Who Is Best Placed to Support Cyber Responsibilized UK Parents?
Abstract
1. Introduction
2. Related Work
2.1. Responsibilization
2.2. Children’s Cybersecurity Education
2.3. Empowering UK Parents with Cyber Advice
2.3.1. Government as Source
2.3.2. Teachers as Source
2.3.3. Family and Friends as Source
2.3.4. Children’s Books as Source
2.3.5. Cybersecurity Academics as Source
2.3.6. Online Advice as Source
2.3.7. Technology Providers as Source
2.3.8. Support Workers as Source
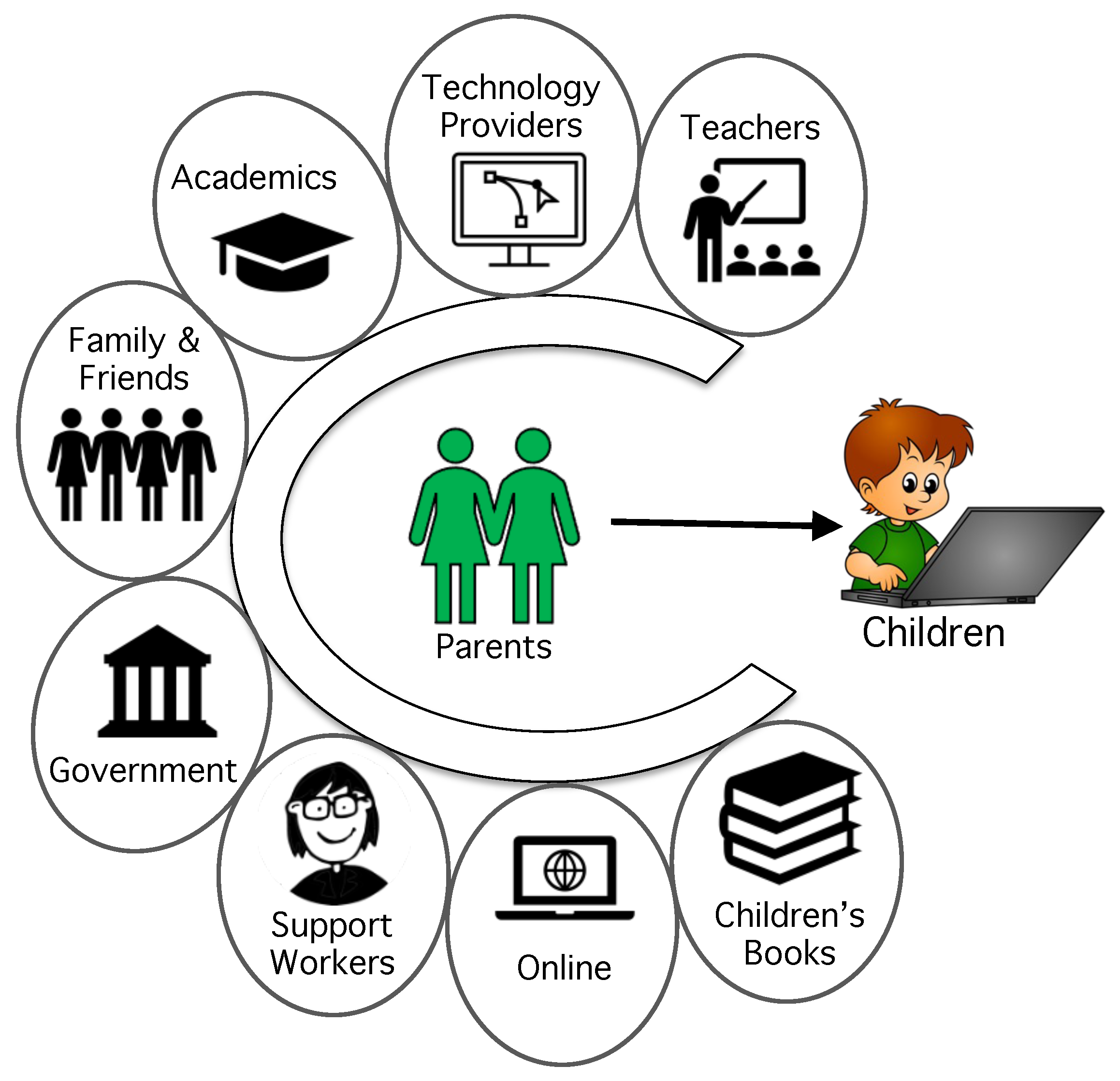
2.4. In Summary
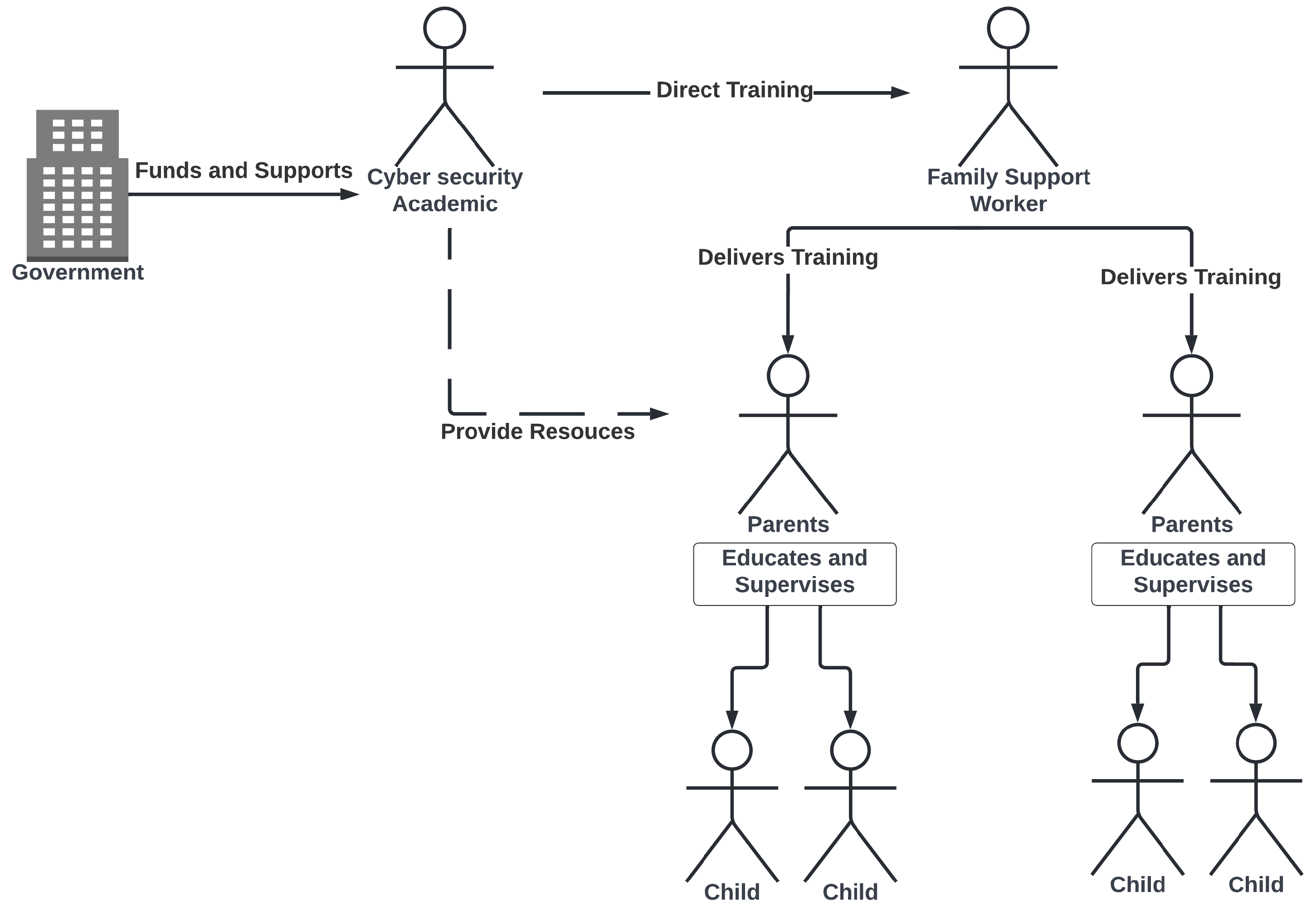
3. Proposal
3.1. Gauging Acceptability of Proposal
3.1.1. Q Statements
3.1.2. Recruiting
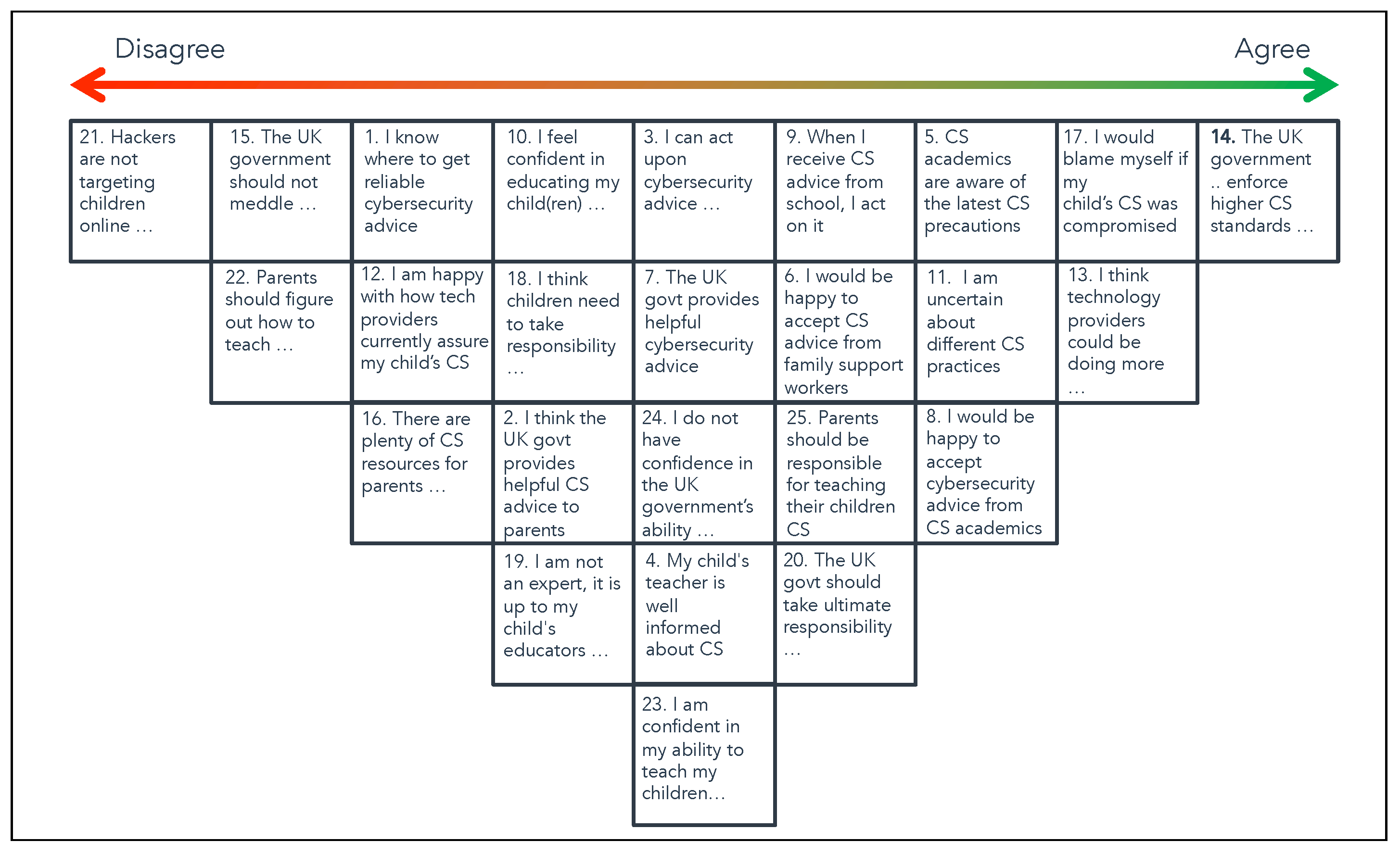
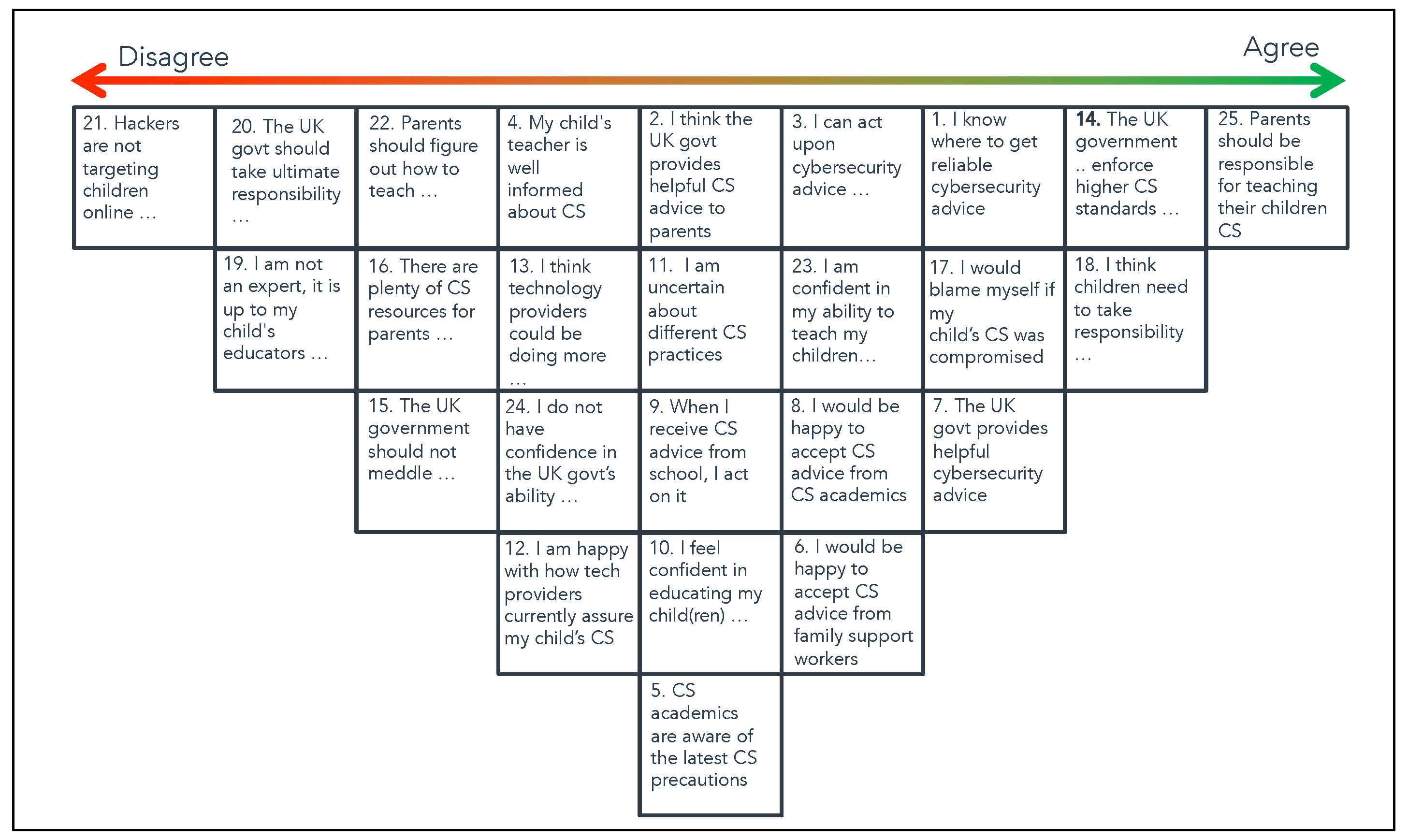
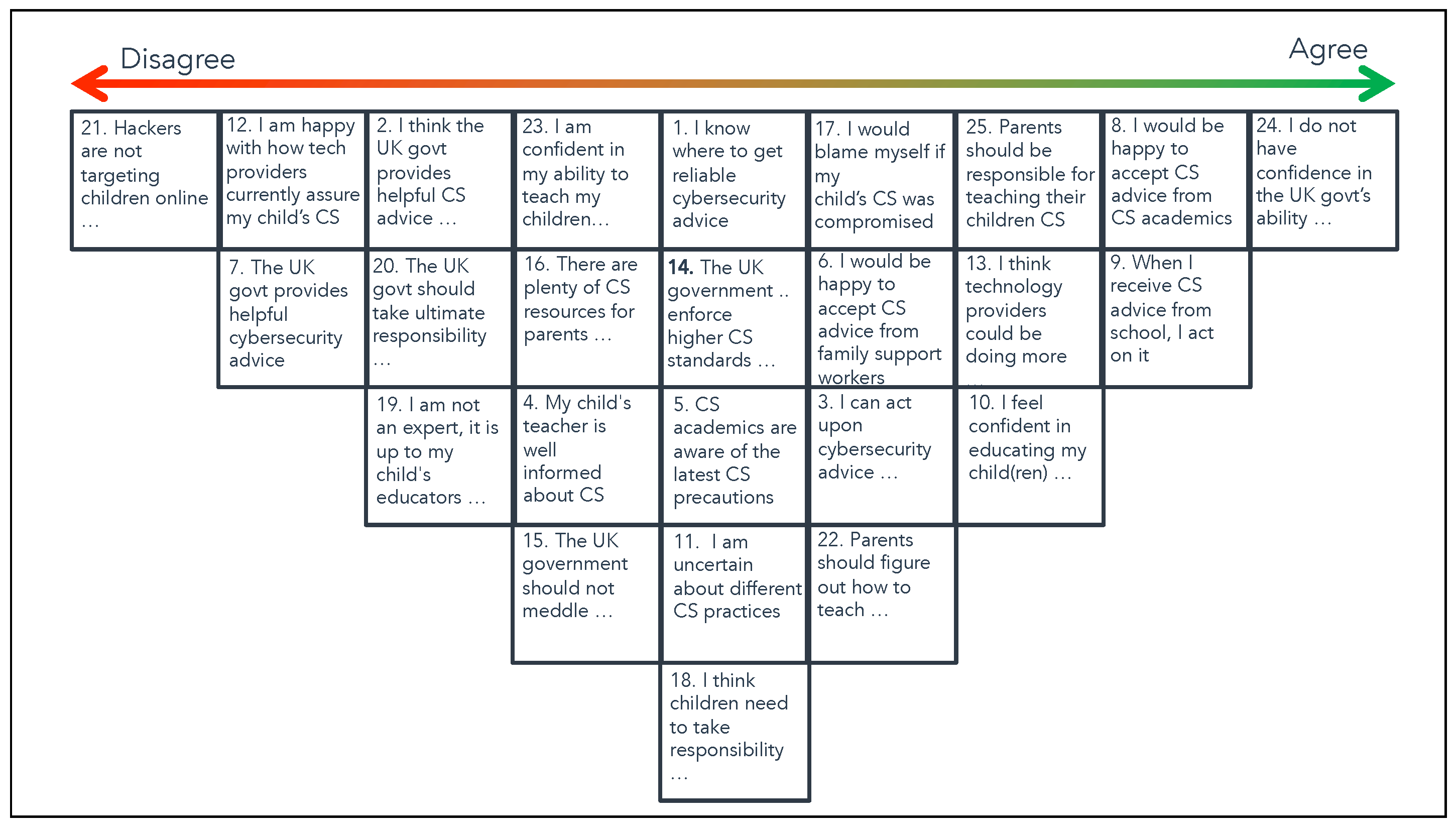
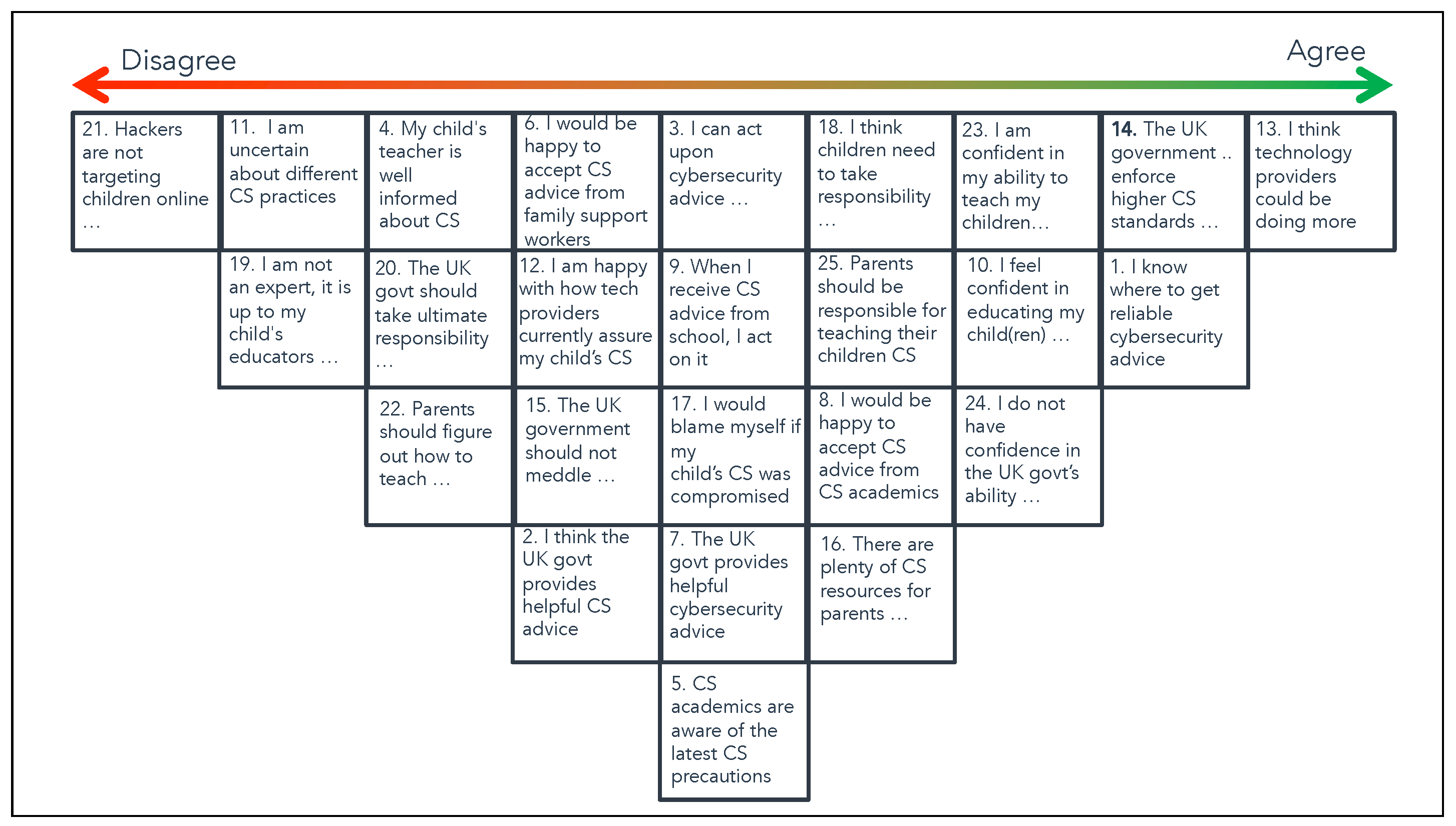
3.2. Analysis & Findings
4. Discussion and Reflection
4.1. Research Implications
4.2. Limitations
5. Conclusions and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
Appendix A


References
- Pérez-Morote, R.; Pontones-Rosa, C.; Núñez-Chicharro, M. The effects of e-government evaluation, trust and the digital divide in the levels of e-government use in European countries. Technol. Forecast. Soc. Chang. 2020, 154, 119973. [Google Scholar] [CrossRef]
- Ofcom. UK’s Internet Use Surges to Record Levels. 2020. Available online: https://www.ofcom.org.uk/about-ofcom/latest/media/media-releases/2020/uk-internet-use-surges (accessed on 1 September 2022).
- Livingstone, S.; Carr, J.; Byrne, J. One in Three: Internet Governance and Children’s Rights; UNICEF, Office of Research-Innocenti: Florence, Italy, 2016. [Google Scholar]
- The Institution of Engineering and Technology. Engineering Kids’ Futures. 2022. Available online: https://www.theiet.org/media/campaigns/engineering-kids-futures/ (accessed on 3 May 2023).
- Office for National Statistics. Children‘s Online Behaviour in England and Wales: Year Ending March 2020. 2020. Available online: https://www.ons.gov.uk/peoplepopulationandcommunity/crimeandjustice/bulletins/childrensonlinebehaviourinenglandandwales/yearendingmarch2020 (accessed on 1 September 2022).
- Fischer, S. Kids’ Daily Screen Time Surges during Coronavirus. 2020. Available online: https://www.axios.com/kids-screen-time-coronavirus-562073f6-0638-47f2-8ea3-4f8781d6b31b.html (accessed on 20 June 2020).
- Torluemke, J.; Kim, C. NortonLifeLock Study: Majority of Parents Say Their Kids’ Screen Time Has Skyrocketed during the COVID-19 Pandemic. 2020. Available online: https://investor.nortonlifelock.com/About/Investors/press-releases/press-release-details/2020/NortonLifeLock-Study-Majority-of-Parents-Say-Their-Kids-Screen-Time-Has-Skyrocketed-During-the-COVID-19-Pandemic/default.aspx (accessed on 20 June 2020).
- Peek, N.; Sujan, M.; Scott, P. Digital health and care in pandemic times: Impact of COVID-19. BMJ Health Care Inform. 2020, 27, e100166. [Google Scholar] [CrossRef] [PubMed]
- Walsh, B.; Rana, H. Continuity of academic library services during the pandemic the University of Toronto libraries’ response. J. Sch. Publ. 2020, 51, 237–245. [Google Scholar] [CrossRef]
- Attatfa, A.; Renaud, K.; De Paoli, S. Cyber diplomacy: A systematic literature review. Procedia Comput. Sci. 2020, 176, 60–69. [Google Scholar] [CrossRef] [PubMed]
- Hazlegreaves, S. Children Are Becoming More Vulnerable to Cybercriminals as IOT Device Use Explodes. 2019. Available online: https://www.openaccessgovernment.org/children-vulnerable-to-cybercriminals/72665/ (accessed on 1 September 2022).
- Renaud, K.; Prior, S. The “three M’s” counter-measures to children’s risky online behaviors: Mentor, mitigate and monitor. Inf. Comput. Secur. 2021, 29, 526–557. [Google Scholar] [CrossRef]
- Byron, T. Safer Children in a Digital World: The Report of the Byron Review: Be Safe, Be Aware, Have Fun. 2008. Available online: https://dera.ioe.ac.uk/id/eprint/7332/ (accessed on 1 May 2023).
- Refsdal, A.; Solhaug, B.; Stølen, K. Cybersecurity. In Cyber-Risk Management; Springer: Oslo, Norway, 2015; pp. 29–32. [Google Scholar] [CrossRef]
- Wurtele, S.K.; Gillispie, E.I.; Currier, L.L.; Franklin, C.F. A comparison of teachers vs. parents as instructors of a personal safety program for preschoolers. Child Abus. Negl. 1992, 16, 127–137. [Google Scholar] [CrossRef]
- Statista. Internet Usage in the United Kingdom (UK)—Statistics & Facts. 2022. Available online: https://www.statista.com/topics/3246/internet-usage-in-the-uk/ (accessed on 1 August 2022).
- Smahel, D.; MacHackova, H.; Mascheroni, G.; Dedkova, L.; Staksrud, E.; Olafsson, K.; Livingstone, S.; Hasebrink, U. EU Kids Online 2020: Survey Results from 19 Countries; London School of Economics and Political Science: London, UK, 2020; (accessed on 10 June 2023). [Google Scholar] [CrossRef]
- Purnama, S.; Ulfah, M.; Machali, I.; Wibowo, A.; Narmaditya, B.S. Does digital literacy influence students’ online risk? Evidence from COVID-19. Heliyon 2021, 7, e07406. [Google Scholar] [CrossRef]
- Renaud, K.; Orgeron, C.; Warkentin, M.; French, P.E. Cyber security responsibilization: An evaluation of the intervention approaches adopted by the Five Eyes countries and China. Public Adm. Rev. 2020, 80, 577–589. [Google Scholar] [CrossRef]
- Behar, N. Good Cybersecurity Starts at Home. Ph.D. Thesis, Cybersecurity, California State University , San Marcos, CA, USA, 2022. [Google Scholar]
- Guan, J.; Huck, J. Children in the digital age: Exploring issues of cybersecurity. In Proceedings of the 2012 iConference, Toronto, ON, Canada, 7–10 February 2012; ACM: Toronto, ON, Canada, 2012; pp. 506–507. [Google Scholar] [CrossRef]
- Anonymous. Exploring UK Parent Cyber Responsibilisation. GIQ under review. 2023. [Google Scholar]
- Muir, K.; Joinson, A. An exploratory study into the negotiation of cyber-security within the family home. Front. Psychol. 2020, 11, 424. [Google Scholar] [CrossRef]
- Office for National Statistics. Trust in Government, UK: 2022. 2022. Available online: https://www.ons.gov.uk/peoplepopulationandcommunity/wellbeing/bulletins/trustingovernmentuk/2022 (accessed on 4 April 2023).
- Edelman. 2023 Edelman Trust Barometer. 2023. Available online: https://edl.mn/3X0QXQE (accessed on 1 June 2023).
- Renaud, K.; van de Schyff, K.; MacDonald, S. Would US citizens accept cybersecurity deresponsibilization? Perhaps not. Comput. Secur. 2023, 2023, 103301. [Google Scholar] [CrossRef]
- Shamir, R. The age of responsibilization: On market-embedded morality. Econ. Soc. 2008, 37, 1–19. [Google Scholar] [CrossRef]
- Pellandini-Simányi, L.; Conte, L. Consumer de-responsibilization: Changing notions of consumer subjects and market moralities after the 2008–2009 financial crisis. Consum. Mark. Cult. 2021, 24, 280–305. [Google Scholar] [CrossRef]
- Ahmad, N.; Asma’Mokhtar, U.; Fauzi, W.F.P.; Othman, Z.A.; Yeop, Y.H.; Abdullah, S.N.H.S. Cyber security situational awareness among parents. In Proceedings of the 2018 Cyber Resilience Conference (CRC), Utrajava, Malaysia, 13–15 November 2018; pp. 1–3. [Google Scholar] [CrossRef]
- Prior, S.; Renaud, K. The impact of financial deprivation on children’s cybersecurity knowledge & abilities. Educ. Inf. Technol. 2022, 27, 10563–10583. [Google Scholar] [CrossRef]
- Rahman, N.A.A.; Sairi, I.; Zizi, N.; Khalid, F. The importance of cybersecurity education in school. Int. J. Inf. Educ. Technol. 2020, 10, 378–382. [Google Scholar] [CrossRef]
- Sağlam, R.B.; Miller, V.; Franqueira, V.N. A Systematic Literature Review on Cyber Security Education for Children. IEEE Trans. Educ. 2023, 66, 274–286. [Google Scholar] [CrossRef]
- Quayyum, F. Cyber security education for children through gamification: Challenges and research perspectives. In Proceedings of the 10th International Conference on Methodologies and Intelligent Systems for Technology Enhanced Learning, L’Aquila, Italy, 16–19 June 2020; Kubincová, Z., Lancia, L., Popescu, E., Nakayama, M., Scarano, V., Gil, A., Eds.; Springer International Publishing: Berlin, Germany, 2021; Volume 2, pp. 258–263. [Google Scholar] [CrossRef]
- Amankwa, E. Relevance of Cybersecurity Education at Pedagogy Levels in Schools. J. Inf. Secur. 2021, 12, 233–249. [Google Scholar] [CrossRef]
- Chiou, Y.M.; Shen, C.C.; Mouza, C.; Rutherford, T. Augmented reality-based cybersecurity education on phishing. In Proceedings of the International Conference on Artificial Intelligence and Virtual Reality (AIVR), Taichung, Taiwan, 15–17 November 2021; pp. 228–231. [Google Scholar] [CrossRef]
- Yuliana, Y. The importance of cybersecurity awareness for children. Lampung J. Int. Law 2022, 4, 41–48. [Google Scholar] [CrossRef]
- Nicholson, J.; Terry, J.; Beckett, H.; Kumar, P. Understanding Young People’s Experiences of Cybersecurity. In Proceedings of the EuroUSEC’21: Proceedings of the 2021 European Symposium on Usable Security, Online, 11–12 October 2021; pp. 200–210. [Google Scholar] [CrossRef]
- Lamond, M.; Renaud, K.; Wood, L.; Prior, S. SOK: Young children’s cybersecurity knowledge and skills. In Proceedings of the EuroUSEC, Karlsruhe, Germany, 29–30 September 2022; pp. 14–27. [Google Scholar] [CrossRef]
- National Cyber Security Centre. Create Your Cyber Action Plan. 2022. Available online: https://www.ncsc.gov.uk/cyberaware/actionplan (accessed on 1 September 2022).
- Nicholson, J.; Coventry, L.; Briggs, P. Introducing the Cybersurvival Task: Assessing and Addressing Staff Beliefs about Effective Cyber Protection. In Proceedings of the Fourteenth Symposium on Usable Privacy and Security (SOUPS 2018), Baltimore, MD, USA, 12–14 August 2018; pp. 443–457. [Google Scholar]
- Ondrušková, D.; Pospíšil, R. The good practices for implementation of cyber security education for school children. Contemp. Educ. Technol. 2023, 15, ep435. [Google Scholar] [CrossRef]
- Chrispeels, J. Effective schools and home-school-community partnership roles: A framework for parent involvement. Sch. Eff. Sch. Improv. 1996, 7, 297–323. [Google Scholar] [CrossRef]
- Quayyum, F. Collaboration between parents and children to raise cybersecurity awareness. In Proceedings of the European Interdisciplinary Cybersecurity Conference, Stavanger, Norway, 14–15 June 2023; pp. 149–152. [Google Scholar] [CrossRef]
- Clark, A. Cybersecurity in the UK; House of Commons Library: London, UK, 2023. [Google Scholar]
- Prior, S.; Renaud, K. Age-appropriate password “best practice” ontologies for early educators and parents. Int. J. Child-Comput. Interact. 2020, 23–24, 100169. [Google Scholar] [CrossRef]
- Renaud, K.; Prior, S. Children’s password-related books: Efficacious, vexatious and incongruous. Early Child. Educ. J. 2021, 49, 387–400. [Google Scholar] [CrossRef]
- Rawlings, R. Password Habits in the US and the UK: This Is What We Found. 2020. Available online: https://nordpass.com/blog/password-habits-statistics/ (accessed on 24 June 2023).
- Özer, Ö.; Subramanian, U.; Wang, Y. Information sharing, advice provision, or delegation: What leads to higher trust and trustworthiness? Manag. Sci. 2018, 64, 474–493. [Google Scholar] [CrossRef]
- Redmiles, E.M.; Malone, A.R.; Mazurek, M.L. I think they’re trying to tell me something: Advice sources and selection for digital security. In Proceedings of the IEEE Symposium on Security and Privacy (SP), San Jose, CA, USA, 22–26 May 2016; pp. 272–288. [Google Scholar] [CrossRef]
- Marques, J.F. Unlearning: The hardest lesson of all. Perform. Improv. 2007, 46, 5–6. [Google Scholar] [CrossRef]
- Liebowitz, S.J.; Margolis, S.E. Path dependence, lock-in, and history. J. Law Econ. Organ. 1995, 11, 205–226. [Google Scholar] [CrossRef]
- Jennings, W.; Stoker, G.; Valgarðsson, V.; Devine, D.; Gaskell, J. How trust, mistrust and distrust shape the governance of the COVID-19 crisis. J. Eur. Public Policy 2021, 28, 1174–1196. [Google Scholar] [CrossRef]
- Meredith, S. UK Prime Minister Boris Johnson Resigns. 2022. Available online: https://www.cnbc.com/2022/07/07/boris-johnson-resigns-as-uk-prime-minister.html (accessed on 1 August 2022).
- Davies, B.; Lalot, F.; Peitz, L.; Heering, M.S.; Ozkececi, H.; Babaian, J.; Davies Hayon, K.; Broadwood, J.; Abrams, D. Changes in political trust in Britain during the COVID-19 pandemic in 2020: Integrated public opinion evidence and implications. Humanit. Soc. Sci. Commun. 2021, 8, 166. [Google Scholar] [CrossRef]
- Solly, B. In Teachers We (Absolutely Must) Trust. 2021. Available online: https://www.sec-ed.co.uk/best-practice/in-teachers-we-absolutely-must-trust-school-improvement-retention-teaching-learning-pedagogy-accountability-leadership/ (accessed on 4 February 2023).
- Mori, I. Ipsos Veracity Index. 2022. Available online: https://www.ipsos.com/en-uk/ipsos-veracity-index-2022 (accessed on 5 April 2023).
- Pusey, P.; Sadera, W.A. Cyberethics, cybersafety, and cybersecurity: Preservice teacher knowledge, preparedness, and the need for teacher education to make a difference. J. Digit. Learn. Teach. Educ. 2011, 28, 82–85. [Google Scholar] [CrossRef]
- Pusey, P.; Sadera, W. Preservice teacher concerns about teaching cyberethics, cybersafety, and cybersecurity: A focus group study. In Proceedings of the Society for Information Technology & Teacher Education International Conference, Austin, TX, USA, 5–9 March 2012; pp. 3415–3419. [Google Scholar]
- Weale, S. UK Teachers ’Popping Pills’ as Workload Grinds Them Down, Union Told. 2022. Available online: https://www.theguardian.com/education/2022/apr/16/uk-teachers-popping-pills-workload-grinds-down-union-nasuwt (accessed on 14 September 2022).
- National Literacy Trust. Book Ownership in 2022. 2022. Available online: https://literacytrust.org.uk/research-services/research-reports/book-ownership-in-2022/ (accessed on 15 October 2022).
- Starbuck, L. Camilla and Kate Join Forces to Get Children Reading. 2022. Available online: https://royalcentral.co.uk/uk/camilla-and-kate-join-forces-to-get-children-reading-173402/ (accessed on 15 October 2022).
- Parr, C. People Trust Academics Far More than They Did in the 1990s. 2019. Available online: https://www.researchprofessionalnews.com/rr-news-uk-careers-2019-11-people-trust-academics-far-more-than-they-did-in-the-1990s/ (accessed on 22 November 2022).
- Radrizzani, S.; Fonseca, C.; Woollard, A.; Pettitt, J.; Hurst, L.D. Both trust in, and polarization of trust in, relevant sciences have increased through the COVID-19 pandemic. PLoS ONE 2023, 18, e0278169. [Google Scholar] [CrossRef]
- The British Academy. Academics Top ‘Trust’ List in British Academy Poll. 2022. Available online: https://www.thebritishacademy.ac.uk/news/academics-top-trust-list-in-british-academy-poll/ (accessed on 3 February 2023).
- Al-Naser, A.E.; Bushager, A.; Al-Junaid, H. Parents’ awareness and readiness for smart devices’ cybersecurity. In Proceedings of the 2nd Smart Cities Symposium (SCS 2019), Manama, Bahrain, 24–26 March 2019; pp. 1–7. [Google Scholar] [CrossRef]
- Google. How Google Fights Disinformation. 2019. Available online: https://www.blog.google/documents/37/How_Google_Fights_Disinformation.pdf (accessed on 17 January 2023).
- National Cyber Security Centre. Advice on How to Stay Secure Online from the UK’s National Cyber Security Centre. 2022. Available online: https://www.ncsc.gov.uk/cyberaware/home (accessed on 1 September 2022).
- BBC. The Official Home of CBBC-CBBC-BBC. 2022. Available online: https://www.bbc.co.uk/cbbc (accessed on 1 August 2022).
- Chartered Society of Physiotherapy. Thinking Differently about Support Workers. 2020. Available online: https://www.csp.org.uk/networks/associates-support-workers/thinking-differently-about-support-workers (accessed on 1 June 2023).
- Skills for Schools. Parent Support Adviser, Undated. Available online: http://www.skillsforschools.org.uk/roles-in-schools/parent-support-adviser/ (accessed on 1 September 2022).
- Stewart, C. Teaching Union Warns of Staffing Issues in Scottish Schools. 2023. Available online: https://www.heraldscotland.com/business_hq/23550569.teaching-union-warns-staffing-issues-scottish-schools/ (accessed on 1 June 2023).
- GOV.UK. Government Cyber Security Strategy: 2022 to 2030. 2022. Available online: https://www.gov.uk/government/publications/government-cyber-security-strategy-2022-to-2030 (accessed on 6 May 2023).
- Skipp, A.; Hopwood, V. Deployment of Teaching Assistants in Schools. 2019. Available online: https://www.gov.uk/government/publications/the-deployment-of-teaching-assistants-in-schools (accessed on 1 June 2023).
- Robinson, J. Northumberland Youth Clubs Could Be Forced to Turn Children Away after Council Cuts 12 Jobs. 2023. Available online: https://www.chroniclelive.co.uk/news/north-east-news/northumberland-youth-clubs-could-forced-27170272 (accessed on 1 June 2023).
- Ricci, J.; Breitinger, F.; Baggili, I. Survey results on adults and cybersecurity education. Educ. Inf. Technol. 2019, 24, 231–249. [Google Scholar] [CrossRef]
- Federal Bureau of Investigation. Internet Crime Report 2020. 2020. Available online: https://www.ic3.gov/Media/PDF/AnnualReport/2020_IC3Report.pdf (accessed on 1 June 2023).
- Stephenson, W. Correlating Persons Instead of Tests. J. Personal. 1935, 4, 17–24. [Google Scholar] [CrossRef]
- Brown, S.R. A Primer on Q Methodology. Operant. Subj. 1993, 16, 91–138. [Google Scholar] [CrossRef]
- Watts, S.; Stenner, P. Doing Q methodology: Theory, method and interpretation. Qual. Res. Psychol. 2005, 2, 67–91. [Google Scholar] [CrossRef]
- Nicholson, J.; Coventry, L.; Briggs, P. “If It’s Important It Will Be A Headline” Cybersecurity Information Seeking in Older Adults. In Proceedings of the 2019 CHI Conference on Human Factors in Computing Systems, Glasgow, UK, 4–9 May 2019; pp. 1–11. [Google Scholar] [CrossRef]
- Bada, M.; Sasse, A.M.; Nurse, J.R. Cyber security awareness campaigns: Why do they fail to change behaviour? arXiv 2019, arXiv:1901.02672. [Google Scholar]
- Watson, H.; Moju-Igbene, E.; Kumari, A.; Das, S. “We Hold Each Other Accountable”: Unpacking How Social Groups Approach Cybersecurity and Privacy Together. In Proceedings of the CHI Conference on Human Factors in Computing Systems, Online, 25–30 April 2020; pp. 1–12. [Google Scholar] [CrossRef]
- Turner, S.; Pattnaik, N.; Nurse, J.R.; Li, S. “You Just Assume It Is In There, I Guess”: Understanding UK Families’ Application and Knowledge of Smart Home Cyber Security. Proc. ACM Hum.-Comput. Interact. 2022, 6, 1–34. [Google Scholar] [CrossRef]
- Wallace, S.; Green, K.; Johnson, C.; Cooper, J.; Gilstrap, C. An Extended TOE Framework for Cybersecurity Adoption Decisions. Commun. Assoc. Inf. Syst. 2021, 47, 51. [Google Scholar] [CrossRef]
- Tazi, F.; Shrestha, S.; Norton, D.; Walsh, K.; Das, S. Parents, educators, & caregivers cybersecurity & privacy concerns for remote learning during COVID-19. In Proceedings of the CHI Greece 2021: 1st International Conference of the ACM Greek SIGCHI Chapter, Online, 25–27 November 2021; pp. 1–5. [Google Scholar]
- Quayyum, F.; Bueie, J.; Cruzes, D.S.; Jaccheri, L.; Vidal, J.C.T. Understanding parents’ perceptions of children’s cybersecurity awareness in Norway. In Proceedings of the Conference on Information Technology for Social Good, Rome, Italy, 9–11 September 2021; pp. 236–241. [Google Scholar] [CrossRef]
- AlShabibi, A.; Al-Suqri, M. Cybersecurity awareness and its impact on protecting children in cyberspace. In Proceedings of the 22nd International Arab Conference on Information Technology (ACIT), Ajman, United Arab Emirates, 22–24 November 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Milkaite, I.; Lievens, E. The internet of toys: Playing games with children’s data? In The Internet of Toys: Practices, Affordances and the Political Economy of Children’S Smart Play; Mascheroni, G., Holloway, D., Eds.; Springer: Cham, Switzerland, 2019; pp. 285–305. [Google Scholar] [CrossRef]
- Halevi, T.; Memon, N.; Lewis, J.; Kumaraguru, P.; Arora, S.; Dagar, N.; Aloul, F.; Chen, J. Cultural and psychological factors in cyber-security. In Proceedings of the 18th International Conference on Information Integration and Web-Based Applications and Services, Singapore, 28–30 November 2016; pp. 318–324. [Google Scholar] [CrossRef]
- Odebade, A.T.; Benkhelifa, E. Evaluating the impact of government Cyber Security initiatives in the UK. arXiv 2023, arXiv:2303.13943. [Google Scholar]
- UK Parliament. Online Safety Bill: HL Bill 87 of 2022–2023. 2023. Available online: https://lordslibrary.parliament.uk/research-briefings/lln-2023-0005/ (accessed on 1 May 2023).
- Lepper, D. Cost-of-Living Crisis: The Challenges in 2023. 2023. Available online: https://charitydigital.org.uk/topics/topics/cost-of-living-crisis-the-challenges-in-2023-10678#:~:text=Cost-of-living (accessed on 1 June 2023).
- Rose, R.; Wessels, B. Money, sex and broken promises: Politicians’ bad behaviour reduces trust. Parliam. Aff. 2019, 72, 481–500. [Google Scholar] [CrossRef]
- Grimmelikhuijsen, S.; Knies, E. Validating a scale for citizen trust in government organizations. Int. Rev. Adm. Sci. 2017, 83, 583–601. [Google Scholar] [CrossRef]
- Bayrakdar, S.; Guveli, A. Inequalities in Home Learning and Schools’ Provision of Distance Teaching during School Closure of COVID-19 Lockdown in the UK; Technical Report ISER Working Paper Series No. 2020-09; Institute for Social and Econmic Research: Colchester, UK, 2020; Available online: https://repository.essex.ac.uk/27995/ (accessed on 27 June 2023).

| Acronym | Advice Source | Provides Correct Advice | Trustworthiness |
|---|---|---|---|
| G | UK Government | ✔ | ✗ (Mistrusted) |
| T | Teachers | ≈ | ✔ (Trusted) |
| FF | Family & Friends | ≈ | ✔ (Trusted) |
| O | Online | ✗ | ✔ (Trusted) |
| A | Cybersecurity Academics | ✔ | ✔ (Trusted) |
| BK | Children’s Books | ✗ | ✔ (Trusted) |
| SW | Support Workers | ? | ✔ (Trusted) |
| # | Statement | Entity |
|---|---|---|
| 1. | I know where to get reliable cybersecurity advice [80] | P |
| 2. | I think the UK government provides helpful cybersecurity advice to parents (testing source) | G |
| 3. | I can act upon the cybersecurity advice I am given by the UK government [81] | G |
| 4. | My child’s teacher is well informed about cybersecurity [46] | T |
| 5. | Cybersecurity academics are aware of the latest cybersecurity precautions (testing source) | A |
| 6. | I would be happy to accept cybersecurity advice from family support workers/family liaison officers [82] | SW |
| 7. | The UK government provides helpful cybersecurity advice [22] | G |
| 8. | I would be happy to accept cybersecurity advice from cybersecurity academics (testing source) | A |
| 9. | When I receive cybersecurity advice from my child’s school, I act on it (testing source) | S |
| 10. | I feel confident in educating my child(ren) about cybersecurity precautions and good practice [75] | P |
| 11. | I am uncertain about different cybersecurity practices [83] | P |
| 12. | I am happy with how technology providers currently assure my child’s cybersecurity [84] | P |
| 13. | I think technology providers could be doing more to provide better cyber security controls for children [84] | TP |
| 14. | The UK government needs to enforce higher cybersecurity standards from technology providers [84] | G, TP |
| 15. | The UK government should not meddle with the way technology providers deal assure cybersecurity | G |
| 16. | There are plenty of cybersecurity resources for parents, schools do not need to get involved [85,86] | P |
| 17. | I would blame myself if my child’s cybersecurity was compromised [87] | P |
| 18. | I think children need to take responsibility for their online cyber security actions (testing responsibility) | C |
| 19. | I am not an expert, it is up to my child’s educators to teach them about cybersecurity [32] | T |
| 20. | The UK government should take ultimate responsibility for protecting my child’s cybersecurity (testing responsibility) | G |
| 21. | Hackers are not targeting children online so they don’t need to learn about cybersecurity until they are adults [88] | |
| 22. | Parents should figure out how to teach their children about cybersecurity without help from anyone else (testing responsibility) | P |
| 23. | I am confident in my ability to teach my children about cybersecurity [89] | P |
| 24. | I do not have confidence in the UK government’s ability to help me teach my child about cybersecurity [90] | G |
| 25. | Parents should be responsible for teaching their children about cybersecurity [22] | P |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Prior, S.; Renaud, K. Who Is Best Placed to Support Cyber Responsibilized UK Parents? Children 2023, 10, 1130. https://doi.org/10.3390/children10071130
Prior S, Renaud K. Who Is Best Placed to Support Cyber Responsibilized UK Parents? Children. 2023; 10(7):1130. https://doi.org/10.3390/children10071130
Chicago/Turabian StylePrior, Suzanne, and Karen Renaud. 2023. "Who Is Best Placed to Support Cyber Responsibilized UK Parents?" Children 10, no. 7: 1130. https://doi.org/10.3390/children10071130
APA StylePrior, S., & Renaud, K. (2023). Who Is Best Placed to Support Cyber Responsibilized UK Parents? Children, 10(7), 1130. https://doi.org/10.3390/children10071130







