Differential Analysis of a Cryptographic Hashing Algorithm HBC-256
Abstract
1. Introduction
2. Related Works
3. Materials and Methods of Research
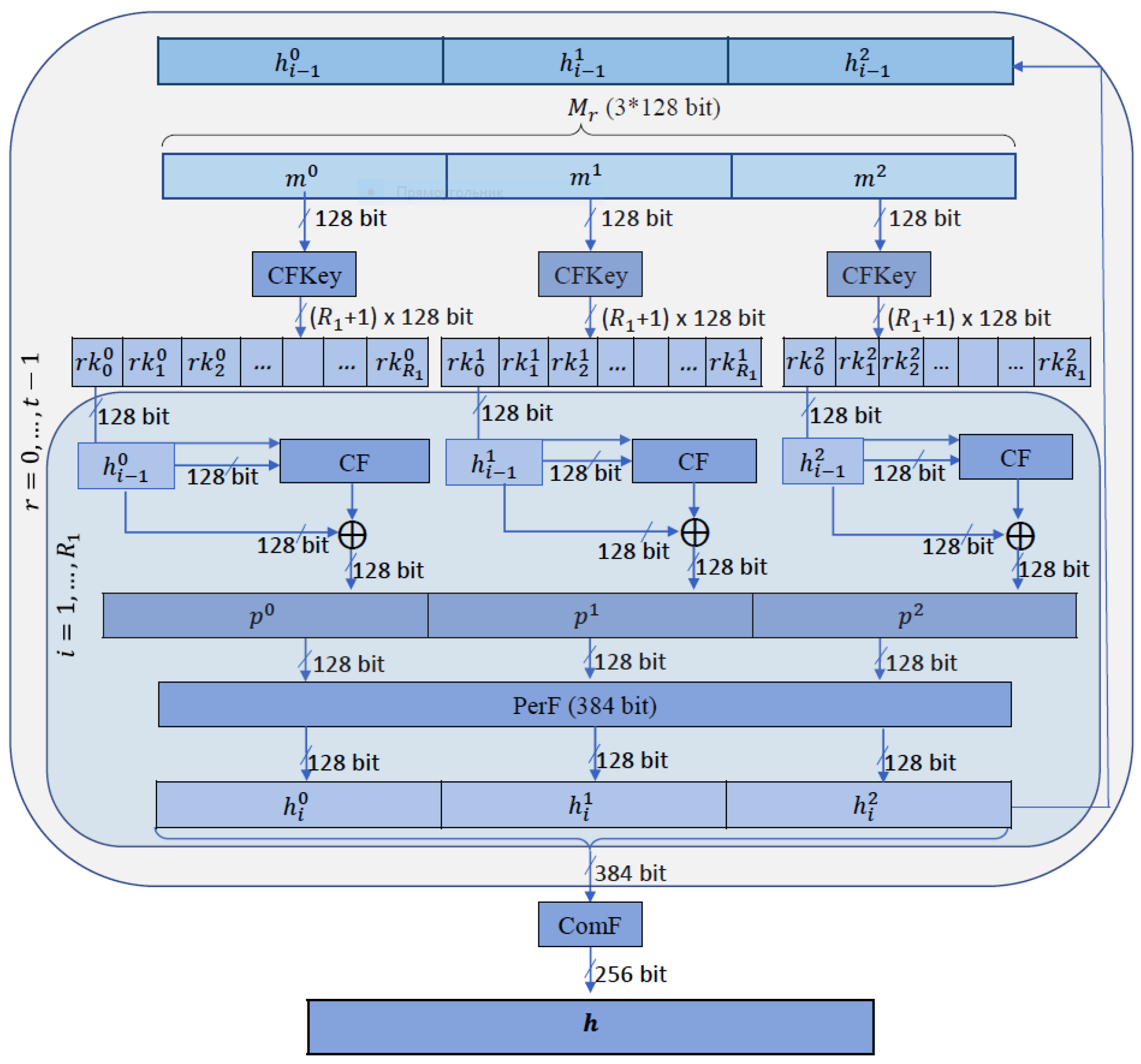
3.1. HBC-256 Hash Function
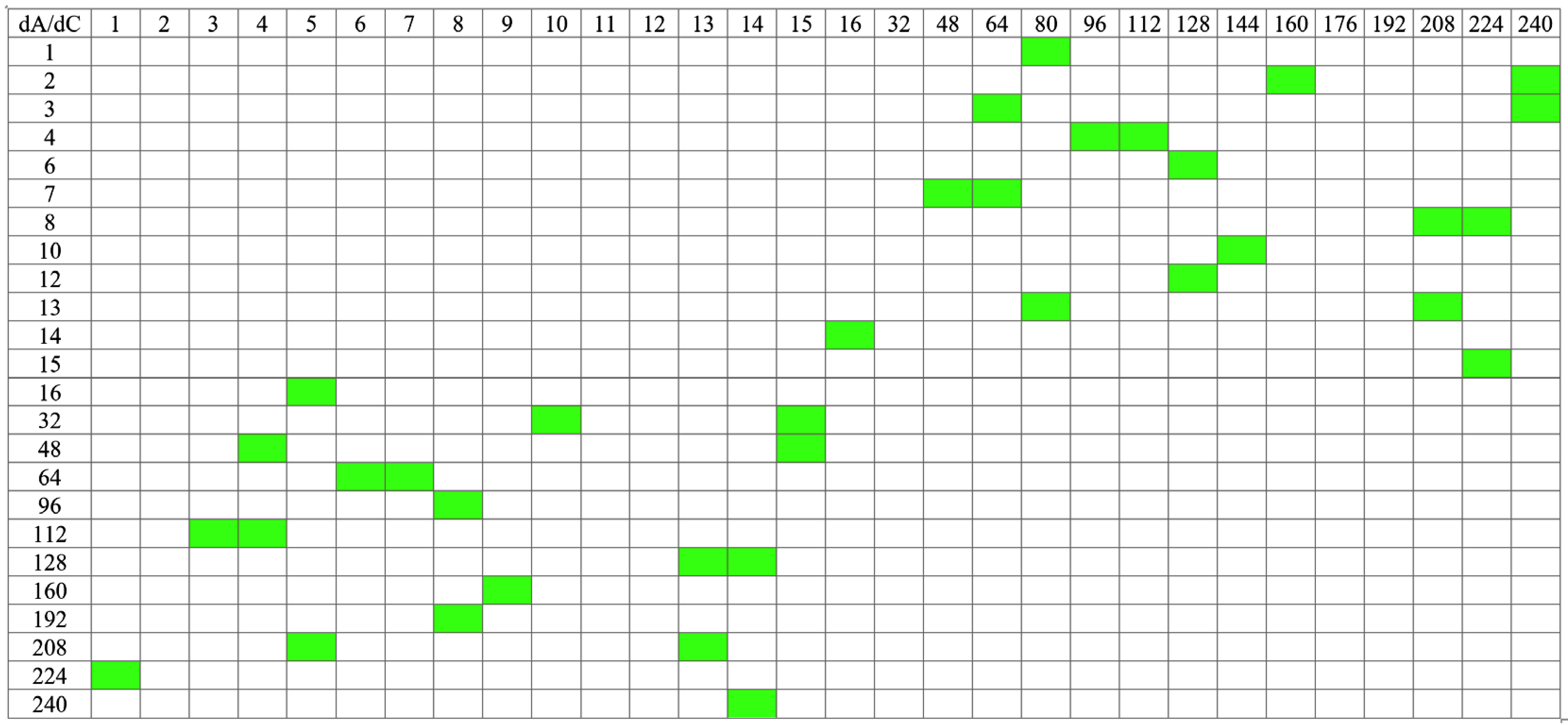
3.2. Method of Differential Cryptanalysis
- Analysis of non-linear elements and determination of the most probable differences for them;
- Construction of a multi-round characteristic (type input difference–output difference) from simple to complex, that is, from one round to n rounds. Determining the probability of the appearance of the constructed characteristic. Search for correct pairs of texts, i.e., such texts for which the sum of the input values is the same as the value of the input difference, and the sum of the output values is the same as the output difference.
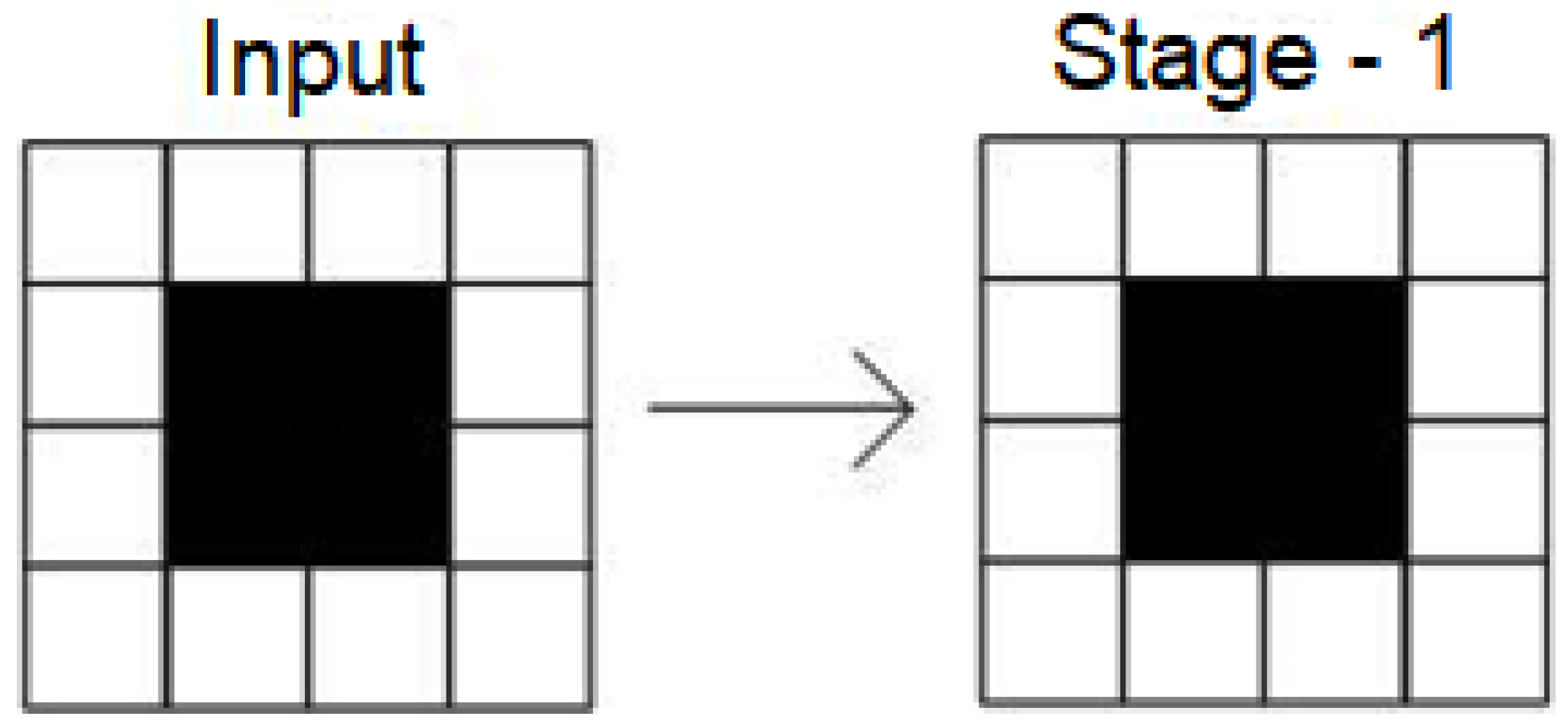
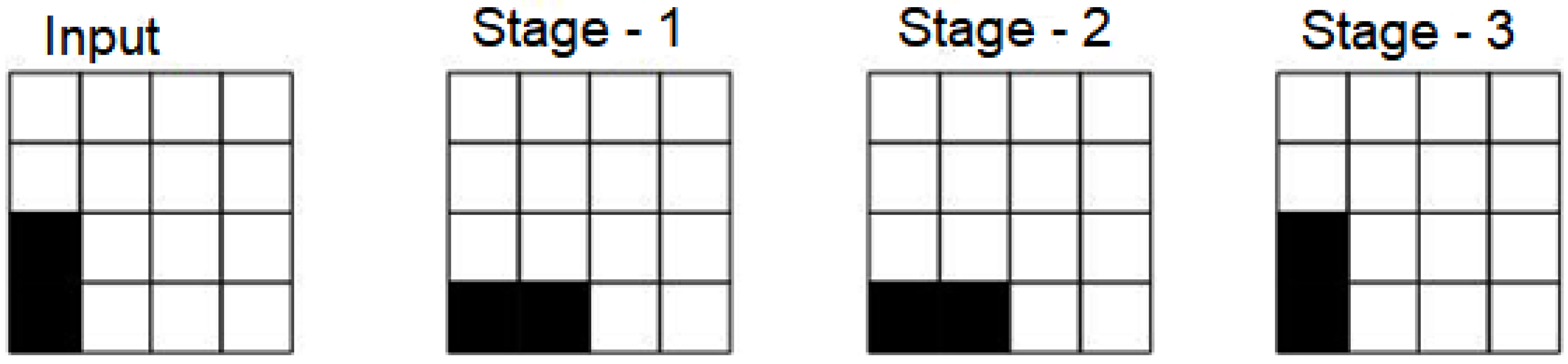
4. Results and Discussion
5. Conclusions
Author Contributions
Funding
Institutional Review Board Statement
Informed Consent Statement
Data Availability Statement
Acknowledgments
Conflicts of Interest
References
- Katz, J.; Lindell, Y. Introduction to Modern Cryptography, 2nd ed.; Chapman & Hall/CRC: New York, NY, USA, 2014; pp. 231–235. [Google Scholar]
- Bogdanov, A.; Knezevic, M.; Leander, G.; Toz, D.; Varici, K.; Verbauwhede, I. SPONGENT: The Design Space of Lightweight Cryptographic Hashing. IEEE Trans. Comput. 2013, 62, 2041–2053. [Google Scholar] [CrossRef]
- Harshvardhan, T. Merkle-Damgård Construction Method and Alternatives: A Review. J. Inf. Organ. Sci. 2017, 41, 283–304. [Google Scholar] [CrossRef]
- Boneh, D.; Shoup, V. A Graduate Course in Applied Cryptography; Version 0.5; Stanford University: Stanford, CA, USA, 2020; pp. 248–258. [Google Scholar]
- Yano, M.; Dai, C.; Masuda, K.; Kishimoto, Y. Correction to: Blockchain and Crypto Currency; Springer Open: Berlin/Heidelberg, Germany, 2020; pp. 1–20. [Google Scholar] [CrossRef]
- Morris, J.D. Sha-3 standard: Permutation-based-hash-and-extendable-output-functions. In Federal Information Processing Standards—(FIPS-202); U.S. Department of Commerce: Washington, DC, USA, 2015. [Google Scholar] [CrossRef]
- Mestiri, H.; Barraj, I.; Machhout, M. A High-Speed KECCAK Architecture Resistant to Fault Attacks. In Proceedings of the 32nd International Conference on Microelectronics (ICM), Aqaba, Jordan, 14–17 December 2020; pp. 1–4. [Google Scholar] [CrossRef]
- Mestiri, H.; Barraj, I.; Machhout, M. Analysis and Detection of Errors in KECCAK Hardware Implementation. In Proceedings of the IEEE International Conference on Design & Test of Integrated Micro & Nano-Systems (DTS), Sfax, Tunisia, 7–10 June 2021; pp. 1–6. [Google Scholar] [CrossRef]
- Tran, X.D.; Łukowiak, M.; Radziszowski, S.P. Effectiveness of variable bit-length power analysis attacks on SHA-3 based MAC. In Proceedings of the 2016 IEEE Military Communications Conference, Baltimore, MD, USA, 1–3 November 2016; pp. 794–799. [Google Scholar] [CrossRef]
- Luo, P.; Fei, Y.; Zhang, L.; Ding, A.A. Differential Fault Analysis of SHA3-224 and SHA3-256. In Proceedings of the Workshop on Fault Diagnosis and Tolerance in Cryptography (FDTC), Santa Barbara, CA, USA, 16 August 2016; pp. 4–15. [Google Scholar] [CrossRef]
- Luo, P.; Athanasiou, K.; Fei, Y.; Wahl, T. Algebraic fault analysis of SHA-3. In Proceedings of the Design, Automation & Test in Europe Conference & Exhibition (DATE), Lausanne, Switzerland, 27–31 March 2017; pp. 151–156. [Google Scholar] [CrossRef]
- Song, L.; Liao, G.; Guo, J. Non-full Sbox linearization: Applications to collision attacks on round-reduced Keccak. In Proceedings of the 37th Annual International Cryptology Conference, Santa Barbara, CA, USA, 20–24 August 2017; Volume 10402, pp. 428–451. [Google Scholar] [CrossRef]
- Song, L.; Guo, J.; Shi, D.; Ling, S. New MILP Modeling: Improved Conditional Cube Attacks on Keccak-Based Constructions. Advances in Cryptology—ASIACRYPT 2018. In Proceedings of the 24th International Conference on the Theory and Application of Cryptology and Information Security, Brisbane, Australia, 2–6 December 2018; Volume 11273, pp. 65–95. [Google Scholar] [CrossRef]
- Liu, F.; Isobe, T.; Meier, W.; Yang, Z. Algebraic Attacks on Round-Reduced Keccak. In Proceedings of the 26th Australasian Conference, ACISP 2021, Virtual, 1–3 December 2021; Volume 13083, pp. 91–110. [Google Scholar] [CrossRef]
- Li, C.; Zhang, Y.; Xie, E.Y. When an attacker meets a cipher-image in 2019: A year in review. J. Inf. Secur. Appl. 2019, 48, 102361. [Google Scholar] [CrossRef]
- Sakan, K.; Nyssanbayeva, S.; Kapalova, N.; Algazy, K.; Khompysh, A.; Dyusenbayev, D. Development and analysis of the new hashing algorithm based on block cipher. Eastern-Eur. J. Enterp. Technol. 2022, 2, 60–73. [Google Scholar] [CrossRef]
- Cherckesova, L.V.; Safaryan, O.A.; Lyashenko, N.G.; Korochentsev, D.A. Developing a NewCollision-Resistant HashingAlgorithm. Mathematics 2022, 10, 2769. [Google Scholar] [CrossRef]
- Al-Odat, Z.; Khan, S. Constructions and Attacks on Hash Functions. In Proceedings of the 2019 International Conference on Computational Science and Computational Intelligence (CSCI), Las Vegas, NV, USA, 5–7 December 2019; pp. 139–144. [Google Scholar] [CrossRef]
- Mouha, N.; Velichkov, V.; De Cannière, C.; Preneel, B. The Differential Analysis of S-Functions. In Selected Areas in Cryptography; Biryukov, A., Gong, G., Stinson, D.R., Eds.; SAC 2010. Lecture Notes in Computer Science; Springer: Berlin/Heidelberg, Germany, 2011; Volume 6544. [Google Scholar] [CrossRef]
- Biham, E.; Shamir, A. Differential cryptanalysis of the full 16-round DES. In Proceedings of the 12th Annual International Cryptology Conference, Santa Barbara, CA, USA, 16–20 August 1992; pp. 487–496. [Google Scholar] [CrossRef]
- Biham, E.; Shamir, A. Differential Cryptanalysis of the Data Encryption Standard; Springer: Berlin/Heidelberg, Germany, 1993; pp. 133–148. ISBN 978-1-4613-9314-6. [Google Scholar]
- Biham, E.; Dunkelman, O. Differential Cryptanalysis in Stream Ciphers; No. CS Technion Report CS-2007-10; Computer Science Department, Technion: Haifa, Israel, 2007; pp. 1–12. Available online: http://eprint.iacr.org/ (accessed on 1 July 2022).
- Algazy, K.T.; Babenko, L.K.; Biyashev, R.G.; Ishchukova, E.A.; Kapalova, N.A.; Nysynbaeva, S.E.; Smolarz, A. Differential Cryptanalysis of New Qamal Encryption Algorithm. Int. J. Electron. Telecommun. 2020, 66, 647–653. [Google Scholar] [CrossRef]
- Ishchukova, E.; Tolomanenko, E.; Babenko, L. Differential analysis of 3 round Kuznyechik. In Proceedings of the 10th International Conference on Security of Information and Networks, Jaipur, India, 13 October 2017; pp. 29–36. [Google Scholar] [CrossRef]
- Khompysh, A.; Kapalova, N.; Algazy, K.; Dyusenbayev, D.; Sakan, K. Design of substitution nodes (S-Boxes) of a block cipher intended for preliminary encryption of confidential information. Cogent Eng. 2022, 9, 2080623. [Google Scholar] [CrossRef]



| x | 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| (x) | 0 | F | B | 8 | C | 9 | 6 | 3 | D | 1 | 2 | 4 | A | 7 | 5 | E |
| (x) | 2 | E | F | 5 | C | 1 | 9 | A | B | 4 | 6 | 8 | 0 | 7 | 3 | D |
| (x) | 7 | C | E | 9 | 2 | 1 | 5 | F | B | 6 | D | 0 | 4 | 8 | A | 3 |
| (x) | 4 | A | 1 | 6 | 8 | F | 7 | C | 3 | 0 | E | D | 5 | 9 | B | 2 |
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 16 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 0 | 0 | 2 | 0 | 4 | 2 | 0 | 0 | 0 | 0 | 2 | 2 | 2 | 0 | 2 |
| 2 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 2 | 0 | 2 | 4 | 2 | 0 | 0 | 0 | 4 |
| 3 | 0 | 0 | 2 | 2 | 4 | 0 | 0 | 0 | 2 | 2 | 0 | 0 | 0 | 0 | 0 | 4 |
| 4 | 0 | 0 | 0 | 0 | 0 | 0 | 4 | 4 | 0 | 0 | 2 | 2 | 2 | 2 | 0 | 0 |
| 5 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 0 | 2 | 2 | 2 | 2 | 2 | 0 | 2 | 0 |
| 6 | 0 | 2 | 0 | 2 | 0 | 0 | 2 | 2 | 4 | 0 | 0 | 0 | 2 | 0 | 0 | 2 |
| 7 | 0 | 0 | 2 | 4 | 4 | 2 | 0 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 2 | 0 |
| 8 | 0 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 0 | 2 | 4 | 4 | 0 |
| 9 | 0 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 2 | 0 | 2 | 2 | 0 | 0 | 0 | 2 |
| A | 0 | 0 | 2 | 0 | 2 | 0 | 2 | 2 | 0 | 4 | 0 | 2 | 2 | 0 | 0 | 0 |
| B | 0 | 2 | 2 | 0 | 2 | 2 | 0 | 0 | 0 | 2 | 2 | 0 | 2 | 2 | 0 | 0 |
| C | 0 | 2 | 0 | 0 | 2 | 0 | 2 | 2 | 4 | 0 | 2 | 0 | 0 | 0 | 2 | 0 |
| D | 0 | 2 | 2 | 0 | 2 | 4 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 4 | 0 | 0 |
| E | 0 | 4 | 2 | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 2 | 2 | 2 |
| F | 0 | 0 | 2 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 2 | 2 | 2 | 0 | 4 | 0 |
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 16 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 0 | 0 | 2 | 0 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 2 | 2 | 4 | 2 |
| 2 | 0 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 0 | 2 | 4 | 2 | 4 | 0 | 0 |
| 3 | 0 | 2 | 2 | 2 | 2 | 0 | 2 | 2 | 2 | 0 | 0 | 0 | 0 | 2 | 0 | 0 |
| 4 | 0 | 0 | 0 | 2 | 0 | 4 | 2 | 0 | 0 | 0 | 0 | 2 | 0 | 0 | 2 | 4 |
| 5 | 0 | 0 | 2 | 2 | 2 | 2 | 0 | 0 | 0 | 0 | 0 | 4 | 4 | 0 | 0 | 0 |
| 6 | 0 | 0 | 0 | 2 | 4 | 0 | 2 | 0 | 2 | 2 | 0 | 2 | 0 | 0 | 0 | 2 |
| 7 | 0 | 2 | 0 | 0 | 0 | 0 | 2 | 4 | 4 | 2 | 0 | 0 | 0 | 0 | 2 | 0 |
| 8 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 4 | 4 | 0 | 2 | 2 | 0 | 0 |
| 9 | 0 | 2 | 0 | 2 | 2 | 2 | 2 | 2 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 0 |
| A | 0 | 2 | 0 | 0 | 4 | 0 | 2 | 0 | 0 | 2 | 0 | 0 | 2 | 2 | 0 | 2 |
| B | 0 | 2 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 0 | 4 | 2 | 0 | 0 | 4 | 0 |
| C | 0 | 0 | 4 | 0 | 0 | 2 | 0 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 0 | 2 |
| D | 0 | 2 | 2 | 0 | 0 | 2 | 2 | 0 | 2 | 0 | 2 | 0 | 2 | 0 | 2 | 0 |
| E | 0 | 2 | 4 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 0 | 0 | 2 | 2 |
| F | 0 | 2 | 0 | 0 | 2 | 2 | 0 | 2 | 2 | 0 | 0 | 0 | 0 | 4 | 0 | 2 |
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 16 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 0 | 0 | 2 | 0 | 0 | 0 | 2 | 0 | 2 | 2 | 2 | 2 | 4 | 0 | 0 |
| 2 | 0 | 0 | 0 | 0 | 0 | 2 | 4 | 2 | 0 | 2 | 0 | 2 | 0 | 0 | 4 | 0 |
| 3 | 0 | 0 | 4 | 0 | 2 | 0 | 0 | 2 | 0 | 0 | 0 | 4 | 0 | 2 | 2 | 0 |
| 4 | 0 | 0 | 0 | 2 | 0 | 2 | 2 | 2 | 0 | 0 | 0 | 2 | 0 | 2 | 2 | 2 |
| 5 | 0 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 0 | 0 | 2 | 0 | 2 | 0 | 4 | 0 |
| 6 | 0 | 2 | 2 | 2 | 0 | 2 | 0 | 0 | 4 | 2 | 0 | 0 | 2 | 0 | 0 | 0 |
| 7 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 0 | 4 | 2 | 0 | 2 | 2 | 0 | 0 | 2 |
| 8 | 0 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 0 | 4 | 2 | 0 | 4 | 0 | 0 | 2 |
| 9 | 0 | 2 | 0 | 0 | 2 | 4 | 2 | 2 | 0 | 0 | 2 | 0 | 0 | 0 | 2 | 0 |
| A | 0 | 2 | 2 | 0 | 0 | 2 | 0 | 2 | 2 | 0 | 2 | 0 | 2 | 0 | 0 | 2 |
| B | 0 | 4 | 2 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 0 | 4 | 0 | 2 | 0 | 0 |
| C | 0 | 0 | 0 | 2 | 4 | 0 | 0 | 2 | 2 | 2 | 2 | 0 | 0 | 0 | 0 | 2 |
| D | 0 | 0 | 2 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 2 | 0 | 2 |
| E | 0 | 4 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 0 | 2 | 2 | 4 |
| F | 0 | 0 | 2 | 2 | 4 | 0 | 4 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 0 |
| 0 | 1 | 2 | 3 | 4 | 5 | 6 | 7 | 8 | 9 | A | B | C | D | E | F | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0 | 16 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 |
| 1 | 0 | 0 | 0 | 4 | 0 | 0 | 0 | 4 | 0 | 2 | 0 | 2 | 2 | 0 | 2 | 0 |
| 2 | 0 | 0 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 4 | 2 | 2 |
| 3 | 0 | 0 | 4 | 0 | 2 | 0 | 0 | 2 | 2 | 0 | 0 | 2 | 0 | 0 | 4 | 0 |
| 4 | 0 | 0 | 0 | 0 | 0 | 4 | 4 | 0 | 0 | 2 | 2 | 0 | 2 | 0 | 0 | 2 |
| 5 | 0 | 2 | 2 | 0 | 0 | 2 | 2 | 0 | 0 | 0 | 2 | 2 | 2 | 2 | 0 | 0 |
| 6 | 0 | 0 | 2 | 2 | 2 | 0 | 2 | 0 | 2 | 4 | 0 | 2 | 0 | 0 | 0 | 0 |
| 7 | 0 | 2 | 0 | 0 | 0 | 0 | 0 | 2 | 4 | 0 | 0 | 2 | 0 | 2 | 4 | 0 |
| 8 | 0 | 0 | 0 | 0 | 0 | 0 | 2 | 2 | 0 | 0 | 2 | 2 | 2 | 2 | 2 | 2 |
| 9 | 0 | 2 | 0 | 0 | 2 | 2 | 0 | 2 | 2 | 2 | 2 | 0 | 2 | 0 | 0 | 0 |
| A | 0 | 0 | 4 | 2 | 0 | 2 | 2 | 2 | 0 | 0 | 2 | 0 | 0 | 2 | 0 | 0 |
| B | 0 | 2 | 0 | 0 | 4 | 2 | 0 | 0 | 0 | 4 | 2 | 0 | 0 | 0 | 2 | 0 |
| C | 0 | 4 | 0 | 2 | 2 | 0 | 0 | 0 | 0 | 2 | 2 | 2 | 0 | 0 | 0 | 2 |
| D | 0 | 0 | 2 | 2 | 0 | 0 | 0 | 0 | 2 | 0 | 2 | 0 | 2 | 4 | 0 | 2 |
| E | 0 | 0 | 2 | 0 | 4 | 0 | 2 | 0 | 2 | 0 | 0 | 0 | 2 | 0 | 0 | 4 |
| F | 0 | 4 | 0 | 2 | 0 | 2 | 2 | 2 | 2 | 0 | 0 | 0 | 0 | 0 | 0 | 2 |
| Hashing Function | Keys Generation | |
|---|---|---|
| Stage 1 | a → a + b | a → b |
| Stage 2 | 0 → 0 | a + b → a + b |
| Input difference → Difference after Stage1 (a) → Difference after StageKey2 → Difference after Stage3 (b) → Input Difference XOR Difference after Stage3 (a + b) | Input difference (a + b) → Difference after Stage1 → Difference after StageKey2 → Difference after Stage3 (a + b) |
|---|---|
| 27 (8|8) → 19 → 38 → 245(4|4) → 238 27 (8|8) → 19 → 38 → 53 (4|4) → 46 27 (8|8) → 23 → 46 → 245 (4|4) → 238 27 (4|4) → 43 → 86 → 140 (8|8) → 151 | 238 (4|4) → 92 → 184 (8|4) → 238 46 (8|4) → 93 → 186 (4|8) → 46 238 (4|4) → 92 → 184 (8|4) → 238 151 (8|8) → 69 → 138 (8|4) → 151 |
| 151 (8|4) → 73 → 146 (4|4) → 151 151 (4|4) → 85 → 170 (8|4) → 151 | |
| 27 (4|4) → 43 → 86 → 60 (4|4) → 39 | 39 (8|8) → 69 → 138 (4|4) → 39 |
| 39 (8|4) → 79 → 158 (4|4) → 39 39 (4|4) → 85 → 170 (4|4) → 39 | |
| 27 (4|8) → 46 → 92 → 140 (8|8) →151 | 151 (8|8) → 69 → 138 (8|4) → 151 |
| 151 (8|4) → 73 → 146 (4|4) →151 151 (4|4) → 85 → 170 (8|4) → 151 | |
| 28 (8|8) → 19 → 38 → 59 (4|4) → 39 | 39 (8|8) → 69 → 138 (4|4) → 39 |
| 39 (8|4) → 79 → 158 (4|4) → 39 39 (4|4) → 85 → 170 (4|4) → 39 | |
| 28 (8|8) → 23 → 46 → 190 (4|8) → 162 | 162 (8|4) → 82 → 164 (8|8) → 162 |
| 29 (8|8) → 19 → 38 → 197 (4|4) → 216 29 (8|8) → 23 → 46 → 213 (4|4) → 200 29 (4|4) → 43 → 86 → 54 (4|4) → 43 | 216 (4|8) → 50 → 100 (4|8) → 216 200 (4|4) → 52 → 104 (4|4) → 200 43 (8|8) → 45 → 90 (4|4) → 43 |
| 43 (4|8) → 69 → 138 (4|4) → 43 | |
| 39 (8|8) → 69 → 138 → 108 (4|8) → 75 | 75 (8|8) → 69 → 138 (4|4) → 75 |
| 75 (8|16) → 70 → 140 (4|4) → 75 | |
| 75 (8|16) → 70 → 140 → 143 (8|8) → 196 | 196 (8|4) → 99 → 198 (4|8) → 196 |
| 196 (8|4) → 100 → 200 (4|8) → 196 | |
| 77 (8|8) → 69 → 138 → 102 (4|4) → 43 | 43 (8|8) → 45 → 90 (4|4) → 43 |
| 43 (4|8) → 69 →138 (4|4) → 43 | |
| 43 (8|8) → 45 → 90 (4|4) → 43 | |
| 43 (4|8) → 69 → 138 (4|4) → 43 | |
| 77 (8|16) → 70 → 140 → 239 (4|4) → 162 77 (8|16) → 70 → 140 → 31 (4|4) → 82 77 (16|4) → 85 → 170 → 149 (8|8) → 216 97 (4|4) → 99 → 198 → 195 (4|4) → 162 97 (4|4) → 100 → 200 → 147 (4|4) → 242 | 162 (8|4) → 82 → 164 (8|8) → 162 82 (4|4) → 113 → 226 (4|4) → 82 216 (4|8) → 50 → 100 (4|8) → 216 162 (8|4) → 82 → 164 (8|8) → 162 242 (8|4) → 113 → 226 (8|8) → 242 |
| 242 (4|8) → 119 → 238 (4|8) → 242 | |
| 108 (4|16) → 70 → 140 → 166 (4|4) → 202 | 202 (4|4) → 35 → 70 (4|4) → 202 |
| 202 (4|4) → 43 → 86 (4|4) → 202 202 (4|8) → 74 → 148 (4|4) → 202 202 (4|4) → 99 → 198 (4|4) → 202 202 (4|4) → 100 → 200 (4|4) → 202 | |
| 154 (4|4) → 73 → 146 → 85 (4|8) → 207 154 (4|8) → 105 → 210 → 82 (4|4) →200 154 (4|8) → 105 → 210 → 189 (8|4) → 39 154 (4|8) → 105 → 210 → 189 (8|4) → 39 | 207 (4|4) → 35 → 70 (4|4) → 207 200 (4|4) → 52 → 104 (4|4) → 200 39 (8|8) → 69 → 138 (4|4) → 39 39 (8|4) → 79 → 158 (4|4) → 39 |
| 39 (4|4) → 85 → 170 (4|4) → 39 | |
| 202 (4|4) → 43 → 86 → 18 (4|4) → 216 202 (4|8) → 74 → 148 → 215 (4|4) → 29 | 216 (4|8) → 50 → 100 (4|8) → 216 29 (8|8) → 19 → 38 (8|8) → 29 |
| 29 (8|8) → 23 → 46 (16|8) → 29 29 (4|4) → 43 → 86 (4|8) → 29 29 (4|8) →46 → 92 (4|8) → 29 | |
| 221 (8|4) → 82 → 164 → 181 (4|4) → 104 | 104 (4|8) → 50 → 100 (8|8) → 104 |
| 104 (4|4) → 52 → 104 (4|8) → 104 |
| Input difference → Difference after Stage1 → Difference after Stage2 → Difference after Stage3 | Input difference → Difference after Stage1 → Difference after Stage2 → Difference after Stage3 |
|---|---|
| 27 (8|8) → 19 → 53 (8|4) → 238 27 (4|4) → 25 → 43 (4|8) → 46 27 (4|4) → 27 → 45 (4|8) → 46 27 (8|8) → 19 → 53 (8|4) → 238 27 (8|8) → 19 → 53 (4|4) → 151 27 (8|8) → 23 → 57 (4|4) → 39 27 (8|8) → 19 → 53 (4|4) → 151 28 (8|8) → 119 → 153 (4|4) → 39 28 (4|4) → 73 → 219 (4|4) → 162 29 (4|4) → 43 → 125 (16|16) → 216 29 (4|4) → 73 → 219 (4|4) → 200 29 (4|4) → 25 → 43 (4|4) → 43 29 (4|4) → 27 → 45 (4|4) → 43 29 (4|4) → 43 → 125 (4|4) → 43 39 (4|4) → 43 → 125 (4|4) → 75 39 (8|8) → 45 → 119 (8|8) → 75 75 (8|16) → 70 → 202 (4|8) → 196 | 77 (4|4) → 73 → 219 (4|4) → 162 77 (4|4) → 25 → 43 (4|4) → 43 77 (4|4) → 73 → 219 (4|4) → 82 77 (4|4) → 73 → 219 (4|4) → 216 97 (4|4) → 52 → 92 (4|4) → 162 97 (4|8) → 50 → 86 (4|4) → 241 108 (4|8) → 120 → 136 (4|4) → 202 154 (4|4) → 73 → 219 (4|4) → 207 154 (4|8) → 120 → 136 (4|4) → 207 154 (4|4) → 73 → 219 (4|4) → 200 154 (4|4) → 113 → 147 (4|4) → 39 202 (4|4) → 73 → 219 (4|4) → 216 202 (4|4) → 79 → 209 (4|4) → 216 202 (4|4) → 73 → 219 (8|4) → 29 221 (4|8) → 44 → 116 (16|16) → 104 221 (4|4) → 79 → 209 (4|4) → 104 |
Publisher’s Note: MDPI stays neutral with regard to jurisdictional claims in published maps and institutional affiliations. |
© 2022 by the authors. Licensee MDPI, Basel, Switzerland. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/).
Share and Cite
Algazy, K.; Sakan, K.; Kapalova, N.; Nyssanbayeva, S.; Dyusenbayev, D. Differential Analysis of a Cryptographic Hashing Algorithm HBC-256. Appl. Sci. 2022, 12, 10173. https://doi.org/10.3390/app121910173
Algazy K, Sakan K, Kapalova N, Nyssanbayeva S, Dyusenbayev D. Differential Analysis of a Cryptographic Hashing Algorithm HBC-256. Applied Sciences. 2022; 12(19):10173. https://doi.org/10.3390/app121910173
Chicago/Turabian StyleAlgazy, Kunbolat, Kairat Sakan, Nursulu Kapalova, Saule Nyssanbayeva, and Dilmukhanbet Dyusenbayev. 2022. "Differential Analysis of a Cryptographic Hashing Algorithm HBC-256" Applied Sciences 12, no. 19: 10173. https://doi.org/10.3390/app121910173
APA StyleAlgazy, K., Sakan, K., Kapalova, N., Nyssanbayeva, S., & Dyusenbayev, D. (2022). Differential Analysis of a Cryptographic Hashing Algorithm HBC-256. Applied Sciences, 12(19), 10173. https://doi.org/10.3390/app121910173







