Steganalysis of Inactive Voice-Over-IP Frames Based on Poker Test
Abstract
1. Introduction
2. Related Work
2.1. Improved VAD Algorithm
2.2. Steganography in Inactive Frame
- Step 1:
- Voice activity detection. Speech samples are divided into frames, and each frame is input into the VAD detector, where the inactive frames are marked with a tag.
- Step 2:
- Encoding and embedding secret messages in inactive frames. All frames are encoded without applying silence compression function. If the frame has been marked in Step 1, suitable parameters of the frame will be embedded with secret messages.
- Step 3:
- Encapsulation and send. All the frames are encapsulated in VoIP packets, which are transmitted over the Internet.
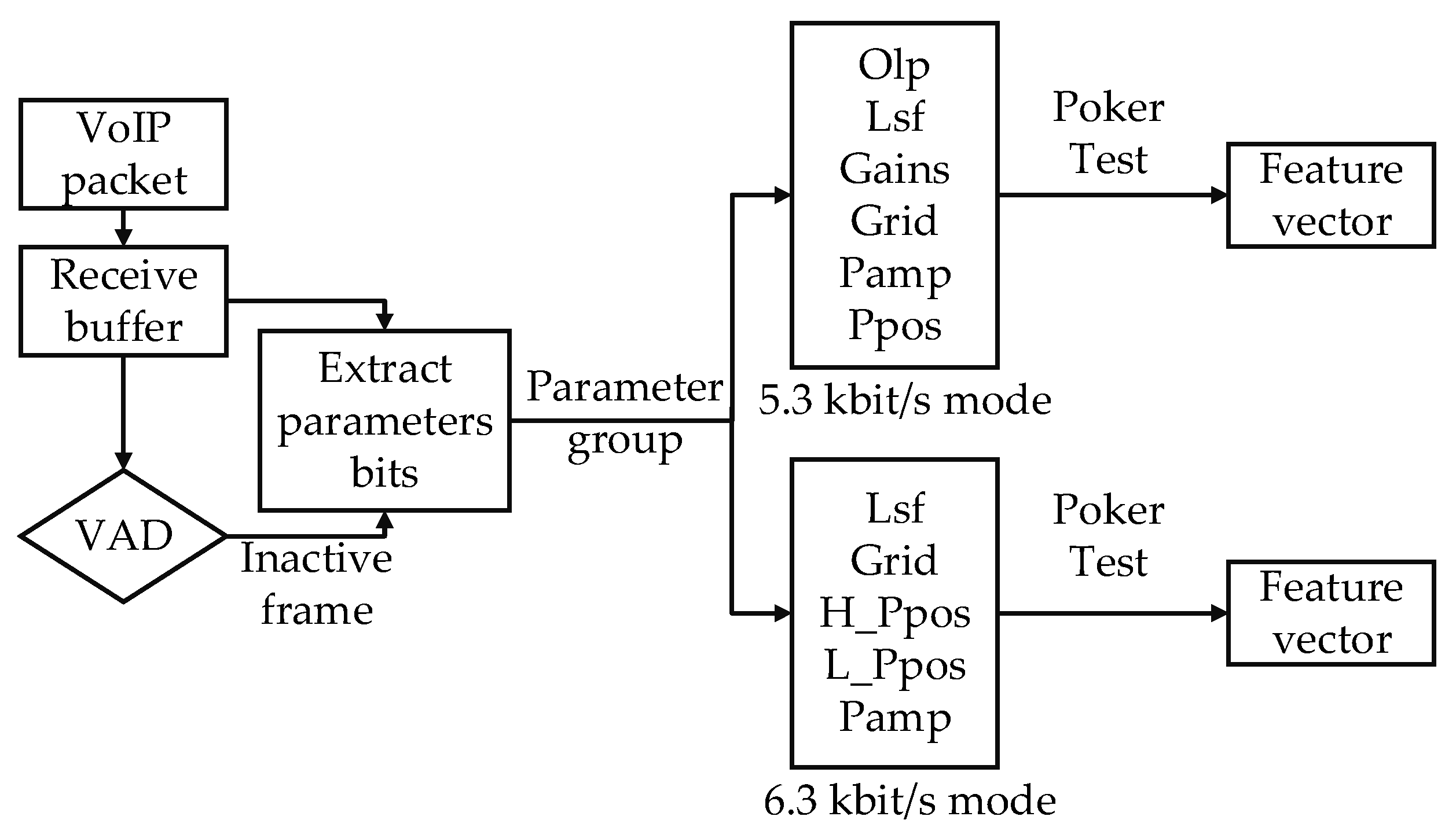
3. Steganalysis Based on Poker Test
4. SVM-Based Steganalysis Method
- Step 1:
- Sample preparation. Collect a great quantity of speech samples encoded by G.723.1 with both encoding modes and embed secret messages with the steganography in Section 2.2 at different embedding rates.
- Step 2:
- Step 3:
- Classifier training. Train the SVM classifier with the feature vector built in Step 2.
- Step 1:
- Feature extraction. Extract the proposed features from the samples to be detected.
- Step 2:
- Decision-making. Input the features extracted in Step 1 into the trained SVM classifier to determine whether the samples to be detected contain secret messages according to the classification results.
5. Experimental Result and Analysis
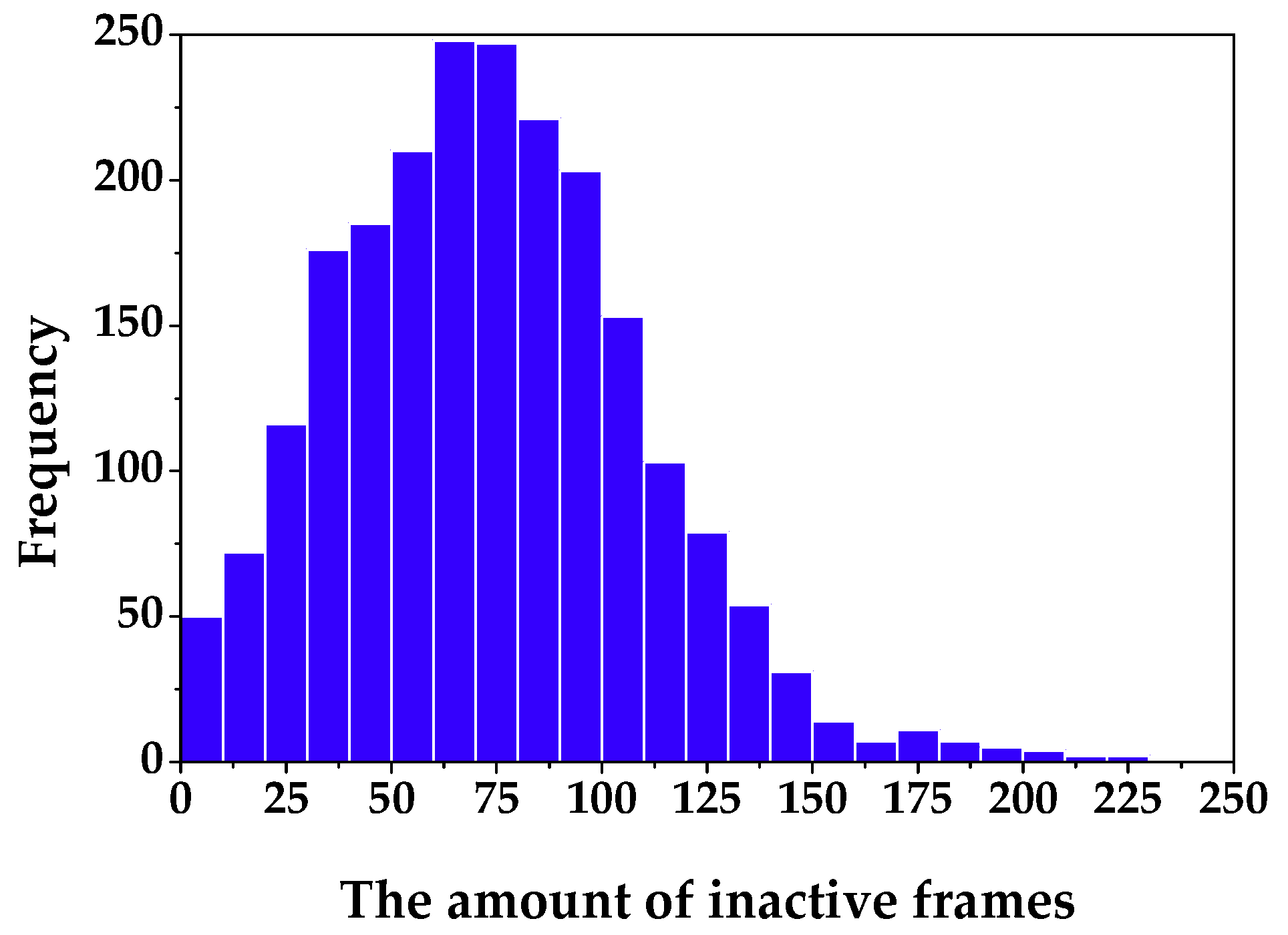
5.1. Experiment Setup and Performance Evaluation
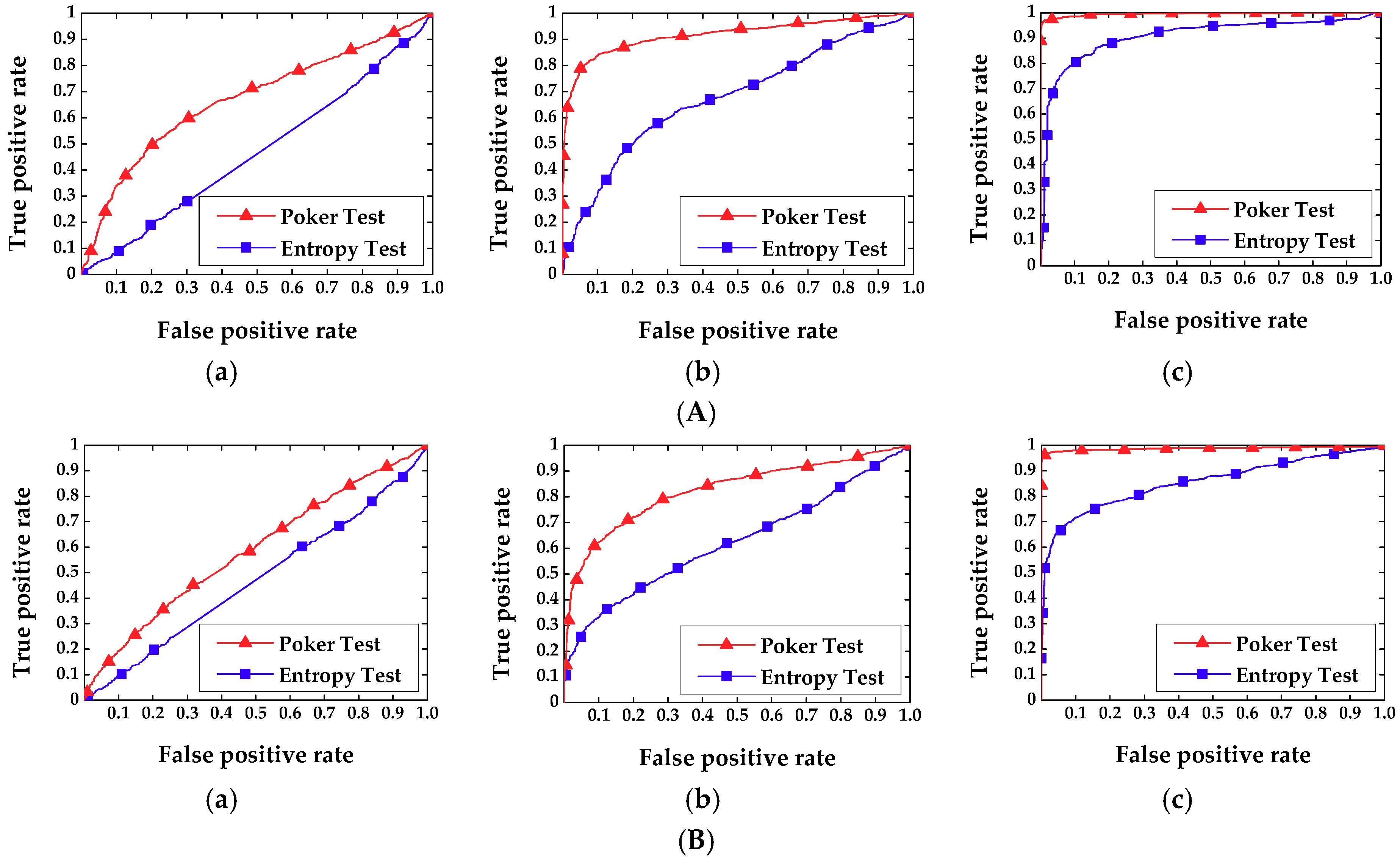
5.2. Performance and Analysis
6. Conclusions
Author Contributions
Funding
Conflicts of Interest
References
- Naidu, T.R.K.; Kumar, G.P.; Prasad, T.G. Overview of digital audio steganography techniques. Int. J. Emerg. Technol. Eng. 2016, 3, 62–66. [Google Scholar]
- Joshi, R.; Venugopala, P.S. Improved security in audio steganography using packet forger at the third level. In Proceedings of the 2017 International Conference on Smart Technologies for Smart Nation (SMARTTECHCON), Bangalore, India, 17–19 August 2017; pp. 363–368. [Google Scholar]
- Liu, H.; Liu, J.; Hu, R.; Yan, X.; Wan, S. Adaptive Audio Steganography Scheme Based on Wavelet Packet Energy. In Proceedings of the 2017 IEEE 3rd International Conference on Big Data Security on Cloud (BIGDATASECURITY), IEEE International Conference on High Performance and Smart Computing (HPSC), and IEEE International Conference on Intelligent Data and Security (IDS), Beijing, China, 26–28 May 2017; pp. 26–31. [Google Scholar]
- Hussain, M.; Wahab, A.W.A.; Javed, N.; Jung, K.H. Hybrid Data Hiding Scheme Using Right-Most Digit Replacement and Adaptive Least Significant Bit for Digital Images. Symmetry 2016, 8, 41. [Google Scholar] [CrossRef]
- Rajendran, S.; Doraipandian, M. Chaotic Map Based Random Image Steganography Using LSB Technique. Int. J. Netw. Secur. 2017, 19, 593–598. [Google Scholar]
- Kordov, K.; Stoyanov, B. Least Significant Bit Steganography using Hitzl-Zele Chaotic Map. Int. J. Electron. Telecommun. 2017, 63, 417–422. [Google Scholar] [CrossRef]
- Stoyanov, B.P.; Zhelezov, S.K.; Kordov, K.M. Least significant bit image steganography bit image steganography algorithm based on chaotic rotation equations. Mathematiques 2016, 69, 845–850. [Google Scholar]
- Aziz, M.; Tayarani-N, M.H.; Afsar, M. A cycling chaos-based cryptic-free algorithm for image steganography. Nonlinear Dyn. 2015, 80, 1271–1290. [Google Scholar] [CrossRef]
- Almutairi, A. A Comparative Study on Steganography Digital Images: A Case Study of Scalable Vector Graphics (SVG) and Portable Network Graphics (PNG) Images Formats. Int. J. Adv. Comput. Sci. Appl. 2018, 9, 170–175. [Google Scholar] [CrossRef]
- Mondal, B.; Sinha, N.; Mandal, T. A Secure Image Encryption Algorithm Using LFSR and RC4 Key Stream Generator. In Proceedings of the 3rd International Conference on Advanced Computing, Networking and Informatics, Bhubaneswar, India, 23–25 June 2016; pp. 227–237. [Google Scholar]
- Kar, N.; Mandal, K.; Bhattacharya, B. Improved chaos-based video steganography using DNA alphabets. ICT Express 2018, 4, 6–13. [Google Scholar] [CrossRef]
- Dasgupta, K.; Mondal, J.K.; Dutta, P. Optimized video steganography using genetic algorithm (GA). Procedia Technol. 2013, 10, 131–137. [Google Scholar] [CrossRef]
- Kordov, K.; Lachezar, B. Using Circle Map for Audio Encryption Algorithm. Math. Softw. Eng. 2017, 2, 183–189. [Google Scholar]
- Bashir, Z.; Wątróbski, J.; Rashid, T.; Zafar, S.; Sałabun, W. Chaotic Dynamical State Variables Selection Procedure Based Image Encryption Scheme. Symmetry 2017, 9, 312. [Google Scholar] [CrossRef]
- Mazurczyk, W. VoIP steganography and its Detection—A survey. ACM Comput. Surv. 2013, 46, 20. [Google Scholar] [CrossRef]
- Mazurczyk, W.; Szczypiorski, K. Covert Channels in SIP for VoIP Signalling. Commun. Comput. Inf. Sci. 2008, 12, 65–72. [Google Scholar]
- Forbes, C.R. A New Covert Channel over RTP. Master’s Thesis, Rochester Institute of Technology, New York, NY, USA, 2009. [Google Scholar]
- Geiser, B.; Vary, P. High rate data hiding in ACELP speech codecs. In Proceedings of the 2008 IEEE International Conference on Acoustics, Speech and Signal Processing, Las Vegas, NV, USA, 31 March–4 April 2008; pp. 4005–4008. [Google Scholar]
- Miao, H.; Huang, L.; Chen, Z.; Yang, W.; Al-hawbani, A. A new scheme for covert communication via 3G encoded speech. Comput. Electr. Eng. 2012, 38, 1490–1501. [Google Scholar] [CrossRef]
- Zhijun, W.; Yongpeng, S. An implementation of speech steganography for iLBC by using fixed codebook. In Proceedings of the 2016 2nd IEEE International Conference on Computer and Communications (ICCC), Chengdu, China, 14–17 October 2016; pp. 1970–1974. [Google Scholar]
- Liu, P.; Li, S.; Wang, H. Steganography integrated into linear predictive coding for low bit-rate speech codec. Multimed. Tools Appl. 2017, 76, 2837–2859. [Google Scholar] [CrossRef]
- Liu, P.; Li, S.; Wang, H. Steganography in vector quantization process of linear predictive coding for low-bit-rate speech codec. Multimed. Syst. 2017, 23, 485–497. [Google Scholar] [CrossRef]
- Tian, H.; Liu, J.; Li, S. Improving security of quantization-index-modulation steganography in low bit-rate speech streams. Multimed. Syst. 2014, 20, 143–154. [Google Scholar] [CrossRef]
- Nishimura, A. Data Hiding in Pitch Delay Data of the Adaptive Multi-Rate Narrow-band Speech Codec. In Proceedings of the 2009 Fifth International Conference on Intelligent Information Hiding and Multimedia Signal Processing, Kyoto, Japan, 12–14 September 2009; pp. 483–486. [Google Scholar]
- Huang, Y.; Liu, C.; Tang, S.; Bai, S. Steganography integration into a low-bit rate speech codec. IEEE Trans. Inf. Forensics Secur. 2012, 7, 1865–1875. [Google Scholar] [CrossRef]
- Wu, Z.; Yang, W.; Yang, Y. ABS-based speech information hiding approach. Electron. Lett. 2003, 39, 1617–1619. [Google Scholar] [CrossRef]
- Janicki, A. Pitch-based Steganography for speex voice codec. Secur. Commun. Netw. 2016, 9, 2923–2933. [Google Scholar] [CrossRef]
- Huang, Y.F.; Tang, S.; Yuan, J. Steganography in inactive frames of VoIP streams encoded by source codec. IEEE Trans. Inf. Forensics Secur. 2011, 6, 296–306. [Google Scholar] [CrossRef]
- Lin, R.S. High capacity information hiding scheme using VAD algorithm. In Proceedings of the 2016 IEEE International Conference on Consumer Electronics-Taiwan (ICCE-TW), Nantou, Taiwan, 27–29 May 2016; pp. 1–2. [Google Scholar]
- Li, S.; Jia, Y.; Kuo, C.C.J. Steganalysis of QIM Steganography in Low-Bit-Rate Speech Signals. IEEE/ACM Trans. Audio Speech Lang. Process. 2017, 25, 1011–1022. [Google Scholar] [CrossRef]
- Lin, Z.; Huang, Y.; Wang, J. RNN-SM: Fast Steganalysis of VoIP Streams Using Recurrent Neural Network. IEEE Trans. Inf. Forensics Secur. 2018, 13, 1854–1868. [Google Scholar] [CrossRef]
- Ren, Y.; Yang, J.; Wang, J.; Wang, L. AMR Steganalysis Based on Second-Order Difference of Pitch Delay. IEEE Trans. Inf. Forensics Secur. 2017, 12, 1345–1357. [Google Scholar] [CrossRef]
- Tian, H.; Wu, Y.; Chang, C.C.; Huang, Y.; Chen, Y.; Wang, T.; Cai, Y.; Liu, J. Steganalysis of adaptive multi-rate speech using statistical characteristics of pulse pairs. Signal Process. 2017, 134, 9–22. [Google Scholar] [CrossRef]
- Miao, H.; Huang, L.; Shen, Y.; Lu, X.; Chen, Z. Steganalysis of compressed speech based on Markov and entropy. Lect. Notes Comput. Sci. 2013, 8389, 63–76. [Google Scholar]
- Ren, Y.; Cai, T.; Tang, M.; Wang, L. AMR Steganalysis Based on the Probability of Same Pulse Position. IEEE Trans. Inf. Forensics Secur. 2015, 10, 1801–1811. [Google Scholar]
- Malik, H.; Subbalakshmi, K.P.; Chandramouli, R. Nonparametric Steganalysis of QIM Steganography Using Approximate Entropy. IEEE Trans. Inf. Forensics Secur. 2012, 7, 418–431. [Google Scholar] [CrossRef]
- Yang, W.; Tang, S.; Li, M.; Cheng, Y.; Zhou, Z. Steganalysis of Low Embedding Rates LSB Speech Based on Histogram Moments in Frequency Domain. Chin. J. Electron. 2017, 26, 1254–1260. [Google Scholar] [CrossRef]
- Shannon, C.E. A mathematical theory of communication. Bell Syst. Tech. J. 1948, 27, 379–423. [Google Scholar] [CrossRef]
- Dual Rate Speech Coder FOR Multimedia Communications Transmitting at 5.3 and 6.3 kbit/s. Available online: https://www.itu.int/net/itu-t/sigdb/speaudio/AudioForm-s.aspx?val=1117231 (accessed on 1 May 2018).
- Menezes, A.J.; Vanstone, S.A.; Oorschot, P.C.V. Handbook of Applied Cryptography, 1st ed.; CRC Press Inc.: Boca Raton, FL, USA, 1996; ISBN 0-8493-8523-7. [Google Scholar]
- Ibrahim, A.; Dragomir, S.S. A Survey on Cauchy–Bunyakovsky–Schwarz Inequality for Power Series. In Analytic Number Theory, Approximation Theory, and Special Function; Springer: New York, NY, USA, 2014; pp. 247–295. [Google Scholar]
- Chang, C.C.; Lin, C.J. LIBSVM: A Library for Support Vector Machines. ACM Trans. Intell. Syst. Technol. 2011, 2, 27. [Google Scholar] [CrossRef]
- Garrido, A. Symmetry and Asymmetry Level Measures. Symmetry 2010, 2, 707–721. [Google Scholar] [CrossRef]

| Parameters | Subframe 0 | Subframe 1 | Subframe 2 | Subframe 3 | Subtotal (bits) |
|---|---|---|---|---|---|
| Adaptive codebook lags (Olp/Aclg) | 7 | 2 | 7 | 2 | 18 |
| LPC indices (Lsf) | - | - | - | - | 24 |
| Grid index (Grid) | 1 | 1 | 1 | 1 | 4 |
| All the gains combined (Mamp) | 12 | 12 | 12 | 12 | 48 |
| Pulse positions (Ppos) | 20 | 18 | 20 | 18 | 73 |
| Pulse signs (Pamp) | 6 | 5 | 5 | 5 | 22 |
| Total | - | - | - | - | 189 |
| Parameters | Subframe 0 | Subframe 1 | Subframe 2 | Subframe 3 | Subtotal (bits) |
|---|---|---|---|---|---|
| Adaptive codebook lags (Olp/Aclg) | 7 | 2 | 7 | 2 | 18 |
| LPC indices (Lsf) | - | - | - | - | 24 |
| rid index (Grid) | 1 | 1 | 1 | 1 | 4 |
| All the gains combined (Mamp) | 12 | 12 | 12 | 12 | 48 |
| Pulse positions (Ppos) | 12 | 12 | 12 | 12 | 48 |
| Pulse signs (Pamp) | 4 | 4 | 4 | 4 | 16 |
| Total | - | - | - | - | 158 |
| Parameter Name | Lsf | Grid | H_Ppos | L_Ppos | Pamp | Total Bits |
|---|---|---|---|---|---|---|
| Number of bits | 2 | 4 | 13 | 60 | 22 | 101 |
| Parameter Name | Olp | Lsf | Gains | Grid | Pamp | Ppos | Total Bits |
|---|---|---|---|---|---|---|---|
| Number of bits | 2 | 3 | 8 | 4 | 16 | 48 | 81 |
| Parameters | Embedding Rate | ||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 10% | 20% | 30% | 40% | 50% | 60% | 70% | 80% | 90% | 100% | |
| Lsf | 93.68 | 93.68 | 94.66 | 79.55 | 67.59 | 56.76 | 43.99 | 17.81 | 5.93 | 18.78 | 12.47 |
| Grid | 3.01 | 3.09 | 2.60 | 2.93 | 3.13 | 6.04 | 4.22 | 5.76 | 5.23 | 3.10 | 0.59 |
| H_Ppos | 4.12 | 5.23 | 4.28 | 6.55 | 3.18 | 3.00 | 3.31 | 1.30 | 5.23 | 4.71 | 0.39 |
| L_Ppos | 7.52 | 8.25 | 6.26 | 6.67 | 5.88 | 4.48 | 2.73 | 7.93 | 2.71 | 2.85 | 3.06 |
| Pamp | 201.45 | 203.87 | 182.85 | 161.63 | 119.60 | 131.89 | 84.86 | 74.00 | 30.68 | 4.37 | 2.99 |
© 2018 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Liu, J.; Tian, H.; Chang, C.-C.; Wang, T.; Chen, Y.; Cai, Y. Steganalysis of Inactive Voice-Over-IP Frames Based on Poker Test. Symmetry 2018, 10, 336. https://doi.org/10.3390/sym10080336
Liu J, Tian H, Chang C-C, Wang T, Chen Y, Cai Y. Steganalysis of Inactive Voice-Over-IP Frames Based on Poker Test. Symmetry. 2018; 10(8):336. https://doi.org/10.3390/sym10080336
Chicago/Turabian StyleLiu, Jie, Hui Tian, Chin-Chen Chang, Tian Wang, Yonghong Chen, and Yiqiao Cai. 2018. "Steganalysis of Inactive Voice-Over-IP Frames Based on Poker Test" Symmetry 10, no. 8: 336. https://doi.org/10.3390/sym10080336
APA StyleLiu, J., Tian, H., Chang, C.-C., Wang, T., Chen, Y., & Cai, Y. (2018). Steganalysis of Inactive Voice-Over-IP Frames Based on Poker Test. Symmetry, 10(8), 336. https://doi.org/10.3390/sym10080336








