A Cryptocurrency Dual-Offline Payment Method for Payment Capacity Privacy Protection
Abstract
1. Introduction
- (1)
- An innovative payment-credential-based, non-interactive, zero-knowledge proof (NIZKP) verification mechanism is constructed. By designing an end-to-end payment credential generation and verification framework integrated with NIZKP algorithms, this approach achieves dual objectives of payment validity verification and privacy preservation without exposing sensitive information of transacting parties, effectively addressing the critical privacy leakage challenge in offline payment scenarios.
- (2)
- A novel zero-sum verification protocol is designed to enable privacy-preserving authentication of payment data authenticity. Employing innovative verification logic, this mechanism validates credential authenticity without disclosing sensitive information such as the identity of the payer and the payment amount, thereby mitigating risks of fraudulent payment and data tampering while enhancing trust assurance in dual-offline payment systems.
2. Related Works
2.1. Blockchain-Based Offline Payment
2.2. Cryptographic Protocol-Based Schemes
2.3. ECC-Based Privacy Protection
2.4. NFC/CBDC-Oriented Offline Payment
2.5. Mobile Security-Related Offline Payment
3. Offline Payment Methods
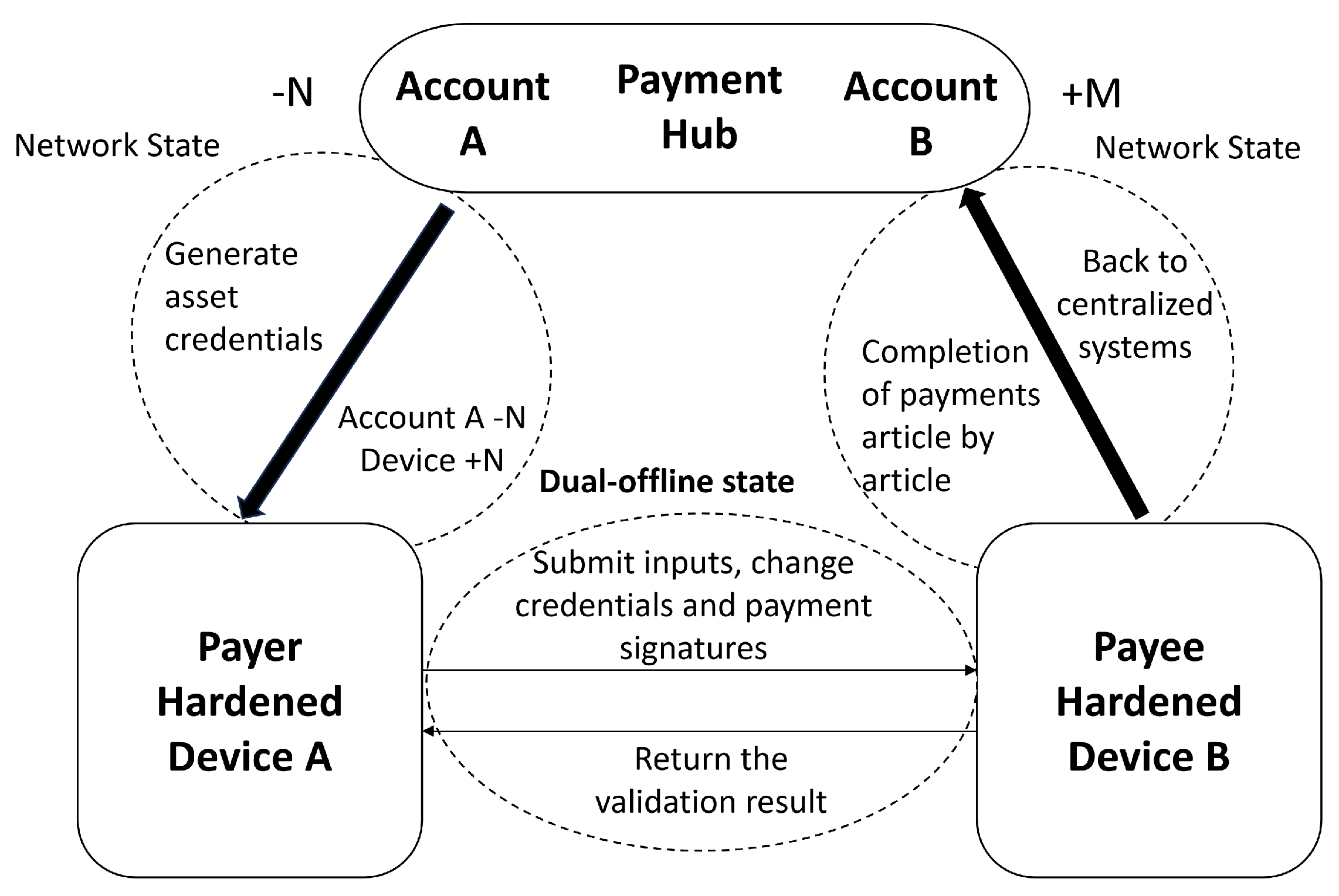
3.1. The Proposed System
- (1)
- Pre-deposit Phase: Under online conditions, the payment hub transfers a specified amount to security-hardened Device A, generating an asset credential. Simultaneously, the payment hub deducts amount N from the account balance, while Device A’s balance increases by N.
- (2)
- Dual-Offline Payment Phase: The payer’s Device A constructs payment data (including payment credential, change credential, and digital signature) and transmits it to the payee’s security-hardened Device B. Upon successful offline verification, Device B accepts and records the payment, marking the transaction as locally settled.This phase adopts a “Bluetooth pairing binding + UUID uniqueness verification” dual mechanism to ensure one-to-one transaction execution: ① Secure Bluetooth pairing prerequisite: Prior to data transmission, the payee’s Device B generates a unique 6-digit pairing code via its Secure Element (SE) (non-extractable and only displayed locally). The payer inputs the code to complete pairing, establishing an exclusive encrypted communication link that prevents the payer from connecting to multiple payees or receiving concurrent payment requests. ② Transaction UUID uniqueness constraint: Each transaction is assigned a globally unique UUID during initialization. After transaction completion, the UUID is stored in the local blacklist of both devices; any repeated request with the same UUID (e.g., due to accidental reconnection) is immediately rejected. This dual mechanism eliminates concurrency risks from both communication links and transaction logic.
- (3)
- Settlement Phase: When the payee’s device reconnects, it submits the payment proof to the payment hub. The hub verifies the proof’s uniqueness and validity, confirms absence of double-spending, executes fund settlement, and updates the distributed ledger.
3.2. Cryptocurrency Dual-Offline Payment Method Design
3.2.1. Pre-Conditions
- (1)
- Exchange and union laws for addition and scalar multiplication of elliptic curves, for any scalar k, j, satisfywhere H is a point on the elliptic curve.
- (2)
- Hash operation: refers to the use of a SHA256 algorithm for the hash calculation of abc, , where the symbol “∣” means that A, B, and C are spliced together.
3.2.2. Zero-Sum Verification Schematic Design
3.2.3. Methodological Process
- (1)
- Generation of payer and payee payment. The steps for generating payer payment information are as follows: First, the payer generates the transaction unique identifier , constructs the input credential , and the payer decoy factor . Subsequently, the payer preemptively executes change operation in advance (before sending the payment information to the payee), partitioning the input credential’s blinding factor as follows:
| Algorithm 1 Offline payment generation. |
|
- (2)
- Verification of the payment. By verifying the signature equations of the payer and payee, the uniqueness and non-tamperability of each signed information are cryptographically enforced. The payer’s signature is defined as:
| Algorithm 2 Offline payment verification. |
|
4. Methodological Theoretical Analysis
4.1. Adversarial Model and Security Assumptions
4.1.1. Model Environment and Participant Assumptions
- 1.
- Environment and Interaction Assumptions: The payment parties (Payer P and Receiver R) complete the offline interaction via secure cryptographic hardware. Payment credentials (, etc.) are stored locally and transferred offline. Upon re-establishing a network connection, the credentials are batch-uploaded to the Payment Center () for final settlement, with no additional real-time data interaction involved.
- 2.
- Participant Behavior Assumptions: Honest participants strictly adhere to the protocol, avoiding proactive leakage or tampering of private keys () or hidden balance information. The Malicious Participant (Adversary A) is a third-party interceptor, possessing the capability of data interception, tampering, and forgery in the offline environment. However, A cannot bypass the physical security of the secure hardware to extract private keys or original balance data.
- 3.
- Cryptographic Hardness Assumptions: The security relies on the computational intractability of the ECDLP on the secp256k1 curve. Hash functions (e.g., SHA−256) satisfy collision resistance and pre-image resistance. The Fiat–Shamir transformation in this scheme is implemented using the SHA256 hash function. Here, we assume that SHA256 satisfies the core properties of the Random Oracle Model (ROM)—its output is uniformly random and independent of the input—laying the foundation for the zero-knowledge property and knowledge extractability of NIZKP.It is important to note the limitations of SHA256 when instantiated in the ROM, as the ROM is an idealized cryptographic model: 1. Ideal vs. Real-World Gap: The ROM assumes SHA256 behaves as a “perfect random function,” but practical implementations may have side-channel vulnerabilities (e.g., timing discrepancies during hash computation on different inputs), which could leak partial information about the input. 2. Future Security Risks: While SHA256 is currently collision-resistant and pre-image-resistant, advancements in quantum computing or cryptographic analysis may undermine these properties in the long term. 3. Fixed Output Length: The 256-bit output length of SHA256 may become insufficient as computational power grows, though this risk is negligible for the current security parameter .These limitations do not invalidate the scheme’s security: side-channel vulnerabilities are mitigated by the SE’s hardware-isolated execution environment (Section 4.1.1), and SHA256 can be replaced with post-quantum hash functions (e.g., SHA-3, XMSS) without modifying the protocol’s core framework.
- 4.
- Malicious payer’s double-spending attack scenario: A malicious payer (Adversary A) exploits the lack of real-time verification in the offline environment to reuse the same input credential , forge supporting proofs (e.g., generate fake , ), and initiate payments to multiple payees. The attacker attempts to complete multiple local verifications before settlement to achieve “repeated spending of the same fund”. The core attack path is Offline reuse of → Generate multiple sets of proofs → Complete local verification with different payees → Batch upload for settlement to conceal double-spending.
- 5.
- Secure Element (SE) Formal Assumptions: The scheme’s security relies on three formal properties of the SE integrated in hardened devices, which are consistent with industrial security standards:
- ➀
- Tamper-Resistance: The SE’s hardware isolation prevents adversaries from extracting or modifying sensitive data stored inside (including private keys , credentials , and transaction state). Formally, for any sensitive data , .
- ➁
- Computational Integrity: All cryptographic operations executed within the SE (elliptic curve scalar multiplication, signature generation, zero-sum equation verification, atomic state update) are correct and unalterable. Formally, for any SE-executed function f and input x, the output is identical to the ideal function output , and .
- ➂
- Secure I/O: The communication channel between the SE and the device’s main processor is authenticated and encrypted. Formally, adversaries cannot intercept or forge data transmitted between the SE and the main processor.
4.1.2. Attacker Capabilities and Security Targets
- Type I: Privacy Theft Attack () Formal Goal: A attempts to derive the Payer’s hidden balance or transaction amounts () from the intercepted public data (Pub). Security Requirement (Balance Privacy): The probability of A’s success must be negligible, formally .
- Type II: Transaction Tampering Attack () Formal Goal: A attempts to bypass the zero-sum verification and signature check through tampering or forgery, to achieve illegal profit (e.g., increasing or double spending). Security Requirement (Transaction Integrity): The probability of A’s successful forgery passing verification must be negligible, formally .
4.1.3. Security Goals
- 1.
- Balance Privacy: Resistance against Type attacks, preventing the derivation of sensitive balance information from public data.
- 2.
- Transaction Integrity: Resistance against Type attacks, ensuring that any malicious tampering or forgery is detected during the offline verification or the final settlement.
4.2. Security Analysis and Proof
4.2.1. Formal Zero-Knowledge Proof: Simulator Construction and Transcription Indistinguishability
Simulator Setup
- -
- Input: Security parameter , secp256k1 curve parameters (), environment ’s input (transaction context, adversary ’s attack queries).
- -
- Output: Simulated transcript , where superscript s denotes simulated values.
Simulation Process
- Simulate Public Parameters: generates random scalars (q is the order of secp256k1), and computes simulated credentials:These simulated credentials follow the same distribution as real credentials (due to the uniform randomness of scalars and ECDLP hardness).
- Simulate Challenge Value : Leveraging the ROM property of SHA256, records the input to the hash function ( ) and returns a uniformly random 256-bit string as . This aligns with the ROM’s ideal randomness assumption, making indistinguishable from the real challenge value E (generated via SHA256 in the protocol).
- Simulate Signature : generates a random scalar , computes , and simulates the payer’s signature:Since and are random, is computationally indistinguishable from real signatures (which use private key ).
- Simulate Verification Result: sets , which is consistent with the real protocol’s 100% success rate in valid transactions.
Transcription Indistinguishability
- -
- The challenge values E (real) and (simulated) are both uniformly random (ROM assumption for SHA256).
- -
- All elliptic curve points ( ) in both transcripts follow the same distribution (group properties of secp256k1), and ECDLP hardness prevents from distinguishing simulated scalars from real ones.
- -
- The verification result is identical in both transcripts, providing no distinguishing information.
4.2.2. Security Analysis
- (1)
- Analysis of Transaction Tampering (Against Type Attacks). An attacker may intercept the payment data during the payment process and try to modify the payment amount , credentials and , or other key information. To counter such attacks, this method employs elliptic curve cryptography to enforce data integrity, with correctness guaranteed by the SE’s computational integrity assumption (Section 4.1.1 (5)(②)).
- (2)
- Defense Against Double-Spending Attacks. The anti-double-spending mechanism of this scheme is realized through the design of “atomic certificate lifecycle management + security hardware isolation”, with validity formally guaranteed by the SE’s core assumptions (Section 4.1.1 (5)):
- (3)
- Proof of Balance Privacy and Anonymity (Against Type Attacks). The attacker attempts to obtain the identity information or other sensitive information of both parties in the payment. This scheme’s privacy protection relies on multi-layered cryptographic mechanisms and the SE’s security assumptions (Section 4.1.1 (5)):
5. Methodological Evaluation
5.1. Comparison with Existing Methods
5.2. Experimental Environment Configuration
5.3. Assessment of the Dual-Offline Payment Methodology
- (1)
- Offline account performance
- (2)
- Security Evaluation
5.4. Cryptographic Cost Comparison (O(1) Complexity)
- This Scheme (ECC+ZKP Principles): The computational complexity for both payment generation and verification is constant time, , as the number of ECPMs is fixed, irrespective of the magnitude of the transaction amount or the number of prior transactions.
- Generic ZKP Systems (e.g., zk-SNARKs): Proof generation typically exhibits complexity ranging from to (where N is the number of gates in the underlying arithmetic circuit), making them significantly heavier for resource-constrained offline devices, especially when N is large [25].
5.5. Analytical Interpretation of Simulation Results
6. Conclusions and Future Work
- Adversarial testing and extended experimental comparison: Future work will conduct comprehensive adversarial testing, including simulating advanced attacks such as differential power analysis (against SE), malicious SE tampering, and transaction replay attacks under extreme offline conditions. We will also extend experimental comparisons to more state-of-the-art dual-offline payment schemes (e.g., zk-SNARKs-based solutions), evaluating performance (latency, memory usage) and security robustness across diverse hardware environments (low-power IoT devices, edge computing nodes) and network constraints.
- Continuous Offline Transactions: The current design does not efficiently support repeated or chained offline spending, where a single payer makes multiple successive transactions before reconnecting to the network. Extending the method to handle continuous transactions requires sophisticated mechanisms for state management and privacy-preserving balance updates without online consensus.
- Advanced Scenario Complexity: Further research is needed on complex scenarios, such as multi-hop payments (transferring funds through multiple intermediate offline devices), and detailed analyses of malicious behavior by the payer or payee during the final settlement reconciliation.
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
Abbreviations
| DCTS | Digital Currency Transaction System |
| CBDCs | Central Bank Digital Currencies |
| e-CNY | China’s Digital Yuan |
| PBOC | People’s Bank of China |
| NFC | Near Field Communication |
| BS | Blind Signature |
| RSA | Rivest–Shamir–Adleman |
| HCE | Host Card Emulation |
| SE | Secure Element |
| TEE | Trusted Execution Environment |
References
- Li, J.; Yuan, Y.; Wang, F. Blockchain-based digital currency: The state of the art and future trends. Acta Autom. Sin. 2021, 47, 715–729. [Google Scholar]
- Westermeier, C. The digital euro: A materialization of (in) security. Rev. Int. Polit. Econ. 2024, 31, 1569–1592. [Google Scholar] [CrossRef]
- Mainetti, L.; Aprile, M.; Mele, E.; Vergallo, R. A sustainable approach to delivering programmable peer-to-peer offline payments. Sensors 2023, 23, 1336. [Google Scholar] [CrossRef] [PubMed]
- Ungratwar, S.; Dipasha, S.; Satish, K. Mapping the digital banking landscape: A multi-dimensional exploration of fintech, digital payments, and e-wallets, with insights into current scenarios and future research. Humanit. Soc. Sci. Commun. 2025, 12, 1–22. [Google Scholar] [CrossRef]
- Mue, I. An Analysis on Strategic Objectives of the Issuance of the Digital Renminbi. In Proceedings of the 2024 2nd International Conference on Cyber Resilience (ICCR), Dubai, United Arab Emirates, 26–28 February 2024; pp. 1–4. [Google Scholar]
- Onumadu, P.; Abroshan, H. Near-field communication (nfc) cyber threats and mitigation solutions in payment transactions: A review. Sensors 2024, 24, 7423. [Google Scholar] [CrossRef] [PubMed]
- Ahamad, S.S. A novel NFC-based secure protocol for merchant transactions. IEEE Access 2021, 10, 1905–1920. [Google Scholar] [CrossRef]
- Reddy, A.V.S.K.; Banda, G. ElasticPay: Instant Peer-to-Peer Offline Extended Digital Payment System. Sensors 2024, 24, 8034. [Google Scholar] [CrossRef]
- Li, Z.; Li, J. Architecting Inclusion in e-CNY: Settlement-Upon-Payment, Domestic Interoperability, and User Control. Encyclopedia 2025, 5, 179. [Google Scholar] [CrossRef]
- Aboulaiz, L.; Akintade, B.; Daud, H.; Lansey, M.; Rodden, M.; Sawyer, L.; Yip, M. Offline Payments: Implications for Reliability and Resiliency in Digital Payment Systems. J. Digit. Payment Syst. 2024, 8, 45–68. [Google Scholar] [CrossRef]
- Sravan, S.S.; Mandal, S.; Alphonse, P.J.A. LIO-PAY: Sustainable low-cost offline payment solution. Electron. Commer. Res. Appl. 2024, 67, 101440. [Google Scholar]
- Gong, X.; Cheung, C.M.; Liu, S.; Zhang, K.Z.; Lee, M.K. Battles of mobile payment networks: The impacts of network structures, technology complementarities and institutional mechanisms on consumer loyalty. Inf. Syst. J. 2022, 32, 696–728. [Google Scholar] [CrossRef]
- Kochar, S.; Nikam, H.; Tripathi, R.; Vidhate, A. Offline transaction system. ITM Web Conf. 2022, 44, 03072. [Google Scholar] [CrossRef]
- Herath, H.; Madhusanka, B. Data protection challenges in the processing of sensitive data. In Data Protection: The Wake of AI and Machine Learning; Springer: Berlin/Heidelberg, Germany, 2024; Volmue 1, pp. 155–179. [Google Scholar]
- Xia, Z.; Wang, L.; Tang, J.; Xiong, N.N.; Weng, J. A Privacy-Preserving Image Retrieval Scheme Using Secure Local Binary Pattern in Cloud Computing. IEEE Trans. Netw. Sci. Eng. 2021, 8, 318–330. [Google Scholar] [CrossRef]
- Chen, X.; Zhang, Z.; Qiu, A.; Xia, Z.; Xiong, N.N. Novel Coverless Steganography Method Based on Image Selection and StarGAN. IEEE Trans. Netw. Sci. Eng. 2022, 9, 219–230. [Google Scholar] [CrossRef]
- Xia, Z.; Jiang, L.; Ma, X.; Yang, W.; Ji, P.; Xiong, N.N. A Privacy-Preserving Outsourcing Scheme for Image Local Binary Pattern in Secure Industrial Internet of Things. IEEE Trans. Ind. Inform. 2020, 16, 629–638. [Google Scholar] [CrossRef]
- Xu, W.; Fang, W.; Ding, Y.; Zou, M.; Xiong, N.N. Accelerating Federated Learning for IoT in Big Data Analytics with Pruning, Quantization and Selective Updating. IEEE Access 2021, 9, 38457–38466. [Google Scholar] [CrossRef]
- Ivanov, N.; Yan, Q. System-Wide Security for Offline Payment Terminals. In Security and Privacy in Communication Networks; Springer International Publishing: Cham, Switzerland, 2022; Volume 399, pp. 92–112. [Google Scholar] [CrossRef]
- Jie, W.; Qiu, W.; Koe, A.S.V.; Li, J.; Wang, Y.; Wu, Y.; Li, J.; Zheng, Z. A Secure and Flexible Blockchain-Based Offline Payment Protocol. IEEE Trans. Comput. 2024, 73, 408–421. [Google Scholar] [CrossRef]
- Fang, Z.; Yu, J.; Huang, G.; Dong, R.; Gai, K. PROMISE: A Pedersen Commitment-Based Transaction Hiding Scheme for Blockchain System. In Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering; Springer: Berlin/Heidelberg, Germany, 2025; Volume 587, pp. 177–188. [Google Scholar]
- Ivanov, N.; Yan, Q. System-Wide Security for Offline Payment Terminals. In Lecture Notes of the Institute for Computer Sciences, Social Informatics and Telecommunications Engineering; Springer: Berlin/Heidelberg, Germany, 2021; Volume 399, pp. 92–112. [Google Scholar]
- Sadiku, P.O.; Oladele, O.T.; Balogun, G.B.; Atolagbe, E.O.; Usman-Hamza, F.E.; Olatunji, M.A. Development of an Offline Payment System Using Cryptographic Digital Time Signature. J. Emerg. Trends Comput. Inf. Sci. 2025, 16, 215–226. [Google Scholar]
- Feng, L.; Chen, Y.; Wang, J.; Zhang, H. A Secure Multi-Party Computation Protocol Combines Pederson Commitment with Schnorr Signature for Blockchain. In Proceedings of the 2020 IEEE 20th International Conference on Communication Technology (ICCT), Nanning, China, 28–30 October 2020; pp. 1341–1346. [Google Scholar]
- Xie, T.; Zhang, Y.; Song, D. Orion: Zero Knowledge Proof with Linear Prover Time. In Lecture Notes in Computer Science; Springer Nature: Cham, Switzerland, 2022; pp. 299–328. [Google Scholar]
- Huang, W. ECC-based three-factor authentication and key agreement scheme for wireless sensor networks. Sci. Rep. 2024, 14, 1787. [Google Scholar] [CrossRef] [PubMed]
- Fariss, M.; El Gafif, H.; Toumanari, A. A lightweight ECC-based three-factor mutual authentication and key agreement protocol for WSNs in IoT. Int. J. Adv. Comput. Sci. Appl. 2022, 13, 212–219. [Google Scholar] [CrossRef]
- Sun, Q.; Zhou, Y.; Tang, T. Mobile Payment Innovations in China: China UnionPay’s Practice and Experience. Bus. Innov. New ICT Asia-Pac. 2020, 257–279. [Google Scholar]
- Jayasinghe, D.; Markantonakis, K.; Gurulian, I.; Akram, R.N.; Mayes, K. Extending EMV Tokenised Payments to Offline-Environments. In Proceedings of the 2016 IEEE Trustcom/BigDataSE/ISPA, Tianjin, China, 23–26 August 2016; pp. 443–450. [Google Scholar]
- Chu, Y.; Lee, J.; Kim, S.; Kim, H.; Yoon, Y.; Chung, H. Review of offline payment function of CBDC considering security requirements. Appl. Sci. 2022, 12, 4488. [Google Scholar] [CrossRef]
- Hong, Z.; Chen, J. A solution for the offline double-spending issue of digital currencies. In Proceedings of the International Conference on Science of Cyber Security, Cham, Switzerland, 10–12 August 2022; pp. 455–471. [Google Scholar]
- Yanga, B.; Feng, W.; Qin, Y.; Zhang, Y.; Tong, D. Dual Offline Anonymous E-payment Scheme for Mobile Devices Based on TEE and SE. J. Softw. 2024, 35, 3553–3576. [Google Scholar]
- Yang, B.; Zhang, Y.; Tong, D. DOPS: A Practical Dual Offline Payment Scheme of CBDC for Mobile Devices. In Proceedings of the 2023 IEEE 22nd International Conference on Trust, Security and Privacy in Computing and Communications (TrustCom), Exeter, UK, 1–3 November 2023; pp. 1835–1844. [Google Scholar]
- Yang, B.; Zhang, Y.; Tong, D. DOT-M: A dual offline transaction scheme of central bank digital currency for trusted mobile devices. In International Conference on Network and System Security; Springer: Cham, Switzerland, 2022; pp. 233–248. [Google Scholar]
- Alpirez Bock, E.; Brzuska, C.; Fischlin, M.; Janson, C.; Michiels, W. Security reductions for white-box key-storage in mobile payments. In Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2020; Volume 12492, pp. 221–252. [Google Scholar]
- Rejeb, A.; Rejeb, K.; Keogh, J.G. Centralized vs. decentralized ledgers in the money supply process: A SWOT analysis. Quant. Financ. Econ. 2021, 5, 40–66. [Google Scholar] [CrossRef]
- Chaum, D. Blind signatures for untraceable payments. In Advances in Cryptology: Proceedings of Crypto 82; Springer: Boston, MA, USA, 1983; pp. 199–203. [Google Scholar]
- Camenisch, J.; Hohenberger, S.; Lysyanskaya, A.A. Compact e-cash. In Annual International Conference on the Theory and Applications of Cryptographic Techniques; Springer: Berlin/Heidelberg, Germany, 2005; pp. 302–321. [Google Scholar]
- Luo, J.N.; Yang, M.H. Offline Transferable E-Cash Mechanism. In Proceedings of the 2018 IEEE Conference on Dependable and Secure Computing (DSC), Kaohsiung, Taiwan, 10–13 December 2018; pp. 1–2. [Google Scholar]
- Regenscheid, A. Recommendations for Discrete-Logarithm Based Cryptography: Elliptic Curve Domain Parameters; NIST Special Publication (SP) 800-186-Draft; National Institute of Standards and Technology (NIST): Gaithersburg, MD, USA, 2019. [CrossRef]
- Kumar, A.; Kumar, S.; Mehrotra, T.; Rajput, G.K. A Review on Double Spending Problem in Blockchain. In Proceedings of the 2023 International Conference on Computational Intelligence and Sustainable Engineering Solutions (CISES), Greater Noida, India, 28–30 April 2023; pp. 881–889. [Google Scholar]
- Michalopoulos, P.; Olowookere, O.; Pocher, N.; Sedlmeir, J.; Veneris, A.; Puri, A. Compliance Design Options for Offline CBDCs: Balancing Privacy and AML/CFT. In Proceedings of the 2024 IEEE International Conference on Blockchain and Cryptocurrency (ICBC), Dublin, Ireland, 27–30 May 2024; pp. 307–315. [Google Scholar]
- Yang, X.; Yu, X.; Hou, H.; Tan, Z.; Wu, F. Efficient Asymmetric Encryption Scheme based on Elliptic Encryption Technology. In Proceedings of the 2023 IEEE 6th Information Technology, Networking, Electronic and Automation Control Conference (ITNEC), Shanghai, China, 24–26 February 2023; pp. 709–714. [Google Scholar]







| Symbol | Description |
|---|---|
| A random point on an elliptic curve is obtained by randomly generating a private key and obtaining its corresponding public key. | |
| The result of scalar multiplication of the private key K with the point H is used as the public key. | |
| The amount in the payer’s input credentials. | |
| The amount in the payer’s change credentials. | |
| The amount the recipient needs to receive. | |
| Large, random numbers (decoy factors), used to hide payment information. | |
| The payer’s input credentials with the expression | |
| The payer’s change credentials with the expression | |
| The payee’s receipt credentials with the expression | |
| Random numbers associated with and , | |
| Credentials zero-sum results, | |
| The large number, the random number (Nonce) required by the paying parties to generate a signature. | |
| Based on random numbers and random points for signatures. | |
| E | The hash value required to sign the payment data, computed by SHA256 () |
| Signature of the payer, | |
| Signature of the payee, | |
| Total payment signature, | |
| Points corresponding to the sum of the two Nonces, |
| Implementation Functions | Data Integrity and Authenticity | Anti-DS Mechanism | Privacy Protection |
|---|---|---|---|
| Blockchain-based system [19,20] | ✓ | ✓ | |
| Utilizing BS Cryptography Protocol [22,23] | ✓ | ✓ | |
| TEE+SE [32,33,34] | ✓ | ||
| Utilizing NFC technology [28,29] | |||
| CBDC Payment Program [30] | ✓ | ||
| Electronic cash [39] | ✓ | ||
| Proposed scheme | ✓ | ✓ | |
| Proposed scheme (with secure element) | ✓ | ✓ | ✓ |
| Evaluation Criteria Definitions: | |||
| |||
| Phase | Average Time Consumption | Standard Deviation |
|---|---|---|
| Elliptic curve operations | 7.61 ms | 1.11 ms |
| Key generation | 11.89 ms | 1.33 ms |
| Hash computation | 0.20 ms | 0.53 ms |
| Signature generation | 10.10 ms | 1.24 ms |
| Proposed Scheme | Proposed Scheme with SE | TEE-Based Blockchain Offline Payment [20] | DOPS [33] | |
|---|---|---|---|---|
| Avg. Gen. Time | 29.13 ms | 129.7 ms | 32 ms | 80 ms 1 |
| Avg. Ver. Time | 25.09 ms | 64.1 ms | 16.7 ms | - |
Disclaimer/Publisher’s Note: The statements, opinions and data contained in all publications are solely those of the individual author(s) and contributor(s) and not of MDPI and/or the editor(s). MDPI and/or the editor(s) disclaim responsibility for any injury to people or property resulting from any ideas, methods, instructions or products referred to in the content. |
© 2026 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license.
Share and Cite
Si, H.; Huang, Y.; Li, G.; Zhao, Y.; Qi, Y.; Chen, W.; Gao, Z. A Cryptocurrency Dual-Offline Payment Method for Payment Capacity Privacy Protection. Electronics 2026, 15, 400. https://doi.org/10.3390/electronics15020400
Si H, Huang Y, Li G, Zhao Y, Qi Y, Chen W, Gao Z. A Cryptocurrency Dual-Offline Payment Method for Payment Capacity Privacy Protection. Electronics. 2026; 15(2):400. https://doi.org/10.3390/electronics15020400
Chicago/Turabian StyleSi, Huayou, Yaqian Huang, Guozheng Li, Yun Zhao, Yuanyuan Qi, Wei Chen, and Zhigang Gao. 2026. "A Cryptocurrency Dual-Offline Payment Method for Payment Capacity Privacy Protection" Electronics 15, no. 2: 400. https://doi.org/10.3390/electronics15020400
APA StyleSi, H., Huang, Y., Li, G., Zhao, Y., Qi, Y., Chen, W., & Gao, Z. (2026). A Cryptocurrency Dual-Offline Payment Method for Payment Capacity Privacy Protection. Electronics, 15(2), 400. https://doi.org/10.3390/electronics15020400






