Abstract
Optimistic Fair Exchange protocol was designed for two parties to exchange in a fair way where an arbitrator always remains offline and will be referred only if any dispute happens. There are various optimistic fair exchange protocols with different security properties in the literature. Most of the optimistic fair exchange protocols satisfy resolution ambiguity where a signature signed by the signer is computational indistinguishable from the one resolved by the arbitrator. Huang et al. proposed the first generic framework for accountable optimistic fair exchange protocol in the random oracle model where it possesses resolution ambiguity and is able to reveal the actual signer when needed. Ganjavi et al. later proposed the first generic framework in the standard model. In this paper, we propose a new generic framework for accountable optimistic fair exchange protocol in the standard model using ordinary signature, convertible undeniable signature, and ring signature scheme as the underlying building blocks. We also provide an instantiation using our proposed generic framework to obtain an efficient pairing-based accountable optimistic fair exchange protocol with short signature.
1. Introduction
A fair exchange protocol was first designed to overcome the issue of fairness during an exchange between two parties such as contract signing [1,2], digital exchange [3], certified mail [4,5,6], etc. It is widely accepted that at the end of the exchange protocol, both parties have either received their expected items or none of them have received anything. There are two types of fair exchange protocols, namely, protocols that involve the arbitrator and protocols that do not involve the arbitrator [7]. Protocol that involve an arbitrator can be further divided into three types, namely, inline arbitrator protocol [8,9], online arbitrator protocol [10,11], and offline arbitrator protocol [12,13,14]. In 1997, the offline arbitrator protocol, which is also known as optimistic fair exchange (OFE) protocol, was introduced by Asokan et al. [12] to overcome the disadvantage of the inline and online arbitrator protocols, where the arbitrator is required to always remain online. At the same time, both parties can never exchange a secret message in a fair manner without leaking some information to the arbitrator. In OFE protocol, the arbitrator always remains offline and is called for resolution if and only if any dispute happens (e.g., one of the parties is cheating or the communication channel is interrupted). Asokan et al.’s OFE protocol was later broken and formally redefined by Dodis and Reyzin [13].
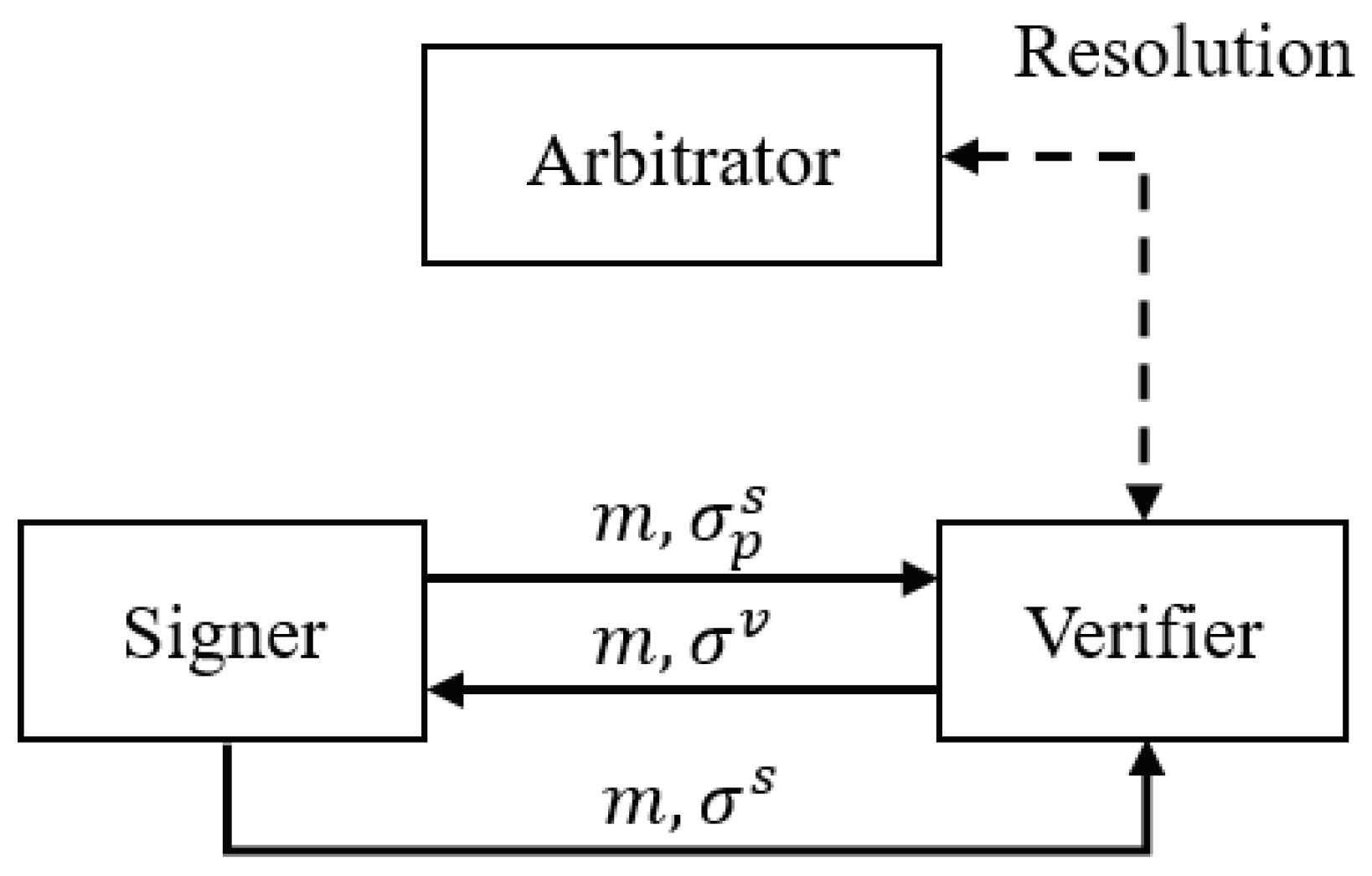
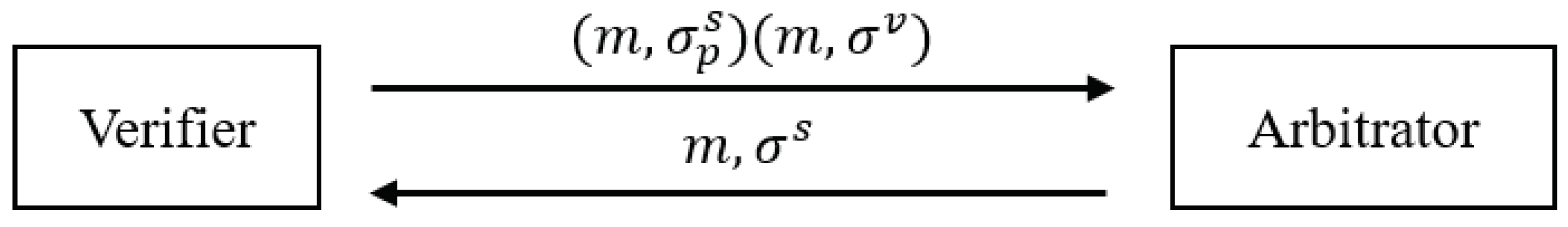
For the rest of the paper, the notion of fair exchange protocol is generally referred to as fair exchange protocol for digital data. Figure 1 illustrates the OFE protocol. At first, the signer generates a message and partial signature pair and sends to the verifier. The verifier then checks the validity of and returns to the signer. If everything goes well, the signer will reply to the verifier, and the protocol ends. However, if a dispute happens where the verifier sent to the signer, but the signer did not reply back to the verifier, the verifier can contact the arbitrator to resolve the issue. Figure 2 illustrates the resolution protocol. During the resolution, the verifier first sends and to the arbitrator. Once the arbitrator verifies the validity, the arbitrator resolves into and returns back to the verifier.
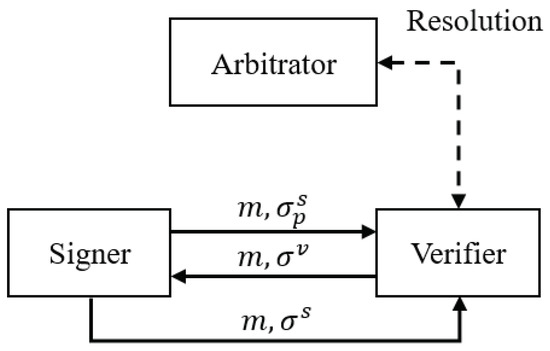
Figure 1.
Optimistic Fair Exchange Protocol.
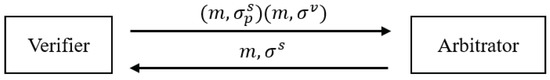
Figure 2.
Resolution Protocol.
As the partial signature is publicly verifiable and non-repudiable, may not be completely useless to the verifier as evidently represents the signer’s commitment. In this case, an unfair situation may occur for the signer if the verifier does not send out the full signature . Suppose that Bob received Alice’s as an offer, Bob may show to Alice’s competitor, and ask for a better offer. If there is a better offer, then Bob may stop running the protocol with Alice which indicates that he is not willing to negotiate, and instead Bob carries out a new run with a better dealer. Bob can repeat the same steps until the best dealer is found. This is undesirable since a fair negotiation is expected. Therefore, the notion of ambiguous optimistic fair exchange (AOFE) was proposed by Huang et al. [15] to solve the unfair situation above. In AOFE protocol, is non-transferable. More precisely, Bob has the ability to issue partial signatures that are computationally indistinguishable from those issued by Alice. Hence, the verifier will not be able to use the signer’s as evidence of the signer being involved in the exchange protocol.
Although AOFE protocol has managed to solve the issue of the verifier in getting a better offer, in some cases, the parties involved in the exchange should remain anonymous before the exchange has been done. For example, in the event that Apple engages Intel to sign a contract that terminates their agreement. This information can be very valuable to third parties such as stockbrokers or other companies.
In order to overcome the above issue, the notion of perfect ambiguous optimistic fair exchange (PAOFE) was proposed by Wang et al. [16]. PAOFE was constructed by combining AOFE and public key encryption (PKE). It guarantees that leaks no information about the signer nor the verifier. Although the privacy of the involved parties is protected in a normal run of the PAOFE protocol, the arbitrator can actually gain knowledge while the dispute occurs, when the arbitrator is requested to resolve it. It is very undesirable that in some sensitive applications such as contract signing, where information leakage is not desired at all, the arbitrator is requested to resolve the dispute. Hence, the notion of privacy-preserving optimistic fair exchange (OFE) was proposed by Huang et al. [17] where does not leak any information about the signer and the verifier even after the resolution has been executed by the arbitrator. Later, a generic framework for OFE protocols was proposed by Guo et al. [18] using tag-based public key encryption, ordinary signature, and one-time signature scheme.
Based on the above reviews from the notion of ordinary OFE to OFE, it shows that can be classified into two types, namely, the actual signature generated by the signer and the resolved signature generated by the arbitrator. An OFE protocol should possess the resolution ambiguity where the actual signature and resolved signature are both computational indistinguishable. However, there is actually a threat that the arbitrator can perform resolution without having any valid proof checking, or the arbitrator might be corrupted by the verifier. Hence, the notion of accountable OFE was proposed by Huang et al. [19] to identify who is the one responsible for , and thus it forces the arbitrator and the signer to behave honestly in generating .
1.1. Motivation
In cryptography, a scheme is said to be provably secure if breaking the scheme is as hard as breaking the polynomial time hard problem. If the scheme is provably secure using only mathematical hard problems, it is said to be provably secure in the standard model. As the standard model is hard to be achieved, the random oracle model was later introduced by Bellare and Rogaway [20]. An idealistic hash function is used in the random oracle model where the hash function can return any uniformly random value for any input. However, the random oracle model is not preferable during the security proof of a scheme due to the nature of the random oracle being a black-box function.
The first generic framework for accountable OFE protocol in the random oracle model was introduced by Huang et al. [19] where the partial signature is an ordinary signature, and the full signature consists of a partial signature, a random salt, and an undeniable signature along with an -signature. It possesses resolution ambiguity due to the anonymity of undeniable signature scheme and the witness indistinguishability of -signature. In order to construct the -signature in their generic framework, one must use the private key of undeniable signature scheme to generate a signature based on proofs of knowledge (SPK) [21]. Due to the property of SPK, one can generate a proof to either claim or deny an undeniable signature during the stage of revealing the original signer in an accountable OFE protocol. A SPK can be constructed by applying the Fiat-Shamir heuristic [22] to a proof of knowledge where it is a zero-knowledge protocol that allows the signer to convince the verifier that he knows a secret without leaking it [23]. It is known that a SPK that transformed by applying Fiat-Shamir heuristic is secure in the random oracle model [22].
Ganjavi et al. [24] then proposed the first provably secure generic framework for accountable OFE protocol in the standard model. In their generic framework, the partial signature is also an ordinary signature, and the full signature consists of a partial signature and a traceable ring signature. The notion of traceable ring signature was proposed by Fujisaki and Suzuki [25]. It is a variant of ring signature having the additional property to restrict the anonymity of the signer. It possesses two additional security properties, namely, traceability and exculpability. Traceability ensures that the identity of the signer can be traced as long as the signer signs two different messages with respect to the same tag, whereas exculpability ensures that the signer cannot be accused of signing twice with respect to the same tag. However, to the best of our knowledge, there are very few traceable ring signature schemes [25,26,27,28] which can be adopted in the construction of accountable OFE protocol following Ganjavi et al.’s proposed generic framework. Hence, it is desirable if there exists another generic framework which is provably secure in the standard model.
1.2. Contribution
In this paper, we present a full version of our recent work [29], proposing another generic framework for accountable OFE protocol. As shown in Table 1, the partial signature in our newly proposed generic framework is also an ordinary signature, and the full signature is an intermediate solution between Huang et al. and Ganjavi et al.’s generic frameworks, where it consists of a partial signature, a convertible undeniable signature, and a ring signature. There are two types of convertible undeniable signature scheme, namely, selectively convertible and universally convertible. Our generic framework requires the former which allows the signer to convert only a specific undeniable signature into a universally verifiable one. We show that the proposed generic framework is secure in the standard model under multi-user setting and chosen-key model as long as the underlying schemes satisfy certain security properties. We then exhibit an efficient pairing-based accountable OFE protocol with short signature as a concrete example following our proposed generic framework. Similar to Ganjavi et al.’s approach, we aim to construct an efficient accountable OFE protocol. We select the short signature scheme proposed by Boneh et al. [30] as the ordinary signature scheme with the combination of convertible undeniable signature scheme proposed by Li et al. [31] and ring signature scheme proposed by Shim [32], we manage to obtain an efficient pairing-based accountable OFE protocol with short signature. More specifically, the public and private key pair from Li et al.’s convertible undeniable signature scheme can be shared with Boneh et al.’s short signature scheme and Shim’s ring signature scheme, though the derived protocol is only provably secure in the random oracle model.

Table 1.
A comparison of the Generic Frameworks for Accountable optimistic fair exchange (OFE) Protocol.
1.3. Organisation of the Paper
The organisation of the paper is as follows. In Section 2, we recall the formal definitions and security models of accountable OFE protocol in the multi-user setting and chosen-key model. In Section 3, we provide a brief review on the notion of bilinear pairings. We also recall the definitions and security models of ordinary signature, convertible undeniable signature, and ring signature scheme which are served as the underlying building blocks for the proposed generic framework. In Section 4, we propose a new generic framework for accountable OFE protocol and provide its security analysis in the standard model. In Section 5, we provide an instantiation of an efficient pairing-based accountable OFE protocol with short signature. Finally, we conclude this paper in Section 6.
2. Definitions and Security Models of Accountable Optimistic Fair Exchange Protocol
In this section, we recall the formal definitions and security models of accountable OFE protocol in the muilti-user setting and chosen-key model which formalised by Huang et al. [19]. The security model of OFE protocol is setup-driven if the initial key registration needs to be done between the signer and the arbitrator, and the model is setup-free if that is not required. Since most of the existing exchange protocols consider more than one signer in the system, an OFE protocol should be applicable to multi-user setting, but items are exchanged between one signer and one verifier. More precisely, a multi-user setting OFE protocol consists of many signers and many verifiers along with only one arbitrator [33]. As previous works only considered the certified-key model, Huang et al. [14] then proposed a secure OFE protocol in the multi-user setting and chosen-key model. In contrast to the certified-key model, the adversary in chosen-key model is able to make queries with respect to the public key even without showing the knowledge of the private key.
2.1. Accountable OFE Protocol
An accountable OFE protocol consists of the following algorithms:
- : On input a security parameter , it outputs a public parameter .
- : On input , it generates an arbitrator’s public and private key pair ().
- : On input , it generates a user’s public and private key pair ().
- : On input a message m and ), it generates a partial signature .
- : On input (), it validates () and outputs if is valid on or otherwise.
- : On input (), it generates a full signature .
- : On input (), it validates () under () and outputs if is valid or otherwise.
- : On input (), it resolves by first checking its validity. If is valid on , it generates a full signature or outputs otherwise.
- : On input (), it generates an arbitrator proof that can claim or deny whether was generated by using .
- : On input (), it generates a user proof that can claim or deny whether was generated by using .
- : On input (), it first validates under . It then outputs if can prove is generated by the algorithm or if is generated by the algorithm . Otherwise, it outputs which indicates is invalid and it cannot be opened.
Correctness: The following algorithms will always output “1" if is generated correctly. If is a valid on and is generated correctly, the algorithm will always output either or .
2.2. Accessible Oracles
The following oracles are all the accessible oracles that define for an adversary in the accountable OFE protocol.
- Partial Sign Oracle : On input , it runs and returns as a partial signature.
- Full Sign Oracle : On input , it runs and returns as a full signature.
- Resolution Oracle : On input , it runs and returns as a resolved signature.
- Arbitrator Prove Oracle : On input under , it runs and returns as an arbitrator proof.
- User Prove Oracle : On input under , it runs and returns as a user proof.
2.3. Security Properties
An accountable OFE protocol possesses resolution ambiguity, accountability, security against signers, security against verifiers, and security against arbitrator. Its security models in the multi-user setting and chosen-key model are defined as the game between a probabilistic polynomial time (PPT) adversary and a challenger .
2.3.1. Resolution Ambiguity
A full signature generated by the signer or resolved by the arbitrator should be computationally indistinguishable. Note that this security model is referred from the transparent third party property as defined by [19].
- Phase 1: runs and . then passes to .
- Phase 2: can make queries to all oracles defined in Section 2.2. At the end, outputs a challenge message and partial signature pair with the restriction that .
- Phase 3: picks a random bit and generates a challenge signature . If , . Otherwise, .
- Phase 4: Once receives , can still continue to make queries to all oracles with the restriction that has never been queries to or . At the end, outputs the guess . wins the game if .
Definition 1.
An OFE protocol is -resolution ambiguous if no PPT can have success probability more than in its game with at most queries to , queries to , queries to , queries to , and queries to in time t.
2.3.2. Accountability
An OFE protocol possesses accountability if it satisfies three types of accountability as follows [19]:
- Type I: It is impossible for a dishonest signer to produce a full signature that can be proven as an output of the algorithm .
- -
- Phase 1: runs and . then passes to .
- -
- Phase 2: can make queries to all oracles defined in Section 2.2. At the end, chooses a challenge user’s public key and passes it to .
- -
- Phase 3: continues to make queries to and only as does not know .
- -
- Phase 4: outputs a challenge message and signature pair that is valid on and a proof with the restriction that is not generated from . wins the game if
Definition 2.An OFE protocol is -type I accountable if no PPT can have success probability more than ε in its game with at most queries to , queries to , queries to , queries to , and queries to in time t. - Type II: It is impossible for a dishonest arbitrator to resolve a full signature that can be proven as an output of the algorithm .
- -
- Phase 1: chooses a challenge arbitrator’s public key and passes it to .
- -
- Phase 2: can make queries to all oracles defined in Section 2.2 except and due to does not have the knowledge of .
- -
- Phase 3: outputs a valid on and a proof with the restriction that is not generated from . wins the game if and only if
Definition 3.An OFE protocol is -type II accountable if no PPT can have success probability more than ε in its game with at most queries to , queries to , and queries to in time t. - Type III: It is impossible for the signer and the arbitrator to both claim or deny a valid full signature .
- -
- Phase 1: runs . is then given to run both and .
- -
- Phase 2: outputs a valid on and two proofs . wins the game if and only if either one of the following statements holds:
- is both claimed by the signer and the arbitrator. Such that
- is both denied by the signer and the arbitrator. Such that
Definition 4.An OFE is -type III accountable if no PPT can have success probability more than ε in its game in time t.
2.3.3. Security against Signers
It is impossible for a dishonest signer to produce a valid partial signature which cannot be resolved by the arbitrator using [24].
- Phase 1: runs and passes to .
- Phase 2: can make queries to .
- Phase 3: outputs a challenge message and partial signature pair on . wins the game if .
Definition 5.
An OFE protocol is -secure against signers if no PPT can have success probability more than ε in its game with at most queries to in time t.
2.3.4. Security against Verifiers
It is impossible for a dishonest verifier to produce a valid full signature without the assistance from the signer or the arbitrator. The security model is referred from [24]. Note that we allow to access as we want to simulate the scenario that a dishonest verifier can forge a full signature on either the signer or the arbitrator.
- Phase 1: first runs and both and . is then given .
- Phase 2: can make queries to , , and .
- Phase 3: outputs a challenge message and signature pair on with the restriction that is not generated from or . wins the game if .
Definition 6.
An OFE protocol is -secure against verifiers if no PPT can have success probability more than ε in its game with at most queries to , queries to , and queries to in time t.
2.3.5. Security against Arbitrator
It is impossible for a dishonest arbitrator to produce a valid without having the corresponding from the signer [24].
- Phase 1: runs and passes to .
- Phase 2: runs and sends to .
- Phase 3: can make queries to .
- Phase 4: outputs a challenge message and signature pair on with the restriction that has not been a query to . wins the game if .
Definition 7.
An OFE protocol is -secure against arbitrator if no PPT can have success probability more than ε in its game with at most queries to in time t.
2.3.6. Security in the Multi-User Setting and Chosen-Key Model
A secure OFE protocol in the multi-user setting and chosen-key model should satisfy the following properties, namely, security against signers, security against verifiers, and security against arbitrator as defined in Section 2.3.3, Section 2.3.4 and Section 2.3.5 respectively [33,34].
Definition 8.
An accountable OFE protocol is secure in the multi-user setting and chosen-key model if it is accountable, secure against signers, secure against verifiers, and secure against arbitrator.
3. Preliminaries
In this section, we first provide a brief review on the notion of bilinear pairings. We then review some variants of digital signature scheme such as ordinary signature, convertible undeniable signature, and ring signature scheme. We also review their respective security models.
3.1. Bilinear Pairings
Let be cyclic groups of prime order p and two generators and . The map is a bilinear map which satisfies the following properties [35]:
- Bilinearity: for all , , and , we have .
- Non-degeneracy: if is a generator of and , then is a generator of , which also implies .
- Computability: there exists an efficient algorithm to compute for all and .
3.2. Ordinary Signature Scheme
Ordinary signature is a publicly verifiable digital signature. The message and signature pair can be verified as long as the signer’s public key is known. It was formalised by Goldwasser et al. [36] with the following three algorithms:
- : On input security parameter , it outputs a public and private key pair .
- : On input a message and private key , it outputs an ordinary signature .
- : On input , it outputs if is valid and outputs otherwise.
Correctness. Every ordinary signature generated in a correct way is always accepted to be a valid signature, such that .
Unforgeability
Unforgeability ensures that there is no computational way to forge a valid ordinary signature on the public key . Its security model is defined as the following game between a probabilistic polynomial time (PPT) adversary and a challenge [36].
- Setup: runs , then is given .
- Queries: can query the Sign Oracle : On input a message m, it outputs a signature that is valid on .
- Output: At the end, is required to output a challenge message and signature pair that is valid on , with the restriction that has not been a query to before.
Definition 9.
An ordinary signature scheme is -existential unforgeable against chosen message attack (EUF-CMA) if no PPT can have success probability more than ε in its game with at most queries to in time t.
3.3. Convertible Undeniable Signature
An undeniable signature is a special featured digital signature proposed by Chaum and van Antwerpen [37] which is only verifiable with the help of the signer. Unlike ordinary digital signature, undeniable signature has a distinctive feature, i.e., without the help of the signer, the verifier will not be able to verify the validity of the undeniable signature. The notion of convertible undeniable signature was proposed by Boyar et al. [38] which is an extension of undeniable signature that allows the signer to transform an undeniable signature into a universally verifiable ordinary digital signature. There are two types of convertible undeniable signature, namely, selectively convertible and universally convertible. The selectively convertible undeniable signature allows the signer to convert only a specific undeniable signature into a universally verifiable one by releasing a token, and the universally convertible undeniable signature allows the signer to release a universal token that can publicly verify every undeniable signature. A convertible undeniable signature scheme has the following algorithms:
- : On input a security parameter, , outputs a signer public and private key pair ().
- : On input a message and a signer private key, , outputs an undeniable signature .
- : An interactive protocol that runs between the signer and the verifier on common input . The signer uses to check the validity of , the output is a non-transferable proof that shows is valid/invalid on .
- : On input , it computes a selective token which can be used to publicly verify on .
- : On input , it outputs if is an invalid token on . It outputs if is a valid signature and outputs otherwise.
Completeness and Soundness. Completeness can be defined as a valid (invalid) signature that can always be proven valid (invalid) and Soundness can be defined as a valid (invalid) signature that cannot be proven as invalid (valid). The following two cases describe their definitions:
- If is valid on , then
- Or else, if is invalid on , then
3.3.1. Unforgeability
The same as in Section 3.2, it implies the inability to forge an undeniable signature. Its security model is defined as the following game between a PPT and in the undeniable signature setting.
- Setup: runs , then is given .
- Queries: is allowed to make queries to the following oracles:
- -
- Sign Oracle : On input a message m, it outputs an undeniable signature that is valid on .
- -
- Confirmation/Disavowal Oracle : On input any message and signature pair , it runs the protocol with and outputs a non-transferable proof to show the validity of .
- -
- (For convertible schemes only) SConvert Oracle : On input a message and signature pair , it outputs a selective token .
- Output: At the end, is required to output a challenge message and undeniable signature pair , with the restriction that has not been a query to . If the scheme is convertible, must not have been queried to . wins the game if is valid on .
Definition 10.
An undeniable signature, convertible undeniable signature, or designated confirmer signature scheme is -EUF-CMA if no PPT can have success probability more than ε in its game with at most queries to , queries to , queries to , and queries to in time t.
3.3.2. Anonymity
The notion of anonymity was proposed by Galbraith and Mao [39]. This security property requires that given a valid message and signature pair and two possible signers’ public keys (), there is no computational way to decide who the real signer is. Huang et al. [40] later further studied the anonymity in order to cover the convertible schemes. Its security model is defined as the following game between a PPT and .
- Setup: first runs and and sends to .
- Queries I: Same as in Section 3.3.1.
- Output I: At some point, outputs a challenge message to request a challenge signature . If the scheme is deterministic, is restricted where it has not been submitted to during Queries I. responds by randomly choosing and generates a challenge signature that is valid on either or .
- Queries II: Once obtains , can continue making queries to the accessible oracles as in Queries I. If the scheme is deterministic, is restricted to be submitted to . An additional restriction is added where any in the equivalence class of is not allowed to submit to (and if the scheme is convertible).
- Output II: outputs a guess and wins the game if .
Definition 11.
An undeniable signature, convertible undeniable signature, or designated confirmer signature scheme is -anonymous if no PPT can have success probability more than in its game with at most queries to , queries to , queries to , and queries to in time t.
3.4. Ring Signature
Ring signature was introduced by Rivest et al. [41]. It is a group-oriented signature with the anonymity property where the signer can sign on behalf of a group of members, and the ring signature is publicly verifiable without revealing the actual signer. A ring signature scheme consists of the following three algorithms:
- : On input , it outputs a public and private key pair .
- : On input a message, a private key, and a list of public keys where with n members, it outputs a ring signature .
- : On input , it outputs if is valid and output otherwise.
Correctness. Every ring signature that generated in a correct way can always be accepted with the equation .
3.4.1. Unforgeability
This security property ensures that there is no computational way to forge a ring signature with only the knowledge of a list of public keys of n members. Its security model is defined as the following game between a PPT and [42].
- Setup: runs for n times to generate n public and private key pair , where n is the number of members. is given .
- Queries: can query the Sign Oracle : On input , where is a sub list of members within and e is a selected member. It then runs to produce a ring signature to .
- Output: At the end, is required to output a challenge message and ring signature pair on a challenge sub list of members with the restriction that has not been a query to before. wins the game if
Definition 12.
A ring signature scheme is -existential unforgeable against chosen subring attack (EUF-CSA) if no PPT can have success probability more than ε in its game with at most queries to in time t.
3.4.2. Anonymity
The definition of anonymity for ring signature scheme can be phrased in either a computational or an unconditional sense [43]. This security property requires that given a valid and two possible signers’ public keys (), there is no computational way to decide who the real signer is.
- Setup: Same as in Section 3.4.1.
- Queries: Same as in Section 3.4.1.
- Output: At the end, is required to output a challenge message and a sub list of members and two distinct indices such that . then chooses randomly and computes a challenge ring signature . is given and is required to output a guess . wins the game if .
Definition 13.
A ring signature scheme is -anonymous with respect to adversarially chosen keys if no PPT can have success probability more than ε in its game with at most queries to in time t.
4. Generic Transformation
4.1. Generic Framework
We propose a generic framework for accountable OFE protocol using ordinary signature, convertible undeniable signature, and ring signature scheme as the underlying building blocks. The partial signature is an ordinary signature, , and the full signature consists of a partial signature, a convertible undeniable signature, and a ring signature, . Let be an ordinary signature scheme, be a convertible undeniable signature scheme, and be a ring signature scheme. We need a hash function , where is the message space. An accountable OFE protocol consists of the following algorithms:
- : On input the security parameter , it generates the public parameters needed for the ordinary signature, convertible undeniable signature, and ring signature scheme.
- : On input , it runs and to compute an arbitrator public and private key pair .
- : On input , it runs , , and to compute a user public and private key pair .
- : On input a message and a signer private key , it runs and outputs a partial signature .
- : On input , it can validate by running . It outputs if is valid and outputs otherwise.
- : On input . Let . It runs and , where and outputs a full signature .
- : On input , it can verify by running and , where . Therefore, if and are valid, this algorithm outputs and otherwise.
- : On input , it first checks the validity of by running . It outputs if is invalid. Otherwise, it continues to compute . It then runs and , where and outputs a full signature
- : On input , it first runs to check its validity and continue if and only if it is valid. Then it computes and runs and outputs a proof . Otherwise, it outputs .
- : On input , it first runs to check its validity and continue if and only if it is valid. Then it computes and runs and outputs a proof . Otherwise, it outputs .
- : On input , it first runs to check its validity and continue if and only if it is valid. Otherwise, it outputs . It computes and parses in the following cases:
- -
- If , it runs . If , it outputs which indicates is originally generated by the arbitrator using . Otherwise, it outputs . If the output is , it means is invalid.
- -
- Else if , it runs . If , it outputs which indicates is originally generated by the signer using . Otherwise, it outputs . If the output is , it means is invalid.
Correctness. The correctness of our generic framework follows the correctness of the underlying ordinary signature, convertible undeniable signature, and ring signature scheme.
4.2. Security Analysis
In this subsection, we provide the security analysis on our proposed framework. The proof approach for resolution ambiguity and accountability are inspired by Huang et al. [19], and the proof approach for security against signers, security against verifiers, and security against arbitrator are inspired by Ganjavi et al. [24].
4.2.1. Resolution Ambiguity
Lemma 1.
Our proposed generic framework is resolution ambiguity if the underlying convertible undeniable signature scheme and ring signature scheme satisfy anonymity.
Proof.
As the full signature contains a partial signature, a convertible undeniable signature, and a ring signature , the resolution ambiguity follows the anonymity of the underlying convertible undeniable signature scheme and ring signature scheme. □
4.2.2. Type I Accountability
Lemma 2.
Our proposed generic framework is -type I accountable if the underlying convertible undeniable signature scheme is -EUF-CMA and complete and sound.
Proof.
Let be the PPT adversary which -breaks the type I accountability, we build a PPT algorithm which runs as a subroutine and -breaks the EUF-CMA and the completeness and soundness of the underlying convertible undeniable signature scheme with the success probability more than in its game with at most queries to , queries to , queries to , queries to , and queries to in time t.
- Phase 1: On input to , sets and passes to .
- Phase 2: can make queries to its accessible oracles defined in Section 2.2. At the end, runs to generate users’ private and public key pairs. then passes a challenge public key to .
- Phase 3: can make queries to the following oracles:
- -
- Resolution Oracle : On input , requests from convertible undeniable signature scheme’s on input , where . then requests from ring signature scheme’s on input , where and is the selected public key position in . Note that is generated with respectively. Finally, returns a signature to .
- -
- Arbitrator Prove Oracle : On input , requests a selective token on from convertible undeniable signature scheme’s on input , where . then returns an arbitrator proof .
- Phase 4: outputs a challenge message and signature pair that is valid on and a proof with the restriction that is not generated from . Note that be can either by or by .
Assume that wins the game because and is not generated from , there exist two possible cases:
- Case 1: is generated by using , so and hold.
- Case 2: is generated by using , but is not sound. Hence, and .
Hence, if takes as the output, breaks the EUF-CMA of convertible undeniable signature scheme in Case 1 and breaks the completeness and soundness of the underlying convertible undeniable signature scheme in Case 2. This shows that there exists a PPT which can either -break the EUF-CMA or the completeness and soundness of the underlying convertible undeniable signature scheme if there exists which can -break the type I accountability. This contradicts the EUF-CMA and the completeness and soundness of the underlying convertible undeniable signature scheme, hence our OFE protocol is type I accountable. □
4.2.3. Type II Accountability
Lemma 3.
Our generic framework is -type II accountable if the underlying convertible undeniable signature scheme is -EUF-CMA and complete and sound.
Proof.
Let be the PPT adversary which -breaks the type II accountability, we build a PPT algorithm which runs as a subroutine and -breaks the EUF-CMA and the completeness and soundness of the underlying convertible undeniable signature scheme with the success probability more than in its game with at most queries to , queries to , and queries to in time t.
- Phase 1: On input to , then passes to which then runs and passes to .
- Phase 2: can make queries to the following oracles for a selected :
- -
- Partial Sign Oracle : On input , requests a signature from ordinary signature scheme’s on input . then returns a partial signature .
- -
- Full Sign Oracle : On input , requests from convertible undeniable signature scheme’s on input , where . then requests from ring signature scheme’s on input , where and is the selected public key position in . Note that is generated with respectively.
- -
- User Prove Oracle : On input , requests a selective token on from convertible undeniable signature scheme’s on input , where . then returns a user proof .
- Phase 3: outputs a challenge message and signature pair that is valid on and a proof , with the restriction that is not generated from . Note that can either be the by or the by .
Assume that wins the game because and is not generated from , there exist two possible cases:
- Case 1: is generated by using , so and hold.
- Case 2: is generated by using , but is not sound. Therefore, and .
Hence, if takes as the output, breaks the EUF-CMA of convertible undeniable signature scheme in Case 1 and breaks the completeness and soundness of convertible undeniable signature scheme in Case 2. This shows that there exists a PPT that can either -break the EUF-CMA or the completeness and soundness of the underlying convertible undeniable signature scheme if there exists which can -break the type II accountability. This contradicts the EUF-CMA and the completeness and soundness of the underlying convertible undeniable signature scheme, hence our OFE protocol is type II accountable. □
4.2.4. Type III Accountability
Lemma 4.
Our proposed generic framework is -type III accountable if the underlying convertible undeniable signature scheme is -complete and sound.
Proof.
Let be the PPT adversary which -breaks the type III accountability, we build a PPT algorithm which runs as a subroutine and -breaks the completeness and soundness of the underlying convertible undeniable signature scheme with the success probability more than in its game in time t.
- Phase 1: On input to , then passes to which then runs and .
- Phase 2: outputs a challenge message and signature pair that is valid on and two proofs .
At the end of the game, takes as the output. breaks the completeness and soundness of the underlying convertible undeniable signature scheme if either one of the following statements holds:
- A valid on but
- A valid on but ∧
This shows that there exists a PPT which can -break the completeness and soundness of the underlying convertible undeniable signature if there exists which can -break the type III accountability with the success probability more than in its game in time t. This contradicts the completeness and soundness of the convertible undeniable signature scheme, hence our OFE protocol is type III accountable. □
4.2.5. Security against Signers
Lemma 5.
Our proposed generic framework is unconditionally secure against signers.
Proof.
The security against signers in our generic framework follows unconditionally as a full signature contains a partial signature, a convertible undeniable signature, and a ring signature, , the arbitrator can always convert to , by generating on and . □
4.2.6. Security against Verifiers
Lemma 6.
Our proposed generic framework is -secure against verifiers if the underlying convertible undeniable signature scheme is -EUF-CMA and ring signature scheme is -EUF-CSA.
Proof.
Let be the PPT adversary which -break the security against verifiers, we build a PPT algorithm which runs as a subroutine and -breaks the EUF-CMA of the underlying convertible undeniable signature scheme and the EUF-CSA of the underlying ring signature scheme with the success probability more than in its game with at most queries to and queries to in time , where is the time cost to generate a partial signature.
- Phase 1: On input two challenge public key pairs to , first runs . then chooses and sets and . is given .
- Phase 2: can make queries to the following oracles:
- -
- Partial Sign Oracle : On input , returns to .
- -
- Full Sign Oracle : On input , requests from convertible undeniable signature scheme’s on input , where . then requests from ring signature scheme’s on input , where and is the selected public key position in . Note that is generated with respectively. Finally, returns a signature to .
- -
- Resolution Oracle : This oracle is similar to above, but is generated with respectively, where is from convertible undeniable signature scheme’s on input and is from ring signature scheme’s on input where and is the selected public key position in .
- Phase 3: outputs a challenge message and signature pair , where with the restriction that is not generated from or .
At the end of the game, takes as the output where . breaks the EUF-CMA of the underlying convertible undeniable signature scheme if is valid on either or . also breaks the EUF-CSA of the underlying ring signature scheme if is valid on either or . Therefore, this shows that there exists a PPT which can -break the EUF-CMA of the underlying convertible undeniable signature scheme and EUF-CSA of the underlying ring signature scheme if there exists which can -break the security against verifiers with the success probability more than in its game with at most queries to and queries to in time . This contradicts the EUF-CMA of the underlying convertible undeniable signature scheme and the EUF-CSA of the underlying ring signature scheme, hence our OFE protocol is secure against verifiers. □
4.2.7. Security against Arbitrator
Lemma 7.
Our proposed generic framework is -secure against the arbitrator if the underlying ordinary signature scheme is -EUF-CMA.
Proof.
Let be the PPT adversary which -breaks the security against the arbitrator, we build a PPT algorithm which runs as a subroutine and -breaks the EUF-CMA of the underlying ordinary signature scheme with the success probability more than in its game with at most queries to in time t.
- Phase 1: On input a challenge public key to . first generates public parameters and passes to .
- Phase 2: then runs and sends to .
- Phase 3: can make queries to Partial Sign Oracle : On input , where requests a signature from ordinary signature scheme’s on input . returns a partial signature .
- Phase 4: outputs a challenge message and signature pair , where with the restriction that has not been queried to .
At the end of the game, takes as the output. breaks the EUF-CMA of the underlying ordinary signature scheme if . This shows that there exists a PPT which can -break the EUF-CMA of the underlying ordinary signature scheme if there exists which can -break the security against arbitrator with the success probability more than in its game with at most queries to in time t. This contradicts the EUF-CMA of the underlying ordinary signature scheme, hence our OFE protocol is secure against arbitrator. □
Theorem 1.
Our proposed generic framework is secure in the multi-user setting and chosen-key model.
Proof.
The proof follows directly from Lemmas 1–7. □
5. An Instantiation of Accountable Optimisitc Fair Exchange Protocol
The derived protocol is built from Boneh et al.’s short signature scheme [30], Li et al.’s convertible undeniable signature scheme [31], and Shim’s ring signature scheme [32], following our proposed generic framework. We first review the respective underlying schemes.
5.1. Boneh et al.’s Short Signature Scheme
The same public parameters is used following the definition as in Section 3.1, and is a hash function. The scheme consists of the following algorithms [30]:
- : It randomly picks and computes . It then returns a public and private key pair .
- : On input a message and a private key , it returns an ordinary signature .
- : On input , it checks whether . It outputs if is valid and otherwise.
5.2. Li et al.’s Convertible Undeniable Signature Scheme
The same public parameters as in Boneh et al.’s short signature scheme is used in this scheme with the following algorithms [31]:
- : It randomly picks to compute and . It outputs a public and private key pair .
- : On input a message and private key , it computes an undeniable signature .
- : Given a message and signature pair , it can confirm or deny with the following designated verifier non-interactive zero knowledge proof of knowledge :or
- : On input , it computes a converter .
- : On input , it first verifies by checking whether or not. If is valid, then it proceeds to validate by checking whether holds or not.
5.3. Shim’s Ring Signature Scheme
The same public parameters as in Boneh et al.’s short signature are used in this scheme with the following algorithms [32]:
- : For a user i, it randomly picks to compute . It outputs a public and private key pair .
- : Let be a list of users’ public keys with n members. On input a signer’s public and private key pair and a message , it first randomly chooses and computes for and . It then chooses a random salt and computes , whereFinally, it outputs a ring signature .
- : On input , where is a list of users’ public keys with n members. It first computes for . It then checks whether holds or not. If it holds, it outputs and otherwise.
5.4. The Derived Accountable Optimistic Fair Exchange Protocol
In order to reduce the key pair needed, we use the same approach as in the concrete protocol proposed by [19], where we utilise the public and private key pair from Li et al.’s convertible undeniable signature scheme to construct the ordinary signature and the ring signature. The signature in our protocol is short and it is more efficient in generating signature and proof as compared to Huang et al. and Ganjavi et al.’s concrete protocols. However, it takes longer to verify a signature due to the pairing-based setting, and this results in the derived protocol to be secure in the random oracle model only.
Let be Boneh et al.’s signature scheme, be Li et al.’s convertible undeniable signature scheme, and be Shim’s ring signature scheme. The derived accountable OFE protocol consists of the following algorithms:
- : On input , it generates , where ,, are cyclic groups of prime order q, and are two generators, and is a bilinear map. Let , , and , where is the message space. Finally, it outputs .
- : On input , it runs , where and . Note that will be used for ring signature later. Lastly, it returns an arbitrator public and private key pair .
- : On input , it runs , where and . Note that will be used for ordinary signature and ring signature later. Lastly, it returns a user public and private key pair .
- : On input , it runs to compute an ordinary signature, . It outputs a partial signature .
- : On input , it runs to check the validity by comparing . It returns if the equation holds and otherwise.
- : On input , it runs and continues if and only if is valid. Let , it runs to generate a convertible undeniable signature, . It then runs to generate a ring signature, . Let , it randomly chooses and computes . It then chooses a random salt and computes :Finally, it outputs a full signature where .
- : On input , it first runs and continues if and only if is valid. It then runs to verify . Let , it then computes and . It then checks whether holds or not. If it holds, it outputs and otherwise.
- : On input , it runs and continues if and only if is valid. Let , it runs to compute a convertible undeniable signature, . It then runs to generate a ring signature, . Let , it first randomly chooses and computes . It then chooses a random salt and computes :Finally, it outputs a full signature where .
- : On input , it first runs and continues if and only if is valid. Let , it runs to compute a proof . Otherwise, it outputs
- : On input , it first runs and continues if and only if is valid. Let , it runs to compute a proof . Otherwise, it outputs
- : On input , it runs and continues if and only if is valid. Let , it runs to verify , where
- -
- If , it first checks the validity of by running and outputs if is invalid. Otherwise, it proceeds to validate by running . If the equation holds, it means was signed by the arbitrator and outputs , otherwise it outputs .
- -
- If , it first checks the validity of by running and outputs if is invalid. Otherwise, it proceeds to validate by running . If the equation holds, it means was signed by the signer and outputs , otherwise it outputs .
Security Analysis
In this section, we show the derived protocol is secure in the multi-user setting and chosen-key model which follows from Theorem 1.
- Resolution Ambiguity: This property requires that the underlying convertible undeniable signature and ring signature scheme satisfy anonymous. The derived protocol is resolution ambiguous which follows Lemma 1, such that the underlying Li et al.’s convertible undeniable signature scheme [31] is proven invisible based on One-more Decisional Co-Tripartite-Diffie-Hellman (1m-DCTDH) in the random oracle model, where it is also well known that the invisibility and anonymity are equivalent as proven by Galbraith and Mao [39]. Besides, the underlying Shim’s ring signature scheme is unconditionally anonymous as shown by the author [32].
- Accountability: This property requires that the underlying convertible undeniable signature scheme satisfies EUF-CMA and completeness and soundness. The derived protocol is accountable which follows Lemmas 2–4, such that the underlying Li et al.’s convertible undeniable signature scheme [31] achieves EUF-CMA based on Computational co-Diffie-Hellman (Co-CDH) in the random oracle model. The completeness and soundness of Li et al.’s scheme is unconditionally satisfied as shown by the author.
- Security against Signers: This property is unconditionally satisfied which follows Lemma 5 as the generic framework follows the same construction as in Huang et al. [19] and Ganjavi et al. [24], such that the arbitrator can always convert a partial signature into a full signature by generating a convertible undeniable signature and ring signature.
- Security against Verifiers: This property requires that the underlying convertible undeniable signature and ring signature scheme satisfy EUF-CMA and EUF-CSA respectively. The derived protocol is secure against verifiers which follows Lemma 6, such that the underlying Li et al.’s convertible undeniable signature scheme [31] and Shim’s ring signature scheme [32] are both proven EUF-CMA and EUF-CSA respectively based on Co-CDH in the random oracle model.
- Security against Arbitrator: This property requires that the underlying ordinary signature scheme satisfies EUF-CMA. The derived protocol is secure against arbitrator which follows Lemma 7, such that the underlying Boneh et al.’s ordinary signature [30] acheives EUF-CMA based on Co-CDH in the random oracle model.
6. Conclusions
We proposed a generic framework to construct accountable OFE protocol in the multi-user setting and chosen-key model which is proven secure in the standard model by using the ordinary signature, convertible undeniable signature, and ring signature scheme as the underlying building blocks. We also provided a concrete instantiation of accountable OFE protocol based our proposed generic framework in the random oracle model.
Author Contributions
All the authors have contributed equally to this research work.
Funding
This work was supported by the Malaysia government’s Fundamental Research Grant Schemes (FRGS/1/2015/ICT04/MMU/03/5 and FRGS/1/2018/ICT04/MMU/01/1).
Conflicts of Interest
The authors declare no conflict of interest.
References
- Bao, F.; Wang, G.; Zhou, J.; Zhu, H. Analysis and Improvement of Micali’s Fair Contract Signing Protocol. In Information Security and Privacy; Wang, H., Pieprzyk, J., Varadharajan, V., Eds.; Springer: Berlin/Heidelberg, Germany, 2004; pp. 176–187. [Google Scholar]
- Ben-Or, M.; Goldreich, O.; Micali, S.; Rivest, R.L. A fair protocol for signing contracts. IEEE Trans. Inf. Theory 1990, 36, 40–46. [Google Scholar] [CrossRef]
- Park, J.M.; Chong, E.K.P.; Siegel, H.J. Constructing Fair-exchange Protocols for E-commerce via Distributed Computation of RSA Signatures. In Proceedings of the PODC ‘03 Twenty-Second Annual Symposium on Principles of Distributed Computing, Boston, MA, USA, 13–16 July 2003; ACM: New York, NY, USA, 2003; pp. 172–181. [Google Scholar] [CrossRef]
- Abadi, M.; Glew, N.; Horne, B.; Pinkas, B. Certified email with a light on-line trusted third party: Design and implementation. Int. World Wide Web Conf. 2002, 2, 387–395. [Google Scholar]
- Ateniese, G.; Nita-Rotaru, C. Stateless-Recipient Certified E-Mail System Based on Verifiable Encryption. In Topics in Cryptology—CT-RSA 2002; Preneel, B., Ed.; Springer: Berlin/Heidelberg, Germany, 2002; pp. 182–199. [Google Scholar]
- Imamoto, K.; Sakurai, K. A Certified E-mail System with Receiver’s Selective Usage of Delivery Authority. In Progress in Cryptology—INDOCRYPT 2002; Menezes, A., Sarkar, P., Eds.; Springer: Berlin/Heidelberg, Germany, 2002; pp. 326–338. [Google Scholar]
- AlOtaibi, A.; Aldabbas, H. A review of fair exchange protocols. Int. J. Comput. Netw. Commun. 2012, 4, 307. [Google Scholar] [CrossRef]
- Bahreman, A.; Tygar, J. Certified electronic mail. In Proceedings of the 1994 Network and Distributed System Security Symposium (NDSS 1994), New York, NY, USA, February 1994; pp. 3–19. [Google Scholar]
- Coffey, T.; Saidha, P.; Burrows, P. Analysing the Security of a Non-repudiation Communication Protocol with Mandatory Proof of Receipt. In Proceedings of the ISICT ‘03 1st International Symposium on Information and Communication Technologies, Dublin, Ireland, 24–26 September 2003; Trinity College Dublin: Dublin, Ireland, 2003; pp. 351–356. [Google Scholar]
- Cox, B.; Tygar, J.D.; Sirbu, M. NetBill Security and Transaction Protocol. In Proceedings of the USENIX Workshop on Electronic Commerce, New York, NY, USA, 11–12 July 1995; Volume 1. [Google Scholar]
- Deng, R.H.; Gong, L.; Lazar, A.A.; Wang, W. Practical protocols for certified electronic mail. J. Netw. Syst. Manag. 1996, 4, 279–297. [Google Scholar] [CrossRef]
- Asokan, N.; Schunter, M.; Waidner, M. Optimistic Protocols for Fair Exchange. In Proceedings of the CCS ‘97 4th ACM Conference on Computer and Communications Security, Zurich, Switzerland, 1–4 April 1997; ACM: New York, NY, USA, 1997; pp. 7–17. [Google Scholar] [CrossRef]
- Dodis, Y.; Reyzin, L. Breaking and Repairing Optimistic Fair Exchange from PODC 2003. In Proceedings of the DRM ‘03 3rd ACM Workshop on Digital Rights Management, Washington, DC, USA, 27 October 2003; ACM: New York, NY, USA, 2003; pp. 47–54. [Google Scholar] [CrossRef]
- Huang, Q.; Yang, G.; Wong, D.S.; Susilo, W. Efficient Optimistic Fair Exchange Secure in the Multi-user Setting and Chosen-Key Model without Random Oracles. In Topics in Cryptology—CT-RSA 2008; Malkin, T., Ed.; Springer: Berlin/Heidelberg, Germany, 2008; pp. 106–120. [Google Scholar]
- Huang, Q.; Yang, G.; Wong, D.S.; Susilo, W. Ambiguous Optimistic Fair Exchange. In Advances in Cryptology–ASIACRYPT 2008; Pieprzyk, J., Ed.; Springer: Berlin/Heidelberg, Germany, 2008; pp. 74–89. [Google Scholar]
- Wang, Y.; Au, M.H.; Susilo, W. Perfect Ambiguous Optimistic Fair Exchange. In Information and Communications Security; Chim, T.W., Yuen, T.H., Eds.; Springer: Berlin/Heidelberg, Germany, 2012; pp. 142–153. [Google Scholar]
- Huang, Q.; Wong, D.S.; Susilo, W. P2OFE: Privacy-Preserving Optimistic Fair Exchange of Digital Signatures. In Topics in Cryptology—CT-RSA 2014; Benaloh, J., Ed.; Springer: Cham, Switzerland, 2014; pp. 367–384. [Google Scholar]
- Guo, Q.; Cui, Y.; Zou, X.; Huang, Q. Generic Construction of Privacy-Preserving Optimistic Fair Exchange Protocols. J. Internet Serv. Inf. Secur. 2017, 7, 44–56. [Google Scholar]
- Huang, X.; Mu, Y.; Susilo, W.; Wu, W.; Zhou, J.; Deng, R.H. Preserving Transparency and Accountability in Optimistic Fair Exchange of Digital Signatures. IEEE Trans. Inf. Forensics Secur. 2011, 6, 498–512. [Google Scholar] [CrossRef]
- Bellare, M.; Rogaway, P. Random Oracles Are Practical: A Paradigm for Designing Efficient Protocols. In Proceedings of the CCS ‘93 1st ACM Conference on Computer and Communications Security, Fairfax, VA, USA, 3–5 November 1993; ACM: New York, NY, USA, 1993; pp. 62–73. [Google Scholar] [CrossRef]
- Bellare, M.; Goldreich, O. On Defining Proofs of Knowledge. In Advances in Cryptology—CRYPTO’ 92; Brickell, E.F., Ed.; Springer: Berlin/Heidelberg, Germany, 1993; pp. 390–420. [Google Scholar]
- Fiat, A.; Shamir, A. How To Prove Yourself: Practical Solutions to Identification and Signature Problems. In Advances in Cryptology—CRYPTO’ 86; Odlyzko, A.M., Ed.; Springer: Berlin/Heidelberg, Germany, 1987; pp. 186–194. [Google Scholar]
- Cramer, R.; Damgård, I.; Schoenmakers, B. Proofs of Partial Knowledge and Simplified Design of Witness Hiding Protocols. In Advances in Cryptology—CRYPTO ’94; Desmedt, Y.G., Ed.; Springer: Berlin/Heidelberg, Germany, 1994; pp. 174–187. [Google Scholar]
- Ganjavi, R.; Asaar, M.R.; Salmasizadeh, M. A traceable optimistic fair exchange protocol. In Proceedings of the 2014 11th International ISC Conference on Information Security and Cryptology, Tehran, Iran, 3–4 September 2014; pp. 161–166. [Google Scholar] [CrossRef]
- Fujisaki, E.; Suzuki, K. Traceable Ring Signature. In Public Key Cryptography–PKC 2007; Okamoto, T., Wang, X., Eds.; Springer: Berlin/Heidelberg, Germany, 2007; pp. 181–200. [Google Scholar]
- Fujisaki, E. Sub-linear Size Traceable Ring Signatures without Random Oracles. In Topics in Cryptology—CT-RSA 2011; Kiayias, A., Ed.; Springer: Berlin/Heidelberg, Germany, 2011; pp. 393–415. [Google Scholar]
- Gu, K.; Wu, N. Constant Size Traceable Ring Signature Scheme without Random Oracles. Cryptology ePrint Archive, Report 2018/288, 2018. Available online: https://eprint.iacr.org/2018/288 (accessed on 6 June 2018).
- Hu, C.; Li, D. Forward-Secure Traceable Ring Signature. In Proceedings of the Eighth ACIS International Conference on Software Engineering, Artificial Intelligence, Networking, and Parallel/Distributed Computing (SNPD 2007), Qingdao, China, 30 July–1 August 2007; Volume 3, pp. 200–204. [Google Scholar] [CrossRef]
- Loh, J.C.; Heng, S.H.; Tan, S.Y. A Generic Framework for Accountable Optimistic Fair Exchange Protocol. In Lecture Notes in Computer Science, Proceeding of the 14th International Conference on Information Security Practice and Experience, Tokyo, Japan, 25–27 September 2018; Su, C., Kikuchi, H., Eds.; Springer: New York, NY, USA, 2018; Volume 11125, pp. 299–309. [Google Scholar]
- Boneh, D.; Lynn, B.; Shacham, H. Short Signatures from the Weil Pairing. In Advances in Cryptology—ASIACRYPT 2001; Boyd, C., Ed.; Springer: Berlin/Heidelberg, Germany, 2001; pp. 514–532. [Google Scholar]
- Li, F.; Gao, W.; Wang, Y.; Wang, X. Short Convertible Undeniable Signature From Pairing. J. Softw. 2013, 8, 2983–2990. [Google Scholar] [CrossRef]
- Shim, K.A. An efficient ring signature scheme from pairings. Inf. Sci. 2015, 300, 63–69. [Google Scholar] [CrossRef]
- Dodis, Y.; Lee, P.J.; Yum, D.H. Optimistic Fair Exchange in a Multi-user Setting. In Public Key Cryptography—PKC 2007; Okamoto, T., Wang, X., Eds.; Springer: Berlin/Heidelberg, Germany, 2007; pp. 118–133. [Google Scholar]
- Zhu, H.; Susilo, W.; Mu, Y. Multi-party Stand-Alone and Setup-Free Verifiably Committed Signatures. In Public Key Cryptography—PKC 2007; Okamoto, T., Wang, X., Eds.; Springer: Berlin/Heidelberg, Germany, 2007; pp. 134–149. [Google Scholar]
- Boneh, D.; Franklin, M. Identity-Based Encryption from the Weil Pairing. In Advances in Cryptology—CRYPTO 2001; Kilian, J., Ed.; Springer: Berlin/Heidelberg, Germany, 2001; pp. 213–229. [Google Scholar]
- Goldwasser, S.; Micali, S.; Rivest, R.L. A Digital Signature Scheme Secure Against Adaptive Chosen-Message Attacks. SIAM J. Comput. 1988, 17, 281–308. [Google Scholar] [CrossRef]
- Chaum, D.; van Antwerpen, H. Undeniable Signatures. In Advances in Cryptology—CRYPTO’ 89 Proceedings; Brassard, G., Ed.; Springer: New York, NY, USA, 1990; pp. 212–216. [Google Scholar]
- Boyar, J.; Chaum, D.; Damgård, I.; Pedersen, T. Convertible Undeniable Signatures. In Advances in Cryptology-CRYPT0’ 90; Menezes, A.J., Vanstone, S.A., Eds.; Springer: Berlin/Heidelberg, Germany, 1991; pp. 189–205. [Google Scholar]
- Galbraith, S.D.; Mao, W. Invisibility and Anonymity of Undeniable and Confirmer Signatures. In Topics in Cryptology—CT-RSA 2003; Joye, M., Ed.; Springer: Berlin/Heidelberg, Germany, 2003; pp. 80–97. [Google Scholar]
- Huang, X.; Mu, Y.; Susilo, W.; Wu, W. Provably Secure Pairing-Based Convertible Undeniable Signature with Short Signature Length. In Pairing-Based Cryptography—Pairing 2007; Takagi, T., Okamoto, T., Okamoto, E., Okamoto, T., Eds.; Springer: Berlin/Heidelberg, Germany, 2007; pp. 367–391. [Google Scholar]
- Rivest, R.L.; Shamir, A.; Tauman, Y. How to Leak a Secret. In Advances in Cryptology—ASIACRYPT 2001; Boyd, C., Ed.; Springer: Berlin/Heidelberg, Germany, 2001; pp. 552–565. [Google Scholar]
- Bender, A.; Katz, J.; Morselli, R. Ring Signatures: Stronger Definitions, and Constructions Without Random Oracles. In Theory of Cryptography; Halevi, S., Rabin, T., Eds.; Springer: Berlin/Heidelberg, Germany, 2006; pp. 60–79. [Google Scholar]
- Bender, A.; Katz, J.; Morselli, R. Ring Signatures: Stronger Definitions, and Constructions without Random Oracles. J. Cryptol. 2009, 22, 114–138. [Google Scholar] [CrossRef]
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).