Blockchain and Building Information Modeling (BIM): Review and Applications in Post-Disaster Recovery
Abstract
1. Introduction
2. Problem Statement
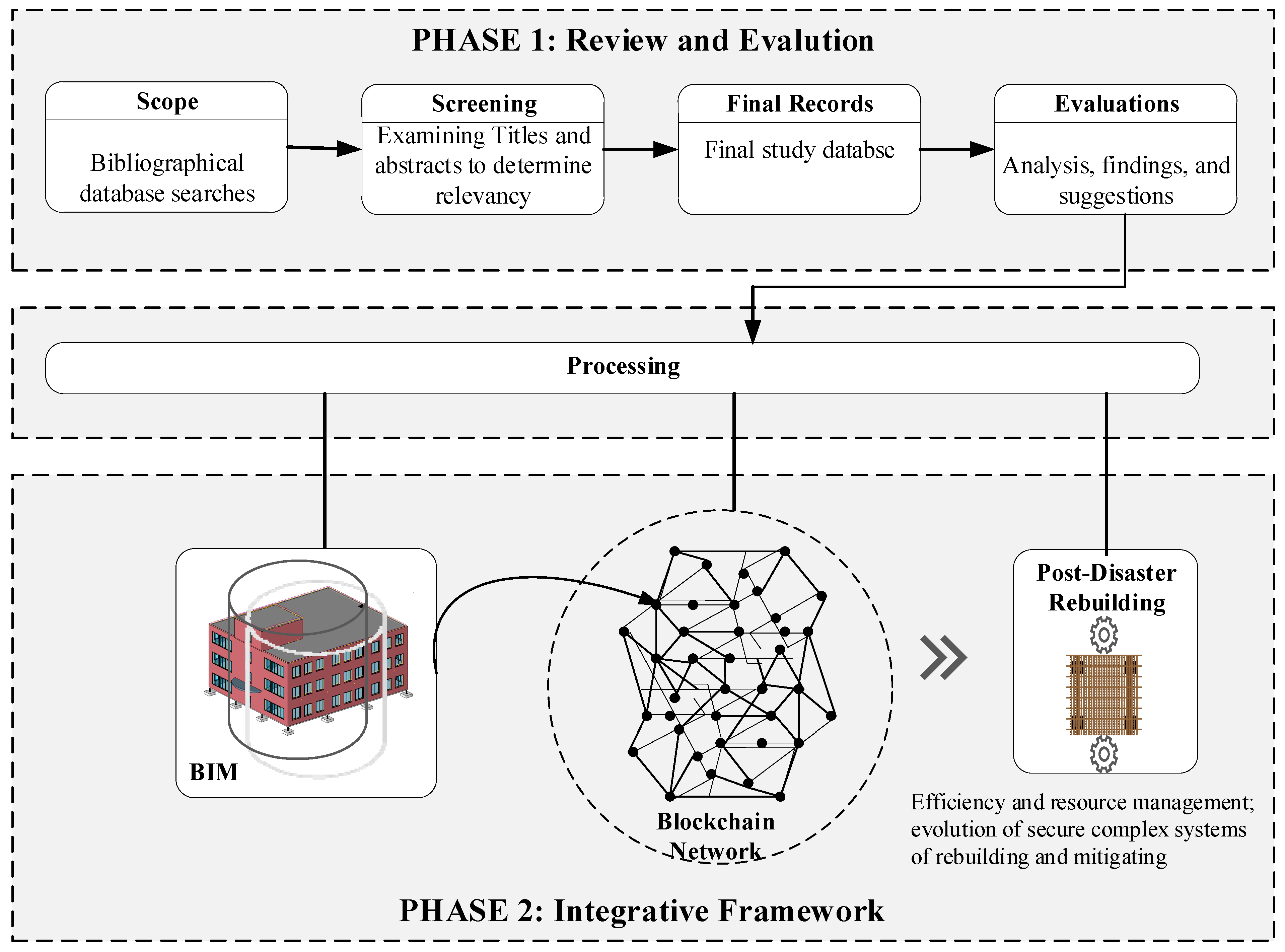
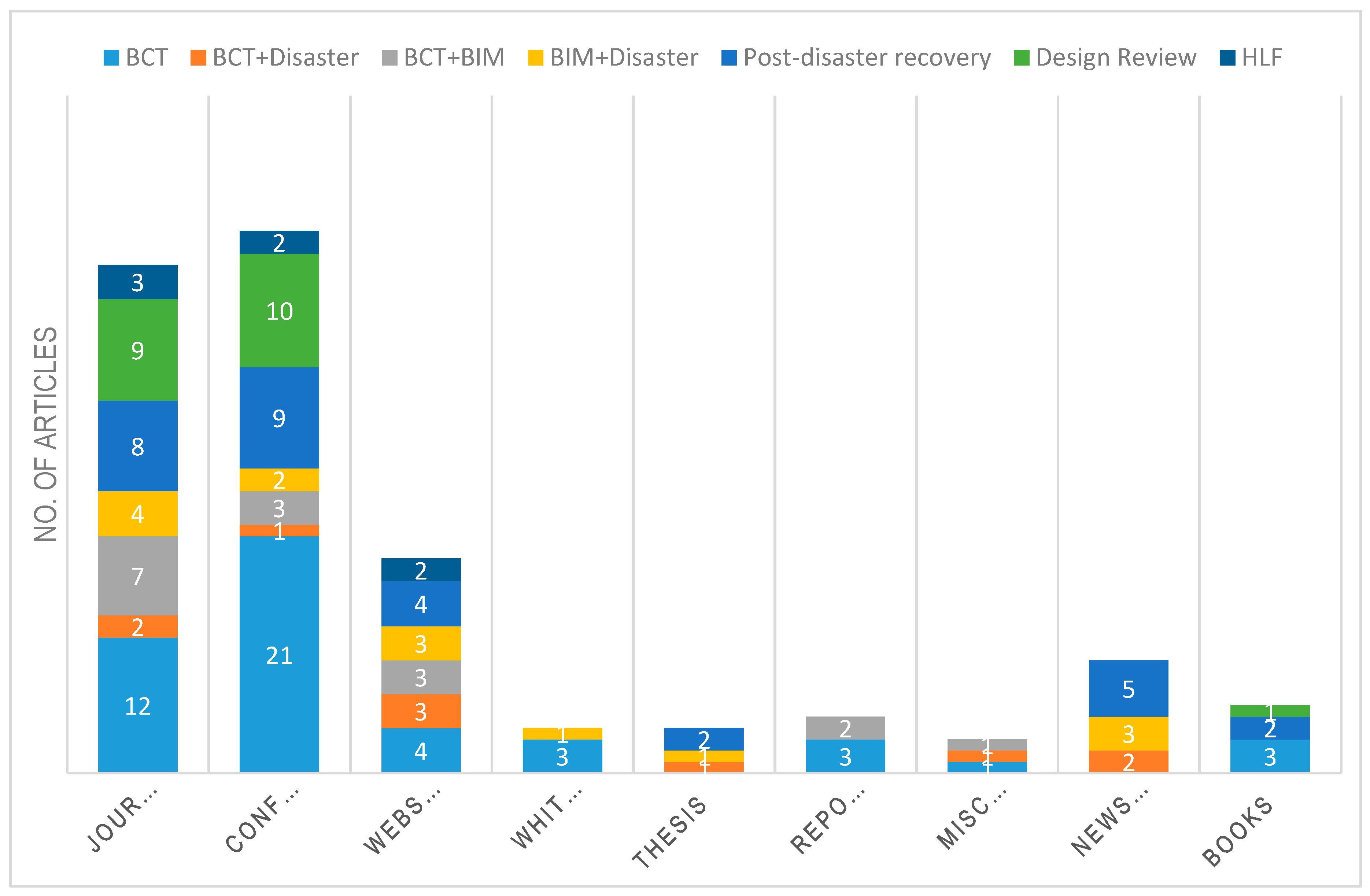
3. Methodology
4. Blockchain Technology (BCT)
4.1. BCT Basics
- Block header, consisting of the block version, a timestamp, Merkle tree root hash equivalent of the transactions, nBits, Nonce, and a parent block. A Block version indicates the set of the block validation. Timestamp displays the current universal time. Nonce is a 4 byte field that generally starts from zero, and increases by one for every hash calculation, thus acting somewhat as a transaction counter. The parent block hash is the 256 bit hash value that references the parent block, i.e., the sequentially preceding block to the one in the discussion. The first block in the chain that does not have a precursor is called the genesis block.
- Block body, which contains the actual transaction data. This is the part of the block that effectively dictates the upper limit of the possible transactions, as well as the transaction time [18].
4.2. Decentralized Systems
4.3. Trust Systems
- Proof of Work: ‘Mining’ or the Proof of Work (PoW) mechanism works by determining the node that writes a block on ledgers using a combination of game theory, cryptography, and incentive engineering [18]. The nodes in the network compete to solve a mathematical puzzle (generally a computationally difficult but easily verifiable pattern) to record a transaction. Upon resolving the puzzle, a consensus is reached by broadcasting the resolved solution to other nodes in the network, thereby ensuring transparency, robustness, and incorruptibility of the network. Consequently, the group with larger total computing power dictates the decision-making and reaching consensus. The two most popular BCT systems, Bitcoin and Ethereum, operate on a PoW mechanism. However, this involves expensive transaction fees, extensive computing tower, and cumbersome mining processes to create new blocks.
- Proof of Stake: The creator of the block is chosen in a deterministic method, depending on the stake held by the participant. An algorithm is employed to determine collective decision-making and the level of privacy between participants. This mechanism requires the credibility of data, which is denoted by proof of ownership of cryptocurrency coins. If a created block can be validated, the cryptocurrency will be returned to the original node as a bonus. This method involves no block rewards but operates solely on transaction fees. It is thus an energy-saving alternative to PoW and presents several economic benefits. Ethereum aims to shift the paradigm by transitioning to a PoS mechanism.
- Practical Byzantine Fault Tolerance (PBFT): This is a Byzantine agreement consensus method that can tolerate a maximum of 1/3 malicious byzantine replicas. A primary is selected in each round and is responsible for ordering the transaction. A node enters the next phase if it receives 2/3 of votes from the remaining nodes in the network [18]. Thus, PBFT requires each node to query other nodes. Hyperledger fabric uses the PBFT algorithm;
- Delegated Proof of Stake (DPOS): Stakeholders elect representatives to validate blocks. Since this mechanism features a relatively small number of nodes, the processing of transactions is quicker [18]. The delegates are authorized to modify the network parameters.
4.4. Mining
4.5. Privacy
- Permissioned blockchains: Permissioned Blockchains restrict the actors that can contribute to the consensus of the system state. Only a restricted set of users have the rights to validate transactions and may also restrict access to approved actors who can create smart contracts. HLF is an example of this permission type.
- Permission-less or public blockchains: Blockchain networks that are permission-less allow any participant to create consensus, as well as smart contracts, and uses the PoW mechanism to reach a consensus. They typically use a native cryptocurrency or none to validate transactions. Bitcoin and Ethereum blockchains are good examples of this type of permission.
4.6. Smart Contracts
- Smart legal contracts: This term focuses on the expression and implementation of the software and encompasses operational aspects and issues about the composition and interpretation of the contract.
- Automation: Automation is accomplished by linking the legal prose to the smart contract code via parameters that generate instructions regarding the final operational details.
- Enforceability: The smart contract code must execute successfully, accurately, and within a reasonable timeframe. A smart legal contract must include legally enforceable obligations and rights that are expressed in complex, time-dependent, sequential, context-sensitive prose. These may also include overriding obligations based on the fulfilment of certain conditions.
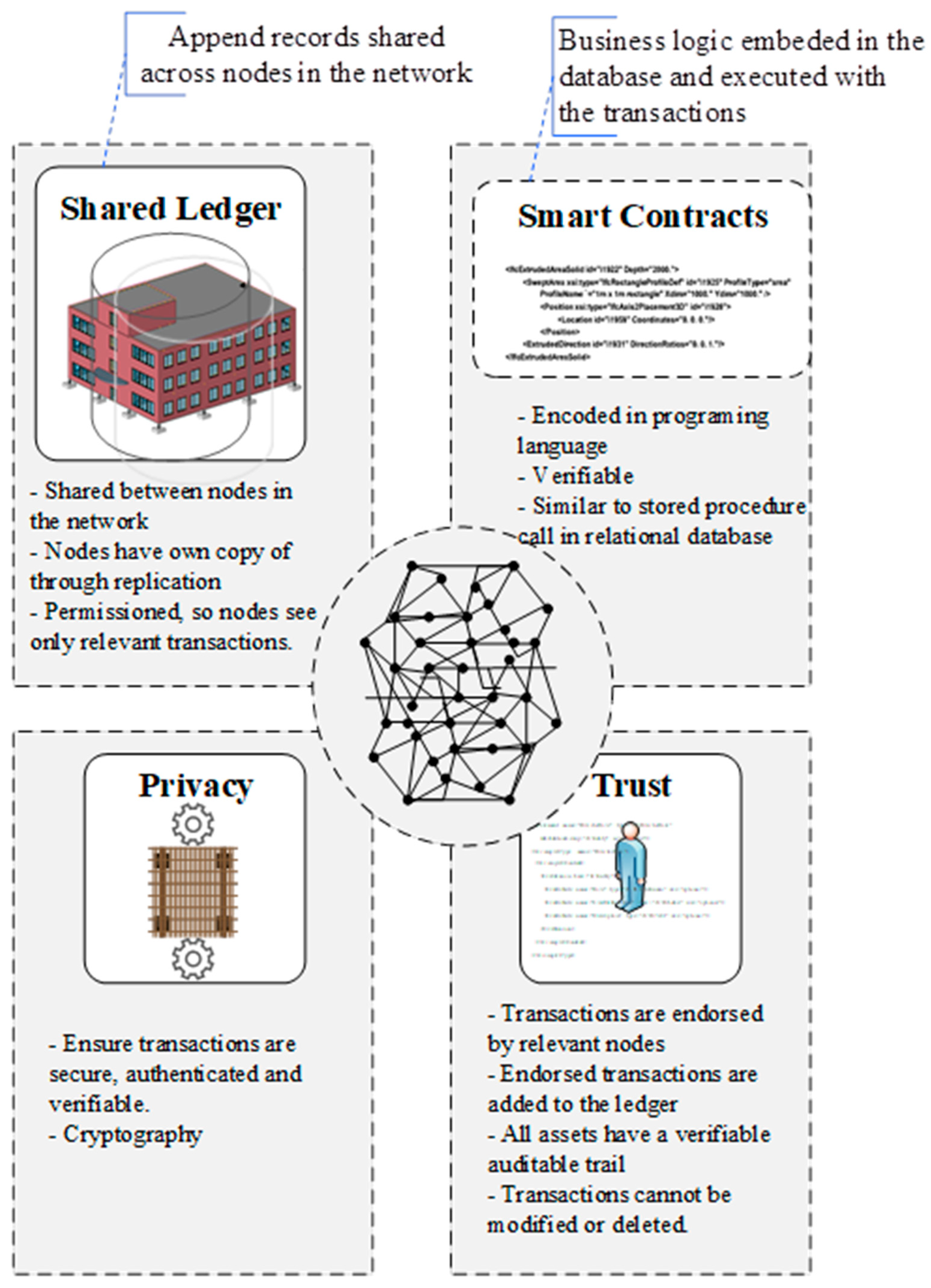
4.7. Hyperledger Fabric (HLF)
- Assets: Assets can range from physical objects (real estate and hardware) to the intangible (BIM models, contracts, and intellectual property). Hyperledger Fabric provides the ability to modify assets using chaincode transactions.
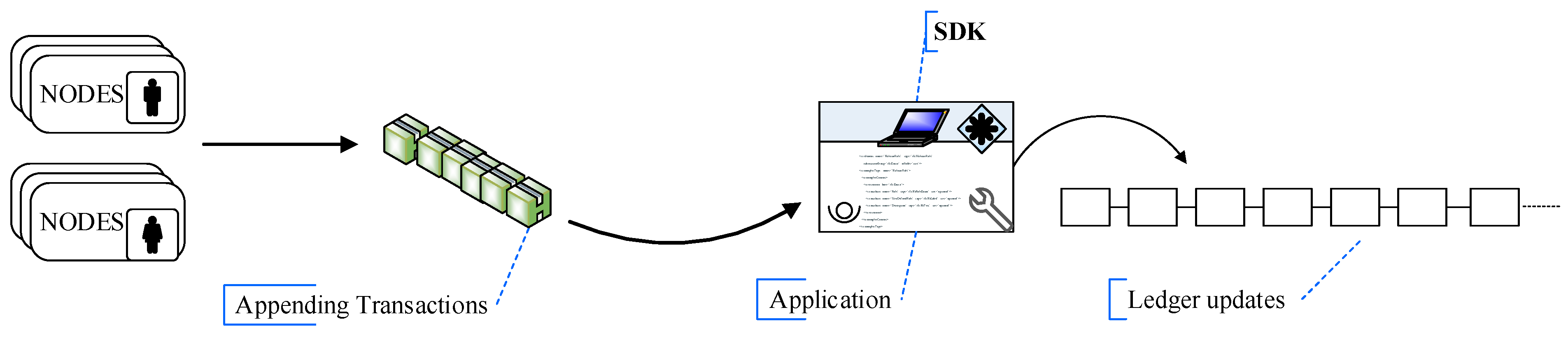
- Ledger: It is comprised of a blockchain to save the immutable, sequenced records in blocks, as well as a state database to preserve the fabric state. There is generally one ledger per channel. Each node sustains a copy of the ledger for each channel of which a node is a member. The shared ledger encodes the entire transaction history for each channel and includes SQL-like query capabilities for efficient processing.
- Privacy: Channels enable multi-lateral data exchanges with the high degrees of privacy and confidentiality required by the AEC specialized and other regulated industries that exchange data on a shared network. A ledger exists in the scope of a channel and it can be shared across the entire network (assuming every participant is operating on one common channel), or it can be constrained to only contain a specific set of participants.
- Security and Membership Services: Permissioned membership provides a trusted blockchain network, where participants know that all transactions can be detected and traced by authorized regulators and auditors.
- Consensus: It is defined as the full cycle of verification of the correctness of a set of transactions comprising a block in a distributed ledger system. HLF consensus covers the entire transaction flow, from proposal and endorsement to ordering, validation, and commitment. Hyperledger Fabric has been designed to allow a new application to select a consensus mechanism that best characterizes the relationships that exist between participants in the network.
- Smart Contracts: Hyperledger Fabric smart contracts are written in chaincode and are invoked by an application external to the BCT when that application needs to interact with the ledger. In most cases, chaincode interacts only with the database component of the ledger, the world state (querying it, for example), and not the transaction log. Chaincode can be implemented in several programming languages. The currently supported chaincode language is Go, with support for Java and other languages coming in future releases.
4.8. Limitations
4.9. Summary of BCT
5. Applications of BCT
5.1. General
5.2. BCT and the AEC Industry
5.2.1. Current Advances
5.2.2. Blockchain in Construction Management
- Building information modelling software for intelligent and collaborative 3D design and modelling;
- cloud-based technology, allowing for real-time creation and coordination of a visualized database and serving as a platform for multi-disciplinary collaboration;
- smart contracts, a set of coded instructions that can automatically execute upon the fulfillment of certain conditions;
- reality capture technology, allowing verification and conversion of digital assets into real value;
- managing the Internet of Things (IoT);
- functionally permissioned blockchains that facilitate consensus-based collaboration.
5.3. BCT Applications in Disaster Relief
6. Blockchain and BIM
- an insufficient toolset or methods that can efficiently comment or mark upon Requests For Information (RFIs) [67],
- no archive of BIM model changes and modification history,
- impracticality in the generated list of design errors [68],
- a clear generation of comparative deviation reports contrast design changes between different file versions,
- detailed open model templates [70],
- a lack of tools to map complex collaborative workflows and insufficient levels of interoperability [74],
- insufficient cyber-resilience of the software platform and consequent risks and liability to data theft, tampering, and other cyber-attacks,
- time-consuming re-modeling, conversions, and other repetitive tasks that could be automated during the project phases [74],
- the lack of a legal framework detailing model data ownership and legal/contractual issues [74].
6.1. Data Ownership
6.2. Cybersecurity
6.2.1. BIM workflow and Security
- External threat agents: unconnected malicious outsiders, criminal entities attempting to access data for reconnaissance, hackers, intellectual property theft, the leak of sensitive or confidential information, and malware that can attack the BIM database;
- Internal threat agents: involved participants who may bear malicious intent, the abuse of authorized access to steal, leak, or corrupt information to disrupt BIM operations, as well as human errors like omissions, ignorance, or negligence of work;
- Systems and business failures: natural causes by extreme weather, interference from animals, storage device failures, poor maintenance of the centralized IT infrastructure, bankruptcies, and business failures.
6.2.2. Advantages of using BCT for Improving Cybersecurity
6.2.3. Trust
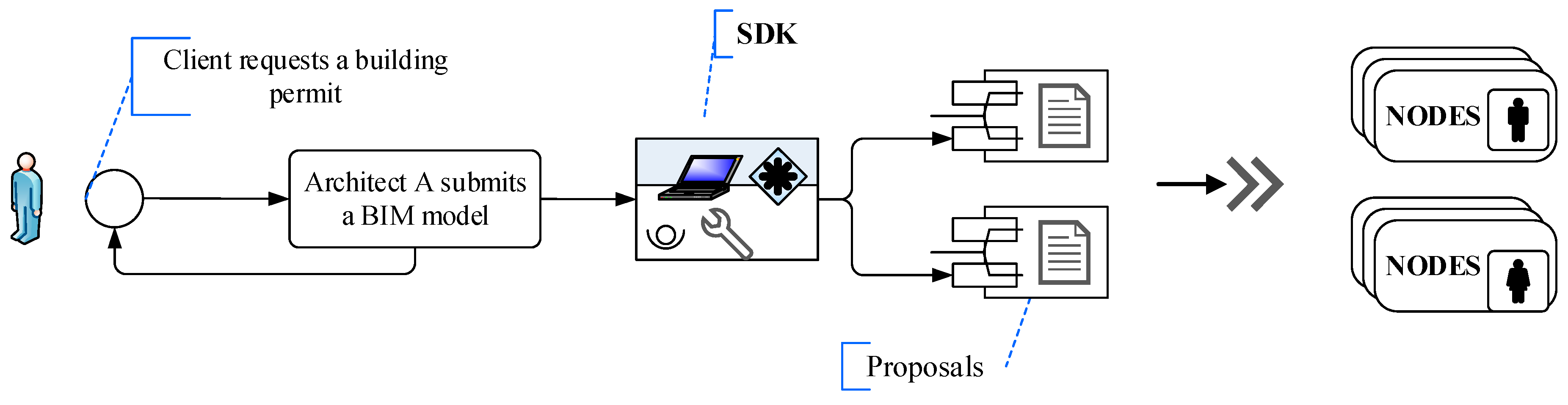
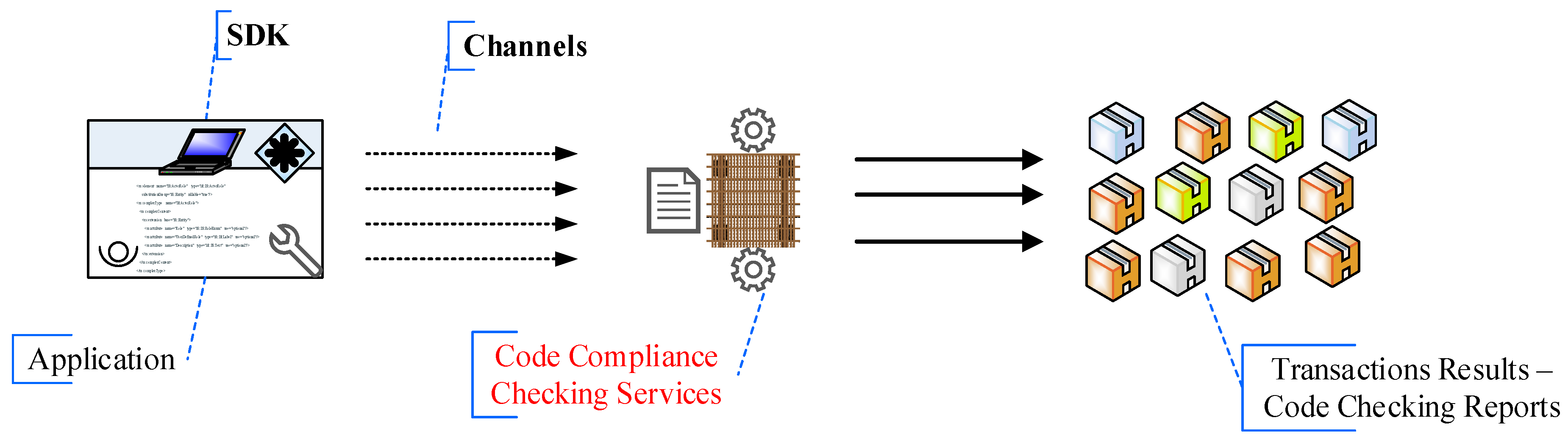
7. Automation of the Building Permit Process
7.1. Background
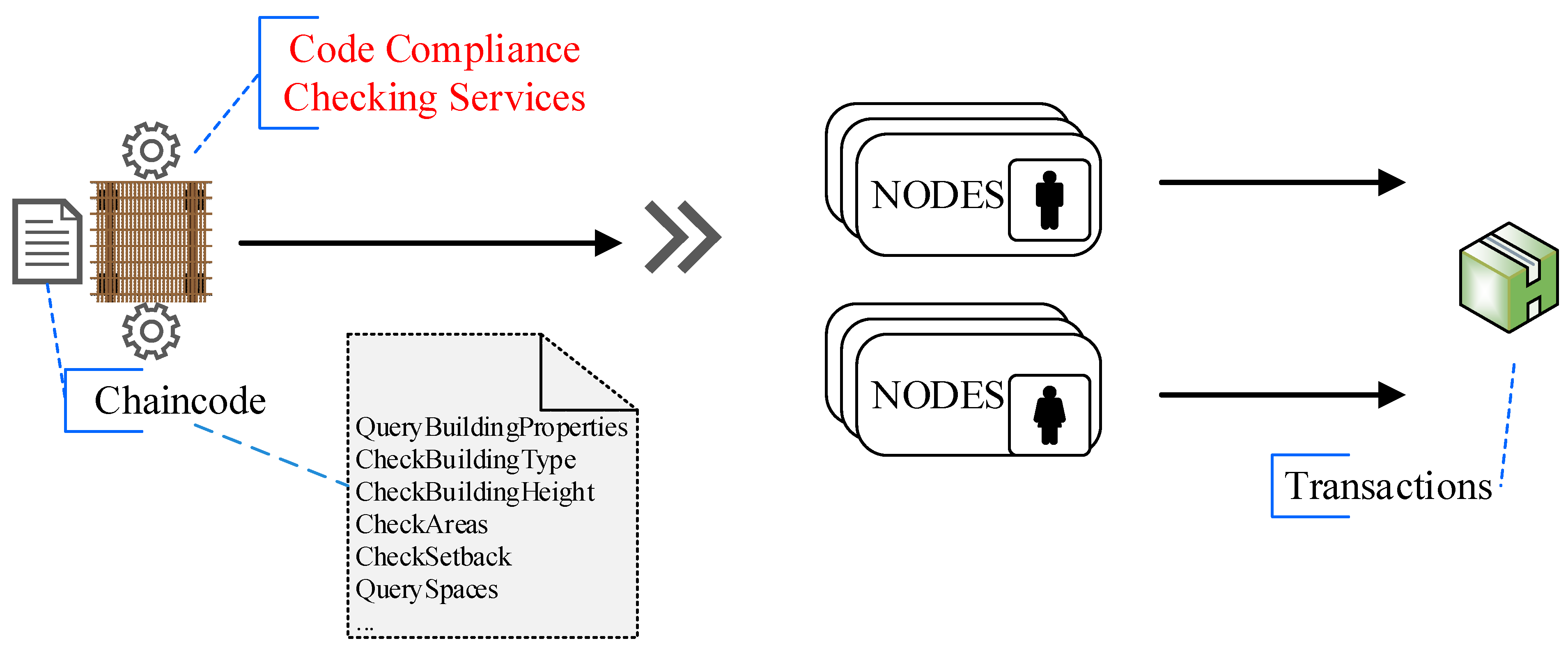
7.2. Automated Code-Checking and Compliance (ACCC) Framework
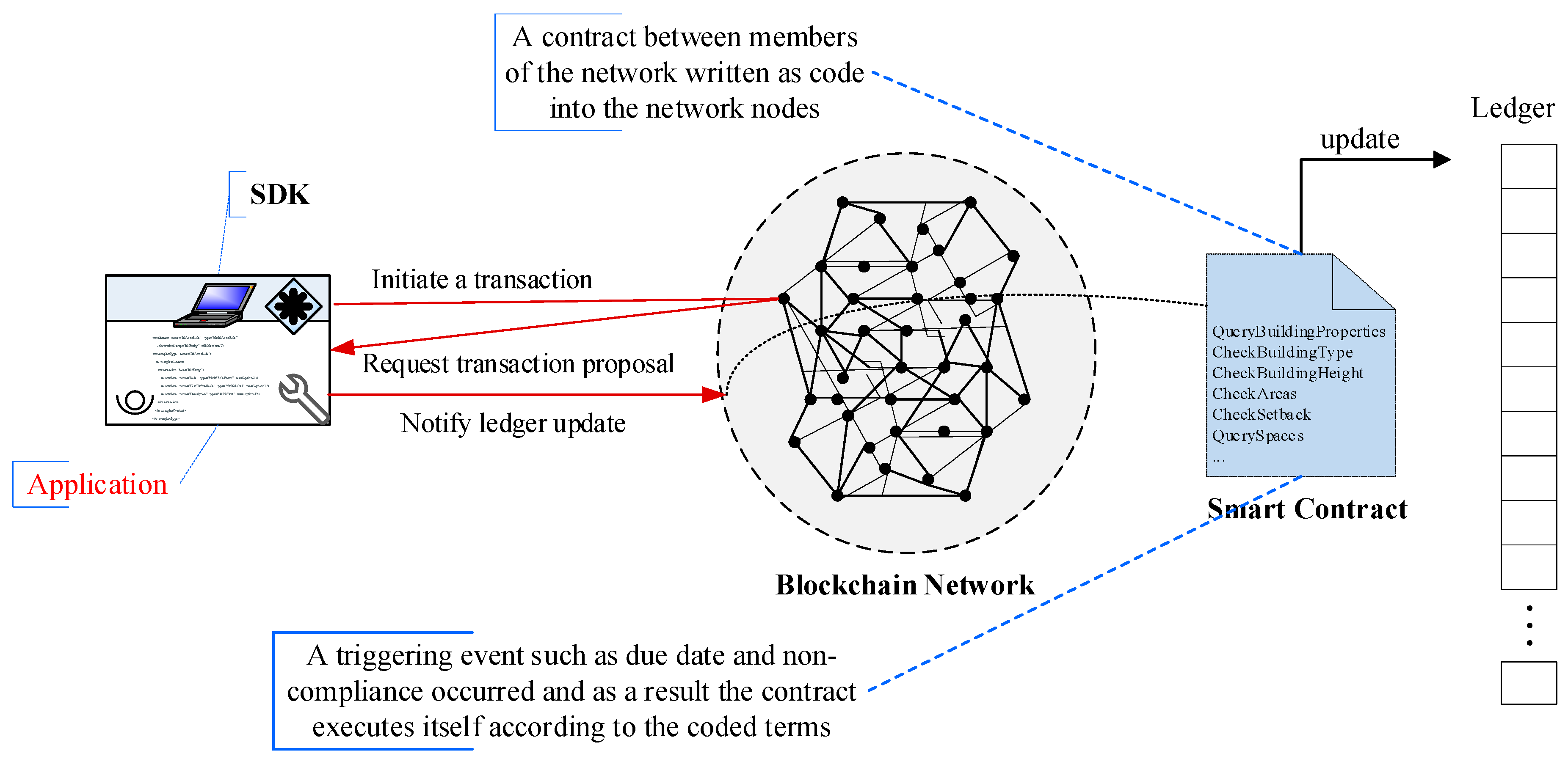
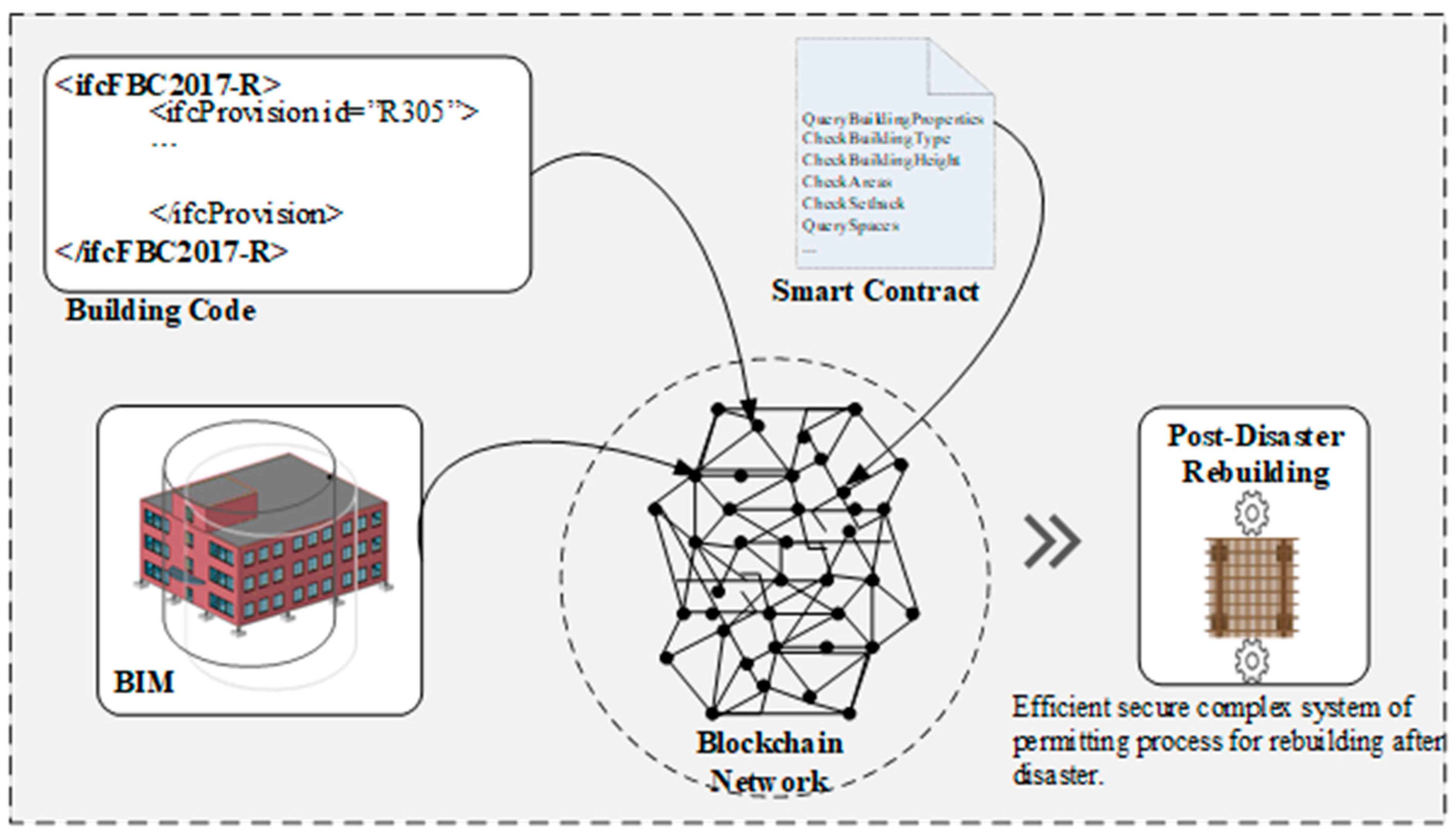
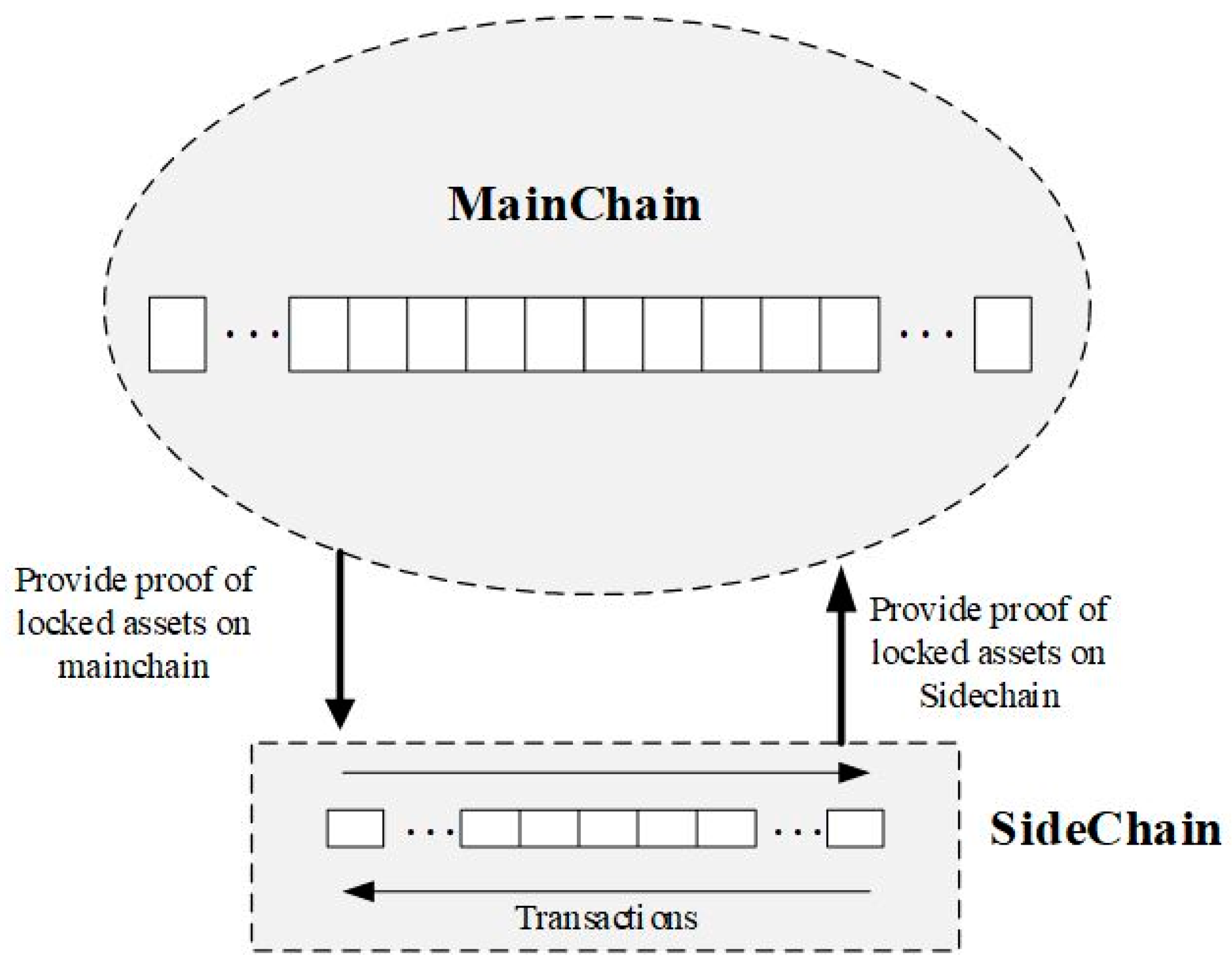
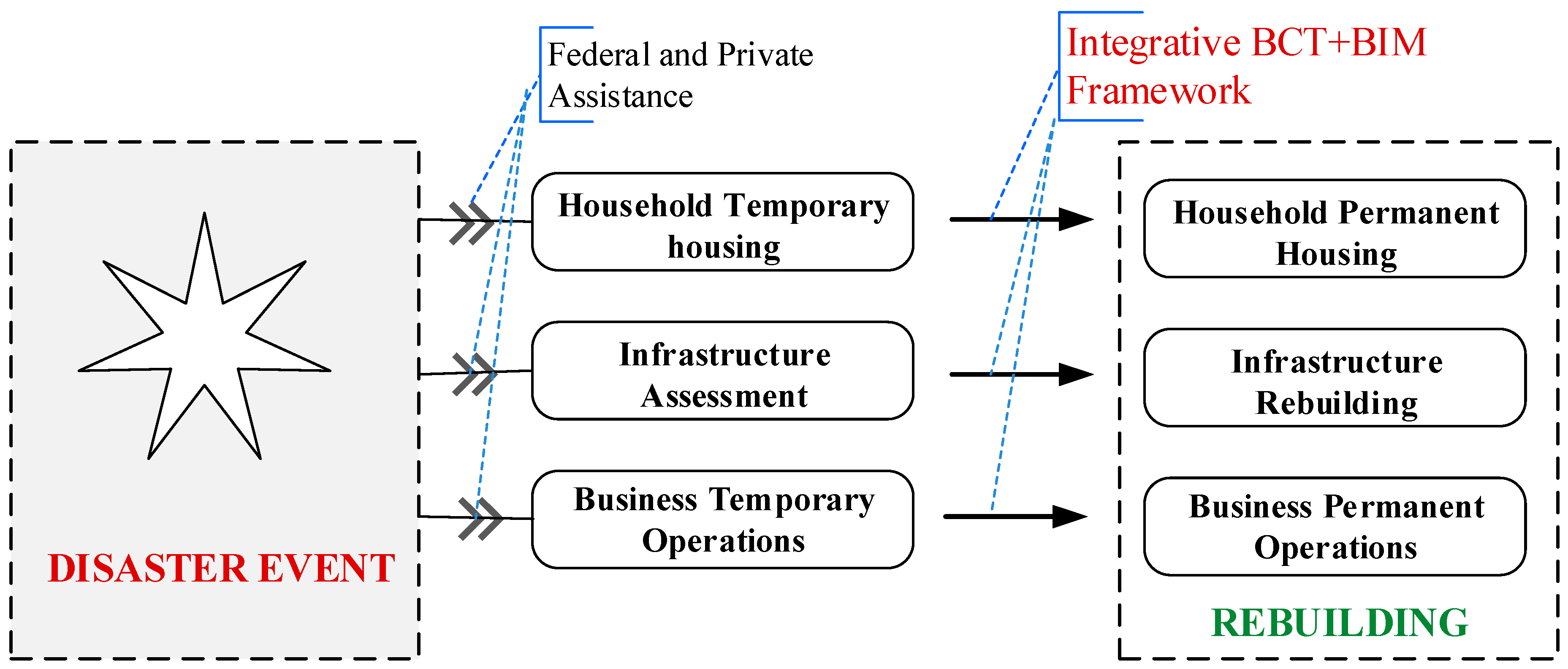
7.3. Proposed Integrative BCT+BIM Framework
- (a)
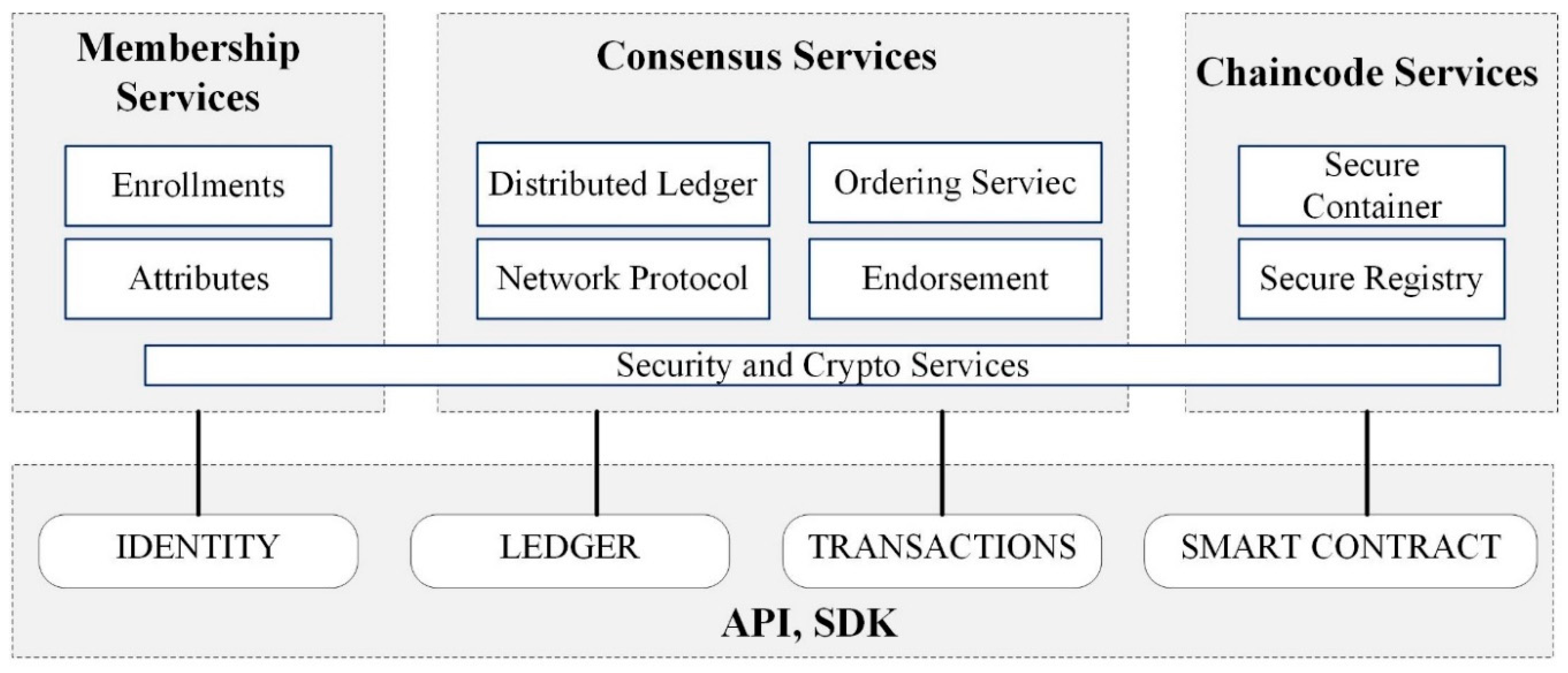
- Membership services: This module deals with permissioning and serves to create a root of trust during network formation. This module is also vital in managing the identity of members participating in the blockchain network. It provides a specialized digital certificate authority for issuing certificates to members of the blockchain network.
- (b)
- Chaincode services: A chaincode, or a smart contract, is application-level code stored on the ledger as a part of a transaction. The chaincode runs transactions that may modify the data on the ledger. Business logic is written as a chaincode (often in the Go or Java languages). A chaincode is installed on network members’ machines, which require access to the asset states to perform read and write operations. The chaincode is then instantiated on particular channels for specific peers. Ledgers are normally shareable across entire networks of peers or include only a specific set of participants. Peers can participate in multiple blockchain channels.
- (c)
- Consensus services: These services are at the heart of any blockchain application. They enable a trust system. The consensus service permits digitally signed transactions to be proposed and validated by network members. The consensus is normally pluggable and tightly linked to the endorse-order-validation model that the Hyperledger proposes. The ordering services in HLF represent the consensus system. The ordering service groups multiple transactions into blocks and outputs a hash-chained sequence of blocks containing transactions.
- (a)
- The building codes or regulations upon which the BIM model data are to be examined must be processed into a computable language. A smart contract (chaincode) can be programmed to process the rules from a natural language using GAF [81]. This contract must be defined carefully to account for all clauses, terms, and variables used in the building code and regulations. After transformation of the rules, the smart contract generates a second appended smart contract that can now be used by the model checker. If the smart contract’s capabilities do not support adequate levels of semantic enrichment, the rules can be directly expressed in the scripting languages.
- (b)
- The BIM model data are exported from the platform in IFC format (ifcXML) and accessed using the scripting language, such as Java or Go, employed by the smart contract platform. The BIM model data file is now generated and used as off-chain data.
- (c)
- A model checker is programmed in the form of another smart contract that can extract information from the BIM model data upon calling and verify that information against the translated rules created in step (a).
- (d)
- The model checker invokes the code-checking functions and creates another smart contract where the results are reported and sent to an authority to confirm the final permit.
A Case Study
8. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- NOAA National Centers for Environmental Information (NCEI). U.S. Billion-Dollar Weather and Climate Disasters. 2019. Available online: https://www.ncdc.noaa.gov/billions/ (accessed on 22 April 2019).
- Berke, P.; Newman, P.; Lee, J.; Combs, T.; Kolosna, C.; Salvesen, D. Evaluation of Networks of Plans and Vulnerability to Hazards and Climate Change: A Resilience Scorecard. J. Am. Plan. Assoc. 2015, 81, 287–302. [Google Scholar] [CrossRef]
- Olshansky, R.B.; Johnson, L.A.; Horne, J.; Nee, B. Longer View: Planning for the Rebuilding of New Orleans. J. Am. Plan. Assoc. 2008, 74, 273–287. [Google Scholar] [CrossRef]
- Garrett, T.A.; Sobel, R.S. The Political Economy of FEMA Disaster Payments. Econ. Inq. 2003, 41, 496–509. [Google Scholar] [CrossRef]
- Gunes, E.; Kovel, J.P. Using GIS in Emergency Management Operations. J. Urban Plan. Dev. 2000, 126, 136–149. [Google Scholar] [CrossRef]
- Dakhil, A.; Alshawi, M. Client’s Role in Building Disaster Management through Building Information Modelling. Procedia Econ. Financ. 2014, 18, 47–54. [Google Scholar] [CrossRef]
- Link, L.E. The anatomy of a disaster, an overview of Hurricane Katrina and New Orleans. Ocean Eng. 2010, 37, 4–12. [Google Scholar] [CrossRef]
- Guillot, C. How Blockchain Could Speed Hurricane Disaster Relief, ThirtyK. 2018. Available online: https://thirtyk.com/2018/07/31/hurricane-relief-blockchain/ (accessed on 20 April 2019).
- Muis, S.; Güneralp, B.; Jongman, B.; Aerts, J.C.J.H.; Ward, P.J. Flood risk and adaptation strategies under climate change and urban expansion: A probabilistic analysis using global data. Sci. Total Environ. 2015, 538, 445–457. [Google Scholar] [CrossRef]
- Pelling, H. Social Geography of British Elections 1885–1910; Springer: New York, NY, USA, 1967. [Google Scholar]
- Bosher, L.; Dainty, A.; Carrillo, P.; Glass, J. Built-in resilience to disasters: A pre-emptive approach. Eng. Constr. Archit. Manag. 2007, 14, 434–446. [Google Scholar] [CrossRef]
- Drogemuller, R. BIM support for disaster response. In Proceedings of the 9th Annual International Conference of the International Institute for Infrastructure Renewal and Reconstruction (8–10 July 2013); Barnes, P.H., Goonetileke, A., Eds.; Queenland University of Technology: Brisbane, Australia, 2015; pp. 391–405. [Google Scholar]
- Crosby, M.; Nachiappan, P.; Verma, S.; Kalyanaraman, V. Blockchain Technology: Beyond Bitcoin; Sutardja Center for Entrepreneurship & Technology Technical Report; University of California: Berkely, CA, USA, 2015. [Google Scholar]
- Crosby, M.; Pattanayak, P.; Verma, S.; Kalyanaraman, V. Blockchain technology: Beyond bitcoin. Appl. Innov. 2016, 2, 6–10. [Google Scholar]
- Wible, R.C. Best Practices in Electronic Plan Submittal, Review, Tracking and Storage. Alliance for Building Regulatory Reform in the Digital Age at FIATECH. 2007. Available online: http://www.natlpartnerstreamline.org/documents/WhitePaper_ElectPlan_092107.pdf (accessed on 4 May 2019).
- Wible, R.C. Federal Grants to State and Local Governments for Streamlining and Information Technology. Report Prepared by Wible & Associates, Alliance for Building Regulatory Reform in the Digital Age. 2009. Available online: http://www.natlpartnerstreamline.org/documents/GrantReportRW-IT_Streamlining_111009.pdf (accessed on 14 June 2019).
- Tama, B.A.; Kweka, B.J.; Park, Y.; Rhee, K.H. A critical review of blockchain and its current applications. In Proceedings of the ICECOS 2017, 2017 International Conference on Electrical Engineering and Computer Science: Sustaining the Cultural Heritage Toward the Smart Environment for Better Future, Palembang, Indonesia, 22–23 August 2017; pp. 109–113. [Google Scholar] [CrossRef]
- Zheng, Z.; Xie, S.; Dai, H.; Chen, X.; Wang, H. An Overview of Blockchain Technology: Architecture, Consensus, and Future Trends. In Proceedings of the 2017 IEEE 6th International Congress on Big Data, BigData Congress, Honolulu, HI, USA, 25–30 June 2017; pp. 557–564. [Google Scholar] [CrossRef]
- Brandão, A.; São Mamede, H.; Gonçalves, R. Systematic review of the literature, research on Blockchain technology as support to the trust model proposed applied to smart places. In World Conference on Information Systems and Technologies; Springer: Cham, Switzerland, 2018; pp. 1163–1174. [Google Scholar]
- Nakamoto, S. Bitcoin: A Peer-to-Peer Electronic Cash System. 2008. Available online: www.Bitcoin.Org (accessed on 5 May 2019).
- Mathews, M.; Robles, D.; Bowe, B. BIM+ Blockchain: A Solution to the Trust Problem in Collaboration? In Proceedings of the CITA BIM Gathering, Dublin, Ireland, 23–24 November 2017; p. 11. [Google Scholar]
- Turk, Ž.; Klinc, R. Potentials of Blockchain Technology for Construction Management. Procedia Eng. 2017, 196, 638–645. [Google Scholar] [CrossRef]
- Atkins, B.J.B.; Mendelson, A.D. BIM Me Up, Scotty: Navigating Risk in Digital. White Paper. 2013. Available online: https://www.theaiatrust.com/white-paper-bim-me-up-scotty-navigating-risk-in-digital-practice/ (accessed on 22 January 2019).
- Boyes, H. Cybersecurity and Cyber-Resilient Supply Chains. Technol. Innov. Manag. Rev. 2015, 5, 28–34. [Google Scholar] [CrossRef]
- Swan, M. Blockchain Temporality: Smart Contract Time Specifiability with Blocktime. In Rule Technologies. Research, Tools, and Applications, 10th International Symposium, RuleML, Stony Brook, NY, USA; Springer: Cham, Switzerland, 2016; pp. 399–404. [Google Scholar]
- Andersen, M.P.; Kolb, J.; Chen, K.; Fierro, G.; Culler, D.E.; Katz, R. Democratizing authority in the built environment. In Proceedings of the 4th ACM International Conference on Systems for Energy-Efficient Built Environments—BuildSys ’17, Delft, The Netherlands, 8–9 November 2017; pp. 1–10. [Google Scholar]
- Wang, J.; Wu, P.; Wang, X.; Shou, W. The outlook of blockchain technology for construction engineering management. Front. Eng. Manag. 2017, 4, 65–67. [Google Scholar] [CrossRef]
- Cong, L.W.; He, Z. Blockchain Disruption and Smart Contracts. Rev. Financ. Stud. 2019, 32, 1754–1797. [Google Scholar] [CrossRef]
- Coyne, R.; Onabolu, T. Blockchain for architects: Challenges from the sharing economy. Archit. Res. Q. 2017, 21, 369–374. [Google Scholar] [CrossRef]
- Puthal, D.; Malik, N.; Mohanty, S.P.; Kougianos, E.; Yang, C. The Blockchain as a Decentralized Security Framework [Future Directions]. IEEE Consum. Electron. Mag. 2018, 7, 18–21. [Google Scholar] [CrossRef]
- Li, J.; Greenwood, D.J.; Kassem, M. Blockchain in the built environment: Analysing current applications and developing an emergent framework. In Proceedings of the Creative Construction Conference, Ljubljana, Slovenia, 30 June–3 July 2018; pp. 1–10. [Google Scholar] [CrossRef]
- Feig, E. A Framework for Blockchain-Based Applications. arXiv 2018, arXiv:1803.00892v1. [Google Scholar]
- Hasan, H.R.; Salah, K.; Member, S. Blockchain-based Proof of Delivery of Physical Assets with Single and Multiple Transporters. IEEE Access 2018, 6, 46781–46793. [Google Scholar] [CrossRef]
- Mahamadu, A.M.; Mahdjoubi, L.; Booth, C. Challenges to bim-cloud integration: Implication of security issues on secure collaboration. In Proceedings of the International Conference on Cloud Computing Technology and Science, CloudCom, Bristol, UK, 2–5 December 2013; Volume 2, pp. 209–214. [Google Scholar] [CrossRef]
- Mason, J. Intelligent Contracts and the Construction Industry. J. Leg. Aff. Disput. Resolut. Eng. Constr. 2017, 9, 04517012. [Google Scholar] [CrossRef]
- Mason, J.; Escott, H. Smart Contracts in Construction: Views and Perceptions of Stakeholders. In Proceedings of the FIG Conference, Istanbul, Turkey, May 2018; Available online: http://eprints.uwe.ac.uk/35123/ (accessed on 10 April 2019).
- Hammi, A.; Bouras, A. Towards Safe-Bim Curricula Based on the Integration of Cybersecurity and Blockchains Features. In Proceedings of the INTED, Valencia, Spain, 5–7 March 2018; pp. 2380–2388. [Google Scholar]
- Glaser, F. Pervasive Decentralisation of Digital Infrastructures: A Framework for Blockchain enabled System and Use Case Analysis. In Proceedings of the HICSS 2017 Proceedings, Waikoloa Village, HI, USA, 4–7 January 2017; pp. 1543–1552. [Google Scholar] [CrossRef]
- Buterin, V. On public and private blockchains; Ethereum blog. Available online: https://blog.ethereum.org/2015/08/07/on-public-and-private-blockchains (accessed on 14 June 2019).
- Christidis, K.; Devetsikiotis, M. Blockchains and Smart Contracts for the Internet of Things. IEEE Access. 2016, 4, 2169–3536. [Google Scholar] [CrossRef]
- Wood, D.G. Blockchains: What and Why. 2016. Available online: https://www.slideshare.net/gavofyork/blockchain-what-and-why (accessed on 11 April 2019).
- Wang, Y.; Han, J.H.; Beynon-Davies, P. Understanding blockchain technology for future supply chains: A systematic literature review and research agenda. Supply Chain Manag. Int. J. 2019, 24, 62–84. [Google Scholar] [CrossRef]
- Brakeville, S.; Perepa, B. Blockchain Basics: Introduction to Business Ledgers Get to Know This Game-Changing Technology and IBM’s Contribution to It. 2016. Available online: https://scooblr.com/assets/uploads/2016/08/cl-blockchain-basics-intro-bluemix-trs-pdf.pdf (accessed on 22 April 2019).
- Xu, X.; Pautasso, C.; Zhu, L.; Gramoli, V.; Ponomarev, A.; Tran, A.B.; Chen, S. The Blockchain as a Software Connector. In Proceedings of the 2016 13th Working IEEE/IFIP Conference on Software Architecture (WICSA), Venice, Italy, 5–8 April 2016; pp. 182–191. [Google Scholar] [CrossRef]
- Clack, C.D.; Bakshi, V.A.; Braine, L. Smart Contract Templates: Essential requirements and design options. arXiv 2016, arXiv:1612.04496. [Google Scholar]
- Clack, C.D.; Bakshi, V.A.; Braine, L. Smart Contract Templates: Foundations, design landscape and research directions. arXiv 2016, arXiv:1608.00771. [Google Scholar]
- Frantz, C.K.; Nowostawski, M. From Institutions to Code: Towards Automated Generation of Smart Contracts. In Proceedings of the 2016 IEEE 1st International Workshops on Foundations and Applications of Self* Systems (FAS* W), Augsburg, Germany, 12–16 September 2016. [Google Scholar] [CrossRef]
- Seijas, P.L.; Thompson, S.; McAdams, D. Scripting smart contracts for distributed ledger technology. IACR Cryptol. ePrint Arch. 2016, 1156. [Google Scholar]
- Bhargavan, K.; Delignat-Lavaud, A.; Fournet, C.; Gollamudi, A.; Gonthier, G.; Kobeissi, N.; Kulatova, N.; Rastogi, A.; Sibut-Pinote, T.; Swamy, N.; et al. Formal Verification of Smart Contracts. In Proceedings of the 2016 ACM Workshop on Programming Languages and Analysis for Security—PLAS’16, Vienna, Austria, 24 October 2016; pp. 91–96. [Google Scholar] [CrossRef]
- Dhawan, M. Analyzing Safety of Smart Contracts. In Proceedings of the Conference: Network and Distributed System Security Symposium, San Diego, CA, USA, 16–17 February 2017. [Google Scholar] [CrossRef]
- Hyperledger. Hyperledger-Fabric Docs Master Documentation. 2017. Available online: https://hyperledger-fabric.readthedocs.io/en/release-1.1/key_concepts.html (accessed on 10 March 2018).
- Androulaki, E.; Barger, A.; Bortnikov, V.; Cachin, C.; Christidis, K.; De Caro, A.; Enyeart, D.; Ferris, C.; Ferris, C.; Manevich, Y.; et al. Hyperledger Fabric: A Distributed Operating System for Permissioned Blockchains. In Proceedings of the Thirteenth EuroSys Conference on—EuroSys ’18, Porto, Portugal, 23–26 April 2018; pp. 1–15. [Google Scholar] [CrossRef]
- Liang, X.; Zhao, J.; Shetty, S.; Liu, J.; Li, D. Integrating blockchain for data sharing and collaboration in mobile healthcare applications. In Proceedings of the 2017 IEEE 28th Annual International Symposium on Personal, Indoor, and Mobile Radio Communications (PIMRC), Montreal, QC, Canada, 8–13 October 2017; pp. 1–5. [Google Scholar] [CrossRef]
- Bartoletti, M.; Pompianu, L. An Empirical analysis of smart contracts: Platforms, applications, and design patterns. In Lecture Notes in Computer Science (including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); 10323 LNCS; Springer: Cham, Switzerland, 2017; pp. 494–509. [Google Scholar]
- Kshetri, N. Blockchain’s roles in strengthening cybersecurity and protecting privacy. Telecommun. Policy 2017, 41, 1027–1038. [Google Scholar] [CrossRef]
- ACT-IAC. Enabling Blockchain Innovation in the U.S. Federal Government. 2017. Available online: https://www.actiac.org/system/files/ACT-IAC ENABLING BLOCKCHAIN INNOVATION_3.pdf (accessed on 10 May 2019).
- Belle, I. The architecture, engineering and construction industry and blockchain technology. In Proceedings of the 2017 National Conference on Digital Technologies in Architectural Education and DADA 2017 International Conference on Digital Architecture; China Architecture Industry Publishers: Nanjing, China, 2018; pp. 279–284. [Google Scholar]
- Sherif, A.; Jinkook, L.; Chuck, E. Automated Cost Analysis of Concept Design BIM Models. In Designing Together: Proceedings of the 14th International Conference on Computer Aided Architectural Design; Les Éditions de l’Université de Liège: Liège, Belgium, 2011; pp. 403–418. [Google Scholar]
- Mannakkara, S.; Wilkinson, S. Post-Disaster Legislation for Building Back Better. Constr. Law J. 2013, 29, 495–506. [Google Scholar]
- Smith, G.; Sandler, D. State Disaster Recovery Guide; Department of Homeland Security Coastal Hazards Center of Excellence: Chapel Hill, NC, USA, 2012. [Google Scholar]
- Rohr, J. Blockchain for Disaster Relief: Creating Trust Where It Matters Most. Available online: https://www.digitalistmag.com/improving-lives/2017/11/23/blockchain-for-disaster-relief-creating-trust-where-it-matters-most-05527536 (accessed on 24 June 2019).
- Zambrano, R.; Young, A.; Verhulst, S. BLOCKCHANGE CASE STUDY: Connecting Refugees to Aid through Blockchain-Enabled ID Management: World Food Programme’s Building Blocks. 2018. Available online: https://blockchan.ge/blockchange-resource-provision.pdf (accessed on 14 June 2019).
- Panesir, M.S. Blockchain Applications for Disaster Management and National Security. Master Thesis, Faculty of the Graduate School of the University at Buffalo, State University of New York, Buffalo, NY, USA, 2018. [Google Scholar]
- Azhar, S. Building Information Modeling (BIM): Trends, Benefits, Risks, and Challenges for the AEC Industry. ASCE Lead. Manage. Eng. 2011, 11, 241–252. [Google Scholar] [CrossRef]
- Cannistrato, M.P. Savings Through Collaboration: A case study on the value of BIM. J. Build. Inf. Model. Fall 2010, 29–30. [Google Scholar]
- Bryde, D.; Broquetas, M.; Volm, J.M. The project benefits of building information modelling (BIM). Int. J. Proj. Manag. 2013, 31, 971–980. [Google Scholar] [CrossRef]
- Shourangiz, E.; Mohamad, M.I.; Hassanabadi, M.S.; Banihashemi, S.S.; Bakhtiari, M.; Torabi, M. Flexibility of BIM towards Design Change. In Proceedings of the 2nd International Conference on Construction and Project Management, Singapore, 16–18 September 2011; Volume 15, pp. 79–83. [Google Scholar]
- Kerosuo, H.; Miettinen, R.; Paavola, S.; Mäki, T.; Korpela, J. Challenges of the expansive use of Building Information Modeling (BIM) in construction projects. Production 2015, 25, 289–297. [Google Scholar] [CrossRef]
- Miettinen, R.; Paavola, S. Beyond the BIM utopia: Approaches to the development and implementation of building information modeling. Autom. Constr. 2014, 43, 84–91. [Google Scholar] [CrossRef]
- Cerovsek, T. A review and outlook for a “Building Information Model” (BIM): A multi-standpoint framework for technological development. Adv. Eng. Inform. 2011, 25, 224–244. [Google Scholar] [CrossRef]
- Nawari, N.O. BIM Standard in Off-Site Construction. J. Archit. Eng. 2012, 18, 107–113. [Google Scholar] [CrossRef]
- Nawari, N.O. BIM standards: Advancement and industry deployment. In Proceedings of the 14th International Conference on Computing in Civil and Building, Engineering, Moscow State University of Civil Engineering, Moscow, Russia, 27–29 June 2012. [Google Scholar]
- Nawari, N.O.; Alsaffar, A. Advancing BIM Standardization: Floating Structures. In Proceedings of the International Conference on Civil and Building Engineering Informatics (ICCBEI 2015), Tokyo, Japan, 22–24 April 2015; p. 78. [Google Scholar]
- Ahn, Y.H.; Kwak, Y.H.; Suk, S.J. Contractors’ Transformation Strategies for Adopting Building Information Modeling. J. Manag. Eng. 2015, 32, 05015005. [Google Scholar] [CrossRef]
- FEMA. Building Codes Fact Sheet [Official Website of the Department of Homeland Security]. Retrieved from Building Codes Toolkit—Fact Sheet Website; 2013. Available online: https://www.fema.gov/media-library-data/20130726-1903-25045-6626/building_codes_toolkit_fact_sheet_508.pdf (accessed on 3 May 2019).
- Earles, M.D. Clicking on the Dotted Line: Florida’s Enactment of the Uniform Electronic Transactions Act as a Boost to E-Commerce. Nova Law Rev. 2000, 25, 9. [Google Scholar]
- Rankin, J.H.; Chen, Y.; Christian, A.J. E-Procurement in the Atlantic Canadian AEC Industry. ITcon 2006, 11, 75–87. [Google Scholar]
- Eastman, C.; Lee, J.M.; Jeong, Y.S.; Lee, J.K. Automatic rule-based checking of building designs. Autom. Constr. 2009, 18, 1011–1033. [Google Scholar] [CrossRef]
- Nawari, N.O. Automating Codes Conformance. J. Archit. Eng. 2012, 18, 315–323. [Google Scholar] [CrossRef]
- Nawari, N. Building Information Modeling: Automated Code Checking and Compliance Processes; CRC Press, Taylor & Francis Group, LLC: Boca Raton, FL, USA, 2018. [Google Scholar]
- Nawari, N.O. A Generalized Adaptive Framework for Automating Design Review Process: Technical Principles. In Proceedings of the 35th CIB W78 Conference, Chicago, IL, USA, 1–3 October 2018; pp. 405–414. [Google Scholar]
- Dimyadi, J. Automated Compliance Audit Processes for Building Information Models with an Application to Performance-Based Fire Engineering Design Methods. Ph.D. Thesis, The University of Auckland, Auckland, New Zealand, 2016. [Google Scholar]
- Dimyadi, J.; Clifton, C.; Spearpoint, M.; Amor, R. Computerizing Regulatory Knowledge for Building Engineering. J. Comput. Civ. Eng. 2016, 30, 1–13. [Google Scholar] [CrossRef]
- Lee, H.; Lee, J.K.; Park, S.; Kim, I. Translating building legislation into a computer-executable format for evaluating building permit requirements. Autom. Constr. 2016, 71, 49–61. [Google Scholar] [CrossRef]
- Salama, D.M.; El-Gohary, N.M. Semantic Modeling for Automated Compliance Checking. In Proceedings of the 2011 ASCE International Workshop on Computing in Civil Engineering, Miami, FL, USA, 19–22 June 2011; pp. 641–648. [Google Scholar] [CrossRef]
- Kiyavitskaya, N.; Zeni, N.; Mich, L.; Cordy, J.R.; Mylopoulos, J. Text mining through semi automatic semantic annotation. In International Conference on Practical Aspects of Knowledge Management; Springer: Berlin/Heidelberg, Germany, 2006; pp. 143–154. [Google Scholar]
- Pauwels, P.; Van Deursen, D.; Verstraeten, R.; De Roo, J.; De Meyer, R.; Van de Walle, R.; Van Campenhout, J. A semantic rule checking environment for building performance checking. Autom. Constr. 2011, 20, 506–518. [Google Scholar] [CrossRef]
- Cao, D.; Wang, G.; Li, H.; Skitmore, M.; Huang, T.; Zhang, W. Practices and effectiveness of building information modelling in construction projects in China. Autom. Constr. 2015, 49, 113–122. [Google Scholar] [CrossRef]
- Zhang, J.; El-Gohary, N.M. Semantic NLP-Based Information Extraction from Construction Regulatory Documents for Automated Compliance. J. Comput. Civ. Eng. 2012, 30, 04015014. [Google Scholar] [CrossRef]
- Zhang, S.; Teizer, J.; Lee, J.K.; Eastman, C.M.; Venugopal, M. Building Information Modeling (BIM) and Safety: Automatic Safety Checking of Construction Models and Schedules. Autom. Constr. 2013, 29, 183–195. [Google Scholar] [CrossRef]
- Zhang, S.; Boukamp, F.; Teizer, J. Ontology-based semantic modeling of construction safety knowledge: Towards automated safety planning for job hazard analysis (JHA). Autom. Constr. 2015, 52, 29–41. [Google Scholar] [CrossRef]
- Zhang, J.; El-Gohary, N.M. Extending Building Information Models Semiautomatically Using Semantic Natural Language Processing Techniques. J. Comput. Civ. Eng. 2016, 30, C4016004. [Google Scholar] [CrossRef]
- Bloch, T.; Katz, M.; Sacks, R. Machine learning approach for automated code compliance checking. In Proceedings of the 17th International Conference on Computing in Civil and Building Engineering, Tampere, Finland, 5–7 June 2018. [Google Scholar]
- Bloch, T.; Sacks, R. Comparing machine learning and rule-based inferencing for semantic enrichment of BIM models. Autom. Constr. 2018, 91, 256–272. [Google Scholar] [CrossRef]
- Getuli, V.; Ventura, S.M.; Capone, P.; Ciribini, A.L. BIM-based Code Checking for Construction Health and Safety. Procedia Eng. 2017, 196, 454–461. [Google Scholar] [CrossRef]
- Croman, K.; Decker, C.; Eyal, I.; Gencer, A.E.; Juels, A.; Kosba, A.; Miller, A.; Saxena, P.; Shi, E.; Sirer, E.G.; et al. On scaling decentralized blockchains (A position paper). In Lecture Notes in Computer Science (including Subseries Lecture Notes in Artificial Intelligence and Lecture Notes in Bioinformatics); 9604 LNCS; Springer: Berlin/Heidelberg, Germany, 2016; pp. 106–125. [Google Scholar] [CrossRef]

© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Nawari, N.O.; Ravindran, S. Blockchain and Building Information Modeling (BIM): Review and Applications in Post-Disaster Recovery. Buildings 2019, 9, 149. https://doi.org/10.3390/buildings9060149
Nawari NO, Ravindran S. Blockchain and Building Information Modeling (BIM): Review and Applications in Post-Disaster Recovery. Buildings. 2019; 9(6):149. https://doi.org/10.3390/buildings9060149
Chicago/Turabian StyleNawari, Nawari O., and Shriraam Ravindran. 2019. "Blockchain and Building Information Modeling (BIM): Review and Applications in Post-Disaster Recovery" Buildings 9, no. 6: 149. https://doi.org/10.3390/buildings9060149
APA StyleNawari, N. O., & Ravindran, S. (2019). Blockchain and Building Information Modeling (BIM): Review and Applications in Post-Disaster Recovery. Buildings, 9(6), 149. https://doi.org/10.3390/buildings9060149




