1. Introduction
Privacy protection and security provision have been of great concern in proportion to the number of sensor nodes in wireless sensor networks. In addition, due to the features of wireless environments, efficiency is one noticeable aspect. The characteristics of low transmission bandwidth, insufficient memory, low computing power, and battery dependency demand more lightweight and efficient security mechanisms that provide a similar level of security to wired environments. Considering a mobile sensor node that travels in various networks and wants to receive roaming service from a foreign agent, an anonymous authentication scheme is necessary to preserve the sensor node’s privacy and security. If the scheme is also lightweight, it is more suitable for wireless sensor networks.
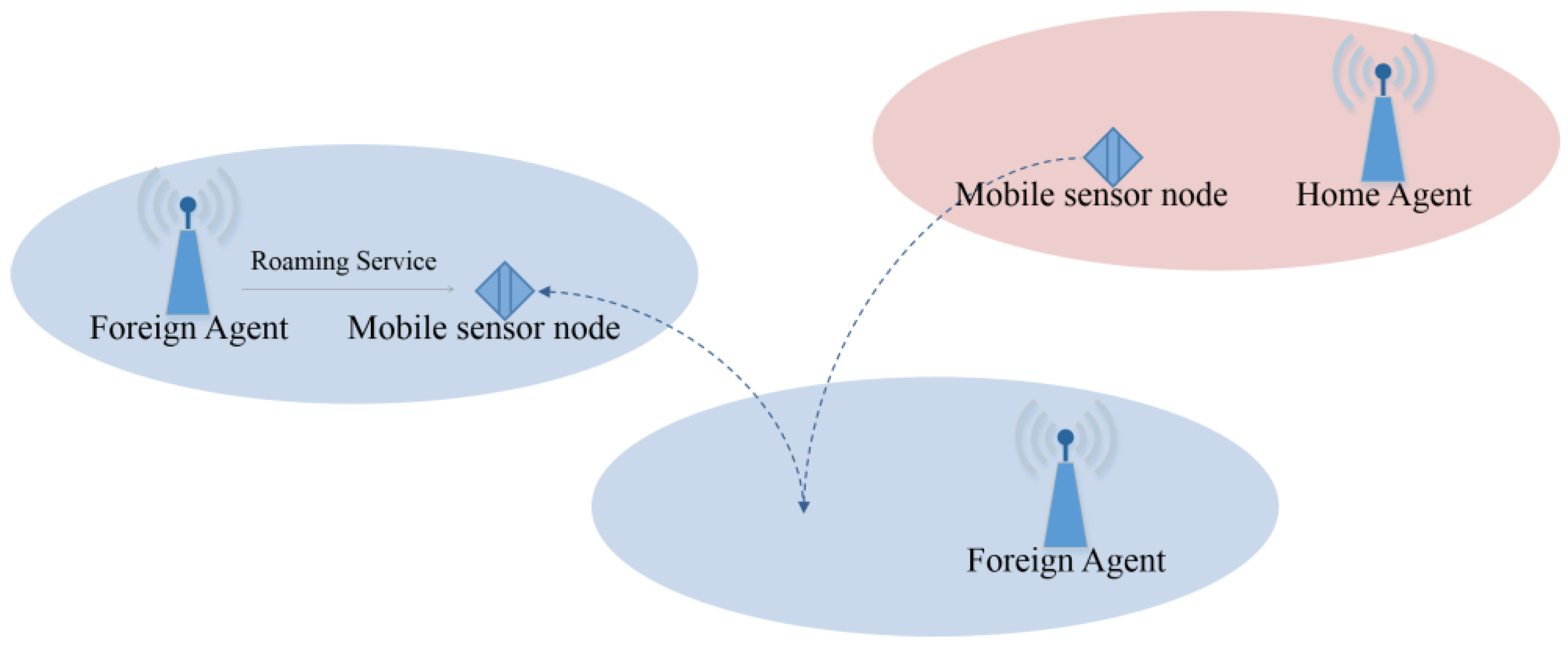
Figure 1 illustrates a simple model of wireless sensor networks for roaming service. If a mobile sensor node registered for its home agent visits a foreign network, it wants to access the foreign agent to receive roaming service. The foreign agent then needs to check the identification of the sensor node through its home agent. In this situation, a lightweight anonymous authentication scheme is necessary to guarantee secure authentication and efficient communication.
In recent years, various anonymous authentication schemes and related protocols in wireless networks have been proposed [
1,
2,
3,
4,
5,
6,
7,
8,
9,
10,
11,
12,
13,
14,
15,
16,
17,
18,
19,
20,
21,
22,
23,
24,
25]. They have been followed by proofs of vulnerability of the schemes and associated improvements. Some of these schemes use high-cost functions, such as symmetric cryptographic functions, asymmetric cryptographic functions, and modular operations [
1,
2,
3,
4,
5,
6,
7,
8,
9,
10,
11,
12,
13,
14,
15,
16,
17,
18]. On the other hand, the others are based on low-cost functions, such as one-way hash functions and bit-wise exclusive-OR operations [
19,
20,
21,
22,
23,
24,
25]. To analyze these schemes, we categorize them into two groups according to the computation cost: schemes based on high-cost functions and schemes based on low-cost functions. If all of them provide the same security level, schemes based on low-cost functions are more suitable for wireless sensor networks, since they consume less energy. Farash et al. [
18] proposed one of the most recent anonymous authentication schemes for roaming service. They claimed that their scheme improved security and reduced computation time. However, their scheme still has security weaknesses, and does not have computational benefit.
The contributions of this paper are two points. Firstly, we point out that Farash et al.’s scheme does not provide anonymity against a legitimate but malicious adversary, foreign agent authentication, or password replacement. In addition, we present that Farash et al.’s scheme has less computational merits than our proposed scheme, even if their scheme is superior to other previous schemes in terms of the computation cost. Secondly, we propose an enhanced lightweight anonymous authentication scheme that resolves the above weaknesses. Our proposed scheme has the advantage of security and efficiency. In other words, it has enhanced security features and resistance against well-known attacks, as well as the fastest running time among other schemes. More specifically, the proposed scheme preserves weak and strong anonymity, hop-by-hop authentication, and untraceability; resistance against password guessing, impersonation, forgery, and known session key attack; and fair key agreement. There have been no recent schemes, which guarantee all the above. In addition, since the proposed scheme is based only on low-cost functions, it runs faster and more efficiently than previous schemes. Although most schemes including ours are adaptable to wireless sensor networks, our proposed scheme, due to better efficiency, has superiority over other previous schemes.
The remainder of this paper is organized as follows.
Section 2 briefly describes related works, and
Section 3 reviews Farash et al.’s scheme.
Section 4 then presents its weaknesses.
Section 5 proposes our enhanced scheme, and
Section 6 presents the formal analysis of our proposed protocol.
Section 7 and
Section 8 then analyze the security and performance of our scheme, respectively. Finally,
Section 9 concludes the paper.
2. Related Works
Previous schemes, which have recently been proposed, show the following research trends. Zhu and Ma [
1] in 2004 proposed an anonymous authentication scheme based on high-cost functions, and Lee et al. [
2] proved that it has security weaknesses. Wu et al. [
3] argued that both Zhu and Ma’s and Lee et al.’s schemes fail to preserve anonymity and backward secrecy, and they presented improvements of Lee et al.’s scheme. However, Lee et al. [
5] and Xu [
6] showed vulnerabilities of Wu et al.’s scheme. Kun et al. [
7] improved Xu and Feng’s scheme, but Tsai et al. [
8] showed that Kun et al.’s scheme is also vulnerable. In addition, Mun et al. [
9] showed Wu et al.’s scheme suffers from various attacks, and proposed an enhanced scheme. However, Zhao et al. [
10] proved that Mun et al.’s scheme is insecure.
Independently, Chang et al. [
19] in 2009 proposed an enhanced authentication scheme that uses only low-cost functions. Unfortunately, Youn et al. [
20] proved that Chang et al.’s scheme is vulnerable. In addition, Zhou and Xu [
13] showed that Chang et al.’s scheme has weaknesses, and they proposed an improved scheme. Lately, Gope and Hwang [
24] have proved that Zhou and Xu’s scheme suffers from some security faults, such as unsuccessful key agreement and vulnerability to replay attack. They showed that a malicious adversary, by replacing transmission messages, can disturb valid communication between a normal user and a foreign agent. In addition, they proved that an attacker can successfully retransmit authentication messages that have been transmitted during a previous session of communication. At the same time, they proposed an improved scheme. Their improved scheme guarantees several security features as follows. Since all participants can normally verify parameters in each message, their scheme preserves mutual authentication. The fact that each participant makes the same contribution to the freshness of a session key provides their scheme with fair key agreement. In addition, both passive eavesdroppers and active intruders cannot identify or keep track of a normal user. Since only a legitimate user can form a valid one-time-alias using a real identity, secret value, nonce, and timestamp, no attackers can forge the alias to cheat users. In addition, it is impossible to accomplish a known session key attack because there is no significant relation among any session keys. It means that the compromised session key never helps to recover any past or future session keys. Moreover, since their scheme is based on low-cost functions, it has computational merits.
Meanwhile, He et al. [
21] proved that Chang et al.’s scheme has a security fault, and that their scheme is not efficient. After that, Jiang et al. [
14] showed the weaknesses of He et al.’s scheme. They proposed an enhanced protocol, but Wen et al. [
15] presented its weaknesses. Subsequently, Gope and Hwang [
17] showed that Wen et al.’s scheme suffers from several attacks. In Wen et al.’s scheme, an attacker, by performing an exhaustive search operation of all possible values, can obtain secret information stored in the lost or stolen smart card. After jamming all transmission messages and resetting a counter, he or she can also establish a session key between a normal user and a foreign agent. Since a session key contains only one random number generated by one side of the participants, it fails to preserve fair key agreement. In addition, Gope and Hwang proposed an enhanced scheme that preserves mutual authentication, fair key agreement, user anonymity, resistance against forgery attack, and security assurance in the case of a lost smart card. In their schemes, all participants can authenticate each other by verifying parameters. While computing a session key, each participant contributes equally, by providing independent random numbers. Since the difficulty of the quadratic residue problem makes a real identity secure, the identity cannot be revealed. No attackers can forge transmission messages because they do not have the knowledge of a secret key and a real identity. In addition, an attacker cannot use the lost or stolen smart card to perform any masquerade attacks because there is no way to obtain a secret key, an identity, and a password from the smart card.
In addition, Shin et al. [
16] proved He et al.’s scheme is vulnerable, and proposed an improved scheme. Then, Farash et al. simultaneously presented the vulnerabilities of both Wen et al.’s scheme and Shin et al.’s scheme, proving that Wen et al.’s scheme suffers from session key disclosure attack and known session key attack, while Shin et al.’s scheme does not guarantee untraceability, secrecy of the sensitive parameter of home agent, secrecy against impersonation attack, or session key secrecy. Farash et al. also proposed an improved scheme that preserves security and reduces the computation time of their scheme.
3. Review of Farash et al.’s Scheme
In this section, we review the lightweight anonymous authentication scheme proposed by Farash et al. Their scheme consists of three phases: registration, login and authentication, and password change. Three different entities are involved in each phase.
is a mobile node that wants to receive roaming service while visiting a foreign network.
is the foreign agent of a foreign network, and
is the home agent of the mobile node
. When
visits a foreign network, it sends a login request message to
to be authenticated. Then,
sends an authentication request message to
for authentication of
, since
is not the home agent of
, and it cannot directly check
’s identity. After
authenticates
using the message received from
,
sends a response message to
. Finally,
sends a response message to
and shares a common session key with
. In this process, it is supposed that
and
are in a trusting relationship, and that they secretly share and store a long-term secret key. Because of this, it is possible for
to anonymously authenticate
through
.
Table 1 denotes the notations used in this paper.
3.1. Registration Phase
To register for
,
first selects
,
, and the random number
. Then,
sends
and
to
in a secure manner. After receiving
and
,
computes the following parameters for
:
Next, sends , , and to ; and stores , as well as , , and .
3.2. Login and Authentication Phase
and
perform the login and authentication phase to achieve the following goals with the aid of
:
anonymously authenticates ;
and mutually authenticate each other;
and share a session key.
In this phase, it is supposed that the common secret key
is shared between
and
beforehand.
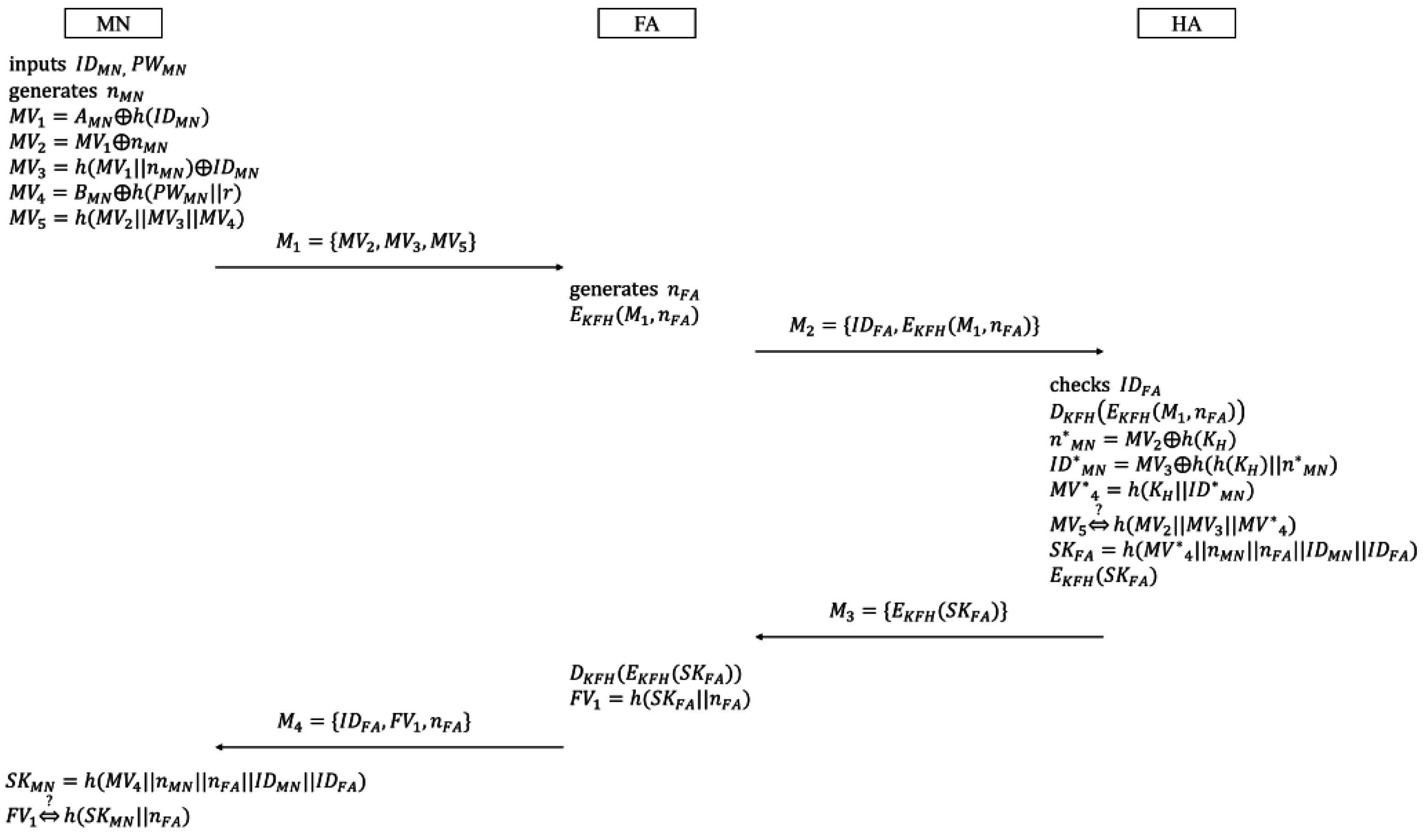
Figure 2 illustrates the login and authentication phase. The procedure of this phase is as follows:
- (1)
inputs
and
. Then
generates the random nonce
, and loads
,
,
, and
to compute
’s verifiers:
Next, sends the message to .
- (2)
Upon receiving , generates the random nonce , and encrypts and using the symmetric encryption function such that . Then, sends the message to .
- (3)
After receiving
,
first checks
to confirm that
is a valid agent. If so,
retrieves
, and makes the following computations:
If
checks the equivalence between the received
and the computed
normally,
computes the following session key, and encrypts it with
:
Then, sends the message to .
- (4)
After receiving
,
decrypts the encrypted session key, and computes
’s verifier:
Then, sends the message to .
Upon receiving
,
computes the session key:
By checking the validity of the session key after computing , confirms that successfully authenticates , and the session key is established between them at the same time.
3.3. Password Change Phase
, which wants to change its password, is supposed to perform the password change phase. In this phase,
renews the password after acquiring the confirmation from
.
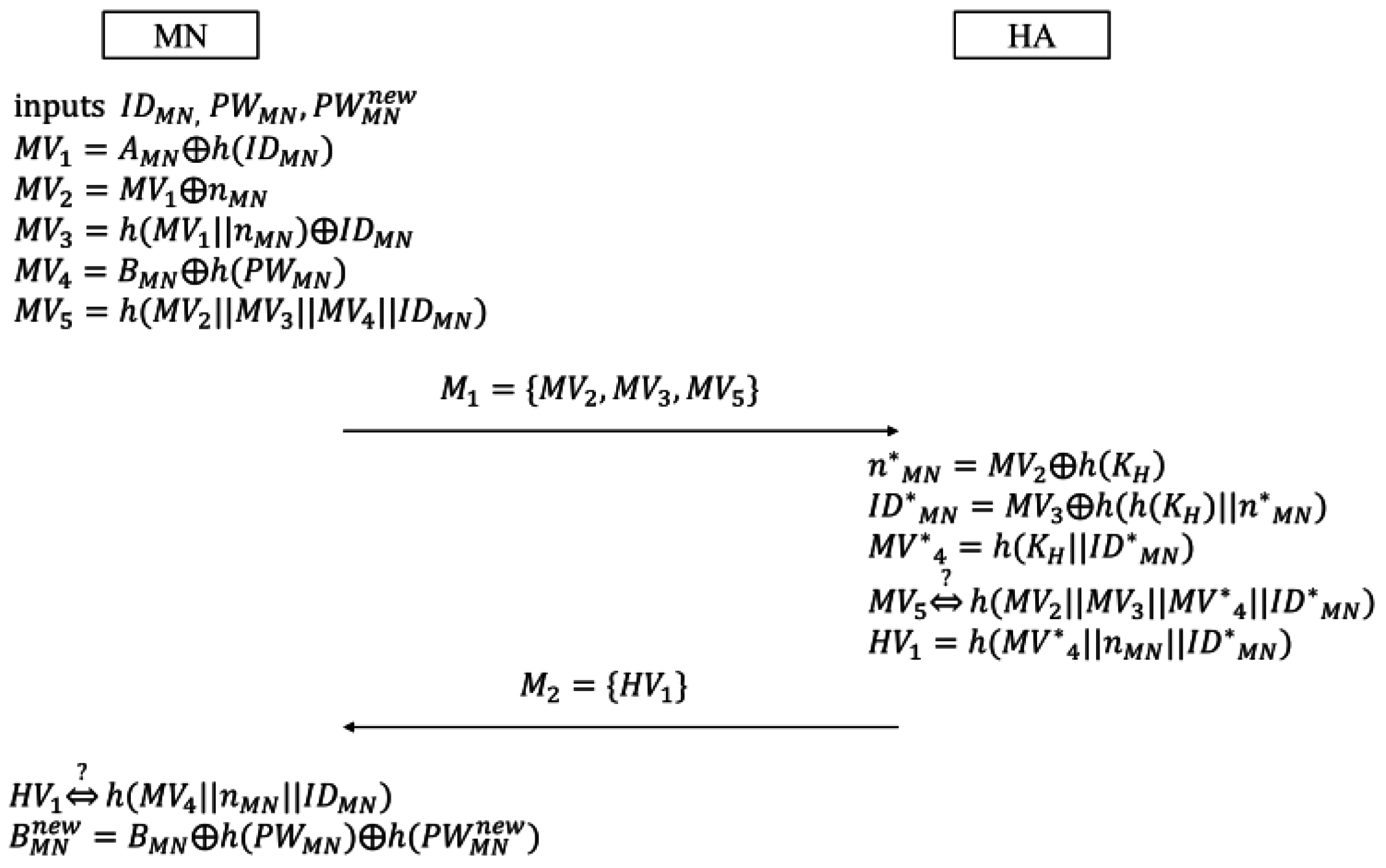
Figure 3 describes the password change phase.
- (1)
inputs the identity
, the current
, and the new password
. Then,
generates the random nonce
, and computes the following verifiers in a similar way to what it does in the login and authentication phase:
Next, sends the message to .
- (2)
Upon receiving
,
computes
,
, and
as shown in Equations (20)–(22):
After computing
,
checks the validity of
. The successful check means
authenticates
normally. Then,
computes the following verifier
, and sends
to
:
- (3)
After receiving
,
checks the equivalence between
and
to confirm that
has successfully authenticated
. Finally,
computes the following
, and replaces
with
:
4. Weaknesses of Farash et al.’s Scheme
Farash et al. proved that their scheme guarantees authentication, authentication, anonymity and untraceability, resistance against offline password guessing attack, secure key establishment, and no verification table at . However, there still remain several security weaknesses in their scheme. In this section, we will prove that Farash et al.’s scheme does not guarantee anonymity or authentication. In addition, we will show that their scheme does not achieve password replacement.
4.1. Anonymity
Farash et al.’s scheme guarantees anonymity against a foreign agent and a normal mobile node. However, it does not preserve anonymity against a malicious mobile node. Suppose that there is a malicious mobile node
normally registered for
, as in Farash et al.’s attack scenario. Then,
can get
by accomplishing the following procedures:
- (1)
inputs and . Then, can get .
- (2)
To get
,
eavesdrops
, and computes
. Since the equation described below holds,
can successfully get
:
- (3)
Next, by computing as follows,
gets
:
As a result, a malicious mobile node that eavesdrops the message can easily know the other’s identity, so anonymity is not guaranteed.
4.2. Authentication
In Farash et al.’s scheme,
can authenticate both
and
. In
’s case, after computing
from
and
from
,
can authenticate
by checking the equivalence between
and
. In addition,
can authenticate
by a successful decryption using the pre-shared secret key
corresponding to
’s identity. Meanwhile,
is able to anonymously authenticate
with the aid of
. In addition, a successful decryption using
makes
check
’s identity. This is the same as what
does. However, while it is possible to authenticate
,
cannot authenticate
. There is no obvious way for
to confirm the received message that is made with the aid of
. The reason is as follows. After receiving
from
,
just computes the following session key
, without checking any verifiers computed by
:
Clearly,
contains
which is computed as follows:
Since is the only entity that can compute , can only authenticate through a successful checking of , namely . This implies that there is no way for to authenticate . In addition, if failure while checking occurs, cannot confirm whether or is illegal. For these reasons, authenticating the foreign agent is impossible.
4.3. Password Replacement
In the password change phase,
computes the following
, while
computes
:
Since
is not equal to
, there is no equivalence between
and
, as shown in:
To originally authenticate , needs to confirm the validity of ; but it is impossible to check this. As a result, the home agent cannot authenticate a mobile node in the password change phase, and the password replacement cannot be accomplished. Moreover, there is no contribution to change the password. This means that by computing , can change the password as it wants, without accomplishing any other steps.
5. The Proposed Scheme
In this section, we propose an enhanced scheme to remedy the faults of Farash et al.’s scheme. Our scheme also consists of three phases. In each phase, , , and are involved, and use a timestamp as a nonce. After receiving a message, they first validate a timestamp to ensure that old messages cannot be used in replay attacks. We use the same terms as Farash et al.’s scheme does. However, to apply our scheme to wireless sensor networks, we regard as a mobile sensor node. Clearly, and are server systems, which have a powerful computing capability. On the other hand, is a battery-powered sensor node, which has less computing capability. In the registration phase, registers for , and gives secret parameters in a secure manner. and establish a trusting relationship through this phase. Then, roams in a foreign network, and tries to receive roaming service from . Since is not a mobile sensor node of , wants to authenticate through . For this, the login and authentication phase is necessary. It is assumed that and share a long-term secret key beforehand, the same as in Farash et al.’s scheme. and are supposed to use when they try to authenticate each other. Meanwhile, in the password change phase, , with the aid of , securely changes the secret key, as well as the password. Each phase is described in detail as follows.
5.1. Registration Phase
The first thing
accomplishes is to register for
in the registration phase.
Figure 4 shows this phase:
selects its identity
and the password
. In addition,
chooses the random number
as a salt of a one-way hash function.
then submits
and
to
through a secure channel. Upon receiving the registration request message,
, using its secret key
, computes three secret parameters for
as follows:
where
is the secret key allocated only to
. Then,
secretly stores
in its database, and sends
,
,
, and
to
in a secure way. Finally,
stores
,
,
,
, and
.
5.2. Login and Authentication Phase
When
visits a foreign network and logins to
,
anonymously authenticates
through
.
and
then share a session key for secure communication.
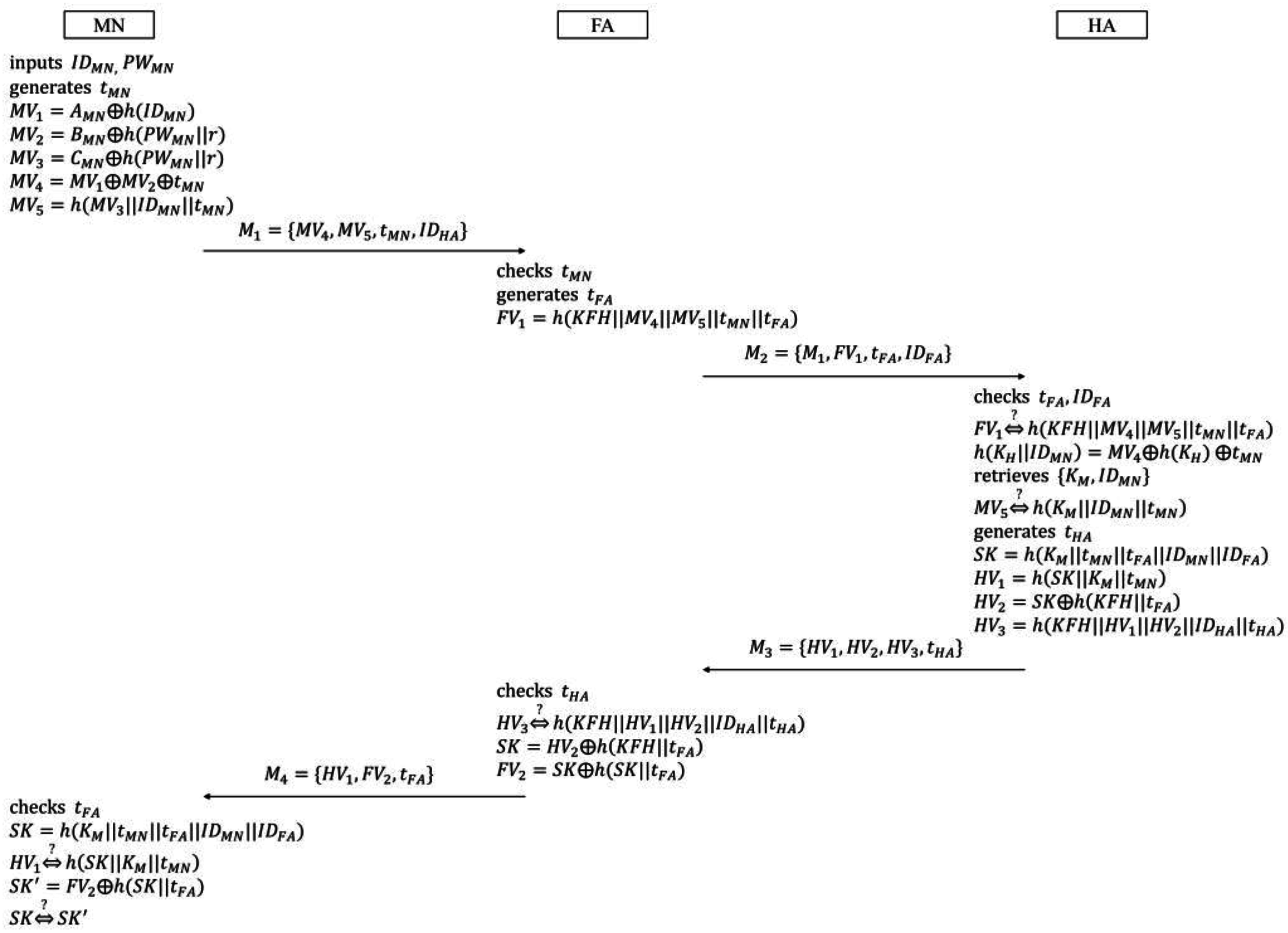
Figure 5 illustrates the login and authentication phase:
- (1)
inputs
and
to make the login request message. Then,
generates the timestamp
, and loads
,
,
,
, and
to compute
’s verifiers:
Next, sends the login request message to .
- (2)
, which receives
from
, first checks
to confirm whether it is valid or not. If
confirms the validity of
,
also generates the timestamp
, and computes
’s verifier as follows:
Then, sends the authentication request message to .
- (3)
After receiving
,
first checks
and
to confirm whether
is valid or not, as well as whether
is an ally or not. If
confirms the validities of both
and
,
fetches the secret key
corresponding to
, and checks the equivalence between
and
. If they are equal,
computes:
Then,
searches
from its database, using
as a keyword. If there are no value matches with
in the database,
regards
as a forged message. In this case,
does not move on to the next step, and informs
of this. Otherwise,
checks the equivalence between
and
. If this is successfully verified,
generates the timestamp
, and computes the session key and
’s verifiers:
Then, sends the authentication response message to .
- (4)
Upon receiving
,
computes
) after checking
, and checks it equals
. If the equality holds,
computes the following session key and
’s verifier, to send the login response message
to
:
- (5)
After receiving
,
first checks
, and computes the session key:
To authenticate , checks the equivalence between and . If this is confirmed normally, obtains by computing . Then, checks equals to authenticate . Finally, and complete mutual authentication of each other, and share the session key between them.
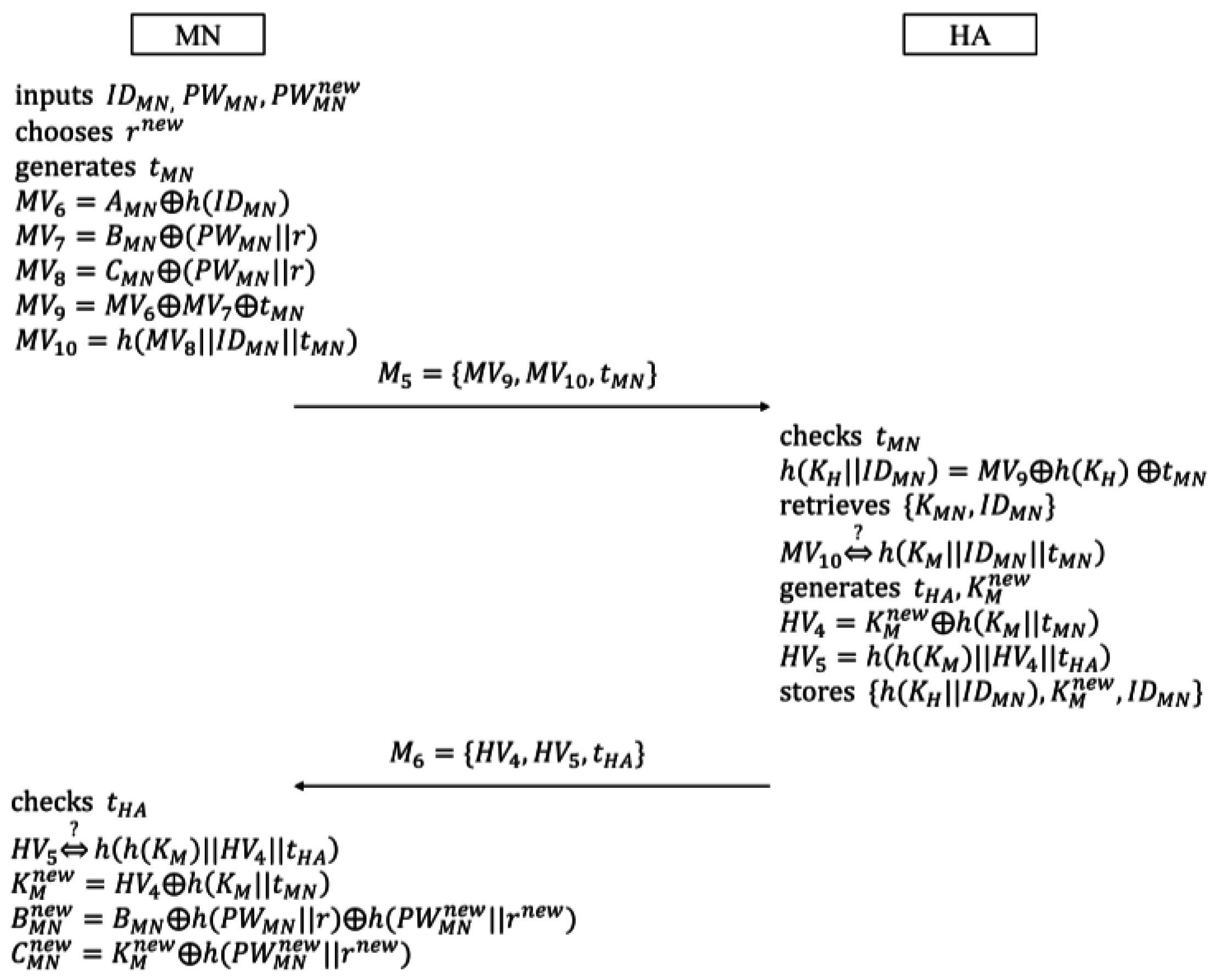
5.3. Password Change Phase
In this phase,
not only renews its password, but also the secret key.
can change the password for itself, without being authenticated by
. However, in order to change the secret key, it is necessary for
to accomplish the password change procedure with
.
Figure 6 shows this phase:
- (1)
inputs its identity
, the current
, and the new password
. In addition,
chooses the new random number
as a new salt of a one-way hash function, and generates the timestamp
. Then,
computes the following verifiers in the same form as they are in the login and authentication phase:
Next, sends the message to .
- (2)
, after receiving
, checks
to confirm whether it is valid or not. Then,
computes
. In addition,
, using
as a keyword, searches for
from its database. If it is impossible to search
due to no matching value,
immediately stops continuing, and informs
of this. If not,
computes
, and checks that it equals
. To renew the secret key
,
generates the timestamp
and the new secret key
, and computes the following verifiers:
Then, after replacing with , sends the message to .
- (3)
Upon receiving
,
validates
, and then checks the equivalence between
and
. If both
and
are successfully verified,
computes the new secret key
after checking :
Finally,
computes the following secret parameters, and replaces
with
:
6. Protocol Analysis
In this section, we present the formal analysis of our proposed scheme usingBurrows–Abadi–Needham logic [
26] (also known as the BAN logic), which is a useful model to prove the validity of authentication and key agreement protocol. The main goal of the login and authentication phase in our scheme is that
and
authenticate each other, and share a session key. Since both
and
participate and equally contribute while establishing a session key, it can be regarded as a two-way key agreement. In addition, in the password change phase, it is the main goal that
and
authenticate each other, and renew
’s secret key. Only
contributes while generating
’s secret key. Therefore, renewing
’s secret key can be regarded as a one-way key agreement.
To prove that our proposed scheme meets these goals, we need to transform the scheme into the idealized form by the analytic procedures of BAN logic. We first define the constructs and some rules of BAN logic as follows:
[Constructs]
: believes .
: sees .
: said .
: has jurisdiction over .
: Formula is fresh.
: and may use the shared key to communicate.
[Rules]
, Message-meaning rule:
, Nonce-verification rule:
Then, using BAN logic rules, we transform our goals into the following forms. The login and authentication phase needs mutual authentication and a two-way key agreement. In addition, the password change phase needs mutual authentication and a one-way key agreement.
[Transformation of the goals of the login and authentication phase]
,
,
[Transformation of the goals of the password change phase]
Next, the messages
,
,
, and
in
Figure 5, and
and
in
Figure 6 are transformed into the idealized messages as follows:
[Idealized messages]
.
In addition, we make the following assumptions to analyze our proposed scheme.
[Assumptions]
, where is or ,
, where is or ,
, where is or ,
,
is unknown for anyone except
Using the above rules and assumptions, we analyze the idealized form of our proposed scheme. The following procedure shows how the proposed scheme meets the goals described above:
- (1)
We apply
and
to
to derive the following statement:
- (2)
We apply
and
to
to derive
- (3)
We apply
and
to
to derive
- (4)
To break conjunctions, we apply the rule of BAN logic to
, then get
- (5)
We apply
and
to
to derive
- (6)
We apply
and
to
to derive
- (7)
We apply
and
to
to derive
- (8)
From
and
, we can deduct the following rule:
- (9)
From
and
, we can also deduct the following rule:
- (10)
We apply
and
to
to derive
- (11)
We apply
and
to
to derive
- (12)
To break conjunctions, we apply the rule of BAN logic to
, then get
- (13)
We apply
,
, and
to
to derive
- (14)
From
and
, we can imply the following statement:
In this step, we achieve
.
- (15)
We apply
and
to
to derive
In this step, we achieve
.
- (16)
We apply
,
, and
to
to derive
- (17)
To break conjunctions, we apply the rule of BAN logic to
, then get
- (18)
We apply
,
,
, and
to
to derive
- (19)
We apply
,
,
, and
to
to derive
In this step, we achieve
.
- (20)
We apply
and
to
to derive
In this step, we achieve
.
- (21)
We apply
,
, and
to
to derive
- (22)
To break conjunctions, we apply the rule of BAN logic to
, then get
- (23)
We apply
and
to
to derive
- (24)
We apply
and
to
to derive
- (25)
We apply
and
to
to derive
- (26)
From
and
, we can deduct the following rule:
- (27)
From
and
, we can also deduct the following rule:
In this step, we achieve
.
- (28)
We apply
and
to
to derive
- (29)
We apply
and
to
to derive
- (30)
We apply
,
, and
to
to derive
In this step, we achieve
.
- (31)
We apply
and
to
to derive
In this step, we achieve .
As a result, , , , and accomplish the goals of the login and authentication phase, and , , and accomplish the goals of the password change phase. By this fact, our proposed scheme preserves mutual authentication and a session key establishment between and , and mutual authentication and a secret key renewal between and .
7. Security Analysis
The proposed scheme guarantees anonymity, hop-by-hop authentication, untraceability, resistance against password guessing attack, resistances against impersonation and forgery attacks, resistance against known session key attack, and fair key agreement. We define two different anonymity preservations in this paper. One is weak anonymity preservation against a passive adversary who accomplishes a passive attack, like eavesdropping. The other is strong anonymity preservation against a valid but malicious node. Clearly, a malicious node is more powerful than a passive adversary because it possesses a valid sensor. If a scheme guarantees strong anonymity, it also absolutely preserves weak anonymity. The detail analysis of our scheme is described below.
7.1. Strong Anonymity
Among the transmission messages, only
and
contain
’s identity
, which is formed as:
An adversary who refers to a malicious sensor node can know and . Clearly, a valid sensor node can provide , while can reveal . Thus, it is easy for the adversary to know and . However, although knowing and , there is no way to get from and . This is because is one of the input parameters of a one-way hash function, and it is always used with the secret key or . Namely, only the entity who knows or can obtain . As a result, the proposed scheme guarantees strong anonymity against a malicious sensor node.
7.2. Hop-by-Hop Authentication
In the login and authentication phase, each entity, , , and , needs to authenticate the others. Trusting relationships between and , and and make it possible for them to check each other’s identities. First, after computing , can authenticate , by checking . Since is only known to and , a successful verification of implies normally computes and . can also authenticate , by checking with the verified . is another entity other than that can compute , but there is no reason for to compute instead of . This means that only can compute a valid . Second, by verifying , can authenticate , since is a securely pre-shared secret key between and . In addition, can anonymously authenticate through . Although has no information related to , can authenticate , by confirming that ensures the identification of . Lastly, can authenticate , through verifying . For the same reason as , can identify , due to . Since is the only entity to compute using and , checking makes authenticate . As a result, the proposed scheme provides hop-by-hop authentication among , , and , while they accomplish the login and authentication phase.
7.3. Untraceability
If there are transmission messages that have the same value throughout several sessions, an adversary can trace those messages, and know all the messages that originate from one sensor node. However, since they always contain different timestamps, every transmission message in the proposed scheme is unique in each session. In addition, an adversary cannot link two or more different sessions of the same sensor node. Therefore, the proposed scheme preserves the freshness and untraceability of every message in every session.
7.4. Resistance Against Password Guessing Attack
An adversary can eavesdrop any transmission messages, but there is no way to get the sensor node’s password from those messages. The reason is that no transmission messages contain the password itself, or even related information. Even if the secret parameters and a salt stored in the sensor node are revealed, it is still impossible to obtain the password. An adversary can generate a lookup table to make pre-computed hash values with candidate passwords and salt. However, changing salts in the password change phase makes it impossible to generate pre-computed hash values. Therefore, in the proposed scheme, the possibility to verify the correctness of a guessed password does not exist, and a password guessing attack is impossible.
7.5. Resistance Against Impersonation and Forgery Attacks
If an adversary can compute
formed as
, he or she is able to impersonate
, by sending a valid login and authentication request message. However, this is absolutely impossible, since the adversary cannot know
and
. Meanwhile, suppose that the adversary makes the following forged message
, and sends it to
via
:
where
is the identity of the adversary,
is the timestamp generated by the adversary,
is the secret key of the adversary, and
is the fake secret key of
. Then, after computing
,
tries to search
in its database. Unfortunately,
finds no matching value, and then it recognizes the fact that the adversary sent
.
7.6. Resistance Against Known Session Key Attack
Even if the session key established between and is revealed, there is no way to compute the next session key, using the exchanged messages, and . To compute the session key, it is necessary to know the sensor node’s secret key or the long-term secret key , which is shared between and . Clearly, an adversary cannot compute the session key, since he or she does not know or . Moreover, since every session key contains unique timestamps, they have no relation with each other. For this reason, the proposed scheme is resistant against known session key attack.
7.7. Fair Key Agreement
When , , and perform the login and authentication phase, the session key contains two timestamps generated by and , respectively. This implies that and make the same contribution to the freshness and randomness of the session key. In other words, both and contribute equally during the establishment of the session key. As a result, the proposed scheme achieves fair key agreement.
8. Security and Performance Comparisons
In this section, we compare security and performance of our scheme with the previous schemes of Jiang et al., Wen et al., Shin et al., Gope and Hwang, and Farash et al. To analyze security of each scheme, we apply the following security features to them:
SF1: Weak anonymity,
SF2: Strong anonymity,
SF3: Hop-by-hop authentication,
SF4: Untraceability,
SF5: Resistance against password guessing attack,
SF6: Resistance against impersonation and forgery attack,
SF7: Resistance against known session key attack,
SF8: Fair key agreement,
SF9: No verification table.
In addition, we apply the experiment result of Li et al. [
4] to analyze performance. The following notations show the execution times of each operation:
H: Execution time of a one-way hash function (1H ≈ 0.0005 s),
S: Execution time of a symmetric operation (1S ≈ 0.0087 s),
E: Execution time of a modular exponential operation (1E ≈ 0.522 s),
To describe concisely, we also use the following terms:
Table 2 denotes the security comparison of each scheme.
Table 2 shows that our proposed scheme provides more enhanced security than previous schemes do. However, the schemes of Wen et al. and Shin et al. and our scheme need to maintain a verification table. The verification table stored in
contains information for user authentication. Namely, it contains identity/counter pairs in Wen et al.’s scheme, identity/password pairs in Shin et al.’s scheme, and identity/secret key pairs in our scheme. Looking up this information takes time. However, considering
’s strong computational power, it is negligible.
Meanwhile,
Table 3 compares the computation cost in the login and authentication phase. Our proposed scheme, which is based only on low-cost functions, needs the lowest computation cost among all schemes.
Table 4 shows the performance comparison in the password change phase. In the schemes of Jiang et al., Wen et al., and Gope and Hwang,
changes his or her password without any help of
. Whereas, the schemes of Shin et al., Farash et al., and our scheme require that both
and
participate while updating
’s password. Clearly, the schemes that
performs the password change phase alone have a little bit better efficiency. However, the computation cost of the password change phase in each scheme is slightly different, and thus it does not affect the performance of all over the scheme.
Table 5 shows the total computation cost of each scheme. Consequently, as shown in
Table 5, our proposed scheme runs the fastest and has the highest efficiency.
9. Conclusions
In this paper, we first prove that Farash et al.’s scheme fails to guarantee strong anonymity, foreign agent authentication, or password replacement. To remedy these weaknesses, we propose an enhanced security authentication scheme. The secret key for each sensor node and the password by hashing with a different salt enhance the security of our scheme. By comparing our scheme with other recent schemes, we show that it is more secure from various aspects. In addition, to reduce the computation time, our scheme only uses low-cost functions. Performance comparison shows that, as compared with the previous ones, our proposed scheme provides better lightness. This means that it provides better efficiency. Consequently, the proposed scheme is more suitable for battery-powered sensors and wireless sensor networks.