This section presents an analysis of some of the existing security frameworks to strengthen the SDN-IoT architecture based on BC technology and ML methods. The analysis is structured into themes as follows:
4.1. BC-Based Security Integration
This subsection presents selected studies on BC integration in SDN, summarised in
Table 2. Fan et al. [
8] proposed BCC, a permissioned BC framework securing SDN/SD-WAN control planes against insider threats and PKI vulnerabilities. Using Auth-SC and Coord-SC smart contracts, the system achieved sub-second consensus for certificate and key distribution with minimal networking overhead. Rahouti et al. [
9] developed BRAVE-SDN to protect east–west controller communication with BC and identity-based cryptography, enabling decentralised key generation and mitigating impersonation and MITM attacks; formal AVISPA analysis confirmed robustness, though specific performance metrics were not reported. Chattaraj et al. [
10] introduced PBAC-SDN, combining attribute-based encryption, certificate-based key agreements, and private BC for multi-layer access control, showing low computational overhead (switch: 7.064 + 0.021n ms; controller: 1.735 + 0.006n ms) and reduced communication cost (2336 bits per access). Zainal et al. [
11] addressed scalability and Northbound interface security with SBAC-SDN, reporting CPU peaks of 60.3% across eight controllers, memory under 8 GB, response times below 1 s, throughput of 4.34–4.67 req/s, and zero errors. Kovacs et al. [
14] examined BC deployment on SDN controllers for large-scale ISP networks via virtual ISP federations, demonstrating robust connectivity over encrypted TCP/UDP links, while highlighting the need for evaluation of smart contracts, traffic isolation, and scalability.
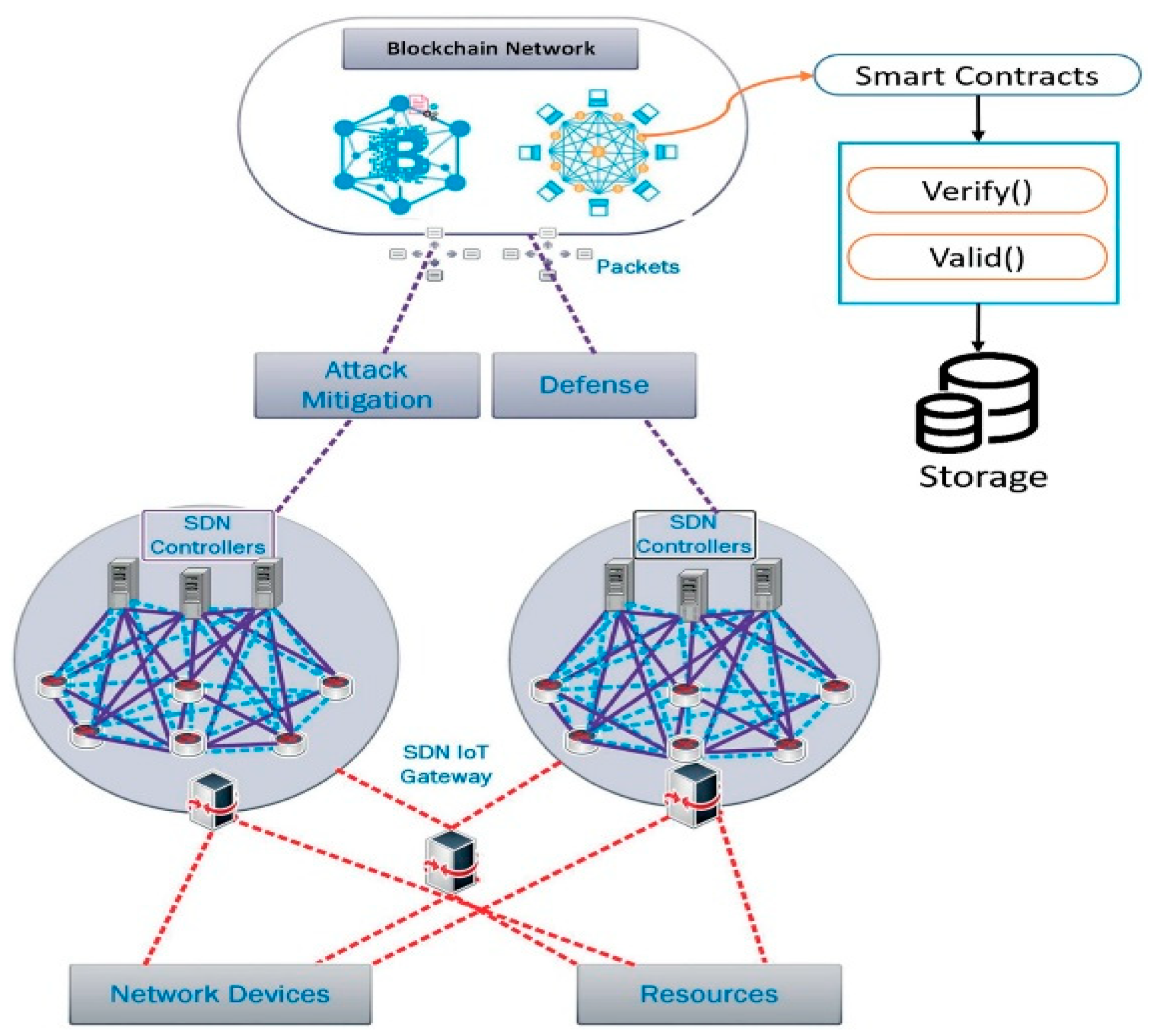
For BC-SDN-IoT architectures targeting security, energy efficiency, and routing, Yazdinejad et al. [
29] designed a cluster-based SDN controller framework combining public and private BCs, SDN-managed authentication, and energy-aware routing, achieving ~97% accuracy with improved throughput, lower end-to-end delay, and reduced energy consumption in Mininet-WiFi simulations of six clusters with 90 devices. Ghamdi [
50] proposed a hybrid SDN-BC classifier to mitigate flooding attacks, showing ~23% lower packet-loss recovery, ~50% energy reduction, higher throughput, and lower response time in Mininet/OpenStack tests with 50 devices. For smart building and condominium deployments, Rahman et al. [
51] presented DistB-Condo, a BC-based IoT-SDN-NFV framework using energy-efficient CHS and smart contracts, achieving higher throughput, faster response, improved bandwidth resilience under DDoS, and efficient CPU utilisation. Similarly, DistBlockBuilding [
52] combined multi-controller SDN, IoT sensing, and BC for secure, private data transfer, showing increased throughput, lower round-trip times, and stable performance with growing node counts, outperforming OpenFlow-based and MINA solutions. Both studies highlight BC-SDN applications for energy-efficient, secure, and resilient smart building environments, with further evaluation needed for BC performance and optimisation.
As shown in
Table 2, BC-SDN integration improves security, scalability, and efficiency across multi-controller, IoT, and smart networks. For instance, frameworks like BCC, BRAVE-SDN, PBAC-SDN, and SBAC-SDN enhance trust, access control, and consensus while maintaining low latency and computational overhead [
8,
9,
10,
11]. Large-scale ISP deployments show strong cross-layer communication [
14], and IoT or smart building architectures achieve higher throughput, lower delay, and reduced energy consumption, primarily in simulation or emulation studies [
29,
50,
51,
52]. These solutions are generally effective, though further work is needed to address real-world scalability, energy optimisation, and deployment challenges.
Particularly, all studies employed BC mechanisms across all SDN layers, utilising varied consensus and trust approaches such as PBFT, permissioned ledgers, smart contracts-based, and dual-ledger architectures. Ethereum, being either private, permissioned, or hybrid, is the most common BC substrate, with Hyperledger Fabric and other permissioned solutions less frequent. Moreover, SDN controllers are typically specified, such as Ryu, ODL, POX, or multi-controller setups, though a few studies did not report details of the controller used. Likewise, evaluation focuses on communication, computation, and energy metrics, with several studies reporting throughput, latency, packet loss, or efficiency indicators. However, reporting detail is uneven: while some works provided quantitative measures of CPU, memory, energy, and related performance metrics, others rely on protocol analysis without numerical data. Test methods include simulations, emulation, and prototype deployment, indicating a mix of conceptual and empirical validation methods.
4.2. BC-SDN-IoT Security Integrations
This subsection presents studies integrating BC into SDN-IoT/IIoT, summarised in
Table 3. Rahman et al. [
3] proposed Block-SDoTCloud, a hybrid SDN-BC architecture securing IoT cloud storage. SDN provides centralised control, load balancing, and dynamic management, while BC ensures immutability and distributed trust. Simulations with Mininet-WiFi and OpenFlow showed improved throughput, faster file transfers, reduced response times, and stable CPU usage during DDoS attacks, though the evaluation was limited to DDoS. Islam et al. [
16] combined SDN, BC, and NFV for smart city IoT, employing a CHS algorithm to prioritise high-energy nodes. Experiments using Mininet-WiFi and Ethereum demonstrated higher throughput under increasing transactions, stable CPU, and linear gas growth for over 1200 requests, with limitations including energy overhead from multiple controllers and unmeasured end-to-end delays.
For IIoT security, Dildar et al. [
5] introduced a hybrid BC architecture with lightweight cryptography, smart contracts, and off-chain storage, supporting 10,000 devices with 100 TPS, BC latency of 5 s (2.8 s with DPoS), and ~30% energy reduction, constrained by simulation-based validation. Rahman et al. [
53] proposed DistB-SDCloud, a four-layer SDN-BC-IIoT architecture covering data extraction, SDN control, distributed BC, and cloud management. Experiments showed improved throughput, latency, bandwidth stability, and DDoS resilience compared to standard SDN and BC solutions, with future work suggesting AI integration. However, these performance metrics are not directly comparable across studies due to heterogeneous network sizes, traffic models, and hardware.
For large-scale IoT and cloud networks, Faizullah et al. [
17] developed a permissioned BC-integrated SDN framework where servers act as BC nodes for access validation, policy enforcement, and flow-table management. Evaluations with ten controllers and 990 IoT nodes showed stable bandwidth (~2.1 Gb/s) and efficient flow updates under high traffic, limited by controlled experimental settings and potential overhead in larger deployments. Rahman et al. [
54] proposed SmartBlock-SDN, a layered SDN-BC framework incorporating CHS, rogue switch isolation, flow-rule verification, and IDS monitoring. Simulations indicated up to 50% energy reduction at SDN controllers, lower end-to-end delays, and higher throughput, constrained by fixed-node assumptions and limited-scale testing.
Table 3 presents SDN-BC studies that enhance security, efficiency, and scalability in IoT, IIoT, and cloud networks. Architectures such as Block-SDoTCloud, SmartBlock-SDN, and DistB-SDCloud enhance throughput, reduce response times and delays, stabilise CPU usage, and cut energy consumption by up to 50% under DDoS and high-traffic conditions [
3,
53,
54]. Large-scale IoT cloud frameworks maintain stable bandwidth (~2.1 Gb/s) and efficient flow updates [
17], while smart city deployments show linear BC gas growth and stable CPU under 1200+ transactions [
16].
Similar to
Table 2, all studies used BC mechanisms across SDN layers, often with explicit cross-layer coordination. However, consensus and trust methods vary, including distributed ledgers, hybrid public–private chains with DPoS, permissioned consensus, and access-control validation. Among these, Ethereum still maintains its position as the most common BC substrate, while permissioned and hybrid deployments are less frequent. Most works involved SDN controllers or OpenFlow switches, though a few omit controller details. In terms of evaluation, metrics such as throughput, delay, or response time, bandwidth stability, and energy consumption were utilised. Reported results generally indicate throughput improvements, reduced delays, and low energy usage; however, the level of quantification varies across studies. Test methods include simulations, emulations, and large-scale experimental setups. While some studies incorporated DDoS or adversarial scenarios, others focused on protocol execution and resource efficiency. This indicates that, across the studies, the environments vary in both deployment realism and depth of method used. However, limitations remain across studies, including reliance on simulations, fixed-node assumptions, unmeasured end-to-end delays, and limited attack coverage, indicating a need for real-world validation and broader threat testing.
4.3. ML-Based Security Integration in SDN-IoT
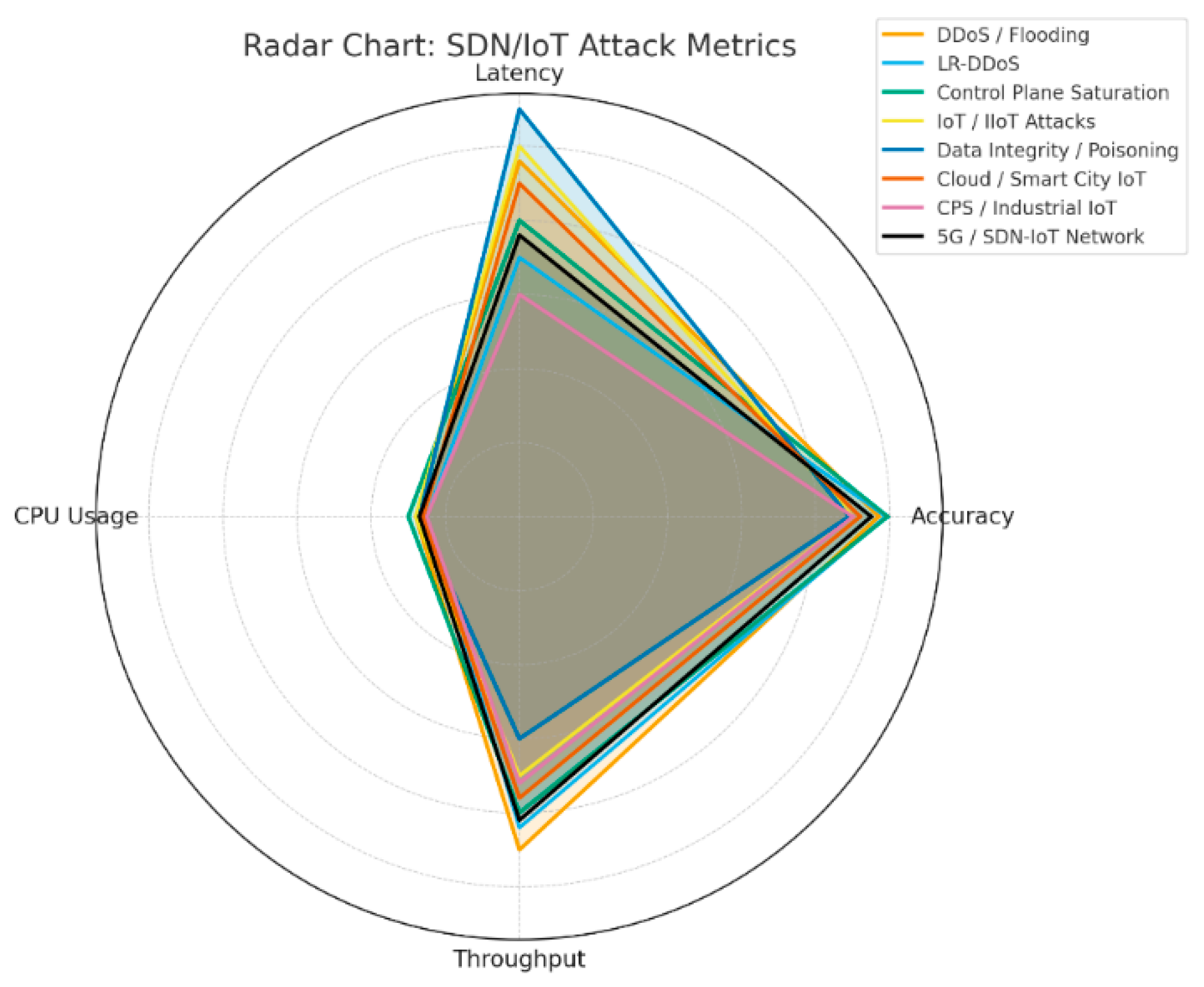
Studies on ML-based anomaly detection in SDN-IoT/IIoT environments show extensive use of ensemble and DL methods, summarised in
Table 4 and
Table 5. Maheshwari et al. [
12] proposed an Optimised Weighted Voting Ensemble (OWVE) combining six classifiers (SVM, RF, GBM) with hybrid optimisation (BHO) to secure control and data planes via a POX controller. Evaluated on CIC-DDoS2019 and CAIDA-2007 datasets, it achieved 99.416–99.359% accuracy and a 0.4978% false alarm rate. Limitations included dependence on dataset features and the absence of large-scale deployment metrics. Hnamte et al. [
55] developed a DNN integrated with the Ryu controller for real-time traffic classification, achieving 99.98–100% accuracy and minimal false positives. Mininet-based simulations showed efficient CPU use and rapid mitigation, though IoT-specific datasets and scalability remain open issues.
Several studies focused on ensemble-based methods. Bithi et al. [
22] combined RF with Recursive Feature Elimination (RFE), achieving near-100% accuracy and zero false positives, with XAI providing transparency. Hirsi et al. [
56] enhanced this with RF ensembles and PCA, reaching 100% accuracy, precision, recall, and F1-score, with low testing times (0.25364 s). Kaur et al. [
57] introduced a Hierarchical DDoS Defence System (HDDS) with multi-layered adaptive ML, achieving 95% overall accuracy (100% for high-rate attacks) and effective mitigation of diverse traffic types. Other studies compared algorithms and explored domain-specific applications. Lai [
58] benchmarked multiple ML algorithms in simulated SDN environments, with RF achieving an ROC AUC of 1.00 and XGBoost/LightGBM excelling in minority-class attacks. Oyucu et al. [
58] targeted SDN-based SCADA systems, proposing an optimised DT ensemble with boosting, bagging, and RUSBoost, achieving 95.17% accuracy, 97.3% sensitivity, and 94.8% specificity. Limitations include reliance on simulations and potential scalability challenges.
Furthermore, studies on SDN-enabled IoT DDoS detection show diverse approaches integrating ML, FL, and RL techniques. Yousuf and Mir [
59] proposed DALCNN, an RNN with Tanh2 activation, deployed on the ODL platform. The three-tier architecture (Device, Controller, Application) achieved 99.98% detection accuracy and improved throughput, latency, and controller performance. Mitigation was implemented via firewall rules, though the framework remains limited in attack diversity and activation function exploration. Similarly, Sinha et al. [
27] introduced DDoSBlocker, a lightweight RF-based system integrated with the Floodlight controller. It achieved 99.71% accuracy, a 0.51% FPR, and sub-second mitigation while maintaining low CPU use. Future directions include adaptation for malicious switches and dynamic traffic. Bhayo et al. [
61] developed a supervised ML framework with the SDN-WISE controller, employing DT, NB, and SVM classifiers for 96.1–98.1% detection accuracy. Resource use remained efficient (~30% CPU/memory), but evaluation was limited to simulations and lacked mitigation. Kavitha and Ramalakshmi [
62] extended detection to a distributed multi-controller architecture, achieving 99.99% accuracy, reduced execution times, and improved CPU utilisation, enhancing resilience against controller failures, though scalability remains uncertain.
Federated and online learning approaches also feature prominently. Ali et al. [
63] proposed Weighted Federated Learning (WFL), where local ANNs share model weights aggregated via preference weighting. The system achieved 98.85% accuracy, with reduced communication overhead and enhanced privacy. However, validation was simulation-based, and real-time deployment challenges persist. Alashhab et al. [
23,
64,
65] introduced multiple frameworks: an LSTM-based RNN for sequence-dependent IoT detection (98.88% accuracy on Edge-IIoTset), a Passive-Aggressive model for continuous LDDoS detection, and an earlier modular ensemble system integrating IDS/IPS for adaptive defence. These studies consistently reported 98–99.7% detection accuracy with adaptability, but faced limitations in scope, computational efficiency, and reliance on simulations.
More recent work integrates federated learning with deep models. Babbar and Rani [
66] developed FRHIDS, combining FL with a CNN-LSTM hybrid and a recommender system. Evaluated on UNSW-NB15, it achieved 99.8% accuracy, outperforming prior models by ~12%. Uddin and Kumar [
67] extended FL to Satellite-IoT, combining SDN, LEO satellites, LPWANs, and supervised ML, achieving up to 99.66% accuracy with RF. Enhancements such as load balancing, honeypots, and differential privacy were suggested for scalability and security in space-IoT contexts. For reinforcement learning, Guo et al. [
26] presented DQSP, a deep RL-based secure routing protocol using DDPG actor-critic models. Simulations demonstrated a 10% improvement in packet delivery ratio over OSPF, reduced delay, and resilience against malicious routing. However, results were limited by small-scale simulations and sensitivity to reward design.
Table 4 and
Table 5 summarise SDN and SDN-IoT studies on ML, DL, and FL for DDoS detection, mitigation, and adaptive routing. All studies focused on SDN layers, integrating diverse ML approaches such as ensemble (e.g., SVM, RF, GBM, DT) [
22,
56] and hybrid ML models like OWVE [
12], hierarchical systems [
57], sequential or adaptive retraining strategies, DNN such as RNNs and LSTMs [
59,
64], RL such as DDPG [
26], and federated frameworks such as RF-, CNN-, or LSTM-based for privacy-preserving, decentralised detection [
63,
66,
67]. These methods achieved high detection accuracy, low false positives/negative rates, low-latency response, while addressing flow table overflows, controller saturation, and resilience against low-rate or evolving attacks.
SDN controller deployment is generally specified, including POX, Ryu, ODL, SDN-WISE, or multi-controller setups, though some studies omit controller details or use controller-agnostic simulations. Moreover, evaluation metrics consistently cover detection performance using standard metrics like accuracy, F1, precision, recall, resource usage in terms of CPU/memory include throughput, response time, and latency. Reported findings show high accuracy (often ≥95–99%) with low positives and manageable computational overheads. Some studies also measure network-level performance enhancements, like improved packet delivery ratio and reduced delay under attack [
26]. Similarly, to studies reported in
Table 2 and
Table 3, evaluation methods cover simulations (e.g., Mininet, custom IoT topologies, Matlab, etc.), emulation, train–test splits, cross-validations, and comparative studies against baseline classifiers. While some simulated adversarial or DDoS scenarios, others focused on federated aggregation or adaptive routing evaluation. Furthermore, benchmark datasets such as CIC-DDoS2019, NLS-KDD, SCADA, CAIDA, UNSW-NB15, and Edge-IIoTset were used across studies. In general, despite the differences in ML methods, controller configurations, and evaluation practices, the studies consistently report high detection performance across SDN layers. However, limitations remained across studies, including heavy reliance on benchmark datasets, limited real-world deployment, fixed node assumptions, and scalability issues, prompting the need for further or broader validation and deployment studies in operational SDN-IoT settings.
4.4. ML-Based Security Integration in IoT
This subsection summarises FL-based approaches for IoT anomaly detection, where most authors focused on DDoS attacks using broad multi-attack datasets, as shown in
Table 6 and
Table 7. Alshdadi et al. [
68] proposed an FL framework integrating a hybrid DL model, ResVGG-SwinNet, combining ResNet, VGGNet, and Swin-Transformer for multi-label attack detection. IoT devices train locally and share only model updates, preserving privacy and reducing network load. Real-time detection, attack isolation, and dynamic resource allocation are supported by adaptive priority scheduling and threat intelligence. Evaluations on CIC-DDoS2019, UNSW-NB15, and IoT23 achieved 99.0% accuracy, 2.5% false alert rate, 99.3% AUC, and 93.0% optimisation efficiency. Limitations include sensitivity to network congestion, packet loss, and heterogeneity in real-world scenarios. Alhasawi and Alghamdi [
7] introduced FL-DAD, a decentralised FL framework using CNNs on edge devices. Tested on CICIDS2017, FL-DAD achieved ≥98% detection across accuracy, precision, recall, and F1-score, with extremely low false positive (0.009) and false negative (0.007) rates. The system reduces communication overhead during training and scales effectively with 10–100 nodes, addressing privacy, single point of failure, and centralised IDS limitations. Remaining challenges include non-IID data, edge device constraints, legacy system integration, and dataset specificity.
Zhu and Niu [
69] extended FL with Homomorphic Encryption, edge computing, and a trust chain. Computations occur on encrypted model parameters (Paillier scheme), with edge nodes handling initial aggregation. A key generation centre distributes encryption keys securely, while the trust chain ensures transparency and immutability. Evaluated on MNIST, the system maintained accuracy comparable to standard FL with minimal convergence impact, though reliance on a trusted key centre and heterogeneous participant data remains a limitation. Mahmud et al. [
24] developed a privacy-preserving FL-based IDS for CPSs and heterogeneous IoT networks. Using DL models (LeNet, FCN, DNN, LSTM, GRU) and lightweight SSL cryptography, the system detects DoS, DDoS, ransomware, data injection, XSS, PCA, and MITM attacks. Experiments on real-world datasets demonstrated high detection (>91% for LeNet and FCN), scalable training, low computational overhead, and resilience to concept drift. Limitations include small client numbers, reliance on supervised learning, and evaluation against known attacks, highlighting the need for larger deployments, semi-supervised learning, and detection of emerging threats.
Moreover, Janivasya and Rachmawati [
71] evaluated eight ML algorithms on UNSW-NB15, with RF achieving the highest accuracy (97.68%) and DT, LSTM, MLP, and GRU consistently above 96%. Chi-square analysis identified key features enhancing model performance, highlighting the proactive potential of ML-based defences. Otoum et al. [
72] proposed DL-IDS, a DL framework for IoT networks addressing high-dimensional and uncertain data. Using Spider Monkey Optimisation for feature selection and a Stacked-Deep Polynomial Network for classification, DL-IDS achieved 99.02% accuracy, 99.38% precision, 98.91% recall, and 99.14% F1-score on NSL-KDD, outperforming prior approaches.
Alduailij et al. [
73] focused on cloud-based detection, combining Mutual Information and RF Feature Importance to select 19 features, with RF achieving 99.9% accuracy and minimal misclassification on CICIDS2017 and CICDDoS2019 datasets. Siddhartan et al. [
74] proposed SENMQTT-SET for MQTT-based IoT networks, reducing 120 raw features to 11 via an ensemble multi-view cascade feature generation algorithm. DT emerged as the Elite ML model, achieving over 99% accuracy while demonstrating efficient detection under increased packet loss, latency, and delays caused by DoS attacks.
Studies also highlight adversarial vulnerabilities in ML/DL-based NIDS. Qiu et al. [
70] examined black-box attacks on DL-based NIDS, achieving a 94.31% success rate in evading detection or triggering false alarms, notably against Kitsune autoencoder-based systems. Papadopoulos et al. [
75] analysed label poisoning and FGSM attacks on ML/DL models using Bot-IoT, showing that non-targeted FGSM attacks significantly reduced accuracy and recall for DDoS and DoS traffic, while label poisoning, though detectable, could manipulate SVM models during training. These studies underscore the importance of robust, attack-resilient detection mechanisms.
Table 6 and
Table 7 summarise SDN-IoT studies on DDoS detection, anomaly detection, and traffic classification, focusing on FL, hybrid ML/DL models, and classical ML/DL approaches. FL and hybrid methods, such as CNN-based FL-DAD [
7] and ResVGG-SwinNet [
68], achieve high accuracy (>98–99%) while reducing network load and preserving privacy. Improvements, including homomorphic encryption [
69] and DL-based FL for heterogeneous IoT [
24], further enhance security, scalability, and resilience. Classical ML/DL methods such as RF [
71,
73], DL-IDS [
72], and SENMQTT-SET [
74] remain effective but may be vulnerable to adversarial attacks [
70,
75].
All the studies addressed multiple SDN-IoT layers, from device to application layers, with some incorporating cloud or virtualized environments. The coordination and trust mechanisms include federated averaging, trust chains, key management for encrypted updates, hierarchical IDS control, ensemble feature selection, and adversarial training. ML techniques employed are diverse, including CNNs, RNNs, LSTM, GRU, DNN, FCN, SMO, KNN, RF, and Gradient Boosting and ensemble models, often applied for DDoS mitigation, traffic classification, and adaptive detection in IoT networks. On the other hand, SDN controller or aggregation deployments vary, such as cloud servers, FL aggregation servers, IDS-based control planes, MQTT brokers, and NIDS monitoring systems. Also, evaluation metrics were consistently applied, including accuracy, recall, F1, precision, false positive/negative rates, convergence time, training/prediction time, loss, and miscalculation rates. Reported performance is generally high, often ≥97%, though adversarial or concept-drift scenarios can reduce effectiveness.
Furthermore, evaluation methods including simulations, emulations, server-client experiments, train–test splits, benchmark datasets (e.g., CICIDS2017, IoT23, MNIST, Mirai botnet, etc.), and encrypted aggregation tests were used across studies. These studies, although they applied different ML, FL, and deployment approaches, all aim for accurate, scalable, and privacy-aware detection in SDN-IoT. Nonetheless, challenges remain with limited edge resources, non-IID data, real-world testing, adversarial threats, and heterogeneous IoT, indicating areas for further research.
4.5. BC-ML-Based Security Integration in IoT
This subsection summarises studies combining BC and ML with SDN-IoT/IIoT for security, as presented in
Table 8. Ababio et al. [
28] proposed a BC-assisted FL framework for secure, self-optimising digital twins in IIoT. Integrating FL, BC, XAI, and homomorphic encryption, the framework enables decentralised, privacy-preserving edge training while maintaining data integrity and interpretability. Weighted aggregation balances heterogeneous datasets, BC records updates via smart contracts, and XAI supports adaptive training. Evaluated on CIFAR-10, it achieved 95% accuracy, ~300 ms latency, and scalability to 1000 edge devices. Limitations include potential challenges in anomaly detection and adversarial resilience.
Saveetha et al. [
76] introduced a federated ML and BC framework for DDoS detection, with distributed local training preserving privacy and BC ensuring model integrity. Reputation-based miner selection incentivises legitimate participation. Experiments on IDS2018 and CIC-DDoS2019 achieved up to 99.1% accuracy with RF, with future work targeting broader attack types and SDN integration. Abdullah et al. [
77] developed FLDoSADC-DTL, combining FL, BC, and deep transfer learning with stacked autoencoders for DoS detection in IIoT. Feature selection via the Sand Cat Swarm Algorithm and hyperparameter tuning with Black Widow Optimisation improved performance. On the Edge-IIoT Cybersecurity dataset, it achieved 95.11% accuracy, 87.73% precision, 87.77% recall, 87.72% F1-score, and 92.36% AUC, while limitations included edge device constraints and BC overhead.
Arazzi et al. [
78] proposed a privacy-preserving anomaly detection framework using FL, HE, and BC. GRU-based networks model device behaviour, with resource-constrained nodes offloading tasks and BC managing trust and logging. The system achieved 0.85 average detection accuracy and resilience against poisoning, slandering, whitewashing, and sleep deprivation attacks, but required sufficient heterogeneous nodes, frequent communication, and incurred a 16.6% performance reduction due to task delegation. Manh et al. [
79] developed a BC-based IoT cyberattack detection framework (PPDiL) combining AI with HE. Cloud providers train DL models on encrypted data using 1D/2D packing and FedAvg-based distributed learning, reducing computational overhead. Experiments on the BNAT dataset achieved ~91% accuracy, comparable to non-encrypted models, with adaptability to different BC consensus mechanisms and hardware, supporting real-world deployment.
Table 8 shows that combining FL, BC, DL, and homomorphic encryption enables secure, privacy-preserving, and scalable attack detection in heterogeneous IoT and IIoT networks. BC-assisted FL with XAI and HE achieved 95% accuracy for IIoT digital twins [
28], FL-BC frameworks with reputation-based miners and deep transfer learning exceeded 95% accuracy for DDoS/DoS detection [
76,
77], GRU-based FL with HE and BC reached 0.85 accuracy for IoT anomaly detection [
78], and encrypted DL models with FedAvg maintained ~91% accuracy while reducing computational overhead [
79]. Collectively, these studies confirm the effectiveness of FL, BC, and HE for high-accuracy, privacy-preserving, and scalable detection.
4.6. BC-ML-Based Security Frameworks in SDN-IoT/IIoT
This subsection summarises studies combining BC, ML/DL, and SDN-IoT/IIoT for secure DDoS detection and controller placement, as shown in
Table 9 and
Table 10. Benoudifa et al. [
15] proposed a proactive SDN controller placement framework using MuZero RL and Ethereum smart contracts, optimising placements based on latency, traffic, and device connectivity while immutably recording decisions. Simulations on Mininet/ODL/Ganache validated adaptive, tamper-proof placement under DoS attacks. Similarly, Jmal et al. [
4] developed distributed SDN-IoT architectures integrating BC and ANN for real-time DDoS detection. Multi-controller setups reduce centralisation risks, BC ensures immutable inter-controller communication, and encrypted firewalls protect the data plane. Evaluated on IoT intrusion datasets, both frameworks achieved perfect classification metrics, though limitations include hardware/software demands, BC latency, integration challenges, and scalability with growing nodes or transactions.
Pawar et al. [
80] combined multi-controller SDN, BC, and an attention-based CNN-LSTM (At-C-L) for DDoS detection. On the InSDN dataset (343,939 flows), At-C-L achieved 98.3% accuracy, 97.3% F1-score, 97.1% PPV, and AUC 0.979, outperforming CNN, LSTM, and Bi-LSTM baselines. Alotaibi [
25] applied Bi-LSTM-HBA with Honey Badger metaheuristic and SMOTE for large IoT networks, achieving ≈ 99.55% accuracy, precision ≈ 99.36%, recall ≈ 99.44%, F1 ≈ 99.42%, throughput 663 Mbps, latency 0.45 s, and CPU usage 22.46%, surpassing GRU-LSTM baselines. Limitations include BC latency, control-plane bottlenecks, and centralisation; lightweight BC and federated learning are suggested. Hybrid DL-BC approaches include HDL-SDN [
13], integrating CNN-LSTM with BC and RBFT consensus. Evaluated on NSL-KDD, it achieved 92.89–98.02% specificity and 95.42% precision, outperforming CNN, LSTM, and DL-IDPS-SDN models, though deployment and latency metrics are unreported. Hsu and Liu [
6] combined FL, BC, and SDN for IoT/smart city DDoS detection, using DNN, CNN, RNN, and LSTM models optimised via Particle Swarm Optimisation. FL enables local training without raw data sharing, BC provides tamper-proof logging, and SDN supports dynamic traffic control. Evaluations show high accuracy, efficient anomaly detection, and scalability, with future work targeting model compression and lightweight deployment.
Furthermore, Rahman et al. [
36] proposed BlockSD-5GNet, a 5G architecture combining SDN, NFV, BC, and ML to mitigate DDoS, MITM, topology poisoning, and side-channel attacks. SDN provides centralised control, NFV virtualises functions, BC ensures integrity, and ML supports proactive decisions. Simulations demonstrated improved throughput, bandwidth utilisation, latency reduction, and node failure resilience compared to SDN-only or conventional 5G networks. Limitations include BC speed, scalability, and reliance on traditional ML, with future work suggested in FL, DL, energy-efficient management, and optimised consensus. Abdulqadder et al. [
81] presented a directed acyclic graph (DAG)-based BC framework for 5G-enabled SDN, integrating multi-plane SDN controllers, edge computing, NFV-enabled virtual switches, and honeypots. Multi-level authentication uses QUARK hashing, PUFs, biometrics, and one-time pads, while CapsNet honeypots and SAC algorithms validate packets. DAG BC with PoET consensus ensures immutable storage, and Honey Badger Optimisation with time-based handover improves load balancing. Simulations show >99% detection accuracy and improvements in bandwidth, delay, response time, packet loss, and authentication, addressing integrity, availability, confidentiality, authenticity, and backward secrecy. Future research includes real-world deployment and adaptive DAG consensus.
Hu et al. [
82] proposed BC-SDN, deploying edge BC-as-a-Service (BaaS) with smart contracts for SDN-controlled IoT security. BC agents co-located with SDN switches verify flows and maintain immutable ledgers, with contract-theoretic incentives encouraging truthful verification. Game-theoretic analysis maximises social welfare. Simulations show scalability, efficient reward allocation, and low computational complexity, though large-scale deployment and diverse flow policy evaluation remain challenges. Similarly, Prasad et al. [
83] introduced MOBCF-ADDLM, a decentralised DDoS detection framework combining BC, Deep Belief Networks, and evolutionary optimisation (Aquila and Red Panda optimisers for feature selection and hyperparameters). BC ensures tamper-proof records, DBNs model high-dimensional traffic, and metaheuristic optimisation improves accuracy and convergence. Experiments on BoT-IoT datasets achieved 99.22% accuracy, low processing times, and reduced overfitting. Limitations include single-dataset evaluation, adaptability to evolving attacks, and resource overhead; future work suggests cross-dataset validation, real-time SDN integration, and adaptive learning.
Table 10.
Summary of BC-ML-SDN-IoT security frameworks.
Table 10.
Summary of BC-ML-SDN-IoT security frameworks.
| Study | Layers Covered | BC/Consensus | ML Methods | SDN Controller/FL Server | Evaluation Metrics | Performance Insight | Evaluation Method |
|---|
| [4] | Device, Network | Private BC; Inter-controller communication | ANN for detection and payload optimisation | Distributed SDN controllers | Accuracy, precision, recall, F1-score | Perfect metrics (1.0) | Novel SDN Dataset validation |
| [25] | Device, Network, Application | Ethereum; smart contracts; decentralised trust | Bi-LSTM with SE blocks; Honey Badger Algorithm; SMOTE | Centralised SDN controller | Accuracy, precision, recall, F1, throughput, latency, CPU | Accuracy 99.55%; throughput 663 Mbps; Latency 0.45 s; CPU 22.46% | CICIDS 2018 dataset; comparison with GRU-LSTM; runtime measurements |
| [80] | Device, Network | Private Ethereum BC; Oracle; immutable policies | At-C-L: Attention + CNN + LSTM for DDoS detection | Multi-controller SDN | Accuracy, F-score, PPV, AUC | Accuracy 98.3%; F-score 97.3%; outperformed CNN, LSTM, Bi-LSTM; faster attack identification under load | InSDN dataset (343,939 flows); ROC/AUC analysis; controller comparisons |
| [82] | Device, Network, Application | Edge BC Agents; smart contracts; Byzantine consensus | Game-theoretic optimisation for reward allocation | SDN controllers for path calculation and flow rule generation | Social welfare, latency, Blocksize | Immutable flow ledger ensures auditing; IAS latency linear; ISS more efficient; edge deployment reduces overhead. | Analytical simulations with varying verifier cost, number of verifiers, latency/honesty combinations |
| [83] | Device, Network, Application | BC; smart contracts | DBN for DDoS classification; AO feature selection; RPO hyperparameter tuning | SDN controllers | Accuracy, precision, recall, F1-score, MCC, processing time | Accuracy 99.22% (multiclass), 97.41% (binary); processing time 9.31 s | BoT-IoT datasets; 30% TESPHA; training/validation analysis |
Table 9 and
Table 10 present SDN-enabled IoT and 5G studies highlighting BC integration, distributed architectures, and advanced learning for security and performance. Multi-controller SDN with BC and ANN/CNN-LSTM/Bi-LSTM/attention-based models [
4,
6,
13,
15,
25,
44,
66,
80,
82] achieve ≈98–99.5% DDoS detection accuracy, privacy preservation, and real-time anomaly detection. 5G-focused work [
36,
81] combines SDN, NFV, DAG/PoET BC, ML, and optimisation to enhance throughput, latency, and authentication. Edge solutions [
82,
83] ensure tamper-proof records and resilience. Limitations include BC overhead, scalability, and resource demands; future directions include lightweight deployment, federated learning, and adaptive consensus.