1. Introduction
It is noticeable that the automation industry has substantially improved in the last couple of years. The integration of hardware and software components produces better drivability and customer satisfaction. A vehicular ad hoc network (VANET) contains mobile vehicles with on-board processing units (OBPU) and roadside units (RSUs) that assist vehicles [
1,
2,
3]. Vehicle-to-vehicle (V2V) communication is fortified to provide improved information to the drivers regarding roadside accidents, traffic jams, etc. This improves driver safety and the driving comfort of the vehicle in city traffic and on highways [
4]. Highways, crossroads conditions, weather conditions, and vehicles monitoring are now part of the VANET important safety applications that must be complied. Examples of the safety applications include: Slow stop vehicle advisor (SSVA), post-crash notifications (PCN), and collision/congestion avoidance (CCA). These safety applications are important for VANET. VANET utilizes these safety applications to acquire prior knowledge of crossroads, highways, and knowledge of other vehicles conditions. In addition, safety applications enable drivers to execute sound judgment. Through safety applications, drivers are capable to obtain real-time information needed in order to enable them to initiate logical judgment and prevent further road and highway accidents occurrence. Regarding SSVA, vehicles that have slowed down or halted convey messages or information while utilizing warning signals message received from the network and take appropriate action. The warning signal messages sensitizes the surrounding vehicles in the VANET that may be in danger. With regard to PCN, messages are conveyed to highway patrols for further assistance through neighboring vehicles. Neighboring vehicles are closer to each other such that trust establishment in them becomes an urgent issue with VANET. The trust gained through neighboring nodes would enable them to acquire accurate and real-time information of accidents and any emergency situation on roads. It will also identify any denial of service (DoS) and intrusions on emergency activities that may have been encountered in the network. Moreover, safety applications such as SSVA, PCN, and CCA are connected with the RSU and are also deployed in VANET and connected at the traffic management office (TMO). However, the connection of these safety applications with the RSU requires improvement and efficient information delivery. The safety applications and the network devices can function appropriately and also ensure timely notifications about any accidents and road emergency situations. In addition, installation of VANET and appropriate deployment of the RSU with safety applications can help disseminate and process warning messages accurately in real-time without delay. Moreover, it is anticipated that warning messages can be conveyed in a timely manner through the VANET, through which the message can be relayed to other vehicles. The warning messages are usually generated at the TMO and may include notifications of DoS and intrusion attack activity in the network. Some of the DoS and intrusion attacks include congestion/collision (CC), link breakdown, and bad road conditions. CC of vehicles can occur in VANET at any time on the road due to the behavior of the disabled vehicle or accident which requires immediate attention and notification on a timely basis. In addition, some DoS intrusion attacks which this research investigates include smart and normal intrusions (SNI) attacks. DoS and SNI attacks may cause link breakdowns in the network. DoS and SNI attacks also overwhelm the network and block the entire V2V communication within VANET. DoS and SNI attacks encountered in VANET become road threats. When these occur, they prohibit VANET safety applications to function appropriately. In addition, they may lead to further attacks in VANET, including the bad road conditions and highway congestion encountering of many vehicles. This will also make it difficult for drivers to prevent road casualties in a timely manner. DoS, SNI, and DRA (DoS resilience attacker) all have the tendency to overwhelm the RSU. DoS and SNI can also exploit the RSU computational and communication resources and cause flooding with any requested information. However, the intent of RSUs and their deployed safety applications is to be able to collect and analyze the real-time information from vehicles. The information that is eventually received by V2V communication should be appropriately analyzed and evenly distributed to other neighboring vehicles, connected through VANET and safety applications on timely manner through the end-to-end (E2E) communication process. The E2E communications process in VANET is important; however, E2E communication may experience particular DoS and SNI attacks which can also overwhelm the RSU, which would then require urgent attention. The RSU may waste computational time, especially when it encounters false message or information. Therefore, the RSU requires an efficient and secure storage method to safeguard it from being compromised when delivering vehicle to roadside unit (V2RSU) and V2V messages in VANET [
5].
In VANET, V2V and V2RSU communication storage solutions for propagating safety information to nearby vehicles in a timely manner have been investigated using vehicular cloud and fog computing (VCF) [
6]. The VCF model has been developed to utilize VANET resources efficiently due to fog computing (FC) and cloud-based logical interaction. Based upon VCF, grouped vehicles cooperate and communicate with each other and dynamically share sensing, computation, and resources for decision-making on the road, as well as for improving traffic management and road safety. There are some examples of VCF applications that can be relied upon which include:
Collecting local and highways traffic conditions from neighboring vehicles for planning routes.
Processing the big data traffic information through local and highway traffic management authorities.
Critical collaborative events including road congestion, accidents, and all forms of attacks (including DoS and SNI attacks) can be reconstructed.
Although these application scenarios have utilized FC and cloud-based applications for efficient storage and computations, this scheme has not been not appropriately secured. The authors claim that their proposed scheme has achieved their aim in investigating quality of service (QoS) parameters in VANET. Arguably, due to undetected DoS and SNI attacks, further investigation is needed. We believe fog computing (FC) integration and the hybrid deployment of optimization algorithms (OAs) including Cuckoo search algorithms (CSA), firefly algorithms (FA), firefly neural networks, and key distribution establishment (KDE)/authentication sharing mechanisms is a promising solution for investigating real-time data transmission and QoS parameters in VANET that answers to this question very well. Thus, we believe integration of the KDE/authentication mechanism investigation for the network level and the node level security can be achieved appropriately in order to ensure trustworthiness of nodes and trustworthiness for the entire VANET. In addition, since RSUs play a major role in distributing information in VANET, they can be secured appropriately to provide real-time end-to-end V2V and V2RSU communication. Therefore, it has become urgent to investigate QoS parameters such as delay/jitter and throughput in VANET. Moreover, due to the dynamic nature of VANET, it utilizes a vulnerable wireless link. Wireless link deployment and connection with vehicles and associates connect through multimedia safety applications should be secured when vehicles connect with the RSU [
7]. Since multimedia safety applications are now a part of the VANET system, however, they are easily plagued by DoS and SNI attacks through the RSU. Multimedia safety framework demands high QoS support and evaluation. QoS provision, in general, is required to supports the Media Access Control (MAC) architectures [
8]. MAC architectures for VANET rely on the VANET wireless medium which can be implemented on DSRC (dedicated short range communication) data link technology [
9].
In the past, researchers/authors have conducted several investigations on VANET. The authors’ investigation centered on multimedia safety application framework for determining QoS provision in VANET, which also utilized FC for achieving the network level security protection, using the DSRC data link technology. In addition, the authors have conducted separate investigations on OAs based upon FC while utilizing DSRC data link technology for data transmission. The authors’ investigation involved CSA [
10,
11,
12], FAs [
13,
14,
15] and a firefly neural network [
16]. The aim of the authors was to evaluate QoS parameters for delay/jitter and throughput in VANET. In addition, during the research investigation, a firefly neural network was used to train effective misbehavior of the path delayed in the VANET. Though the authors claimed to have succeeded investigating QoS performance in the network, the QoS evaluation was not complete due to the inability of the researchers/authors to consider the node level security evaluation in VANET. In addition, the authors did not investigate KDE sharing, including hybrid integration with OAs. Therefore, there was a limitation in the evaluation of trustworthiness in VANET, and both real-time information delivery and QoS provision within VANET remain a major concern. FC integration with OAs including KDE sharing can be useful for implementing VANET safety applications, since these schemes have the capability to ensure efficient storage, time sensitivity, trustworthiness, and intelligence in real-time information delivery agendas and QoS in Intelligent Transportation systems. To address these concerns, in this paper, we propose a “Secure Intelligent Vehicular Network using fog computing” (SIVNFC) scheme for FC integration and hybrid OAs deployment including CSA, FA, firefly neural networks, and KDE/authentication to detect the network level and node level security in VANET against DoS, SNI, and other forms of attacks.
The main contributions of this research are:
Fog computing (FC) is integrated with hybrid OAs deployment including: CSA, FA, firefly neural networks, and KDE. FC is used to determine the rapidly stored vehicular information. In addition, the integration and deployment of FC with hybrid OAs and KDE provides intelligence which reduces the search space for real-time information. It also prevents increased communication times. Fog computing is an extension of cloud computing that provides computation, storage services, and network communication services between the end nodes. The determination of the rapidly stored vehicular information process relies on the communication behavior of vehicles in this paper [
17].
Secure the VANET at the node level and the network level for trustworthiness.
Determine reduced jitter and improved throughput for the VANET for real-time data transmission.
Use of regression model to confirm the accuracy of jitter/delay in the proposed SIVNFC scheme as a road safety application.
The organization of the rest of the paper is as follows.
Section 2 presents related work.
Section 3 discusses the DoS attacks, intrusions, and preventive mechanisms for the proposed SIVNFC model.
Section 4 presents extensive simulation results and analysis of the results which includes: The feed forward-backward propagation neural network, regression model, and QoS provision for the VANET.
Section 5 is the conclusion including the future work of this research.
3. DoS Attacks, Intrusions and Prevention Mechanism in VANET
3.1. DoS Attacks
VANET experience DoS attacks [
30]. These attacks intercept the channel at the data link layer. DoS attacks are capable of bringing down the available network resources. Through DoS attacks, the VANET can be exploited through the RSU due to the following:
Resources consumption: DoS attacks consume the available network bandwidth. They inject fake routing messages, resulting in congestion over the VANET. This degrades the end communicating entities performance and introduces jitter.
Signal jamming: DoS attacks have a high tendency to jam the transmissions while using channel interference.
Packet Drops: DoS attacks have a high tendency to drop all or any selected packets. This interrupts the routing process from the source to the destination communicating entities.
The investigation of VANET security provisions, such as certificate-based identification and a authentication mechanism are beyond the scope of this research.
3.2. Attack Principles
Unlike wired architectures where the channel blockage or congestion is always due to the increased flow rates at links with bottlenecks, congestion in a VANET may occur due to the aggregation property of the vehicles. If the attacker densely aggregates his attacks near the victim, the attacker can occupy more communication channels [
31]. The total transmission capacity of one node increases a linearly with the increase in the area. If the node count does not vary, then the hop capacity is O (k), where k is the node count of the network. The data transfer requires a route discovery, and the node count in a route may increase with the increase in the area. Each node has a probability of 1/k of interacting with the channel. There are m nodes that can act as attacking nodes such that the victim node has the likelihood of (1 − m/k) of interacting with the channel.
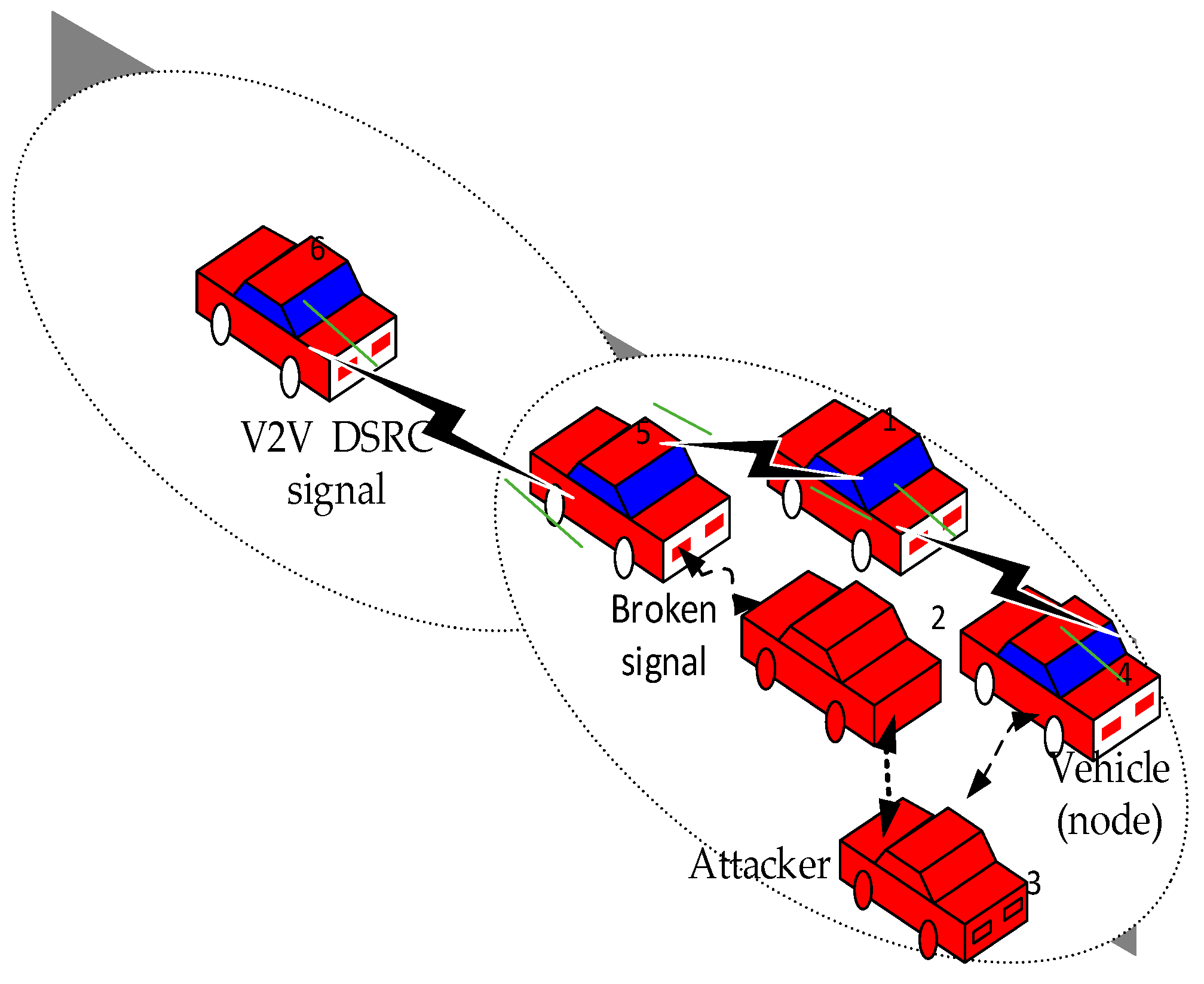
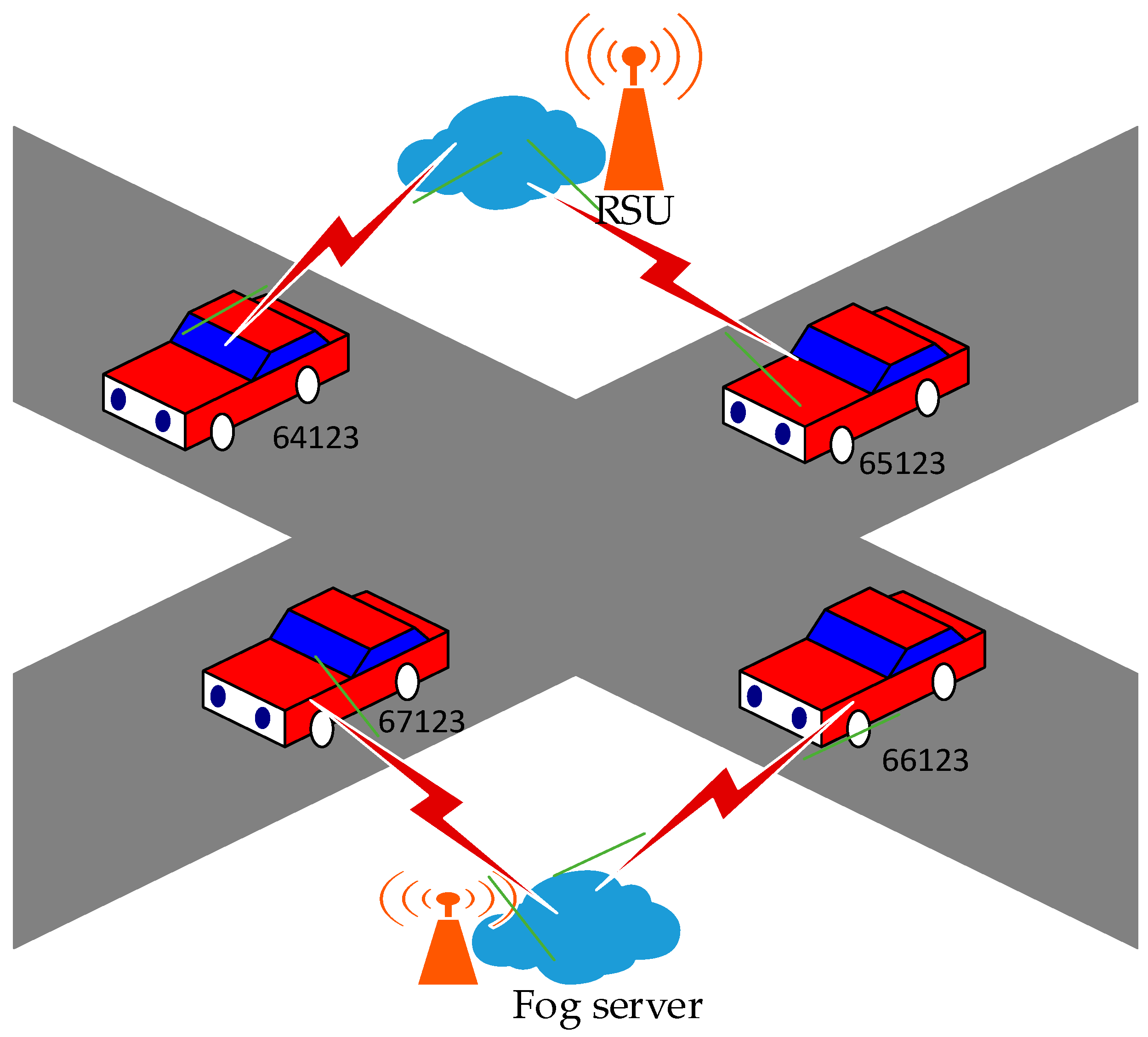
Figure 1 illustrates the channel occupancy and interaction of the proposed model architecture [
32].
VANET utilizes IEEE 802.11 as the most popular V2V DSRC (vehicle-to-vehicle dedicated short range communication) wireless system installed on almost every vehicle where the vehicle/channel congestion/collusion are inevitable due to influence of the attacker vehicle encounter in the network, which could occur at the time when vehicles (or V2V) are required to transmit packets to each other in VANET. CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance) is standard scheme that can be used to avoid such vehicle/channel packet transfer collision/congestion. However, CSMA/CA is only a simple mechanism that can be used to allocate radio resources. In this research, we investigated how vehicle/channel occupancy can cause delayed packet transmission due to misbehavior of attacker vehicle which leads to broken link exposure of the vehicles communication process as shown in
Figure 1.
Figure 1 illustrates channel occupancy scenario based upon the attacker mode of operation.
In
Figure 1, there are two types of vehicles, namely attacker vehicle and normal vehicle. All attacker vehicles have broken signals connections with each other. When attacker vehicle forms a connection with normal vehicle, a delay can be experienced in the network due to channel occupancy as a result of broken signal connection because both normal vehicles and attacker vehicles are in each other’s communication range and the vehicles are traveling on the highway. The first ellipse from left to right has a transmission range (250 m), whereas the next ellipse has an interference range (550 m). Attacker 2 transfers packets to vehicle node 3, and this processes are highlighted in a broken V2V DSRC communicating signal, in which the packet is not received by another normal corresponding vehicle. Now, vehicle nodes 5 and 4 are in the range of vehicle node 3, but since it is occupied by attacker 2, it will have to wait, and an unnecessary delay will occur in the network. The channel occupancy vehicular attacker scenario is also used to illustrate the misbehavior of compromised nodes in VANET due to DoS attacks [
33].
3.3. DoS Attack Illustration
A DoS attack employs multiple vehicles to attain its goal. It locks the job queue of the corresponding vehicle so that it is unable to accept data packet requests from genuine vehicles. Since a DoS attack is distributed over several vehicles, distinguishing authentic users becomes complicated. There are several ways to mitigate the effects of this type of attack, including encryption and the use of classification techniques [
30]. The use of authentication mechanisms can also be beneficial. Sanya Chaba et al. (2017) presented a VANET architectural design for authentication key delivery with less delay between vehicles and with more mobility by utilizing fog and cloud computing. The authors have also introduced fog computing to extend cloud computing to the context of the middle fog layer among cloud and mobile devices for the production of various benefits. In their work, Qi Jian et al. (2018) identified the security goals for VCC (vehicular cloud computing) interoperability.
The authors have provided the AKA (Authentication and Key Agreement) framework for VCC. Notably, the authors have proposed the problems with the challenges for designing a consistent AKA with extra strong security assurance for VCC. A hybrid AKA framework has been suggested that combines the ‘single server 3-factor protocol’ with the ‘non-interactive identity-based key established protocol,’ which computes the performance by a simulated platform. Fog computing is utilized quite often these days for deployment of VANET, but its implementation has not been deployed with any KDE or key sharing for preventing SNI attacks, also utilizing the RSU.
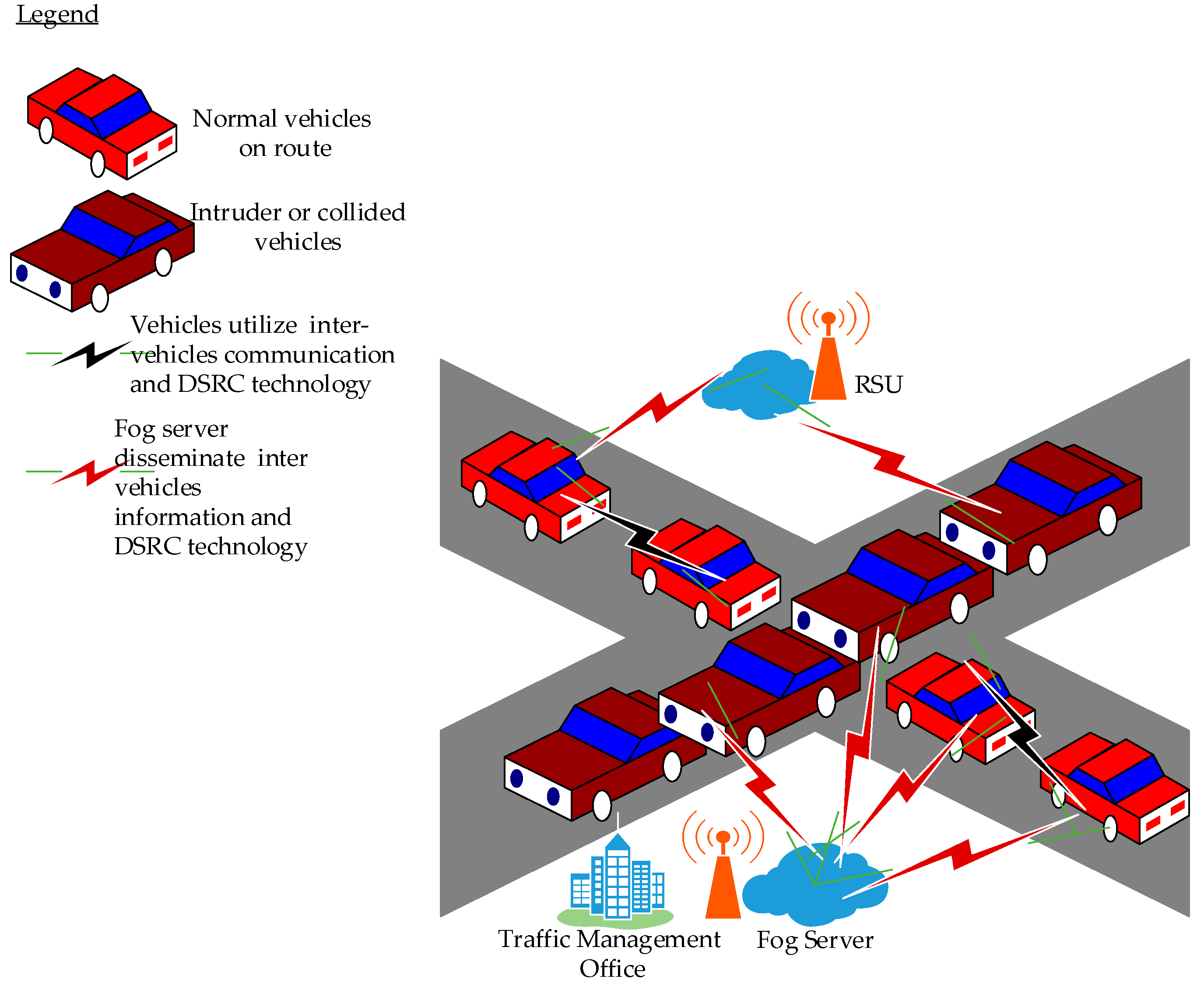
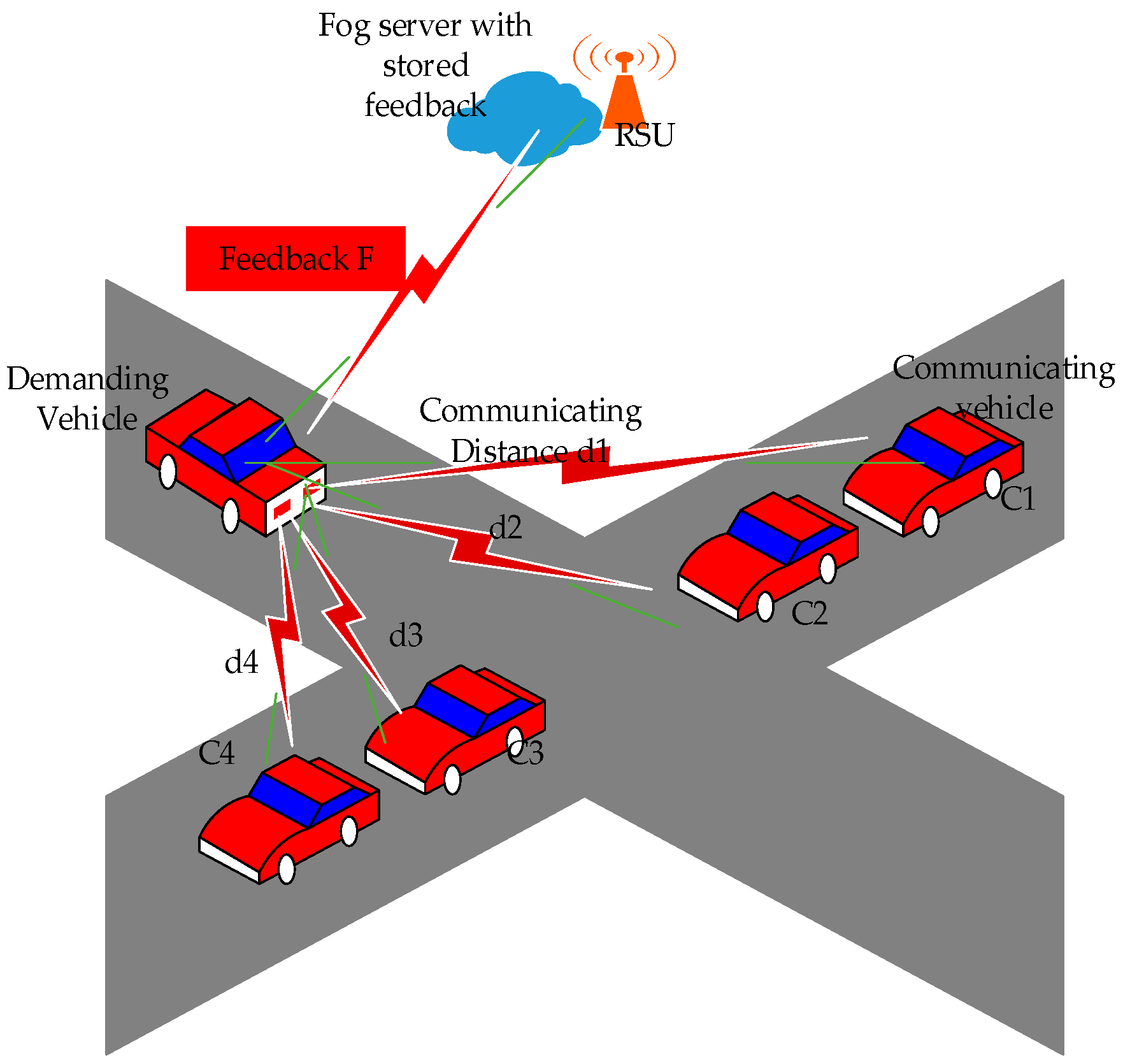
Figure 2 illustrates an attack model scenario with the integration of the fog server with vehicles. In
Figure 2 RSU stands for road side unit. The fog server keeps the information about the vehicles and distributes the required information to other vehicles if required. The intruder may also utilize the same server and may misuse the server’s information to spread false information [
33].
3.4. Intrusion /Attacks Model
Figure 2 illustrate the intrusion/attacker model (IAM). The model detects and mitigates Dos and SNI attacks. The proposed IAM utilizes two types of vehicles, namely normal and intruder or collided vehicles. Normal vehicles are supposed to be on route. Normal vehicles denote all vehicles that have not experienced any form of attacks. Normal vehicles are the type of vehicles that are expected to arrive at their destination safely. The intruder or collided vehicles, on the other hand, are the type of vehicles that have encountered intrusion attacks. Normally they are not expected to arrive to their destination. Moreover, the intruder vehicles have the tendency to introduce delays in the network.
If intruder or collided/disabled vehicles are left unattended and continue to remain in the network, the network will suffer link breakdown and will not function as expected. This will lead to much delay encounter in the network. Delays of the network will lead to further road casualties since vehicles will not be appropriately informed. The proposed IAM initiates a remedy to prevent intruders/attackers in order to lessen road casualties. Therefore, in the proposed IAM, vehicles utilize intervehicle communication and DSRC technology. The vehicles communicate and share safety information with each other vehicle.
The information shared include condition of the vehicle and the road conditions. The information shared may also include congestion/collision and accidents that have already occurred. In addition, the fog server (FS) is deployed such that it addresses the location awareness concern in the cloud. The deployed FS disseminates emergency inter-vehicles information utilizing warning sign to alert other vehicles through the RSU information processing. The warning signal information can be obtained by each vehicle through the RSU and the FS which originates from the traffic management office (TMO). The TMO is the place where road safety applications (RSA) such including as SSVA, PCN, and CCA are deployed and connected with the RSU and the FS. Two inter-vehicle communications, including the FS, utilize DSRC technology. DSRC technology is data link technology which utilizes the IEEE 802.11 standard for transmitting information. Based upon this, real-time information, which convey warning and emergency information about any intruder activity in the network, can be received through the RSA.
The network is also identified with the other forms of intruder/attacker such as smart and normal intrusion (SNI). SNI may sometimes go unnoticed and requires sophisticated approach to detect. Smart intrusions make the network feel like there is no threat in the network. If the intrusion follows a set pattern of dumping the packets, then it becomes easy to identify. However, the smart intrusions do not follow a consistent pattern [
34]. The SNI scenarios that occur in the VANET are depicted as in the figures below.
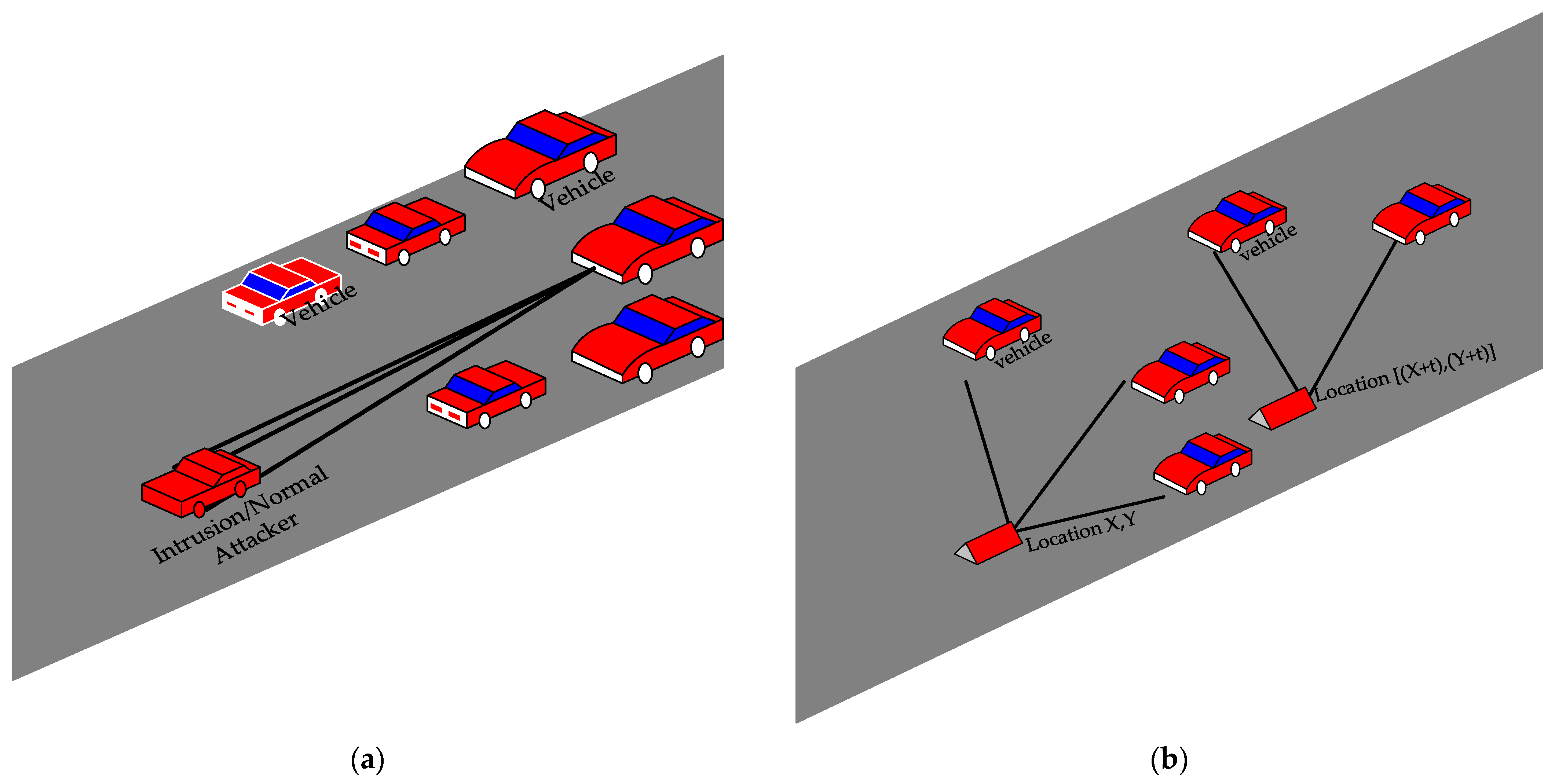
3.4.1. Smart and Normal Intrusion/Attacks Scenario
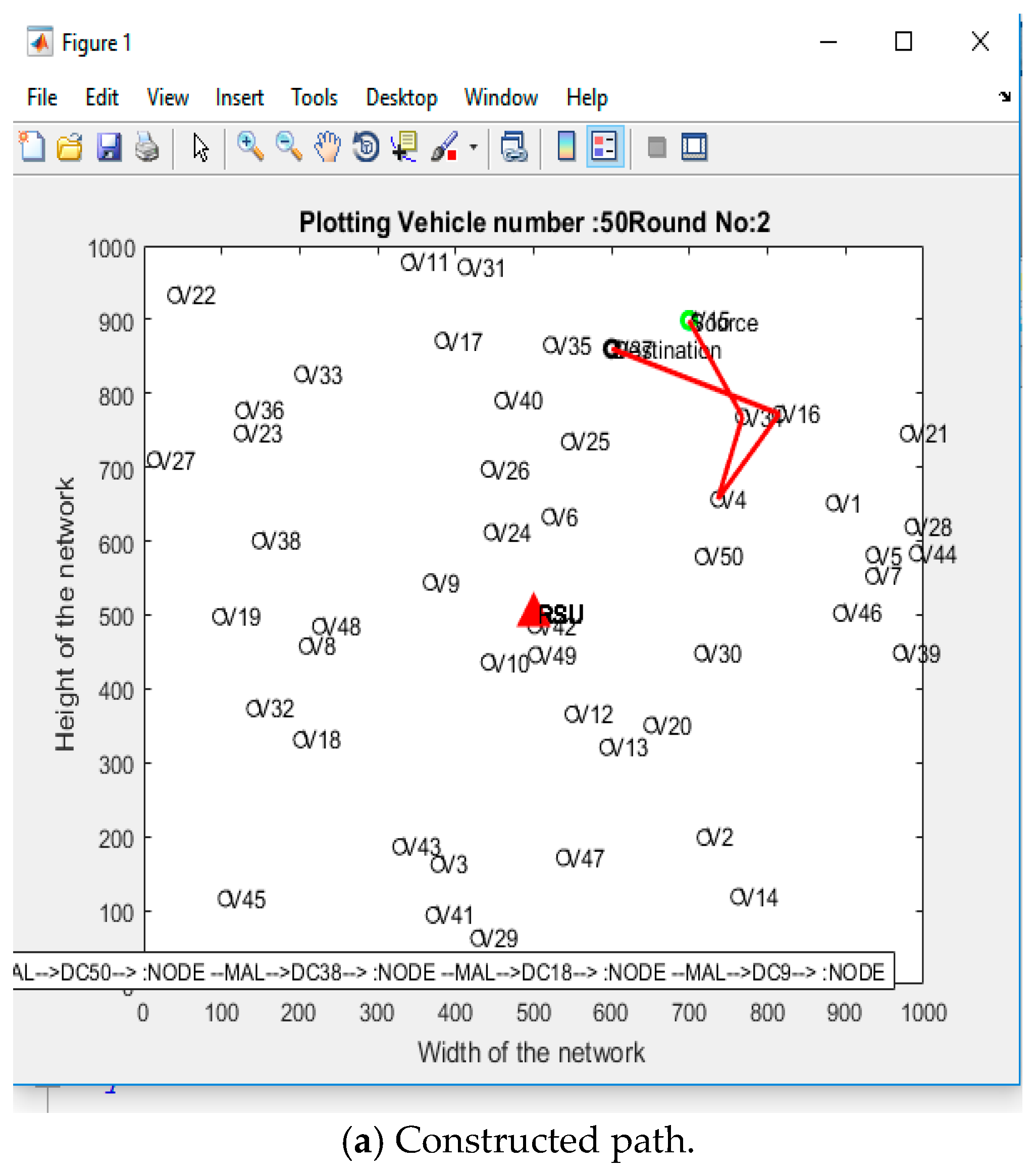
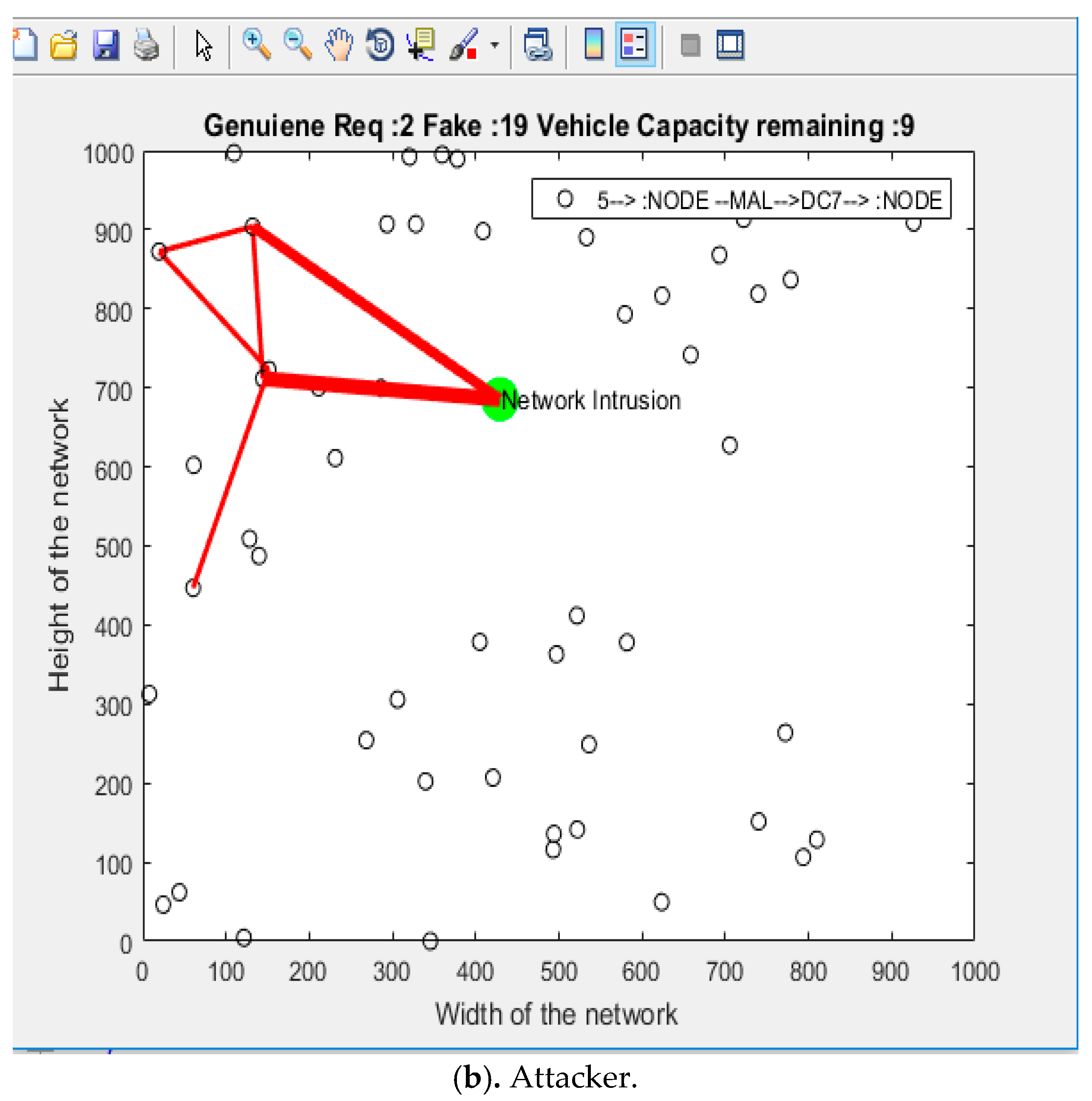
Figure 3a,b represent the normal and smart intrusions (SNI) attacker scenarios. The proposed IAM relies on the SNI intensity to evaluate the delay of the network. The intensity and location of the normal intrusion does not change with the change in the time frame, whereas the smart intrusion changes the location and intensity of the attacks with every instance. As shown in
Figure 3b, the Intrusion is at location (x,y) at time t = 0, and it instantly changes its position at time t = 1 and goes to (x + t) and (y + t). The intrusion even changes the location and intensity of the attack at every instance [
35]. The SIVNFC system architecture prevention mechanism (SAPM) is a sophisticated approach that can be utilized to determine and mitigate the SNI attacker in the VANET as demonstrated below.
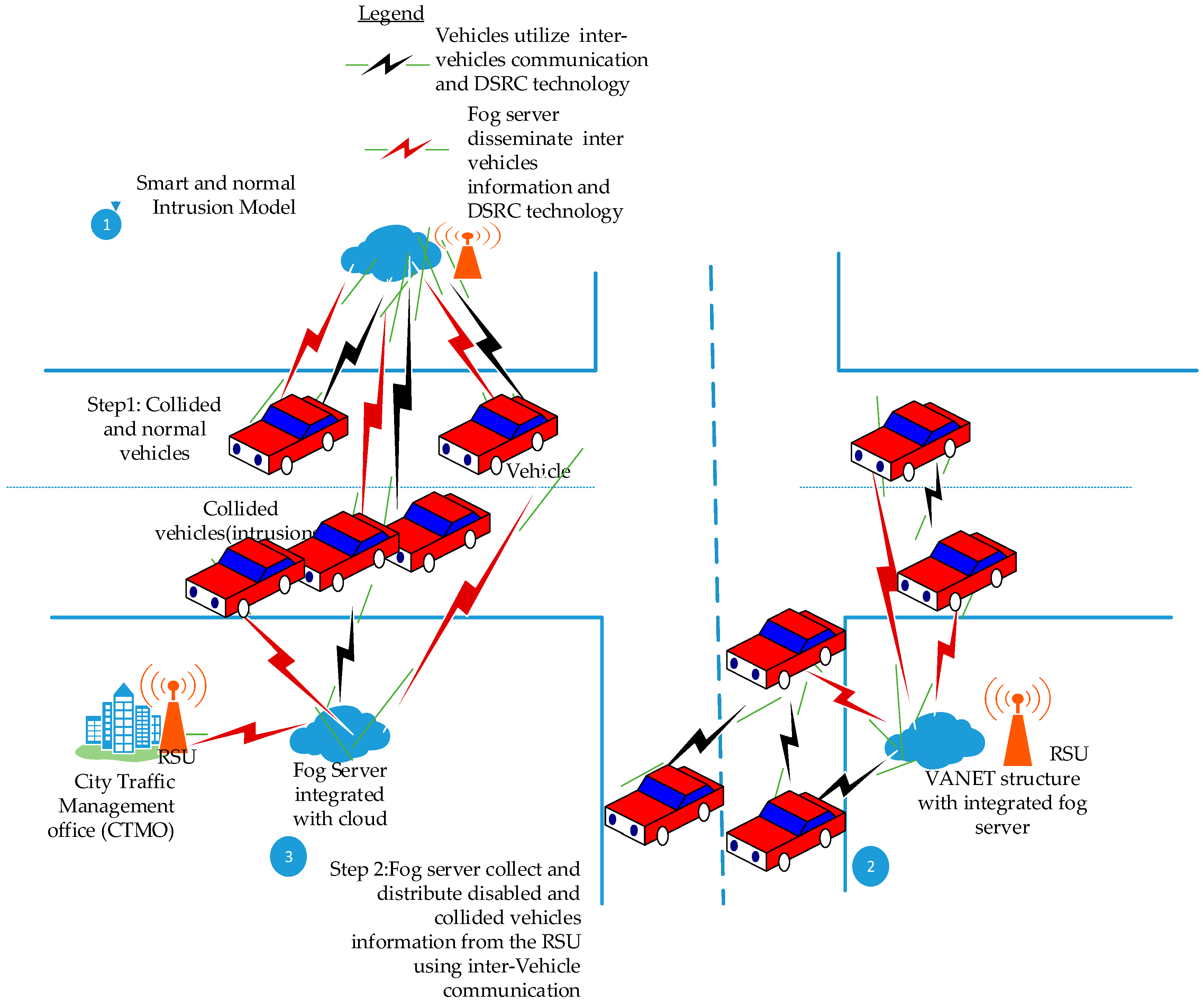
3.5. Proposed SIVNFC System Architecture Prevention Model (SAPM)
Figure 4 depicts the proposed SAPM. In SAPM, vehicles utilize two DSRC technology instances for information transmission (the DSRC technology uses the IEEE 802.11 standard for transmitting information). In one instance of information transmission, vehicles communicate among themselves using intervehicle or V2V communication. In the other instance, the FS forms a connection with the RSU and, through this arrangement, disseminates inter-vehicle information to all vehicles in the network. The information conveyed usually include collusion/congestion, intruder activity of the network such as SNI of vehicles, or information of vehicles that have encountered attacks. The disseminated vehicle information may also include reporting the state of vehicles conditions and the road conditions that are threatening.
The proposed SAPM also employs further preventive measures to detect and mitigate all forms of attacks, including DoS attacks that may go unnoticed. Some of these attacks include but are not limited to packet drop, jamming of channels, and the RSU resources consumption overutilization. Two models are deployed in the SAPM, namely IAM and VANET structure with integrated for server (VSIF) models. The models utilize steps and scenarios for prevention and protection of the network against DoS and SNI attacks. In step 1, collided/disabled vehicles or intruder activity are detected and reported to the other vehicles in the network utilizing the IAM. The IAM detection of intruder/attacker has already been explained in detail above. In scenario 2, the VSIF model is deployed. The deployment of the VSIF model is also illustrated in
Figure 5. The VSIF model relates and connect with the proposed SAPM as below.
The VSIF model deployment in SAPM includes the RSU connection with the FS Step 3. Scenario 3 (
Figure 4) illustrates the deployment of VSIF model, the FS, and the RSU connection. FS collects intruder or collided vehicles or any unusual network attack information. The FS also obtains information concerning all forms of DoS and SNI attacks that may be eminent in the network through the RSA which is installed at the TMO. The TMO is presumed connected with the RSU. The VSIF model utilizes inter-vehicle communications connections based upon the following deployment explanations.
RSU (Road side unit): RSUs are gateways. Gateways are also deployed in the proposed SAPM which establishes connections with the FS. The RSU is equipped with network devices. It utilizes DSRC inter-vehicle communication packet transfer based on IEEE 802.11.
RSU to FS: VANET utilizes V2V and V2RSU communication to propagate safety/non-safety information. RSUs communicates with each other as well. Thus, RSU behaves as the FS backbone. Wireless and wired connections are formed between RSU and FS (
Figure 4). The RSU is aligned with FS.
Fog Server to Fog Server (FS to FS): FSs are identified at different locations. They interact with each other. Consequently, a pool of VANET resources that is localized can be managed through the TMO. This connection can be achieved via vehicular control center traffic management or TMO, as shown in
Figure 4. Thus, direct wireless and wired communication between peer FS can be possible. In addition, collaborative services provision and the FS peer contents delivery can be initiated at the TMO, which improves the entire SAPM. In addition, the cloud is logically connected with the FS and has the tendency to aggregates information.
Fog Server to Cloud: In the proposed SAPM, FSs utilize fog computing to address location awareness concern of cloud computing. Thus, cloud computing represents a central portal of information which does not require location awareness for information processing. The cloud centrally controls the FS in various locations. A FS possesses the capability to aggregate the information that it has obtained from other FSs. The VSIF utilizes centralized computations whereby FS transmit intervehicle information that it has received from the cloud to the application users [
36], utilizing the DSRC technology.
Due to open nature of the VANET deployment and associated vulnerabilities, RSU and the FS utilize an authentication/KDE preventive mechanism in the proposed SAPM for ensuring real-time packet delivery.
The proposed SAPM utilizes two levels of authentication/KDE preventive mechanisms for the FS and the RSU aggregation of information, namely, the fog Level (FL) and the RSU Level (RSU-L). The RSU-L considers the vehicle’s displacement and jitter in the VANET, whereas the FL utilizes the Lagrange Polynomial for the identification of untrusted nodes as well [
37].
3.5.1. FL Prevention Mechanism
The FL keeps one global key for the entire network; hence, each vehicle is identified by the global key itself. Distributing the global key in the vehicles is insecure; therefore, the vehicles follow a shared system. Each vehicle has its own shared value.
When a vehicle requests the information from a server either directly or through an RSU, the fog server will demand three shares from any vehicle in the network or will choose two of them randomly [
38]. Three total shares will be considered, including the demanding vehicle. The fog server will utilize the Lagrange polynomial to calculate the following.
The Lagrange polynomial S(X) containing degree
demands
vehicles with coordinates
is given by:
where
is given by
If written explicitly for n = 3 vehicles,
The separate polynomial can also be formulated as with Szeto (1975), which was later called Lagrange’s fundamental interpolation.
The key that is generated by the integration of separate polynomials is represented as
If matches the network key, only then does the vehicle pass any information from the fog server. Second, the RSU level security is also applied, which makes the network more secure. To understand the structure of this security, the pseudo code is also given as follows.
| Pseudo Code Algorithm for Share Verification |
Notations:
SODFSV: Shares Ordering Demanded by FS from Vehicles:
I: Initial Share for Vehicle Value being Empty
SCV: Share for Current Vehicles
SKV: Share Key Value
SVCV: Share Vehicle Current value
: Individual Number of Share for Vehicle
ICNSV: Initial Counter Number for Share of Vehicle
CSVBI: Current Share for Vehicle/Node Begin Iteration
Share Key Vehicle/Node Identification or Initial Reference
: Share Numerator key for Vehicle/Node Identification in Network
: Share Denominator key for Vehicle/Node Identification in Network
: Individual Vehicle Chosen for Share in next Iteration
: When first Vehicle Share is Chosen there will be 2 remaining Share for the Vehicle
SVCNS: Share for Vehicle Chosen Current not same as next Share Chosen
RSCV: Remaining Share Counter for Current Vehicle
Input. , j,
Process
1. Initialization
;
SODFSV=2
;
2. If ISV;
3. for
While ICNSV = =1; then
a. CSVBI = SVNID;
b. for
c. CSVBI =;
d. If CSVBI.
e. ;
4. RSCV= RSCV +1;
5. End if
6. End for
8. -
9.
10. I
11. SKV= SVCV*I
12. End for
Output SCV |
The pseudo code uses the interpolation order [
39] of two and only three nodes for communication. Whether the nodes will be selected for the data communication or not depends upon the final key result, which is calculated using Lagrange’s method. One key generation method requires a numerator and a denominator. The numerator is calculated using network IDs of the vehicles that remain for the iteration [
40]. For example, we consider 45, 53, and 61 to be the nodes that are selected for the verification. Therefore, the numerator value
for
is
The denominator
is calculated by multiplying the difference of the network IDs of the remaining nodes. For 45, the
value will be
. The verification key would be the product of the Shared key of 45 to
. Similarly, the
for 53 and 61 will be calculated. The final verification key would be the sum of all the generated verification keys.
If the
is equal to the network security key, then the nodes are selected for communication. Lagrange’s theorem randomly selects the nodes for verification. Though the verification process of Lagrange is good enough, to make it more efficient, the CSA is applied to select the nodes for which the verification keys will be generated. The CSA uses the node distance and its feedback to judge whether it should be considered for key generation or not.
Table 1 shows the specifications considered for the Cuckoo search algorithm (CSA).
LD is the location difference between the demanding node and the communicating node. The CSA fetches the feedback values of nodes from the fog server, which also obtains intervehicle information through the RSU.
As shown in
Figure 6, the main node computes the distance between the demanding node and the communicating node. It fetches the feedback from the fog server through the RSU and utilizes it for the fitness function.
where
is the distance between the fog and the user and f is the feedback of the fog server.
The data transfer will take place once the route discovery process is complete. A network suffers from two kinds of security issues—namely, the node level and the data level. This paper further addresses the node level security [
41].
3.6. Node level Security
VANET is a type of ad hoc network whose survival depends on vehicle/nodes cooperation and trust. Therefore, trust between vehicles requires enforcement. Trust models can be categorized into vehicle/node trust or data trust.
With node level trust security, vehicles/nodes evaluate trustworthiness between them, whereby each vehicle crosscheck their neighbors redundant sensing data with their results. Trust in vehicles can be calculated through a lightweight method and data which includes three parameters: Sensing a data consistency value (or throughput), VANET communication ability, and the Vehicle/nodes remaining lifetime. Trust assertion makes inconsistent data from DoS and SNI attacks to be detected [
42].
The node level security is achieved by calculating the trust of neighboring nodes. The calculated trust values are stored in the fog server for further processing.
The mathematical equation for node level security in the VANET is calculated by determining the trust values of the node which is given as:
The above equation shows that there is
number of trust factors. N(Y) indicates the trust value of the node of ith category. It is seen that if B is greater than or equal to N, the associated risk is less than threshold value and then node x will do work for Y. Node X keeps on checking to see any recommendations about Y node from neighboring nodes, and, if so, the trust value is calculated using the following equation.
where z indicates number of neighboring nodes and N
x(Y) indicates the trust value of node X on node Y.
The vehicles that have been identified as trusted nodes interact with the RSUs through the FS to obtain the data in the appropriate order [
43]. The proposed SIVNFC scheme utilizes an RSU prevention mechanism whose model is as follows.
3.7. RSU-L Prevention Mechanism
The network deployment is based upon the specifications in
Table 2.
| Pseudo Code for Vehicle Placement |
// To maintain the randomness in the network, the network is set in a random manner
1. For each n Nodes
2. Xloc(n)=1000*rand// Create a random x coordinate
3. Yloc(n)=1000*rand
4. lace(Xloc(n),Yloc(n))// Place the node in the network
5. End For |
Vehicles have different sets of parameters. The functions are designed to initiate the network parameters. A real-time simulation may result in different structures. In addition, a network may not include any fixed structure; however, for the sake of any simulation, some parameters should be initialized.
| Pseudo Code to Initialize Vehicle Features |
1. For i=1:Nodes // Loop running for each node
2. Delay_n(i)=Random D; // Include a delay value if the node is acting normally
3. Delay_t(i)=; // For now, the expected reality is unpredictable; hence, just the random //architecture is it set to be the square of the normal delay
4. End for |
As the delay is initialized in a similar fashion, the other network parameters such as the jitter and packet drop are also initialized. The battery consumption is not a problem in the case of a VANET since the battery continues charging as long as the vehicle is running [
44].
Figure 7a,b represents the path construction and attack mode of the attacker.
Figure 7b shows that the intensity of the attacker varies at different times. If the intensity is high, the attacker is attempting to dump more packets. The above attacker scenario is demonstrated in the equations below.
where Tpd is the total packet drop, Pdn is the total number of dropped packets in the normal mode, and Pda is the dropped packets when the network is threatened.
where Pdr is the packet delivery ratio, and Tp is the total number of packets. The random behavior of an attack makes the network architecture more sophisticated. Now, the challenge is to identify them. The proposed solution utilizes the feedforward back propagation neural network (FFBP-NN), and the general utilities of the FFBP-NN are given in
Table 3.
The Artificial Intelligence (AI) method is made up of two sections:
● Training and Classification
The classification section is used in the identification model. The training module utilizes the jitter as the training parameter. To train the neural network, the neural network toolbox in MATLAB is utilized. The training layer is provided with the target set as well. The target is the identification of the nodes. The training consists of two phases. First, training is performed for the identification of the path, and then the training is performed for the identification of the affected vehicle(s) in the route [
45].
The following equation can be defined:
where Jtr is the jitter, Dp is the delay of the path, and ‘a’ and ‘n’ represent the advanced (under threat) and normal situations, respectively. Nd is the network delay. For each path in every iteration, there will be jitter. The proposed solution uses the first 400 iterations’ data for training and then uses the next 600 iterations’ data with the training structure for identification.
| Algo Train_Neural (Iteration_Data,Total_Iterations) |
For i=1:Total_Iterations
Training Data (i) =Iteration Data (i);
Targetable (i) =Path ID;
End For
Neural=Initialize Neural (Training Data, Target Label, k); // k→ Total Neurons (30 in this case)
NeuralI.TrainParam.Epochs=100; // Total training iterations
Train (NeuralITraining_Data, Target_Label); // Training with Initialized Neural and Training data
End Algorithm |
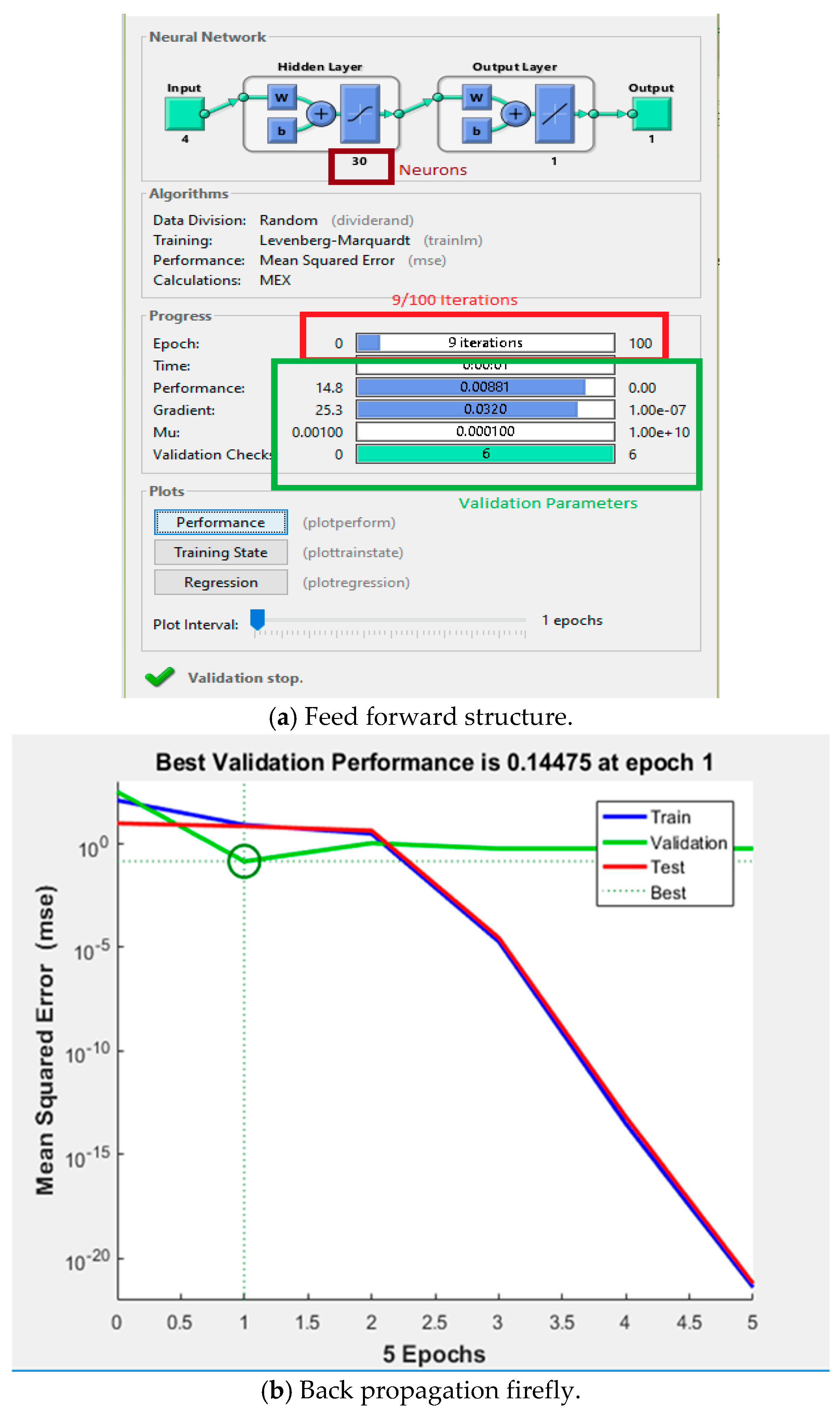
The training section results in FFBP-NN structure given in
Figure 8.
3.8. Identification of Affected Node(s) and Recovery
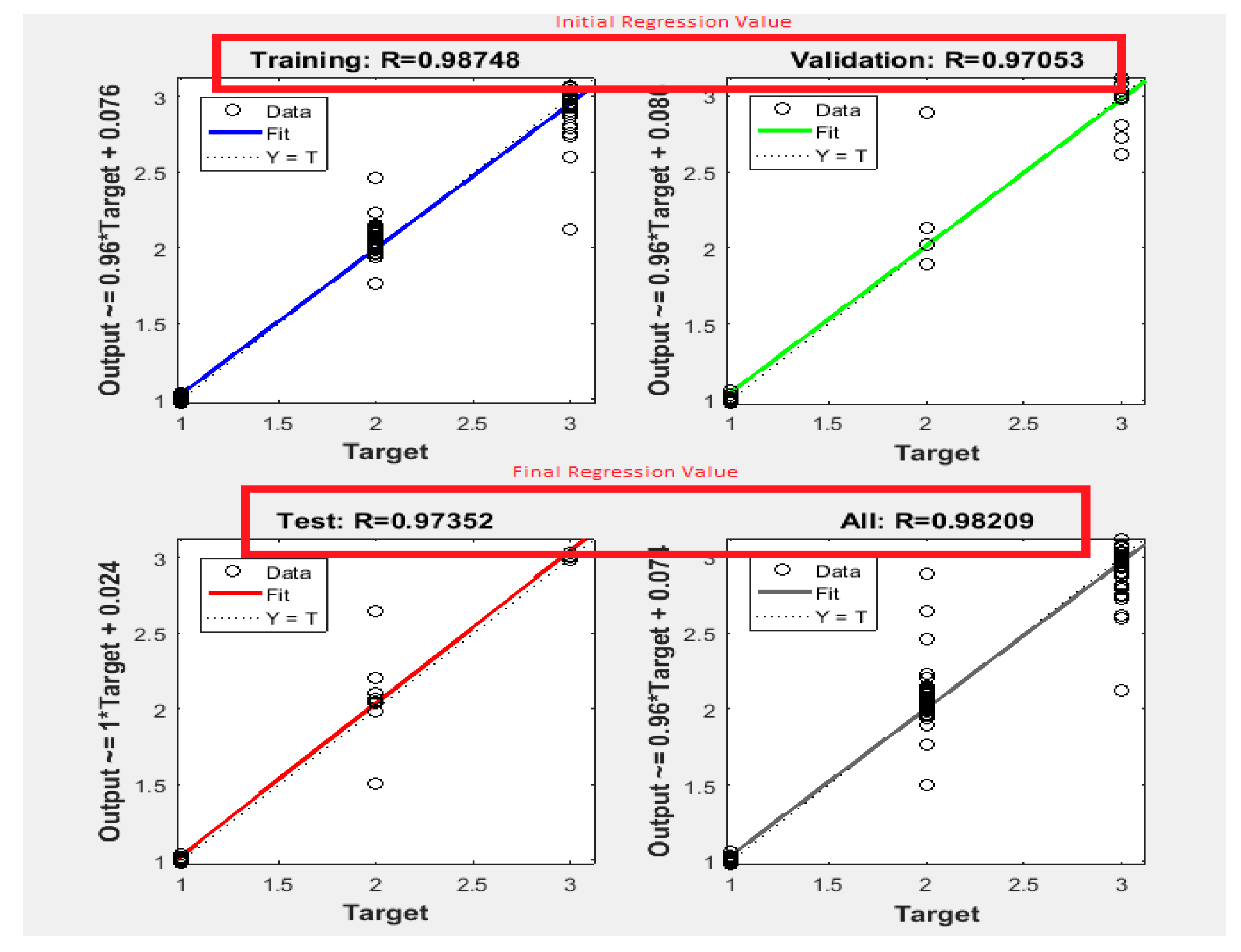
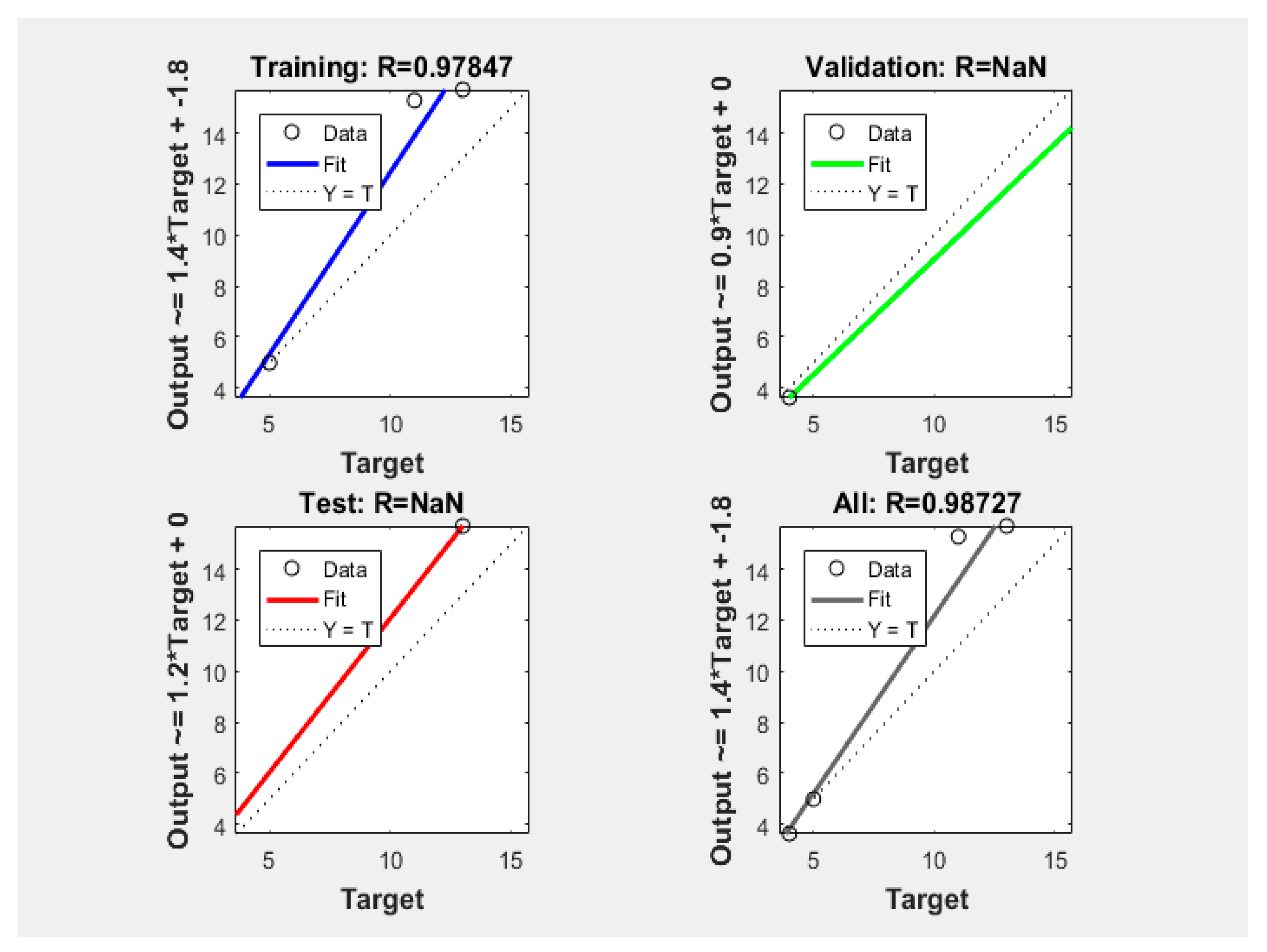
The proposed research work also presents a regression model with backpropagation.
Figure 9 represents the regression model and values.
5. Conclusions
This paper proposed a fog-integrated VANET scheme termed SIVNFC. The proposed scheme simultaneously considers the node level and network level security. The node level security includes the fog computing merged with the VANET, a node level security mechanism, a new fitness function of the Cuckoo search, and a collaborated neural network structure. The node level security establishes trust collaboration with all the neighbors of the network. The node level trustworthiness ensures that the entire network rapidly delivers packets to the entire network system. The proposed SIVNFC scheme also prevent DoS attacks and SNI from attacking the entire network. The proposed SIVNFC scheme is an ad hoc network, and new vehicles, including DoS attacks, may easily enter into the network. To prevent the network from being accessed by foreigners (or outsiders) until they become part of the home network, the proposed SIVNFC scheme uses Lagrange’s interpolation method through which node level and the network level security attacks such as DoS attacks entry is secured.
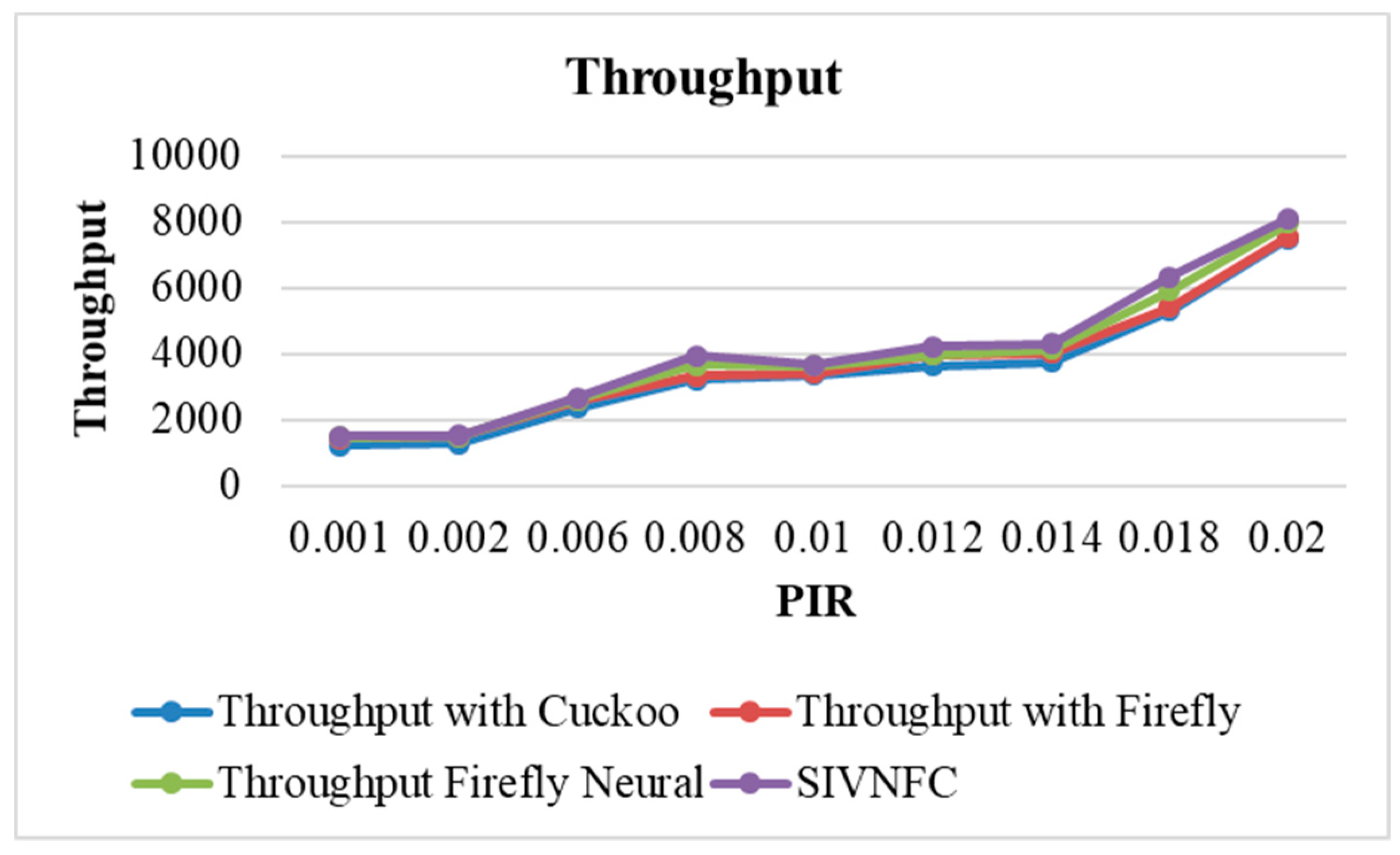
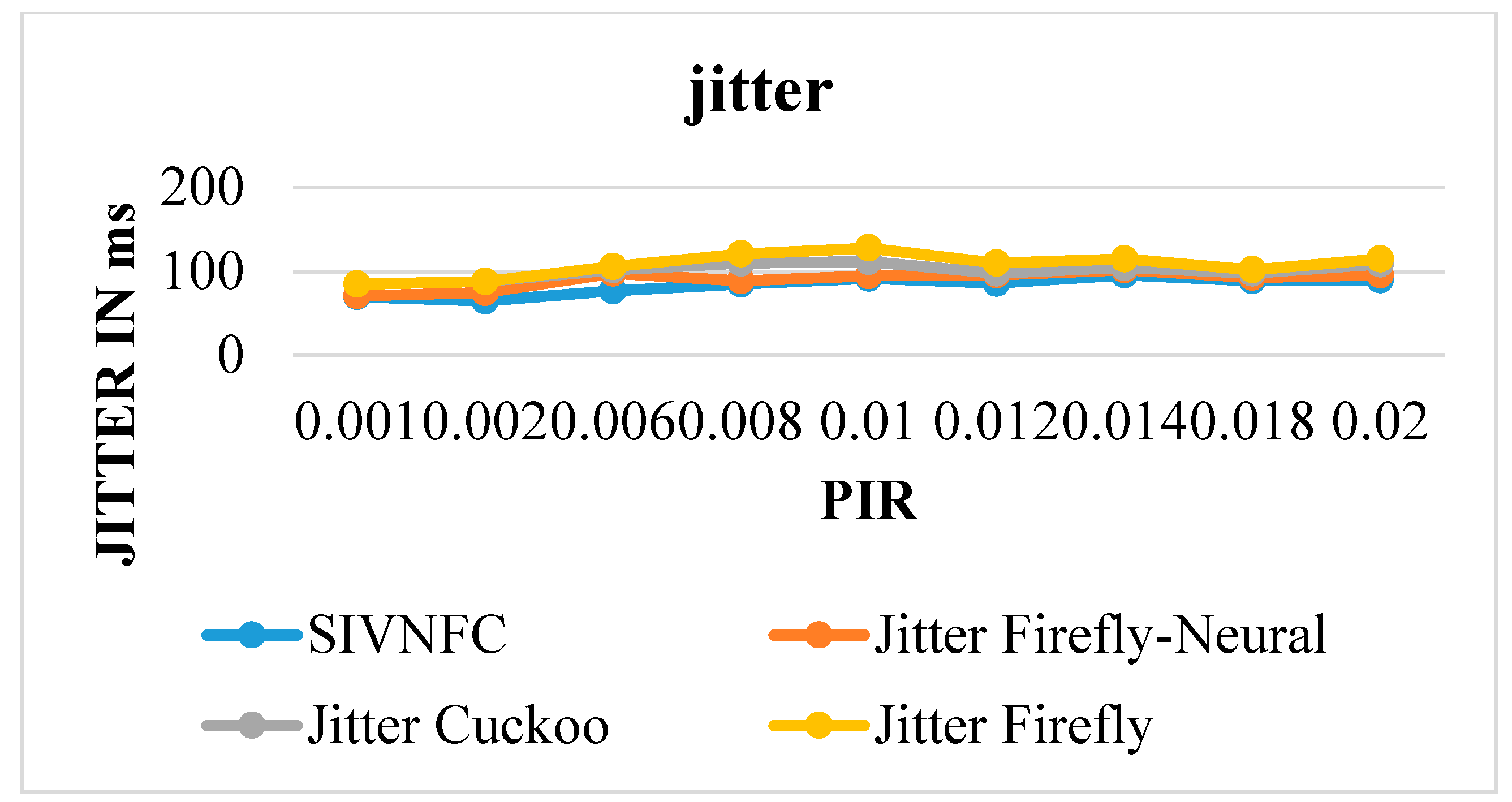
The proposed SIVNFC scheme also utilizes an integrated SAPM. The SAPM includes intrusion/attacker and VSIF models. Both models deployment in SAPM are utilized to mitigate all other forms of attacks and secure the network. The models are also deployed to provide real-time information in the network through safety application deployment of the RSU at the TMO, where information can be processed on timely to reduce delay and enhanced the throughput in the network. The evaluation of the proposed SIVNFC scheme is evaluated using QoS parameters—namely, the throughput and jitter. The proposed model is also compared with the firefly algorithm, a single neural network, a neural network combined with the firefly algorithm, and the Cuckoo Search algorithm.
The evaluation of the QoS parameters is done using the PIR as the basis of every simulation. The proposed SIVNFC scheme provided a total throughput of 8100 for the PIR value of 0.2. The maximum throughput of the network was also offered. For the same scenario, the second-best throughput was 7900 for the combination of Firefly and the neural network. The jitter is inconsistent throughout the simulations, and it varied based on the model architecture and algorithm. Even after nonlinear computations, the jitter for the SIVNFC scheme is a maximum of 96 ms, whereas it is 102 ms for the firefly neural network.
The proposed SIVNFC scheme also utilizes the regression model to indicate the reduced delay of the network. The current research work has potential for future research directions. The neural network structure can be varied to assess if there are any differences in the QoS parameters. A hybrid classifier can also be tested to see if it enhances the current proposed neural architecture. This paper utilized Lagrange’s interpolation method, and it would be interesting to examine the performances of other interpolation methods such as Spline and the Polynomial fit. A combination of interpolation methods can also be considered.