An Image Encryption Algorithm Based on Time-Delay and Random Insertion
Abstract
1. Introduction
2. The Proposed Cryptosystem
2.1. Image Cryptosystem
2.2. Encryption Steps
- Step 1.
- Read the plain-image as P and obtain its size .
- Step 2.
- Compute the sum s over the plain-image.
- Step 3.
- Generate the two sets H and L by simulating a time-delay phenomena.
- Step 4.
- Apply circular permutation to both rows and columns, and obtain T.
- Step 5.
- Insert random numbers into the permuted image T and obtain B by simulating a one-time pad.
- Step 6.
- Iterate the chaotic map again and obtain matrix M.
- Step 7.
- Apply the diffusion operation to revise the gray distribution, on both row and column dimensions.
- Step 8.
- Obtain the cipher-image E.
2.3. Decryption
3. Experimental Results
4. Security Analyses
4.1. Key Space Analysis
4.2. Histogram Analysis
4.3. Information Entropy Analysis
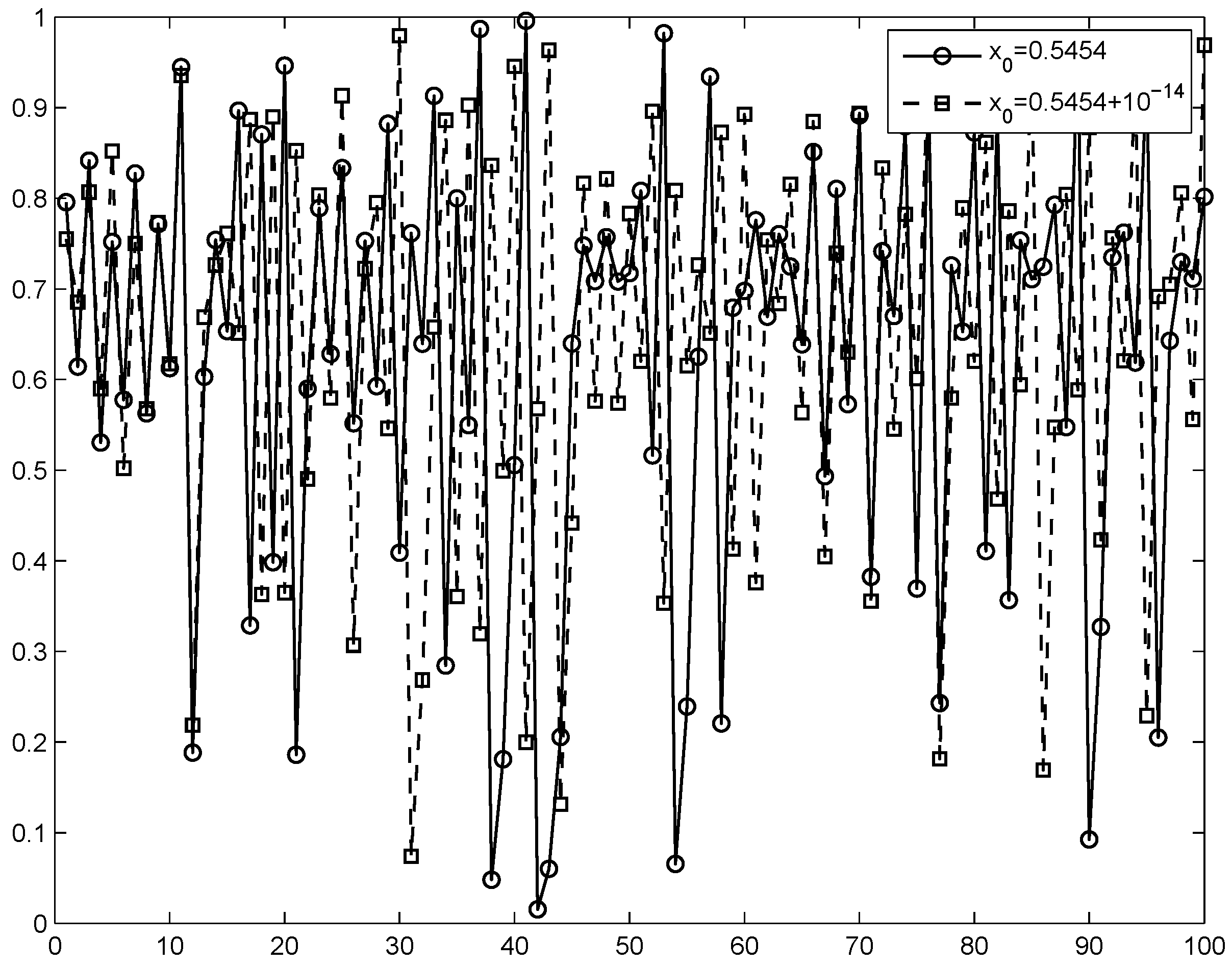
4.4. Key Sensitivity Analysis
4.5. Differential Analysis
4.6. Run Test for Randomness
4.7. Comparisons
5. Discussion and Conclusions
- (1)
- High sensitivity to keys and the plain-image.
- (2)
- Time-delay phenomenon is simulated according to outputs of the chaotic map.
- (3)
- One-time pad is designed by inserting random numbers before diffusion.
- (4)
- The keystream used in the diffusion stage is affected by keys assigned in the permutation stage.
- (5)
- Faster speed to implement the encryption.
Author Contributions
Acknowledgments
Conflicts of Interest
References
- Wu, X.J.; Wang, K.S.; Wang, X.Y.; Kan, H.B. Lossless chaotic color image cryptosystem based on DNA encryption and entropy. Nonlinear Dyn. 2017, 90, 855–875. [Google Scholar] [CrossRef]
- Huang, X.L.; Ye, G.D. An efficient self-adaptive model for chaotic image encryption algorithm. Commun. Nonlinear Sci. 2014, 19, 4094–4104. [Google Scholar] [CrossRef]
- Fridrich, J. Symmetric ciphers based on two-dimensional chaotic maps. Int. J. Bifurc. Chaos 1998, 8, 1259–1284. [Google Scholar] [CrossRef]
- Xu, L.; Li, Z.; Li, J.; Hua, W. A novel bit-level image encryption algorithm based on chaotic maps. Opt. Laser Eng. 2016, 78, 17–25. [Google Scholar] [CrossRef]
- Seyedzadeh, S.M.; Norouzi, B.; Mosavi, M.R.; Mirzakuchaki, S. A novel color image encryption algorithm based on spatial permutation and quantum chaotic map. Nonlinear Dyn. 2015, 81, 511–529. [Google Scholar] [CrossRef]
- Norouzi, B.; Seyedzadeh, S.M.; Mirzakuchaki, S.; Mosavi, M.R. A novel image encryption based on hash function with only two-round diffusion process. Multimed. Syst. 2014, 20, 45–64. [Google Scholar] [CrossRef]
- Norouzi, B.; Mirzakuchaki, S.; Seyedzadeh, S.M.; Mosavi, M.R. A simple, sensitive and secure image encryption algorithm based on hyper-chaotic system with only one round diffusion process. Multimed. Tools Appl. 2014, 71, 1469–1497. [Google Scholar] [CrossRef]
- Yang, Y.G.; Pan, Q.X.; Sun, S.J.; Xu, P. Novel image encryption based on quantum walks. Sci. Rep. 2015, 5, 7784. [Google Scholar] [CrossRef]
- Yang, Y.G.; Xu, P.; Yang, R.; Zhou, Y.H.; Shi, W.M. Quantum Hash function and its application to privacy amplification in quantum key distribution, pseudo-random number generation and image encryption. Sci. Rep. 2016, 6, 19788. [Google Scholar] [CrossRef]
- Bibi, N.; Farwa, S.; Muhammad, N.; Jahngir, A.; Usman, M. A novel encryption scheme for high-contrast image data in the Fresnelet domain. PLoS ONE 2018, 13, e0194343. [Google Scholar] [CrossRef]
- Guesmi, R.; Farah, M.A.B.; Kachouri, A.; Samet, M. A novel chaos-based image encryption using DNA sequence operation and Secure Hash Algorithm SHA-2. Nonlinear Dyn. 2016, 83, 1123–1136. [Google Scholar] [CrossRef]
- Chen, J.X.; Zhu, Z.L.; Zhang, L.B.; Zhang, Y.S.; Yang, B.Q. Exploiting self-adaptive permutation-diffusion and DNA random encoding for secure and efficient image encryption. Inf. Sci. 2016, 345, 257–270. [Google Scholar] [CrossRef]
- Huang, X.L.; Ye, G.D. An image encryption algorithm based on hyper-chaos and DNA sequence. Multimed. Tools Appl. 2014, 72, 57–70. [Google Scholar] [CrossRef]
- Shen, Q.; Liu, W.B. A novel digital image encryption algorithm based on orbit variation of phase diagram. Int. J. Bifurc. Chaos 2017, 27, 1750204. [Google Scholar] [CrossRef]
- Zhang, Y.S.; Xiao, D. Double optical image encryption using discrete Chirikov standard map and chaos-based fractional random transform. Opt. Laser Eng. 2013, 51, 472–480. [Google Scholar] [CrossRef]
- Ghebleh, M.; Kanso, A.; Noura, H. An image encryption scheme based on irregularly decimated chaotic maps. Signal Process.-Image 2014, 29, 618–627. [Google Scholar] [CrossRef]
- Hua, Z.Y.; Zhou, B.H.; Zhou, Y.C. Sine-transform-based chaotic system with FPGA implementation. IEEE Trans. Ind. Electron. 2018, 65, 2557–2566. [Google Scholar] [CrossRef]
- Hua, Z.Y.; Yi, S.; Zhou, Y.C. Medical image encryption using high-speed scrambling and pixel adaptive diffusion. Signal Process. 2018, 144, 134–144. [Google Scholar] [CrossRef]
- Karawia, A.A. Encryption algorithm of multiple-image using mixed image elements and two dimensional chaotic economic map. Entropy 2018, 20, 801. [Google Scholar] [CrossRef]
- Abdallah, E.E.; Hamza, A.B.; Bhattacharya, P. Video watermarking using wavelet transform and tensor algebra. Signal Image Video Process. 2010, 4, 233–245. [Google Scholar] [CrossRef]
- Abdallah, E.E.; Hamza, A.B.; Bhattacharya, P. MPEG video watermarking using tensor singular value decomposition. In Proceedings of the 2007 International Conference Image Analysis and Recognition, Montreal, QC, Canada, 22–24 August 2007; pp. 772–783. [Google Scholar]
- Li, S.L.; Ding, W.K.; Yin, B.S.; Zhang, T.F.; Ma, Y.D. A novel delay linear coupling logistics map model for color image encryption. Entropy 2018, 20, 463. [Google Scholar] [CrossRef]
- Li, C.Q. Cracking a hierarchical chaotic image encryption algorithm based on permutation. Signal Process 2016, 118, 203–210. [Google Scholar] [CrossRef]
- Yeo, J.C.; Guo, J.I. Efficient hierarchical chaotic image encryption algorithm and its VLSI realization. IEE Proc.-Vis. Image Signal Process. 2000, 147, 167–175. [Google Scholar]
- Jolfaei, A.; Wu, X.W.; Muthukkumarasamy, V. On the security of permutation-only image encryption schemes. IEEE Trans. Inf. Forensics Sec. 2016, 11, 235–246. [Google Scholar] [CrossRef]
- Li, C.Q.; Lin, D.D.; Lü, J.H. Cryptanalyzing an image-scrambling encryption algorithm of pixel bits. IEEE Multimed. 2017, 24, 64–71. [Google Scholar] [CrossRef]
- Eslami, Z.; Bakhshandeh, A. An improvement over an image encryption method based on total shuffling. Opt. Commun. 2013, 286, 51–55. [Google Scholar] [CrossRef]
- Akhavan, A.; Samsudin, A.; Akhshani, A. Cryptanalysis of “an improvement over an image encryption method based on total shuffling”. Opt. Commun. 2015, 350, 77–82. [Google Scholar] [CrossRef]
- Hermassi, H.; Belazi, A.; Rhouma, R.; Belghith, S.M. Security analysis of an image encryption algorithm based on a DNA addition combining with chaotic maps. Multimed. Tools Appl. 2014, 72, 2211–2224. [Google Scholar] [CrossRef]
- Liu, Y.S.; Tang, J.; Xie, T. Cryptanalyzing a RGB image encryption algorithm based on DNA encoding and chaos map. Opt. Laser Technol. 2014, 60, 111–115. [Google Scholar] [CrossRef]
- Zhu, C.X.; Sun, K.H. Cryptanalyzing and improving a novel color image encryption algorithm using RT-enhanced chaotic tent maps. IEEE Access 2018, 6, 18759–18770. [Google Scholar] [CrossRef]
- Xie, E.Y.; Li, C.Q.; Yu, S.M.; Lü, J.H. On the cryptanalysis of Fridrich’s chaotic image encryption scheme. Signal Process 2017, 132, 150–154. [Google Scholar] [CrossRef]
- Solak, E.; Çokal, C.; Yildiz, O.T.; Biyikoğu, T. Cryptanalysis of Fridrich’s chaotic image encryption. Int. J. Bifurc. Chaos 2010, 20, 1405–1413. [Google Scholar] [CrossRef]
- Hua, Z.Y.; Zhou, Y.C.; Pun, C.M.; Chen, C.L.P. 2D Sine Logistic modulation map for image encryption. Inf. Sci. 2015, 297, 80–94. [Google Scholar] [CrossRef]
- Zhu, C.X. A novel image encryption scheme based on improved hyperchaotic sequences. Opt. Commun. 2012, 285, 29–37. [Google Scholar] [CrossRef]
- Hua, Z.Y.; Zhou, B.H.; Zhou, Y.C. Sine chaotification model for enhancing chaos and its hardware implementation. IEEE Trans. Ind. Electron. 2019, 66, 1273–1284. [Google Scholar] [CrossRef]
- Ye, G.D.; Huang, X.L. An efficient symmetric image encryption algorithm based on an intertwining logistic map. Neurocomputing 2017, 251, 45–53. [Google Scholar] [CrossRef]
- Liu, H.J.; Wang, X.Y. Color image encryption using spatial bit level permutation and high-dimension chaotic system. Opt. Commun. 2011, 284, 3895–3903. [Google Scholar] [CrossRef]
- Dăscălescu, A.C.; Boriga, R.E. A novel fast chaos-based algorithm for generating random permutations with high shift factor suitable for image scrambling. Nonlinear Dyn. 2013, 74, 307–318. [Google Scholar] [CrossRef]
- Kadir, A.; Hamdulla, A.; Guo, W.Q. Color image encryption using skew tent map and hyper chaotic system of 6th-order CNN. Optik 2014, 125, 1671–1675. [Google Scholar] [CrossRef]
- Stoyanov, B.; Kordov, K. Image encryption using chebyshev map and rotation equation. Entropy 2015, 17, 2117–2139. [Google Scholar] [CrossRef]
- Stoyanov, B.; Kordov, K. Novel image encryption scheme based on chebyshev polynomial and duffing map. Sci. World J. 2014, 2014, 283639. [Google Scholar] [CrossRef] [PubMed]
- Seyedzade, S.M.; Mirzakuchaki, S.; Atani, R.E. A novel image encryption algorithm based on hash function. In Proceedings of the 2010 Iranian Conference on Machine Vision and Image Processing, Isfahan, Iran, 27–28 October 2010. [Google Scholar]
- Chai, X.L.; Gan, Z.H.; Yuan, K.; Lu, Y.; Chen, Y.R. An image encryption scheme based on three-dimensional Brownian motion and chaotic system. Chin. Phys. B 2017, 26, 020504. [Google Scholar] [CrossRef]
- Ramadan, N.; Ahmed, H.H.; El-khamy, S.E.; El-Samie, F.E.A. Permutation-substitution image encryption scheme based on a modified chaotic map in transform domain. J. Cent. South Univ. 2017, 24, 2049–2057. [Google Scholar] [CrossRef]
- Huang, X.L. Image encryption algorithm using chaotic Chebyshev generator. Nonlinear Dyn. 2012, 67, 2411–2417. [Google Scholar] [CrossRef]
- Ye, G.D.; Huang, X.L. A novel block chaotic encryption scheme for remote sensing image. Multimed. Tools Appl. 2016, 75, 11433–11446. [Google Scholar] [CrossRef]
- Fouda, J.S.A.E.; Effa, J.Y.; Sabat, S.L.; Ali, M. A fast chaotic block cipher for image encryption. Commun. Nonlinear Sci. Numer. Simul. 2014, 9, 578–588. [Google Scholar] [CrossRef]




| Test Images | Plain-Image | Cipher-Image |
|---|---|---|
| Lena | 7.4532 | 7.9970 |
| Boat | 7.1238 | 7.9993 |
| Peppers | 7.5715 | 7.9992 |
| Baboon | 7.3579 | 7.9993 |
| Test Images | UACI | NPCR |
|---|---|---|
| Lena | 33.3537 | 99.6109 |
| Boat | 33.4899 | 99.5900 |
| Peppers | 33.5186 | 99.6044 |
| Baboon | 33.5280 | 99.6136 |
| Images | Lena | Peppers | Boat | Baboon |
|---|---|---|---|---|
| Results | 0 | 0 | 0 | 0 |
| Randomness | Pass | Pass | Pass | Pass |
| Channels | R | G | B | Average |
|---|---|---|---|---|
| Ref. [1] | 7.9903 | 7.9890 | 7.9893 | 7.9895 |
| Ref. [38] | 7.9871 | 7.9881 | 7.9878 | 7.9877 |
| Ref. [40] | 7.9278 | 7.9744 | 7.9705 | 7.9576 |
| Ref. [46] | 7.9969 | 7.9974 | 7.9970 | 7.9971 |
| Ref. [47] | 7.9895 | 7.9897 | 7.9893 | 7.9895 |
| Ref. [48] | 7.9968 | 7.9970 | 7.9972 | 7.9970 |
| Ours | 7.9977 | 7.9973 | 7.9975 | 7.9975 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Huang, X.; Ye, G. An Image Encryption Algorithm Based on Time-Delay and Random Insertion. Entropy 2018, 20, 974. https://doi.org/10.3390/e20120974
Huang X, Ye G. An Image Encryption Algorithm Based on Time-Delay and Random Insertion. Entropy. 2018; 20(12):974. https://doi.org/10.3390/e20120974
Chicago/Turabian StyleHuang, Xiaoling, and Guodong Ye. 2018. "An Image Encryption Algorithm Based on Time-Delay and Random Insertion" Entropy 20, no. 12: 974. https://doi.org/10.3390/e20120974
APA StyleHuang, X., & Ye, G. (2018). An Image Encryption Algorithm Based on Time-Delay and Random Insertion. Entropy, 20(12), 974. https://doi.org/10.3390/e20120974




