Abstract
In this paper, we consider the trust degree of a jammer, defined as the probability that the jammer cooperates to secure the legitimate transmission, and investigate its influence on confidential cooperative communication. According to the trust degree, we derive the closed-form optimal transmit signal-to-noise ratio (SNR) of the confidential message, , to maximize the expected secrecy rate, and further obtain the relationship between and the trust degree associated with the transmit SNR at the transmit user and channel gains. Simulation results demonstrate that the trust degree has a great effect on the transmit SNR of the confidential message and helps improve the performance of confidential cooperation in terms of the expected secrecy rate.
1. Introduction
With the rapid growth of communications between socially-connected users, not only physical parameters, e.g., channel qualities and traffic demands, but also the social relationship among users, such as kinship, friendship, and acquaintance, have been taken into account as key design parameters for efficient cooperative communications [1,2,3,4,5]. As the most fundamental concept, the trust degree of the social relationship is interpreted as the degree that reveals how willingly a node helps other nodes’ communication in cooperative communications [5]. In other words, the node would like to cooperate with others by consuming their own resources if they have a close relationship, i.e., a high trust degree, which can be evaluated and quantified based on the previous direct or indirect information according to observations of behavior [6].
In the literature, the trust degree has triggered plenty of research interest in various fields, including content caching, mobile social communications, and especially cooperative communications [1,2,3,4,5]. More specifically, the optimal social-aware relay selection strategy was proposed in [1], while a partner selection algorithm was designed based on the social-position relationship in [2]. The trust degree-based beamforming and transmission strategies were investigated for one relay in [3] and two relays with different trusts in [4] for a MISO cooperative communication system. Meanwhile, the traffic demand-driven user cooperation strategies were considered for various antenna configurations based on the trust degree in [5].
Due to the broadcasting nature of wireless mediums, physical (PHY)-layer security has also drawn significant attention in communication networks [7,8,9,10,11]. Specifically, the authors in [8] gave a constructive survey on threats and attacks on mobile networks, while a comprehensive survey on cooperative relaying and jamming strategies for physical layer security was presented in [9]. Meanwhile, the performance analysis of mmWave-overlaid microwave cellular networks was given in [10] from the security perspective, and secrecy analysis with passive eavesdroppers by using partial cooperation was investigated in [11]. Furthermore, with the rapid development of social awareness networks, the combination of the trust degree and PHY-layer security with application to cooperative communications has attracted plenty of research [12,13,14,15]. To be specific, the authors in [12] treated potential eavesdroppers as relays to transmit messages and maximize the expected secrecy rate according to their trustworthiness, instead of regarding them as wiretappers all the time. In [13,14], trust degree-based cooperative secure transmission strategies were proposed, and users with sufficiently high trust degrees would cooperate to transmit data or jamming signals. In [15], jamming-aided cooperative cooperation based on trust degree was investigated to maximize the security rate of the data transmission for P2P communications, where the authors applied a brute-force approach to search over all possible power allocations of the confidential message and jamming signal. However, the trust degree in [13,14] was exploited to choose trustworthy users (jammer [13], jammer and relay [14]) and filter out untrustworthy users (dummy nodes), and the explicit relationship between power allocations and trust degree had not been investigated and given in [15]. Therefore, the characteristics of the jammer’ trust degree were not fully utilized to effectively design cooperative secure transmission strategies, and the insight into how the trust degree affects the confidential cooperation was not explicitly investigated and well presented.
Motivated by the aforementioned research and problems, we have observed that the trust degree plays a significant role in cooperative secure communications. Hence, in this paper, we consider the probability that the jammer cooperates in secure legitimate transmission as its trust degree and investigate its influence on the performance of confidential cooperative communications. Different from [15], we not only consider the transmit signal-to-noise ratios (SNRs) of the confidential message and jamming signal, but also investigate the influence of artificial interference at the transmit user (Tu) in the case that the jamming signal from the jammer is not sufficient when the channel gain between the jammer and eavesdropper is weak and obtain their optimal transmit SNRs in closed-form to maximize the expected secrecy rate according to the trust degree. Meanwhile, we further achieve some meaningful results based on the relationship among the trust degree, channel gains, and the transmit SNR at Tu.
Notation: For a complex scalar x, its complex conjugate is denoted by . and denote the statistical expectation and complex Gaussian distributions, respectively.
2. Trust Degree and System Model
2.1. Trust Degree
With the rapid growth of online social networks, more and more people are getting involved in online social interactions. Therefore, the social relationship has emerged as an important issue to investigate how the degree of closeness of the social relationship between users affects their communication strategies [5,16,17,18]. In the cooperative communication systems, the trust degree can be interpreted as the degree that reveals how much a node is willing to help the communication of the other node [1,3,5]. Similarly, in our system model, the trust degree between and , , is defined by the probability that helps to secure the transmission between and , and thus, is a value in the range of .
In the literature, the trust degree has been evaluated and quantified in various ways [6,19,20,21,22,23]. In emergency networks such as disaster relief and public safety networks, the most trustworthy nodes would be those in the immediate region, so the trust degree can be measured based on the proximity between nodes, e.g., physical distance [19]. In general mobile networks, the trust degree can be evaluated by the observations of the previous behaviors of the node [6,20,21,22,23]. In [22,23], the trust degree was determined using the Bayesian framework. In the Bayesian framework, the trust degree is given by the ratio of the observations of the positive behavior among total observations, where the positive behavior is that the node behaves in the predefined way of the network. Similar to [23], in this paper, the positive behavior is defined by jammer, which helps to secure the transmission of Tu, and hence, Tu can estimate the trust degree based on the historical observations of the positive behavior of jammer. The trust degree can also be updated according to new observations. However, when the number of observations is sufficiently large, the trust degree will have ignorable change according to new observation, and it will be more like a constant. Therefore, in our system model, we assume that the trust degree remains unchanged during the transmission [5].
2.2. System Model
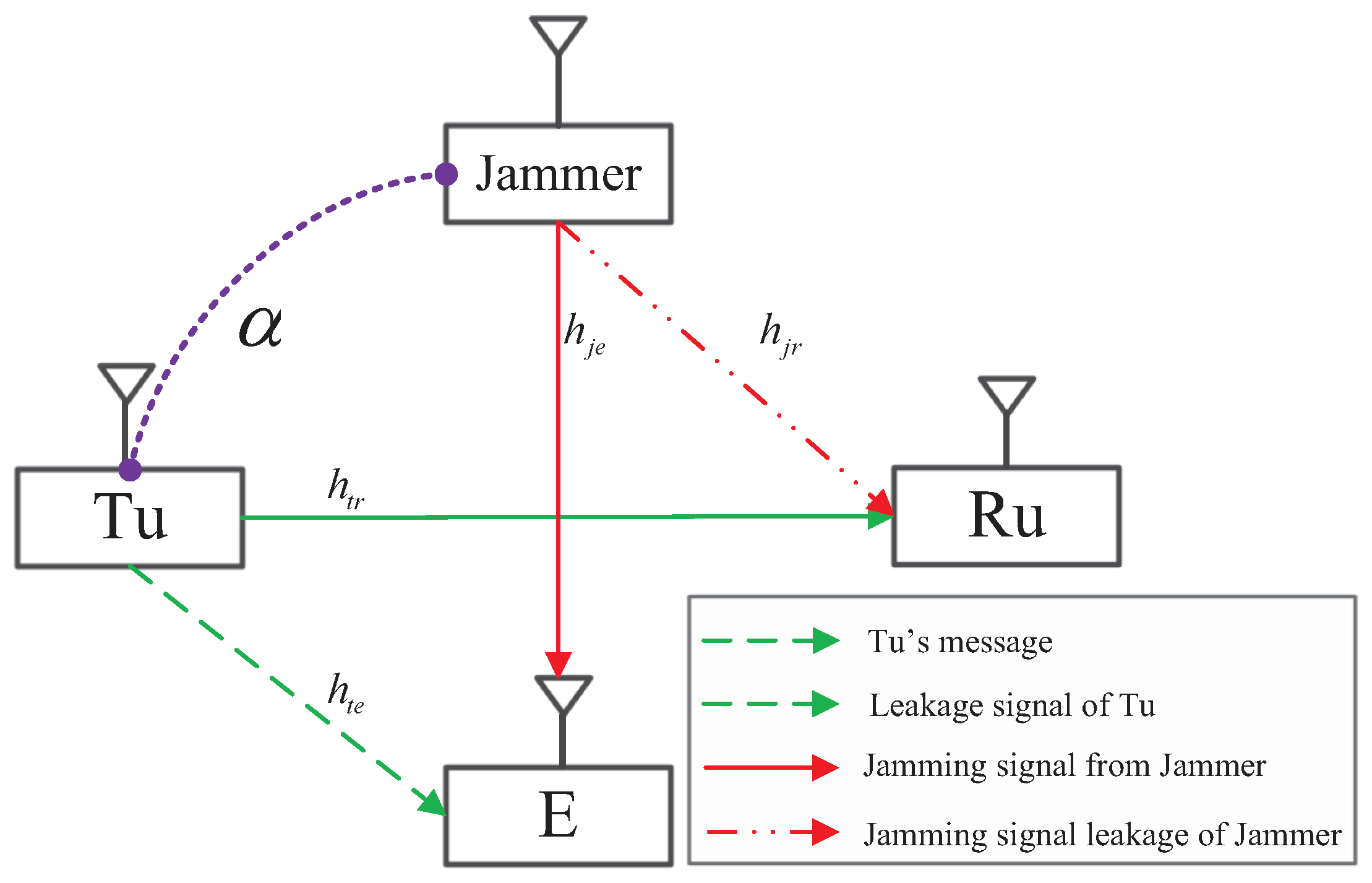
Consider a user cooperation network as shown in Figure 1, where there are four single-antenna nodes, including a Tu, a receive user (Ru), a jammer, and an eavesdropper, and we denote them by , , , and , respectively. The channels from to and , and from to and are denoted by , , , and , where all of them follow a complex Gaussian distribution with zero mean and different covariances, , , m and , respectively.
Figure 1.
System model. Tu, transmit user; Ru, receive user; E, Eavesdropper.
In this paper, we consider that will transmit the jamming signal to confound in order to help the legitimate transmission between and based on trust degree , which characterize the willingness that cooperates with for secure communications, i.e., helps with high probability when the trust degree is high. In this system, we consider the following two transmission strategies for confidential communications:
(a) Direct transmission: does not help to confound with jamming signal , and thus, transmits artificial interference, , together with a confidential message, , to keep its transmission secure, where and are independent. In this strategy, the transmit data at and are written as , while and , where and is the maximum transmit budget at .
(b) Cooperative transmission: transmits jamming signal to guarantee additionally the secure transmission between and and helps to reserve more power for the confidential message at . However, also needs to generate artificial interference for this strategy in case the jamming signal from the jammer is not sufficient when channel gain is small. Thus, the transmit data at and are given by , while , where and is the maximum transmit budget at .
According to the above strategies, the expected secrecy rate with respect to (w.r.t.) trust degree , the similar structure of which was given in [15], is obtained by:
in which we assume that and are prior-known at , and can completely cancel and from its received signal, which is a common assumption used in [12,24]. Notice that the information of jamming and artificial interference can be shared through an alternative wired connection between the transmitter or jammer and the receiver. In (1), and . The channel gains are defined as and . The transmit SNRs are given as and , where is the variance of the complex Gaussian distribution, , associated with the additive white Gaussian noise (AWGN) at and . The first term of (1) denotes the secrecy rate at obtained by the direct transmission strategy when does not help with the possibility , while the second term represents the secrecy rate achieved by the cooperative transmission when helps to jam with the possibility .
3. Problem Formulation and Solution
From (1), it is noted that for given , (1) is a monotonic increasing function w.r.t. , and thus, the optimal transmit SNR of artificial interference that maximizes (1) is achieved when i.e., , where . Meanwhile, it also applies to the case that for given , the optimal transmit SNR of the jamming signal is , which maximizes (1). Therefore, the problem that maximizes (1) can be formulated as:
where:
To maximize the expected secrecy rate in , the optimal transmit SNR of confidential message, , at can be achieved resorting to the following theorem.
Theorem 1.
For given channel conditions and transmit SNRs, and , the optimal transmit SNR of confidential message, , that maximizes the expected secrecy rate at is obtained as:
where , ,
in which , , and . It is true that , and the proof is given as:
Proof.
Define . With some mathematic manipulations, we can obtain:
Based on the property of the derivative, it is straightforward to know that is a decreasing function w.r.t. for , and . □
Proof.
The proof of Theorem 1 is presented in Appendix A. □
Notice that the one yielding the larger expected secrecy rate is regarded as between and ; meanwhile, the optimal transmit SNR of artificial interference is given by . To get a better insight into the relationship between the optimal transmit SNR of the confidential message, , and trust degree , we have the following corollary.
Corollary 1.
When the transmit SNR of the jamming signal goes to infinity, i.e., , the optimal transmit SNR of the confidential message, , can be obtained as:
where , , , and .
Proof.
The proof is given in Appendix C. □
Remark 1.
From Corollary 1, we observe that the optimal transmit SNR of the confidential message, , is mainly determined by the relationship among the trust degree, channel qualities, and the transmit SNR at . If the eavesdropping channel quality is better than that of the legitimate channel such that , it is not secure to transmit any confidential message when α is small. With growing α within a moderate range, the transmit SNR of the confidential message basically depends on α. More specifically, will reduce the power for artificial interference and allocate more power for the confidential message to exploit the cooperation of fully. Furthermore, when helps to jam with high probability, equivalently α is high, relies on to guarantee secure transmission and assigns all the power for confidential message. Notice that when the legitimate channel quality is good such that , it is still secure to send the confidential message with an appropriate transmit SNR even if α is small.
4. Simulation Results
In this section, we evaluate the performance of the trust degree-based confidential cooperative communication and use the average gains of channel elements as dB, and the expected secrecy rates are averaged over channel realizations.
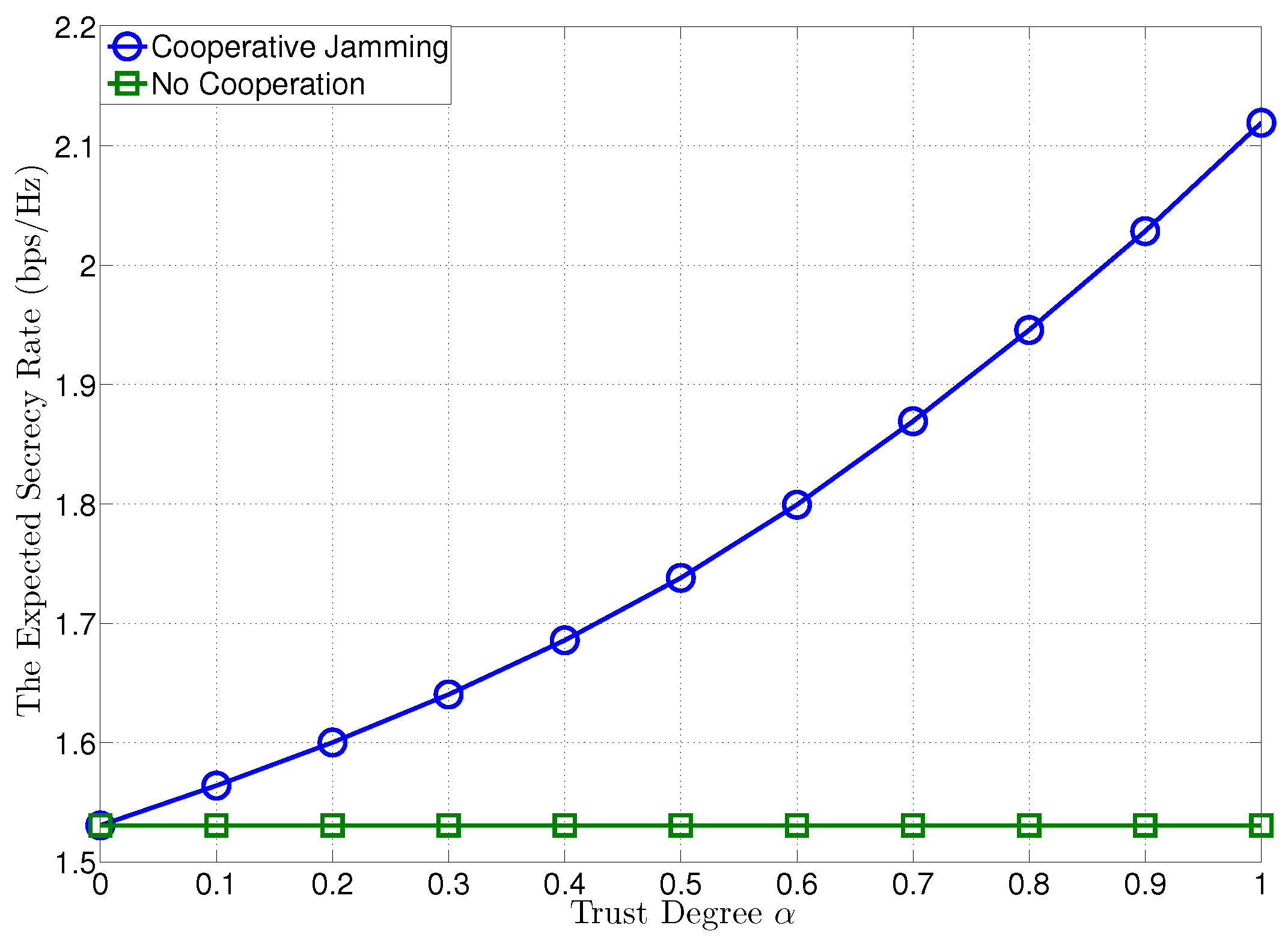
In Figure 2, we plot the expected secrecy rates at versus the trust degree of , when the transmit SNRs at and are given by dB. To compare with the proposed confidential cooperation scheme, we also plot the expected secrecy rate of the no cooperation case (NCC) (). For the proposed confidential cooperation, the optimal transmit SNR of the confidential message at for cooperation is obtained as in Theorem 1. In Figure 2, it is certified that the expected secrecy rate can be significantly improved by the jammer’s cooperation and increased with growing the trust degree of , yielding a higher expected secrecy rate than NCC.
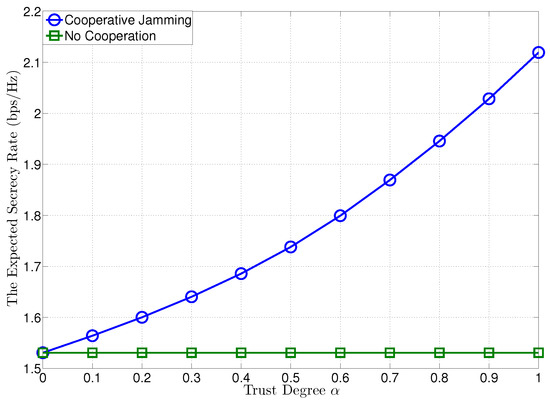
Figure 2.
The expected secrecy rate versus trust degree , where dB.
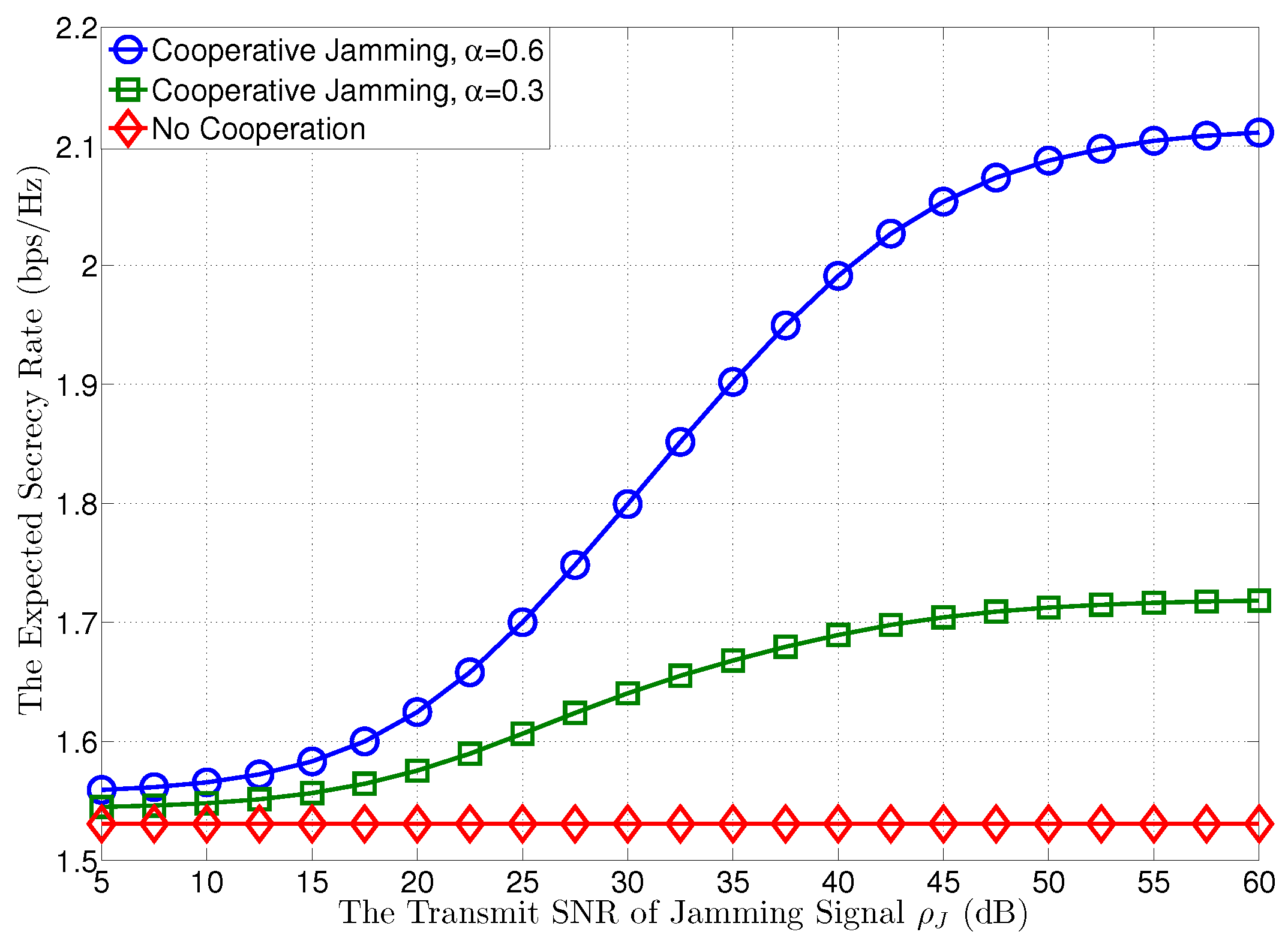
In Figure 3, we plot the expected secrecy rates at versus the transmit SNR of the jamming signal at , when the transmit SNR at is given by dB. In this figure, we first observe that when the transmit SNR of the jamming signal increases from 5 dB to 60 dB, i.e., goes to infinity, as shown in Corollary 1, the expected secrecy rate at can be increased through the cooperation of , and will assign more power for the confidential message with growing to achieve a higher expected secrecy rate. However, the expected secrecy rate does not increase all the time and will become saturated with the growth of , as shown in (A5), which has no relationship with when goes to infinity.
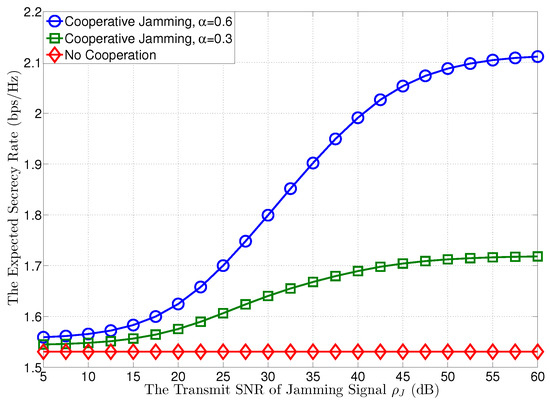
Figure 3.
The expected secrecy rate versus the transmit SNR of jamming signal , where dB.
5. Conclusions
In this paper, we investigated the confidential cooperative communication according to the jammer’s trust degree and exploited its characteristics to design efficient cooperative strategies. To maximize the expected secrecy rate, we derived the closed-form optimal transmit SNR of the confidential message based on the trust degree and observed that the expected secrecy rate will become saturated along with the increasing . Simulation results showed that will achieve a better performance with more power assignment for the confidential message instead of artificial interference with the growing trust degree of , which has a great influence on the performance of confidential cooperation in terms of the expected secrecy rate.
Author Contributions
Conceptualization, M.Z.; investigation, M.Z.; methodology, D.L.; supervision, W.F.; writing, original draft, M.Z.; writing, review and editing, H.G; all authors have read and approved the final manuscript.
Funding
This work of Mingxiong Zhao is supported in part by the National Natural Science Foundation of China under Grant 61801418, in part by Yunnan Applied Basic Research Projects under Grant 2019FD-12, in part by the Open Foundation of Key Laboratory in Software Engineering of Yunnan Province under Grant 2017SE203. This work of Hui Gao is supported by the National Natural Science Foundation of China under Grant 61401041 and 61671072.
Conflicts of Interest
The authors declare no conflict of interest.
Appendix A. Proof of Theorem 1
If , from (3), we first deal with the operation of in (3) and consider two conditions (i) and (ii) to make the first and the second term in (3) non-negative. Notice that and . According to (i) and (ii), we investigate (3) and solve as follows:
(1) If , we obtain , and .
(2) If ,
which is a concave function w.r.t. . Resorting to , we can get . Based on whether lies in , different situations are given as follows:
(3) If or , where the boundary point can be included in this interval without affecting the optimal transmit SNR of confidential message , the formulation of is the same, given by:
which is concave w.r.t. , and the proof is given in Appendix B. With the help of factorization, the optimal transmit SNR of the confidential message that maximizes (A2) is obtained by using to get , which is part of and in Theorem 1. Notice that it is necessary to check the feasibility of whether it lies in . If not, the boundary point is chosen as due to the concavity of (A2), and thus, the result in the second part of (2) in this Appendix can be classified in this part.
(4) If , we obtain , and the formulation of is given by (A1). Resorting to , we can get . Based on the feasibility check, we can get the following results:
- If , , the optimal transmit SNR of the confidential message is obtained by due to the concavity of (A1);
- If , , the optimal transmit SNR of the confidential message is obtained by ;
- If , , the optimal transmit SNR of the confidential message is , and this result can be categorized into (3) in this Appendix.
If , the formulation of is given in (A2) with , and the optimal transmit SNR of the confidential message is similar to that in (3).
Appendix B. Proof of the Concavity of (A2)
The following proof is to show the concavity of (A2). We first obtain the derivative of (A2) w.r.t. as:
To know whether (A2) is concave or not w.r.t , we further obtain its second derivative as:
Based on the expression of above, the second derivative is negative, and thus, (A2) is concave w.r.t. [25].
Appendix C. Proof of Corollary 1
When , we only need to consider Case (3), Case (4), and the case when in Appendix A. If , (3) is recast as follows:
(1) If ,
which is concave w.r.t. . Resorting to , we have . Based on whether lies in , different situations are given as:
(2) If , where the boundary point can be included in this interval without affecting the optimal transmit SNR of confidential message , , and the optimal transmit SNR of the confidential message is .
If , the formulation of is the same as (A5) with . Due to its concavity w.r.t. , we can get resorting to . Based on whether lies in , the following different situations are given as:
- If , , the optimal transmit SNR of the confidential message is ;
- If , , the optimal transmit SNR of the confidential message is due to the concavity of (A5).
References
- Zhang, M.; Chen, X.; Zhang, J. Social-aware relay selection for cooperative networking: An optimal stopping approach. In Proceedings of the 2014 IEEE International Conference on Communications (ICC), Sydney, Australia, 10–14 June 2014; pp. 2257–2262. [Google Scholar]
- Mao, H.; Feng, W.; Zhao, Y.; Ge, N. Joint social-position relationship based cooperation among mobile terminals. IEEE Commun. Lett. 2014, 18, 2165–2168. [Google Scholar] [CrossRef]
- Ryu, J.Y.; Lee, J.; Quek, T.Q. Trust degree based beamforming for MISO cooperative communication system. IEEE Commun. Lett. 2015, 19, 1957–1960. [Google Scholar] [CrossRef]
- Ryu, J.Y.; Lee, J.H. Trust Degree-Based MISO Cooperative Communications with Two Relay Nodes. Wirel. Commun. Mob. Comput. 2019. [Google Scholar] [CrossRef]
- Zhao, M.; Ryu, J.Y.; Lee, J.; Quek, T.Q.; Feng, S. Exploiting trust degree for multiple-antenna user cooperation. IEEE Trans. Wirel. Commun. 2017, 16, 4908–4923. [Google Scholar] [CrossRef]
- Sun, Y.L.; Han, Z.; Yu, W.; Liu, K.R. A Trust Evaluation Framework in Distributed Networks: Vulnerability Analysis and Defense Against Attacks. In Proceedings of the 25th IEEE International Conference on Computer Communications (INFOCOM 2006), Barcelona, Spain, 23–29 April 2006; pp. 1–13. [Google Scholar]
- Zhao, M.; Wang, X.; Feng, S. Joint Power Splitting and Secure Beamforming Design in the Multiple Non-Regenerative Wireless-Powered Relay Networks. IEEE Commun. Lett. 2015, 19, 1540–1543. [Google Scholar] [CrossRef]
- Mavoungou, S.; Kaddoum, G.; Taha, M.; Matar, G. Survey on threats and attacks on mobile networks. IEEE Access 2016, 4, 4543–4572. [Google Scholar] [CrossRef]
- Jameel, F.; Wyne, S.; Kaddoum, G.; Duong, T.Q. A comprehensive survey on cooperative relaying and jamming strategies for physical layer security. IEEE Commun. Surv. Tutor. 2018. [Google Scholar] [CrossRef]
- Vuppala, S.; Tolossa, Y.J.; Kaddoum, G.; Abreu, G. On the physical layer security analysis of hybrid millimeter wave networks. IEEE Trans. Commun. 2017, 66, 1139–1152. [Google Scholar] [CrossRef]
- Atallah, M.; Kaddoum, G. Secrecy Analysis in Wireless Network with Passive Eavesdroppers by Using Partial Cooperation. IEEE Trans. Veh. Technol. 2019. [Google Scholar] [CrossRef]
- Ryu, J.Y.; Lee, J.; Quek, T.Q. Confidential Cooperative Communication with Trust Degree of Potential Eavesdroppers. IEEE Trans. Wirel. Commun. 2016, 15, 3823–3836. [Google Scholar] [CrossRef]
- Tang, L.; Chen, H.; Li, Q. Social tie based cooperative jamming for physical layer security. IEEE Commun. Lett. 2015, 19, 1790–1793. [Google Scholar] [CrossRef]
- Wang, H.M.; Xu, Y.; Huang, K.W.; Han, Z.; Tsiftsis, T.A. Cooperative secure transmission by exploiting social ties in random networks. IEEE Trans. Commun. 2018, 66, 3610–3622. [Google Scholar] [CrossRef]
- Wang, L.; Wu, H.; Stüber, G.L. Cooperative jamming-aided secrecy enhancement in P2P communications with social interaction constraints. IEEE Trans. Veh. Technol. 2017, 66, 1144–1158. [Google Scholar] [CrossRef]
- Gong, X.; Chen, X.; Zhang, J. Social group utility maximization game with applications in mobile social networks. In Proceedings of the 2013 51st Annual Allerton Conference on Communication, Control, and Computing (Allerton), Monticello, IL, USA, 2–4 October 2013; pp. 1496–1500. [Google Scholar]
- Gong, X.; Chen, X.; Zhang, J. Social group utility maximization in mobile networks: From altruistic to malicious behavior. In Proceedings of the 2014 48th Annual Conference on Information Sciences and Systems (CISS), Princeton, NJ, USA, 19–21 March 2014; pp. 1–6. [Google Scholar]
- Chen, X.; Proulx, B.; Gong, X.; Zhang, J. Exploiting social ties for cooperative D2D communications: A mobile social networking case. IEEE Trans. Wirel. Commun. 2015, 23, 1471–1484. [Google Scholar] [CrossRef]
- Coon, J.P. Modelling trust in random wireless networks. In Proceedings of the 2014 11th International Symposium on Wireless Communications Systems (ISWCS), Barcelona, Spain, 26–29 August 2014; pp. 976–981. [Google Scholar]
- Li, J.; Li, R.; Kato, J. Future trust management framework for mobile ad hoc networks. IEEE Commun. Mag. 2008, 46, 108–114. [Google Scholar]
- Theodorakopoulos, G.; Baras, J.S. On trust models and trust evaluation metrics for ad hoc networks. IEEE J. Sel. Areas Commun. 2006, 24, 318–328. [Google Scholar] [CrossRef]
- Zouridaki, C.; Mark, B.L.; Hejmo, M.; Thomans, R.K. A quantitative trust establishment framework for reliable data packet delivery in MANETs. In Proceedings of the Milcom 2010 Military Communications Conference, San Jose, CA, USA, 31 October–3 November 2005; pp. 1–10. [Google Scholar]
- Changiz, R.; Halabian, H.; Yu, F.R.; Lambadaris, I.; Tang, H.; Mason, P.C. Trust establishment in cooperative wireless networks. In Proceedings of the 3rd ACM Workshop on Security of Ad Hoc and Sensor Networks, Lexandria, VA, USA, 7 November 2005; pp. 1074–1079. [Google Scholar]
- Jorgensen, M.L.; Yanakiev, B.R.; Kirkelund, G.E.; Popovski, P.; Yomo, H.; Larsen, T. Shout to secure: Physical-layer wireless security with known interference. In Proceedings of the IEEE GLOBECOM 2007—IEEE Global Telecommunications Conference, Washington, DC, USA, 26–30 November 2007; pp. 33–38. [Google Scholar]
- Boyd, S.; Vandenberghe, L. Convex Optimization; Cambridge University Press: Cambridge, UK, 2004. [Google Scholar]
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).