An Intrusion Detection and Classification System for IoT Traffic with Improved Data Engineering
Abstract
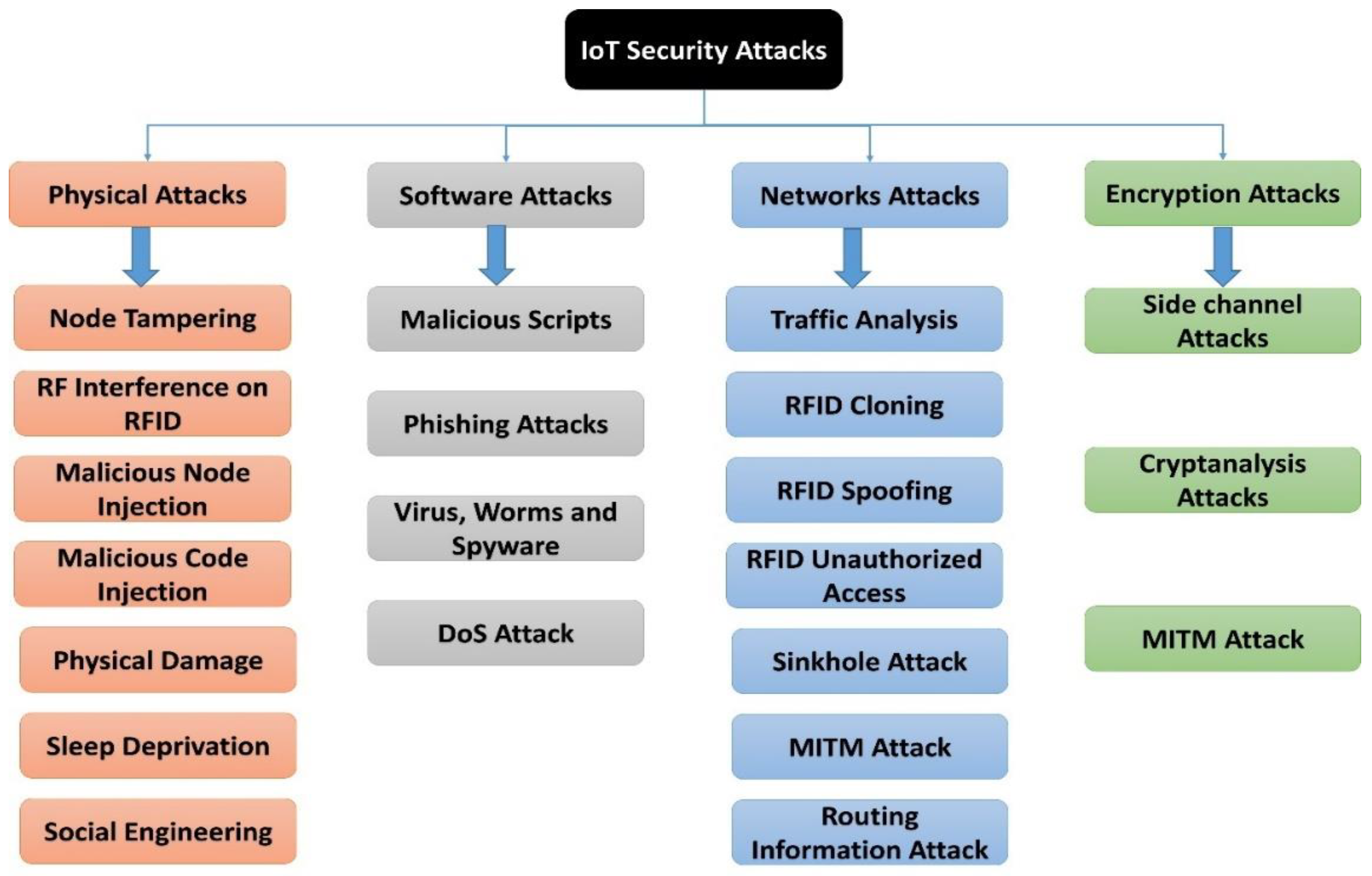
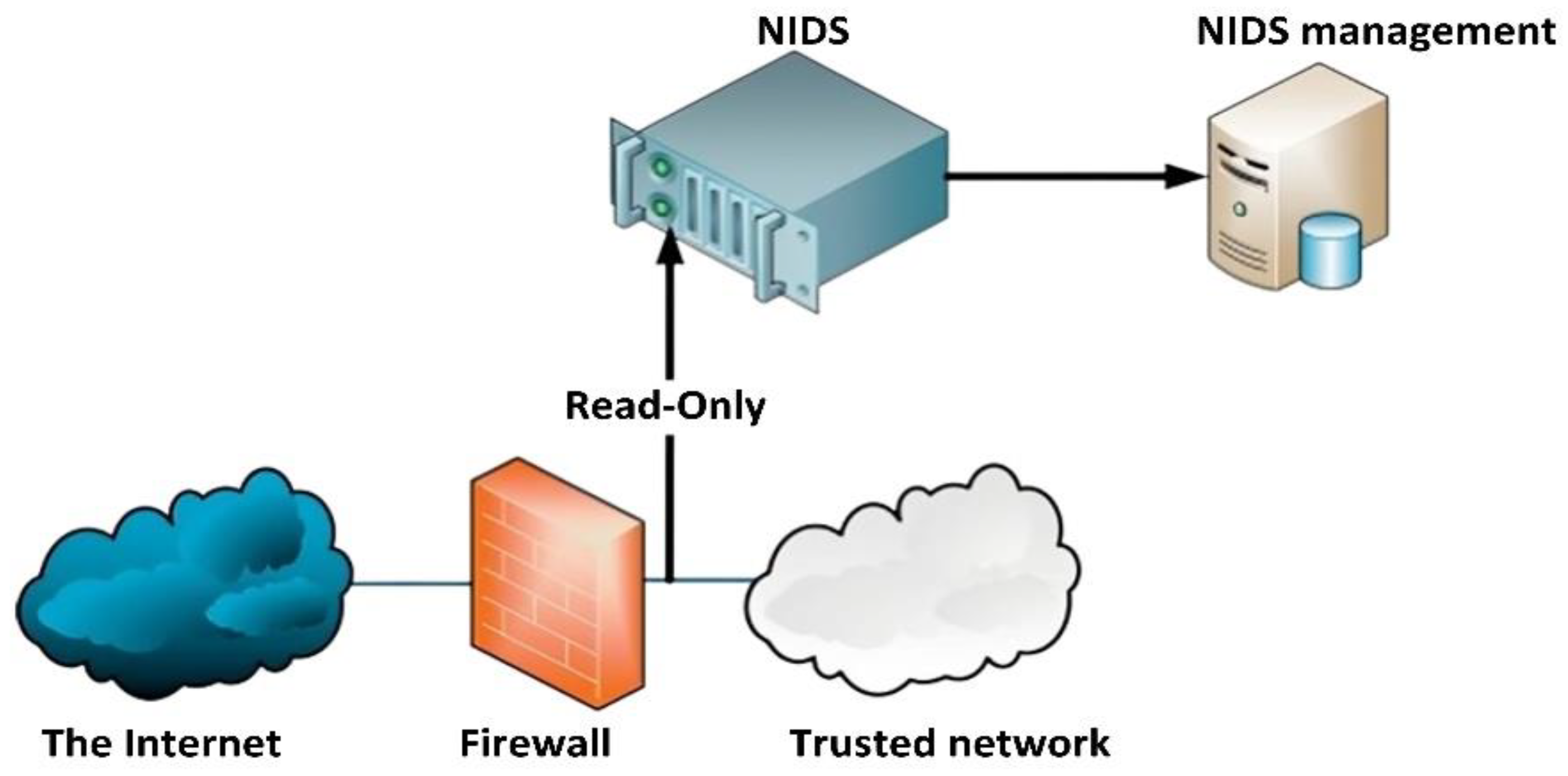
1. Introduction
1.1. Our Contributions
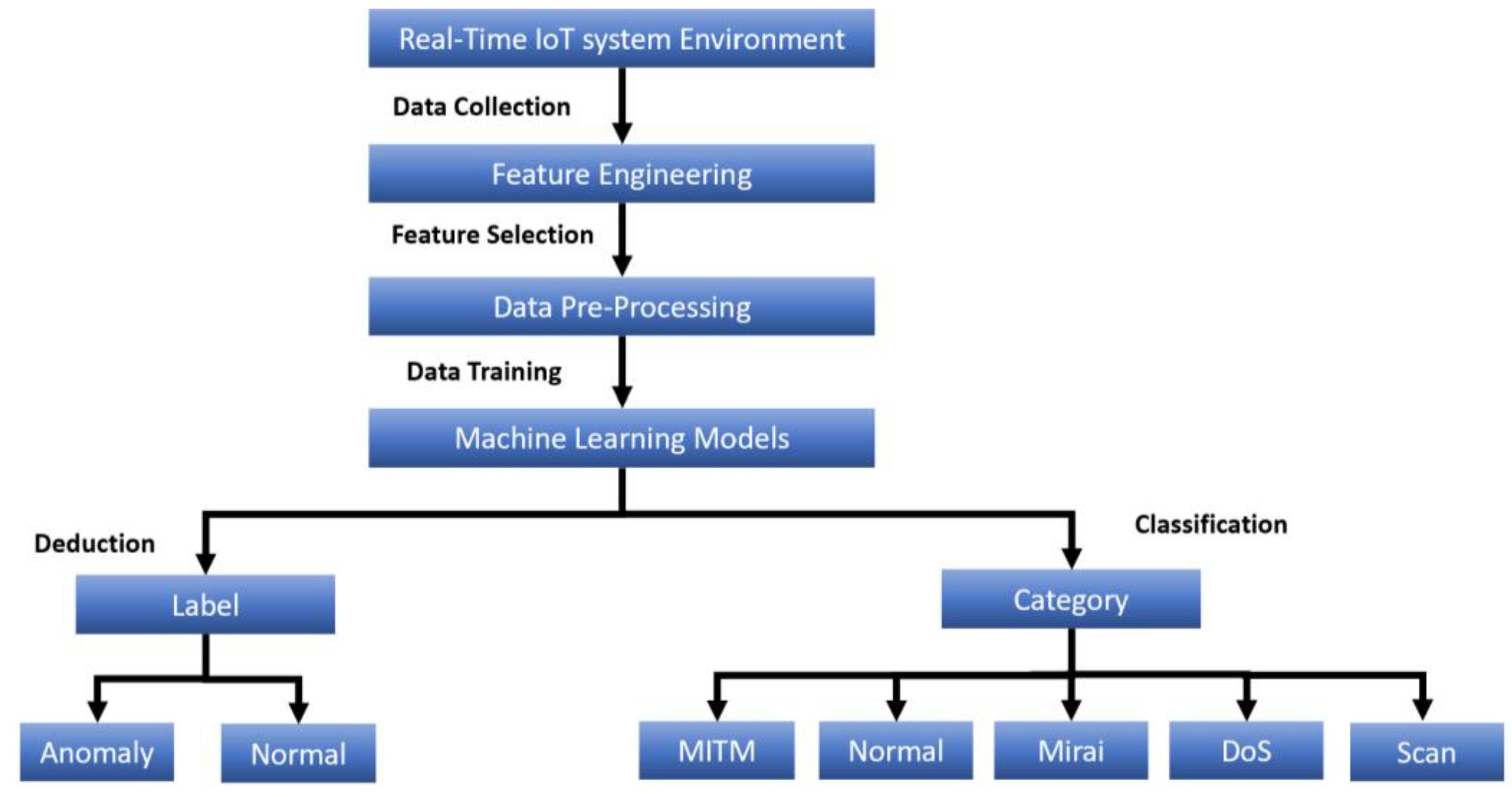
- We present a comprehensive intrusion detection and classification system that can identify and classify the IoT traffic of an IoTID20 dataset into binary classes (normal and anomaly) or five classes (normal, Mirai attack, DoS attack, Scan attack, and MITM attack). In addition, we stipulate an illuminated depiction of our system modules and the machine learning algorithms.
- We provide an extensive feature engineering and data preprocessing framework that significantly improves the system performance evaluation. In addition, we provide a thorough development, validation environment, configurations, and extensive simulation results to better perceive the proposed solution methodology. The system has been evaluated using standard performance indicators of machine learning models such as confusion matrix, accuracy, precision, recall, F-score, and specificity.
- We compare our findings with other related state-of-the-art works, machine-learning-based intrusion detection systems (ML-IDSs), and intrusion classification systems (ML-ICSs) employing the same dataset. We show that our proposed system is superior.
1.2. Paper Organization
2. Related Research
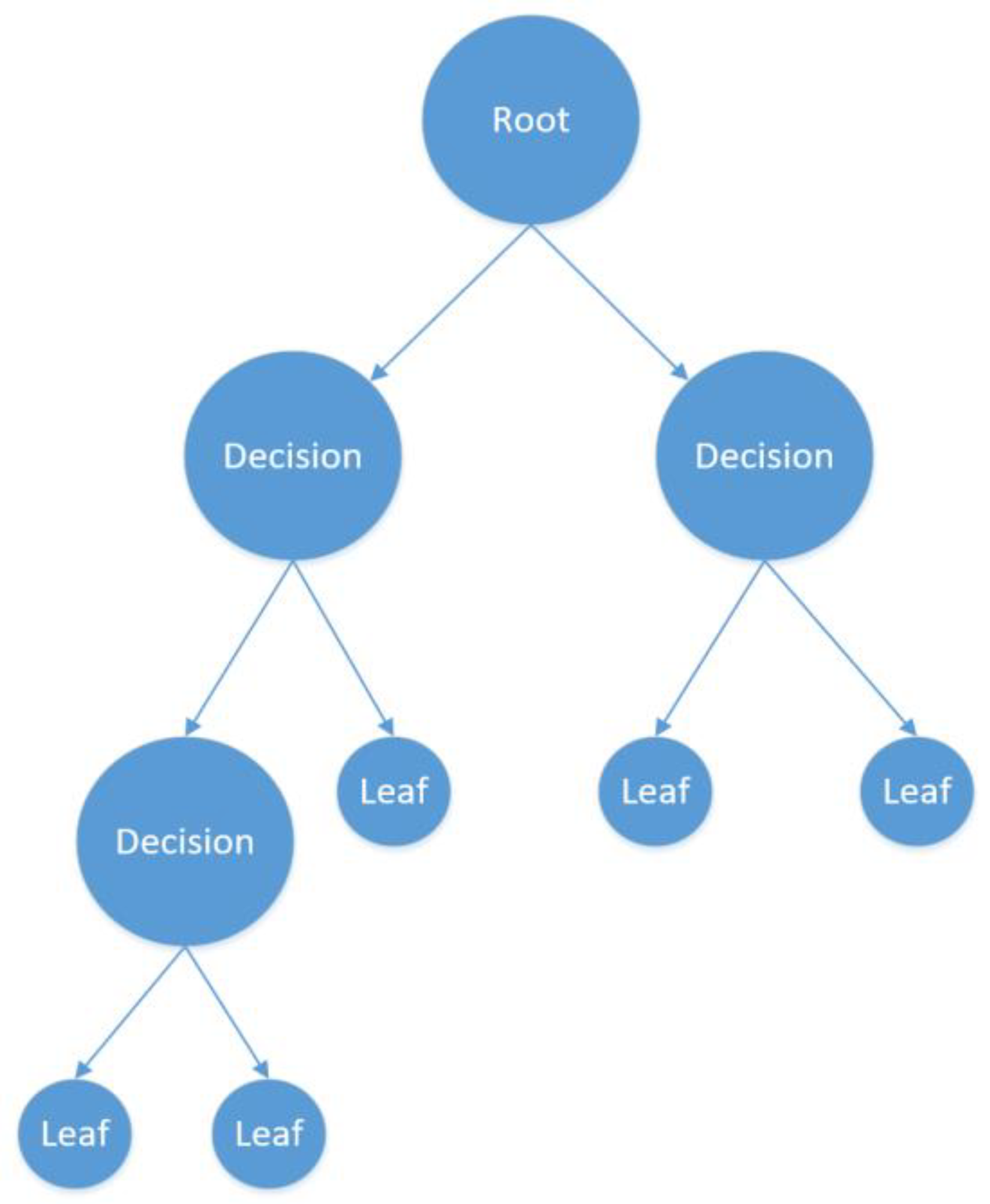
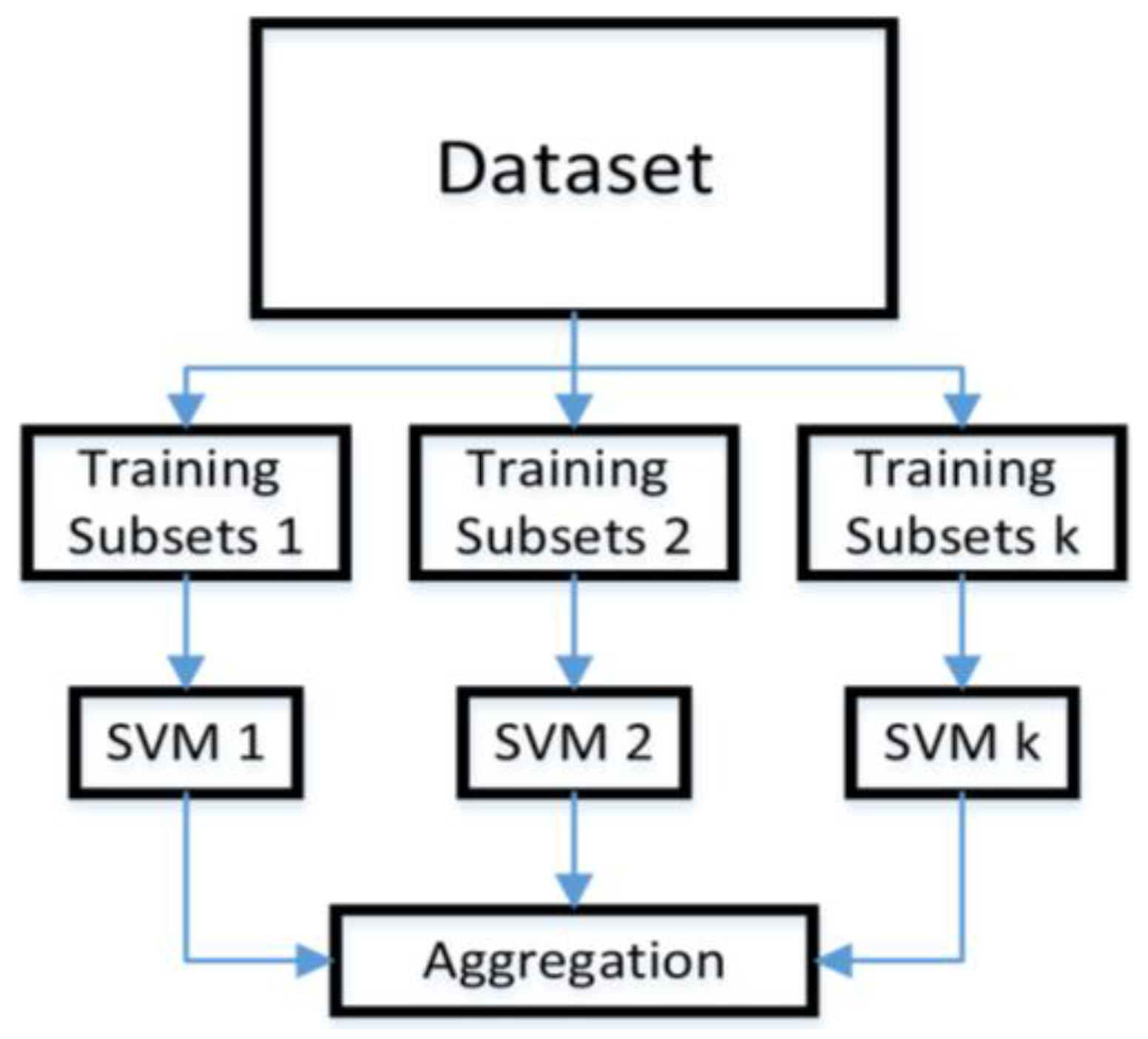
3. Machine Learning Algorithms-Revisited
4. Data Collection and Engineering
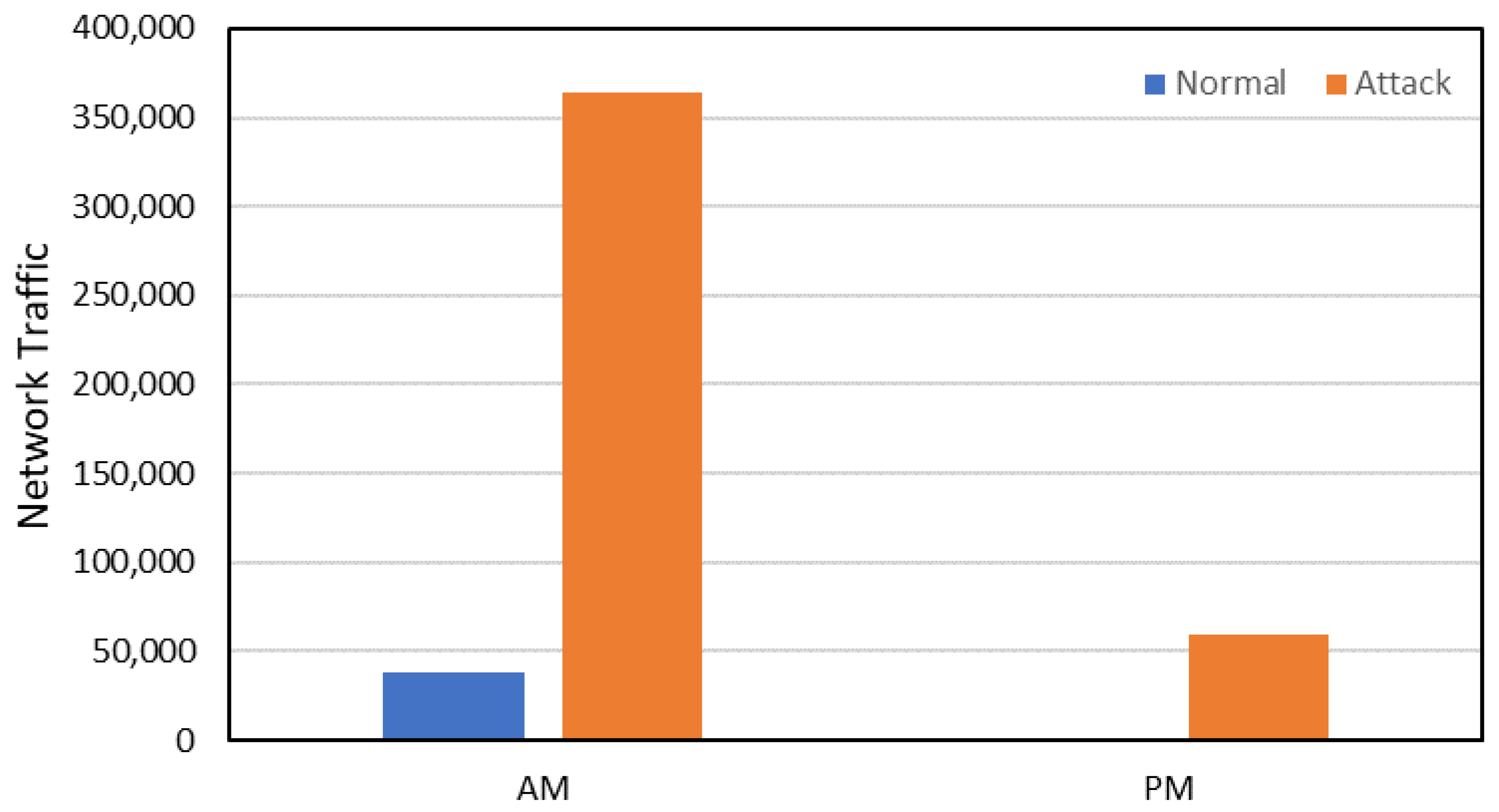
4.1. Dataset of IoT System
4.2. Features Engineering
5. System Development and Specifications
5.1. Data Pre-Processing
5.2. Detection and Classification Procedures
5.3. Implementation and Validation Environment
6. Results and Discussion
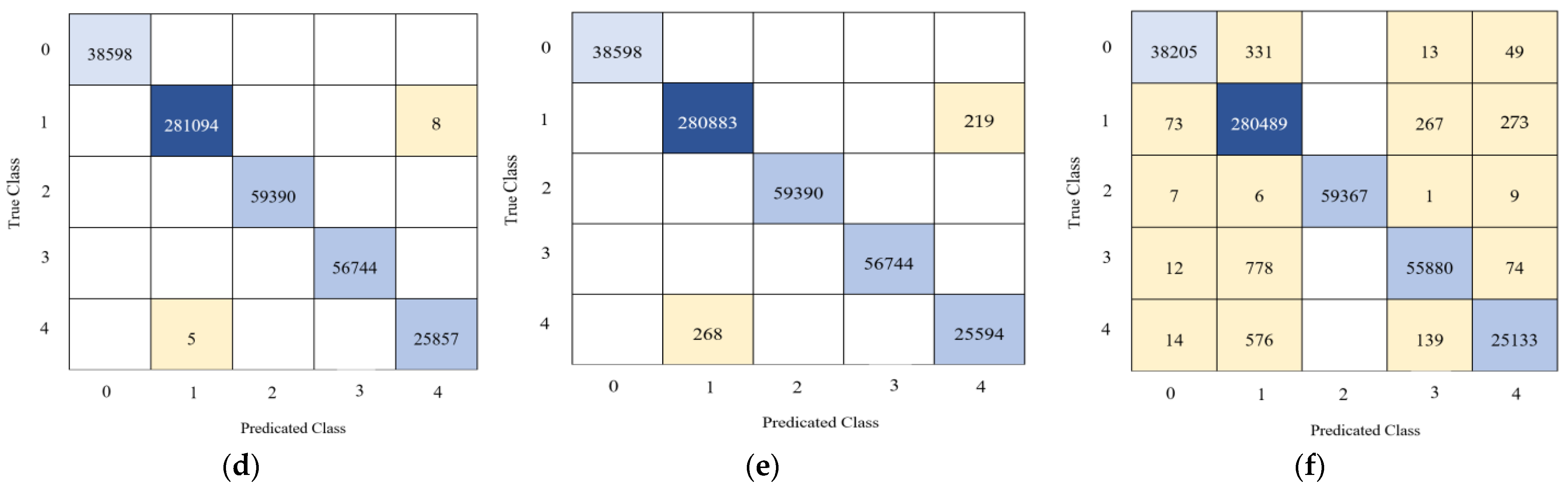
6.1. Accuracy Evaluation
6.2. Our Results
6.3. Comparing Our Findings with Existing Results
6.4. Limitations of the Study
7. Conclusions and Future Work
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Conflicts of Interest
References
- Kiourtis, A.; Mavrogiorgou, A.; Kyriazis, D.; Maglogiannis, I.; Themistocleous, M. Exploring the complete data path for data interoperability in cyber-physical systems. Int. J. High-Perform. Comput. Netw. 2018, 12, 339–349. [Google Scholar] [CrossRef]
- Smadi, A.A.; Ajao, B.T.; Johnson, B.K.; Lei, H.; Chakhchoukh, Y.; Abu Al-Haija, Q. A Comprehensive survey on cyber-physical smart grid testbed architectures: Requirements and challenges. Electronics 2021, 10, 1043. [Google Scholar] [CrossRef]
- Al-Haija, A.Q.; Krichen, M.; Elhaija, A. Machine-learning-based darknet traffic detection system for IoT applications. Electronics 2022, 11, 556. [Google Scholar] [CrossRef]
- Hassija, V.; Chamola, V.; Saxena, V.; Jain, D.; Goyal, P.; Sikdar, B. A survey on IoT security: Application areas, security threats, and solution architectures. IEEE Access 2019, 7, 82721–82743. [Google Scholar] [CrossRef]
- Gharaibeh, A. Smart cities: A survey on data management, security, and enabling technologies. IEEE Commun. Surv. Tutor. 2017, 19, 2456–2501. [Google Scholar] [CrossRef]
- Ray, S.; Jin, Y.; Raychowdhury, A. The changing computing paradigm with the internet of things: A Tutorial Introduction. IEEE Des. Test Comput. 2016, 33, 76–96. [Google Scholar] [CrossRef]
- Abu Al-Haija, Q.; Smadi, A.A.; Allehyani, M.F. Meticulously intelligent identification system for smart grid network stability to optimize risk management. Energies 2021, 14, 6935. [Google Scholar] [CrossRef]
- Quy, V.K.; Hau, N.V.; Anh, D.V.; Quy, N.M.; Ban, N.T.; Lanza, S.; Randazzo, G.; Muzirafuti, A. IoT-enabled smart agriculture: Architecture, applications, and challenges. Appl. Sci. 2022, 12, 3396. [Google Scholar] [CrossRef]
- Jose, A.C.; Malekian, R. Improving smart home security: Integrating logical sensing into smart home. IEEE Sens. J. 2017, 17, 4269–4286. [Google Scholar] [CrossRef]
- Al-Haija, Q.A.; Al-Saraireh, J. Asymmetric identification model for human-robot contacts via supervised learning. Symmetry 2022, 14, 591. [Google Scholar] [CrossRef]
- Albulayhi, K.; Smadi, A.A.; Sheldon, F.T.; Abercrombie, R.K. IoT intrusion detection taxonomy, reference architecture, and analyses. Sensors 2021, 21, 6432. [Google Scholar] [CrossRef] [PubMed]
- Mahmoud, R.; Yousuf, T.; Aloul, F.; Zualkernan, I. Internet of things (IoT) security: Current status, challenges, and prospective measures. In Proceedings of the 2015 10th International Conference for Internet Technology and Secured Transactions (ICITST), London, UK, 14–16 December 2015; pp. 336–341. [Google Scholar]
- Albulayhi, K.; Sheldon, F.T. An adaptive deep-ensemble anomaly-based intrusion detection system for the internet of things. In 2021 IEEE World AI IoT Congress (AIIoT); AIIoT: Seattle, WA, USA, 2021; pp. 0187–0196. [Google Scholar]
- Abu Al-Haija, Q. Top-down machine learning-based architecture for cyberattacks identification and classification in IoT communication networks. Front. Big Data 2022, 4, 782902. [Google Scholar] [CrossRef] [PubMed]
- Ahmad, Z.; Khan, A.S.; Wai Shiang, C.; Abdullah, J.; Ahmad, F. Network intrusion detection system: A systematic study of machine learning and deep learning approaches. Trans. Emerg. Telecommun. Technol. 2021, 32, e4150. [Google Scholar] [CrossRef]
- Abu Al-Haija, Q.; Ishtaiwi, A. Machine learning based model to identify firewall decisions to improve cyber-defense. Int. J. Adv. Sci. Eng. Inf. 2021, 11, 1688–1695. [Google Scholar] [CrossRef]
- Abdulhammed, R.; Hassan, M.; Ali, A.; Miad, F.; Abdelshakour, A. Features dimensionality reduction approaches for machine learning-based network intrusion detection. Electronics 2019, 8, 322. [Google Scholar] [CrossRef]
- Sarwar, A.; Hasan, S.; Khan, W.U. Design of an advance intrusion detection system for IoT networks. In Proceedings of the 2022 2nd International Conference on Artificial Intelligence (ICAI), Islamabad, Pakistan, 30–31 March 2022. [Google Scholar]
- Song, Y.; Hyun, S.; Cheong, Y.-G. Analysis of autoencoders for network intrusion detection. Sensors 2021, 21, 4294. [Google Scholar] [CrossRef]
- Alkahtani, H.; Aldhyani, T.H.H. Intrusion detection system to advance internet of things infrastructure-based deep learning algorithms. Complexity 2021, 2021, 5579851. [Google Scholar] [CrossRef]
- Yang, L.; Shami, A. A lightweight concept drift detection and adaptation framework for IoT data streams. IEEE Internet Things Mag. 2021, 4, 96–101. [Google Scholar] [CrossRef]
- Al-Haija, Q.A.; Zein-Sabatto, S. An efficient deep-learning-based detection and classification system for cyber-attacks in IoT communication networks. Electronics 2020, 9, 2152. [Google Scholar] [CrossRef]
- Albulayhi, K.; Abu Al-Haija, Q.; Alsuhibany, S.A.; Jillepalli, A.A. IoT intrusion detection using machine learning with a novel high performing feature selection method. Appl. Sci. 2022, 12, 5015. [Google Scholar] [CrossRef]
- Shahraki, A.; Abbasi, M.; Haugen, Ø. Boosting algorithms for network intrusion detection: A comparative evaluation of real AdaBoost, Gentle AdaBoost and Modest AdaBoost. Eng. Appl. Artif. Intell. 2021, 94, 10370–10380. [Google Scholar] [CrossRef]
- Moustafa, N. A new distributed architecture for evaluating AI-based security systems at the edge: Network TON_IoT datasets. Sustain. Cities Soc. 2021, 72, 102994. [Google Scholar] [CrossRef]
- Priya, V.; Thaseen, I.S.; Gadekallu, T.R.; Aboudaif, M.K.; Nasr, E.A. Robust attack detection approach for IIoT using ensemble classifier. Comput. Mater. Contin. 2021, 66, 2457–2470. [Google Scholar]
- Abu Al-Haija, Q.; Al-Dala’ien, M. ELBA-IoT: An ensemble learning model for botnet attack detection in iot networks. J. Sens. Actuator Netw. 2022, 11, 18. [Google Scholar] [CrossRef]
- AlShahrani, B.M.M. Classification of cyber-attack using Adaboost regression classifier and securing the network. Turk. J. Comput. Math. Educ. 2021, 12, 1215–1223. [Google Scholar]
- Yang, X.; David, L.; Xia, X.; Sun, J. TLEL: A two-layer ensemble learning approach for just-in-time defect prediction. Inf. Softw. Technol. 2017, 87, 206–220. [Google Scholar] [CrossRef]
- Al-Haija, Q.A.; Al-Badawi, A. Attack-Aware IoT network traffic routing leveraging ensemble learning. Sensors 2022, 22, 241. [Google Scholar] [CrossRef]
- Ashraf, J.; Keshk, M.; Moustafa, N.; Abdel-Basset, M.; Khurshid, H.; Bakhshi, A.D.; Mostafa, R.R. IoTBoT-IDS: A novel statistical learning-enabled botnet detection framework for protecting networks of smart cities. Sustain. Cities Soc. 2021, 72, 103041. [Google Scholar] [CrossRef]
- Abu Al-Haija, Q.; Al Badawi, A.; Bojja, G.R. Boost-defence for resilient iot networks: A head-to-toe approach. Expert Syst. 2022, 39, e12934. [Google Scholar] [CrossRef]
- Uddin, S.; Khan, A.; Hossain, M.E.; Moni, M.A. Comparing different supervised machine learning algorithms for disease prediction. BMC Med. Inform. Decis. Mak. 2019, 19, 281. [Google Scholar] [CrossRef]
- Derhab, A.; Aldweesh, A.; Emam, A.Z.; Khan, F.A. Intrusion detection system for internet of things based on temporal convolution neural network and efficient feature engineering. Wirel. Commun. Mob. Comput. 2020, 2020, 16. [Google Scholar] [CrossRef]
- Ullah, I.; Mahmoud, Q.H. A scheme for generating a dataset for anomalous activity detection in IoT networks. In Proceedings of the Canadian Conference on Artificial Intelligence (CCAI), Ottawa, ON, Canada, 13–15 May 2020; pp. 508–520. [Google Scholar]
- Shao, E. Encoding IP Address as a Feature for Network Intrusion Detection. Ph.D. Thesis, Purdue University Graduate School, West Lafayette, IN, USA, 2019. [Google Scholar]
- Al-Haija, Q.A.; Alsulami, A.A. High-performance classification model to identify ransomware payments for heterogeneous bitcoin networks. Electronics 2021, 10, 2113. [Google Scholar] [CrossRef]
- Ahmad, T.; Aziz, M.N. Data preprocessing and feature selection data preprocessing and feature selection. ICIC Express Lett. 2019, 13, 93–101. [Google Scholar]
- MathWorks Introduces Release 2022A of Matlab and Simulin MATLAB and Simulink. Available online: https://www.mathworks.com/company/newsroom/mathworks-introduces-release-2022a-of-matlab-and-simulink.html (accessed on 26 November 2022).
- Classification Learner, MATLAB. Available online: https://www.mathworks.com/help/stats/classificationlearner-app.html (accessed on 26 November 2022).
- User Guides for Nvidia Graphics Cards NVIDIA. Available online: https://nvidia.custhelp.com/app/answers/detail/a_id/4756/~/user-guides-for-nvidia-graphics-cards (accessed on 25 November 2022).
- Alsulami, A.A.; Abu Al-Haija, Q.; Alqahtani, A.; Alsini, R. Symmetrical Simulation Scheme for Anomaly Detection in Autonomous Vehicles Based on LSTM Model. Symmetry 2022, 14, 1450. [Google Scholar] [CrossRef]
- Nancy, A.A.; Ravindran, D.; Vincent, P.D.R.; Srinivasan, K.; Reina, D.G. Iot-cloud-based smart healthcare monitoring system for heart disease prediction via deep learning. Electronics 2022, 11, 2292. [Google Scholar] [CrossRef]
- Abdi, A.; Nabi, R.M.; Sardasht, M.; Mahmood, R. Multiclass classifiers for stock price prediction: A comparison study. J. Harbin Inst. Technol. 2022, 54, 2022. [Google Scholar]
- Reddy, D.K.K.; Behera, H.S.; Nayak, J.; Naik, B.; Ghosh, U.; Sharma, P.K. Exact greedy algorithm based split finding approach for intrusion detection in fog-enabled IoT environment. J. Inf. Secur. Appl. 2021, 60, 102866. [Google Scholar] [CrossRef]
- Fang, H.; Tang, P.; Si, H. Feature selections using minimal redundancy maximal relevance algorithm for human activity recognition in smart home environments. J. Healthc. Eng. 2020, 2020, 8876782. [Google Scholar] [CrossRef]
- Zhao, Z.; Anand, R.; Wang, M. Maximum relevance and minimum redundancy feature selection methods for a marketing machine learning platform. In Proceedings of the 2019 IEEE International Conference on Data Science and Advanced Analytics (DSAA), Washington, DC, USA, 5–8 October 2019; pp. 442–452. [Google Scholar]
- Sun, H.; Grishman, R. Lexicalized dependency paths based supervised learning for relation extraction. Comput. Syst. Sci. Eng. 2022, 43, 861–870. [Google Scholar] [CrossRef]









| Ref. | Learning Models | Datasets | Number of Features/Number of Records | Cyber-Attacks |
|---|---|---|---|---|
| [17] | Auto-Encoder, random forest (RF), naïve Bayes (NB), Linear/Quadratic Discriminator | CICIDS2017 | 83 Features/ 2,830,540 records | Distributed DoS (DDoS), Heartbleed, structured query language (SQL) Injection, Botnet. |
| [18] | Particle Swarm (PSO), XG Boost, RF | IoTID20 | 83 Features/ 450,00 records | Mirai, DoS, Scan, MITM |
| [19] | Auto-Encoders (AEs) | NSL-KDD/IoTID20/ N-BaIoT | 43 Features/140,000 83 Features/450,000 114 Features/612,000 | Norm, DoS, Probe, R2L, U2R /Mirai, DoS, Scan, MITM /Normal, Bashlite, Mirai |
| [20] | Convolutional neural network (CNN), long short-term memory (LSTM), CNN-LSTM | NSL-KDD/IoTID20/ | 43 Features/140,000 83 Features/450,000 | Norm, DoS, Probe, root to local (R2L), user to root (U2R), /Mirai, DoS, Scan, MITM |
| [21] | LightGBM, Optimized Adaptive and Sliding Windowing (OASW) | NSL-KDD/IoTID20/ | 43 Features/140,000 83 Features/450,000 | Norm, DoS, Probe, R2L, U2R /Mirai, DoS, Scan, MITM |
| [22] | Shallow CNN | NSL-KDD | 43 Features/ 150,000 Records | Norm, DoS, Probe, R2L, U2R |
| [23] | Bagging, J48, KNN, Multilayer Perceptron (MLP), Ensemble. | NSL-KDD/ IoTID20 | 11–60 Features/ 150,00–450,00 | Norm, DoS, Probe, R2L, U2R /Mirai, DoS, Scan, MITM |
| [24] | Adaboost, DT | KDDCUP99, UNSW-NB15, NSL-KDD, CICIDS2017 | 43–100 Features/ 140,000–612,000 | DDoS, flooding, U2R, Jamming |
| [25] | Gradient Boosting Machines, RF, NB, Deep Neural Networks (DNN) | ToN_IoT | 7 Features/ 1,300,000 records | Normal, DoS, DDoS, Injection, MITM, Password, Scan, Cross-site scripting (XSS), Backdoor, Ransome. |
| [26] | SVM, NB, SNN, RF | N_BaIoT, Bot_IoT | 114 Features/ 612,000 records | Normal, Bashlite, Mirai |
| [27] | Adaboost, RusBoost, Bagging, Ensemble | WUSTL_IIOT-2018, N_BaIoT, and Bot_IoT | 100–114 Features/ 100,000–612,000 | Normal, Bashlite, Mirai, Port/Address Scanner. |
| [28] | AdaBoost | CICIDS 2019. | 88 Features/ 4,201,795 Records | DDoS, Heartbleed, SQL Injection, Botnet. |
| [29] | SNN, SVM, NB, RF, Self-organizing map | NSL-KDD, KDDCup99, ADFA-LD12, UNSWNB15 | 43–100 Features/ 140,000–612,000 | DDoS, flooding, U2R, Jamming |
| [30] | Ensembles:(Boosted DT, Subspace kNN, RUSBoosted DT), SNN, Bilayered NN, Logistic Regression Kernel | Distilled-Kitsune-2018/NSL-KDD dataset | 43 Features/ 145,00–150,000 | Mirai, operating system (OS) Scan, Fuzzing, Video Injection, Address Resolution Protocol (ARP), Wiretap, simple service discovery protocol (SSDP), Synchronous DoS, secure sockets layer(SSL)/DoS, Probe, R2L, U2R |
| [31] | Beta Mixture Model | BoT-IoT 21 | 12 Features/ 3,000,000 records | DoS, DDoS, Keylogging, OS and Service Scan, and Data exfiltration attacks |
| [32] | AdaBoost DT | TON_IoT_2020 datasets | 7 Features/ 1,300,000 | DoS, DDoS, Injection Attacks, MITM, Password Attacks, Scanning, XSS Attacks, Backdoor attacks, and Ransomware attacks. |
| Labels | Number of Records | Category | Number of Records |
|---|---|---|---|
| Normal | 38,598 | Normal | 38,598 |
| Anomaly | 423,098 | Mirai | 281,102 |
| DoS | 59,390 | ||
| Scan | 56,744 | ||
| MITM | 25,862 |
| Features | Description | Type |
|---|---|---|
| Src_Port | Source port number | INT |
| Dst_Port | Destination port number | INT |
| Protocol | Protocol type assigned number | INT |
| Flow_Duration | Flow duration in seconds | INT |
| Tot_Fwd_Pkts | Total number of forwarding packets | INT |
| Tot_Bwd_Pkts | Total number of backward packets | INT |
| TotLen_Fwd_Pkts | The total length of forwarding packets | INT |
| TotLen_Bwd_Pkts | The total length of backward packets | INT |
| Fwd_Pkt_Len_Max | Max length of forwarding packets | INT |
| Fwd_Pkt_Len_Min | Min length of forwarding packets | INT |
| Fwd_Pkt_Len_Mean | Mean length of forwarding packets | DOB |
| Fwd_Pkt_Len_Std | Stander deviation length of forwarding packets | DOB |
| Bwd_Pkt_Len_Max | Max length of backward packets | INT |
| Bwd_Pkt_Len_Min | Min length of backward packets | INT |
| Bwd_Pkt_Len_Mean | Mean length of backward packets | DOB |
| Bwd_Pkt_Len_Std | Stander deviation length of backward packets | DOB |
| Flow_Byts/s | Flow bytes in seconds | INT |
| Flow_Pkts/s | Flow packets in seconds | INT |
| Flow_IAT_Mean | Mean of the flow inter-arrival time (IAT) | DOB |
| Flow_IAT_Std | Stander deviation of the flow IAT | DOB |
| Flow_IAT_Max | Max of the flow IAT | INT |
| Flow_IAT_Min | Min of the flow IAT | INT |
| Fwd_IAT_Tot | Total of the forwarding IAT | INT |
| Fwd_IAT_Mean | Mean of the forwarding IAT | DOB |
| Fwd_IAT_Std | Stander deviation of the forwarding IAT | DOB |
| Fwd_IAT_Max | Max of the forwarding IAT | INT |
| Fwd_IAT_Min | Min of the forwarding IAT | INT |
| Bwd_IAT_Tot | Total of the backward IAT | INT |
| Bwd_IAT_Mean | Mean of the backward IAT | DOB |
| Bwd_IAT_Std | Stander deviation of the backward IAT | DOB |
| Bwd_IAT_Max | Max of the backward IAT | INT |
| Bwd_IAT_Min | Min of the backward IAT | INT |
| Fwd_Header_Len | Length of the forwarding header | INT |
| Bwd_Header_Len | Length of the backward header | INT |
| Fwd_Pkts/s | Forward packet in seconds | INT |
| Bwd_Pkts/s | Backward packet in seconds | INT |
| Pkt_Len_Min | Min of packet length | INT |
| Pkt_Len_Max | Max of packet length | INT |
| Pkt_Len_Mean | Mean of packet length | DOB |
| Pkt_Len_Std | Stander deviation of packet length | DOB |
| Pkt_Len_Var | The variance in packet length | DOB |
| ACK_Flag_Cnt | Acknowledgment flag Cnt | INT |
| Down/Up_Ratio | Down or up ratio | INT |
| Pkt_Size_Avg | Average packet size | DOB |
| Fwd_Seg_Size_Avg | Average forward segment size | DOB |
| Bwd_Seg_Size_Avg | Average backward segment size | DOB |
| Subflow_Fwd_Pkts | Subflow forward packet | INT |
| Subflow_Fwd_Byts | Subflow forward bytes | INT |
| Subflow_Bwd_Pkts | Subflow backward packet | INT |
| Subflow_Bwd_Byts | Subflow backward bytes | INT |
| Init_Bwd_Win_Byts | Initial backward window bytes | INT |
| Fwd_Act_Data_Pkts | Forward acknowledgment data packets | INT |
| Active_Mean | Mean active time | DOB |
| Active_Std | Stander deviation active time | DOB |
| Active_Max | Max active time | INT |
| Active_Min | Min active time | INT |
| Idle_Mean | Mean idle time | DOB |
| Idle_Std | Stander deviation idle time | DOB |
| Idle_Max | Max idle time | INT |
| Idle_Min | Min idle time | INT |
| Src_IP_oct1 | Source IP octet number part 1 | INT |
| Src_IP_oct2 | Source IP octet number part 2 | INT |
| Src_IP_oct3 | Source IP octet number part 3 | INT |
| Src_IP_oct4 | Source IP octet number part 4 | INT |
| Dst_IP_oct1 | Destination IP octet number part 1 | INT |
| Dst_IP_oct2 | Destination IP octet number part 2 | INT |
| Dst_IP_oct3 | Destination IP octet number part 3 | INT |
| Dst_IP_oct4 | Destination IP octet number part 4 | INT |
| Timestamp_DayOfWeek | Timestamp day of the week | INT |
| Timestamp_Hour | Timestamp in hour | INT |
| Timestamp_AmPm_n | Timestamp AM or PM | INT |
| Hardware/Software | Description |
|---|---|
| MATLAB | Version 2022a |
| CPU | Intel® Core™ i7-9750H CPU @ 2.60 GHz |
| Memory | 16.0 GB |
| GPU | NVIDIA GeForce RTX 2070 GDDR6 @ 8 GB |
| ML Model | Detection/Classification | Precision | Recall | F1-Score | Specificity |
|---|---|---|---|---|---|
| SSNs | Detection | 100% | 100% | 100% | 100% |
| SSNs | Classification | 100% | 99.99% | 99.99% | 100% |
| DT | Detection | 100% | 100% | 100% | 100% |
| DT | Classification | 99.99% | 99.99% | 99.99% | 100% |
| BT | Detection | 100% | 100% | 100% | 100% |
| BT | Classification | 100% | 99.99% | 99.99% | 100% |
| SVM | Detection | 100% | 100% | 100% | 100% |
| SVM | Classification | 99.78% | 99.81% | 99.79% | 99.96% |
| KNN | Detection | 100% | 100% | 100% | 100% |
| KNN | Classification | 98.88% | 99.36% | 99.12% | 99.84% |
| Research | Detection/Classification | ML Model | Accuracy |
|---|---|---|---|
| Sarwar et al. [18] | Detection | Random Forest | 98% |
| Sarwar et al. [18] | Classification | Random Forest | 83% |
| Song. et al. [19] | Classification | Auto-Encoders | 94.50% |
| Alkahtani et al. [20] | Classification | Convolutional Neural Networks + Long Short-Term Memory | 98.40% |
| Yang et al. [21] | Detection | LightGBM + Optimized Adaptive Sliding Windowing | 99.9% |
| Al-Haija et al. [22] | Classification | Convolutional Neural Networks | 98.2% |
| Reddy et al. [45] | Classification | XGBoost | 99.7% |
| Proposed Method | Classification | Shallow Neural Networks | 100% |
| Proposed Method | Detection | Shallow Neural Networks | 100% |
| Proposed Method | Classification | Decision Trees | 99.9% |
| Proposed Method | Detection | Decision Trees | 100% |
| Proposed Method | Classification | Bagged Trees | 99.9% |
| Proposed Method | Detection | Bagged Trees | 100% |
| Proposed Method | Classification | Support Vector Machines | 99.80% |
| Proposed Method | Detection | Support Vector Machines | 100% |
| Proposed Method | Classification | K-Nearest Neighbor (KNN) | 99.40% |
| Proposed Method | Detection | K-Nearest Neighbor (KNN) | 100% |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Alsulami, A.A.; Abu Al-Haija, Q.; Tayeb, A.; Alqahtani, A. An Intrusion Detection and Classification System for IoT Traffic with Improved Data Engineering. Appl. Sci. 2022, 12, 12336. https://doi.org/10.3390/app122312336
Alsulami AA, Abu Al-Haija Q, Tayeb A, Alqahtani A. An Intrusion Detection and Classification System for IoT Traffic with Improved Data Engineering. Applied Sciences. 2022; 12(23):12336. https://doi.org/10.3390/app122312336
Chicago/Turabian StyleAlsulami, Abdulaziz A., Qasem Abu Al-Haija, Ahmad Tayeb, and Ali Alqahtani. 2022. "An Intrusion Detection and Classification System for IoT Traffic with Improved Data Engineering" Applied Sciences 12, no. 23: 12336. https://doi.org/10.3390/app122312336
APA StyleAlsulami, A. A., Abu Al-Haija, Q., Tayeb, A., & Alqahtani, A. (2022). An Intrusion Detection and Classification System for IoT Traffic with Improved Data Engineering. Applied Sciences, 12(23), 12336. https://doi.org/10.3390/app122312336









