Provably Secure Mutual Authentication and Key Agreement Scheme Using PUF in Internet of Drones Deployments
Abstract
:1. Introduction
1.1. Research Contributions
- We review and perform a security analysis of Akram et al.’s scheme. Then, we propose a MAKA scheme designed to ensure high security using biometrics and PUF. Hash functions and exclusive-OR operations are used for lightweight architecture, making the proposed scheme suitable for drone networks. Moreover, a fuzzy extractor and PUF are applied in the proposed scheme to enhance the security level.
- We perform an informal analysis to ensure that the proposed scheme can provide security against various attacks, including offline password guessing, session key disclosure, verification table leakage, impersonation, and DoS attacks. Additionally, we show that the proposed scheme can achieve mutual authentication, perfect forward secrecy, untraceability, and anonymity.
- We evaluate and compare the security features, communication, and computation costs of the proposed scheme with existing authentication schemes, including Akram et al.’s scheme.
1.2. Organization
2. Related Works
3. Preliminaries
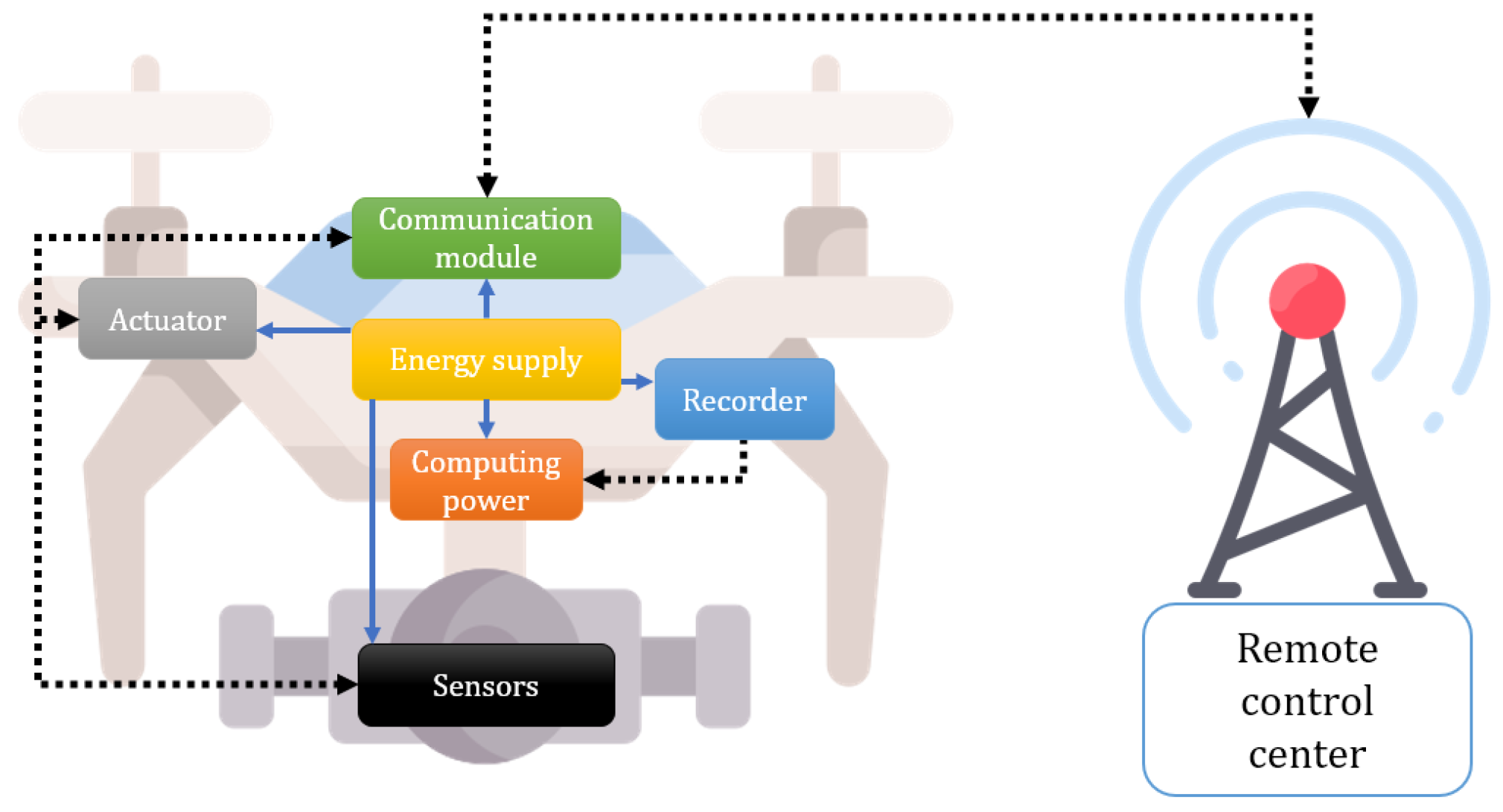
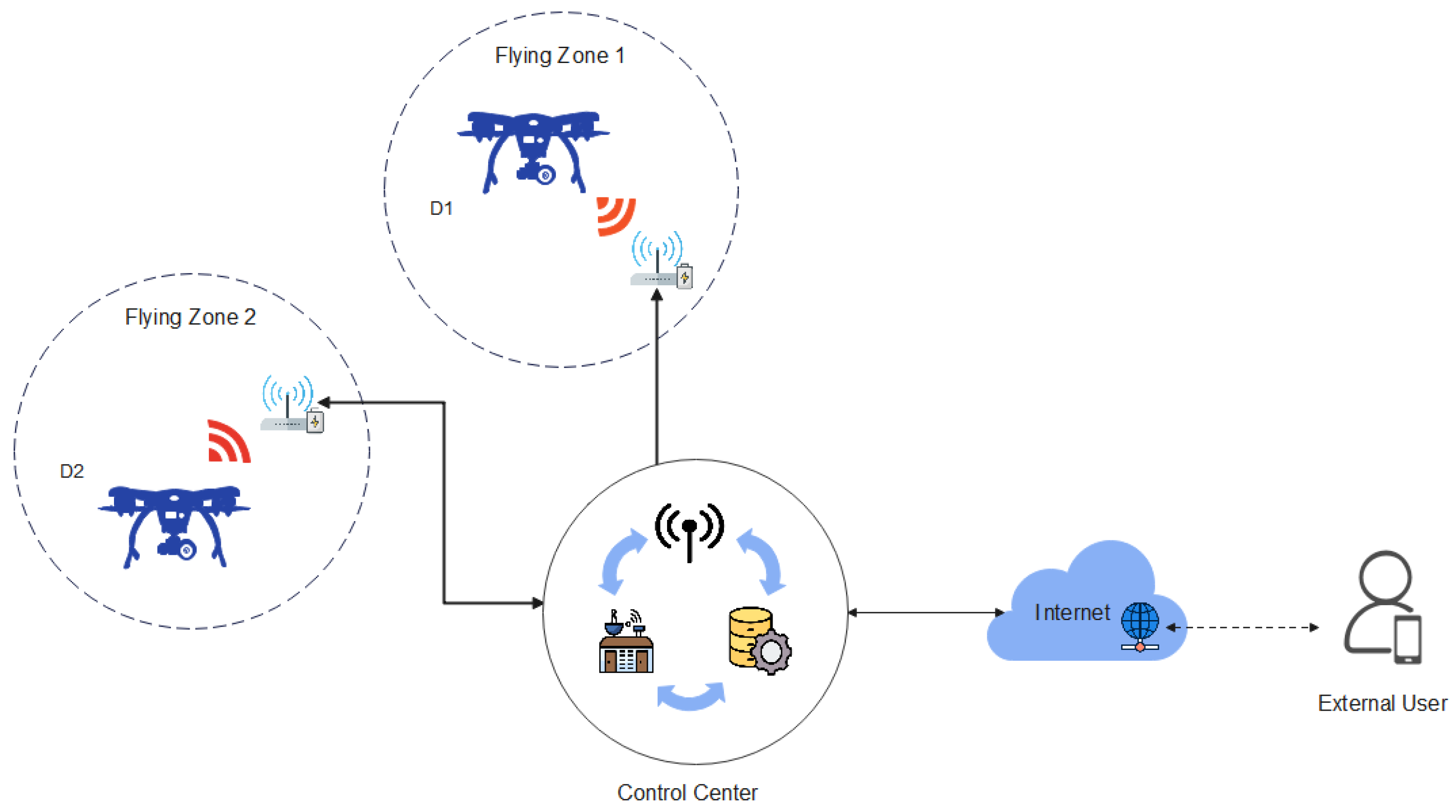
3.1. System Model
- Remote user (): A remote user owns a mobile device to receive IoD services. To communicate with a drone , must register with the control center. utilizes biometric technology in addition to identity and password to store sensitive information safely.
- Control center: The control center is a trusted third party with enough computation and storage capacities. Therefore, the control center perform a role as the system manager of IoD environments. Furthermore, the control center authenticates with both and information and helps to access the . The control center generates secret keys for and against their identities.
- Drone (): A drone collects the data in their particular flying zone and must be registered by the control center to communicate with . Then, sends the data to = through the control center. Moreover, has restricted computation and storage capacities.
3.2. Adversary Model
3.3. Fuzzy Extractor
- : It is a probabilistic algorithm to generate a secret key . The user inputs biometric , the output of this function is the secret parameter , and the public reproduction parameter .
- : It is a deterministic algorithm to recreate the original . The function accepts a noisy user biometric and controls the noise using the public reproduction parameter . Then, this algorithm reproduces the original biometric secret key .
3.4. Physical Unclonable Function
- The PUF is a physical microstructure of the device.
- It is extremely difficult or impossible to clone the PUF circuit.
- An unpredictable response value must be output.
- It is possible to evaluate and implement a PUF circuit easily.
4. Revisit of Akram et al.’s Scheme
4.1. Registration Phase
4.1.1. Remote User Registration Phase
- Step 1:
- The user inputs their own , and imprints . Then, calculates and sends to the control center.
- Step 2:
- The control center calculates , and generates a random number . After that, the control center computes and sends to .
- Step 3:
- computes , . Then, stores .
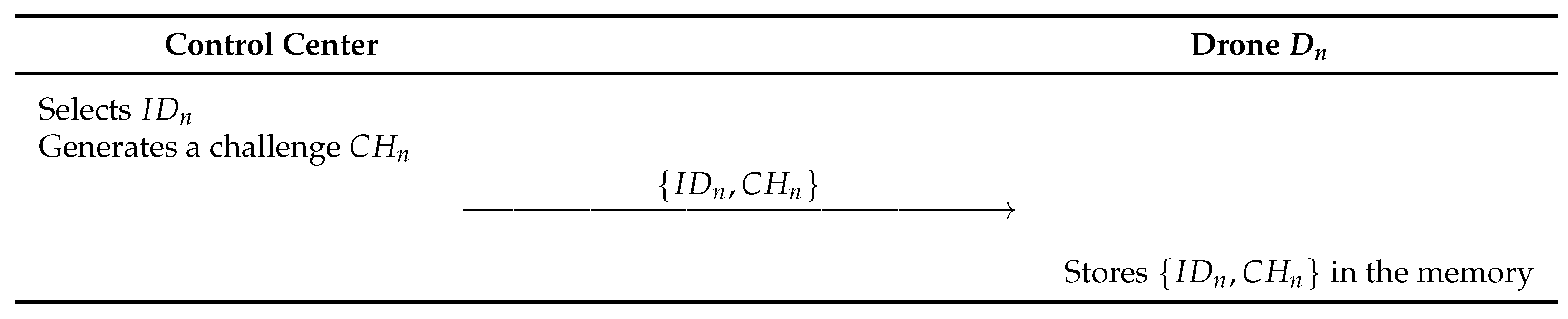
4.1.2. Drone Registration Phase
- Step 1:
- selects and sends it to the control center.
- Step 2:
- The control center computes , and stores in its database. Then, the control center sends to .
- Step 3:
- When receives , saves them in the memory.
4.2. AKA Phase
- Step 1:
- inputs , and also imprints . Then, computes , , . Afterward, generates and computes , and . Finally, sends to the control center.
- Step 2:
- The control center retrieves . Then, the control center computes , and , and verifies against . Then, the control center computes and checks . The control center generates , and computes , , and . Finally, the control center sends , to the drone .
- Step 3:
- computes , and . Then, checks and generates . After that, computes , , and . Finally, sends , to .
- Step 4:
- The computes , and . Then, it validates and computes .
5. Cryptanalysis of Akram et al.’s Scheme
5.1. Session Key Disclosure Attack
- Step 1:
- computes , , and .
- Step 2:
- calculates .
5.2. Drone Impersonation Attack
- Step 1:
- The adversary first intercepts transmitted by the public channel.
- Step 2:
- can obtain , by computing .
- Step 3:
- can compute through .
- Step 4:
- generates random and computes .
- Step 5:
- can successfully compute , .
5.3. Stolen-Verifier Attack
5.4. Perfect Forward Secrecy
5.5. DoS Attack
5.6. Correctness
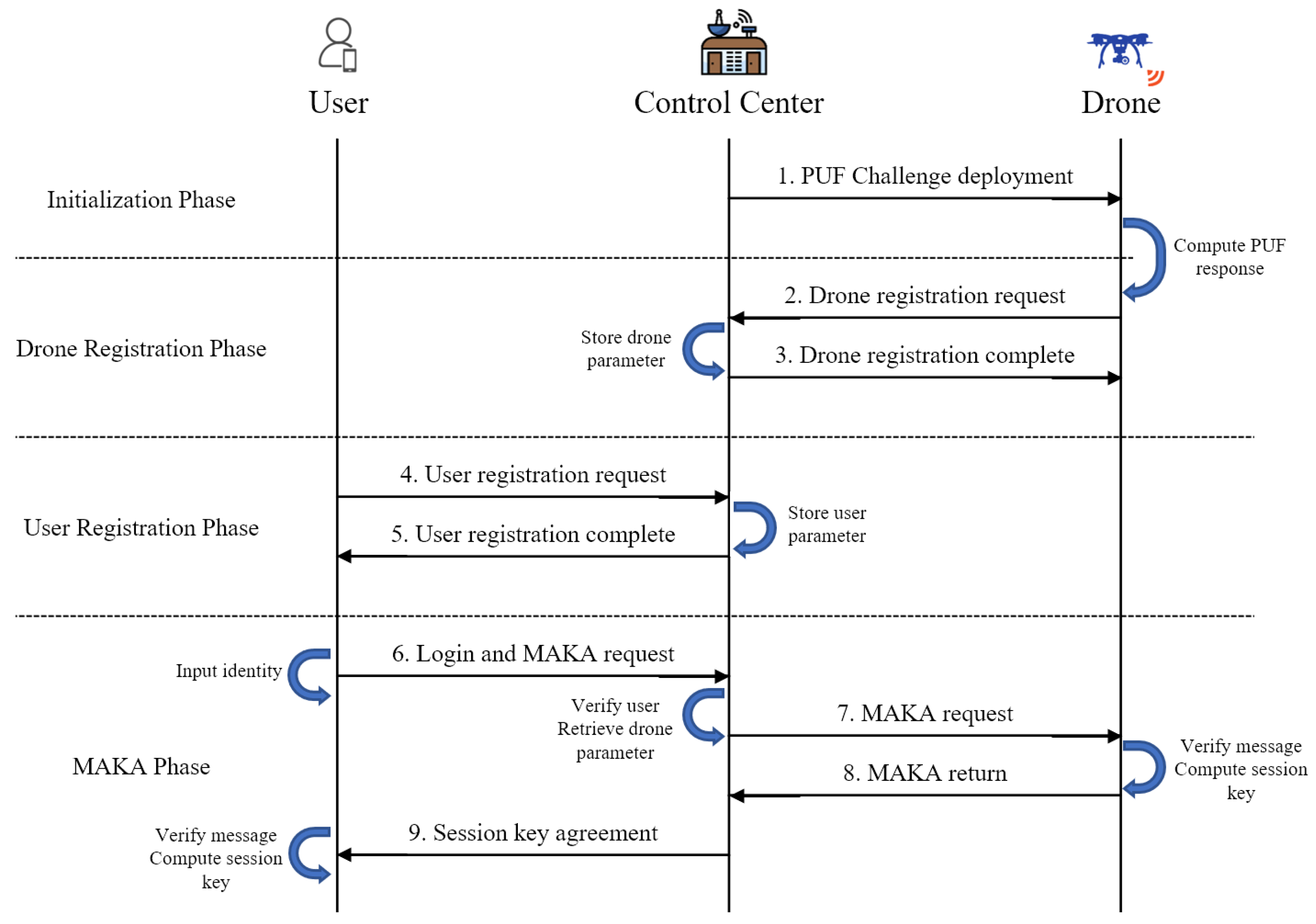
6. Proposed Scheme
6.1. Initialization Phase
- Step 1:
- The control center selects an identity and a challenge and sends to the drone .
- Step 2:
- The drone stores in the memory.
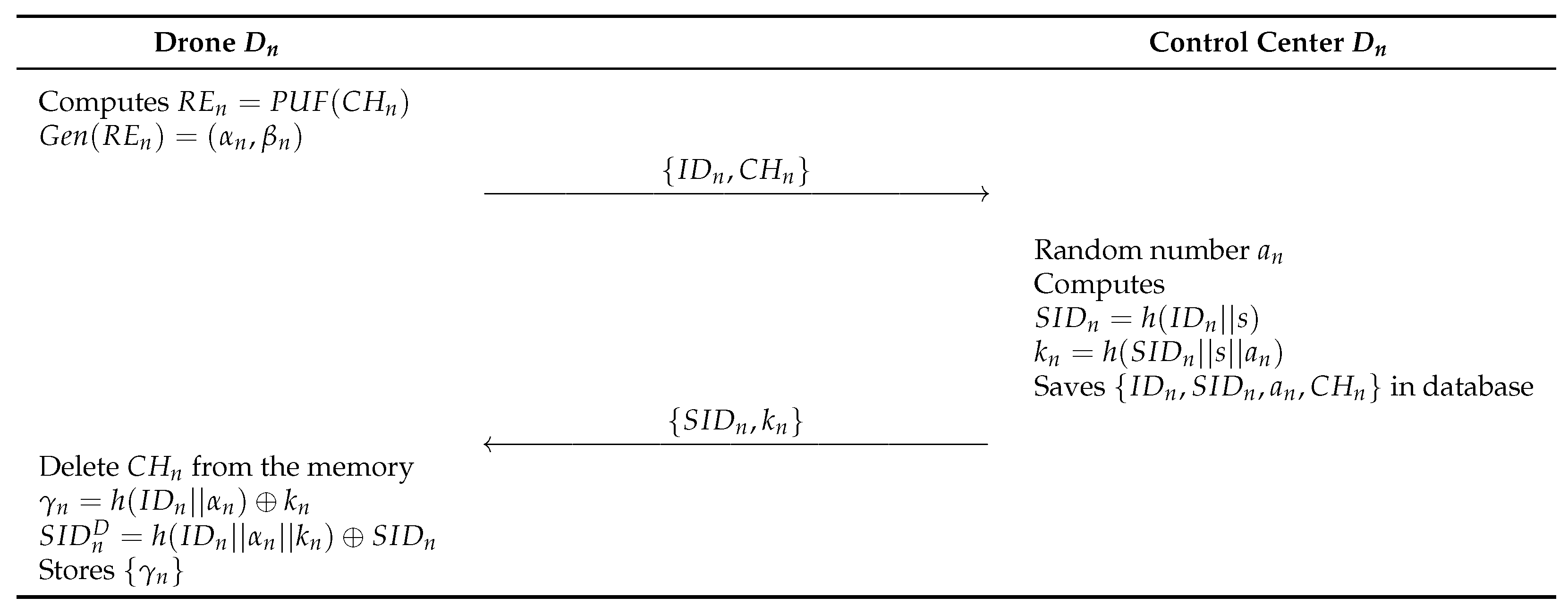
6.2. Drone Registration Phase
- Step 1:
- The drone retrieves the challenge stored in the memory and computes , and . After that, the sends to the control center.
- Step 2:
- The control center generates a random number and computes , , and saves in the database. Then, the control center sends to the .
- Step 3:
- Finally, the deletes the and computes , , and stores in its memory.
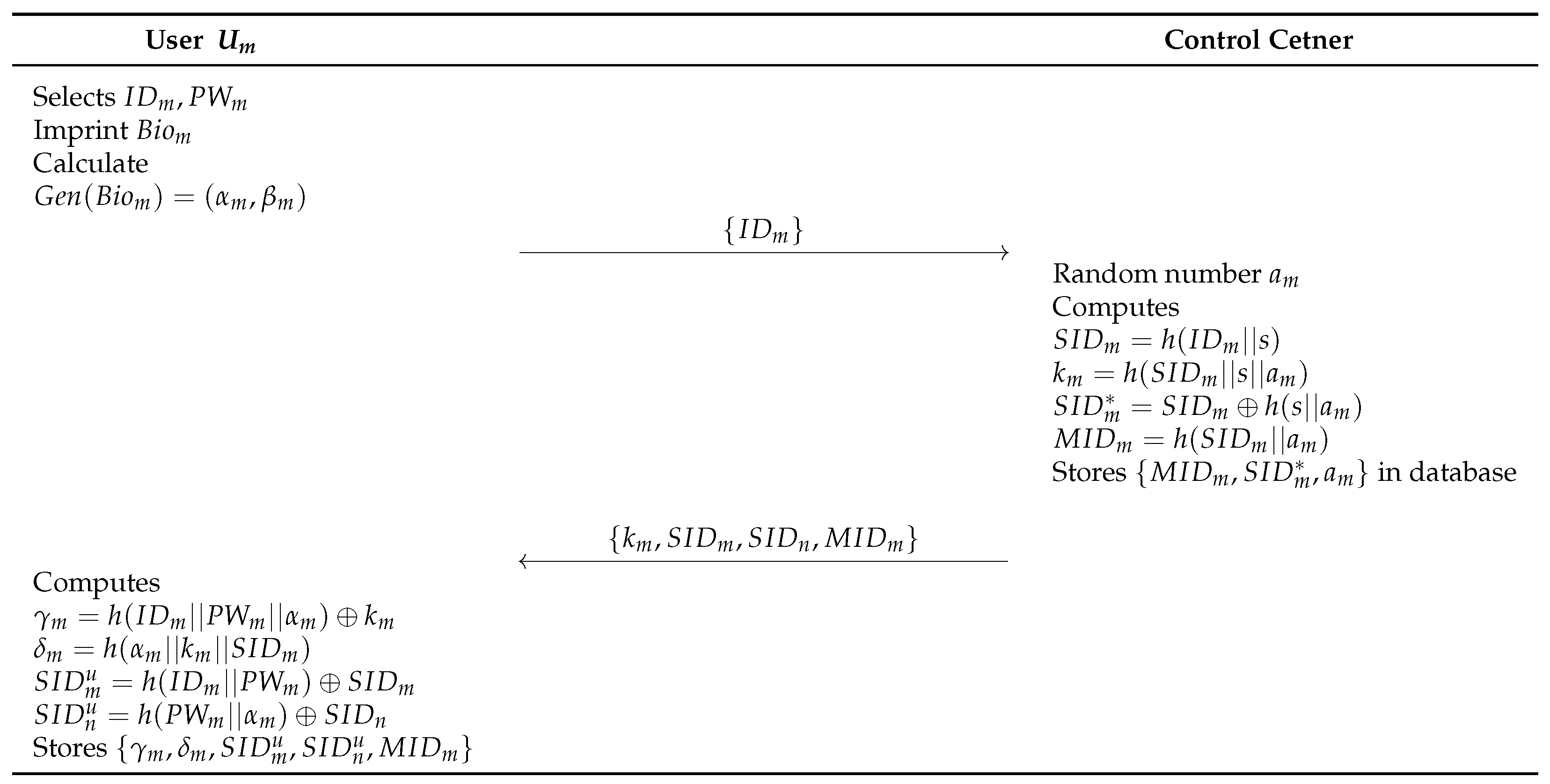
6.3. User Registration Phase
- Step 1:
- The user selects an identity , a password , and a biometric template . After that, the mobile device calculates . The sends to the control center.
- Step 2:
- The control center generates random number and computes , , and . Then, the control center stores in the database, and sends , to the .
- Step 3:
- The computes , , , and , and stores in the memory.
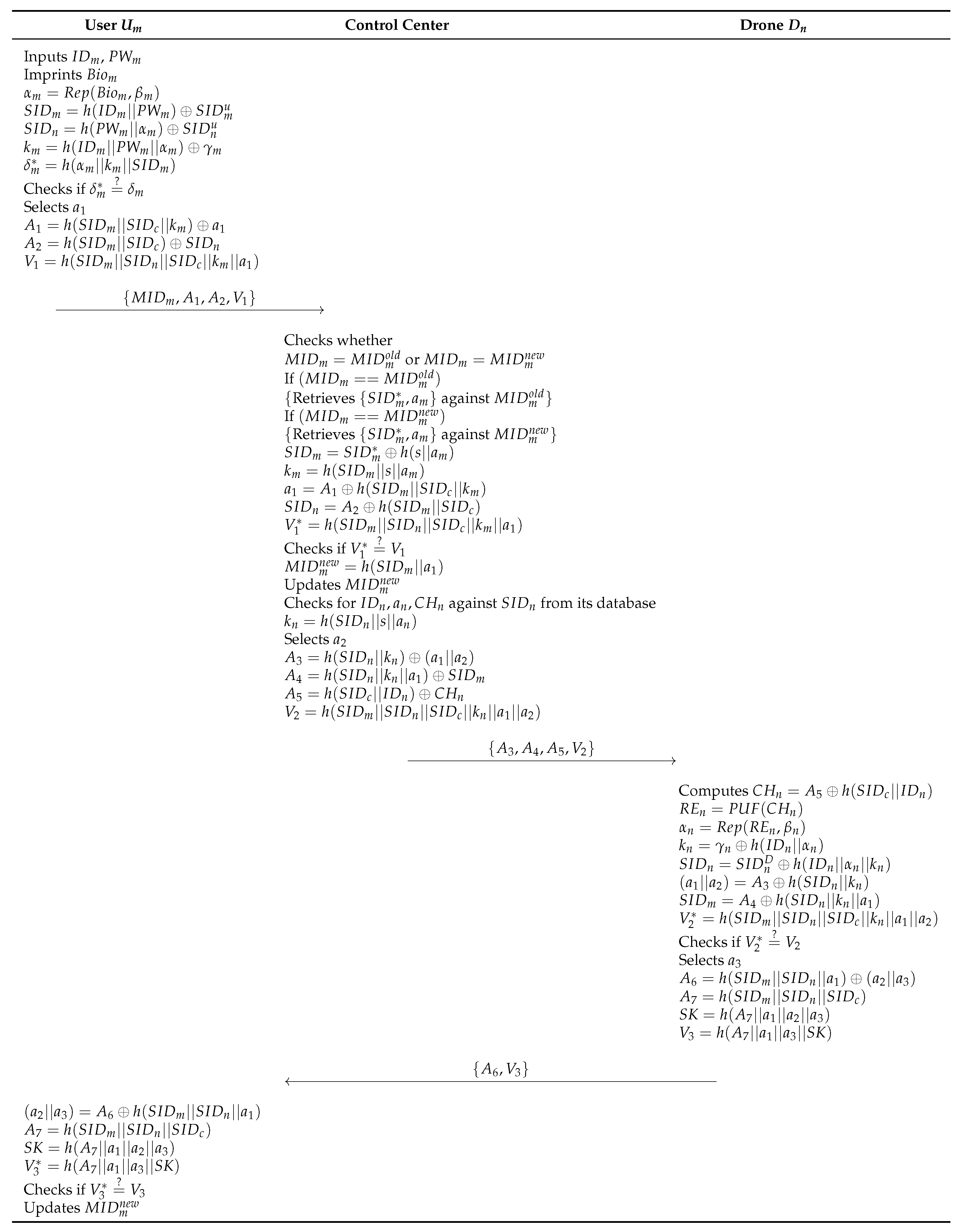
6.4. MAKA Phase
- Step 1:
- The inputs and , and imprints . After that, computes , , , , and , and checks . Then, the generates a random nonce and calculates , , and . The sends to the control center.
- Step 2:
- The control center checks whether or . If then, retrieves against , and if , retrieves against . After that, the control center computes , , , , and . If is correct, the control center computes and updates . Then, the control center checks for against from its database and computes . The control center calculates , , , and and sends to the drone.
- Step 3:
- The drone computes , , , , , , , and . If is correct, the generates a random nonce , and calculates , , , and . Then, the sends to the .
- Step 4:
- The computes , , , and and checks . Then, the updates .
7. Security Analysis
7.1. BAN Logic
7.1.1. Rules
- 1.
- MMR:
- 2.
- NVR:
- 3.
- JR:
- 4.
- BR:
- 5.
- FR:
7.1.2. Goals
- Goal 1:
- Goal 2:
- Goal 3:
- Goal 4:
7.1.3. Idealized Forms
- :
- :
- :
7.1.4. Assumptions
- :
- :
- :
- :
- :
- :
- :
- :
7.1.5. BAN Logic Proof
- Step 1:
- We can obtain from the message .
- Step 2:
- We can obtain from the rule MMR using and .
- Step 3:
- We can obtain from the rule FR using and .
- Step 4:
- We can obtain from the rule NVR using and .
- Step 5:
- We can obtain from the message .
- Step 6:
- We can obtain from the MMR using and .
- Step 7:
- We can obtain from the FR using and .
- Step 8:
- We can obtain from the NVR using and .
- Step 9:
- We can obtain from the message .
- Step 10:
- We can obtain from the MMR using and .
- Step 11:
- We can obtain from the NVR using and .
- Step 12:
- We can obtain and from and . Therefore, and can compute the session key , where .
- Step 13:
- We can obtain and from the jurisdiction rule using and , and and , respectively.
7.2. RoR Model
- : In this query, the adversary eavesdrop messages are transmitted via an open channel. Therefore, the adversary can obtain messages generated from , , and . This query is a passive attack.
- : In this query, the adversary can obtain secret parameters from using a power analysis attack. Therefore, the query CorruptDevice is an active attack.
- : In this query, the adversary can send messages to all participants , , and . Furthermore, the adversary can obtain returned messages from these participants. Thus, this query is an active attack
- : Before starting the game, an unbiased coin is flipped in this query. The adversary obtains when the session key is fresh. The adversary can also obtain when the session key of the proposed scheme cannot guarantee freshness. If not, the adversary obtains a “null value” ⊥. To achieve a secure session key agreement, the adversary cannot discriminate between the session key and the random number.
Security Proof
- :
- In , the adversary selects a random bit r. Thus, we obtain the following equation.
- :
- In , the adversary eavesdrops messages , , and using query. Then, the adversary performs the query to obtain the session key . To compute , the adversary must obtain the random nonces , , and . Moreover, is composed of , , and , where is the secret parameter of user. Therefore, the adversary cannot calculate . Therefore, we can obtain the following equation.
- :
- In , the adversary utilizes and to attack the network. However, all of the parameters are masked in a cryptographic hash function that can prevent the hash collision problem. For this reason, the adversary cannot obtain the session key . According to the birthday paradox [33], we can obtain the following inequation.
- :
- Similar to , the adversary utilizes queries and in this game. According to Section 3.4, the PUF is extremely difficult or impossible to clone. This means the adversary has no advantage in .
- :
- This game is the final game in which the adversary extracts secret parameters from the device of the user using the query . The adversary attempts to calculate from these parameters. However, each parameter consists of a password and the biometrics of a user, and this means that the adversary must guess the password and biometrics at the same time. Since this task is computationally infeasible, the adversary cannot compute . Therefore, we can obtain the following inequation using Zipf’s law [29].
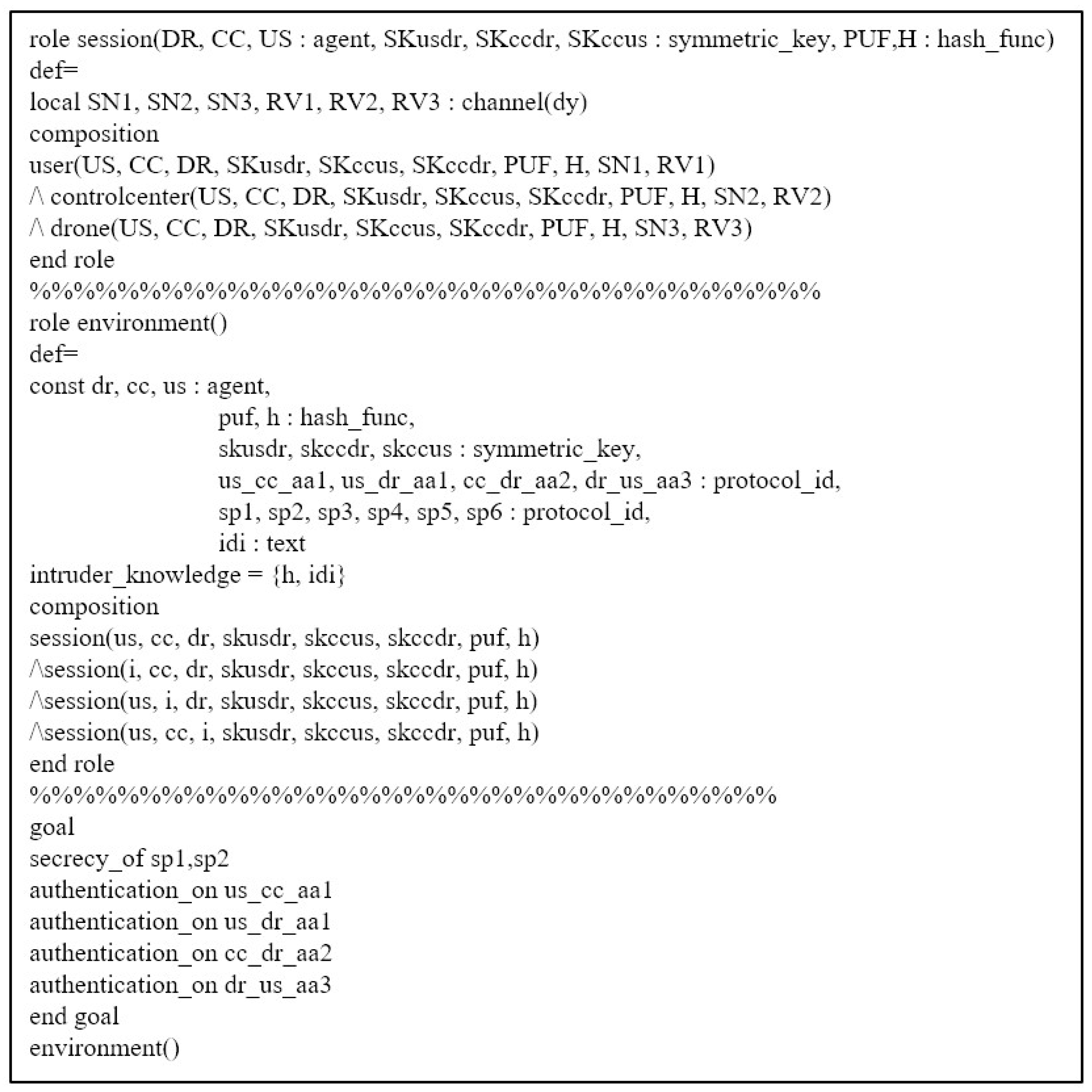
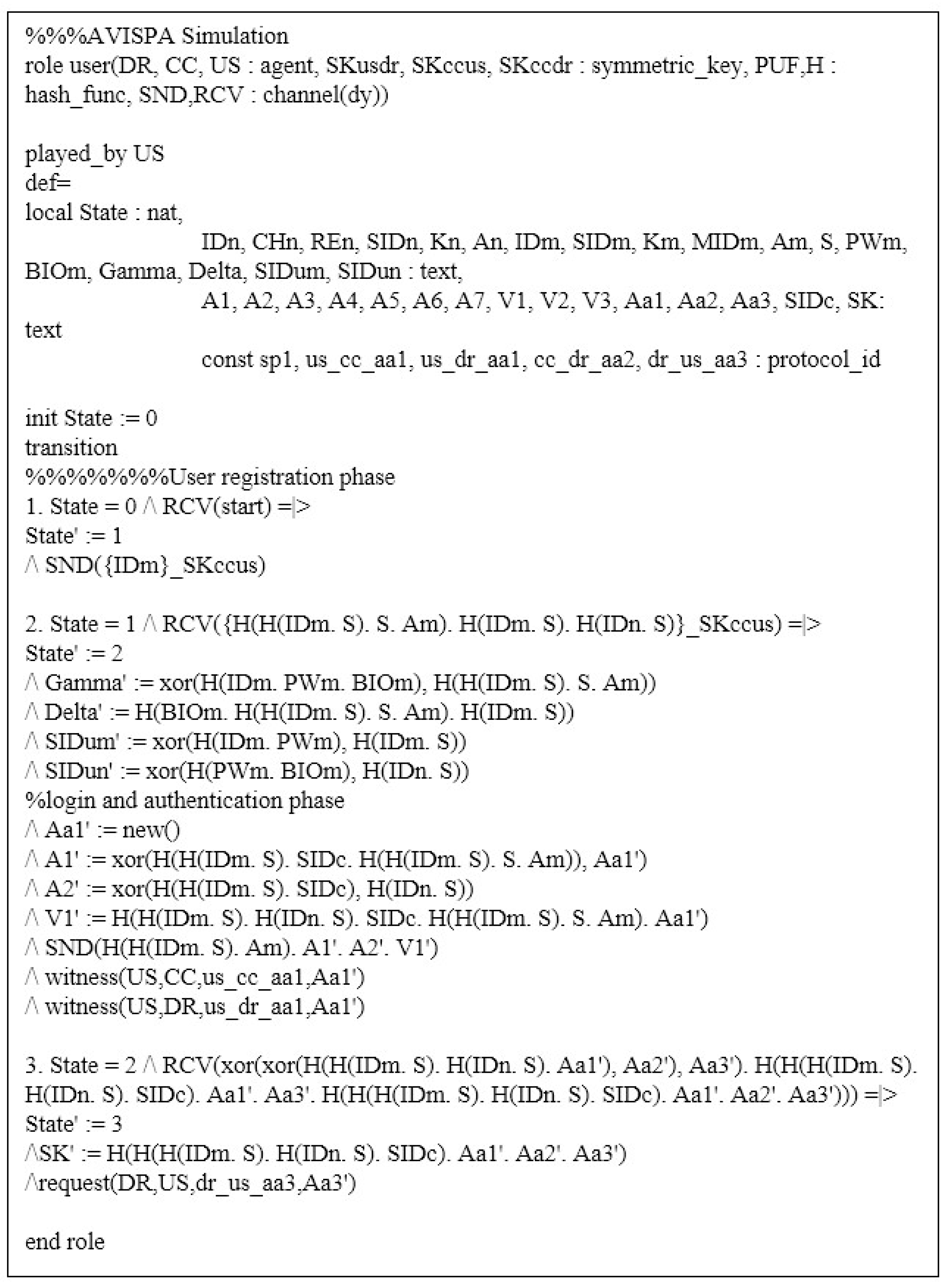
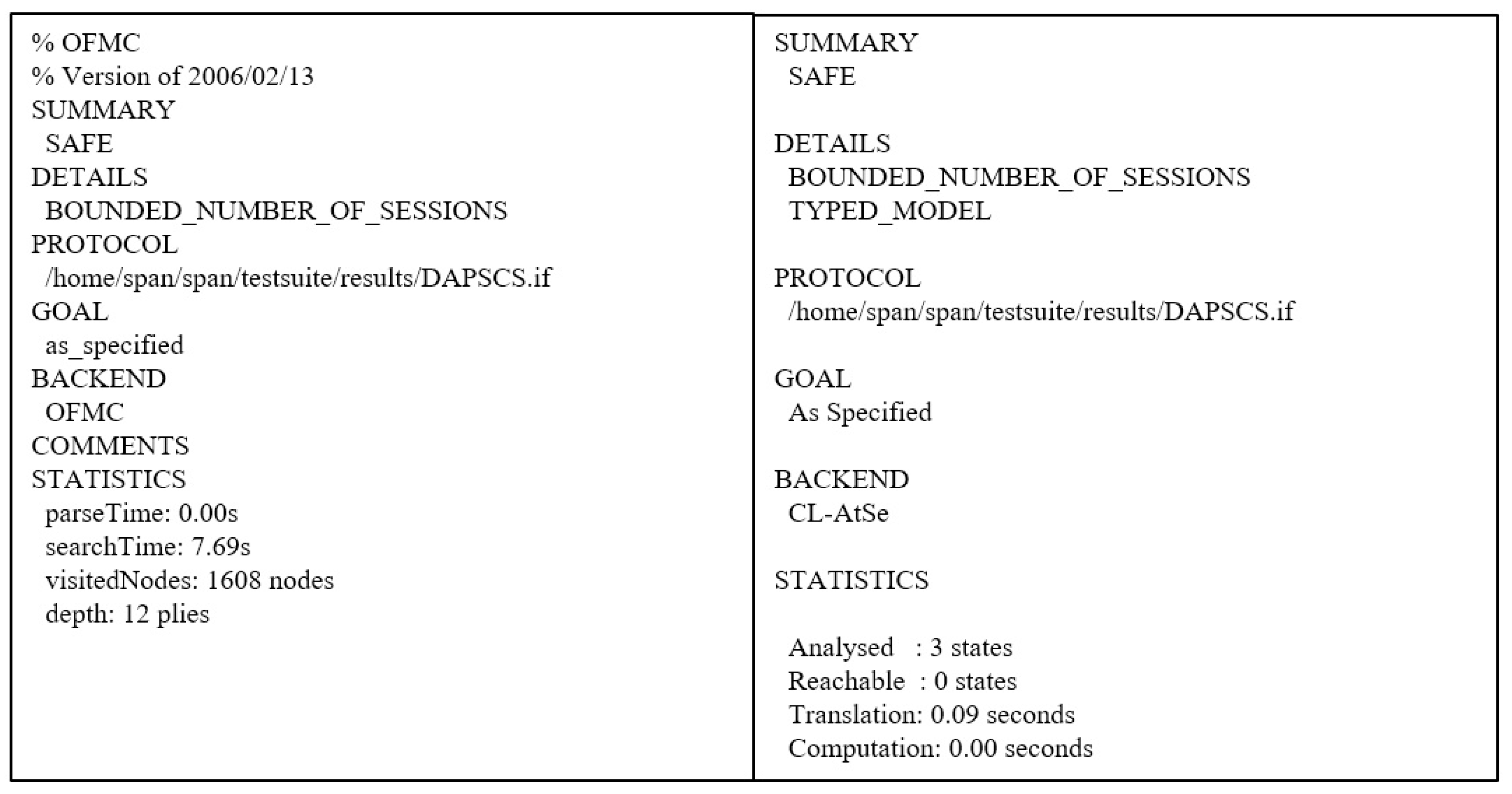
7.3. AVISPA Simulation
7.4. Informal Security Analysis
7.4.1. Stolen/lost Mobile Device Attack
7.4.2. Offline Password-Guessing Attack
7.4.3. Impersonation Attack
- (1)
- User impersonation attack: In this attack, an adversary tries to disguise a legitimate user . has to make a valid login request message . can obtain from the mobile device. However, without having the credentials , and , it is a difficult task for to calculate . Thus, cannot generate a valid login request message on behalf of . Hence, the proposed scheme provides protection against user impersonation attacks.
- (2)
- Control center impersonation attack: For this attack, let us suppose that tries to send the message to the on behalf of the CC. However, without having the credentials , and random nonce , it is computationally hard for to make a valid message. Therefore, the proposed scheme is resilient against the CC impersonation attack.
- (3)
- Drone impersonation attack: This attack is a disguise attack in which a malicious adversary conceals its identity information and attempts to behave as . To do this, computes . Since is a physical unclonable circuit, cannot compute . Therefore, it is impossible to compute , , , to calculate . Thus, the proposed scheme can prevent drone impersonation attacks.
7.4.4. Replay and MITM Attacks
7.4.5. Physical and Cloning Attacks
7.4.6. Privileged Insider Attack
7.4.7. Ephemeral Security Leakage Attack
7.4.8. Stolen-Verifier Attack
7.4.9. User Anonymity and Untraceability
7.4.10. Perfect Forward Secrecy
7.4.11. Mutual Authentication
7.4.12. DoS Attack
7.4.13. Drone Capture Attack
7.4.14. Session Key Disclosure Attack
8. Performance Analysis
8.1. Security Features Comparison
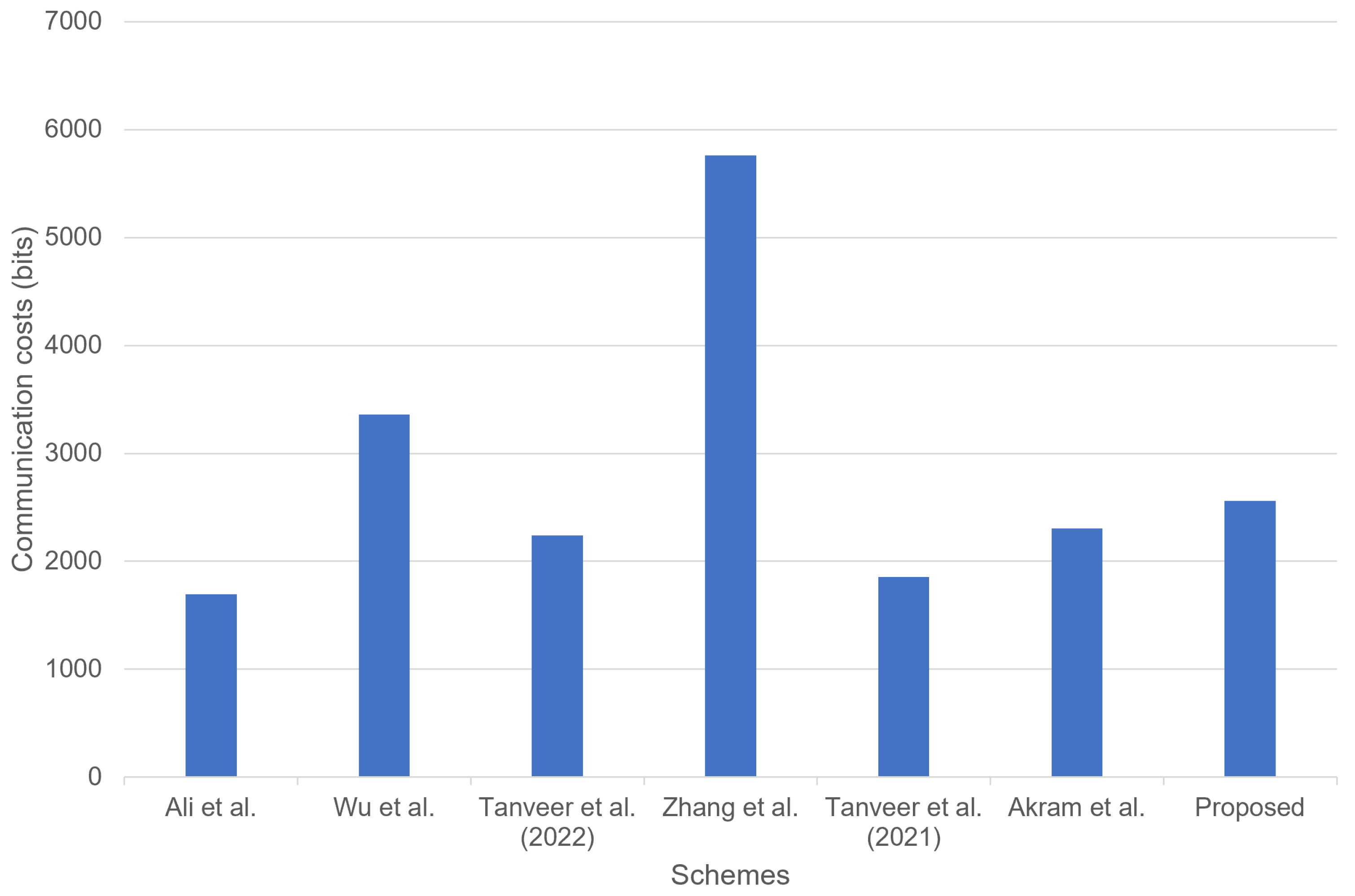
8.2. Communication Costs Comparison
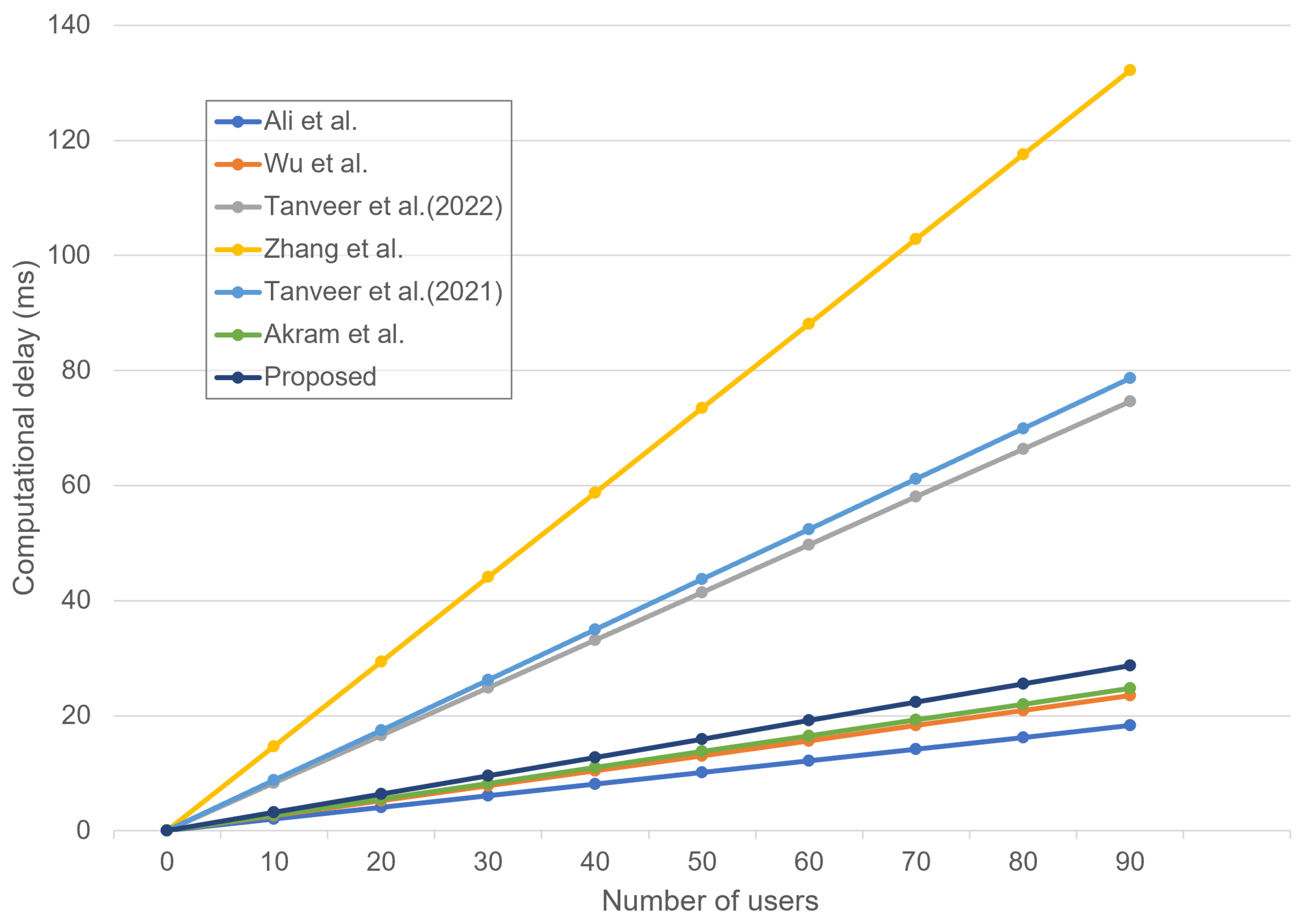
8.3. Computation Costs Comparison
9. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Gharibi, M.; Boutaba, R.; Waslander, S.L. Internet of drones. IEEE Access 2016, 4, 1148–1162. [Google Scholar] [CrossRef]
- Abualigah, L.; Diabat, A.; Sumari, P.; Gandomi, A.H. Applications, deployments, and integration of internet of drones (iod): A review. IEEE Sens. J. 2021, 21, 25532–25546. [Google Scholar] [CrossRef]
- Lin, C.; He, D.; Kumar, N.; Choo, K.K.R.; Vinel, A.; Huang, X. Security and privacy for the internet of drones: Challenges and solutions. IEEE Commun. Mag. 2018, 56, 64–69. [Google Scholar] [CrossRef]
- Akram, M.W.; Bashir, A.K.; Shamshad, S.; Saleem, M.A.; AlZubi, A.A.; Chaudhry, S.A.; Alzahrani, B.A.; Zikria, Y.B. A secure and lightweight drones-access protocol for smart city surveillance. IEEE Trans. Intell. Transp. Syst. 2021, 23, 19634–19643. [Google Scholar] [CrossRef]
- Umar, M.; Islam, S.H.; Mahmood, K.; Ahmed, S.; Ghaffar, Z.; Saleem, M.A. Provable secure identity-based anonymous and privacy-preserving inter-vehicular authentication protocol for VANETS using PUF. IEEE Trans. Veh. Technol. 2021, 70, 12158–12167. [Google Scholar] [CrossRef]
- Herder, C.; Yu, M.D.; Koushanfar, F.; Devadas, S. Physical unclonable functions and applications: A tutorial. Proc. IEEE 2014, 102, 1126–1141. [Google Scholar] [CrossRef]
- AVISPA, T. Automated Validation of Internet Security Protocols and Applications. 2015. Available online: https://www.avispa-project.org/ (accessed on 6 February 2023).
- Glouche, Y.; Genet, T.; Heen, O.; Courtay, O. A security protocol animator tool for AVISPA. In Proceedings of the ARTIST2 Workshop on Security Specification and Verification of Embedded Systems, Pisa, Italy, 18–20 May 2006; pp. 1–7. [Google Scholar]
- Abdalla, M.; Fouque, P.A.; Pointcheval, D. Password-based authenticated key exchange in the three-party setting. In Proceedings of the International Workshop on Public Key Cryptography, Les Diablerets, Switzerland, 23–26 January 2005; Springer: Berlin/Heidelberg, Germany, 2005; pp. 65–84. [Google Scholar]
- Burrows, M.; Abadi, M.; Needham, R. A logic of authentication. ACM Trans. Comput. Syst. (TOCS) 1990, 8, 18–36. [Google Scholar] [CrossRef]
- Wazid, M.; Das, A.K.; Kumar, N.; Vasilakos, A.V.; Rodrigues, J.J. Design and analysis of secure lightweight remote user authentication and key agreement scheme in Internet of drones deployment. IEEE Internet Things J. 2018, 6, 3572–3584. [Google Scholar] [CrossRef]
- Teng, L.; Jianfeng, M.; Pengbin, F.; Yue, M.; Xindi, M.; Jiawei, Z.; Gao, C.; Di, L. Lightweight security authentication mechanism towards UAV networks. In Proceedings of the 2019 International Conference on Networking and Network Applications (NaNA), Daegu City, Republic of Korea, 10–13 October 2019; pp. 379–384. [Google Scholar]
- Srinivas, J.; Das, A.K.; Kumar, N.; Rodrigues, J.J. TCALAS: Temporal credential-based anonymous lightweight authentication scheme for Internet of drones environment. IEEE Trans. Veh. Technol. 2019, 68, 6903–6916. [Google Scholar] [CrossRef]
- Ali, Z.; Chaudhry, S.A.; Ramzan, M.S.; Al-Turjman, F. Securing smart city surveillance: A lightweight authentication mechanism for unmanned vehicles. IEEE Access 2020, 8, 43711–43724. [Google Scholar] [CrossRef]
- Ever, Y.K. A secure authentication scheme framework for mobile-sinks used in the internet of drones applications. Comput. Commun. 2020, 155, 143–149. [Google Scholar] [CrossRef]
- Deebak, B.D.; AI-Turjman, F. A smart lightweight privacy preservation scheme for IoT-based UAV communication systems. Comput. Commun. 2020, 162, 102–117. [Google Scholar] [CrossRef]
- Wu, T.; Guo, X.; Chen, Y.; Kumari, S.; Chen, C. Amassing the security: An enhanced authentication protocol for drone communications over 5G networks. Drones 2022, 6, 10–29. [Google Scholar] [CrossRef]
- Tanveer, M.; Alkhayyat, A.; Naushad, A.; Kumar, N.; Alharbi, A.G. RUAM-IoD: A Robust User Authentication Mechanism for the Internet of Drones. IEEE Access 2022, 10, 19836–19851. [Google Scholar] [CrossRef]
- Alladi, T.; Chamola, V.; Kumar, N. PARTH: A two-stage lightweight mutual authentication protocol for UAV surveillance networks. Comput. Commun. 2020, 160, 81–90. [Google Scholar] [CrossRef]
- Pu, C.; Li, Y. Lightweight authentication protocol for unmanned aerial vehicles using physical unclonable function and chaotic system. In Proceedings of the 2020 IEEE International Symposium on Local and Metropolitan Area Networks (LANMAN), Orlando, FL, USA, 13–15 July 2020; pp. 1–6. [Google Scholar]
- Zhang, N.; Jiang, Q.; Li, L.; Ma, X.; Ma, J. An efficient three-factor remote user authentication protocol based on BPV-FourQ for internet of drones. Peer-to-Peer Netw. Appl. 2021, 14, 3319–3332. [Google Scholar] [CrossRef]
- Dolev, D.; Yao, A. On the security of public key protocols. IEEE Trans. Inf. Theory 1983, 29, 198–208. [Google Scholar] [CrossRef]
- Chattaraj, D.; Bera, B.; Das, A.K.; Rodrigues, J.J.; Park, Y. Designing Fine-Grained Access Control for Software-Defined Networks Using Private Blockchain. IEEE Internet Things J. 2021, 9, 1542–1559. [Google Scholar] [CrossRef]
- Tanveer, M.; Kumar, N.; Hassan, M.M. RAMP-IoD: A robust authenticated key management protocol for the Internet of Drones. IEEE Internet Things J. 2021, 9, 1339–1353. [Google Scholar] [CrossRef]
- Dodis, Y.; Reyzin, L.; Smith, A. Fuzzy extractors: How to generate strong keys from biometrics and other noisy data. In Proceedings of the International Conference on the Theory and Applications of Cryptographic Techniques, Interlaken, Switzerland, 2–6 May 2004; Springer: Berlin/Heidelberg, Germany, 2004; pp. 523–540. [Google Scholar]
- Kim, M.; Lee, J.; Park, K.; Park, Y.; Park, K.H.; Park, Y. Design of secure decentralized car-sharing system using blockchain. IEEE Access 2021, 9, 54796–54810. [Google Scholar] [CrossRef]
- Kwon, D.K.; Yu, S.J.; Lee, J.Y.; Son, S.H.; Park, Y.H. WSN-SLAP: Secure and lightweight mutual authentication protocol for wireless sensor networks. Sensors 2021, 21, 936. [Google Scholar] [CrossRef]
- Shashidhara, R.; Nayak, S.K.; Das, A.K.; Park, Y. On the design of lightweight and secure mutual authentication system for global roaming in resource-limited mobility networks. IEEE Access 2021, 9, 12879–12895. [Google Scholar] [CrossRef]
- Wang, D.; Cheng, H.; Wang, P.; Huang, X.; Jian, G. Zipf’s law in passwords. IEEE Trans. Inf. Forensics Secur. 2017, 12, 2776–2791. [Google Scholar] [CrossRef]
- Bagga, P.; Das, A.K.; Wazid, M.; Rodrigues, J.J.; Choo, K.K.R.; Park, Y. On the design of mutual authentication and key agreement protocol in internet of vehicles-enabled intelligent transportation system. IEEE Trans. Veh. Technol. 2021, 70, 1736–1751. [Google Scholar] [CrossRef]
- Son, S.; Lee, J.; Park, Y.; Park, Y.; Das, A.K. Design of blockchain-based lightweight V2I handover authentication protocol for VANET. IEEE Trans. Netw. Sci. Eng. 2022, 9, 1346–1358. [Google Scholar] [CrossRef]
- Wazid, M.; Bagga, P.; Das, A.K.; Shetty, S.; Rodrigues, J.J.; Park, Y. AKM-IoV: Authenticated key management protocol in fog computing-based Internet of vehicles deployment. IEEE Internet Things J. 2019, 6, 8804–8817. [Google Scholar] [CrossRef]
- Boyko, V.; MacKenzie, P.; Patel, S. Provably secure password-authenticated key exchange using Diffie-Hellman. In Proceedings of the International Conference on the Theory and Applications of Cryptographic Techniques, Bruges, Belgium, 14–18 May 2000; Springer: Berlin/Heidelberg, Germany, 2000; pp. 156–171. [Google Scholar]
- Kwon, D.; Son, S.; Park, Y.; Kim, H.; Park, Y.; Lee, S.; Jeon, Y. Design of Secure Handover Authentication Scheme for Urban Air Mobility Environments. IEEE Access 2022, 10, 42529–42541. [Google Scholar] [CrossRef]
- Ryu, J.; Oh, J.; Kwon, D.; Son, S.; Lee, J.; Park, Y.; Park, Y. Secure ECC-based three-factor mutual authentication protocol for telecare medical information system. IEEE Access 2022, 10, 11511–11526. [Google Scholar] [CrossRef]
| Schemes | Cryptographic Technologies | Advantages and Limitations |
|---|---|---|
| Wazid et al. [11] | * Hash functions * Fuzzy extractor | * Presented IoD environments and utilized biometrics information to ensure the security of remote users * Vulnerable to privileged insider and impersonation attacks |
| Teng et al. [12] | * ECDSA | * Defined security threats in IoD environments named “attacker mode” * Requires large computation overheads |
| Srinivas et al. [13] | * Hash functions * Fuzzy extractor | * Used temporal credentials for mutual authentication * Vulnerable to untraceability and stolen verifier attacks |
| Ali et al. [14] | * Hash functions * Fuzzy extractor * Symmetric key primitives | * Anonymous and lightweight security solution using temporal credentials and symmetric key primitives * Vulnerable to ESL, physical and cloning attacks |
| Ever et al. [15] | * Bilinear pairings * ECC | * Analyzed studies utilized UAVs as mobile sinks * Require high computation overheads * Cannot provide anonymity and untraceability |
| Wu et al. [17] | * Hash functions * Fuzzy extractor | * Proposed a drone-to-user authentication scheme for 5G networks * Vulnerable to physical attacks due to the stored parameters in UAV |
| Tanveer et al. [18] | * Hash functions * Fuzzy extractor * ECC * Symmetric key primitives | * Provides anonymous communication to users using AES and ECC * Vulnerable to physical attacks due to the stored parameters in UAV |
| Alladi et al. [19] | * PUF * Message authentication code * Symmetric key primitives | * Classified drones by layer and proposed PUF-based two-stage authentication protocol * Vulnerable to replay, insider, server spoofing, DoS attacks |
| Pu et al. [20] | * PUF * Chaotic system | * Used PUF and chaotic map technologies to generate random key * Vulnerable to physical attacks because of a stored challenge value in the memory of UAV |
| Zhang et al. [21] | * Hash functions * Fuzzy extractor * FourQ * Symmetric key primitives | * Proposed authentication scheme using FourQ and BPV pre-computation technologies * Require high computation and communication overheads * Cannot provide user anonymity |
| Akram et al. [4] | * Hash functions * Fuzzy extractor * Symmetric key primitives | * Provide privacy of location information to remote users and drones * Vulnerable to drone impersonation, stolen verifier, and DoS attacks, and have correctness problem |
| Notation | Description |
|---|---|
| Identity of the user and drone | |
| Pseudonym of the control center, user and drone | |
| Biometric of the user | |
| Master private key of the user and drone | |
| Secret keys of the control center | |
| Fuzzy biometric reproduction | |
| Fuzzy biometric generator | |
| Random numbers | |
| Session key | |
| Hash function | |
| Concatenation operator | |
| ⊕ | Exclusive-OR operator |
| Notation | Description |
|---|---|
| Principals | |
| Statements | |
| Session key | |
| believes | |
| once said | |
| controls | |
| receives | |
| is fresh | |
| is encrypted with | |
| and have shared key |
| SFF | [14] | [17] | [18] | [21] | [24] | [4] | Proposed |
|---|---|---|---|---|---|---|---|
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | × | ✓ | ✓ | |
| × | × | × | × | × | × | ✓ | |
| × | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | × | × | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| × | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | × | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | × | ✓ | |
| ✓ | ✓ | ✓ | ✓ | ✓ | × | ✓ |
| Schemes | Total Costs | Number of Messages |
|---|---|---|
| Ali et al. [14] | 1696 bits | 3 messages |
| Wu et al. [17] | 3360 bits | 3 messages |
| Tanveer et al. [18] | 2240 bits | 3 messages |
| Zhang et al. [21] | 5760 bits | 4 messages |
| Tanveer et al. [24] | 1856 bits | 3 messages |
| Akram et al. [4] | 2304 bits | 3 messages |
| Proposed | 2560 bits | 3 messages |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2023 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Park, Y.; Ryu, D.; Kwon, D.; Park, Y. Provably Secure Mutual Authentication and Key Agreement Scheme Using PUF in Internet of Drones Deployments. Sensors 2023, 23, 2034. https://doi.org/10.3390/s23042034
Park Y, Ryu D, Kwon D, Park Y. Provably Secure Mutual Authentication and Key Agreement Scheme Using PUF in Internet of Drones Deployments. Sensors. 2023; 23(4):2034. https://doi.org/10.3390/s23042034
Chicago/Turabian StylePark, Yohan, Daeun Ryu, Deokkyu Kwon, and Youngho Park. 2023. "Provably Secure Mutual Authentication and Key Agreement Scheme Using PUF in Internet of Drones Deployments" Sensors 23, no. 4: 2034. https://doi.org/10.3390/s23042034
APA StylePark, Y., Ryu, D., Kwon, D., & Park, Y. (2023). Provably Secure Mutual Authentication and Key Agreement Scheme Using PUF in Internet of Drones Deployments. Sensors, 23(4), 2034. https://doi.org/10.3390/s23042034