1. Introduction
With the development of communication technology, multimedia has become one of the most important means for people to transmit messages. At the same time, with the development of cryptography and people’s attention to security, multimedia information security has become a more concerned field. Information hiding technology plays a deep and extensive role in multimedia information security. Image is an important medium for information transmission. In order to protect the security of data, people often use image encryption technology to encrypt sensitive pictures into meaningless noise pictures. However, the encryption operation exposes the existence of sensitive pictures and is more likely to attract attacks. Compared with image encryption technology, image steganography technology hides the existence of the secret information itself and avoids the attention and suspicion of the third party. Image steganography has the advantages of protecting secret information content and hiding transmission behavior, which make the transmitted secret information more secure and confidential. The rise of image steganography makes up for the deficiency of image encryption and provides technical support for covert communication.
Steganography is defined as the science and art of hiding secret information in a way that only the intended recipient can detect the existence of the secret information [
1,
2]. Secret information is hidden in publicly accessed objects. These publicly accessed objects are called carrier objects. Some examples of carrier objects are audio, video, text, and images, etc., which are used in different steganography methods [
3,
4,
5,
6,
7,
8,
9]. Among different types of carrier objects, images are considered to be excellent carriers because they have a high degree of pixel value redundancy, and the human visual system is insensitive to image details. The original image without secret information is called the cover image or the host image, and the image with secret information is called the steganographic image [
1]. According to different embedding domains, existing image steganography algorithms can be divided into spatial steganography methods based on spatial domain and transform domain steganography methods based on transform domain.
Data hiding techniques in spatial domain are mainly divided into methods based on Least Significant Bit (LSB) substitution, methods based on Pixel Value Differencing (PVD), methods based on Quantization Index Modulation (QIM), and methods based on LSB matching. In this category, LSB substitution is the most commonly used method. In this method, in order to hide the secret data in the cover image, K LSBs of the pixel value of the cover image are directly replaced with K secret message bits, so as to generate a steganographic image [
10,
11]. In the PVD-based method, the difference between consecutive pixels is calculated to determine the number of bits to be embedded in the cover image [
12]. In LSB matching, the LSB of the cover image pixel matches the secret message bit. In the case of no matching, the pixel value of the cover image will randomly increase or decrease [
13]. These techniques have very little computational overhead and are very simple. However, when more bits are embedded in each pixel, the hidden image will lose its quality and has low robustness to frequency-based attacks such as filtering and compression. In the spatial domain, many steganography schemes based on LSB are proposed to improve the quality and security of hidden images. Chang et al. [
14] used the dynamic programming strategy to select the optimal replacement matrix and convert the confidential data into another value, which is then embedded in the least significant bit of the cover image. Chang et al. [
15] also considered a dynamic programming strategy using modular functions to generate alternative data embedded in cover images. Bedi et al. [
16] proposed an efficient spatial domain data hiding method, using the particle swarm optimization algorithm (PSO) to find the best pixel position to hide one image in another image by optimizing the similarity index. These authors extend the techniques in reference [
17] and use PSO to find the best pixel location.
In recent years, with the increasing attention and investment in covert communication technology all over the world, the means of steganography detection and analysis are becoming more and more sophisticated. The existing steganography algorithms are vulnerable to image processing attacks that damage image quality. In addition, in order to limit the channel capacity and not be suspected by third parties, the sender will actively process the steganographic image by adding noise or compression. In the image steganography technology based on the transform domain, secret information is embedded in the transform coefficients of the image. The data hiding method based on the transform domain overcomes the shortcomings of poor extraction ability and incompressibility against attacks in spatial domain technology. In this case, the host image is converted into the frequency domain by calculating the frequency coefficient of the host image. Then, the secret information is embedded by these coefficients, and the inverse transform is used to convert the image from the frequency domain to the spatial domain. Some common transform domain technologies include methods based on DFT (Discrete Fourier transforms), methods based on DCT (Discrete Cosine Transform), methods based on DWT (Discrete Wavelet Transform), and methods based on IWT (Integer Wavelet Transform) [
8,
18,
19]. Due to the widespread use of JPEG images, most of the steganography algorithms based on the transform domain choose the DCT domain of the JPEG image as the embedding domain. The image steganography in the transform domain is developed with the embedding of the discrete cosine transform (DCT) domain. In 2016, Rabie et al. [
20] proposed a DCT domain-embedding algorithm based on a global adaptive region. In [
21], Change proposed a modified quantization table that embeds encrypted information in a verified transmission domain with quantized DCT coefficients. In 2016, Saidi et al. [
22] discussed another steganography scheme based on DCT. The DCT coefficient is obtained by decomposition of the cover image. Chaotic mapping is used to select the embedding position, and the secret information is embedded bit by bit. The results show that the scheme has good concealment. In 2021, Dai et al. proposed a steganography algorithm based on DCT domain quantization-table modification and image scrambling [
23].
The research on steganography algorithms that are more robust and can extract more complete secret information from the attacked steganographic image has important practical significance and application value for privacy protection and information security. With the development of JPEG2000, Discrete Wavelet Transform (DWT) has been widely used in many image processing applications. Chan et al. [
24] proposed a steganography algorithm, which uses Haar discrete wavelet transform to convert spatial coverage image into frequency domain coverage image. Ghebleh et al. [
25] proposed a robust chaotic algorithm based on three-dimensional chaotic Cat mapping and DWT for three-dimensional chaotic images. Ramu et al. [
26] proposed a DWT-based steganography method that uses singular values to embed secret information and uses ant colony optimization to find a compromise between imperceptibility and robustness. In 2017, Miri proposed an adaptive image steganography technology based on DWT transform domain using genetic algorithm, in which the transformation of cover image is more compatible with human visual system [
27]. Compressed sensing is applied to secret data, and its singular value is embedded into the low-frequency sub-band of the cover. For large-scale multimedia applications, Li et al. proposed an image steganography technology that uses cosine transform to obtain an image steganography capacity of 21.5 bpp when the signal-to-noise ratio is 38.24 dB [
28]. Another high-capacity image steganography scheme is proposed by Rabie et al. [
29], which uses the multi-scale Laplacian pyramid of the cover image in wavelet domain to realize data embedding, and they use the method of curve fitting adaptive region to find the appropriate hiding position in the DCT domain. Thanki et al. proposed an image steganography technique based on Finite Ridge Transform (FRT) and Discrete Wavelet Transform (DWT). Applying Arnold scrambling to secret images, this hybrid scheme proves the results in terms of imperceptibility, robustness, and computational complexity [
30]. In 2020, Sharm proposed a safe, higher embedding capacity based on Discrete Wavelet Transform technology. Before embedding the correlation between the cover and the secret image, increase by multiplying some variables (1/k) by the secret image [
31]. In 2021, Chudhary et al. proposed an image steganography scheme based on spectral wavelet using SVD and Arnold transform, which improved the visual quality of steganography images [
32].
In order to solve the problem of poor quality of secret images extracted from steganographic images after image processing attacks, this paper proposes a dual-matrix decomposition image steganography scheme based on wavelet transform with multi-region coverage. (1) Transform the cover image to the transform domain based on the discrete wavelet transform and select the appropriate embedding area. (2) Perform Hessenberg matrix decomposition and SVD transformation on the selected transformation area to obtain singular values for embedding the secret. (3) The secret image is transformed by Arnold transform, and the secret information of the transformed image is embedded into the cover image. Multi-level discrete wavelet transform is used to protect the hidden secret information and reduce the loss of secret information when the steganographic image is attacked by image processing attack. In this paper, multi-level discrete wavelet transform and double-matrix decomposition are used to ensure the robustness of the steganographic scheme, and more complete secret information can be extracted from the attacked steganographic image. The hidden area with multi-region coverage ensures the concealment of the scheme so that it is not suspected by the third party and protects the security of secret information. A variety of image-processing attacks are performed on the steganographic image to check the robustness of the proposed scheme.
The arrangement of this paper is as follows:
Section 2 introduces the theoretical methods applied in this paper.
Section 3 introduces the image steganography scheme, including embedding method and extraction method.
Section 4 presents the results demonstration, performance analysis, and robustness test of the proposed scheme.
Section 5 concludes.
2. Materials and Methods
2.1. Image Wavelet Transform
The translation factor and scale factor in continuous wavelet transform are real numbers of continuous transformation. Therefore, it is necessary to discretize the continuous wavelet transform, retain more information as much as possible through less calculation, and obtain wavelet coefficients with lower redundancy, namely discrete wavelet transform.
In image processing, most of the signals are two-dimensional, even multi-dimensional. Therefore, wavelet analysis theory is more often used in the processing of two-dimensional or multi-dimensional signals. For two-dimensional discrete wavelet transform, it is defined as follows:
The inverse transformation is:
The application of wavelet transform in digital image is to decompose the image in two dimensions, and finally place sub-images in different spaces and different frequencies. The lower the resolution of the sub-image is, the more information it can contain.
After the image is decomposed by wavelet transform, the absolute value of the low-frequency sub-band coefficients is largest, and most of the energy of the image is concentrated in this part. The low-frequency sub-band can be further decomposed, and the transformed low-frequency sub-band is similar to the cover image. Compared with other transforms, the image still has the characteristics of the spatial domain and frequency domain of the original image after wavelet transform [
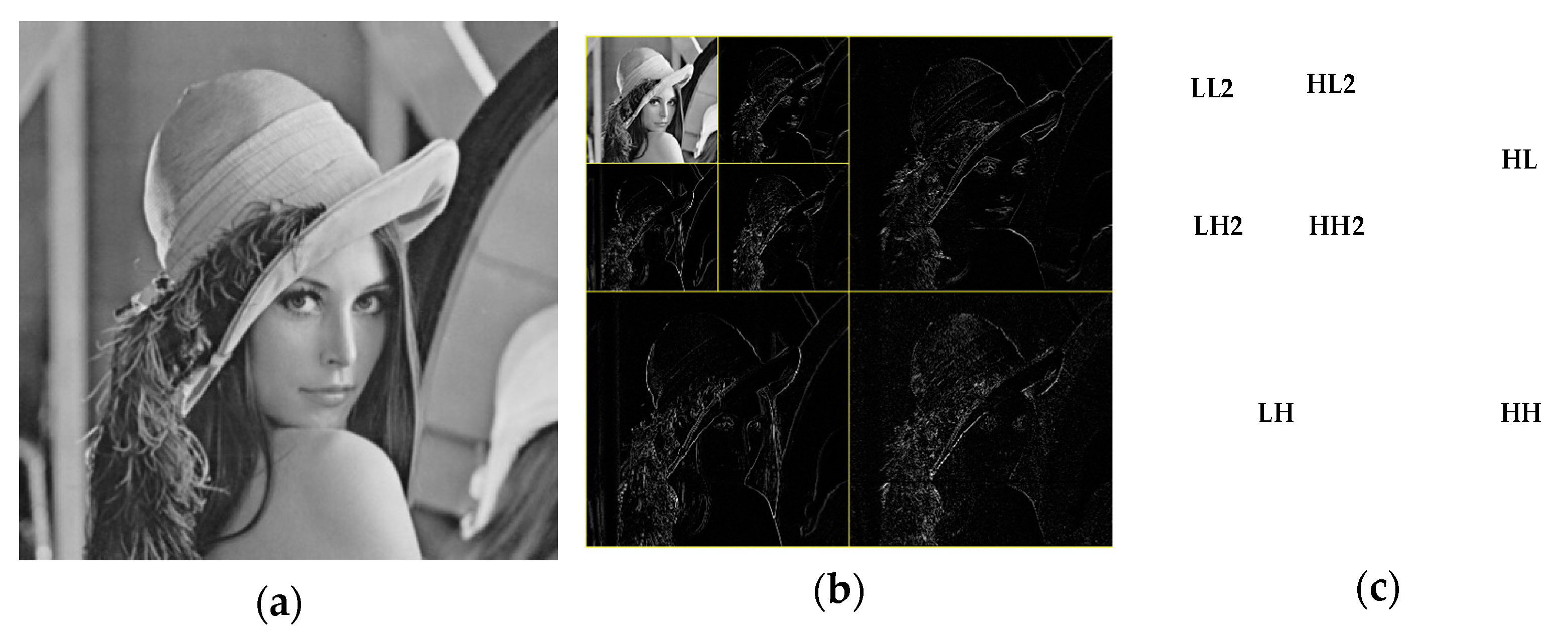
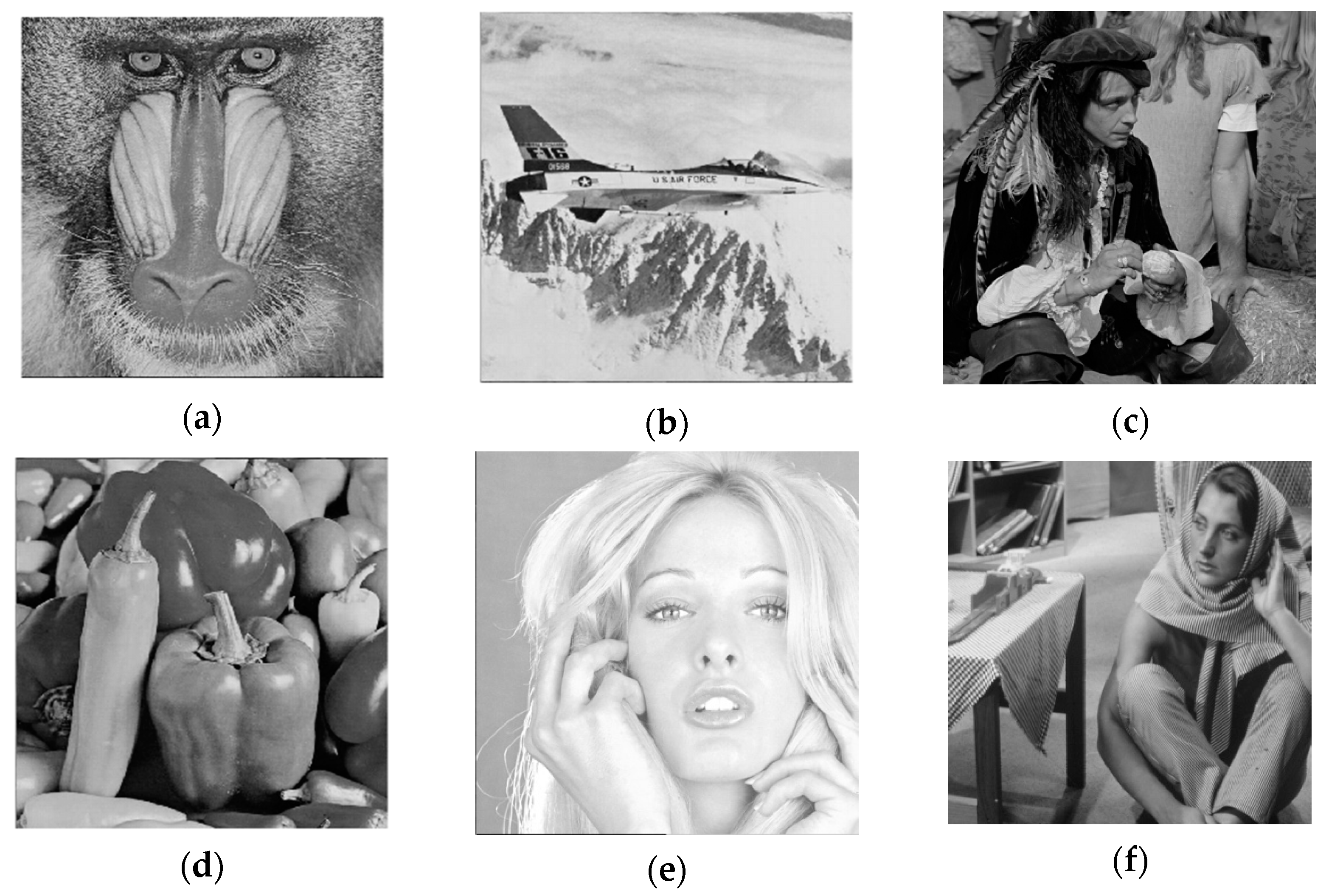
33]. The low-frequency coefficients correspond to the main features of the image, and the high-frequency part contains the information of the edge and texture of the image, as shown in
Figure 1.
The decomposition of the image by wavelet transform is to characterize the image in different frequency bands and spatial directions [
34]. The sensitivity of human eyes to different frequency bands is different. According to the different sensitivity of human vision to different frequency bands, we choose the most suitable position for image steganography to embed secret information in the image, so that the steganographic image has better concealment. At the same time, the image steganography technology in the wavelet domain can effectively resist the attacks of clipping, compression, and filtering.
Therefore, using wavelet transform to process the image to embed secret information can make steganography technology able to resist various attacks on the premise of guaranteeing the original quality of the image, and at the same time ensure the integrity of extracted secret information.
2.2. Arnold Transformation
Arnold transform was proposed by Vladimir Igorevich Arnold, a Russian mathematician. Arnold transform can replace the position of each pixel in the image to achieve the purpose of encryption, so it is mostly used in multimedia such as images to improve safety [
35].
The specific expression of Arnold transformation is:
where
x,
y represent the position of the pixel in the grayscale image before transformation;
xn+1,
yn+1 represent the pixel position after transformation;
a,
b are parameters and both are positive integers;
n represents the number of current transformations;
N is the length or width of the image, and mod is Modular operation.
In particular, when
a =
b = 1 and
N = 1, the Arnold transformation can be written as:
The two reasons that Arnold mapping can produce chaos are stretching and folding. Stretching refers to multiplying by matrix C to increase the value of x, y, and folding refers to taking the modulus to fold x, y back into the unit matrix. Due to xwthe two properties of stretching and folding, the two adjacent points are no longer adjacent after many iterations of transformation, which can be used to fully disrupt the position of the adjacent pixels of an image. The relevant information of the original image cannot be obtained from the image so that the purpose of protecting the image information can be achieved. It should also be noted that the Arnold transform is periodic, and it will return to the original state after many Arnold transformations. The number of iterations to return to the original state will be different with different image sizes, so we pay attention to the number of iterations when selecting images of different sizes.
2.3. Hessenberg Matrix Decomposition
Hessenberg matrix decomposition is a matrix decomposition method that is often used to decompose square matrices. If the elements of the matrix
H = (
hij)
n×nRn×n satisfy
hij = 0(
j >
i + 1), then
H is called the upper Hessenberg matrix, and its specific form is:
Suppose
X = (
aij)
RM×N, then there are orthogonal matrices
Q1,
Q2, …,
Qn−2, so that
X is transformed into an upper Hessenberg matrix through orthogonal similar transformation, that is
Qn−2, …,
Q2, Q1X Q1,
Q2, …,
Qn−2 =
H. From the above, we can acquire the calculation formula of Hessenberg matrix decomposition as follows:
where
P is an orthogonal matrix,
H is a Hessenberg matrix, and for any
i >
j + 1, the element
hi,j of
H is 0.
Hessenberg is usually calculated by the Houthor matrix, and the formula is as follows:
where
is a nonzero vector and
In is the identity matrix of
n×n.
Combining the above two formulas, the Hesseberg decomposition can be evolved into:
Suppose
A is an image block of size 4 × 4 as the formula (9), and after Hesseberg decomposition, that is [
P,6
H] =
hess(
A), we can acquire a unit matrix
P and an upper triangular Hessenberg matrix
H such as (10) and (11). In the
H matrix, the value of
H(2,2) is the largest, which represents most of the energy of the image block. Experimental studies have found that the
H(2,2) element has a certain numerical stability to external disturbances. From this perspective, the Hessenberg matrix decomposition of the image can achieve a more stable part of the image [
36]. In image steganography technology, the cover image is decomposed by Hessenberg matrix, and the secret information is embedded in the matrix obtained after decomposition, which can effectively improve the anti-attack performance.
2.4. Singular-Value Decomposition
Singular-value decomposition is a method of matrix analysis in which the matrix is processed based on the eigenvectors of the matrix. The singular vector of the matrix can be obtained through singular-value decomposition, maintaining the correlation of the rows or columns of the original matrix.
The singular-value decomposition of a matrix means that for a non-zero real number matrix A of any size
M × N, it can be expressed as the product of two-unit orthogonal matrices and a diagonal matrix [
37]. The singular-value decomposition can be written in the following form:
where
S is a singular-value matrix,
S = diag
, the diagonal elements of
S matrix are r singular values of matrix
A,
U and
V are two orthogonal matrices, and each column element of
U and
V represents the left singular vector and the right singular vector, respectively—that is,
,
.
Singular-value reconstruction is to inversely transform the singular-value matrix S and two diagonal matrices to form a new matrix. The secret information can be hidden by modifying the singular value in the singular-value matrix to form a new singular-value matrix to embed the secret information.
The singular value of the singular-value matrix represents the characteristic information of the image. The diagonal elements of the singular-value matrix after matrix transformation are arranged from large to small, and the value of the first diagonal element is larger than the other diagonal elements. Ignoring other singular values will hardly affect the reconstructed image. In addition, when the image is slightly disturbed, the diagonal elements of the singular-value matrix obtained through singular-value decomposition will not change significantly, and the singular-value decomposition of the matrix has the characteristics of rotation invariance. From this aspect, embedding the secret image after the singular-value decomposition of the image can improve the anti-attack performance of the algorithm.
2.5. Logistic Chaotic System
Chaos is an unstable state under certain conditions. Chaotic system has become one of the most popular tools in image encryption technology because of its uncertain chaotic behavior, unpredictable trajectory, universality, ergodicity, and many other excellent characteristics.
Logistic chaotic system is a classical chaotic system. Logistic chaotic map is very simple in mathematical form, but it has extremely complex dynamic behavior [
38]. Therefore, Logistic chaotic system is widely used in data security and secure communication. The mathematical expression of the logistic equation is:
𝜇 is the system parameter of the logistic equation, and the initial value of the system is set to 𝑥0(0 < 𝑥0 < 1). When 3.5699 < 𝜇 < 4, the system goes into chaos.
3. A Steganography Scheme of Dual-Matrix Decomposition Image with Multi-Region Coverage
This section mainly introduces the proposed dual-matrix decomposition image steganography scheme based on wavelet transform with multi-region coverage. It is mainly introduced from four aspects: (1) Select the embedding area of the cover picture. (2) The method and process of embedding the secret image. (3) The extraction process of the secret image. (4) The logistic chaotic encryption algorithm encrypts the key.
3.1. Hidden Region Selection in Wavelet Domain
There are many algorithms for embedding secret images into cover images. From the perspective of embedding, they are mainly divided into two different methods: spatial domain and transform domain. When these methods are implemented, they all need to embed the secret image through the coefficients of some transformations, but in the end, they all achieve the ultimate goal of embedding secret information by changing the grayscale values of some pixels. The image steganography scheme proposed in this paper is to perform multi-discrete wavelet transform on the cover image and embed the secret image in the selected hidden area in the wavelet domain of the cover image.
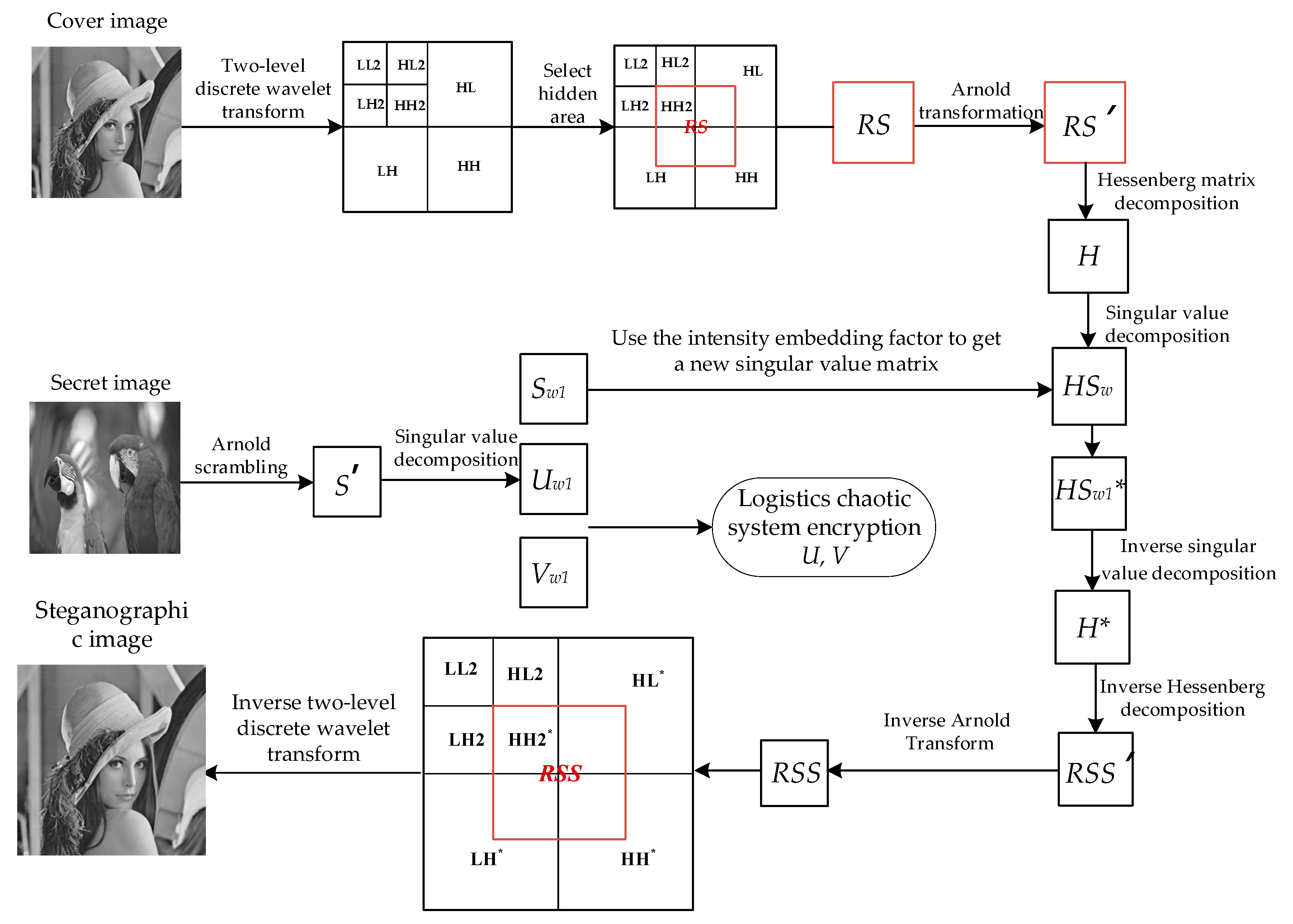
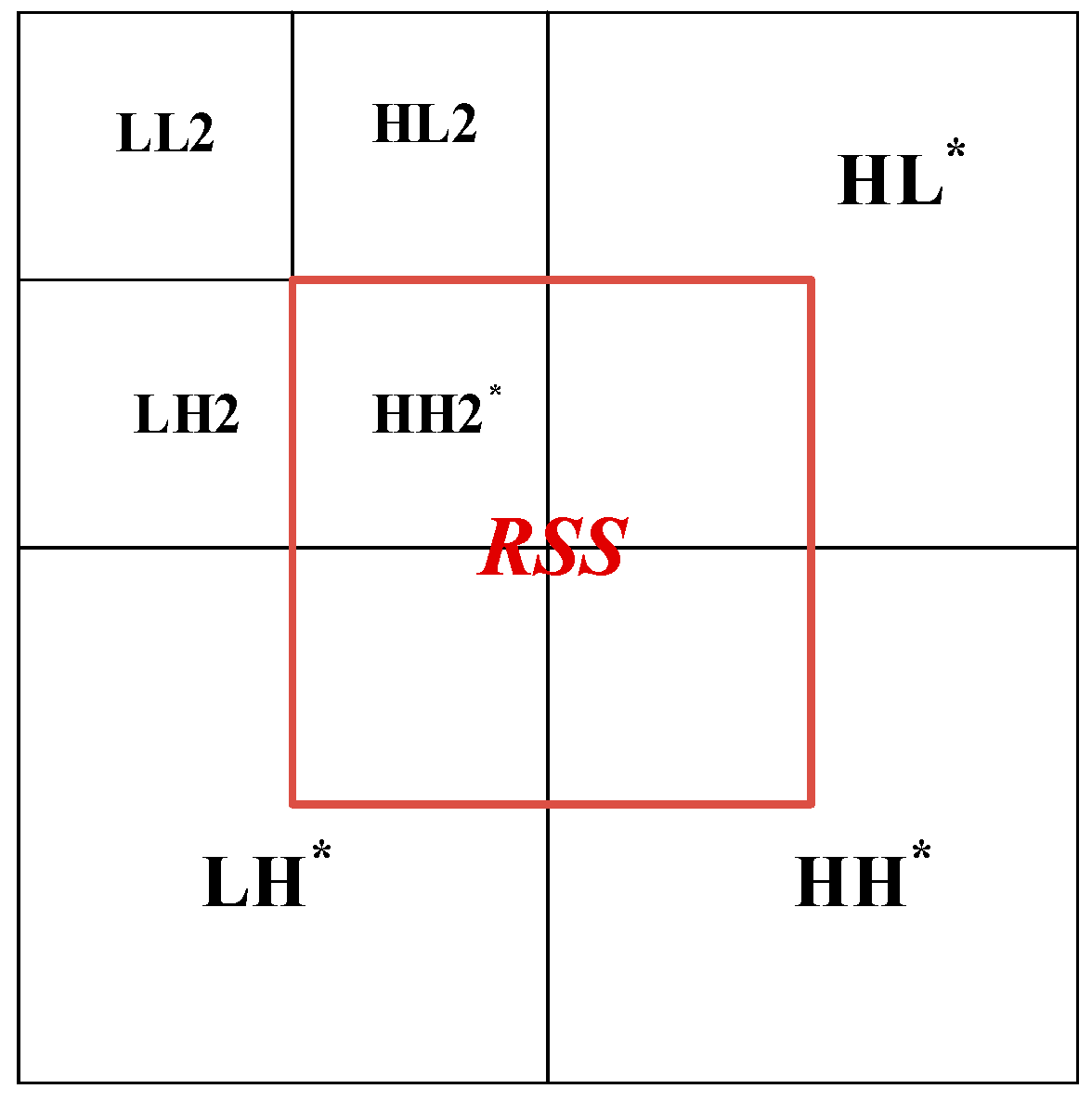
In this paper, the cover image is transformed by two-stage discrete wavelet transform. As shown in
Figure 2, the first-order low-frequency region contains most of the image energy corresponding to the main features of the image and the other parts contain the image edge and texture information, and the second-order component LL2 also contains most of the energy of the first-order component. In this paper, the region shown in
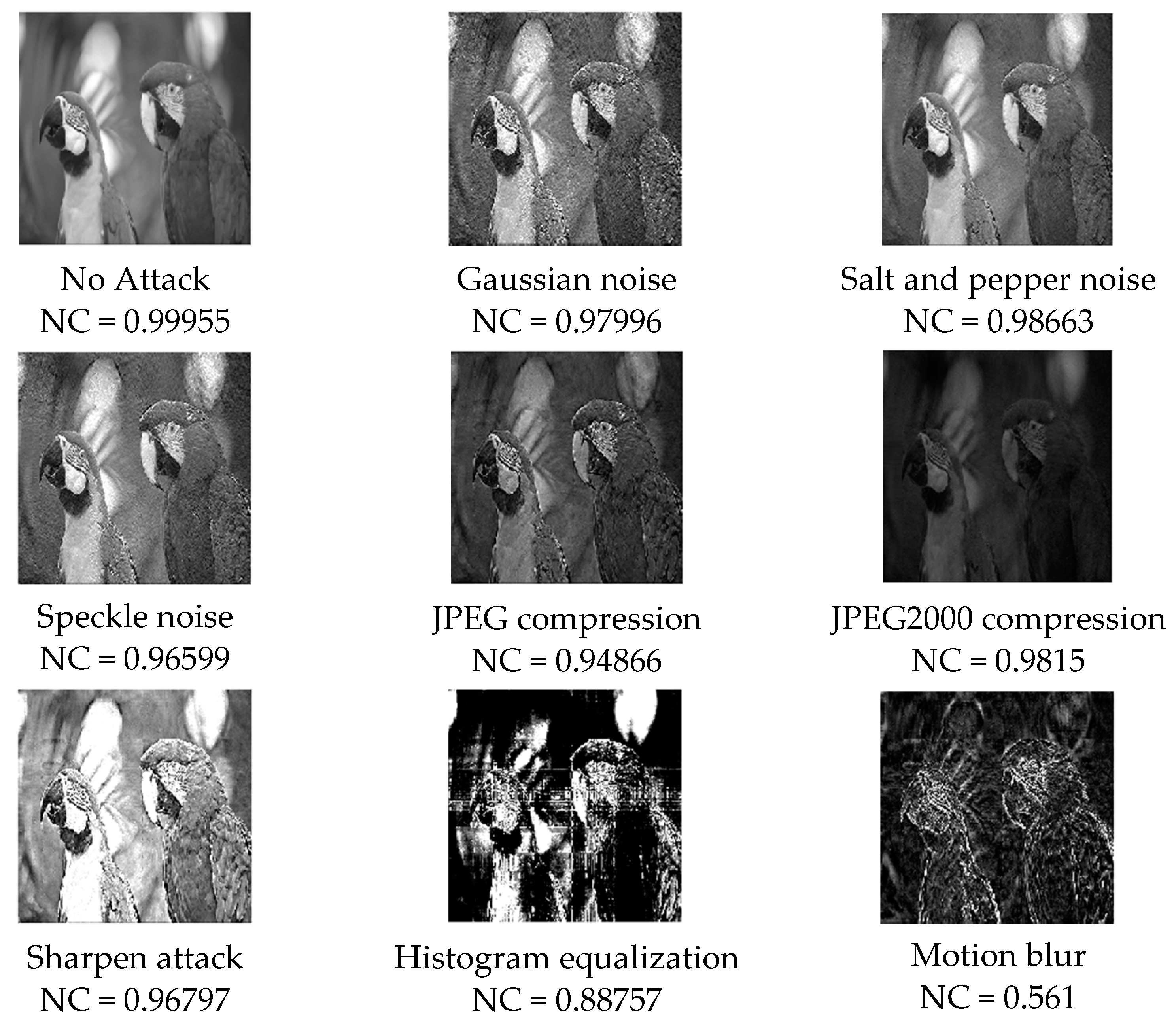
Figure 3 is selected as the embedded region, which is the middle part of the two-level discrete wavelet transform image, including the sub-band HH2 and some edge and texture information with a small contribution rate. Modifying the coefficient value of the selected hidden region has little impact on the overall image. Embedding the secret image in the selected region ensures the robustness and concealment of the steganography scheme.
3.2. Steganographic Embedding Algorithm for Secret Image
The input of the steganography algorithm is the cover image
C, the secret image
S, and embedding factor
. The output image is the steganographic image
C* with secret information. The size of the cover image is
M ×
M, the size of the secret image is
M/2 ×
M/2, and the size of the output image with secret information is
M ×
M. In this paper, Hessenberg matrix decomposition and singular-value decomposition are used to obtain the steganographic image in the embedding process. In addition, this paper selects an appropriate embedding strength factor
to ensure that the steganographic algorithm has better performance in terms of invisibility and robustness. The steps of secret image embedding are shown in
Figure 4. The specific embedding algorithm is Algorithm 1, as follows:
| Algorithm 1: The embedding algorithm |
| Input: Cover image C, Secret image S, embedding factor α. |
| Output: Steganographic image C*, Encrypted key matrix Uw1′, Vw1‘. |
| 1: [LL2, HL2, LH2, HH2, HL, LH, HH] = DWT2level(C) |
2: RS = [HH2, HL(1:128,129:256);LH(129:256,1:128), HH(1:128,1:128)]
3: RS’ = Arnold (RS)
4: P H PT = Hessenberg (RS’)
5: HUw ⋅ HSw HVw = SVD (H)
6: S’ = Arnold (S)
7: Uw1 Sw1 Vw1T = SVD (S’)
Sw1
9: H* = HUw HSw1* HVw
10: RSS’ = P H*PT
11: RSS = Rearnold(RSS’)//The hidden area after embedding secret information is shown in the Figure 5. In Figure 5, HL*, LH*, HH* and HH2* are HL, LH, HH, and HH2 embedded with secret information respectively.
12: HH2* = RSS (1:128,1:128)
13: HL* = HL, LH* = LH, HH* = HH
14: HL*(1:128,129:256) = RSS (129:256,1:128)
15: LH*(129:256,1:128) = RSS (1:128,129:256)
16: HH*(1:128,1:128) = RSS (129:256,129:256)
17: C* = IDWT2level [LL2, HL2, LH2, HH2*, HL*, LH*, HH*]
18: (Uw1′, Vw1‘) = ChaoticEncrypt ( Uw1, Vw) |
Among them, Uw1 and Vw1 are the keys when extracting secret images. To ensure the security of the keys, the encryption algorithm of logistics chaos system is used to encrypt them to obtain Uw1′ and Vw1‘.
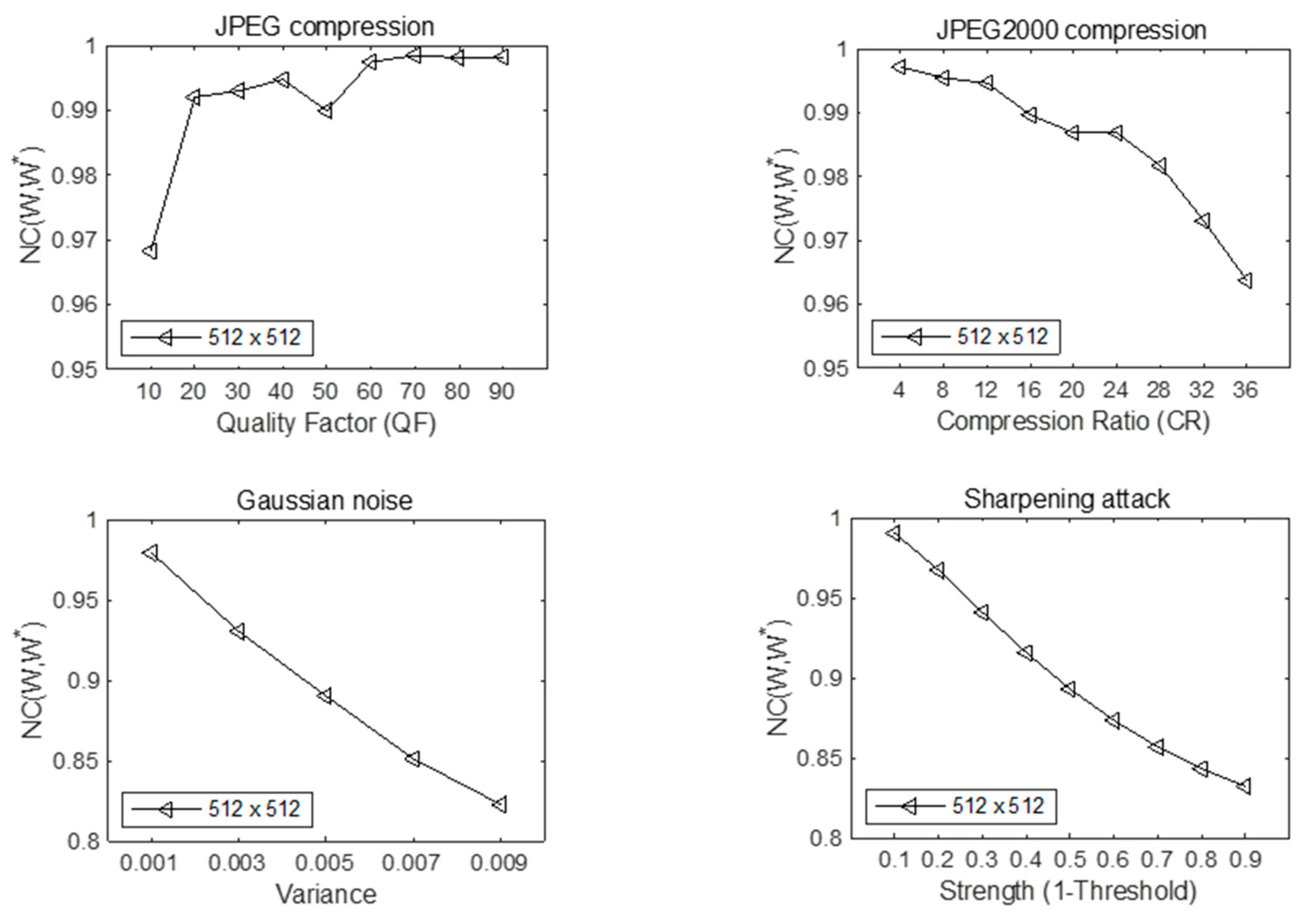
In the embedding algorithm, the secret information is multiplied by the embedding strength factor and then added to the singular value obtained by the two-level matrix decomposition of the selected hidden area to obtain the singular value of the steganographic image, which achieves the purpose of embedding secret information. The larger the value of , the greater the difference between the singular value after embedding the secret information and the original singular value and the greater the difference between the steganographic image and the original cover image. However, the larger the value of , the stronger the ability to extract the secret information from the attacked steganographic image when the steganographic image is attacked. The smaller the value of , the smaller the difference between the singular value after embedding the secret information and the original singular value, and the smaller the difference between the steganographic image and the original cover image. However, the small value of has poor ability to extract the secret information from the attacked steganographic image when the steganographic image is attacked, so it cannot recover the high-quality secret image. In other words, the larger the value of , the stronger the anti-attack performance and the worse the concealment of secret information; the smaller the value of , the worse the anti-attack ability of steganographic image and the better the concealment of secret information. Only selecting the appropriate embedding factor can ensure the ability of extracting secret information from the attacked image and the high concealment of secret information.
The embedding algorithm uses singular-value decomposition and Hessenberg matrix decomposition. The elements in the matrix obtained by singular-value decomposition and Hessenberg matrix decomposition have a certain stability when subjected to external disturbance, which improves the robustness of the steganography scheme. The appropriate embedding strength factor and the hidden area with multi-region coverage ensure the concealment of secret information. Also, the embedding algorithm has low complexity and is easy to implement and apply.
3.3. Steganographic Extraction Algorithm of Secret Image
In the secret image extraction algorithm, the input is the cover image embedded with secret information—steganographic image
C*, embedding factor
and the key
Uw1,
Vw1, and the output is the extracted secret image—extracted image. The overall process of the extraction algorithm is shown in
Figure 6, and the specific extracting algorithm is Algorithm 2, as follows:
| Algorithm 2: The extracting algorithm |
| Input: Steganographic image C*, Encrypted key matrix Uw1′,Vw1′. |
| Output: The extracted Secret image C’. |
1: [LLw2, HLw2, LHw2, HHw2, HLw, LHw, HHw] = DWT2level (C*)
2: RSw = [HHw2, HLw(1:128,129:256); LHw(129:256,1:128), HHw(1:128,1:128)]
2: RSw* = Arnold (RSw)
3: (Uw1, Vw1) = ChaoticDecrypt (Uw1′, Vw1′)
4: PwHwPwT = Hessenberg (RSw*)
5: HUw*HSbw*HVw*T = SVD (Hw)
6: Sw1* = (HSbw1*-HSw)/α
7: C1′ = Uw1 Sw1* Vw1T
8: C’ = Rearnold (C1′) |
3.4. Key Encryption Algorithm of Logistic Chaotic Map
The key is very important for image extraction. Only when the security of the key is ensured can the secret image be successfully extracted. Chaotic system is a cryptographic system with uncertain, nonlinear, and random behavior. It has many characteristics, such as ergodicity, sensitivity to the conditions of initial value occurrence, strong unpredictability, and randomness. Using chaotic system to encrypt the key can ensure the randomness and security of the encrypted key.
The steps of the logistic chaotic encryption algorithm for key encryption are as follows:
Step 1. Determine the parameters and initial values of the logistic chaotic mapping and substitute them into the equation of the Logistic mapping to iterate M × N times (M × N is the size of the key matrix, M is the length and N is the width) and generate the one-dimensional floating point chaotic sequence CL with the length of M × N and the value between (0,1).
Step 2. Each element in the sequence CL is transformed by multiplying 255 to (0, 255), then the integer sequence between (0, 255) is obtained, and the new integer sequence is transformed into an M × N two-dimensional matrix with the same size as the key matrix.
Step 3. XOR the corresponding bits of the two-dimensional matrix obtained through the chaotic system and the key matrix to obtain the encrypted key.
5. Conclusions
In this paper, a double-matrix decomposition image steganography scheme with multi-region coverage is proposed. This scheme solves the problem of poor quality secret-image extraction when the steganographic image is attacked by image processing or the sender takes the initiative to attack the steganographic image.
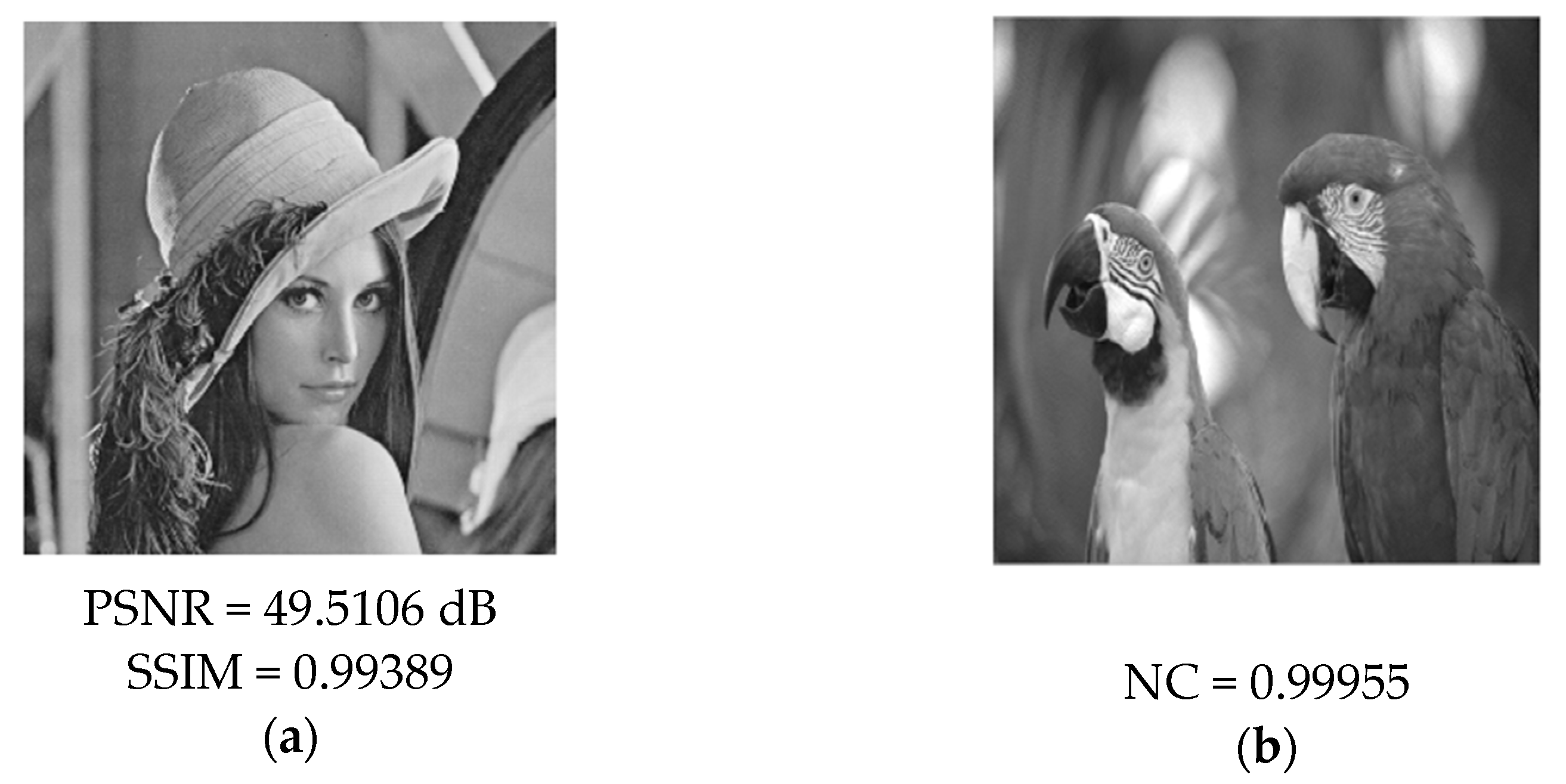
Firstly, the stability of the matrix obtained by Hessenberg matrix decomposition and singular-value decomposition under disturbance is introduced. The steganography scheme of this paper is proposed by using the characteristics of these two kinds of matrix decomposition. The second-order wavelet transform is performed on the cover image, and the hidden regions covering multiple sub-bands are selected in the wavelet domain of the cover image. As the matrix after Hessenberg matrix decomposition has a certain stability to the numerical disturbance, in order to enhance the robustness of the scheme, the hidden area selected in the wavelet domain is Arnold transformed and then subjected to Hessenberg matrix decomposition to obtain the matrix H; the matrix H is decomposed by singular-value decomposition, and the obtained singular-value matrix can remain stable when disturbed. The secret information is embedded into the singular-value matrix of the cover image through the embedding factor, and the steganographic image is obtained through two-level inverse matrix decomposition and inverse Arnold transformation. The PSNR value of the steganographic image is as high as 49.5106dB and the SSIM is 0.99389. Embedding the secret information into the cover image has little effect on the quality of the cover image. It has been proved that the scheme proposed in this paper has a strong invisibility. The NC value of the secret image extracted from the steganographic image is more than 0.9. Most of the information in the secret image can be extracted even if the attack intensity is strong under the dynamic attack coefficient. The robustness of the proposed steganography algorithm is proved.
The steganography scheme proposed in this paper is also suitable for when the cover image is RGB image and the secret image is a grayscale image. The secret image can be embedded into any component image of the cover image, and the grayscale image can be hidden in the color image, which also reflects the excellent concealment and robustness of the steganography scheme. When the secret image and the cover image are both color RGB images, embedding the three component images of the secret image into the three component images of the cover image will degrade the quality of each component image of the cover image. The final steganographic image is quite different from the original image and the existence of the secret image cannot be hidden, so it is easy to be suspected by the third party. This problem is also an important direction for color image steganography in the future.