1. Introduction and Related Works
Currently, we can observe many so-called special applications of the Internet of Things (IoT) in both the civilian and military domains, where IoT is used in environments characterized by unreliable communication infrastructure, high event dynamics, and the need to make decisions in near-real time. In practice, this means that data must be processed locally, close to IoT end devices and users, with minimal dependence on a central data center. Examples of special applications in civilian areas include rescue and crisis management, public safety, and smart cities [
1]. Rescue teams often have to build ad hoc mobile processing nodes in vehicles (tactical clouds) to analyze data from drones, cameras, and sensors without permanent Internet access. The use of IoT in military operations improves effectiveness by enabling the integration, analysis, and exchange of data between sensors, command and control systems, combat platforms, and specialized field devices. The integration of IoT into military environments improves situational awareness [
2], enables faster commander decision making, improves resource management efficiency, and provides real-time decision support, all of which are crucial in the context of today’s asymmetric and multi-dimensional threats [
3].
However, the widespread implementation of IoT systems for special applications poses significant security challenges, including vulnerability to cyberattacks, issues with the integrity and confidentiality of transmitted data, and difficulties in managing access in decentralized operating environments [
4,
5]. In response to these problems, research is being conducted on advanced protection mechanisms, among which attribute-based encryption (ABE) and attribute-based access control (ABAC) play an important role [
6,
7,
8,
9,
10,
11].
ABE is an advanced cryptographic scheme that enables fine-grained access control to encrypted data based on attributes assigned to users, resources, or the environment [
12]. In the ABE model, both users’ private keys and ciphertexts (encrypted messages) are associated with attributes that describe entities, roles, or access contexts. Decryption is possible only if the user’s attributes satisfy the access policy defined when the message was encrypted. There are two basic types of ABE [
12]:
In key-policy attribute-based encryption (KP-ABE), the access policy is embedded in the user’s private key, and the encrypted data are marked with a set of attributes. The user will only decrypt the data if the ciphertext’s attribute set matches the user’s key policy.
In ciphertext-policy attribute-based encryption (CP-ABE), the opposite is true—the access policy is associated with the ciphertext, and the user’s private key contains a set of attributes. Decryption occurs if the user has the required set of attributes consistent with the policy specified during encryption.
ABE provides a solid technical foundation for implementing ABAC models in distributed, dynamic environments, such as military IoT, where flexible, scalable access control is essential [
13,
14]. Thus, ABE can be seen as a cryptographic implementation of the ABAC concept.
ABAC is recommended for military IoT systems due to its ability to enforce security policies in a highly granular, adaptive, and robust manner, being well suited to the dynamic and sensitive nature of military operations and the hostile environments in which they are conducted [
15]. This is expected to bring several benefits, including improved security in the IoT through capabilities such as precise, contextual access control, the mitigation of insider threats, and zero-trust requirements. ABAC enables precise access control by evaluating multiple attributes (e.g., user role, device, location, time, mission context), rather than static roles or simple user lists. This flexibility allows military systems to enforce context-dependent restrictions, tailoring access in real time to operational needs and threat levels. By evaluating actual attributes rather than predefined roles, ABAC reduces the risks of insider threats and privilege escalation by ensuring that only authorized attribute-based actions are allowed—even after credential compromises.
Special applications of the IoT often involve federated systems [
16] across diverse partners (coalitions, allied units, civilian interfaces) [
17], with varying clearance levels and data sensitivity. ABAC’s attribute-centric model supports secure, fine-grained information sharing and coalition operations while respecting policy requirements and minimizing data leakage between partners. The IoT environment in military contexts is highly dynamic, with devices and users frequently joining, leaving, or changing roles and locations.
ABAC can be tightly integrated with cryptographic schemes, especially ABE, to enforce object-level protection and enable a data-centric security [
18] approach in battlefield IoT and military environments [
19]. With ABE, data (objects) can be encrypted using an access policy based on attributes (such as user roles, clearance levels, device types), directly mapping to ABAC policies. Only users or devices with matching attributes (encoded in their cryptographic keys) can decrypt and access the data, regardless of the location of the network or intermediate storage. This ensures secure end-to-end protection at the object level, not just the perimeter. Data are encrypted as soon as they are generated or ingested by IoT devices, with ABAC rules embedded in the encryption policy (ciphertext-policy ABE, or CP-ABE). Decryption is possible only if the requesting user’s or system’s attributes satisfy the policy embedded in the encrypted object, eliminating the reliance on a single enforcement point and supporting multi-domain coalition environments.
Although the potential applications of ABAC in special IoT systems are emerging, the practical deployment of this method requires further research and experimentation to address emerging questions:
Which of the known schemes will be most suitable for use in special IoT systems and in which specific use cases?
How does performance depend on a range of typical parameters for special IoT?
Which scheme is better to use for protection in the edge IoT area and which in larger-scale networks?
Can ABAC policies be scaled to large distributed networks, effectively managing complex relationships between numerous entities without the unmanageable overhead found in traditional models such as role-based access control (RBAC)?
How well is ABE and ABAC integration suited for the special IoT due to support for dynamic, large-scale, and context-driven environments with fine-grained control and reduced management overhead?
To answer the above research questions, a comparative performance analysis between the CIRCL scheme based on CP-ABE pairing and the hybrid post-quantum KEMAC [
20] Covercrypt has been conducted. This research aimed to obtain key information on the implementation of data-centric security (DCS) across the various operating environments of the civilian and military Internet of Things.
The CIRCL library implements an efficient CP-ABE scheme, referred to as tkn20, based on the work by Tomida et al. [
21]. This scheme guarantees IND-CCA2 security and supports expressive policies. In [
7], it has been proven that, under certain assumptions, it is also applicable for resource-constrained IoT devices, which is particularly relevant in demanding military use cases.
In contrast, Covercrypt provides a hybrid post-quantum secure encryption scheme that combines key encapsulation with attribute-based policies. This architecture enables fast encryption and robust access control, which are essential for special IoT systems requiring quantum-resilient security [
22]. Benchmarking studies, such as those conducted by de la Piedra et al. [
23], suggest that pairing-based CP-ABE schemes like tkn20 often incur higher computational costs than hybrid schemes like Covercrypt, which demonstrate advantages in edge computing scenarios.
The integration of ABAC and ABE allows for the scalable, flexible, and secure management of dynamic multi-domain IoT networks. This capability helps to mitigate insider threats and is fundamental to implementing zero-trust environments [
24]. Furthermore, this integration aligns with the data-centric security approach, ensuring data protection from their origin throughout their lifecycle and enabling granular access control [
25]. The adoption of DCS is currently under consideration by multiple entities, including the military sector [
26]. This research also aligns with the recent NIST standardization of device onboarding in IoT networks [
27]. However, further research is required to benchmark these schemes under special IoT application-specific constraints and to optimize their deployment strategies.
This paper contributes to the field by providing a comparative performance analysis between the CIRCL CP-ABE scheme and Covercrypt. This analysis advances our understanding of suitable data-centric security approaches specifically tailored to specialized IoT environments. This study represents the first direct comparison of these two schemes and their potential applications, highlighting their respective strengths and weaknesses. Although benchmarks for various ABE libraries, such as those in [
28], have been provided previously, these two specific libraries have not yet been evaluated together. Furthermore, this study defines operational scenarios based on real-world applications in the civilian and military domains, providing the first direct evaluation of these cryptographic schemes with regard to specific IoT system requirements.
The remainder of the paper is organized as follows.
Section 2 briefly characterizes the foundations of modern data access control, particularly attribute-based access control (ABAC) and the data-centric security paradigm, as well as ETSI’s fundamentals for the standardization of post-quantum attribute-based encryption, and briefly explains the foundations and basic phases involved in applying ciphertext-policy attribute-based encryption (CP-ABE) and Covercrypt as an attribute-based key encapsulation mechanism (KEM).
Section 3 presents the methodology and results of the comparison tests.
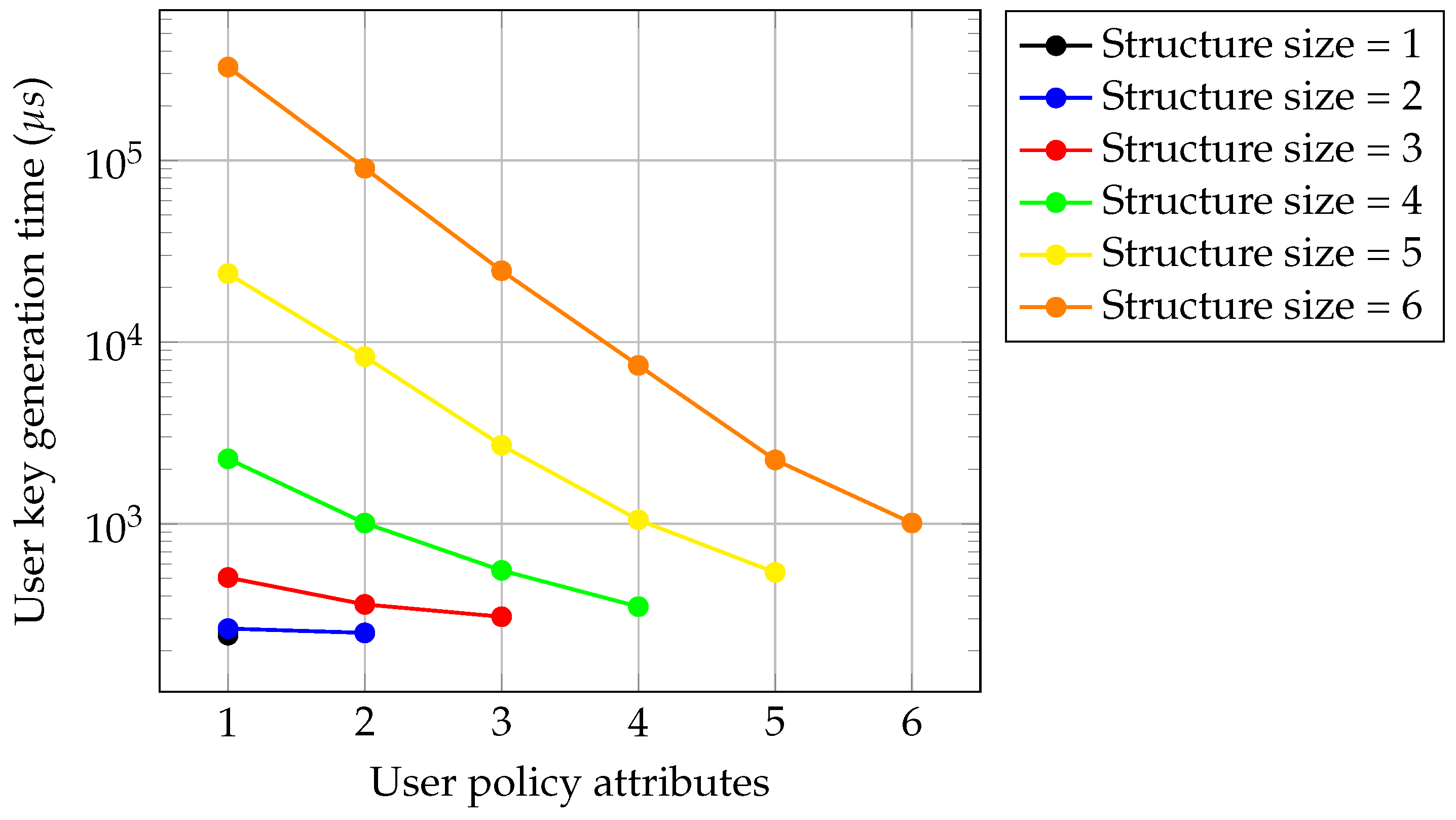
Section 3.9 provides an analysis of the complexity and scalability of the compared schemes in civilian and military IoT, focusing on key parameters. Both ciphertext-policy attribute-based encryption (CP-ABE, as implemented by CIRCL) and the key encapsulation mechanism with access control (KEMAC, as implemented by Covercrypt) are evaluated based on their operational costs as a function of the system parameters. In
Section 3.10, the trade-offs between the highly scalable pairing-based CP-ABE (CIRCL) and the bandwidth-efficient, quantum-safe KEMAC (Covercrypt) are presented in the two distinct IoT operational scenarios. In
Section 4, the results are summarized and directions for further work are identified.
2. Background
2.1. The Foundations of Modern Data Access Control
2.1.1. Attribute-Based Access Control
Attribute-based access control (ABAC) is defined by the National Institute of Standards and Technology (NIST) as an access control model where authorizations to perform operations on resources are granted to subjects based on the evaluation of policies against the attributes of subjects, resources, and the environment [
29].
The core of an ABAC model is a set of policies that combine and evaluate these attributes using logical rules. The fundamental components are as follows:
Subject attributes:Characteristics of the user (e.g., identity, clearance, department).
Resource attributes: Characteristics of the object being accessed (e.g., creation date, data classification, owner).
Action attributes: Characteristics of the operation being attempted (e.g., ‘read’, ‘write’, ‘delete’).
Environmental attributes: Contextual factors such as time of day, location of access, or device security posture [
29].
This structure allows for the creation of highly expressive access control policies (e.g., “Allow doctors to view medical records they created within their own hospital during work hours”), which are essential for securing complex, distributed systems [
29]. In the context of this report, the focus is on cryptographically enforced ABAC. Here, the policy decision point (PDP) and policy enforcement point (PEP) are effectively merged into the cryptographic algorithms themselves. Two approaches can be distinguished:
- KP-ABE
Key-Policy ABE: Attributes are associated with the ciphertext, and policies are embedded in the user’s key. This is useful for database queries or content-centric routing.
- CP-ABE
Ciphertext-Policy: Attributes are associated with the user’s key, and policies are embedded in the ciphertext. This is the most natural fit for DCS, as it allows the data owner (the encryptor) to decide who can access the data at the moment of creation.
Both CIRCL (implementing tkn20) and Covercrypt utilize the CP-ABE model (or its functional equivalent in KEMAC), placing control in the hands of the data originator.
2.1.2. The Need for Data-Centric Security in Coalition Warfare
Modern warfare has evolved into network-centric warfare (NCW), where information superiority is as decisive as firepower. The integration of IoT devices—ranging from unattended ground sensors (UGS) to soldier-worn biometric monitors—generates a torrent of sensitive data that must be shared across disparate branches and coalition partners. Traditional “castle-and-moat” security architectures, which rely on securing the network perimeter (e.g., via VPNs or firewalls), are fundamentally incompatible with the dynamic, ad hoc nature of coalition operations. In these environments, the network infrastructure itself may be untrusted or shared with partners possessing varying clearance levels.
Data-centric security (DCS) addresses this by decoupling data protection from the transport layer. In a DCS model, the data are encrypted at the source (the sensor or soldier) and remain encrypted until they reach an authorized recipient, regardless of the intermediary nodes that they traverse. The access control policy is not enforced by a central server (which represents a single point of failure and a latency bottleneck) but is mathematically embedded within the encrypted data themselves.
Attribute-based encryption (ABE) is the cryptographic cornerstone of DCS. Unlike traditional Public Key Infrastructure (PKI), which encrypts data for a specific identity (e.g., “encrypt for Serial Number 12345”), ABE encrypts data for a policy defined over a set of attributes (e.g., “encrypt for (Role: Medic AND Clearance: Secret) OR (Role: Commander)”). This allows for “one-to-many” encryption and enables the system to grant access to users who may not even exist at the time of encryption, provided that they eventually possess the requisite credentials. This capability is essential for the dynamic join-and-leave behavior of tactical units in the field. The data-centric security (DCS) paradigm marks a strategic shift from protecting network perimeters to protecting the data themselves. In this model, security is not an external shell but an intrinsic property of the data object. The objective is to ensure that the data remain protected regardless of their location, whether they are at rest in a database, in transit over a network, or in use within an application.
DCS is realized by binding security policies, primarily through cryptography, directly to the data. Key mechanisms enabling this paradigm include strong encryption, embedded access control logic, and data classification. By making data self-defending, DCS addresses the shortcomings of perimeter-based models, which become ineffective once a breach occurs or when data are shared with external partners. Attribute-based encryption (ABE) is considered a key cryptographic enabler for achieving a true data-centric architecture, as it allows access policies to be inseparable from the encrypted data [
12].
2.2. ETSI’s Standardization of Post-Quantum, Attribute-Based Encryption
2.2.1. The Quantum Threat and the Need for a New Standard
The emergence of practical quantum computing poses a catastrophic threat to widely used public key cryptographic algorithms, such as RSA and ECC [
30]. A sufficiently powerful quantum computer, leveraging Shor’s algorithm, could break the mathematical foundations of this cryptography, rendering vast amounts of secured data and communications vulnerable. This threat is particularly acute for data with long-term confidentiality requirements due to “harvest now, decrypt later” attacks, where an adversary archives encrypted data today with the intent of decrypting them in the future [
31].
Recognizing this, standardization bodies like ETSI initiated efforts to define cryptographic systems that are secure against both classical and quantum computers. The goal was to establish a clear standard for “crypto-agility”—the ability to transition to quantum-resistant algorithms—while simultaneously enhancing the functionality of cryptographic primitives to better serve modern access control needs [
32]. The strategic utility of ABE is currently threatened by the rapid advancement of quantum computing. Standard ABE schemes rely on the hardness of the Decisional Bilinear Diffie–Hellman (DBDH) problem over elliptic curves. Shor’s algorithm proves that a sufficiently powerful quantum computer could solve the discrete logarithm problem in polynomial time, effectively breaking all pairing-based cryptography. While cryptographically relevant quantum computers (CRQCs) may not be available for another decade, the threat is immediate due to “harvest-now, decrypt-later” strategies. Adversaries are actively intercepting and archiving encrypted military communications today, with the intent of decrypting them once quantum capabilities mature. Consequently, military systems designed with a lifecycle of 10–20 years must integrate post-quantum cryptography (PQC) immediately to protect long-term intelligence. This necessity has driven the European Telecommunications Standards Institute (ETSI) to standardize Covercrypt, a hybrid scheme that combines classical elliptic curve cryptography with quantum-resistant Lattice-based primitives (specifically, variants of the NIST finalist Kyber) [
33]. By layering these protections, Covercrypt ensures that data remain secure as long as at least one of the underlying mathematical problems remains hard.
2.2.2. Covercrypt: A Hybrid KEMAC Solution
In response to these challenges, ETSI published the technical specification ETSI TS 104 015, which standardizes a hybrid, quantum-safe cryptographic scheme known as Covercrypt [
32]. The scheme is formally defined as a key encapsulation mechanism with access control (KEMAC).
Its hybrid nature is a critical feature for a secure transition. It combines a classical, well-established algorithm with a post-quantum algorithm from the finalists/alternates of the NIST PQC standardization process. Security is maintained as long as at least one of the component algorithms remains unbroken, thus providing resilience against unforeseen breaks in either primitive [
20,
34]. Most importantly, Covercrypt natively implements ciphertext-policy attribute-based encryption, as detailed in
Section 2.4. This allows a data originator to encrypt a session key under a specific access policy (e.g., (role = ‘auditor’ AND region = ‘EMEA’) OR clearance = ‘L3’). Only users whose cryptographic keys are associated with attributes that satisfy this policy can decapsulate the session key and decrypt the corresponding data [
32].
2.2.3. Connecting Covercrypt with ABAC and DCS
The ETSI standardization of Covercrypt provides a formal, robust cryptographic foundation for implementing ABAC and realizing the DCS paradigm.
Link to ABAC: Covercrypt is a direct cryptographic enforcement mechanism for ABAC. It translates abstract ABAC policies into immutable cryptographic rules embedded within the ciphertext itself. The authorization check is not performed by a fallible external policy decision point but is an intrinsic part of the decryption process. This eliminates entire classes of vulnerabilities related to policy enforcement and ensures that access control is absolute.
Link to DCS: Covercrypt is a quintessential enabling technology for data-centric security. By binding an attribute-based access policy to the data through encryption, the data become a self-contained, self-protecting entity. Their security is inherent and persists across different environments—cloud storage, third-party applications, or local devices. This directly addresses the core objective of DCS: to protect data throughout their lifecycle, ensuring that only authorized individuals can access them, regardless of where they reside.
Thus, ETSI TS 104 015 not only provides a forward-looking solution to the quantum threat but also standardizes a powerful primitive for building the next generation of secure, fine-grained, and data-centric information systems.
2.3. Ciphertext-Policy Attribute-Based Encryption
Ciphertext-policy attribute-based encryption (CP-ABE) is an advanced cryptographic primitive that enables fine-grained access control over encrypted data. In a CP-ABE system, a user’s private key is associated with a set of descriptive attributes, and a ciphertext is encrypted with an access policy defined over these attributes. A user can only decrypt a ciphertext if the attributes associated with their private key satisfy the policy embedded within the ciphertext.
The tkn20 scheme [
35], available in Cloudflare’s CIRCL library [
36], is a modern and efficient implementation based on the foundational work of Waters. A trusted key authority (KA) is responsible for generating public parameters in the system and a master secret key (MSK). The KA then uses the MSK to issue personalized private keys to users based on their attributes.
2.3.1. Setup
Before any keys can be issued or data encrypted, a trusted entity known as the key authority (KA) must initialize the system. This is accomplished through a ‘Setup’ algorithm that creates the essential public and private parameters for the entire environment.
The ‘Setup’ algorithm generates the following:
Public Parameters (PP): These parameters are made publicly available and are used by anyone who wishes to encrypt data. The PP typically consists of
where
g is a generator of a cyclic group
of order
p,
is a randomly chosen secret exponent, and
H is a public hash function that maps attribute strings to elements in
.
Master Secret Key (MSK): This key is the root of trust for the entire system and must be kept secret by the key authority at all times. The MSK consists of
where
is another randomly chosen secret exponent. The MSK empowers the KA to issue private keys to users.
2.3.2. User Key Generation
The generation of a user’s private key (SK) is a critical process managed exclusively by the key authority. It involves combining the system’s master secret key with the user’s specific attribute set. The core of the process, particularly its security against collusion, lies in the introduction of a unique, random secret for each user.
Let the system’s public parameters be , where g is a generator of a cyclic group , is a secret exponent, and H is a hash function that maps attributes to elements of . The master secret key (MSK) is , where is another secret exponent.
The key generation algorithm, often denoted as ‘KeyGen(MSK, A)’, where A is the user’s attribute set, proceeds as follows:
- 1.
Generate a User-Specific Random Secret: The KA first selects a random secret uniformly at random. This value is unique for each key generation instance and serves as the cornerstone of collusion resistance.
- 2.
Compute the Base Key Component: A base component of the private key,
, is computed. This component binds the user’s secret
t with the master secrets
and
.
This component is essential for the decryption process and ensures that any valid key has been properly derived from the MSK.
- 3.
Compute Attribute-Specific Components: For each attribute
j in the user’s attribute set
A, a corresponding key component
is computed. Crucially, each of these components is also blinded by the same user-specific secret
t.
Here, is the result of hashing the attribute string (e.g., “role: doctor”) to a group element.
The final user private key
is the collection of the base component and all attribute-specific components:
This structure ensures that all parts of a user’s key are mathematically linked through the single secret value
t.
2.3.3. Encryption
An entity wishing to encrypt a message M does so by using the public parameters and defining an access policy . The access policy is a logical formula (e.g., ("role:doctor" AND "department:cardiology") OR "role:admin") that specifies which attributes are required for decryption. This policy is typically represented internally as a linear secret sharing scheme (LSSS).
The Encrypt(PP, M, ) algorithm proceeds as follows:
- 1.
Select an Encryption Secret: The encryptor chooses a random, single-use secret . This secret will be used to encrypt the message and will be embedded in the ciphertext.
- 2.
Encrypt the Message: The main part of the ciphertext,
, is created by binding the message
M with the master secret component
and the encryption secret
s. This is achieved using a pairing function
e:
The term acts as a one-time symmetric key (a blinding factor) that masks the message.
- 3.
Embed the Secret: A second component,
, is created to carry the encryption secret
s, blinded by the master secret
:
- 4.
Encode the Policy: For each attribute
i that is part of the access policy
, a corresponding ciphertext component
is generated. These components securely embed the shares of the secret
s according to the LSSS representation of the policy. For each attribute
i, this resembles
(This is a simplification; in an LSSS, each corresponds to a row in the policy matrix and involves more complex calculations, but the core idea is binding the attribute to the secret s).
The final ciphertext
consists of the access policy
and all generated components:
2.3.4. Decryption
A user with private key can attempt to decrypt a ciphertext . The process is successful only if the user’s attributes A satisfy the ciphertext’s access policy .
The ‘Decrypt(SK, CT)’ algorithm involves the following steps:
- 1.
Policy Check: First, the algorithm determines if the attributes A in the user’s key satisfy the policy in the ciphertext . If not, decryption fails immediately.
- 2.
Reconstruct the Blinding Factor: If the policy is satisfied, the user can use a specific subset of their attribute key components that corresponds to the attributes needed to fulfil the policy. Through a series of pairing operations involving their key components () and the ciphertext components (), the user reconstructs the original blinding factor .
The core mathematical step involves combining the components in such a way that cancels out the user’s secret
t and the policy’s secret shares, leaving only the required term. A simplified view of the final pairing result is
The denominator, representing the pairings of attribute components, is calculated using constants derived from the LSSS matrix to correctly combine the shares of s and cancel out the term.
- 3.
Recover the Message: Once the blinding factor
has been successfully reconstructed, recovering the original message involves simple division:
If a user’s attributes do not satisfy the policy, they will not have the necessary set of components to correctly run the reconstruction algorithm. The mathematical operations will not produce the correct blinding factor, and the result will be garbage data instead of the original message M.
2.3.5. The Collusion Resistance Mechanism
A collusion attack occurs when multiple users pool their private keys to decrypt a ciphertext that none of them could decrypt individually. For example, User 1 with attribute {"doctor"} and User 2 with attribute {"cardiology"} might try to combine their keys to satisfy an access policy of "doctor" AND "cardiology". The key structure of the tkn20 scheme makes this computationally infeasible.
The security comes from the fact that each user’s key is randomized with a differentsecret. Let us analyze the keys of two distinct users.
User 1 (attributes
) is assigned a random secret
. Their private key
is
User 2 (attributes
) is assigned a random secret
. Their private key
is
Since the KA chooses secrets randomly, it is overwhelmingly likely that .
During decryption, pairing-based cryptography is used to check if the attributes satisfy the policy. This process involves pairing operations that must cancel out certain secret terms in the exponent to reconstruct a blinding factor. For this to succeed, all attribute key components used in the decryption equation must be derived from the same exponent.
If the colluding users attempt to mix their key components, they would be using from User 1 and from User 2. The decryption algorithm, which expects all attribute components to be raised to the power of a single t, will fail. The mathematical checks will not reach validation because the underlying exponents ( and ) are different. There is no known algebraic operation that allows attackers to transform and into a valid set for some consistent without knowing and , which are secret.
2.4. Covercrypt Overview
Covercrypt is an attribute-based key encapsulation mechanism (KEM) designed to enable fine-grained access control, privacy of access policies, hybrid (classical + post-quantum) security, and traceability [
20]. It supports Boolean combinations—“AND” and “OR”—over multi-dimensional attributes (e.g., “Department::Sales AND Country::FR”). Ciphertexts are tagged with a set of target attributes, and users hold decryption keys tied to certain attribute sets.
Covercrypt operates through four intertwined phases, namely master setup, user key generation, encryption, and decryption, elegantly combining classical and post-quantum KEMs under an attribute-based paradigm. In the setup phase, the system defines a complete universe of “rights”; each right corresponds to a specific combination of attributes drawn from predefined dimensions, such as department, country, or rank. For each possible right, the authority generates an independent key pair using a KEM (e.g., X25519 or Kyber). These sub-key pairs collectively form a master public key, while the secret halves form the master secret key.
The encryption phase begins with the encryptor defining an access policy and similarly converting it into an explicit right set. Then, for each right in this set, the corresponding public key is used to perform KEM encapsulation, yielding a ciphertext component and a shared secret . A single random seed S is drawn and masked against each to generate . All pairs , together with a consistency tag, form the encryption header. Finally, a symmetric key is derived from S, which is used to encrypt the actual message payload following the KEM-DEM paradigm.
In decryption, the user iterates through their secret sub-keys, testing each one against the corresponding ciphertext component. For each right candidate a, they attempt to restore via decapsulation, recover S using , and verify the consistency tag. Once a matching right is found, the correct symmetric key is derived and used to decrypt the payload. This “early abort” process preserves policy privacy and efficiency.
To support post-quantum security, Covercrypt constructs each right’s KEM in a hybrid fashion: combining a classical scheme with a PQ scheme ensures security as long as at least one underlying primitive remains secure. Since the scheme is modular, any new KEM can be plugged in without altering the overall structure. Additionally, Covercrypt embeds a traceable ElGamal KEM (TKEM) into its hybrid AB-KEMAC. Each user receives a unique secret share enabling decrypt, and any session key successfully recovered can be cryptographically tied back to the specific user key used—without revealing any identity during standard operation.
During user key generation, the key-generating entity takes a user policy, expressed as a Boolean formula over attributes, and converts it into a disjunctive set of rights that satisfy the policy. Every right in this expansion corresponds to one of the subkeys in the master secret key, which are then securely packaged and issued to the user.
The algorithm is explained in detail in the following subsections, in accordance with [
34].
2.4.1. Setup
Let be the set of rights and t a threshold for traceability. The security parameter is denoted by . The setup is as follows:
- 1.
Sample for , and set .
- 2.
Sample
and define
with the constraint that
.
- 3.
Initialize the set of user identities:
- 4.
Define the tracing secret key:
- 5.
Define the tracing public key:
- 6.
Initialize the set of users’ secret keys that show their permissions:
- 7.
For each right with index i in ,
- 7.1.
Sample , and
- 7.2.
- 7.3.
The global public key is
and the master secret key is
2.4.2. User Key Generation
Given a username U, a set Y of rights assigned to U, and the master secret key , the key generation procedure proceeds as follows:
- 1.
Parse the master secret key:
- 2.
Sample a random tuple
such that
and set the user’s secret identifier:
- 3.
Define the user’s secret key:
- 4.
Update the tracing secret key by appending to the identity set .
- 5.
Update the master secret key by appending to the permission set .
2.4.3. Encryption
Given a set X of rights and the public key , the encryption algorithm proceeds as follows:
- 1.
- 2.
Let
denote the key space of
, and sample
- 3.
Set
where
is a hash function mapping into
.
- 4.
For each index
, compute
- 5.
Compute
where
is a hash function mapping into
-bit strings.
- 6.
For each index
, compute
- 7.
- 8.
Compute the final encapsulated output:
where
is a hash function mapping into
-bit strings.
The resulting ciphertext is
and it encapsulates the key
K.
2.4.4. Decryption
Given a user’s secret key and a ciphertext , the decryption algorithm proceeds as follows:
- 1.
Parse the user secret key:
- 2.
- 3.
For each index i such that is in , and for each j such that , do the following:
- 3.1.
- 3.2.
- 3.3.
- 3.4.
- 3.5.
If both checks pass, return
and terminate the algorithm.
- 4.
If no valid pair leads to successful decryption, return NULL.
2.5. Covercrypt and CP-ABE Use Case Example
To illustrate Covercrypt’s operation, consider a simplified three-axis attribute model as demonstrated in the Covercrypt reference implementation [
22]:
Security: {None, Medium, High}
Country: {France, Germany, UK}
Project: {X, Y}
This configuration yields a total of possible attribute combinations, referred to as rights. Moreover, indicates the possibility of omitting one axis.
To complement the Covercrypt illustration, the operation of ciphertext-policy attribute-based encryption (CP-ABE) using the CIRCL scheme is also detailed, employing the same simplified three-axis attribute model: Security, Country, and Project.
In Covercrypt, the authority enumerates all 48 rights and invokes generate_master_keys(), generating a hybrid KEM key pair (classical + Kyber) for each coordinate. These subkeys collectively form the master public key (MPK) and the master secret key (MSK).
In CP-ABE, the authority generates a single set of system keys: public parameters and a master secret key.
Suppose that Alice requests access under the policy
Upon request, Alice is issued the corresponding secret subkey for the coordinate (Medium, France, Y). Additionally, she is issued with subkeys corresponding to each subset within the set of attributes included in conjunction. Summing up, she receives the following keys:
,
,
,
,
,
,
,
.
Suppose that Carol requests access under the policy
Upon request, Carol is issued the corresponding secret subkey for the single coordinate
. However, because the Project dimension is not specified, Carol is also issued additional keys derived from the original policy:
and
. Similarly to Alice, she is also issued with subkeys corresponding to each subset within the set of attributes included in both conjunctions. Summing up, she receives the following keys:
,
,
,
,
,
,
,
,
,
,
,
.
In CIRCL, the authority utilizes the MSK to compute and issue one single, compact secret key: to Alice or to Carol. These are cryptographically bound to their full sets of attributes. Crucially, the size of this key is dependent on the number of attributes that they possess and not the total number of rights in the system.
Bob wishes to encrypt a message under the policy
Since the Project dimension is unspecified in both conjunctions contained in the alternative, and Security is not used in the latter, Bob omits them and uses the following two rights to encrypt the symmetric key: and . For each, he performs hybrid KEM encapsulation:
- 1.
- 2.
Bob draws a single random seed S, masks it as , and constructs the encrypted header with a consistency tag. The payload is symmetrically encrypted under S using AES-GCM under the KEM-DEM framework.
In CP-ABE, Bob defines the access policy, which is then embedded within the ciphertext. Using the public parameters, Bob encrypts the symmetric key for the message under this policy, producing the ciphertext. The size of this ciphertext is primarily determined by the complexity of the access policy (the number of attributes and logical gates), independently of the total number of users or possible rights.
Alice, possessing only keys derived from the subkey, finds no matching right, and her decryption attempt fails.
In contrast, Carol holds both , -) subkeys. She attempts decryption sequentially:
- 1.
She applies decapsulation with , recovers S, verifies the tag, and decrypts the payload.
- 2.
The process halts immediately upon success, exemplifying the early abortmechanism.
For comparison, in CP-ABE, Alice similarly attempts to decrypt the using her secret key . Since Alice’s attribute does not satisfy the policy requirement , she does not possess the private key corresponding to attribute and is unable to succeed during the initial pairing check.
Carol, on the other hand, possesses a key derived from the following attributes:
so Carol’s attribute set satisfies the policy. Consequently, a single, non-iterative decryption operation succeeds, allowing Carol to recover the symmetric key and decrypt the message payload.
2.6. Formal Comparison of Security Models and Assumptions
The security of the CIRCL implementation (based on the tkn20 scheme) relies on the hardness of the Decisional Bilinear Diffie–Hellman (DBDH) problem over the BLS12-381 elliptic curve. This is a classical pairing-based assumption, which is mathematically robust but fundamentally vulnerable to Shor’s algorithm on a sufficiently powerful quantum computer.
In contrast, Covercrypt is capable of employing a hybrid security model. It layers classical elliptic curve cryptography (ECC) with Lattice-based primitives, specifically variants of the NIST-standardized ML-KEM (Kyber). The formal security of Covercrypt is maintained as long as at least one of the underlying mathematical problems (discrete logarithm or Learning With Errors—LWE) remains computationally hard.
Both schemes provide formal proofs for IND-CCA (Indistinguishability under Adaptive Chosen Ciphertext Attack) security [
34,
35]. Both Covercrypt and CIRCL achieve collusion resistance through the user-specific randomization of private keys. Additionally, Covercrypt integrates a traceable KEM, allowing for the forensic attribution of leaked keys—a feature not natively present in the evaluated CIRCL implementation.
CIRCL includes the access policy in the ciphertext metadata in plaintext. This allows an adversary to perform traffic analysis by inferring data sensitivity from the visible policy structure. In contrast, Covercrypt natively supports hidden access policies. The access policy is embedded within the encapsulation header, preventing unauthorized actors from learning who the intended recipients are or which attributes are required for decryption. The comparison is presented in
Table 1.
4. Conclusions
This comparative performance analysis between the pairing-based CP-ABE scheme CIRCL and the hybrid post-quantum KEMAC Covercrypt provides critical insights for implementing data-centric security (DCS) across the diverse operational spectrum of military Internet of Things (IoT) environments. Our findings affirm that no single scheme offers a universal solution; rather, the optimal cryptographic choice is dictated by scenario-specific constraints related to scale, bandwidth, and security horizons. The quantitative findings reveal a critical dichotomy in the architectural suitability of these schemes. The pairing-based CIRCL implementation demonstrates superior scalability in dynamic environments, characterized by a constant-time master key setup phase () and linear scalability with respect to user attributes. Conversely, the Covercrypt scheme, while offering robust post-quantum security and a constant ciphertext size—a decisive advantage for low-bandwidth tactical links—suffers from exponential setup complexity () relative to the attribute universe size. This exponential cost renders Covercrypt operationally prohibitive for high-dimensional attribute spaces typical of large-scale coalition networks but ideal for the static, defined ontologies of tactical edge deployments. Node mobility and the “dynamic join-and-leave” behavior of tactical units require high agility from the key authority. CIRCL’s constant-time setup () and efficient key issuance allow for the immediate onboarding of new coalition partners or retasked units. Covercrypt’s structural rigidity, caused by the exponential cost of modifying the attribute universe (), may limit its use in highly fluid scenarios where new mission-specific attributes must be introduced frequently. This report concludes that no single cryptographic primitive suffices for the entire spectrum of special IoT applications. Instead, a split-horizon deployment strategy is recommended: utilizing pairing-based CP-ABE for the scalable, dynamic operational core and deploying hybrid KEMAC solutions at the tactical edge, where bandwidth efficiency and quantum resilience are paramount. This synthesis provides a roadmap for network planners to balance the competing demands of computational latency, communication overhead, and long-term cryptographic assurance.
The fundamental performance disparity arises from the architectural differences in managing the attribute universe ():
CIRCLexhibits superior scalability and agility for the key authority. Its constant complexity for the phase and compact public parameters () are essential in supporting a high-dimensional or rapidly evolving attribute space. Crucially, CIRCL’s architecture is inherently flexible, accommodating the frequent addition of new attributes in enterprise scenarios without requiring the costly and time-consuming recalculation of the central .
Covercrypt’s exponential complexity for is a severe bottleneck for large deployments, resulting in an unwieldy (e.g., ∼98 MB for structure size ). Furthermore, any change to the attribute universe—even adding a single new attribute or axis—necessitates the complete regeneration and distribution of the , rendering it structurally rigid for broad enterprise adoption.
The data imply a rigid operational doctrine for Covercrypt. The exponential cost of setup means that attributes cannot be treated as tags. In a CIRCL system, a user might tag a document with “Date: 2025-11-22” and “Coordinates: 34.55,12.33”. In Covercrypt, creating attributes for every date or coordinate is impossible as it would explode the universe size. Covercrypt enforces coarser granularity in access control. Access must be defined by broad categories (Role, Region) rather than fine-grained metadata. The tsk (tracing secret key) mechanism in Covercrypt offers an operational advantage. In standard CP-ABE, keys are often shared anonymously. In Covercrypt, the mathematical embedding of the user identity within the key encapsulation allows for forensic attribution. This feature is critical for zero-trust architectures. It moves the trust boundary from “possession of the device” to “accountability of the actor”. Covercrypt natively supports hidden access policies. The ciphertext does not reveal who is allowed to read it (unless they can decrypt it). In contrast, standard CP-ABE (CIRCL) often includes the policy structure in plaintext (metadata) to allow the decryption algorithm to function. Hiding the policy prevents traffic analysis. An adversary capturing encrypted packets cannot distinguish between a “general broadcast” and a “top secret strike order”, preventing them from inferring imminent operations based on the target audience of the messages. It should be noted that a hidden access policy feature can be achieved in CP-ABE scenarios by using homomorphic encryption. In terms of runtime metrics, CIRCL demonstrated decryption throughput that was roughly 300% faster than in Covercrypt’s post-quantum mode, making it the clear choice for latency-sensitive applications. Conversely, Covercrypt’s design provides a significant advantage in terms of communication overhead, achieving a constant, minimal ciphertext size (∼883 bytes for PQ mode) compared to the growing, higher overhead of CIRCL (∼4083 bytes for 6 attributes).
The analysis leads to distinct recommendations for the two scenarios.
CIRCL for Scalability and Real-Time Control (CORP-NET): The classical pairing-based approach is optimal for high-scale, corporate, or federated networks (Scenario I). Its fast key generation and high decryption throughput are paramount in managing a large user base and ensuring a responsive experience. While lacking native post-quantum security (PQS), this vulnerability can be successfully mitigated by adopting PQS protocols for data transit within the high-bandwidth network backbone, effectively layering security without sacrificing performance.
Covercrypt for Communication Efficiency and PQS at the Edge (TEN): The KEMAC-based approach is ideally suited for tactical edge networks (Scenario II). The constant, minimal ciphertext overhead is a critical enabler for severely constrained radio links, offering a typical reduction in data transfer compared to CIRCL. Furthermore, its native hybrid Post-Quantum capabilities and policy privacy are non-negotiable in this high-threat environment. Relying on DCS encryption as the sole cryptographic barrier is crucial here, as introducing any additional protocols would overwhelm the already constrained bandwidth.
This comparative performance analysis confirms that no single cryptographic scheme provides a universal solution for the entire spectrum of IoT environments. Instead, the choice must be dictated by specific operational constraints related to the network scale, available bandwidth, and required security horizon.
It is important to acknowledge the inherent flexibility of the CP-ABE attribute definition, exemplified by the CIRCL implementation, which provides additional operational merits even for tactical networks. The creation of flexible attribute values allows for integration with real-time operational parameters.
User Revocation and Future Encryption: By concatenating attributes with precise timestamps, the system can effectively implement time-bound policies, enabling immediate user revocation (by withholding future keys) and allowing data senders to encrypt messages that can only be decrypted after a specific point in time.
Dynamic Policy Tagging: Attributes can be dynamically generated based on a device’s current state, such as its location (e.g., map grid coordinates) or operational status. This enables highly reactive access control, critical for emergency situations where data access must immediately align with dynamic, rapidly changing geographical contexts.
While the need for post-quantum security strongly encourages the adoption of schemes like Covercrypt, the current, prohibitive cost of its phase severely restricts its practical utility in narrow, low-scale attribute universes typical of tactical deployments. For large-scale enterprise environments, CP-ABE schemes based on bilinear pairings (CIRCL) remain the more viable and agile choice until a comparably efficient post-quantum CP-ABE solution with constant-time becomes widely available.
Based on the experimental results, the following guidance for system architects is proposed. For large-scale, dynamic enterprise networks, pairing-based CP-ABE is the recommended choice. Its constant-time setup and faster decryption throughput are essential in managing thousands of devices with minimal latency, outweighing the lack of native post-quantum resistance in high-bandwidth backbone environments. Conversely, for tactical edge networks characterized by severely constrained radio links and high threat levels, the hybrid KEMAC approach is the superior enabler for data-centric security. Despite its exponential setup complexity, Covercrypt’s constant and smaller ciphertext overhead is paramount for bandwidth conservation, while its native post-quantum security and hidden access policies are non-negotiable in protecting long-term military intelligence against emerging quantum threats.
Ultimately, a split-horizon deployment strategy is recommended: utilizing the scalability of CIRCL for the operational core and the communication efficiency and quantum resilience of Covercrypt for the tactical edge. A binary choice between CIRCL and Covercrypt is not the end of the road. Several emerging frameworks offer middle-ground solutions. The current study assumes a single key authority (KA), which is a single point of failure and a bottleneck. Future research should benchmark Lewko-Waters MA-ABE [
40]. This allows different authorities (e.g., US-DoD, UK-MoD, NATO-HQ) to issue attributes independently. A user can decrypt data if they possess “US-TopSecret” AND “NATO-Mission-X”, without the US and NATO sharing their master keys. This is the “holy grail” for coalition interoperability. Pure Lattice ABE schemes (e.g., BGG+) should also be investigated. These offer full quantum resistance for both the key and the policy logic but historically suffer from massive key sizes (megabytes). Benchmarking these on modern hardware would determine their viability for the considered scenarios.