MedChain: Efficient Healthcare Data Sharing via Blockchain
Abstract
1. Introduction
- (1)
- It has described a MedChain data-sharing framework for flexibly managing different types of information derived from healthcare data.
- (2)
- It has also devised a chained digest creation approach to efficiently check the integrity of shared medical IoT data stream.
- (3)
- It has provided a session-based data-sharing scheme for achieving efficiency improvement and the security, integrity, auditability, and privacy-preservation goals.
2. Related Works
3. MedChain Model
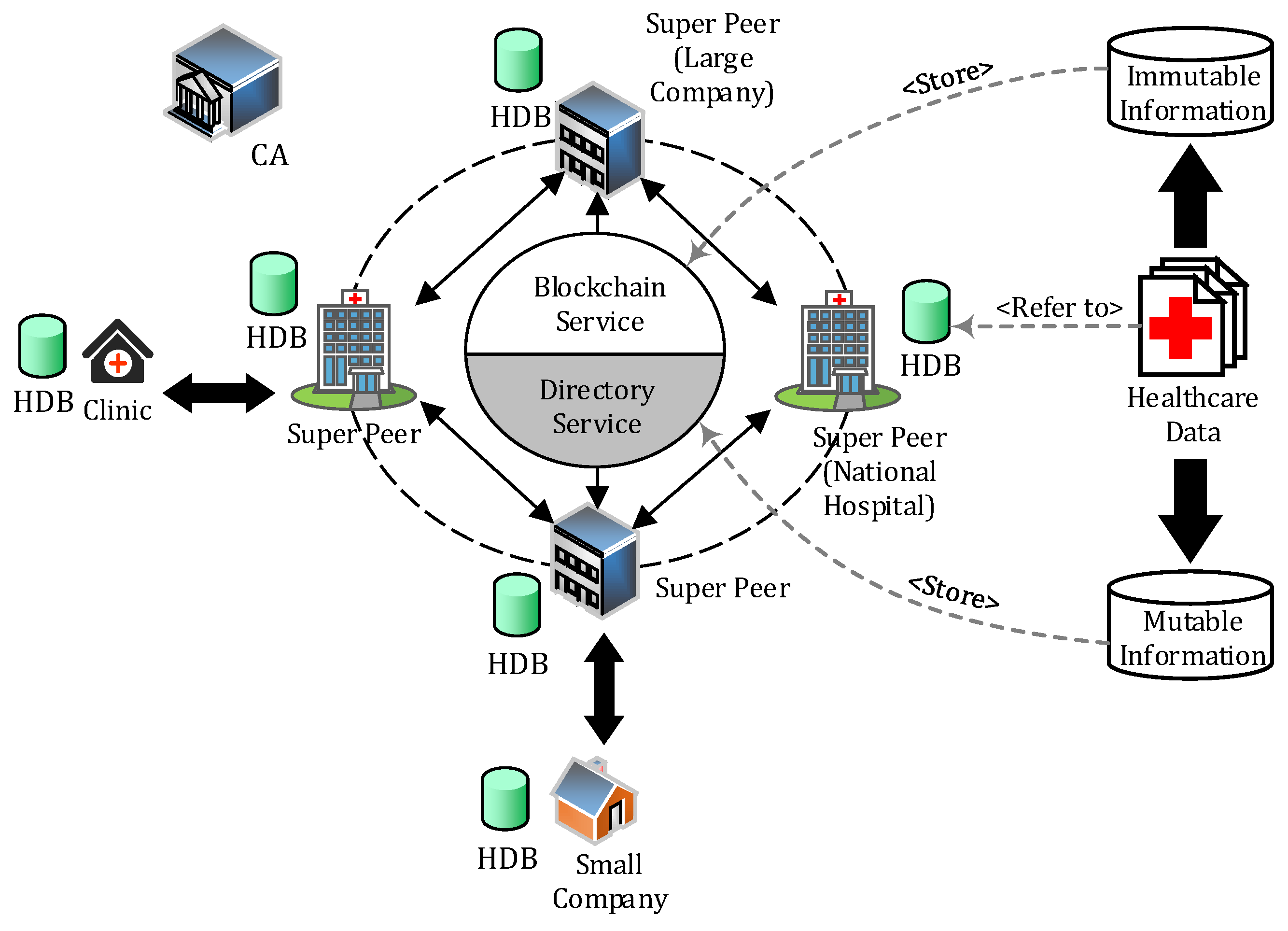
3.1. System Architecture
3.2. Preliminaries
3.2.1. Healthcare Data
3.2.2. User Roles
- (1)
- Patient: shares their data through MedChain with, for instance, a doctor, an insurance company, or a research center for medical consultancy.
- (2)
- Requester: who could be, e.g., a doctor, asks a patient to share some of her healthcare data through MedChain.
- (3)
- Healthcare provider: maintains the actual healthcare data of patients.
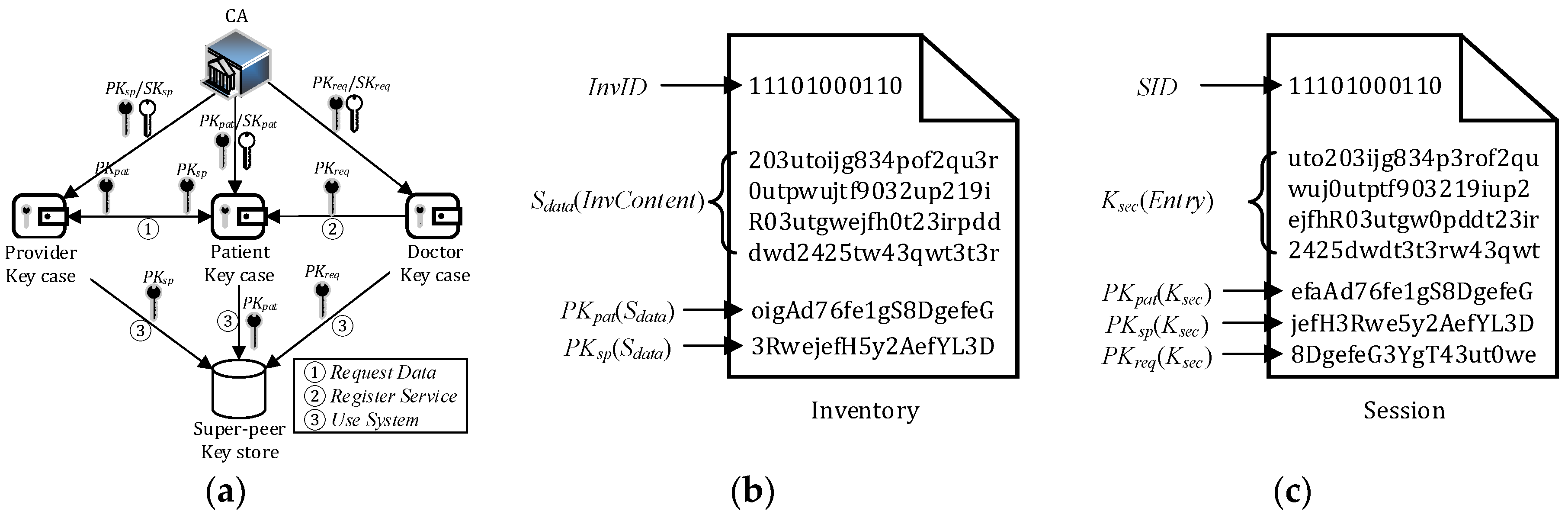
3.2.3. Cryptographic Keys
- Patient public-private key pair (PKpat/SKpat).
- Healthcare provider public-private key pair (PKsp/SKsp).
- Requester public-private key pair (PKreq/SKreq).
- Inventory secret Sdata: a symmetric secret key for patient inventory access, generated by a healthcare provider.
- Section secret Ksec: a symmetric secret key for accessing a section of a session, generated by the patient.
- Ekey(m): encrypts message m with key.
- Dkey(m): decrypts message m with key.
- H(m): creates a hash code/digest of content m.
3.2.4. Other Notations
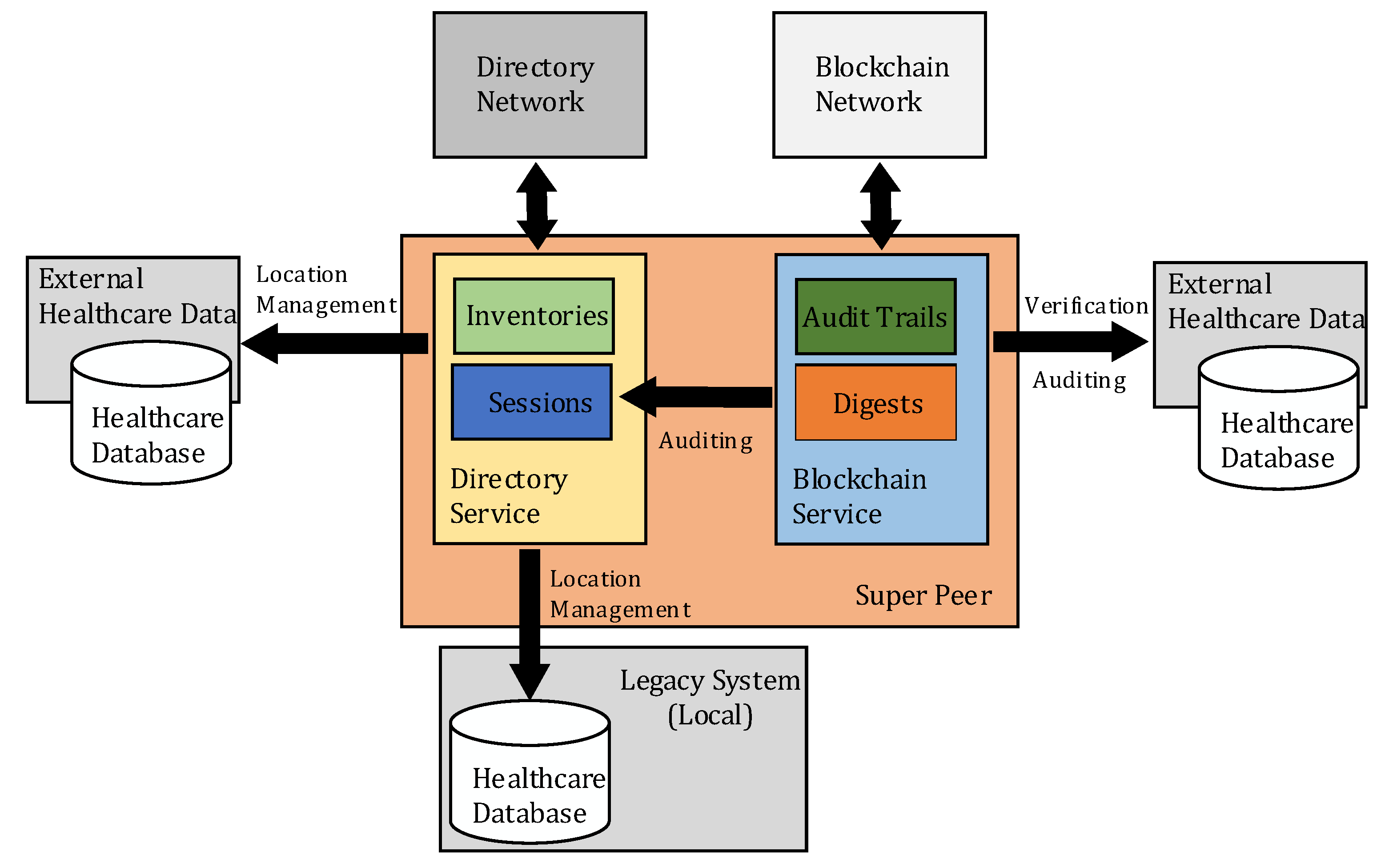
3.3. Blockchain Service
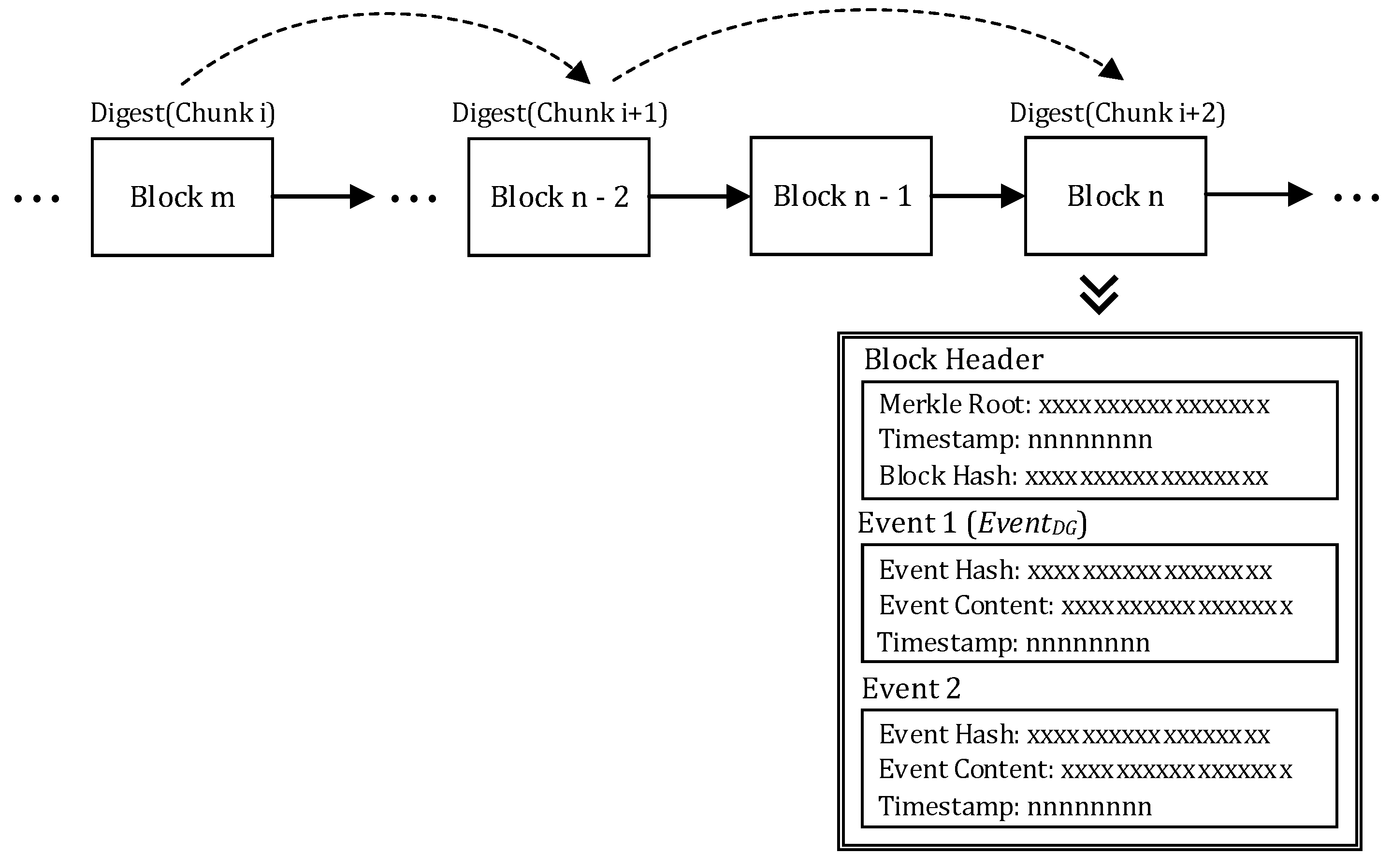
- Merkle Root. The root of the Merkle tree [37] constructed by all the event hashes in the block.
- Timestamp: The time of when the block is created.
- Block hash: The hash code computed based on the hash of the last block, the Merkle root, and the timestamp.
Digest Chain
3.4. Directory Service
Search over Blockchain
4. Healthcare Data Sharing
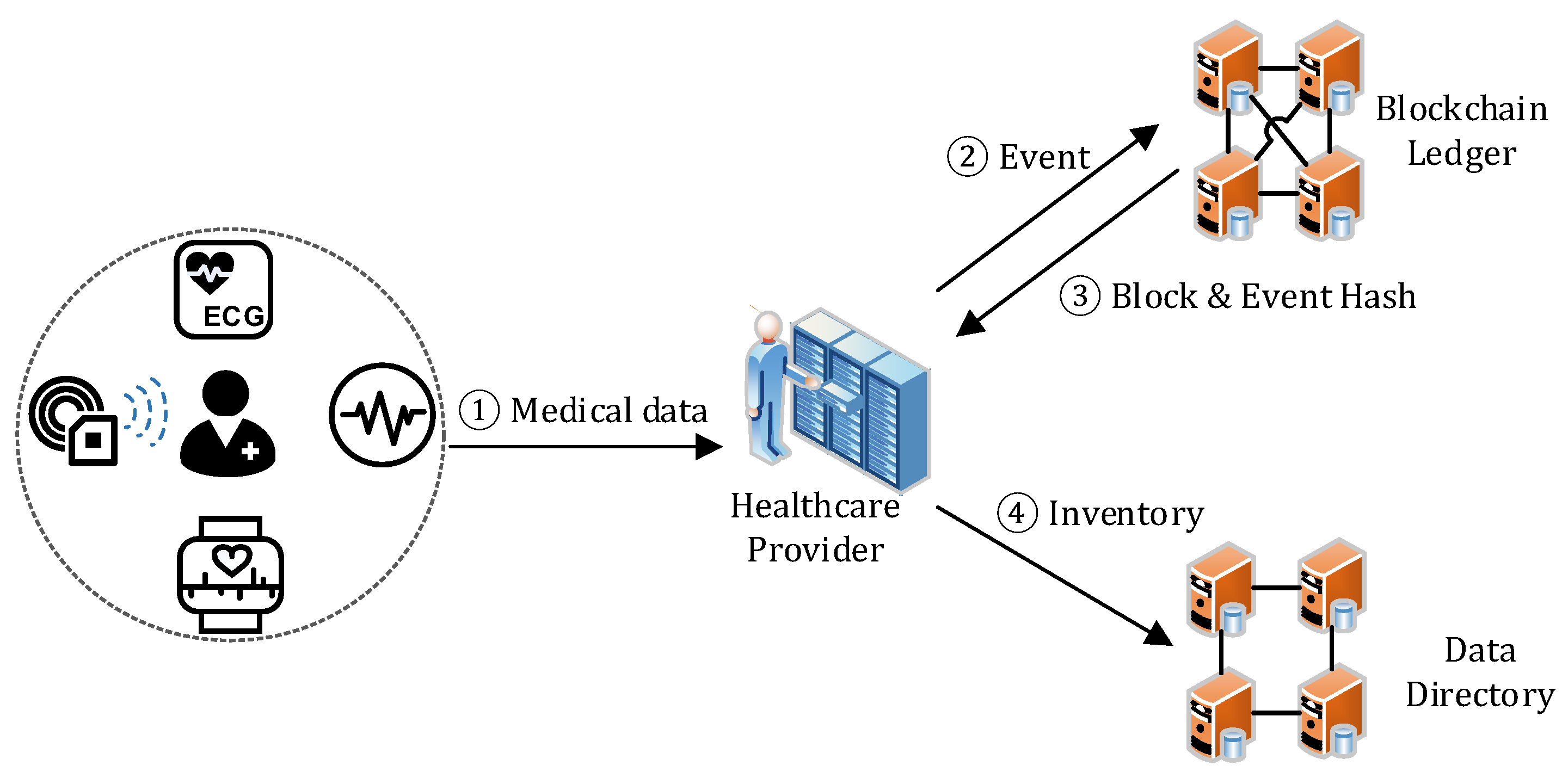
4.1. Data Generation
- Step 1. The healthcare provider collects the healthcare data from a patient through medical devices and sensors.
- Step 2–3. The healthcare provider creates an EventDG and sends it to the blockchain. The blockchain service adds the EventDG to a new block together with other received events, and then replies the block hash and the event hash to the provider.
- Step 4. The healthcare provider adds a new entry to the patient’s inventory for describing the data. If the inventory does not exist, a new inventory will be created. Later, the patient can access it by decrypting the inventory with Sdata, which is retrieved by decrypting the corresponding ESpat with his/her SKpat.
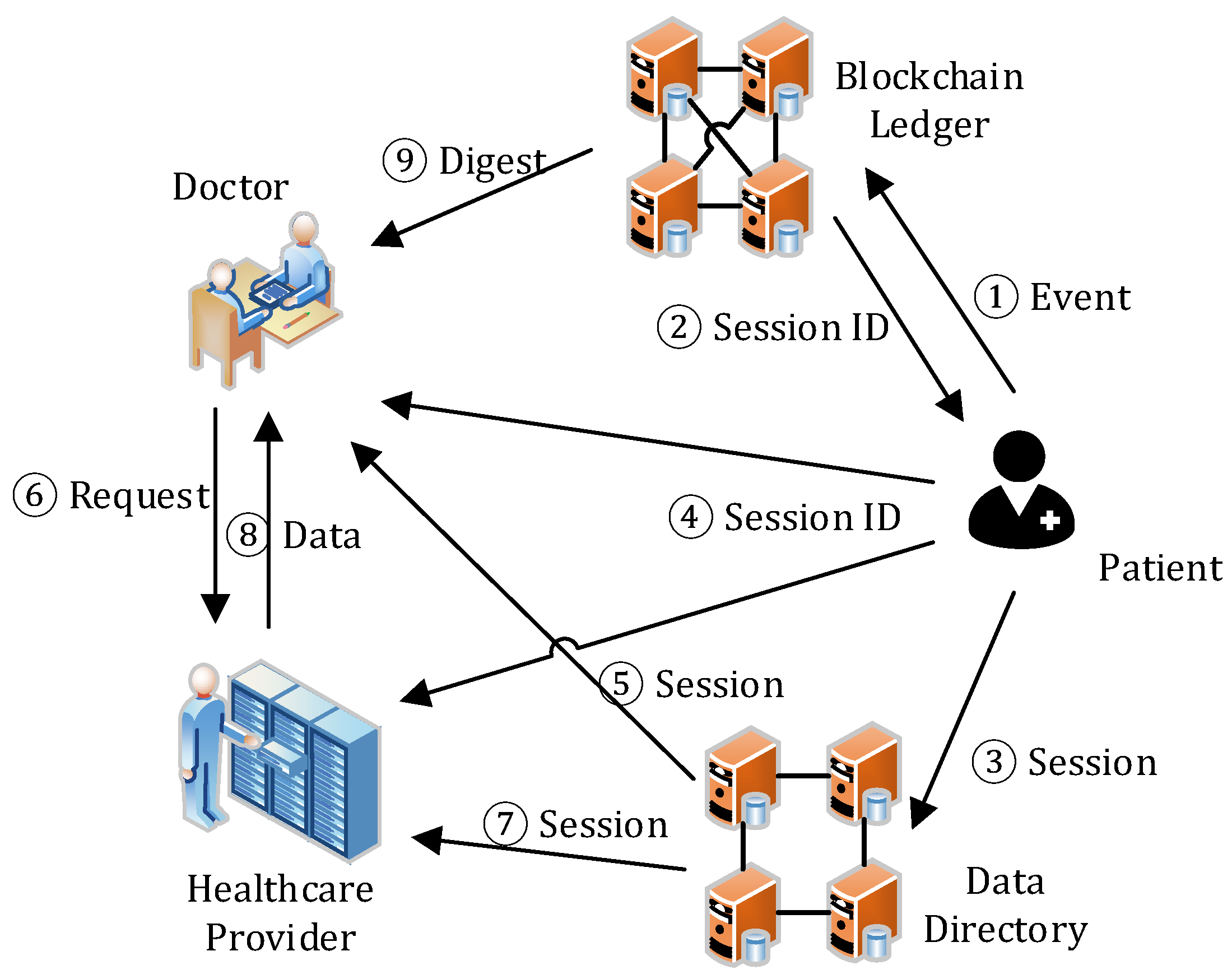
4.2. Session Management
- Step 1–2. As per request, the patient selects the data from his/her inventory for sharing, creates a session with the selected data descriptions and the PKreq, encrypts them with SKpat, generates the session digest to maintain session integrity, creates an EventSC, and sends it to the blockchain service. The blockchain service adds the EventSC to a new block together with other received events, and appends the block to the end of the blockchain. Then, it sends back the SID (i.e., the event hash of EventSC) to the patient.
- Step 3–4. The patient then creates a session in the directory service with the received SID, and notifies the requester and the healthcare provider of the session by sending them the SID. He/she uses Ksec to encrypt the content of the session and then PKreq to encrypt the session key.
- Step 5–6. With the SID, the requester can find and access the session. After decrypting the session key (Ksec) with his/her SKreq and the session with the Ksec, the requester learns the actual location of the shared data and sends the request to the healthcare provider for data access.
- Step 7–8. On receiving the data access request, the healthcare provider checks the session state in the directory service. If the session exists, it then verifies the request, including the message signature and the range of the requested. If they are all valid, the healthcare provider returns the data to the requester. In data transmission, a secure channel can be established through asymmetric encryption on the data with PKreq.
- Step 9. The requester, after receiving and decrypting the data with SKreq, verifies the data integrity by downloading the data digests from the blockchain service. If the data is valid, then he/she can access the data. If the data is invalid due to, for example, data loss/corruption during storage or transmission, an alert will be triggered, which is out of the scope of this paper.
4.3. Key Management
5. Evaluations
5.1. Security Analysis
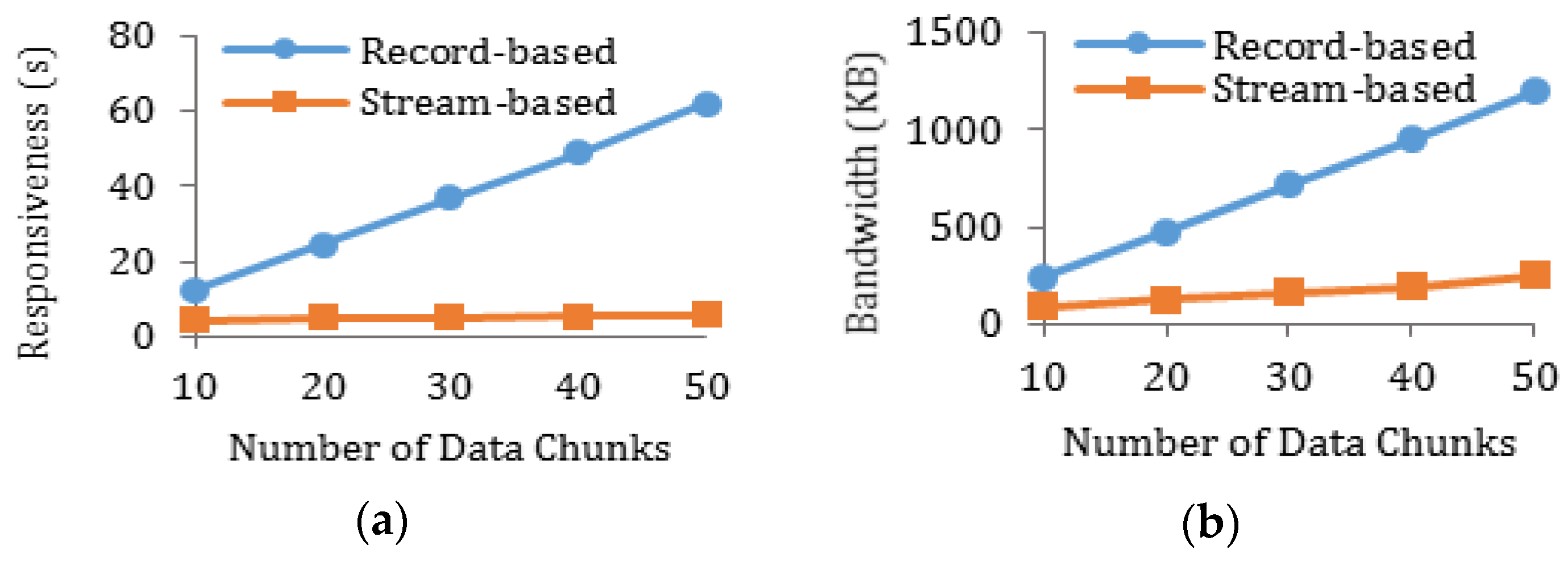
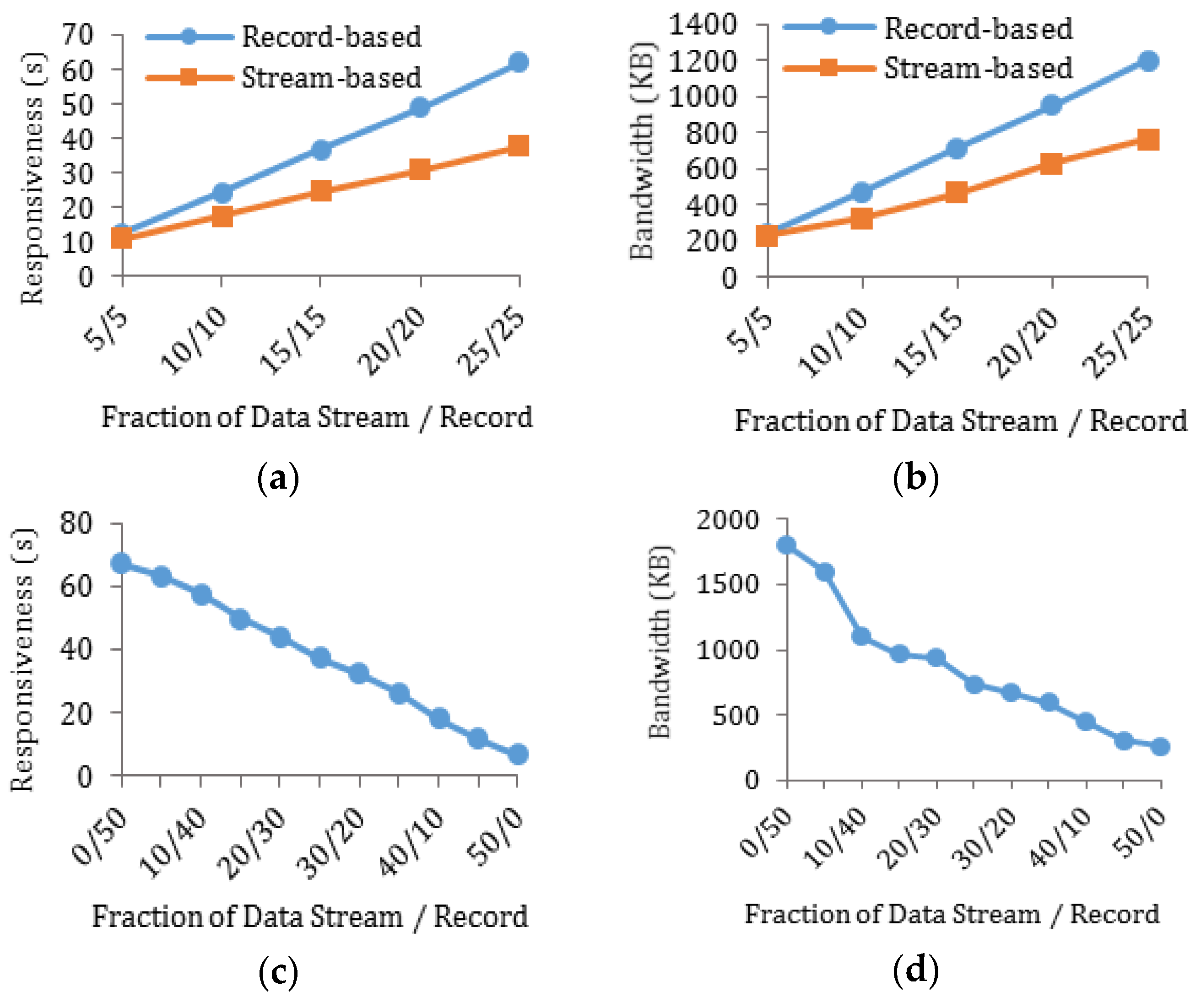
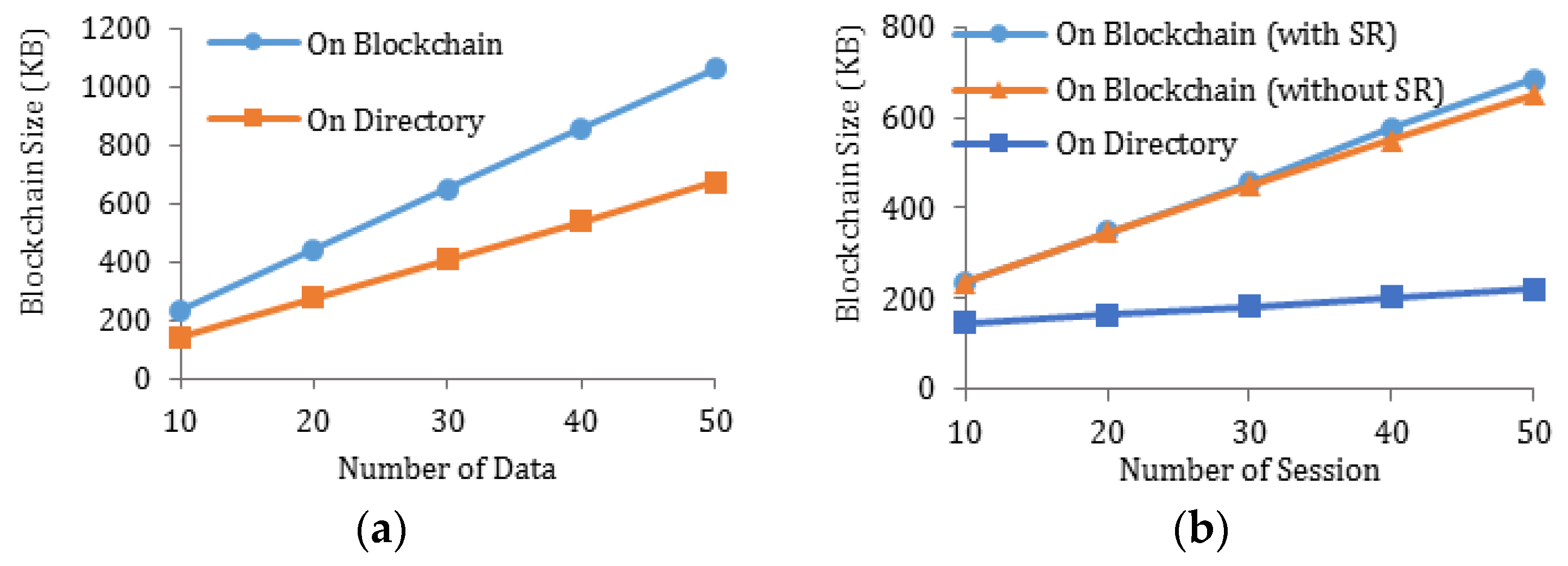
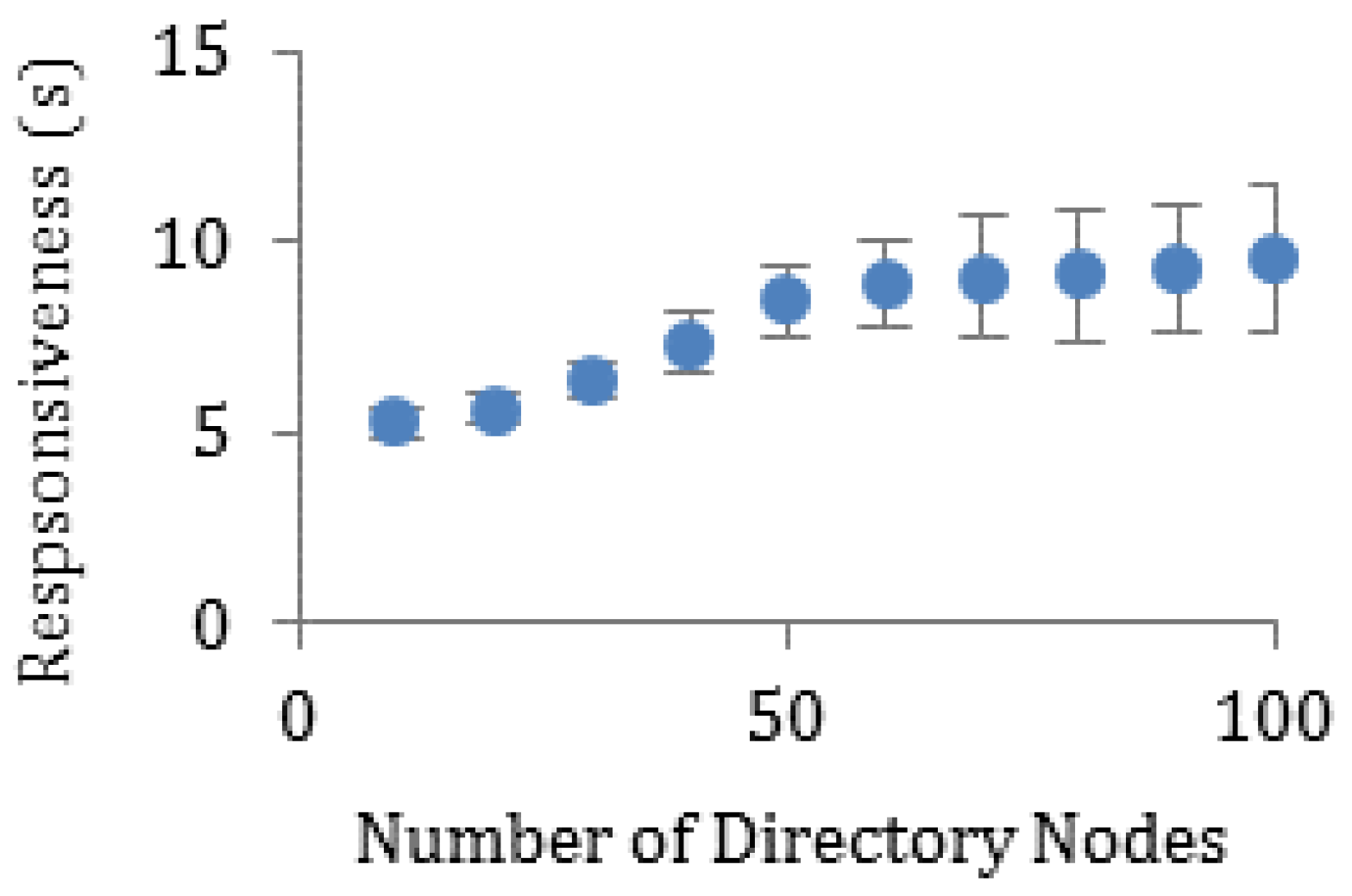
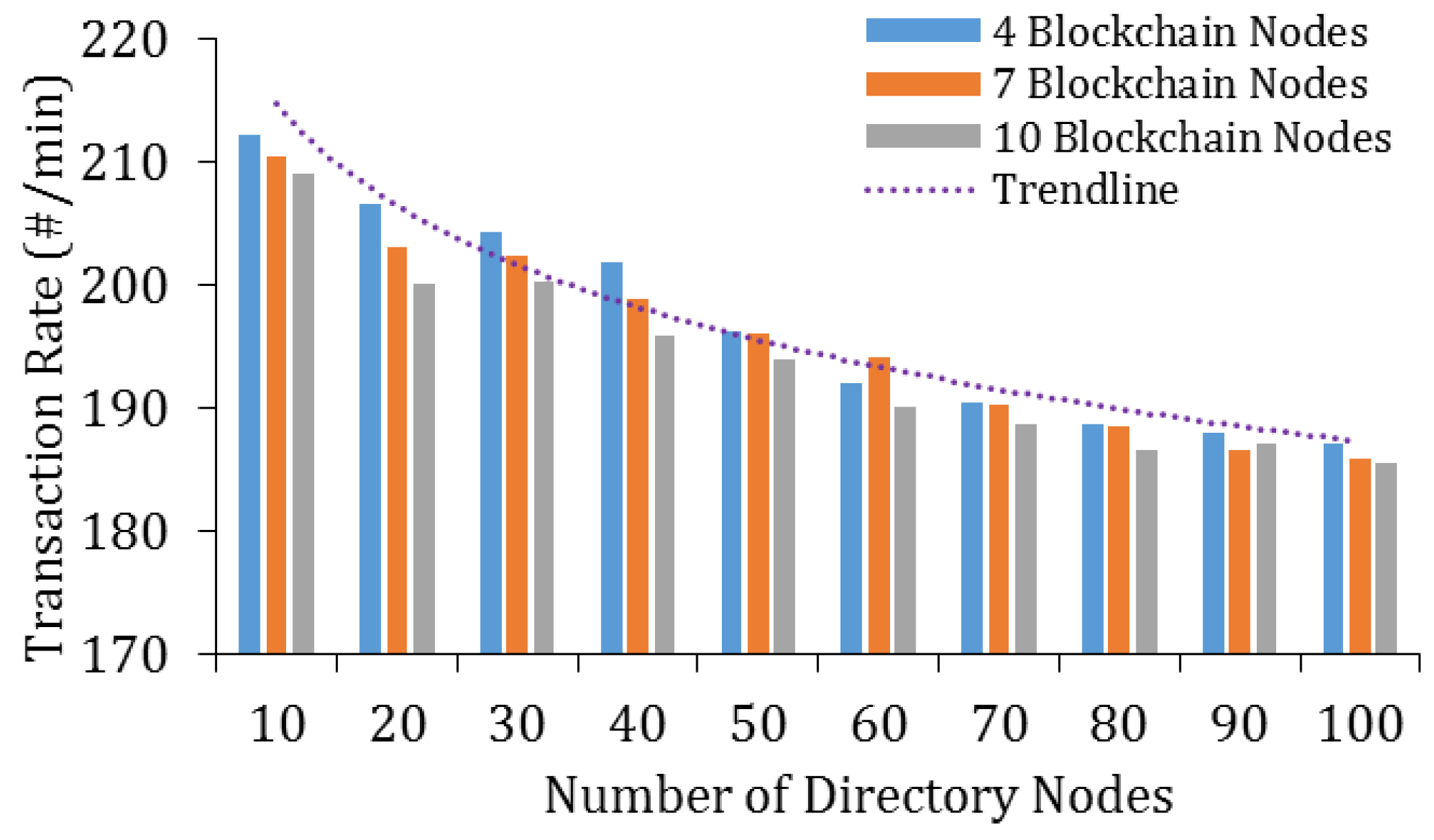
5.2. Efficiency Analysis
5.2.1. Theoretical Analysis on Digest Chain
5.2.2. Theoretical Analysis on Communication Overhead
5.2.3. Performance Analysis through Experiments
5.3. Discussion
6. Conclusions and Future Work
Author Contributions
Funding
Conflicts of Interest
References
- Farahani, B.; Firouzi, F.; Chang, V.; Badaroglu, M.; Constant, N.; Mankodiya, K. Towards fog-driven IoT eHealth: Promises and challenges of IoT in medicine and healthcare. Future Gener. Comput. Syst. 2018, 78, 659–676. [Google Scholar] [CrossRef]
- Hossain, M.; Islam, S.R.; Ali, F.; Kwak, K.S.; Hasan, R. An Internet of Things-based health prescription assistant and its security system design. Future Gener. Comput. Syst. 2018, 82, 422–439. [Google Scholar] [CrossRef]
- Badawi, H.F.; Dong, H.; Saddik, A.E. Mobile cloud-based physical activity advisory system using biofeedback sensors. Future Gener. Comput. Syst. 2017, 66, 59–70. [Google Scholar] [CrossRef]
- MarketsandMarkets Research. IoT Healthcare Market by Component (Medical Device, Systems & Software, Service, Connectivity Technology), Application (Telemedicine, Work Flow Management, Connected Imaging, Medication Management), End User, and Region—Global Forecast to 2022. Available online: https://www.marketsandmarkets.com/Market-Reports/iot-healthcare-market-160082804.html (accessed on 21 December 2018).
- Sahi, M.A.; Abbas, H.; Saleem, K.; Yang, X.; Derhab, A.; Orgun, M.A.; Yaseen, A. Privacy Preservation in e-Healthcare Environments: State of the Art and Future Directions. IEEE Access 2018, 6, 464–478. [Google Scholar] [CrossRef]
- Chen, Y.Y.; Lu, J.C.; Jan, J.K. A secure EHR system based on hybrid clouds. J. Med. Syst. 2012, 36, 3375–3384. [Google Scholar] [CrossRef] [PubMed]
- Abrar, H.; Hussain, S.J.; Chaudhry, J.; Saleem, K.; Orgun, M.A.; Al-Muhtadi, J.; Valli, C. Risk Analysis of Cloud Sourcing in Healthcare and Public Health Industry. IEEE Access 2018, 6, 19140–19150. [Google Scholar] [CrossRef]
- Gordon, W.J.; Catalini, C. Blockchain Technology for Healthcare: Facilitating the Transition to Patient-Driven Interoperability. Comput. Struct. Biotechnol. J. 2018, 16, 224–230. [Google Scholar] [CrossRef]
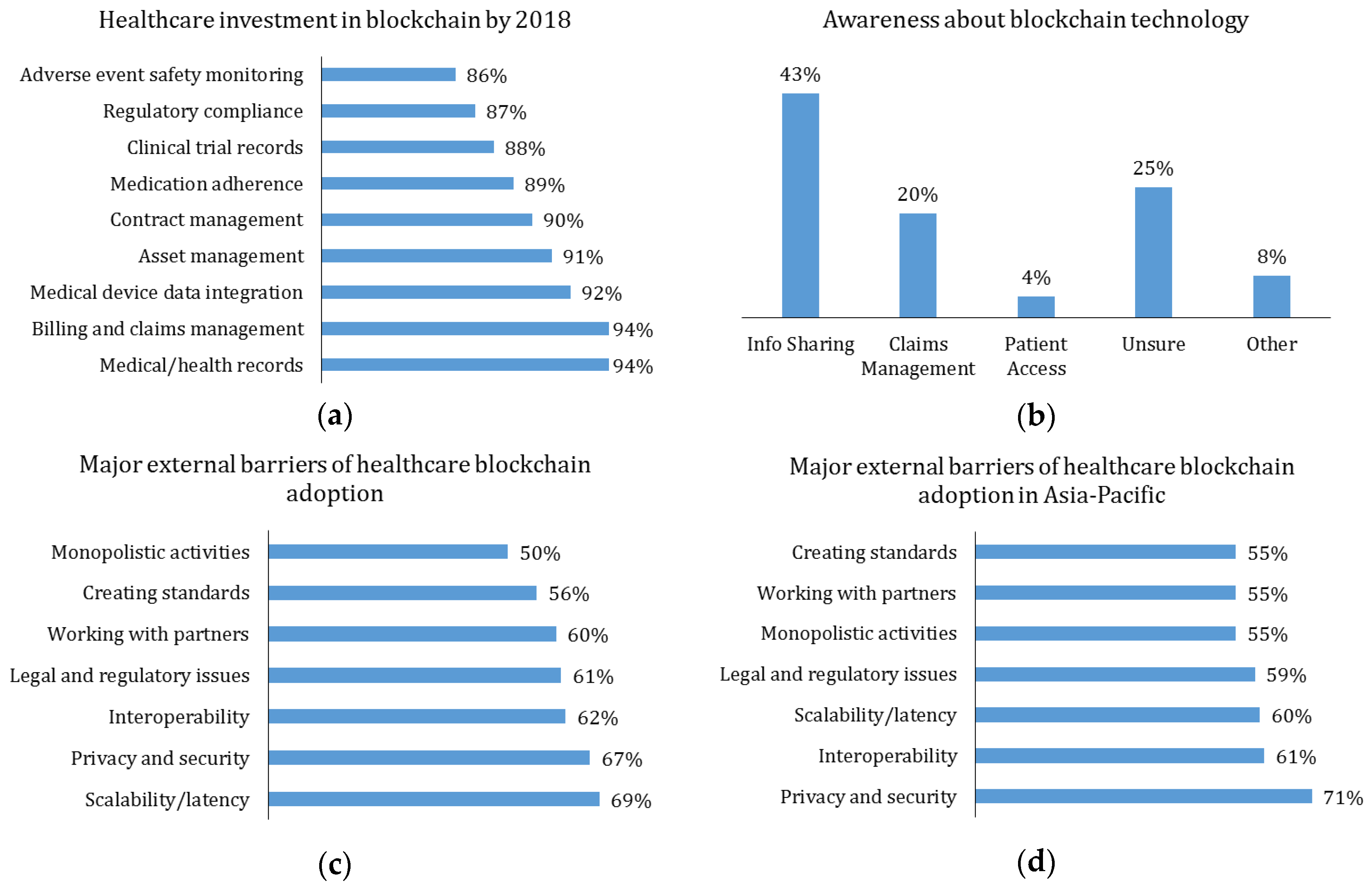
- The Economist Intelligence Unit of IBM Institute for Business Value. Healthcare Rallies for Blockchains: Keeping Patients at the Center. Healthcare and Blockchain Executive Report. 2017. Available online: http://www.ibm.biz/blockchainhealth (accessed on 21 December 2018).
- MGMA. Awareness about Blockchain Technology in the U.S. among Medical Practice Administrators and Executives as of 2017. In Statista—The Statistics Portal. Available online: https://www.statista.com/statistics/828392/knowledge-of-blockchain-technology-and-its-areas-of-impact-in-healthcare/ (accessed on 21 December 2018).
- Cognizant. Healthcare: Blockchain’s CurativePotential for HealthcareEfficiency and Quality. Digital Systems & Technology. 2017. Available online: https://www.cognizant.com/whitepapers/healthcare-blockchains-curative-potential-for-healthcare-efficiency-and-quality-codex2995.pdf (accessed on 21 December 2018).
- Cognizant. Major External Barriers to Adopt Blockchain in Companies in Asia-Pacific in 2017. In Statista—The Statistics Portal. Available online: https://www-statista-com.unh-proxy01.newhaven.edu/statistics/882562/asia-pacific-external-barrier-to-adopt-blockchain-in-companies/ (accessed on 21 December 2018).
- Miller, A.R.; Tucker, C. Health information exchange, system size and information silos. J. Health Econ. 2014, 33, 28–42. [Google Scholar] [CrossRef]
- Sinaci, A.A.; Erturkmen, G.B.L. A federated semantic metadata registry framework for enabling interoperability across clinical research and care domains. J. Biomed. Inform. 2013, 46, 784–794. [Google Scholar] [CrossRef]
- Featherstone, I.; Keen, J. Do integrated record systems lead to integrated services? An observational study of a multi-professional system in a diabetes service. Int. J. Med. Inform. 2012, 81, 45–52. [Google Scholar] [CrossRef]
- Rinner, C.; Sauter, S.K.; Endel, G.; Heinze, G.; Thurner, S.; Klimek, P.; Duftschmid, G. Improving the informational continuity of care in diabetes mellitus treatment with a nationwide shared EHR system: Estimates from Austrian claims data. Int. J. Med. Inform. 2016, 92, 44–53. [Google Scholar] [CrossRef] [PubMed]
- Hyppönen, H.; Reponen, J.; Lääveri, T.; Kaipio, J. User experiences with different regional health information exchange systems in Finland. Int. J. Med. Inform. 2014, 83, 1–18. [Google Scholar] [CrossRef]
- Yang, Y.; Li, X.; Qamar, N.; Liu, P.; Ke, W.; Shen, B.; Liu, Z. MedShare: A Novel Hybrid Cloud for Medical Resource Sharing among Autonomous Healthcare Providers. IEEE Access 2018, 6, 46949–46961. [Google Scholar] [CrossRef]
- Yang, Y.; Quan, Z.; Liu, P.; Ouyang, D.; Li, X. MicroShare: Privacy-Preserved Medical Resource Sharing through MicroService Architecture. Int. J. Biol. Sci. 2018, 14, 907–919. [Google Scholar] [CrossRef] [PubMed]
- Walker-Roberts, S.; Hammoudeh, M.; Dehghantanha, A. A Systematic Review of the Availability and Efficacy of Countermeasures to Internal Threats in Healthcare Critical Infrastructure. IEEE Access 2018, 6, 25167–25177. [Google Scholar] [CrossRef]
- Liu, Y.; Zhang, Y.; Ling, J.; Liu, Z. Secure and fine-grained access control on e-healthcare records in mobile cloud computing. Future Gener. Comput. Syst. 2018, 78, 1020–1026. [Google Scholar] [CrossRef]
- Wang, H. Anonymous Data Sharing Scheme in Public Cloud and Its Application in E-health Record. IEEE Access 2018, 6, 27818–27826. [Google Scholar] [CrossRef]
- Mehmood, A.; Natgunanathan, I.; Xiang, Y.; Poston, H.; Zhang, Y. Anonymous Authentication Scheme for Smart Cloud Based Healthcare Applications. IEEE Access 2018, 6, 33552–33567. [Google Scholar] [CrossRef]
- Yao, X.; Lin, Y.; Liu, Q.; Zhang, J. Privacy-preserving search over encrypted personal health record in multi-source cloud. IEEE Access 2018, 6, 3809–3823. [Google Scholar] [CrossRef]
- Zissis, D.; Lekkas, D. Addressing cloud computing security issues. Future Gener. Comput. Syst. 2012, 28, 583–592. [Google Scholar] [CrossRef]
- Yüksel, B.; Küpçü, A.; Özkasap, Ö. Research issues for privacy and security of electronic health services. Future Gener. Comput. Syst. 2017, 68, 1–13. [Google Scholar] [CrossRef]
- Yue, X.; Wang, H.; Jin, D.; Li, M.; Jiang, W. Healthcare data gateways: Found healthcare intelligence on blockchain with novel privacy risk control. J. Med. Syst. 2016, 40, 218–225. [Google Scholar] [CrossRef] [PubMed]
- Al Omar, A.; Rahman, M.S.; Basu, A.; Kiyomoto, S. MediBchain: A blockchain based privacy preserving platform for healthcare data, Security, Privacy, and Anonymity in Computation, Communication, and Storage, Guangzhou, China, 12–15 December, 2017; Wang, G., Atiquzzaman, M., Yan, Z., Choo, K.K., Eds.; Springer: Cham, Switzerland, 2017. [Google Scholar]
- Guo, R.; Shi, H.; Zhao, Q.; Zheng, D. Secure attribute-based signature scheme with multiple authorities for Blockchain in electronic health records systems. IEEE Access 2018, 6, 11676–11686. [Google Scholar] [CrossRef]
- Li, H.; Zhu, L.; Shen, M.; Gao, F.; Tao, X.; Liu, S. Blockchain-Based Data Preservation System for Medical Data. J. Med. Syst. 2018, 42, 1–13. [Google Scholar] [CrossRef] [PubMed]
- Xia, Q.; Sifah, E.B.; Asamoah, K.O.; Gao, J.; Du, X.; Guizani, M. MeDShare: Trust-less medical data sharing among cloud service providers via blockchain. IEEE Access 2017, 5, 14757–14767. [Google Scholar] [CrossRef]
- Patel, V. A framework for secure and decentralized sharing of medical imaging data via blockchain consensus. Health Inform. J. 2018, 1–14. [Google Scholar] [CrossRef] [PubMed]
- Azaria, A.; Ekblaw, A.; Vieira, T.; Lippman, A. MedRec: Using blockchain for medical data access and permission management. In Proceedings of the 2016 2nd International Conference on Open and Big Data (OBD), Vienna, Austria, 22–24 August 2016; pp. 25–30. [Google Scholar] [CrossRef]
- Fan, K.; Wang, S.; Ren, Y.; Li, H.; Yang, Y. MedBlock: Efficient and Secure Medical Data Sharing Via Blockchain. J. Med. Syst. 2018, 42, 1–11. [Google Scholar] [CrossRef]
- Zhang, A.; Lin, X. Towards Secure and Privacy-Preserving Data Sharing in e-Health Systems via Consortium Blockchain. J. Med. Syst. 2018, 42, 1–18. [Google Scholar] [CrossRef]
- Koblitz, N. Elliptic curve cryptosystems. Math. Comput. 1987, 48, 203–209. [Google Scholar] [CrossRef]
- Merkle, R.C. A digital signature based on a conventional encryption function. In Proceedings of the Conference on the Theory and Application of Cryptographic Techniques, Santa Barbara, CA, USA, 16–20 August 1987; Pomerance, C., Ed.; Springer: Berlin/Heidelberg, Germany, 1987. [Google Scholar]
- Gramoli, V. From blockchain consensus back to byzantine consensus. Future Gener. Comput. Syst. 2017, in press. [Google Scholar] [CrossRef]
- Sousa, J.; Bessani, A. From Byzantine Consensus to BFT State Machine Replication: A Latency-Optimal Transformation. In Proceedings of the 2012 Ninth European Dependable Computing Conference, Sibiu, Romania, 8–11 May 2012; pp. 37–48. [Google Scholar] [CrossRef]
- Stoica, I.; Morris, R.; Karger, D.; Kaashoek, M.F.; Balakrishnan, H. Chord: A scalable peer-to-peer lookup service for internet applications. In Proceedings of the 2001 Conference on Applications, Technologies, Architectures, and Protocols for Computer Communications (SIGCOMM 01), San Diego, CA, USA, 27–31 August 2001; ACM: New York, NY, USA, 2001. [Google Scholar]
- Lua, E.K.; Crowcroft, J.; Pias, M.; Sharma, R.; Lim, S. A survey and comparison of peer-to-peer overlay network schemes. IEEE Commun. Surv. Tutor. 2005, 7, 72–93. [Google Scholar] [CrossRef]
- MedChain Source Code. Available online: https://github.com/sunniel/MedChain (accessed on 21 December 2018).
- WANem—The Wide Area Network Emulator. Available online: http://wanem.sourceforge.net (accessed on 21 December 2018).
- Moody, G.B.; Mark, R.G. The impact of the MIT-BIH Arrhythmia Database. IEEE Eng. Med. Biol. Mag. 2001, 20, 45–50. [Google Scholar] [CrossRef] [PubMed]
- Goldberger, A.L.; Amaral, L.A.N.; Glass, L.; Hausdorff, J.M.; Ivanov, P.C.; Mark, R.G.; Mietus, J.E.; Moody, G.B.; Peng, C.K.; Stanley, H.E. PhysioBank, PhysioToolkit, and PhysioNet: Components of a New Research Resource for Complex Physiologic Signals. Circulation 2000, 101, e215–e220. [Google Scholar] [CrossRef] [PubMed]
- Baden, R.; Bender, A.; Spring, N.; Bhattacharjee, B.; Starin, D. Persona: An online social network with user-defined privacy. In Proceedings of the ACM SIGCOMM 2009 Conference on Data Communication (SIGCOMM 09), Barcelona, Spain, 17–21 August 2009; ACM: New York, NY, USA, 2009. [Google Scholar]
- Ananth, C.; Karthikeyan, M.; Mohananthini, N. A secured healthcare system using private blockchain technology. J. Eng. Technol. 2018, 6, 42–54. [Google Scholar]
- Rahurkar, S.; Vest, J.R.; Menachemi, N. Despite the spread of health information exchange, there is little evidence of its impact on cost, use, and quality of care. Health Aff. 2015, 34, 477–483. [Google Scholar] [CrossRef] [PubMed]
| Notation | Description |
|---|---|
| Definition | |
| Tuple, representing data or message format | |
| Set, representing one or more items of the same type | |
| Optional element(s) | |
| Exclusive disjunction (XOR) | |
| String concatenation operation | |
| . | Membership |
| Message transmission | |
| Assignment |
| Operation | MedChain | Existing Solutions |
|---|---|---|
| Add Data | (TQb +) TQd + TE + TD + TB | TE + TD + TB |
| Add Session | k⋯(TQd + TE) + TD + TB | N/A |
| Retrieve Data | TQd + k⋯(TE′ + n⋯(TQb + TD)) | k⋯n⋯(TE′ + TQb + TD) |
| Parameter | Value |
|---|---|
| Machine Specs | Dell server (CPU: 2.93 GHz quad-core Intel Core i7 870, Cache: 8 M, RAM: 16 G of 2400 MHz DDR3, OS: Windows 7) |
| Network Latency | 50 ms + Jitter (Normal Distribution) |
| Directory Node Concurrency | 10 tasks |
| Blockchain Node Concurrency | 30 tasks |
| Maximal Block Size | 400 events |
| Metrics | [28] | [30] | [31] | [32] | [33] | [34] | [35] | MedChain |
|---|---|---|---|---|---|---|---|---|
| Tamper-proof | Y | Y | Y | Y | Y | Y | Y | Y |
| Non-Repudiation | Y | Y | Y | Y | Y | Y | Y | Y |
| Attack Resistance | Y | Y | Y | Y | Y | Y | Y | Y |
| Access Control | N | N | Y | Y | Y | N | Y | Y |
| Access Revocation | N | N | Y | N | N | N | Y | Y |
| Privacy-Preserving | Y | N | N | N | N | Y | Y | Y |
| Block Search | N | N | N | N | Y | Y | Y | Y |
| Metadata Update | N | N | N | N | N | N | N | Y |
| Storage Space Recycling | N | N | N | N | N | N | N | Y |
| Data Stream Support | N | N | N | N | N | N | N | Y |
© 2019 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (http://creativecommons.org/licenses/by/4.0/).
Share and Cite
Shen, B.; Guo, J.; Yang, Y. MedChain: Efficient Healthcare Data Sharing via Blockchain. Appl. Sci. 2019, 9, 1207. https://doi.org/10.3390/app9061207
Shen B, Guo J, Yang Y. MedChain: Efficient Healthcare Data Sharing via Blockchain. Applied Sciences. 2019; 9(6):1207. https://doi.org/10.3390/app9061207
Chicago/Turabian StyleShen, Bingqing, Jingzhi Guo, and Yilong Yang. 2019. "MedChain: Efficient Healthcare Data Sharing via Blockchain" Applied Sciences 9, no. 6: 1207. https://doi.org/10.3390/app9061207
APA StyleShen, B., Guo, J., & Yang, Y. (2019). MedChain: Efficient Healthcare Data Sharing via Blockchain. Applied Sciences, 9(6), 1207. https://doi.org/10.3390/app9061207





