eavesdropping scheme by introducing friendly jammers to an industrial crowdsensing network. In particular, we establish a theoretical framework considering both the probability of eavesdropping attacks and the probability of successful transmission to evaluate the effectiveness of our scheme. Our framework takes into account various channel conditions such as path loss, Rayleigh fading, and the antenna type of friendly jammers. Our results show that using jammers in industrial crowdsensing networks can effectively reduce the eavesdropping risk while having no significant influence on legitimate communications.
1. Introduction
Crowdsensing is a technique leveraging the crowd power to accomplish sensing tasks collaboratively at a low cost. The participants in crowdsensing networks sense the information and upload the sensed data to crowdsensing platforms voluntarily. As a result, the quality of sensing tasks heavily relies on whether the number of participants is sufficient. However, due to the consumption on time, battery and data, recruiting the participants in crowdsensing networks is difficult, although some incentive mechanisms were proposed [1]. Therefore, to guarantee the sensing quality of accomplished tasks, mobile crowdsensing as the complement of traditional statically deployments has been extensively investigated [2,3].
In recent years, the combination of crowdsensing and Industrial Internet of Things (IIoT) has drawn extensive attention [4,5]. There are a lot of benefits in introducing crowdsensing to IIoT, including: (1) providing mobile and scalable measures; (2) monitoring new areas without installing additional dedicated devices; (3) integrating human wisdom into machine intelligence straight forwardly; (4) sharing information and making decision among the whole industrial community [4]. The performance of personal monitoring, process monitoring and product quality checking in IIoT will be improved with the help of crowdsensing [5].
With the proliferation of wireless sensor devices, the security of transmitting data in such IIoT based crowdsensing networks deserves much attention, especially for the confidential data related with commercial interest and privacy concern. To protect the security of crowdsensing networks, some security encryption schemes were proposed, such as privacy-preserving participant selection scheme [6] and reputation management schemes [7]. Moreover, some encryption schemes for IIoT were presented in [8]. The encryption schemes are feasible for devices with sufficient computing capability and power, such as smart phones or tablet computers. However, the encryption schemes may not be suitable for power-constraint sensor devices in crowdsensing networks (e.g., pulse-sensor-embedded wrists) and machinery in factories, since these schemes often require conducting compute-intensive tasks, consequently consuming a lot of power.
Different from the security encryption schemes, friendly-jamming schemes have been recognized as a promising approach to enhance the network security without bringing extra computing tasks [9,10,11,12,13]. The main idea of friendly-jamming schemes is introducing some friendly jammers to wireless networks, where these friendly jammers can generate a jamming signal to increase the noise level at the eavesdroppers, so that they cannot successfully wiretap the legitimate communications [14,15,16]. Using friendly-jamming schemes to decrease the possibility of eavesdropping attacks has received extensive attention [17,18]. The benefits of friendly jamming schemes is that there is no requirement for strong-computing capability of nodes, and no necessity for centralizing security schemes [19]. Therefore, friendly-jamming schemes can be applied in crowdsensing networks with power-constraint devices.
To mitigate the eavesdropping attack of crowdsensing networks, we propose a novel friendly jamming scheme in this paper. In this scheme, we place multiple jammers at a circular boundary around the protected communication area. Being implied by previous studies [20,21], we also consider equipping directional antennas at jammers. We name such jamming scheme with directional antennas as DFJ. Moreover, we also consider equipping omnidirectional antennas at jammers. We name such a jamming scheme with omnidirectional antennas as OFJ. For comparison purposes, we also consider the case without jammers (named as NFJ).
The main contributions of this paper are summarized as follows.
- We propose friendly jamming schemes (DFJ and OFJ) to protect confidential communications from eavesdropping attacks.
- We establish a theoretical model to analyze the probability of eavesdropping attacks and the probability of successful transmission to evaluate the effectiveness of our proposed scheme.
- We conduct extensive simulations to verify the accuracy of our theoretic model. The results also show that using jammers in crowdsensing networks can effectively reduce the eavesdropping risk while having no significant influence on legitimate communications.
Our proposed schemes have many more merits than other existing anti-eavesdropping schemes. Firstly, our schemes are less resource-intensive (i.e., no extensive computing resource needed) and it does not require any modifications on existing network infrastructure. Secondly, our schemes are quite general since the circular area with jammers can essentially circumscribe any buildings due to the feature that every simple polygon (i.e., the shape of a building) always has a circumscribed circle [22]. As a result, the effective jamming to eavesdroppers can be achieved. Moreover, our schemes can offer a larger effective protection area compared with other friendly jamming schemes like placing jammers at polygons [14] or other shapes [23] due to the largest coverage area of a circle.
2. System Models
In this section, we introduce the models used in this paper. We mainly focus on the uplink transmission from sensor devices (legitimate transmitter) to the receiver. The descriptions of notations are given in Table 1.

Table 1.
Notation Summary.
2.1. Network Model
In this paper, we consider a finite disk communication area with radius R, as shown in Figure 1. In this area, a number of legitimate transmitters are distributed according to Poisson point process (PPP) with density . In particular, each transmitter is assumed to follow uniformly independent identical distribution (i.i.d.). We consider a legitimate receiver, located in the center of this network. We assume there is an eavesdropper E with distance D away from the boundary of this communication area, trying to wiretap the confidential communications within the communication area. In order to protect the legitimate transmission, we place multiple friendly jammers at the circular boundary around the protected communication area.
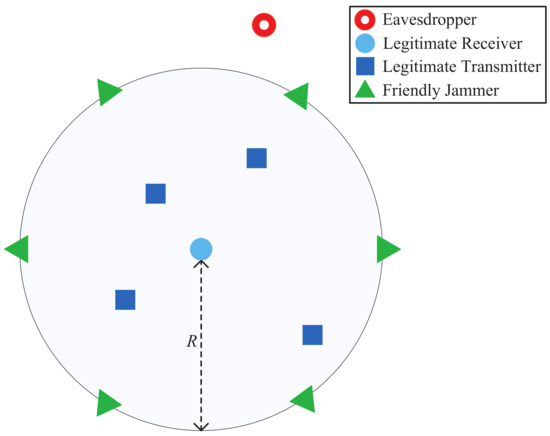
Figure 1.
Network model.
We assume the channel experience Rayleigh fading and path loss. Therefore, the received power of a receiver with distance r from a transmitter is , where h is a random variable following an exponential distribution with mean 1 and is the path loss factor.
2.2. Antennas
There are two types of antennas used in our network: an omni-directional antenna and a directional antenna. Omni-directional antennas radiate/collect radio signals into/from all directions equally. The antenna gain of omni-directional antenna is a constant in all directions, i.e., . Different from an omni-directional antenna, a directional antenna can concentrate transmitting or receiving capability on some desired directions. Due to the high complexity to approximate a realistic directional antenna, we consider a simplified directional antenna model used in [24,25], as shown in Figure 2. This simplified directional antenna model consists of a main lobe within the beamwidth and a side lobe for all other directions. When and is given, can be calculated as follows [25],
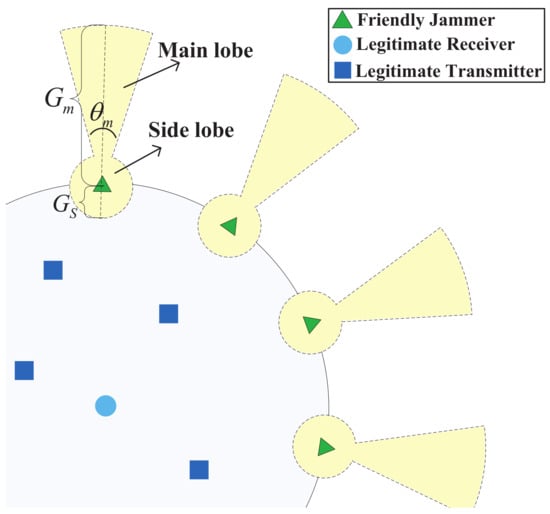
Figure 2.
Friendly Jammers with Directional Antennas.
In this paper, the receiver, the transmitters and the eavedropper are assumed to be equipped with omni-directional antennas. Then, with respect to jammers, we consider two jammer strategies in this network: (i) OFJ scheme, in which jammers are equipped with omni-directional antennas; (ii) DFJ scheme, in which jammers equipped with directional antennas. For comparison purposes, we also consider a scheme: NFJ scheme, in which no friendly jammers are deployed.
3. Impacts of Jamming Schemes on Legitimate Transmission
In this section, we investigate the impacts of different schemes on the legitimate communications. In particular, we consider the probability of successful transmission as a metric to evaluate the transmission quality of legitimate communications. The probability of successful transmission is defined as follows,
Definition 1.
The probability of successful transmission is the expectation of the probability that a reference transmitter can successfully transmit with the legitimate receiver according to the distance between the receiver and the reference transmitter.
To guarantee the successful transmission of legitimate communication, the signal-to-interference- noise-ratio (SINR) at the legitimate receiver, denoted by , must be no less than a threshold T. In particular, when we consider the communication between a reference transmitter and the receiver with distance , can be expressed as
where is the transmission power of transmitters, and are the antenna gains of the reference transmitter and the receiver, respectively (where we have since that the transmitters and receivers are equipped with omni-directional antennas), is the cumulative interference from legitimate users (where is the distance between the ith transmitter and the receiver), is the cumulative interference from N jammers to the receiver (where is the transmission power of the jammers and is the antenna gain of the jammers), and is the noise power.
Thus, we have the probability of successful transmission, denoted by , as follows,
where is the probability density function of the distance between the reference transmitter and the receiver .
Then, we investigate the probability of successful transmission according to the three jammer strategies: NFJ, OFJ, and DFJ schemes.
3.1. Impact of NFJ Scheme
In NFJ scheme, there is no friendly jammer at the boundary of the communication area. Therefore, the cumulative interference from friendly jammers . Then we have in the NFJ scheme as in the following theorem.
Theorem 1.
In the NFJ scheme, the probability of successful transmission is
where , and M is the expectation of the number of legitimate transmitters in the communication area.
Proof.
Let the distance between the receiver and a transmitter be r. Since the receiver is located at the center of the circular area and each transmitter follows uniformly i.i.d., the probability density function of r is as follows,
Since h is a random variable following an exponential distribution with mean 1, in Equation (6) can be expressed as
Next, we calculate . If we denote the expected number of legitimate transmitters by M, we can derive the expression of as follows,
where is derived from the assumption that Rayleigh fading factor of each channel follows exponentially i.i.d., and can be derived from the property of moment generating function of exponential variable.
3.2. Impact of OFJ Scheme
In the OFJ scheme, the friendly jammers placed at the boundary of communication area are equipped with omni-directional antennas, i.e., the antenna gain of jammers is . Therefore, in Equation (3) can be expressed as . Then we give in the OFJ scheme by the following theorem.
Theorem 2.
In the OFJ Scheme, the probability of successful transmission is
Proof.
Similar to the proof of Theorem 1, the probability of successful transmission in the OFJ scheme can be expressed as follows,
where can be derived as follows,
where is given by Equation (8), and can be calculated by
3.3. Impact of DFJ Scheme
In DFJ scheme, the jammers placed at the boundary are equipped with directional antennas. In particular, we can find that the receiver can be only affected by the side lobe of directional antennas, as shown in Figure 2. Therefore, we have =. Thus, in Equation (3) can be expressed as . Then, we obtain in the DFJ scheme by the following theorem.
Theorem 3.
In the DFJ scheme, the probability of successful transmission is
4. Analysis on Probability of Eavesdropping Attacks
In this section, we analyze the influence of friendly jammers on the probability of an eavesdropping attack of this network. In particular, we use the probability of an eavesdropping attack as the metric to evaluate the possibility of being eavesdropped on in this network. We assume that if the eavesdropper can wiretap any of the transmitters, this network can be seen as being attacked. Based on this assumption, we give the definition of the probability of eavesdropping attack as follows.
Definition 2.
The probability of an eavesdropping attack is the probability that the eavesdropper can wiretap any of the transmitters.
Before we analyze the probability of an eavesdropping attack, we first analyze the probability that a certain transmitter can be wiretapped by the eavesdropper, denoted by . If the eavesdropper can wiretap a transmitter with distance , the SINR at the eavesdropper, denoted by , has to be no less than a threshold . Thus, can be expressed as follows,
where is the antenna gain of the eavesdropper (we have since the eavesdropper is equipped by an omni-directional antenna), is the cumulative interference from transmitters to the eavesdropper (where is the distance between the ith transmitter and the eavesdropper), is the cumulative interference from the jammers to the eavesdropper, which will be elaborated later according to different jammer schemes, and is the probability density function of .
Next, based on the analysis of , we give the probability of eavesdropping attack, denoted by , as follows,
The impact of friendly jammers on the eavesdropping attacks will then be investigated. In particular, we will derive the probability of an eavesdropping attack of an eavesdropper in the NFJ scheme, OFJ scheme and DFJ scheme as follows, respectively.
4.1. Impact of NFJ Scheme
Firstly we consider the NFJ scheme in which there is no friendly jammer on the boundary of communication area. In this case, the interference from friendly jammers to eavesdropper , then we have the following theorem:
Theorem 4.
In the NFJ scheme, the probability of eavesdropping attack is
where , and
Proof.
We denote the distance between the eavesdropper and a transmitter by l. The probability density function of l can be expressed as follows [26],
Then can be expressed as
where .
Since is a random variable following an exponential distribution with mean 1, can be expressed as
Following the similar approach in deriving Equation (8), the expression of can be derived by the following equation,
If we set , Equation (24) can be expressed as
4.2. Impact of OFJ Scheme
Then we investigate the OFJ scheme, where friendly jammers are equipped with omni-directional antennas. In order to derive , we need to calculate the interference from jammers to eavesdropper first.
Figure 3 shows the geometrical relationships of the friendly jammers and the eavesdropper. Without loss of generality, we label the jammer which is nearest to the eavesdropper as and the jammer is at the left-hand-side of the eavesdropper. Then we label (where as mth nearest jammer at the right-hand-side of jammer separately. Similarly, we label (where as the nth nearest jammer at the left-hand-side of jammer separately.
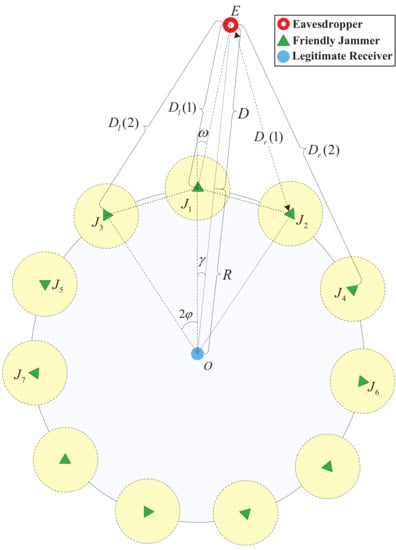
Figure 3.
Geometrical relationship of the friendly jammers and the eavesdropper.
From the observation point O, is the relative degree between neighbour jammers and is the degree between jammer and eavesdropper E. Since the number of jammers is N, we have . Due to the fact that the eavesdropper is randomly located outside of the protected communication area, we have the probability density function of variable ,
Then we can calculate the cumulative interference of the jammers to the eavesdropper based on their geometrical relationships, which is given by the following lemma.
Lemma 1.
When the friendly jammers are equipped with omni-directional antennas, the cumulative interference from the jammers to the eavesdropper is
where .
Proof.
We present the proof of Lemma 1 in Appendix A.
With the interference from the jammers to the eavesdropper , we obtain the probability of eavesdropping attack as the following theorem.
Theorem 5.
In the OFJ scheme, the probability of an eavesdropping attack of an eavesdropper is:
where
and
in which and .
Proof.
Following the similar approach to the proof of Theorem 4, we can get the probability that a certain transmitter can be tapped denoted by as follows,
where .
Since is a random variable following an exponential distribution with mean 1, can be expressed as
where given by Equation (24).
Then we calculate . For simplicity, we denote , . With the expression of given in Lemma 1, we can obtain given by the following equation,
where is derived from the independence between an eavesdropper’s location and the distribution of fading channel, follows from the property of moment generating function of exponential variable, is derived with the probability density function of as given in Equation (27).
4.3. Impact of DFJ Scheme
In order to derive the probability of an eavesdropping attack in the DJF scheme, we need to evaluate the interference from the friendly jammers equipped with directional antenna to the eavesdropper.
However, when the jammers are deployed densely or the distance between the eavesdropper and the commmunication area D is large, there may be more than one jammer that interferes with the eavesdropper via their main lobes simultaneously (as shown in Figure 4). Therefore, we first investigate the number of friendly jammers which interfere with the eavesdropper via main lobes.
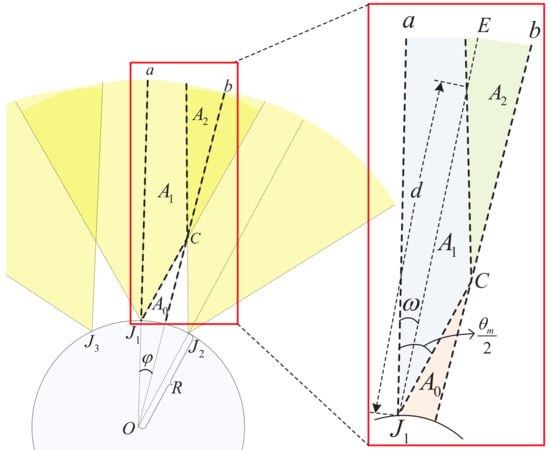
Figure 4.
Geometrical relationship of friendly jammers (three jammers are shown).
In Figure 4, we show the main lobes of 3 jammers. Due to the fact that the eavesdropper is nearest to the jammer , the eavesdropper locates in the area between line a and line b, where line a is the extended line of and line b is the perpendicular bisector of segment .
The term of in Figure 4 is the degree between line a and . When , the eavesdropper locates in area , there is no jammers interfering it with its main lobe. When , the area that the eavesdropper locates depends on the distance D. When , the eavesdropper locates in if , there will be one jammer interfering with the eavesdropper via its main lobe; the eavesdropper locates in if , there will be two jammers interfering with the eavesdropper via their main lobes.
Similarly, we denote to be the intersection area of k jammers’ main lobe directions between line a and line b. When the eavesdropper locates in area , there will be k jammers interfering with the eavesdropper via their main lobes. We denote the number of friendly jammers (interfering the eavesdropper via their main lobes) by . When is fixed, the interference of directional jammers to eavesdroppers is shown in the following lemma.
Lemma 2.
When , the interference of jammers on eavesdropper in the DFJ scheme is
where ,, and
Proof.
We present the proof of Lemma 2 in Appendix B. ☐
With the interference from the jammers to the eavesdropper, we obtain the probability of eavesdropping attack as the following theorem,
Theorem 6.
In DFJ scheme, the upper bound of probability of eavesdropping attack is given by
where ,
, , , ,,
Proof.
We present the proof of Theorem 6 in Appendix C. ☐
5. Results
In this section, we present the simulation results of probability of successful transmission and probability of eavesdropping attack considering the NFJ, OFJ and DFJ schemes. The simulation results are generated via Monte Carlo simulations with 50,000 runs and the parameters are given in Table 2.

Table 2.
Notation and parameters.
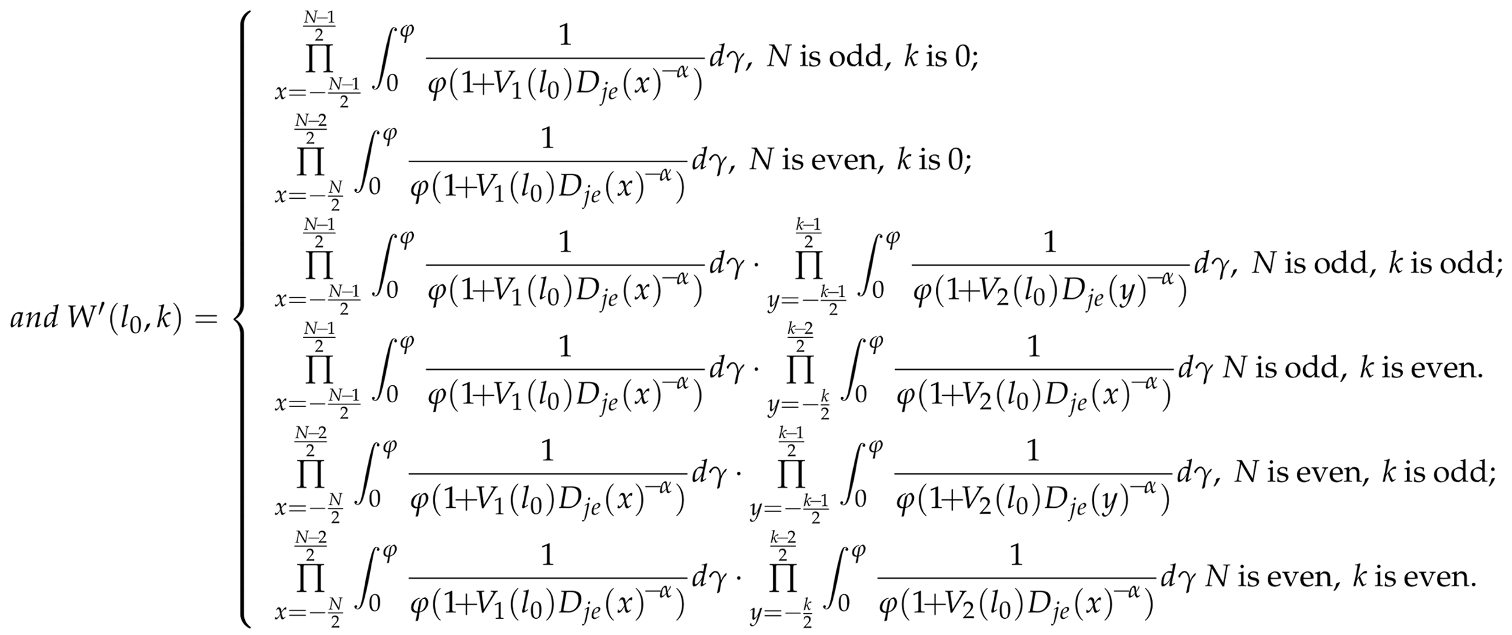
In Figure 5, we present the numerical and simulation results of probability of successful transmission and probability of eavesdropping attack with different schemes. From Figure 5a, we find decreases when the number of legitimate transmitters denoted by M increases. Since the receiver only receives the information from the protected transmitter, the cumulative interference from legitimate transmitters to the receiver increases with M. When we introduce friendly jammers into the network, compared with the NFJ scheme, decreases. The performance of with DFJ scheme is better than with OFJ scheme. This is because the lower antenna gain of side lobe in the DFJ scheme leads to less interference to the legitimate transmission.
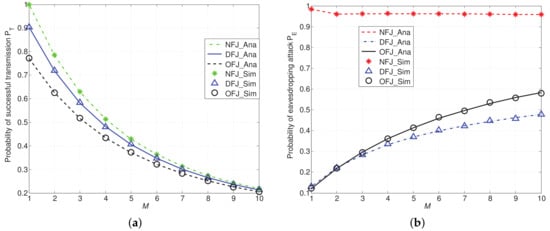
Figure 5.
and with DFJ scheme and OFJ scheme versus NFJ scheme when , , and M varies from 1 to 10. (a) Probability of successful transmission ; (b) Probability of eavesdropping attack .
In Figure 5b, the red curve represents the probability of eavesdropping attack of the NFJ scheme. From numerical results, we find that the red line decreases very slowly, especially when M is larger than 2. For example, when , of NFJ scheme is 0.9626, while becomes 0.9619 and 0.9602 when M becomes 6 and 8, respectively. This result lies in the fact that the eavesdropper may eavesdrop any one of the M legitimate transmitters, rather than a specially appointed transmitter. When M increases, the interference on the eavesdropper increases. However, the eavesdropper may tap more transmitters as the total number of transmitters is increased. In addition, the performance of of DFJ scheme is still better than that of the OFJ scheme, because of the higher antenna gain of main lobe.
From Figure 5a,b we find that introducing friendly jammers into the network will lead to the decrement on both and . However, the influence of friendly jammers on is more obvious than the influence on . For example, when , compared with the NFJ scheme, the reduction of with OFJ scheme is (i.e., reduced), while the reduction of is 0.5485 (i.e., reduced). When , compared with the NFJ scheme, the reduction of with DFJ scheme is (i.e., reduced), the reduction of is 0.5935 (i.e., reduced). Therefore, the DFJ scheme can reduce the probability of eavesdropping attacks more significantly while maintaining the lower impairment to the legitimate communications than the OFJ scheme. This result implies that using friendly jammers can reduce the eavesdropping attack without causing obvious damage on legitimate transmission.
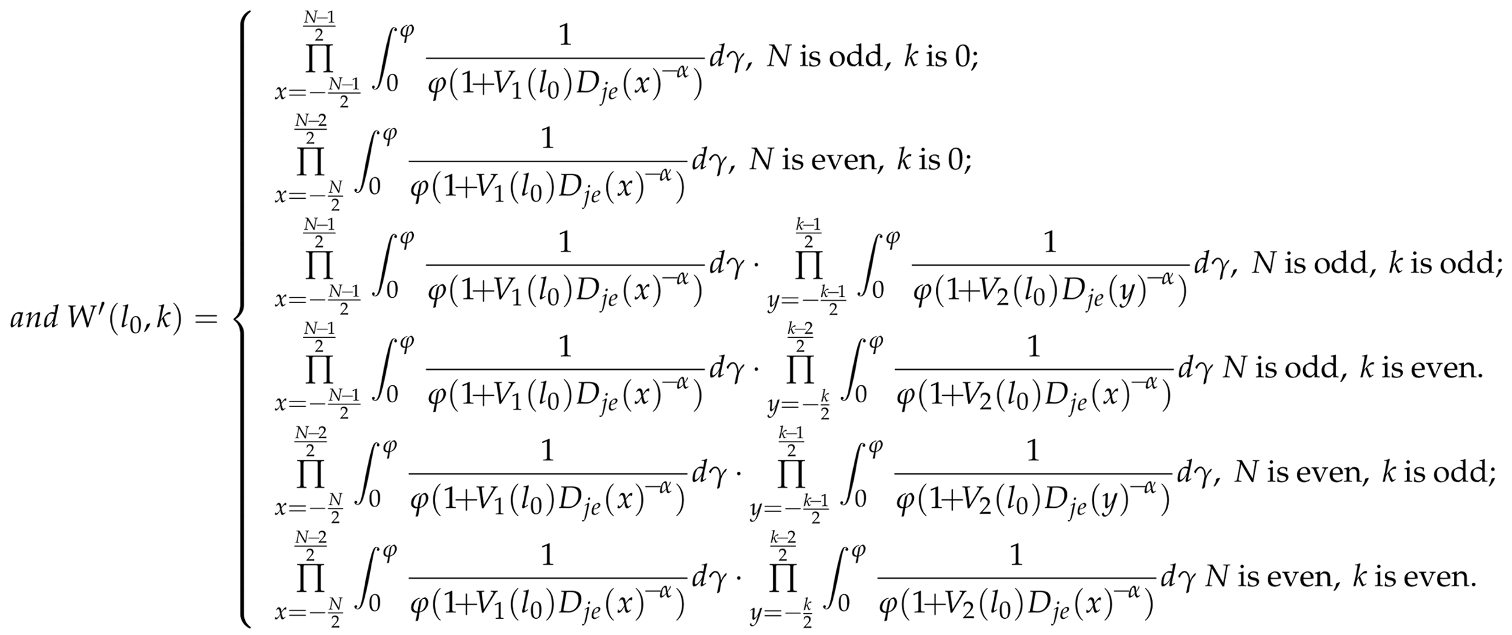
Figure 6 shows the comparison of and in different schemes with the varied number of friendly jammers denoted by N. In Figure 6a, we find that both of the DFJ scheme and that of the OFJ scheme decrease when N increases. The decrement of lies in the increased cumulative interference from friendly jammers. Moreover, Figure 6b shows that decreases rapidly when the number of friendly jammers N increases, especially when friendly jammers are equipped with directional antennas (i.e., in DFJ scheme). This result can help to verify the effectiveness of OFJ and DFJ schemes in reducing the probability of eavesdropping attacks .
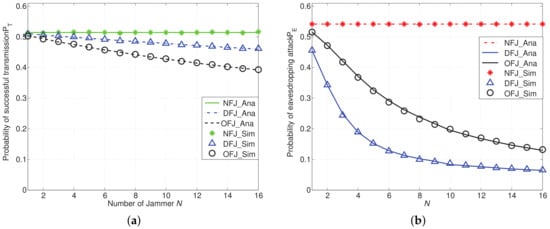
Figure 6.
and with the DFJ scheme and the OFJ scheme versus the NFJ scheme when , , and N varies from 1 to 16. (a) Probability of successful transmission ; (b) Probability of eavesdropping attack .
The results as shown in Figure 6 imply that it may not be necessary to deploy too many friendly jammers in the network. In particular, in the DFJ scheme, we can significantly reduce the probability of eavesdropping attacks while only slightly impairing legitimate communications by introducing a few friendly jammers. For example, when , compared with NFJ scheme, the reduction of in DFJ scheme is (i.e., reduction), while the reduction of in the DFJ scheme is (i.e., reduction).
Figure 7 shows the comparison of and with DFJ, OFJ schemes versus the NFJ scheme with different SINR threshold. It is shown in Figure 7 that decreases with the threshold T and decreases with the threshold . From Figure 7a, similarly to Figure 5b, we find that using friendly jammers can always reduce the probability of eavesdropping attacks compared with the NFJ scheme, and the DFJ scheme performs better than the OFJ scheme obviously.
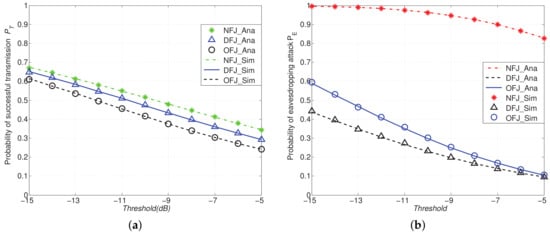
Figure 7.
and with DFJ scheme and OFJ scheme versus NFJ scheme when , , , , SINR threshold T and varies from to . (a) Probability of successful transmission ; (b) Probability of eavesdropping attacks .
In another set of simulations as presented in Figure 8, we compare the probability of eavesdropping attack of different schemes with varied distance between the eavesdropper and the network boundary D. From Figure 8a, we can find that of NFJ, OFJ and DFJ schemes vary slightly when path loss factor . It means when , path loss effect has no obvious impact on . This result lies in the fact that path loss has the influence on both useful signal and interference. However, when the path loss factor increases from 3 to 4, as shown in Figure 8b, of three schemes decreases rapidly, especially in the NFJ scheme. This result implies that the path loss has a more obvious influence on useful signal than that on interference. From Figure 8, we also find that using friendly jammers can reduce the probability of eavesdropping attacks compared with the NFJ scheme.
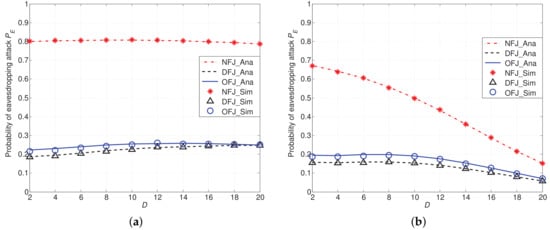
Figure 8.
Probability of eavesdropping attacks with DFJ scheme and OFJ scheme versus NFJ scheme when with distance D ranging from 2 to 20. (a) ; (b) .
6. Discussions
In this section, we first discuss the impact of our friendly jamming schemes when the eavesdropper is located inside the network. Then we discuss the impact of our friendly jamming schemes on legitimate transmissions in other networks.
6.1. Impact on the Eavesdropper Inside of Network
In Section 4, we analyze the impact of friendly jamming schemes on the eavesdropper who is prevented from entering the protected area. It is feasible in a practical industrial environment that the eavesdropper has the difficulty of entering the protected network area (e.g., the barbed wire entanglement around a plant). However, we can also apply our previous results in [27] to analyze the scenario in which an eavesdropper enters the network area. In particular, we consider that friendly jammers are regularly placed at deterministic locations [27] and the eavesdropper is located at the center of this area, as shown in Figure 9. We then apply the general theoretical models presented in [27] to derive the eavesdropping probability.
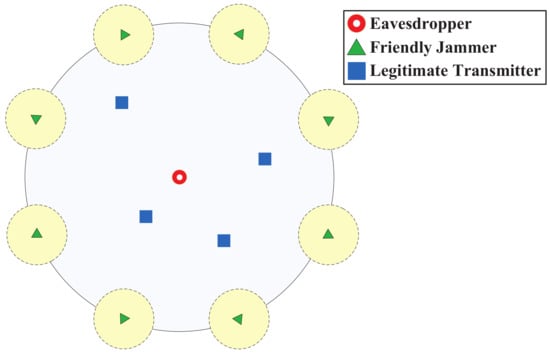
Figure 9.
Eavesdropper inside of the network.
Regarding the case in which the eavesdropper is not located at the center of the network, we can first calculate the cumulative distance from the eavesdropper to each of friendly jammers via the approach proposed in [26] and used [28]. We can then derive the impact of friendly jammers on the eavesdropper inside of network by following the similar steps in [27] and plugging in the cumulative distance. Due to the space limitation and the similarity to our previous method [27], we ignore the derivation of the eavesdropping probability in the scenario that an eavesdropper enters the network.
6.2. Impact on Legitimate Transmissions in Other Networks
In Section 3, we investigated the impact of friendly jamming schemes on legitimate transmissions in our protected network area. Since our friendly jammers are deployed on the boundary of our protected transmission area, the networks near this area may possibly be interfered with by our friendly jamming schemes. Therefore, we next investigate the impacts of friendly jamming schemes on legitimate transmissions in other networks.
In Figure 10, we show the relationship between our protected network (at the left hand side) and another network nearby (at the right hand side). It is worth mentioning that a crowdsensing device in our protected network often has the multi-homing capability [29], i.e., accessing two different networks (e.g., a small cell and a macro cell). The impact of our friendly jamming schemes on legitimate transmissions of another network can be analyzed according to two different scenarios: (1) both protected network and another network are using different channels; (2) both protected network and another network are using the same channel. In the first scenario in which different frequencies are allocated to the protected network and another network. In this scenario, the interference of our friendly jamming schemes is negligible on legitimate transmissions in other networks.
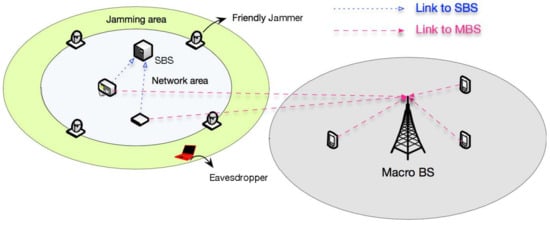
Figure 10.
Impact of friendly jammers on other networks.
Then we analyze the second scenario. In this scenario, both the protected network and another network are using different channels. It is obvious that the analytical result in Section 4 can be trivially used to investigate the interference from friendly jammers on legitimate transmissions in another network. In particular, the interference generated by the OFJ scheme on legitimate transmissions outside the network is given by Lemma 1 in Section 4. The interference from the DFJ scheme on legitimate transmissions outside the network is given by Lemma 2 in Section 4.
Another concern related to our friendly jamming schemes is legitimacy. For example, jamming schemes are restricted in US and Europe. In Europe, the transmitting power of jammers is limited to be less than 20 dBm for 2.4 GHz band [30]. Therefore, we can either limit the jamming range or restrict the jamming period so that the impact on other legitimate communications will be minimized. The analytical results of OFJ and DFJ imply that the intensity of interference generated by our friendly jamming scheme heavily relies on the channel factors, for example, the transmitting power of jammers, antenna gain, path loss, etc. Therefore, we can adjust the transmitting power and the antenna gain of friendly jammers so that the jamming range can be minimized. Another approach of limiting the impact of friendly jamming schemes is restricting the time of the emitting jamming signal. For example, we can only send the jamming signal at the crucial stages (e.g., key generation phase [31] or vulnerable phase [14]).
7. Conclusions
In this paper, we propose a novel friendly jamming scheme to protect confidential communications from eavesdropping attacks. To evaluate the effectiveness of our scheme, we establish a theoretical model to analyze the probability of eavesdropping attacks and the probability of successful transmission. Moreover, we verify our model with extensive simulations. The agreement between analysis and simulation results verifies the accuracy of our analysis.
Our results show that our scheme can significantly decrease the eavesdropping risk compared with the no friendly jamming scenario and meanwhile that it maintains low decrease on the transmission probability. In addition, we find that using directional antennas compared with omni-directional antennas on friendly jammers can further decrease the eavesdropping risk while obviously mitigating the influence on the transmission probability.
Author Contributions
X.L. proposed the idea, derived the results and wrote the paper. H.-N.D. supervised the work and revised versions. Q.W. contributed to proofreading and revising the article. H.W. gave valuable suggestions on the motivation of proposing anti-eavesdropping schemes and assisted in revising the paper.
Funding
The work described in this paper was partially supported by Macao Science and Technology Development Fund under Grant No. 0026/2018/A1, the National Natural Science Foundation of China under Grant No. 61672170 and the Science and Technology Planning Project of Guangdong Province under Grant No. 2017A050501035. The authors would like to express their appreciation for Gordon K.-T. Hon for his thoughtful discussions. The authors would also like to thank the anonymous reviewers for their constructive comments.
Conflicts of Interest
The authors declare no conflict of interest.
Appendix A
Proof of Lemma 1.
From the relationship of in Figure 3, we can calculate the distance between jammer and the eavesdropper E in the following equation,
From the relationship of , we get the distance between eavesdropper E and jammer :
Following the similar approach, we have the distance between eavesdropper E and the mth nearest jammer at the right-hand-side of jammer as follows,
and the distance between eavesdropper E and the nth nearest jammer at the left-hand-side of jammer as follows,
Combining Equations (A1) and (A2), we can have the expression of the distance between jammers and eavesdropper as follows,
where x is an integer whose range depends on N. When N is odd, ; when N is even, .
Substituting the distance into the channel model, we get the cumulative interference of jammers to the eavesdropper as given in Lemma 1. ☐
Appendix B
Proof of Lemma 2.
From Section 4.2 we have the distance between eavesdropper and jammers as given in Equation (A3). Then we show the interference of friendly jammers on eavesdroppers according to different cases of .
Case 0: when , the interference of friendly jammers on eavesdroppers is from side lobe of friendly jammers,
If N is even,
If N is odd,
Case 1: when , the interference of friendly jammers on eavesdroppers is
Case 2: when , the interference of friendly jammers on eavesdroppers is
Case 3: when , the interference of friendly jammers on eavesdroppers is
Case k: when , the interference of friendly jammers on eavesdroppers is
If k is even,
If k is odd,
Therefore, we obtain the expression of in Lemma 2 by integrating the above cases. ☐
Appendix C
Proof of Theorem 6.
According to the definition of the eavesdropping probability , we need to derive the probability first. The derivation of eavesdropping probability in DFJ scheme is similar to the derivation OFJ scheme in Theorem 5, while the main difference is the cumulative interference from friendly jammers. Therefore, we have the following expressions:
where , and
The influence of legitimate transmitters on the eavesdropper remains unchanged. Therefore, we have the given in Equation (24).
From the expression of interference from directional jammers on eavesdropper as given in the Lemma 2, we have
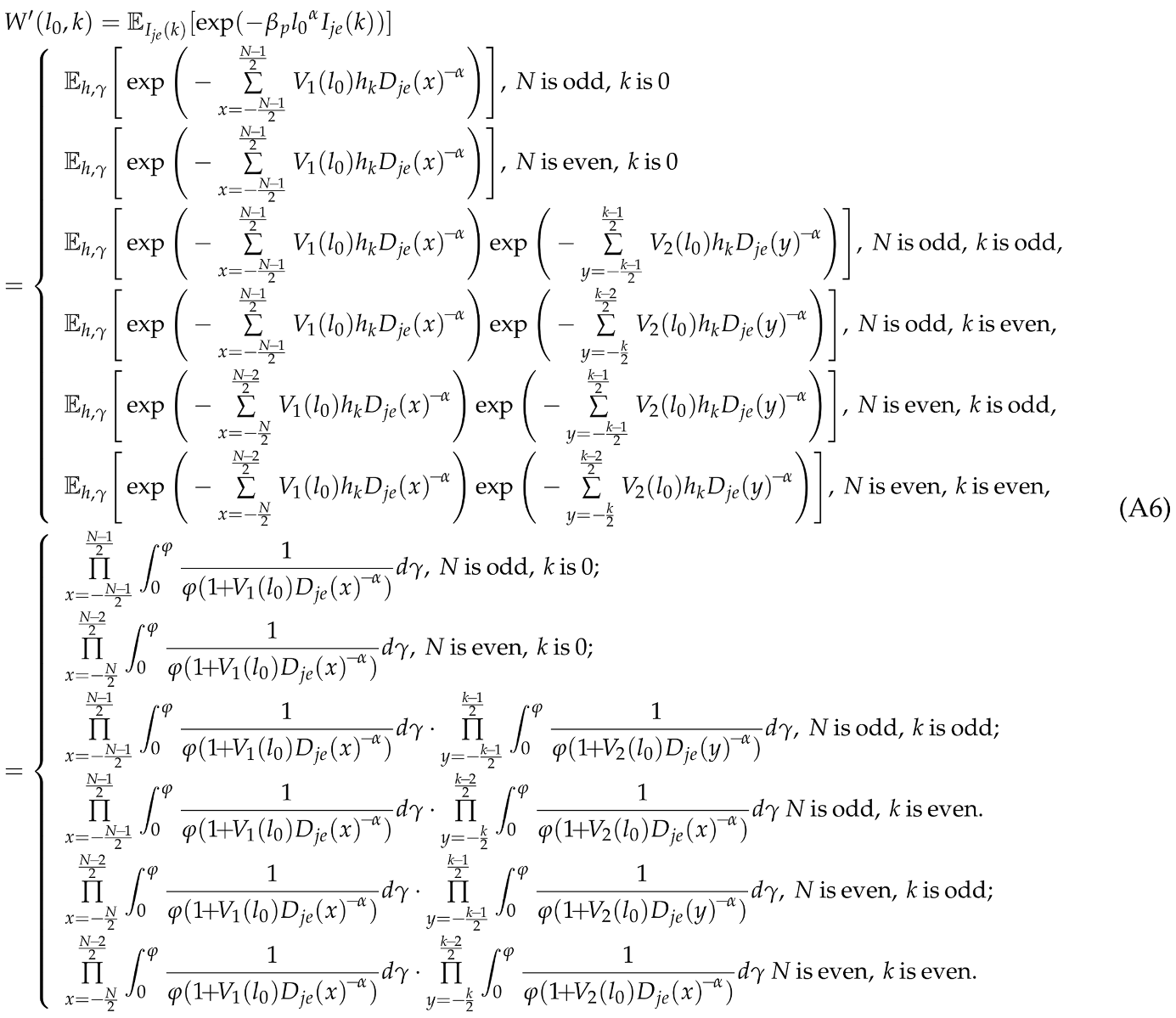 where , and .
where , and .
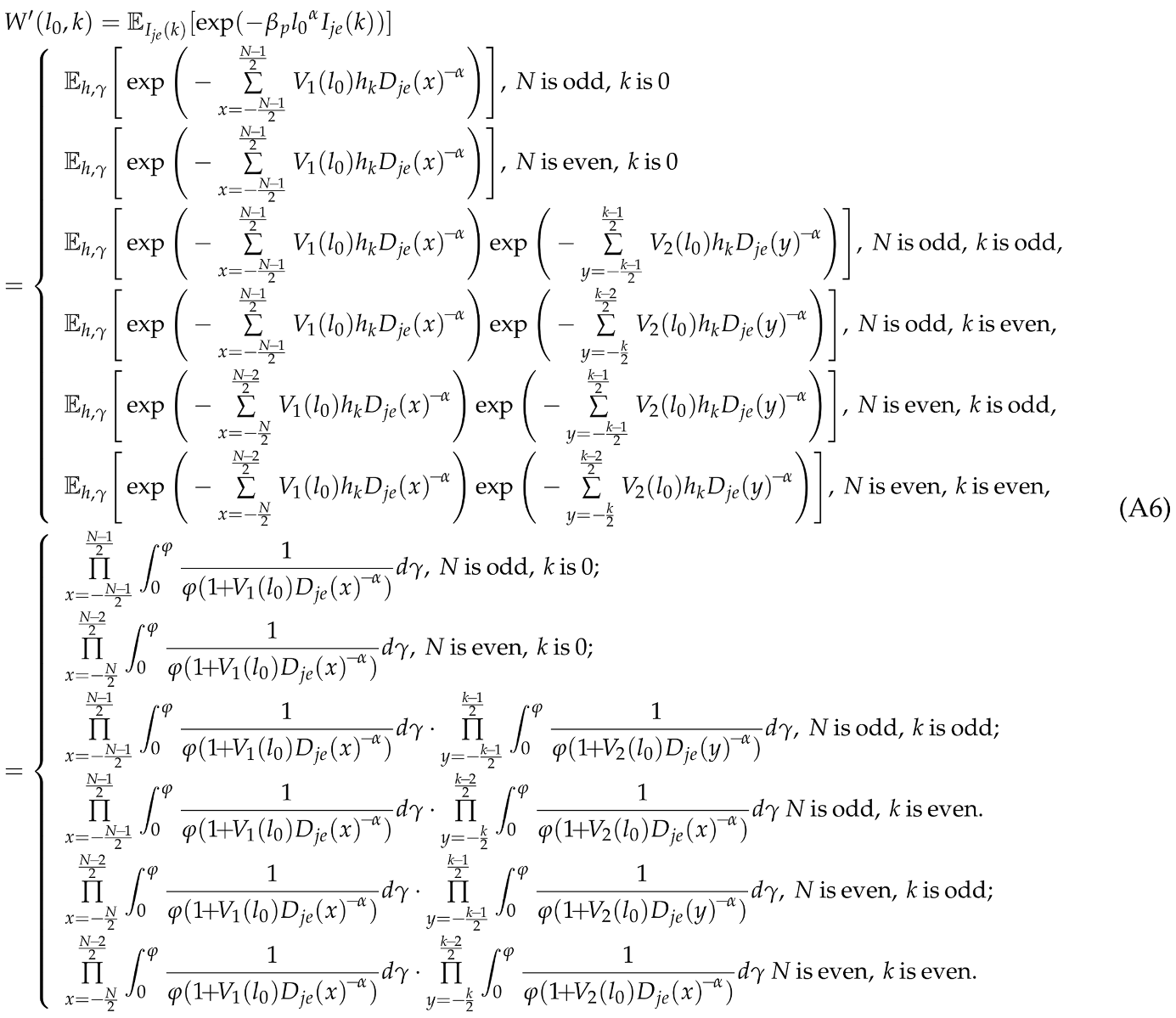 where , and .
where , and .After plugging Equations (25) and (A6) into the Equation (A5), and substituting the new expression of Equation (A5) into Equation (A4), we obtain the result of in the following expression,
Then we derive in the DJF scheme. When there are k jammers interfering with the eavesdropper via main lobes, according to Total Probability Theorem, we have the following expression,
However, the premise of is that both the number of jammers and the distance D between eavesdropper and the communication area are large. Since this situation seldom exists in real communication environment, we simplify the expression of by considering only two scenarios: and . When there is more than one jammer interfering with the eavesdropper via its main lobe, we assume there is one jammer interfering with the eavesdropper via its main lobe. Then we have the upper bound of as follows,
Since our result of is a upper bound, the effect of the DFJ scheme on the eavesdropper in reality will be more highlighted.
From the geometrical relationship as given in Figure 3, we have . We denote . When , we have , which means the eavesdropper locates in area and no jammer interferes with the eavesdropper via its main lobe. Since the degree is uniformly distributed, the result in Equation (A9) becomes
where and can be calculated from Equation (A7). ☐
References
- Yang, G.; He, S.; Shi, Z.; Chen, J. Promoting Cooperation by the Social Incentive Mechanism in Mobile Crowdsensing. IEEE Commun. Mag. 2017, 55, 86–92. [Google Scholar] [CrossRef]
- Han, G.; Liu, L.; Chan, S.; Yu, R.; Yang, Y. HySense: A hybrid mobile crowdsensing framework for sensing opportunities compensation under dynamic coverage constraint. IEEE Commun. Mag. 2017, 55, 93–99. [Google Scholar] [CrossRef]
- Datta, S.K.; da Costa, R.P.F.; Bonnet, C.; Hrri, J. oneM2M Architecture Based Iot Framework for Mobile Crowd Sensing in Smart Cities. In Proceedings of the 2016 European Conference on Networks and Communications (EuCNC), Athens, Greece, 27–30 June 2016. [Google Scholar]
- Pilloni, V. How Data Will Transform Industrial Processes: Crowdsensing, Crowdsourcing and Big Data as Pillars of Industry 4.0. Future Intern. 2018, 10, 24. [Google Scholar] [CrossRef]
- Shu, L.; Chen, Y.; Huo, Z.; Bergmann, N.; Wang, L. When Mobile Crowd Sensing Meets Traditional Industry. IEEE Access 2017, 5, 15300–15307. [Google Scholar] [CrossRef]
- Li, T.; Jung, T.; Qiu, Z.; Li, H.; Cao, L.; Wang, Y. Scalable Privacy-Preserving Participant Selection for Mobile Crowdsensing Systems: Participant Grouping and Secure Group Bidding. IEEE Trans. Netw. Sci. Eng. 2018. [Google Scholar] [CrossRef]
- Ma, L.; Liu, X.; Pei, Q.; Xiang, Y. Privacy-Preserving Reputation Management for Edge Computing Enhanced Mobile Crowdsensing. IEEE Trans. Serv. Comput. 2018. [Google Scholar] [CrossRef]
- Choo, K.; Gritzalis, S.; Park, J.H. Cryptographic Solutions for Industrial Internet-of-Things: Research Challenges and Opportunities. IEEE Trans. Ind. Inform. 2018. [Google Scholar] [CrossRef]
- Zhang, N.; Cheng, N.; Lu, N.; Zhang, X.; Mark, J.W.; Shen, X. Partner Selection and Incentive Mechanism for Physical Layer Security. IEEE Trans. Wirel. Commun. 2015, 14, 4265–4276. [Google Scholar] [CrossRef]
- Hassanieh, H.; Wang, J.; Katabi, D.; Kohno, T. Securing RFIDs by Randomizing the Modulation and Channel. In Proceedings of the 12th USENIX Symposium on Networked Systems Design and Implementation (NSDI 15), Oakland, CA, USA, 4–6 May 2015. [Google Scholar]
- Zou, Y.; Zhu, J.; Yang, L.; Liang, Y.; Yao, Y. Securing physical-layer communications for cognitive radio networks. IEEE Commun. Mag. 2015, 53, 48–54. [Google Scholar] [CrossRef]
- Wang, W.; Sun, Z.; Piao, S.; Zhu, B.; Ren, K. Wireless Physical-Layer Identification: Modeling and Validation. IEEE Trans. Inform. Forensics Secur. 2016, 11, 2091–2106. [Google Scholar]
- Mucchi, L.; Ronga, L.; Zhou, X.; Huang, K.; Chen, Y.; Wang, R. A New Metric for Measuring the Security of an Environment: The Secrecy Pressure. IEEE Trans. Wirel. Commun. 2017, 16, 3416–3430. [Google Scholar] [CrossRef]
- Kim, Y.S.; Tague, P.; Lee, H.; Kim, H. A Jamming Approach to Enhance Enterprise Wi-Fi Secrecy through Spatial Access Control. Wirel. Netw. 2015, 21, 2631–2647. [Google Scholar] [CrossRef]
- Vilela, J.P.; Bloch, M.; Barros, J.; McLaughlin, S.W. Wireless Secrecy Regions with Friendly Jamming. IEEE Trans. Inform. Forensics Secur. 2011, 6, 256–266. [Google Scholar] [CrossRef]
- Hu, J.; Yan, S.; Shu, F.; Wang, J.; Li, J.; Zhang, Y. Artificial-Noise-Aided Secure Transmission with Directional Modulation Based on Random Frequency Diverse Arrays. IEEE Access 2017, 5, 1658–1667. [Google Scholar] [CrossRef]
- Zhang, X.; McKay, M.R.; Zhou, X.; Heath, R.W. Artificial-Noise-Aided Secure Multi-Antenna Transmission with Limited Feedback. IEEE Trans. Wirel. Commun. 2015, 14, 2742–2754. [Google Scholar] [CrossRef]
- Zheng, T.X.; Wang, H.M. Optimal Power Allocation for Artificial Noise under Imperfect CSI Against Spatially Random Eavesdroppers. IEEE Trans. Veh. Technol. 2016, 65, 1658–1667. [Google Scholar] [CrossRef]
- Adams, M.; Bhargava, V.K. Using friendly jamming to improve route security and quality in ad hoc networks. In Proceedings of the 2017 IEEE 30th Canadian Conference on Electrical and Computer Engineering (CCECE), Windsor, ON, Canada, 30 April–3 May 2017; pp. 1–6. [Google Scholar]
- Dai, H.N.; Wang, Q.; Li, D.; Wong, R.C.W. On Eavesdropping Attacks in Wireless Sensor Networks with Directional Antennas. Int. J. Distrib. Sens. Netw. 2013, 9, 760834. [Google Scholar] [CrossRef]
- Kim, M.; Hwang, E.; Kim, J. Analysis of eavesdropping attack in mmWave-based WPANs with directional antennas. Wirel. Netw. 2017, 23, 59–74. [Google Scholar] [CrossRef]
- MacDougall, J.A.; Buchholz, R.H. Cyclic Polygons with Rational Sides and Area. J. Number Theory 2008, 128, 17–48. [Google Scholar]
- Sankararaman, S.; Abu-Affash, K.; Efrat, A.; Eriksson-Bique, S.D.; Polishchuk, V.; Ramasubramanian, S.; Segal, M. Optimization Schemes for Protective Jamming. In Proceedings of the ACM MOBIHOC, Hilton Head Island, SC, USA, 11–14 June 2012. [Google Scholar]
- Singh, S.; Kulkarni, M.N.; Ghosh, A.; Andrews, J.G. Tractable Model for Rate in Self-Backhauled Millimeter Wave Cellular Networks. IEEE J. Sel. Areas Commun. 2015, 33, 2196–2211. [Google Scholar] [CrossRef]
- Wang, Q.; Dai, H.; Zheng, Z.; Imran, M.; Vasilakos, A. On Connectivity of Wireless Sensor Networks with Directional Antennas. Sensors 2017, 17, 134. [Google Scholar] [CrossRef] [PubMed]
- Mathai, A. An Introduction to Geometrical Probability Distributional Aspects with Applications; Gordon and Breach: Philadelphia, PA, USA, 1999. [Google Scholar]
- Li, X.; Dai, H.N.; Wang, H.; Xiao, H. On Performance Analysis of Protective Jamming Schemes in Wireless Sensor Networks. Sensors 2016, 16, 1987. [Google Scholar] [CrossRef] [PubMed]
- Khalid, Z.; Durrani, S. Distance distributions in regular polygons. IEEE Trans. Veh. Technol. 2013, 62, 2363–2368. [Google Scholar] [CrossRef]
- Chen, L.; Wu, J.; Dai, H.N.; Huang, X. BRAINS: Joint Bandwidth-Relay Allocation in Multi-Homing Cooperative D2D Networks. IEEE Trans. Veh. Technol. 2018. [Google Scholar] [CrossRef]
- Berger, D.S.; Gringoli, F.; Facchi, N.; Martinovic, I.; Schmitt, J.B. Friendly jamming on access points: Analysis and real-world measurements. IEEE Trans. Wirel. Commun. 2016, 15, 6189–6202. [Google Scholar] [CrossRef]
- Vo-Huu, T.D.; Vo-Huu, T.D.; Noubir, G. Interleaving Jamming in Wi-Fi Networks. In Proceedings of the 9th ACM Conference on Security & Privacy in Wireless and Mobile Networks, Darmstadt, Germany, 18–20 July 2016. [Google Scholar]
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).