Study on Inside Threats Based on Analytic Hierarchy Process
Abstract
1. Introduction
2. Related Studies
2.1. Insider Threats Based on Machine Learning Approach
2.2. Insider Threats Based on Non-Machine Learning Approach: Statistical Scheme
3. Materials and Methods
3.1. Proposed Model
3.2. Internal Threats from Inside the Organization
3.3. Internal Threats from Outside the Organization
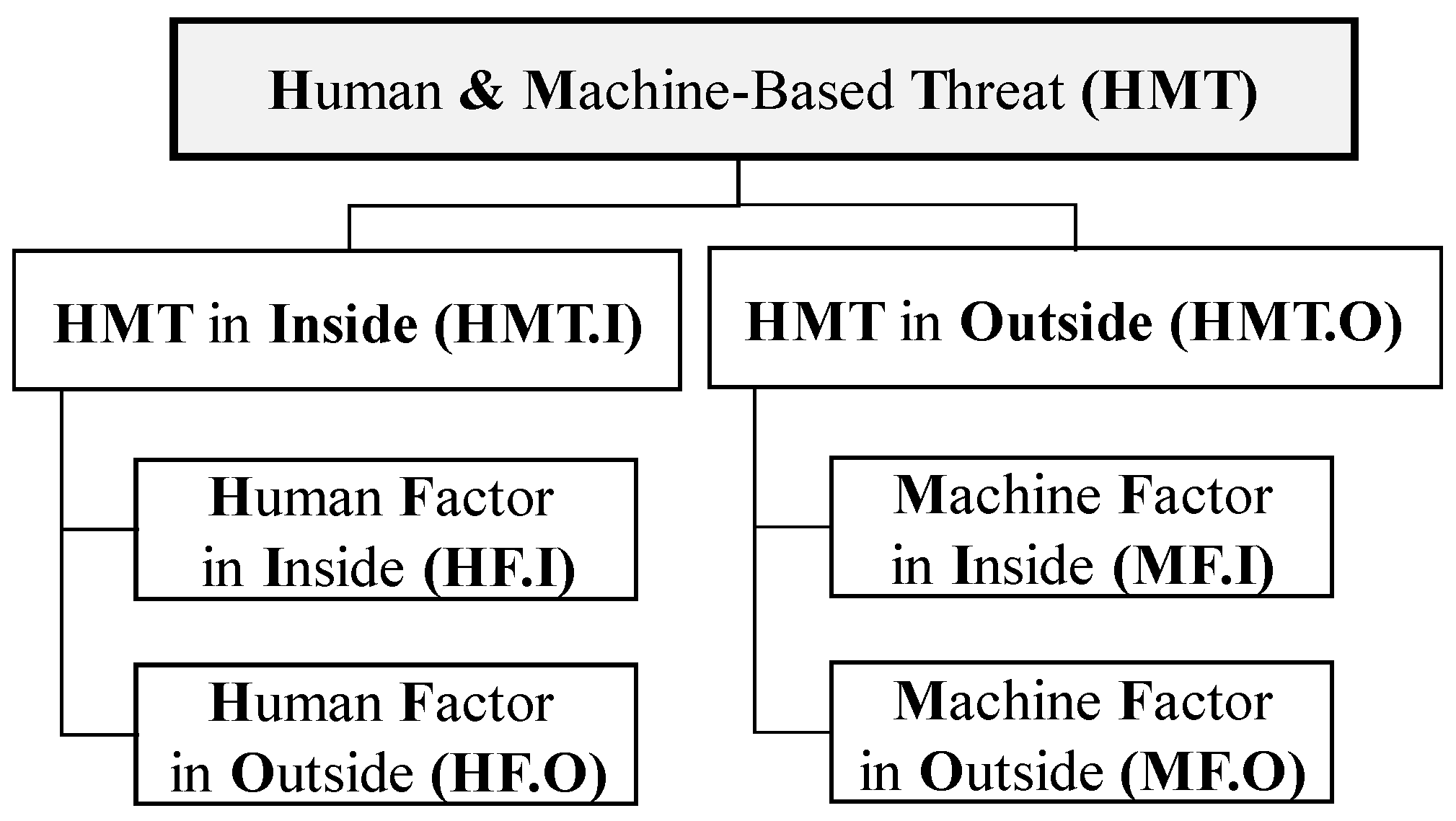
3.4. Human and Machine-Focused Insider Threats Scenario
3.4.1. External Security Breach Scenario
3.4.2. Internal Information Leakage Scenario
3.5. Application of the Proposed Framework by AHP
4. Scenario-Based Insider Threats and Case Analysis
4.1. Scenario (a): Internal Information Leakage by Insiders (IT.I)
4.2. Scenario (b): Internal Information Leakage by Outsiders Using Malware
4.3. Scenario (c): Internal Information Leakage Due to Misuse of Internal System by Insiders
5. Discussion
- -
- This study was based on internal information leakage scenarios arising from a specific organization, and the analysis can be performed differently according to the information security solution, internal/external security policy, business type, and cyber security response capability of each organization.
- -
- The analysis method proposed in this paper is a decision-making tool that supports the development of a response strategy according to the priority of the finally estimated importance of various features. Therefore, from a relative instead of an absolute perspective, it will support the establishment of information protection measures for organizations in the future.
- -
- The scenarios mentioned above can occur independently or be transformed into new or extended interdependent scenarios. Therefore, the proposed method is not intended to be used to establish a standardized policy, but rather is an adaptive and flexible method of analyzing inside threats.
6. Conclusions
Author Contributions
Funding
Acknowledgments
Conflicts of Interest
References
- Insider Threat Report. 2019. Available online: https://www.fortinet.com/content/dam/fortinet/assets/threat-reports/insider-threat-report.pdf (accessed on 14 May 2020).
- Insider Threat Intelligence Report. 2018. Available online: https://nationalinsiderthreatsig.org/itrmresources/DTex%202018%20Insider%20Threat%20Intelligence%20Report.pdf (accessed on 14 May 2020).
- Bishop, M.; Gates, C. Defining the insider threat. In Proceedings of the 4th Annual Workshop on Cyber Security and Information Intelligence Research, Oak Ridge, TN, USA, 12–14 May 2008; pp. 1–3. [Google Scholar]
- Kandias, M.; Mylonas, A.; Virvilis, N.; Theoharidou, M.; Gritzalis, D. An insider threat prediction model. In Proceedings of the International Conference on Trust, Privacy and Security in Digital Business, Bilbao, Spain, 30–31 August 2010; pp. 26–37. [Google Scholar]
- Salem, M.B.; Hershkop, S.; Stolfo, S.J. A survey of insider attack detection research. Adv. Inf. Secur. 2008, 39, 69–70. [Google Scholar]
- Homoliak, I.; Toffalini, F.; Guarnizo, J.; Elovici, Y.; Ochoa, M. Insight into insiders and IT: A survey of insider threat taxonomies, analysis, modeling, and countermeasures. ACM Comput. Surv. 2019, 52, 1–40. [Google Scholar] [CrossRef]
- SEI Cyber Minute: Insider Threats. April 2017. Available online: http://resources.sei.cmu.edu/library/asset-view.cfm?assetid=496626 (accessed on 14 May 2020).
- Cappelli, D.; Moore, A.; Trzeciak, R.; Shimeall, T.J. Common Sense Guide to Prevention and Detection of Insider Threats, 3rd ed.; Version 3.1; CyLab; Carnegie Mellon University; Software Engineering Institute: Pittsburgh, PA, USA, 2009; pp. 1–88. [Google Scholar]
- Vormetric Insider Threat Report. Technical Report. 2015. Available online: https://dtr.thalesesecurity.com/insiderthreat/2015/pdf/2015-vormetric-insider-threat-press-deck-v3.pdf (accessed on 14 May 2020).
- Young, W.T.; Memory, A.; Goldberg, H.G.; Senator, T.E. Detecting unknown insider threat scenarios. In Proceedings of the 2014 IEEE Security and Privacy Workshops, San Jose, CA, USA, 18–21 May 2014; pp. 277–288. [Google Scholar]
- Legg, P.A.; Buckley, O.; Goldsmith, M.; Creese, S. Automated insider threat detection system using user and role-based profile assessment. IEEE Syst. J. 2015, 11, 503–512. [Google Scholar] [CrossRef]
- Kim, J.; Park, M.; Kim, H.; Cho, S.; Kang, P. Insider threat detection based on user behavior modeling and anomaly detection algorithms. Appl. Sci. 2019, 9, 4018. [Google Scholar] [CrossRef]
- Park, K.; Woo, S.; Moon, D.; Choi, H. Secure cyber deception architecture and decoy injection to mitigate the insider threat. Symmetry 2018, 10, 14. [Google Scholar] [CrossRef]
- Vidal, J.M.; Monge, M.A.S. Obfuscation of malicious behaviors for thwarting masquerade detection systems based on locality features. Sensors 2020, 20, 2084. [Google Scholar] [CrossRef]
- Sagar, R.; Jhaveri, R.; Borrego, C. Applications in security and evasions in machine learning: A survey. Electronics 2020, 9, 97. [Google Scholar] [CrossRef]
- Alom, M.Z.; Taha, T.M.; Yakopcic, C.; Westberg, S.; Sidike, P.; Nasrin, M.S.; Hasan, M.; Van Essen, B.C.; Awwal, A.A.S.; Asari, V.K. A state-of-the-art survey on deep learning theory and architectures. Electronics 2019, 8, 292. [Google Scholar] [CrossRef]
- Li, W.; Meng, W.; Kwok, L.F.; Horace, H.S. Enhancing collaborative intrusion detection networks against insider attacks using supervised intrusion sensitivity-based trust management model. J. Netw. Comput. Appl. 2017, 77, 135–145. [Google Scholar] [CrossRef]
- Moya, J.M.; Vallejo, J.C.; Fraga, D.; Araujo, Á.; Villanueva, D.; de Goyeneche, J.M. Using reputation systems and non-deterministic routing to secure wireless sensor networks. Sensors 2009, 9, 3958–3980. [Google Scholar] [CrossRef]
- Fung, C.J.; Baysal, O.; Zhang, J.; Aib, I.; Boutaba, R. Trust management for host-based collaborative intrusion detection. Int. Work. Distrib. Syst. Oper. Manag. 2008, 109–122. [Google Scholar] [CrossRef]
- Fung, C.J.; Zhang, J.; Aib, I.; Boutaba, R. Robust and scalable trust management for collaborative intrusion detection. In Proceedings of the 2009 IFIP/IEEE International Symposium on Integrated Network Management, Long Island, NY, USA, 1–5 June 2009; pp. 33–40. [Google Scholar]
- Azaria, A.; Richardson, A.; Kraus, S.; Subrahmanian, V.S. Behavioral analysis of insider threat: A survey and bootstrapped prediction in imbalanced data. IEEE Trans. Comput. Soc. Syst. 2014, 1, 135–155. [Google Scholar] [CrossRef]
- Greitzer, F.L.; Frincke, D.A. Combining traditional cyber security audit data with psychosocial data: Towards predictive modeling for insider threat mitigation. Insid. Threat. Cyber Secur. 2010, 49, 85–113. [Google Scholar]
- Maloof, M.A.; Stephens, G.D. Elicit: A system for detecting insiders who violate need-to-know. In Proceedings of the International Workshop on Recent Advances in Intrusion Detection, Gold Coast, Australia, 5–7 September 2007; pp. 146–166. [Google Scholar]
- Caputo, D.D.; Maloof, M.A.; Stephens, G.D. Detecting insider theft of trade secrets. IEEE Secur. Priv. 2009, 7, 14–21. [Google Scholar] [CrossRef]
- Mathew, S.; Petropoulos, M.; Ngo, H.Q.; Upadhyaya, S. A data-centric approach to insider attack detection in database systems. In Proceedings of the International Workshop on Recent Advances in Intrusion Detection, Ottawa, ON, Canada, 15–17 September 2010; pp. 382–401. [Google Scholar]
- Ronao, C.A.; Cho, S.B. Anomalous query access detection in RBAC-administered databases with random forest and PCA. Inf. Sci. 2016, 369, 238–250. [Google Scholar] [CrossRef]
- Lo, O.; Buchanan, W.J.; Griffiths, P.; Macfarlane, R. Distance measurement methods for improved insider threat detection. Secur. Commun. Netw. 2018, 2018, 5906368. [Google Scholar] [CrossRef]
- Lindauer, B.; Glasser, J.; Rosen, M.; Wallnau, K. Generating test data for insider threat detectors. J. Wirel. Mob. Netw. Ubiquitous Comput. Dependable Appl. 2014, 5, 80–94. [Google Scholar]
- Tabash, K.A.; Happa, J. Insider-threat detection using Gaussian mixture models and sensitivity profiles. Comput. Secur. 2018, 77, 838–859. [Google Scholar] [CrossRef]
- Moustafa, N.; Creech, G.; Slay, J. Big data analytics for intrusion detection system: Statistical decision-making using finite dirichlet mixture models. In Data Analytics and Decision Support for Cybersecurity; Springer: Cham, Switzerland, 2017; pp. 127–156. [Google Scholar]
- Tuor, A.; Kaplan, S.; Hutchinson, B.; Nichols, N.; Robinson, S. Deep learning for unsupervised insider threat detection in structured cybersecurity data streams. In Proceedings of the Workshops at the Thirty-First AAAI Conference on Artificial Intelligence, San Francisco, CA, USA, 4–5 February 2017; pp. 224–234. [Google Scholar]
- Ndibanje, B.; Lee, H.J.; Lee, S.G. Security analysis and improvements of authentication and access control in the internet of things. Sensors 2014, 14, 14786–14805. [Google Scholar] [CrossRef]
- Saxena, N.; Choi, B.J. State of the art authentication, access control, and secure integration in smart grid. Energies 2015, 8, 11883–11915. [Google Scholar] [CrossRef]
- Liu, D.; Wang, X.F.; Camp, J. Game-theoretic modeling and analysis of insider threats. Int. J. Crit. Infrastruct. Prot. 2008, 1, 75–80. [Google Scholar] [CrossRef]
- Kantzavelou, I.; Katsikas, S. A game-based intrusion detection mechanism to confront internal attackers. Comput. Secur. 2010, 29, 859–874. [Google Scholar] [CrossRef]
- Berninghaus, S.K.; Neumann, T.; Vogt, B. Learning in networks-An experimental study using stationary concepts. Games 2014, 5, 140–159. [Google Scholar] [CrossRef]
- Tang, K.; Zhao, M.; Zhou, M. Cyber insider threats situation awareness using game theory and information fusion-based user behavior predicting algorithm. J. Inf. Comput. Sci. 2011, 8, 529–545. [Google Scholar]
- Zhang, N.; Yu, W.; Fu, X.; Das, S.K. Maintaining defender’s reputation in anomaly detection against insider attacks. IEEE Trans. Syst. Man. Cybern. Part B Cybern. 2010, 40, 597–611. [Google Scholar] [CrossRef] [PubMed]
- Chinchani, R.; Iyer, A.; Ngo, H.Q.; Upadhyaya, S. Towards a theory of insider threat assessment. In Proceedings of the 2005 International Conference on Dependable Systems and Networks, Yokohama, Japan, 28 June–1 July 2005; pp. 108–117. [Google Scholar]
- Luo, S.; Dong, M.; Ota, K.; Wu, J.; Li, J. A security assessment mechanism for software-defined networking-based mobile networks. Sensors 2015, 15, 31843–31858. [Google Scholar] [CrossRef]
- Eberle, W.; Graves, J.; Holder, L. Insider threat detection using a graph-based approach. J. Appl. Secur. Res. 2010, 6, 32–81. [Google Scholar] [CrossRef]
- Serketzis, N.; Katos, V.; Ilioudis, C.; Baltatzis, D.; Pangalos, G. Improving forensic triage efficiency through cyber threat intelligence. Futur. Internet 2019, 11, 162. [Google Scholar] [CrossRef]
- Saaty, T.L. Decision making with the analytic hierarchy process. Int. J. Ser. Sci. 2008, 1, 83–98. [Google Scholar] [CrossRef]
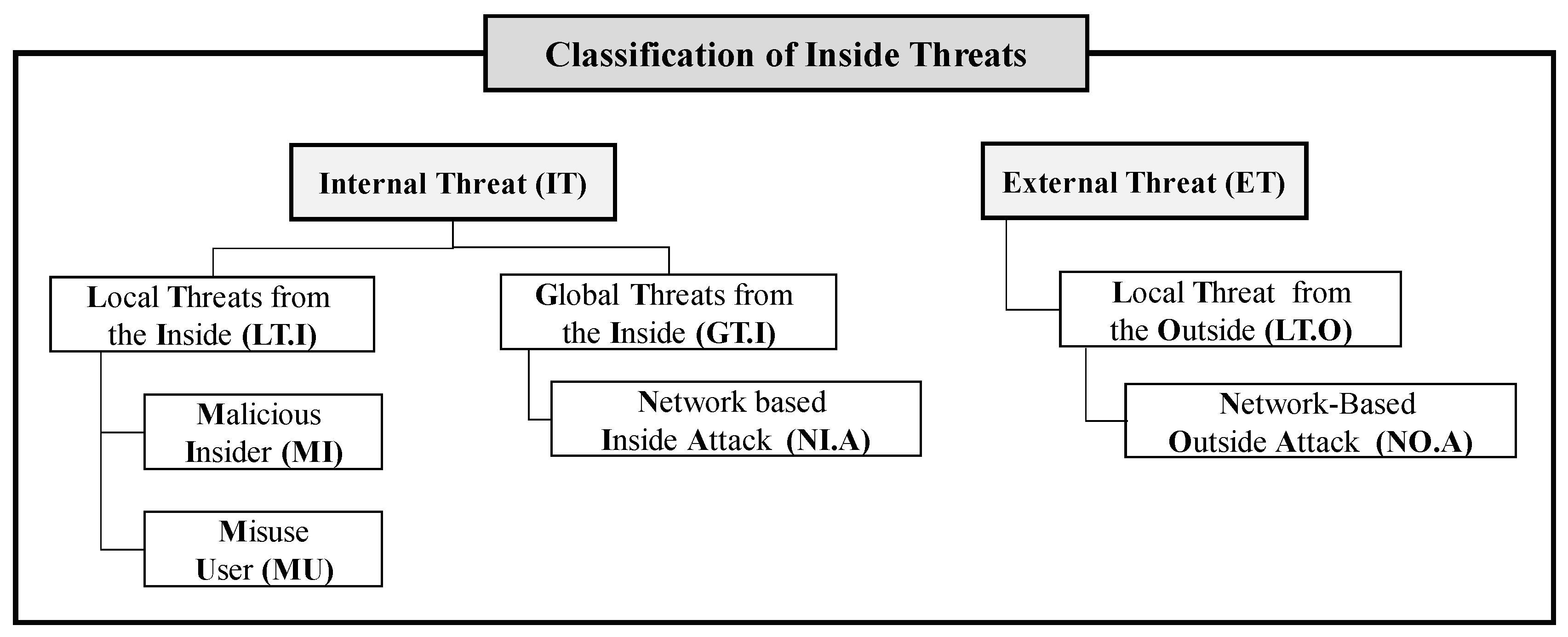
| Threat Type | Attack Type | Main Acts | Content |
|---|---|---|---|
| [IT] Internal threat | [GT.I] Global threat from the inside | [NI.A] Network-based inside attack (e.g., reverse connection, drive by download) | Establishment of a decision process for cases in which outsiders directly cause threats from the inside (internal → external) |
| [LT.I] Local threat from the inside | [MI] Malicious insider | Establishment of a decision process for cases in which insiders cause security breaches with malicious intent through collusion with outsiders (internal → internal) | |
| [MU] Misuse user | Establishment of a decision process for cases in which insiders unintentionally access sensitive data (internal → internal) |
| Subject (Risk Value) | ||
|---|---|---|
| [I] Information (9) | [I.A] Authorized (5) | [I.A_IS] Internal staff (3) |
| [I.A_ES] External staff (7) | ||
| [I.U] Unauthorized (9) | [I.U_IS] Internal staff (5) | |
| [IU.ES] External staff (9) | ||
| Hour (Risk Value) | Place (Risk Value) | Average Access Time (Risk Value) | |
|---|---|---|---|
| [BH] Business hour (5) | [BH_I] Working hour (9) | [IC] Inside company (9) | [M] Min (1) |
| [BH_O] Non-working hour (5) | [OC] Outside company (7) | [H] Hour (3) | |
| [BH_BD] Business day (9) | [D] Domestic (9) | [D] Day (5) | |
| [BH_ND] Non-business day (3) | [I] International (5) | [W] Week (7) | |
| [Mn] Month (9) | |||
| Information Subject (Risk Value) | Information Type (Risk Value) | Leakage Means (Risk Value) | Leakage Path |
|---|---|---|---|
| [CS] Company secret (9) | [BI] Business information (9) | [PCL] PC/laptop (9) | Web mail, Web bulletin board, malware, FTP, Telnet, remote access |
| [RI] Research information (9) | Web cloud, Web hard, shared folder, physical access by unauthorized person | ||
| [MI] Manufacturing information (7) | Portable storage device, mail, screen capture, retired storage media | ||
| [PI] Product information (5) | P2P, torrent, messenger, temporary file, Internet fax | ||
| [HRI] Human resource information (9) | [SDB] Server/DB (7) | Console access, remote access, session border control | |
| [ITRI] IT resource information (9) | [N] Network (7) | Wi-Fi, LAN, Internet, external network | |
| [MI] Management information (7) | [M] Mobile (9) | 3G, 4G, 5G, Bluetooth, recording, tethered shooting | |
| [PI] Personal information (7) | [GPI] General personal information (7) | Mobile storage media, malware, OS vulnerability, ad hoc | |
| [SPI] Sensitive personal information (9) | [OAD] OA device (5) | Digital multifunction printer | |
| [CI] Credit information (9) | [OD] Offline document (7) | Document | |
| [FI] Financial information (9) | [H] Human (9) | Social engineering approach to handling authority | |
| [AI] Account information (9) | Information access by capturing handling rights | ||
| [TI] Transaction information (9) | |||
| [VI] Video information (7) | |||
| [RI] Recording information (7) |
| Threat Type | Attack Type | Main Act | Content |
|---|---|---|---|
| [ET] External threat | [LTO] Local threat from the outside | Acts such as information collection and exploitation | Before performing an initial infiltration into a specific inside environment or lateral movement across the organization, establishment of a decision process for cases where information is collected by scanning, etc., to identify security weaknesses and vulnerabilities of the inside of the organization, or for cases where an exploit is attempted after identifying related vulnerabilities (External → Internal) |
| Access Path (Risk Value) | Time (Risk Value) | Access Location (Risk Value) | Average Access Time (Risk Value) | ||||
|---|---|---|---|---|---|---|---|
| [TIP] Typical IP (5) | [E] Equal (5) | [BD] Bus. day (7) | [WT] Work time (7) [NT] Non-work time (5) | [L] Location (7) | [IC] Internal company (9) | Based on the number of times | [M] Min (1) |
| [M] Multiple (7) | [EC] External company (7) | [H] Hour (3) | |||||
| [IPL] IP Location (7) | [I] Internal (7) | [ND] Non-bus. day (5) | [WT] Work time (7) [NT] Non-work time (3) | [C] Country (7) | [D] Domestic (7) | [D] Day (5) | |
| [E] External (9) | [I] International (7) | [W] Week (7)/[Mn] Month (9) | |||||
| [S] Specific (9) | Period | [P] Periodic (5) | |||||
| [NP] Non-periodic (7) | |||||||
| Type | [S] Simultaneous (5) | ||||||
| [SR] Shot repetition (7) | |||||||
| Subject (Risk Value) | Malicious Activities (Risk Value) | ||
|---|---|---|---|
| [AT] Account type (5) | [E] Equal (5) | [LA] Login attempt (7) | [AT] Account takeout (9) |
| [M] Multiple (7) | [AA] Access attempt (7) | [BDA] Brute force & dictionary attack (7) | |
| [A] Account (7) | [S] Server (9) | [SC] Simultaneous connection (5) | |
| [WA] Web-APP (7) | [PCF] PW change failed (5) | ||
| [D] DB (9) | [EO] Event occurrence | [IIPE] Internal IP event (9) | |
| [P] PC (5) | [FWE] FW event (7) | ||
| [NDS] Network directory service (7) | [EL] Event log (7) | ||
| [FW] Firewall (9) | [SIPL] Source IP log (9) | ||
| [I] IPS (9) | [SS] Signature (word) search (7) | ||
| [WVIS] Web vulnerabilities inspection system (9) | [PC] Periodic communication (5) | ||
| [MS] Mail server (9) | [CWV] Check for web vulnerabilities (7) | ||
| [VS] Vaccine server (9) | [MA] Malware application (9) | ||
| [WAP] Wireless AP (9) | [S] Scanning | [NDP] Network device port (9) | |
| [P] Port (5) | [SP] Server port (9) | ||
| [NDS] Network device switch (7) | [PCP] PC port (7) | ||
| [UC] Unauthorized client (9) | |||
| Threat Type | Attack Type | Main Act | Content |
|---|---|---|---|
| [HMT] Human and machine threat | [HMT.I] HMT on the inside | [HF.I] Human factor on the inside | Establishment of a decision process for cases in which insiders perform direct operations, such as viewing, deleting, and printing of specific important data within the internal network |
| [HF.O] Human factor on the outside | Establishment of a decision process for cases in which outsiders launch targeted attacks against specific vulnerabilities, such as attempting to exploit shellcode that is not patternized based on rules, when performing an initial infiltration into a specific inside environment or lateral movement across the external network | ||
| [HMT.O] HMT on the outside | [MF.I] Machine factor on the inside | Establishment of a decision process for cases in which insiders use automation tools or related scripts when performing lateral movement across the internal network | |
| [MF.O] Machine factor on the outside | Establishment of a decision process for cases in which outsiders attempt to exploit based on automated tools or script patterns in the event of an initial infiltration into a specific inside environment or lateral movement across the external network |
| Classification (Risk Value) | Threat Scenario | Interworking System |
|---|---|---|
| [CL] Certification-based login (9) | Ex) Fail to log into a single account after a certain number of attempts with one IP (e.g., more than 10 attempts within 5 min) | VPN |
| Ex) Fail to log into multiple accounts after a certain number of attempts with one IP (e.g., more than 10 attempts within 5 min) | ||
| Ex) Fail to log into a single account after a certain number of attempts (e.g., more than five attempts within 1 min) | ||
| Ex) Attempt to log into the company’s internal servers periodically with an external IP | Server | |
| Ex) Attempt to log in to the company’s internal web applications periodically with an external IP | Web application | |
| Ex) Attempt to log into the company’s internal DB periodically with an external IP | DB | |
| Ex) Attempt to log into the company’s internal PCs periodically with an external IP | PC | |
| Ex) Attempt to log into the company’s internal network equipment periodically with an external IP | Network equipment | |
| [AA] Access attempt (9) | Ex) The occurrence of the same source IP login in the firewall for a certain number of times (e.g., more than 50,000 within 5 min) | Firewall |
| Ex) When abnormal outbound traffic is detected in the DMZ section | ||
| Ex) The same IPS attack from a specific IP is repeated for a certain number of times (e.g., more than 10 times per hour) | IPS Web application Firewall | |
| Ex) After an IPS attack from a specific IP, a certain number of firewall events (Permit/Deny) (e.g., more than 10 times) | ||
| [PA] Periodic access (7) | Ex) Periodic communication from a specific external IP to the internal server IP (e.g., more than two times in a day) | Firewall IPS/IDS access control system |
| Ex) Periodic communication from a specific external IP to the internal PC IP (e.g., more than two times in a day) | ||
| [PC] Periodic Communication (7) | Ex) Periodic communication from an internal server IP to a specific external IP (e.g., more than two times in a day) | |
| Ex) Periodic communication from an internal PC IP to a specific external IP (e.g., more than two times in a day) | ||
| Ex) Periodic communication from an internal network equipment IP to a specific external IP (e.g., more than two times in a day) | ||
| [SA] Scanning Attempt (9) | Ex) Attempts to connect to multiple server IPs using the same port from a specific external IP for a certain number of times (e.g., more than 10 times in an hour) | Access control system firewall log system |
| Ex) Attempts to connect to multiple PC IPs using the same port from a specific external IP for a certain number of times (e.g., more than 10 times in an hour) | ||
| Ex) Attempts to connect to multiple web application IPs using the same port from a specific external IP for a certain number of times (e.g., more than 10 times in an hour) |
| Leak Paths (Risk Value) | Threat Scenario | Interworking System |
|---|---|---|
| [WW] Webmail/web board (5) | Ex) Internal staff (IS) with access to company secrets repeatedly leaks them through webmail/web board during the workday within the company | PC Security, DLP, mail/messenger monitoring, DRM, audit log creation/inquiry |
| [M] Malware (9) | Ex) IS with access to company secrets repeatedly leaks them through malware during the workday within the company | Vaccine, NAC-SW management |
| [FTR] FTP, Telnet, remote (7) | Ex) IS with access to company secrets repeatedly leaks them through FTP, telnet, remote connection during the workday within the company | DLP (remote desktop control, Telnet control, FTP control) |
| [CW] Cloud/Web-hard (9) | Ex) IS with access to company secrets repeatedly leaks them through web cloud/web hard during the workday within the company | DLP (Web hard blocking, cloud blocking), harmful site blocking, audit log creation/inquiry |
| [SF] Shared folder (9) | Ex) IS with access to company secrets repeatedly leaks them through shared folders during the workday within the company | PC integrated security, NAC, DLP-file management |
| [UA] Unauthorized access (9) | Ex) IS with no access to company secrets repeatedly leaks them through physical access during the workday within the company | Access control |
| [MSD] Mobile storage device (7) | Ex) IS with access to company secrets repeatedly leaks them through mobile storage devices during the workday within the company | External port control |
| [SC] Screen capture (5) | Ex) IS with access to company secrets repeatedly leaks them through screen captures during the workday within the company | DLP, DRM |
| [RSD] Retired storage device (5) | Ex) IS with access to company secrets repeatedly leaks them through retired storage devices during the workday within the company | WPM (automatic deletion system) |
| [PT] P2P, torrent (9) | Ex) IS with access to company secrets repeatedly leaks them through P2P and Torrent during the workday within the company | DLP, harmful web site blocking |
| [M] Messenger (5) | Ex) IS with access to company secrets repeatedly leaks them through the messenger during the workday within the company | PC integrated security, DLP, audit log creation/inquiry, mail/messenger control |
| [TF] Temporary file (5) | Ex) IS with access to company secrets repeatedly leaks them by restoring temporary file history during the workday within the company | DRM, WPM |
| [IF] Internet FAX (3) | Ex) IS with access to company secrets repeatedly leaks them through the internet fax during the workday within the company | Electronic Secure FAX |
| [PF] Password file (9) | Ex) IS with access to company secrets repeatedly leaks them by accessing/obtaining password history files during the workday within the company | PC integrated security (compliance with password policy) |
| [CA] Console access (9) | Ex) IS with access to company secrets repeatedly leaks them through the console access to servers/DB during the workday within the company | Server/DB access control, DBACM |
| [RA] Remote access (9) | Ex) IS with access to company secrets repeatedly leaks them through the remote access to servers/DB during the workday within the company | DLP (remote desktop control) |
| [IWN] Internal Wi-Fi network (9) | Ex) IS with access to company secrets repeatedly leaks them by getting access to internal Wi-Fi networks during the workday within the company | WIPS-access control, AP control, PC control, log creation/inquiry |
| [IL] Internal LAN (5) | Ex) IS with access to company secrets repeatedly leaks them through LAN during the workday within the company | NAC |
| [DE] Document export (9) | Ex) IS with access to company secrets leaks them from inside to outside during the workday | Exit & entry/access control |
| [SEA] Social engineering attack (9) | Ex) IS with no access to company secrets leaks them through a social engineering approach to handling authority | PC integrated security, NAC, DRM, DLP |
| [RD] Right deception (9) | Ex) IS with no access to company secrets leaks them through information access by capturing handling rights | PC integrated security, NAC, DRM, DLP |
| LT.I | LT.I_MI | LT.I_MU | GT.I | GT.I_NI.A | LT.O | LT.O_NO.A | |
|---|---|---|---|---|---|---|---|
| Weight | 0.435 | 0.171 | 0.124 | 0.086 | 0.070 | 0.064 | 0.050 |
| HMT.I | HMT.I_HF.I | HMT.I_HF.O | HMT.O | HMT.O_MF.I | HMT.O_MF.O | |
|---|---|---|---|---|---|---|
| Weight | 0.387 | 0.271 | 0.134 | 0.089 | 0.068 | 0.051 |
| I.A | I.A_IS | CS | BH_ND | BH_O | Hour | PCL | OD | Mobile | Human | |
|---|---|---|---|---|---|---|---|---|---|---|
| Weight | 0.026 | 0.038 | 0.036 | 0.019 | 0.023 | 0.038 | 0.187 | 0.224 | 0.161 | 0.248 |
| Priority | 8 | 6 | 7 | 10 | 9 | 5 | 3 | 2 | 4 | 1 |
| LT.I_MI | LT.I_MU | BH_BD | BH_I | PCL | MA | VS | Scanning | SF | CS | |
|---|---|---|---|---|---|---|---|---|---|---|
| Weight | 0.011 | 0.031 | 0.020 | 0.020 | 0.073 | 0.208 | 0.221 | 0.181 | 0.139 | 0.097 |
| Priority | 10 | 7 | 8 | 8 | 6 | 2 | 1 | 3 | 4 | 5 |
| I.A_IS | PCL | SDB | IL | PF | SEA | VS | MA | PC | CS | |
|---|---|---|---|---|---|---|---|---|---|---|
| Weight | 0.011 | 0.020 | 0.052 | 0.025 | 0.173 | 0.072 | 0.128 | 0.157 | 0.194 | 0.167 |
| Priority | 10 | 9 | 7 | 8 | 2 | 6 | 5 | 4 | 1 | 3 |
© 2020 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Seo, S.; Kim, D. Study on Inside Threats Based on Analytic Hierarchy Process. Symmetry 2020, 12, 1255. https://doi.org/10.3390/sym12081255
Seo S, Kim D. Study on Inside Threats Based on Analytic Hierarchy Process. Symmetry. 2020; 12(8):1255. https://doi.org/10.3390/sym12081255
Chicago/Turabian StyleSeo, Sang, and Dohoon Kim. 2020. "Study on Inside Threats Based on Analytic Hierarchy Process" Symmetry 12, no. 8: 1255. https://doi.org/10.3390/sym12081255
APA StyleSeo, S., & Kim, D. (2020). Study on Inside Threats Based on Analytic Hierarchy Process. Symmetry, 12(8), 1255. https://doi.org/10.3390/sym12081255






