Abstract
A new technique for progressive visual secret sharing (PVSS) with adaptive priority weight is proposed in this paper. This approach employs the bitwise and eXclusive-OR (XOR) based approaches for generating a set of shared images from a single secret image. It effectively overcomes the former scheme limitation on dealing with an odd number of stacked or collected shared images in the recovery process. The presented technique works well when the number of stacked shared images is odd or even. As documented in experimental results, the proposed method offers good results over binary, grayscale, and color images with a perfectly reconstructed secret image. In addition, the performance of the proposed method is also supported with theoretical analysis showing its lossless ability to recover the secret image. However, it can be considered as a strong substitutive candidate for implementing a PVSS system.
1. Introduction
Recently, several approaches have been devoted to dealing with secure image communication. Transferring a secret image via a communication channel has become an open issue nowadays. Two parties often communicate one to the one another via Internet, cloud computing, communication technology, etc. In this way, a digital image is often transmitted or sent via the communication channels with the security and integrity requirements. A simple means for transferring or exchanging secret information between two or multiple parties is by inserting the secret image into the digital cover image. One can select an appropriate technique for transmitting a secret image. Among of them are the secret sharing technique [1,2,3], the image watermarking technique [4], the multiple secret sharing technique [5,6,7], the progressive secret sharing technique [8,9,10,11,12,13,14,15], the lossless progressive secret image technique [16], etc. These aforementioned methods offer promising performances on in regards to rendering the information of the secret image into the other form (such as a digital image host or shared images).
The secret sharing method aims to convert a meaningful secret image into a non-friendly appearance before transmission to the other parties. The noise-like form can be selected to hide the content of secret image such that an unauthorized malicious attacker cannot recognize the important information contained in the secret image. In recent years, a lot of methods have been developed in the field of secret sharing. The most well-known secret image methods are multiple secret sharing [5,6,7], progressive secret sharing [8,9,10,11,12,13,14,15], lossless progressive secret sharing [16], and more sophisticated secret sharing techniques. The multiple secret sharing method [5,6,7] changes a set of secret images into multiple images or a set of shared images, whereas the progressive secret sharing method simply converts a single secret image into a set of shared images. In the multiple secret sharing method, all shared images are required to reconstruct the secret image. If only a partial subset of shared images is involved in the recovery process, one obtains nothing. The progressive secret sharing method [8,9,10,11,12,13,14,15] offers different ways to reconstruct the secret image. Either a partial or a full set of shared images may be used to obtain the recovered secret image. A higher number of involved shared images gives a better quality of the recovered secret image, and vice versa. However, the progressive secret sharing method cannot give warranty in the lossless recovered secret image. However, a new technique (namely, lossless progressive secret sharing [16]) is able to recover the secret image with lossless quality. Some modifications have been made to the progressive visual secret sharing (PVSS) method with the adaptive priority weight [15]. We give illustrations of PVSS and PVSS with adaptive priority weight in the following example: Figure 1 displays a Lena image in color format. Figure 2 shows a set of shared images generated from the PVSS method [16] and the PVSS scheme with adaptive priority weight [15]. Figure 3 gives the reconstructed secret image by stacking several images obtained from the PVSS method [16] and the PVSS scheme with adaptive priority weight [15]. The adaptive priority weight offers better results regarding the quality of the reconstructed secret images.
Figure 1.
Lena image in color formatting.
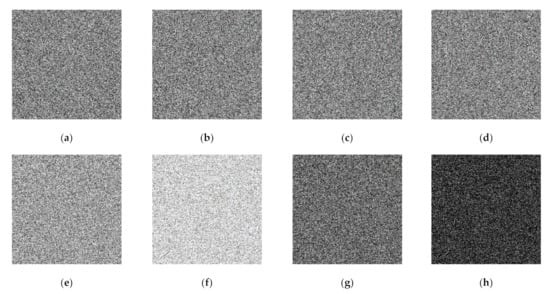
Figure 2.
A set of generated shared images: (a–d) from the progressive visual secret sharing (PVSS) scheme [16], and (e–h) from a PVSS scheme with adaptive priority weight [15].
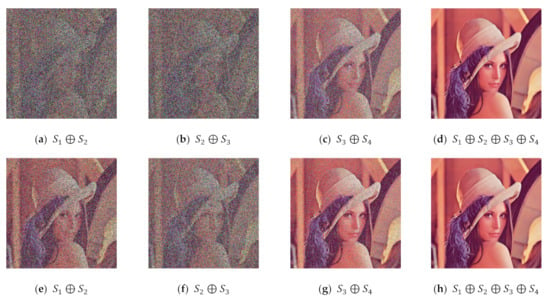
Figure 3.
The quality of the reconstructed secret images obtained from: (a–d) the PVSS scheme [16] and (e–h) the PVSS method with adaptive priority weight [15].
This paper first reviews the former scheme [15] on generating a set of shared images from a secret image and recovering a secret image. The former scheme employs the adaptive priority weight to progressively reconstruct a secret image. The former scheme shows its usability in the PVSS task as reported in [15]. Based on our observation, however, the former scheme suffers from a slight limitation in the secret image recovery process if the number of stacked or collected images is odd. This paper delineates this limitation, along with the theoretical analysis required to prove this issue. Some experiments concerning this limitation are also reported. Thereafter, we develop a new technique for overcoming this problem. This new technique inherits the PVSS with a random grids approach from the former scheme with a simple modification implemented to improve the recovery process when the number of stacked images is odd. This simple modification effectively yields a perfect reconstructed secret image whether the number of stacked images is odd or even. The correctness of the proposed method is also supported by mathematical analysis as well as experimental findings. The proposed PVSS method can be touted as a strong alternative candidate for substitution in place of the former scheme [15].
The former scheme [15] and proposed method exploit the eXclusive-OR (XOR) operation for producing a set of shared images as well as obtaining a recovered secret image. The XOR operation is very simple, with various symmetric properties. These XOR properties are very important for designing the PVSS algorithm. One can produce a set of generated shared images using an XOR operation. Conversely, the XOR operation can be used to recover a secret image without the use of any additional computational techniques. The XOR performs differently with common arithmetic operations. The XOR operator has no negation/inverse operation, while the arithmetic has a negation/inverse operator. For example, the arithmetics addition operator owns the negation operator (i.e., arithmetics subtraction). What follows are some useful XOR properties [7] for the PVSS methods. Herein, we provide examples of each property with both the binary and the decimal number representation.
- Identity:
This property indicates that performing XOR over any arbitrary number with zero yields an identical arbitrary number itself. This property is defined as:
For example, we have (i.e., a number 6 in decimal representation) with the corresponding binary string set as . This property tells us that in binary representation or in decimal format.
- Performing XOR over “odd number” times:
If we perform XOR operation on the same arbitrary number over “odd number” times, we will receive this arbitrary number itself. Specifically, this process is denoted as:
For example, XOR-ing the decimal number 6 over “odd” times gives or, in binary representation, .
- Performing XOR over “even number” times:
In contrast to the previous XOR property, performing an XOR operation on the same arbitrary number over “even number” times yields zero results. This property is shown as follows:
A simple example for this property is in the case in decimal number representation, or, in binary representation, .
- Symmetric Inverse:
This property is almost similar to the common arithmetic inverse, e.g., an addition operator against the subtraction operator. The XOR has no inverse operator. Yet, the XOR can solely perform symmetric inverse by itself. This property is defined as follows:
Suppose that there are two decimal numbers and , with the corresponding binary strings and , respectively. Thus, we have or . It is implied that or, in binary representation, . Conversely, we obtain or . This value is identical to or , showing that the XOR has a unique symmetric inverse property.
- Commutative:
The XOR has a similar property as the common arithmetics (i.e., a commutative property). This property is specified as:
Let and , or, in binary representation, and . The following computations yield identical results (i.e., and ) or, in decimal representation, .
- Associative:
This property herein is similar to that of the common arithmetic operation. The XOR operation also offers associative computation as formally defined as follows:
Suppose that we have , , and . This property gives and in binary form. This result resembles as in the decimal form . However, the XOR operation has been shown to have an associative property.
The main contribution of this paper is to develop a new technique for PVSS with a lossless ability in the secret image reconstruction process whether the number of stacked shared images is odd or even. The other contribution of this paper is a formal mathematical analysis for showing the limitation and correction of the PVSS method. This work has been motivated with the increased demand for secure image transmissions. This work has also motivated the success rate of lossless PVSS in [16]. The organization of this paper is arranged as follows: Section 2 briefly discusses the former PVSS scheme with adaptive priority [15]. This section also shows the limitation of the former scheme [15] as supported with experimental finding and theoretical analysis. Section 3 describes the proposed PVSS method, with adaptive priority analyzed in detail. The proposed method’s usability is supported with the formal mathematical analysis. Section 4 extensively reports some experimental results. The end of this paper delivers the conclusions and direction for future works.
2. Former PVSS Scheme
This section briefly reviews the former PVSS scheme [15] wherein the secret and shared images are in binary format. It presents the step-by-step process of shared image generation and secret image reconstruction. A slight shortcoming of this aforementioned method is also provided in this section along with formal theoretical analysis.
2.1. PVSS Scheme for Binary Image
The PVSS scheme in [15] for binary image generation is first presented in this section. This scheme exploits the random grids to perform the secret sharing task. The former method converts a secret image in binary format into a set of shared binary images. The procedure of shared image generation is described as follows: Suppose that is a binary secret image of size . Each pixel on is denoted as , for and . Since is a binary image, then simply consists of two values (i.e., a black (or ) and white pixel (or )). The former scheme [15] changes into shared images in pixel-based processing and in a bitwise fashion. The symbol is the -th shared image, for . These sets (i.e., shared images) are further transferred to the receiver or decoder side via communication or transmission channel. Each pixel in the shared image is denoted as , for and . Herein, the size of each shared image is identical to that of the size of the secret image (i.e., .
In order to convert a secret image into a set of shared images, the former scheme [15] requires a set of spatial pixel locations () for . These locations are specified by their adaptive priority weight ( for . The adaptive priority weight can be predetermined based on user preference. Figure 4 exhibits some examples of spatial pixel location () for , over various adaptive priority weights . In this figure, the pixel location owns around 50% of the occupied pixels in order to generate a shared image. The has a higher adaptive weight compared to the other spatial pixel locations. In this example, the additional pixels in are caused by the rounding operator in the adaptive priority weight determining the spatial pixel location. Setting a higher priority weight indicates more pixel locations arranged in the -th shared image, and vice versa. Thus, the recovered secret image becomes quickly or easily recognized by human vision in the reconstruction process. In addition, the correct pixel of the recovered secret image will be rapidly obtained by utilizing a higher priority weight.
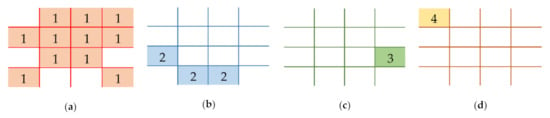
Figure 4.
Examples of spatial pixel locations with various adaptive priority weights : (a) , (b) , (c) , and (d) .
The generation of shared images is formally defined as follows: For each pixel in the secret image (i.e., ) we first must determine two selected indices of shared images for the purpose of encoding. The first and second indices of the selected shared images are denoted as and . The value of is determined based on the information of the pixel location , whereas is simply computed as . The symbols and indicate the arithmetic modulus operator and the assignment operator, respectively. A pixel in a spatial position in the first selected shared image is assigned the following value:
where represents the pixel in the spatial position over the -th shared image. The computation in Equation (7) requires a random number generator. Herein, denotes the uniformly random number generator producing the integer in range . A different strategy is then applied to determine the pixel value of the second selected shared image . The pixel in the secret image specifies the value of . If the processed secret image is a black pixel (i.e., ), then the pixel value in is assigned as:
If the secret image is a white pixel (i.e., ), the former scheme provides the pixel as follows:
where is the bitwise NOT operator. Subsequently, the pixel values of all shared images excluding and (i.e., all for and ) are set as :
This process is conducted for all pixels in the secret image . A set of shared images is created at the end of this process. The shared image is in binary format if the binary secret image is fed into the former scheme [15]. Algorithm 1 explains the shared image generation process in detail.
| Algorithm 1: Former Scheme [15]. |
| Input: Secret image in binary format, , of size |
| Number of shared images, |
| Output: A set of generated shared images, , each of size |
| Step 1: Based on priority weight , determine the location set , for . |
| Step 2: For Each Pixel . Based on information , select two shared images and . Do |
| Step 3: |
| Step 4:If, then |
| Step 5: Else |
| Step 6: For Each other shared images, , with condition and Do |
| Step 7: |
| Step 8: Obtain generated shared images, |
In normal situations, all shared images are transmitted to the decoder or receiver side. However, the receiver often collects a partial set of shared images to reconstruct the secret image. Let be a partial set of collected shared images in the receiver side, where denotes the index of the received shared image and . The reconstruction process of the secret image can be easily performed by stacking a partial set of collected shared images with the bitwise XOR-based operation. This process is descibed as follows:
where is a recovered secret image. The quality can be improved if the PVSS scheme [15] involves more stacked shared images in the secret image reconstruction process. Hopefully, the quality of the recovered secret image would be as similar as possible to that of the original secret image by stacking all shared images with the XOR operator.
2.2. Limitation of PVSS Scheme
As reported in literature [15], the former PVSS scheme offers a promising result in the shared image generation and secret image reconstruction processes. The former scheme yields a correct reconstructed secret image if and only if the number of stacked shared images is even. However, it is little regrettable that the former PVSS scheme cannot restore the secret image if the number of stacked shared images is odd. The following theorem explains this limitation.
Theorem 1.
The former PVSS scheme [15] yields perfect or partial reconstruction if and only if the number of stacked shared images is even.
Proof.
Letbe a set of collected or received shared images involved to reconstruct a secret image. In this proof, we investigate the quality of. The reconstruction process is performed with the XOR operation in a bitwise-based manner over all collected shared images. The reconstruction process is defined as:
If the receiver module collects all shared images, it is implied that. The recovered secret imagecan be obtained as:
There are two selected shared imagesand) in the shared image generation. The other shared images have the value of(i.e.,forand). For sake of simplicity, we remove the pixel positionfor all proofs in this paper. Thus, the form in Equation (12) can be alternatively computed as:
Arranging theandin an orderly fashion, we gain the following form:
The value ofis an even number ifis an even number. This implies the computation ofas follows:
The basic property of XOR operation over “even number times” indicates the result. Thus, the form in Equation (13) can be further simplified as:
The XOR property with “zero number” produces the following result:
If the observed pixel of the secret image is black (i.e.,), then. The XOR property for two identical numbers implies the following result:
The result in Equation (15) tells that the original and the recovered secret image are identical if the secret image isandis even number. Based on this fact, we can conclude that. However, one obtains a correct recovered secret image.
For the situation where is an even number and the secret image is a white pixel (i.e., , the second selected shared image is set as . The substitutive computation of in Equation (14) is indicated as follows:
The XOR property on two complementary numbers yields the following result:
The result in Equation (16) reveals that the qualities of the recovered and the original secret image are identical ifis an even number (i.e.,) whileis white. The former scheme [15] yields a correct result ifis an even number.
Ifis an odd number, the computation ofis given as:
The XOR property “odd number times” yields. The recovered secret image is then:
The XOR operation concerning two identical numbers results in 0. It gives the following result:
The recovered image obtained from Equation (17) is actually a random image (i.e.,with). The recovered secret image cannot be correctly produced ifis an odd number (i.e.,).
Under the similar deduction for(i.e., only a partial set of shared images is involved in the reconstructed process), the imageis computed as:
Suppose that. The computation ofis then given as:
In the former scheme [15], all shared images are simply determined asfor allwithand. This condition implies:
The XOR properties “even number times” and “odd number times” indicate the following result:
Then, the imagecan be finally obtained as follows:
It is clearly revealed from Equation (18) that the recovered secret image can be perfectly reconstructed ifis an even number. Thus, the perfect recovered secret image can be obtained if and only if the number of stacked shared images is even. This concludes the theorem.
3. Proposed PVSS Method
This section gives a detailed explanation for the proposed PVSS method. This new method modifies the former scheme [15] for computing a set of generated shared images. This modification is made to achieve the perfect reconstruction result in the recovery process. Similarly to the former scheme [15], the proposed method also incorporates the adaptive priority weight for a progressive recovery process. However, the proposed method and the former scheme employ an identical approach for performing the secret image reconstruction (i.e., stacking several or all shared images using a bitwise XOR approach). This section presents two techniques for the proposed method using the bitwise-based and XOR-based PVSS approaches.
3.1. Proposed Bitwise-Based PVSS Method
The proposed bitwise-based PVSS method is discussed in detail in this subsection. It inherits the usability of the former scheme [15] with a slight modification. This simple modification simply solves a minor limitation in [15] present when the number of stacked or collected shared images is odd. The proposed method also utilizes the random grid technique for generating a set of shared images. The proposed bitwise-based PVSS method for computing a set of shared images is formally explained with the following procedure: Suppose is a binary image of size . The proposed method transforms the secret image into shared images. Let be a set of generated shared images, and be the spatial position of an image pixel. Similarly to the former scheme [15], the proposed method first determines two selected shared images (denoted as and . The determinations of and are based on the priority weight and location set . Each pixel in the -th shared image is set with a uniformly random number as follows:
for and . Subsequently, each pixel in the -th shared image is determined by considering the pixel value . If an investigated pixel value is black (i.e., ), afterward, the value of is assigned as follows:
Meanwhile, the value of is simply set with the bit negation of as formulated below:
In contrast to the former scheme [15], the proposed method solely utilizes the zero value for all pixels in the shared images under the constraints and . This strategy is formally defined as:
This shared image generation is applied over all pixel values , for and . Algorithm 2 summarizes the procedure of the proposed method for computing a set of shared images .
| Algorithm 2: Proposed Bitwise-Based PVSS Method. |
| Input: Secret image in binary format, , of size |
| Number of shared images, |
| Output: A set of generated shared images, , each of size |
| Step 1: Based on priority weight , determine the location set , for . |
| Step 2: For Each Pixel . Based on information of , select two shared images and . Do |
| Step 3: |
| Step 4: If , Then |
| Step 5: Else |
| Step 6: For Each Generated shared images, , with the condition and Do |
| Step 7: |
| Step 8: Obtain generated shared images, |
Similar to [15], the proposed method collects a partial or full set of generated shared images in order to recover the secret image. Herein, the proposed method also performs an XOR operation over these collected shared images. This process is defined as follows:
where denotes the recovered secret image and is the total number of collected shared images on the receiver side. The proposed bitwise-based PVSS method is quite simple, yet it effectively solves the lossless problem in [15]. The following analysis supports the proposed method performance theoretically.
Theorem 2.
The proposed bitwise-based PVSS method yields a perfectly reconstructed secret image by stacking a partial or full set of generated shared images.
Proof.
We begin this proof with the quality of the recovered secret image produced by the proposed bitwise-based PVSS method. The XOR-ed process over a partial or full set of generated shared images is denoted as:
We first investigate the proposed method performance when one involves all shared images in the recovery process. In this occasion, it similarly performs a recovery process under a condition. However, the computation ofcan be performed as follows:
We know thatandfor alland. This implies that Equation (24) can be recalculated when consideringas an even or odd number as follows:
Performing XOR on any arbitrary number with zero is equivalent to the arbitrary number itself. Thus, the Equation (25) can be simplified as:
Stacking all shared images actually resembles the process of performing an XOR operation between and . In addition, the proposed method gives various values for , depending on the value of . If , then the value of is identically set with the value of . While , the value of is set in bitwise negation of (i.e., ). This condition gives as follows:
The following result is obtained based on the XOR property:
The last form indicates an important result (i.e.,). Herein, the recovered and the original secret image are identical. Thus, the proposed method yields a perfectly reconstructed secret image when all shared images are involved in the recovery process.
If only a partial set of shared images is involved under condition, the recovered secret imagecan be computed as follows:
Suppose that the two selected shared images (and) are in this partial set under the condition. One cannot obtain a perfectly reconstructed secret image if this condition is not satisfied. The computation ofis then given as:
Based on the fact thatfor alland, one can trivially obtain the following form:
The XOR property implies the following result:
The last form indicates that the value ofis identical to that of the XOR-ed result betweenand. By investigating the value of, we acquire the following conclusion:
In the case of, we achieve an important deduction (i.e.,) To simplify, the quality of the recovered secret image is identical to that of the original secret image. In addition, a perfect recovered secret image can be yielded if either a partial set or all generated shared images are involved in the reconstruction process. This completes the proof.
3.2. Proposed XOR-ed Based PVSS Method
In this approach, the proposed method performs a simple computation involving an XOR operation in order to generate a set of shared images. The proposed method takes an image of as the secret image to produce the targeted shared images . Herein, the secret image can be present as binary, grayscale, or color space. For each pixel in the secret image, we perform the following procedure to generate shared images: We first decide two selected shared images and ). In contrast to the former scheme [15] and the proposed bitwise-based approach, the proposed XOR-based method needs to first generate the following constant:
where is a constant. The symbol denotes a uniform random number generator producing an integer in range . We utilize and for the binary image and the 8-bit grayscale image, respectively. A three dimensional image of can be used for the 24-bit color image (i.e., generating a random number for three dimensional color spaces). Subsequently, all pixels in two selected shared images ( and ) are determined as follows:
All pixels in are simply set with zero value for and . Alternatively, the pixels are set according to the following process:
The proposed XOR-ed PVSS method requires simple steps to compute a set of shared images. This simple approach is also applicable for grayscale and color images. The contents of all shared images are totally different compared to that of the original secret image. In addition, the proposed XOR-based PVSS method is designed to solve a slight problem in the former scheme [15]. Algorithm 3 illustrates the shared image generation using the proposed XOR-based PVSS approach.
| Algorithm 3: Proposed XOR-ed Based PVSS Method. |
| Input: A grayscale or color image as secret, , of size |
| Number of shared images, |
| Output: Full set of generated shared images, , each of size |
| Step 1: Based on priority weight , determine the location set , for . |
| Step 2: For Each Pixel Position . Based on the information in , decide the selected shared images and . Do |
| Step 3: |
| Step 4: |
| Step 5: |
| Step 6: For Each other generated shared images, , under the condition and Do |
| Step 7: |
| Step 8: Obtain the generated shared images, |
The proposed method reconstructs the secret image in a similar fashion as compared to the former scheme [15]. Herein, the proposed method simply needs to perform an XOR operation over either a partial set or all generated shared images. The following theorem supports the correctness of the proposed method.
Theorem 3.
The proposed XOR-ed based PVSS method yields a perfectly reconstructed secret image by stacking partial or all generated shared images.
Proof.
In order to prove this theorem, we first examine the quality of recovered secret image produced by our proposed method. Suppose that all generated shared images are involved in the recovery process of a secret image. This indicates that. Thus, thecan be produced as follows:
The simplified form in Equation (32) is actually identical to that of Equation (26). The proposed method applies a similar strategy on(i.e.,forand. The selected shared imagesandare set with the value ofand, respectively. The form in Equation (32) is similar to following computation:
The XOR property indicates that an XOR operation between two identical scalars yields zero value. Thus, the form in Equation (33) has the following result:
The XOR operation between scalar and zero produces the scalar itself. However, one obtains the following result:
The last form in Equation (34) clearly reveals that the proposed XOR-based PVSS method achieves a lossless result. The qualities of the recovered and the original secret image are identical if all generated shared images are utilized in the recovery process.
If only several shared images are involved in the recovery of a secret image (i.e., in the case of), the recovered secret imageis computed as follows:
The conditionimplies the following result:
A similar deduction on Equation (33) can be applied for Equation (35). Thus, we conclude an important result (i.e.,. The proposed XOR-based PVSS method is able to reconstruct a secret image with the lossless condition even if only a partial set of generated shared images is involved in the reconstruction process. The proposed XOR-based PVSS approach yields a perfect recovered secret image whether all or several generated shared images are utilized in the recovery process. This concludes the proof.
4. Experimental Results
The performances of the proposed method and the former scheme [15] are extensively reported in this section in terms of dealing with the PVSS tasks. We first explain several image quality assessment metrics to objectively measure the degree of similarity between the original and the recovered secret image. Subsequently, the performances of the proposed method are compared under visual investigation and objective measurement over binary, grayscale, and color images. These assessments are conducted to further investigate the proposed method’s usability and superiority. The comparisons in terms of algorithm aspects between the proposed method and competing schemes are summarized at the end of this section.
4.1. Performance Evaluation
We first evaluated the performance under the subjective and objective assessments. For the subjective image quality assessment, the quality of the recovered secret image was simply inspected and judged based on a visual observation. Herein, we visually compared the similarities between the original and the recovered secret image under the perception of human vision, whereas the objective image quality assessment utilizes several metrics to calculate the degree of similarity between the original and the recovered secret image. These metrics are referred to as image contrast α, bit error rate β, peak signal-to-noise ratio (PSNR), structural similarity index metric (SSIM), and mean absolute error (MAE). All of these objective metrics are formally defined as follows:
where is the secret image, and is the recovered secret image. These two images are of the same size (i.e., ).
In the SSIM computation, the symbols and are the mean values of and , respectively. However, the standard deviations of and are denoted as and , respectively. Meanwhile, the covariance between and is denoted as . The and are two predetermined constants. In the case of a binary image, the symbols and denote the average light transmission [8] of the recovered secret images over a white pixel (1) and a black pixel (0), respectively. In our subsequent experiment, a better performance is indicated by higher scores of , PSNR, and SSIM, and vice versa. On the other hand, a better performance is also implied by lower values of and MAE, and vice versa.
4.2. Visual Evaluation on Binary Image
The visual investigation between the proposed method and the former scheme [15] in terms of a binary image is reported in this subsection. We examined the performances of the proposed method and the former scheme [15] under a set of binary images as displayed in Figure 5. In this experiment, we simply set the adaptive priority weights as and for and . Figure 6 exhibits a set of generated shared images for with the proposed bitwise-based PVSS method. Setting a higher value for adaptive priority weight implies a brighter shared image compared to that obtained by setting a lower value of . In addition, the contents of all generated shared images are in a noise-like appearance, meaning that each image cannot easily be distinguished. This clearly reveals that the proposed method satisfies the PVSS constraint (i.e., that the content of the generated shared images cannot be recognized by an unauthorized party).
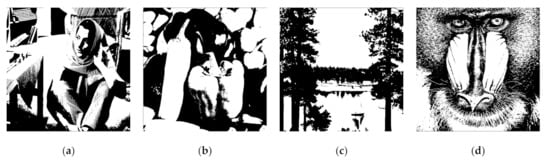
Figure 5.
Four secret images in a binary format for experiment (a) , (b) , (c) , and (d) .
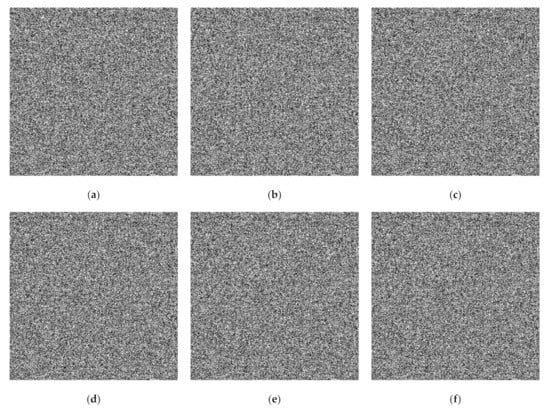
Figure 6.
Generated binary shared images using the proposed bitwise-based PVSS method for : (a–f) .
Subsequently, we verified the quality of the recovered secret image. We select Barbara from Figure 5a as a binary secret image. We investigated and compared the performances of the proposed method and former scheme using visual inspection of the recovered secret image. Figure 7 displays the recovery process of the Barbara secret image for , while Figure 8 displays the recovery process for . These two figures demonstrated the superiority of the proposed method compared to that of [15]. The proposed method was able to produce the recovered secret image when the number of stacked shared image is odd. However, one cannot reconstruct the secret image using the former scheme [15] if is an odd number. In addition, the recovered secret image produced by the proposed method is lossless if all shared images are stacked using an XOR operation. This experiment indicates that the proposed method offers a promising result in the PVSS task.
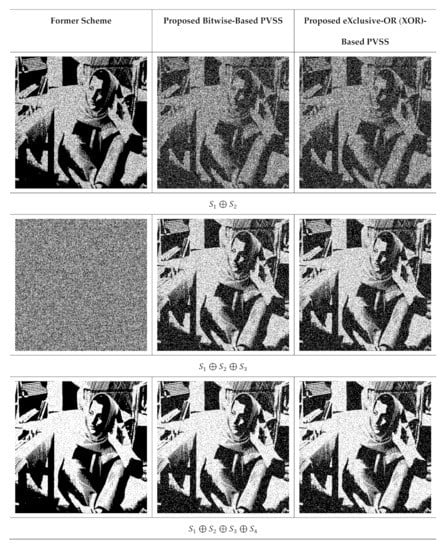
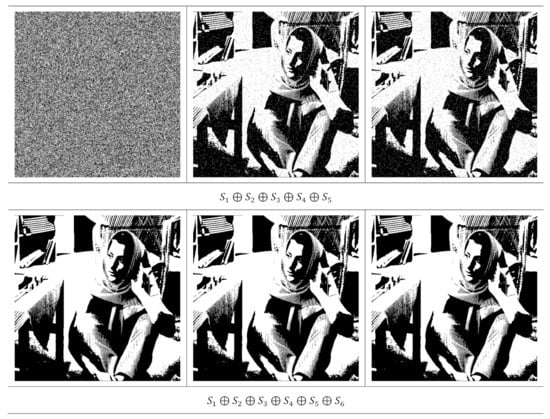
Figure 7.
The results of stacking several shared images with , by setting . The first colum is from the former scheme [15], while the second and third columns are from the proposed method.
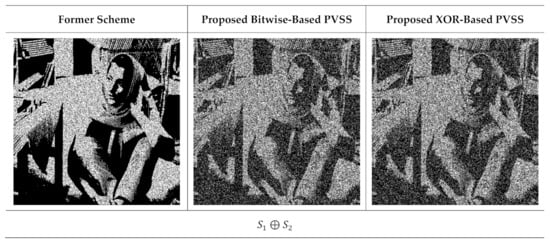
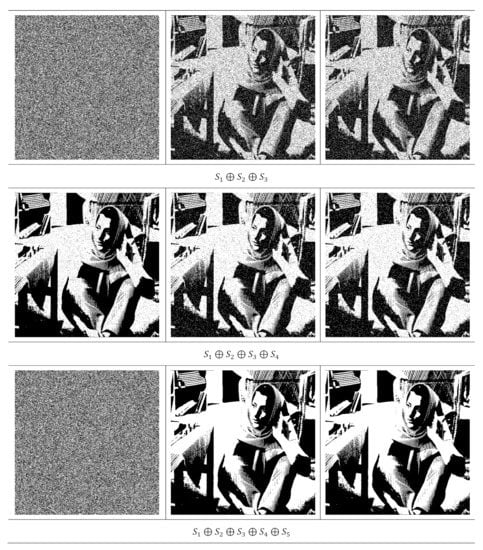
Figure 8.
Stacking several shared images , by setting . The first column is from the former scheme [15], while the second and third columns are from the proposed method.
4.3. Visual Investigation on Grayscale Image
We subsequently considered the performance of the proposed method and the former scheme [15] under visual investigation. In this experiment, we examined the performances of four secret images in grayscale, as shown in Figure 9. The adaptive priority weights were identically set to those used in the binary image case. In the shared image generation, we simply employed and . Figure 10 displays a set of shared images for when the Barbara grayscale image is selected as a secret image. As depicted in this figure, the content of the generated shared images cannot be perceived and understood by human vision. This means that the shared images are effectively produced by the proposed method.
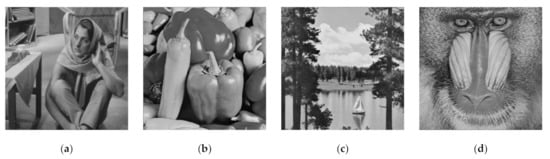
Figure 9.
Four grayscale images as secret for experiment: (a–d) .
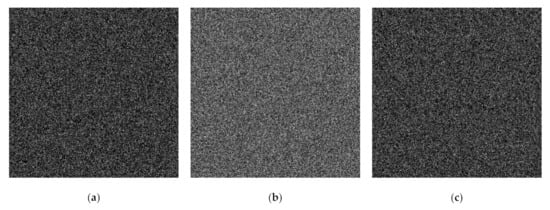
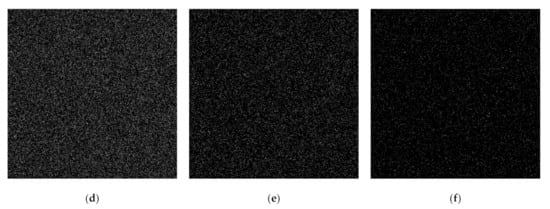
Figure 10.
Generated shared images using the proposed eXclusive-OR (XOR)-based PVSS method: (a–f) , by setting .
The qualities of the recovered secret image were further inspected under visual investigation. Herein, the recovered secret image produced by stacking several shared images is shown in Figure 11 and Figure 12 for and , respectively. As shown in these two figures, the quality of the recovered secret image is increased if more shared images are involved in the reconstruction process. However, the former scheme [15] produces an incorrectly recovered secret image if the number of stacked shared images is odd (i.e., the content of the recovered secret image cannot be correctly reconstructed after the stacking process). Conversely, the proposed XOR-based method works well, indicating its superiority compared to that of the former scheme [15].
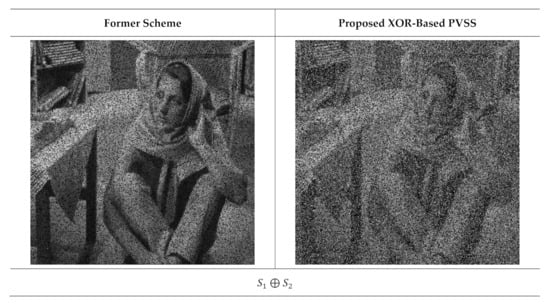
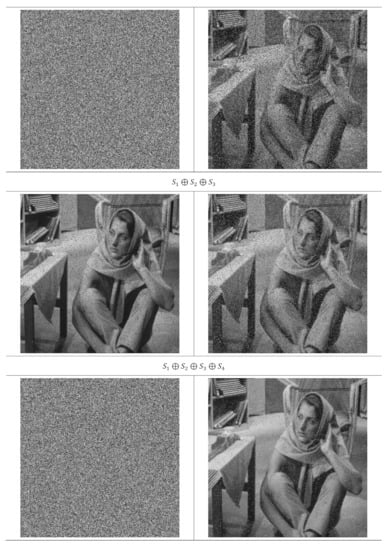
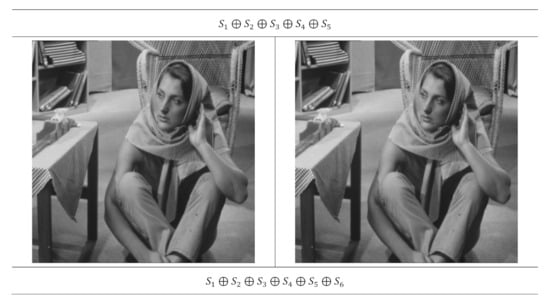
Figure 11.
Stacking several shared images with and . The left and right columns are from the former scheme [15] and the proposed method, respectively.
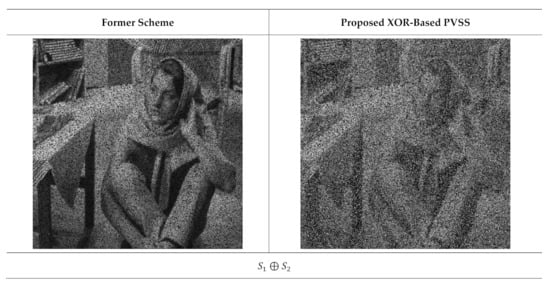
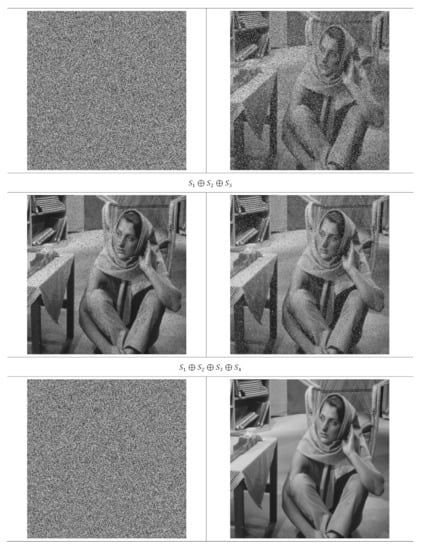

Figure 12.
Reconstructed secret images when several shared images are stacked, with and . The left and right columns are from the former scheme [15] and the proposed method, respectively.
4.4. Visual Assessment of Color Image
This subsection compares the performances of the former scheme [15] and the proposed method under the visual inspection on color image. Four color images (as shown in Figure 13) were used for experimentation. Herein, the number of shared images is set as and . We applied an identical adaptive priority weight, as used in the binary image case. Figure 14 displays a set of shared images in color format, while the color image in Figure 13a was chosen as a secret image. Human vision cannot recognize the object or image content from all shared images as delivered in Figure 14. Thus, it can be concluded that the proposed method effectively produces a set of shared images in color format.
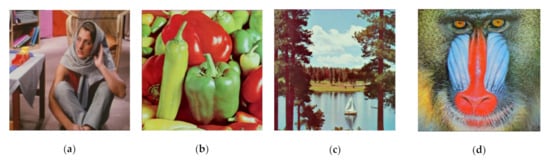
Figure 13.
A set of color images used as secret images in the experiment, denoted as: (a) , (b) , (c) , and (d)
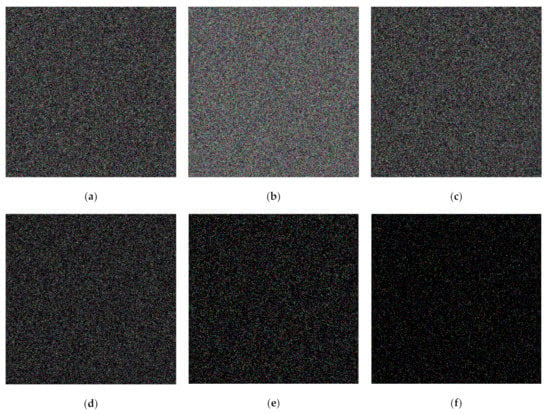
Figure 14.
Shared images obtained from the secret image in the color format using the proposed XOR-based PVSS method: (a–f) .
Subsequently, we observed the quality of the recovered secret image after stacking several shared images using an XOR operation. In this experiment, we reconstructed the secret image by stacking two shared images until reaching shared images. Figure 15 displays the recovered secret image obtained from the former scheme [15] and the proposed method for , while Figure 16 shows the results for . It can be observed from Figure 15 and Figure 16 that the former scheme [15] and the proposed method satisfy the progressive constraint (i.e., the quality of the recovered secret image is increased if more shared images are involved and stacked with an XOR operation). Similarly to the binary and grayscale image cases, the proposed XOR-based PVSS method produces a good result whether the number of stacked shared images is odd or even, whereas the former scheme [15] cannot correctly yield the recovered secret image if the number of stacked shared images is odd. The proposed XOR-based PVSS overcomes the limitation of [15] with a simple approach. Thus, the proposed method delivers a promising result for binary, grayscale, and color images.
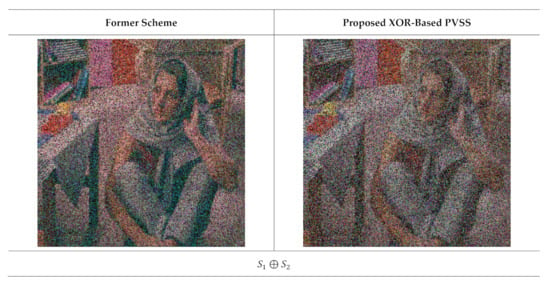
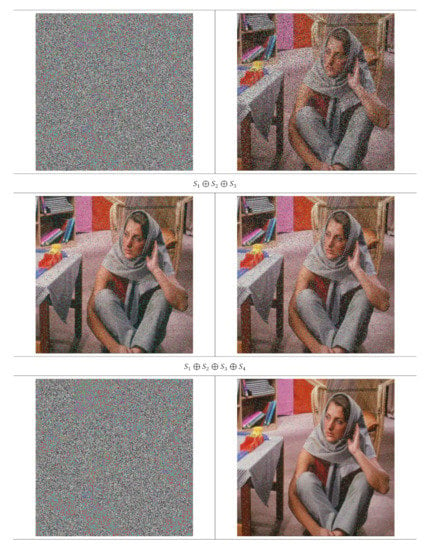
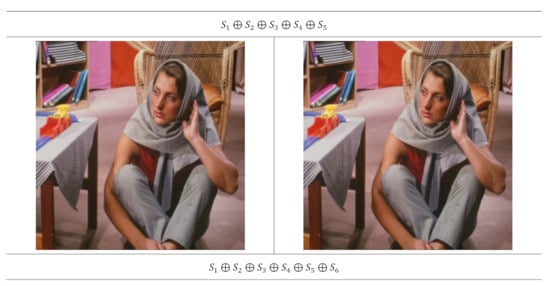
Figure 15.
The results of stacking several shared images with and . The left and right columns are from the former scheme [15] and the proposed method, respectively.
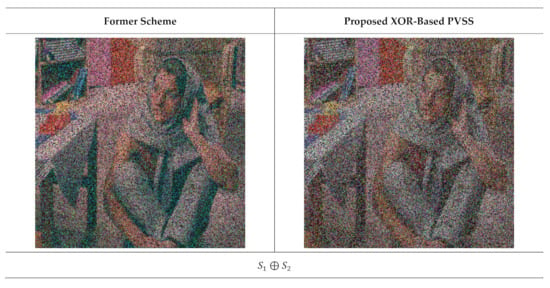
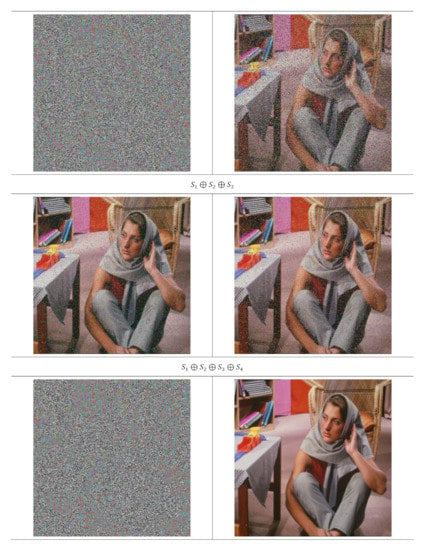

Figure 16.
The results of stacking several shared images and . The left and right columns are the recovered secret image from the former scheme [15] and the proposed method, respectively.
4.5. Performance Comparisons in Terms of Objective Image Quality Assessment
This subsection compares the performances of the proposed method and the former scheme [15] in detail based on an objective image quality assessment. For a binary image, the performance is simply measured and compared under two objective measurements (i.e., an average image contrast and average bit error rate). Herein, four secret images (as shown in Figure 5) were first converted into a set of shared images. The recovery process was subsequently conducted on these generated shared images to produce the recovered secret image. The averages of and were then computed for all recovered secret images. Figure 17 and Figure 18 display the performance comparisons in terms of average and average , respectively, between the proposed method (with a bitwise and XOR-based approach) and the former scheme [15]. In this experiment, we set the number of shared images as and . As shown in Figure 17 and Figure 18, the former scheme [15] yields an unacceptable average and , respectively, if or is an odd number. However, the proposed method performs well for or whether they are odd or even numbers. In addition, the proposed method yields progressive results, indicating the increasing average value of and the decreasing average value of over different values of or .
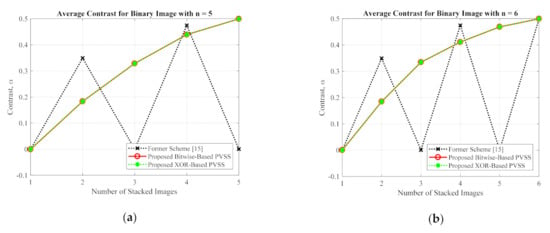
Figure 17.
The average image contrast between the proposed method and the former scheme [15] of the binary secret image with (a) , and (b) .
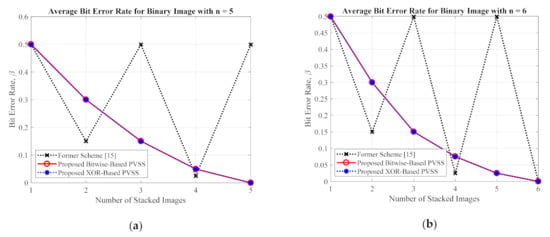
Figure 18.
The average bit error rate between the proposed method and the former scheme [15] for a binary secret image with: (a) , and (b) .
For the grayscale and color images, the comparisons between the proposed method and the former scheme [15] are examined based on the average values of PSNR, SSIM, and MAE. We selected all secret images in grayscale and color spaces shown in Figure 9 and Figure 13 as secret images. All secret images were then converted into a set of shared images. The recovered secret images were further computed by stacking several shared images using an XOR operation. The qualities of all of the recovered secret images were then measured in terms of average PSNR, SSIM, and MAE. Figure 19 and Figure 20 display the performance comparisons for grayscale and color image, respectively. As depicted in these two figures, the former scheme [15] delivers unacceptable results if or is an odd number. The proposed method gives correct results whether or is an odd or an even number. The proposed method satisfies the progressive constraint for the PVSS task, as indicated by the improving PSNR and SSIM scores that result if more stacked images are utilized in the secret image reconstruction stage. It also gives a good result, decreasing the average MAE value if more stacked images are used to recover a secret image. However, the proposed method is a good candidate for implementing PVSS with adaptive priority and a perfect reconstruction process.
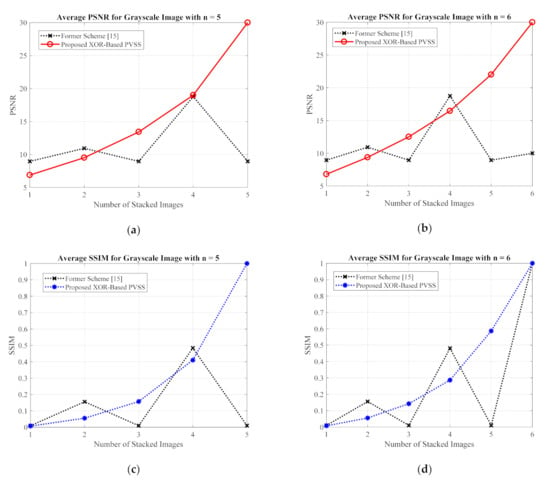
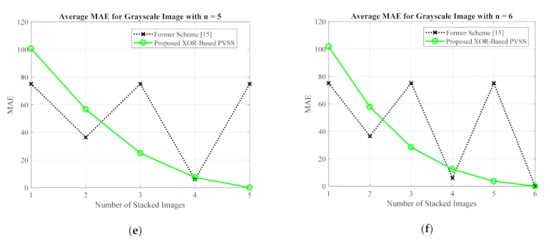
Figure 19.
Comparisons between the proposed method and the former scheme [15] in terms of (a,b) PSNR, (c,d) SSIM, and (e,f) MAE values. The comparisons are conducted for a secret image in grayscale format.
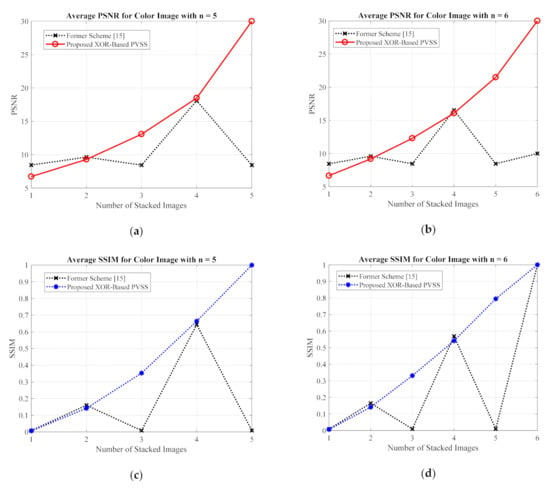
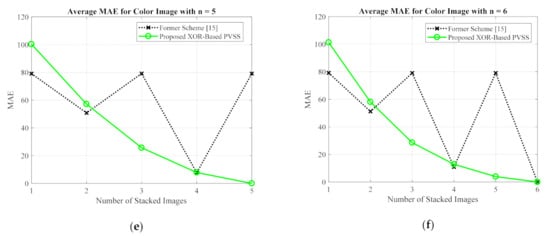
Figure 20.
Comparisons between the proposed method and former scheme [15] in terms of (a,b) PSNR, (c,d) SSIM, and (e,f) MAE values. Herein, the secret image is in a color format.
4.6. Comparison of Algorithm Aspects for the Proposed Method and Other Schemes
The proposed method and former scheme [15] works on a pixel-by-pixel basis in the shared image generation and secret image reconstruction processes. The computational times of these two methods completely depends on the image size. Let and be the width and height of an original secret image. The computational complexity for generating one shared image is for both the proposed method and the former scheme [15]. In reality, the former scheme requires a slightly higher computational burden, since it involves more steps to be conducted in order to compute the shared image, compared to those required in the proposed method. However, the difference is not quite significant. The proposed method and the former scheme [15] need identical computational complexity in the secret image reconstruction process (i.e., ). These two methods simply perform a stacking process with an XOR operation in order to reconstruct a secret image. However, the proposed method and the former scheme have am almost identical computational complexity, except in terms of the quality of the recovered secret image. Thus, the proposed method is a better choice for implementing a PVSS algorithm.
This subsection also reports the algorithm aspects between the proposed method and other competing schemes. Herein, we simply compared the proposed method with others PVSS schemes [9,10,11,12,13,14,15] based on the share style, encoding matrix, pixel expansion, and adaptive priority weight. Table 1 summarizes this comparison. This table shows that the proposed method is able to perform the PVSS task with an priority adaptive weight similar to that of [12,14,15]. The other schemes cannot utilize the priority adaptive weight in the recovery stage of the secret image. The former approach [15] is the most competitive candidate when compared to the proposed method in these terms. However, the proposed method reveals its superiority since it works regardless of whether the number of stacked shared images is odd or even. The former scheme [15] has a limitation when the number of stacked images is odd. In addition, the proposed method does not require the encoding matrix and pixel expansion in the secret image recovery step, meaning that it requires a lower amount of storage space. In addition, the proposed method generates a set of shared images in the form of a noise-like appearance. Thus, the content of the shared images cannot be easily distinguished from one to the other. The contents of each shared image cannot be easily recognized and perceived by human vision. At the end, the proposed method offers its benefit for the PVSS task with adaptive priority and a perfect reconstruction process for recovering a secret image.

Table 1.
Comparisons between the proposed method and the former scheme in terms of algorithm aspects.
5. Conclusions
A simple approach for overcoming the limitation of the former PVSS with adaptive priority weight is presented in this paper. The proposed method is designed to satisfy the lossless constraint and adaptive priority weight required for the PVSS system. The proposed method exploits the bitwise-based and XOR-based techniques for generating a set of shared images. It achieves perfect reconstruction on a recovered secret image whether the number of stacked or collected images is odd or even. While this works for a binary image, the proposed method also works well for grayscale and color images. This superiority can be further applied and extended for video processing or other image processing applications. Thus, the proposed method can be considered and viewed as a strong PVSS alternative with a perfect reconstruction ability.
Author Contributions
Conceptualization, H.P. and C.-H.H.; methodology, H.P.; software, H.P.; validation, H.P., C.-H.H. and A.W.H.P.; formal analysis, H.P.; investigation, H.P.; resources, A.W.H.P.; data curation, H.P.; writing—original draft preparation, H.P.; writing—review and editing, C.-H.H.; visualization, A.W.H.P.; supervision, C.-H.H.; project administration, H.P.; funding acquisition, H.P. All authors have read and agreed to the published version of the manuscript.
Funding
This work was supported by the Hibah Penelitian Fundamental (PF-UNS), Universitas Sebelas Maret (UNS), Indonesia, year 2020, under contract numbers 452/UN27.21/PN/2020.
Institutional Review Board Statement
Not applicable.
Informed Consent Statement
Not applicable.
Data Availability Statement
Not applicable.
Conflicts of Interest
The authors declare no conflict of interest.
References
- Zarepour-Ahmadabadi, J.; Shiri-Ahmadabadi, M.; Latif, A. A cellular automata-based multi-stage secret image sharing scheme. Multimed. Tools Appl. 2018, 77, 24073–24096. [Google Scholar] [CrossRef]
- Bharti, S.S.; Gupta, M.; Agarwal, S. A novel approach for verifiable (n, n) audio secret sharing scheme. Multimed. Tools Appl. 2018, 77, 25629–25657. [Google Scholar] [CrossRef]
- Liu, Y.-N.; Zhong, Q.; Xie, M.; Chen, Z.-B. A novel multiple-level secret image sharing scheme. Multimed. Tools Appl. 2017, 77, 6017–6031. [Google Scholar] [CrossRef]
- Guo, J.-M.; Riyono, D.; Prasetyo, H. Hyperchaos permutation on false-positive-free SVD-based image watermarking. Multimed. Tools Appl. 2019, 78, 29229–29270. [Google Scholar] [CrossRef]
- Prasetyo, H.; Hsia, C.-H. Improved multiple secret sharing using generalized chaotic image scrambling. Multimed. Tools Appl. 2019, 78, 29089–29120. [Google Scholar] [CrossRef]
- Guo, J.M.; Riyono, D.; Prasetyo, H. Improved Beta Chaotic Image Encryption for Multiple Secret Sharing. IEEE Access 2018, 6, 46297–46321. [Google Scholar] [CrossRef]
- Prasetyo, H.; Guo, J.-M. A Note on Multiple Secret Sharing Using Chinese Remainder Theorem and Exclusive-OR. IEEE Access 2019, 7, 37473–37497. [Google Scholar] [CrossRef]
- Yan, X.; Lu, Y. Contrast-improved visual secret sharing based on random grid for general access structure. Digit. Signal Process. 2017, 71, 36–45. [Google Scholar] [CrossRef]
- Fang, W.-P.; Lin, J.-C. Progressive viewing and sharing of sensitive images. Pattern Recognit. Image Anal. 2006, 16, 632–636. [Google Scholar] [CrossRef]
- Wang, R.-Z. Region Incrementing Visual Cryptography. IEEE Signal Process. Lett. 2009, 16, 659–662. [Google Scholar] [CrossRef]
- Hou, Y.-C.; Quan, Z.-Y. Progressive Visual Cryptography with Unexpanded Shares. IEEE Trans. Circuits Syst. Video Technol. 2011, 21, 1760–1764. [Google Scholar] [CrossRef]
- Hou, Y.-C.; Quan, Z.-Y.; Tsai, C.-F. A privilege-based visual secret sharing model. J. Vis. Commun. Image Represent. 2015, 33, 358–367. [Google Scholar] [CrossRef]
- Lin, C.-H.; Lee, Y.-S.; Chen, T.-H. Friendly progressive random-grid-based visual secret sharing with adaptive contrast. J. Vis. Commun. Image Represent. 2015, 33, 31–41. [Google Scholar] [CrossRef]
- Yang, C.-N.; Liao, J.-K.; Wang, D.-S. New privilege-based visual cryptography with arbitrary privilege levels. J. Vis. Commun. Image Represent. 2017, 42, 121–131. [Google Scholar] [CrossRef]
- Chao, H.-C.; Fan, T.-Y. Random-grid based progressive visual secret sharing scheme with adaptive priority. Digit. Signal Process. 2017, 68, 69–80. [Google Scholar] [CrossRef]
- Prasetyo, H.; Hsia, C.-H. Lossless progressive secret sharing for grayscale and color images. Multimed. Tools Appl. 2019, 78, 24837–24862. [Google Scholar] [CrossRef]
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2021 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).